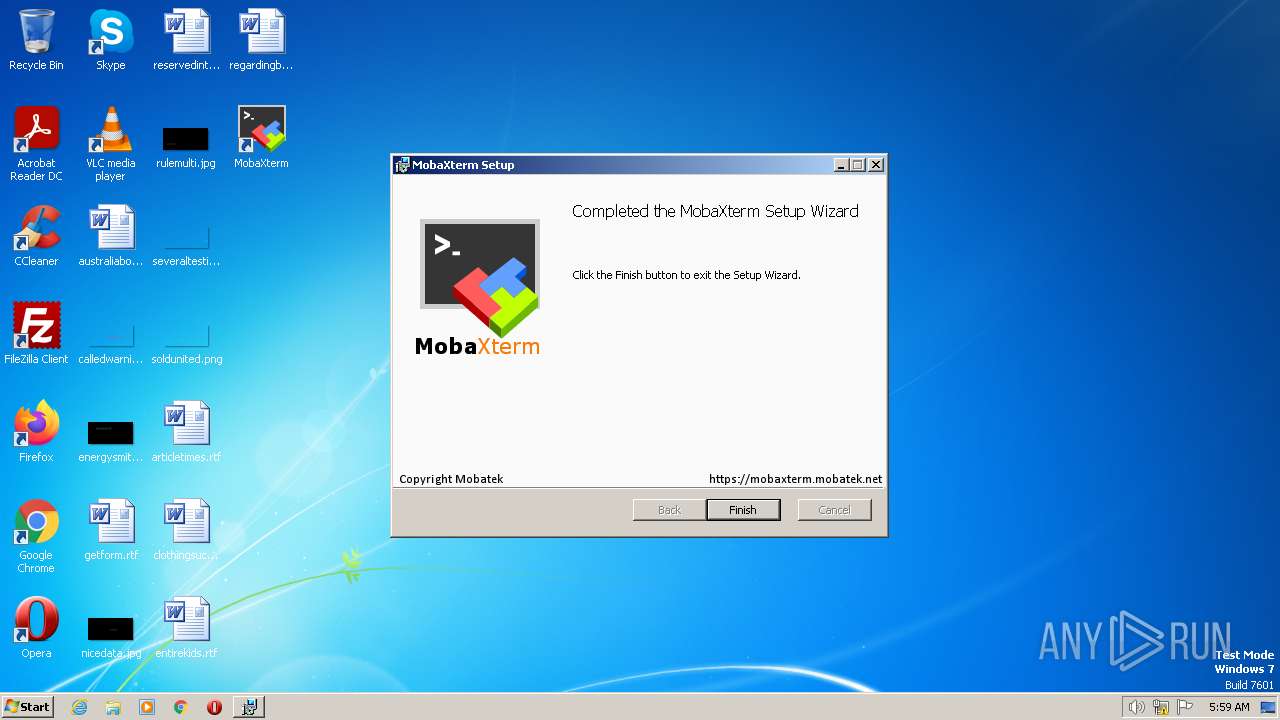
| File name: | MobaXterm_installer_23.2.msi |
| Full analysis: | https://app.any.run/tasks/9e76bfec-27a9-41fc-99c5-ce2f2aaa9d89 |
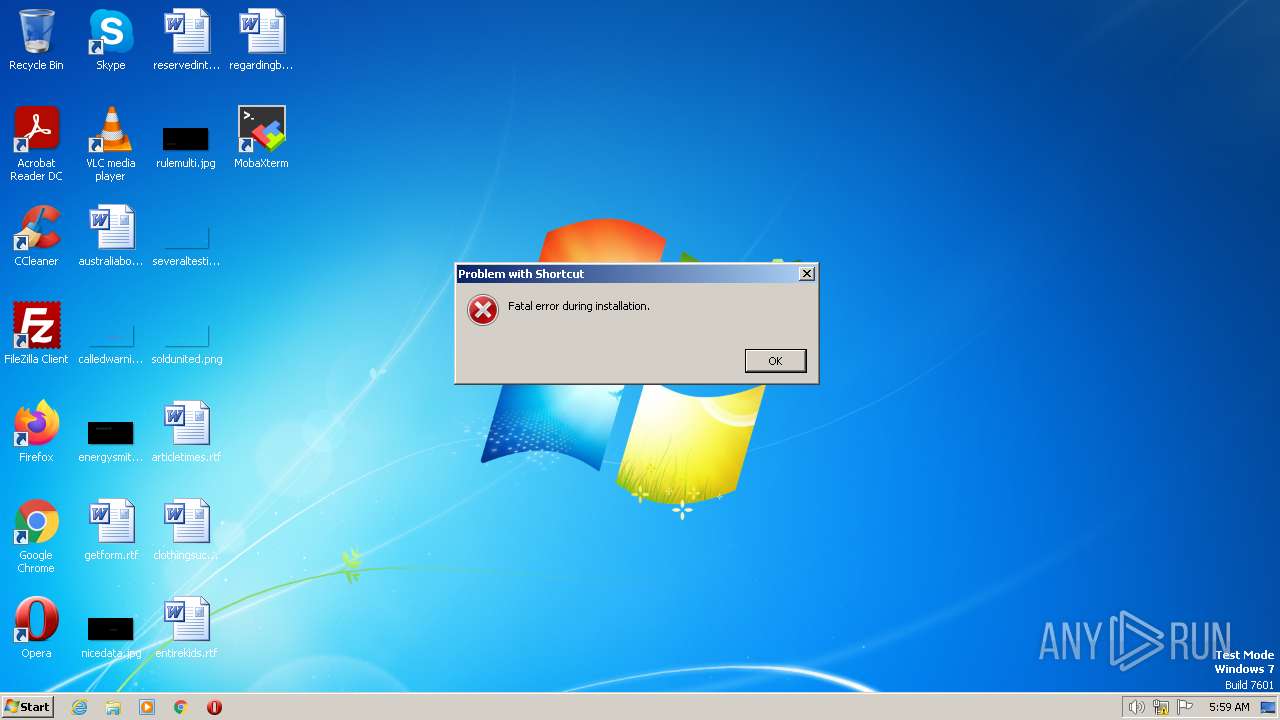
| Verdict: | Malicious activity |
| Analysis date: | July 05, 2023, 04:58:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-msi |
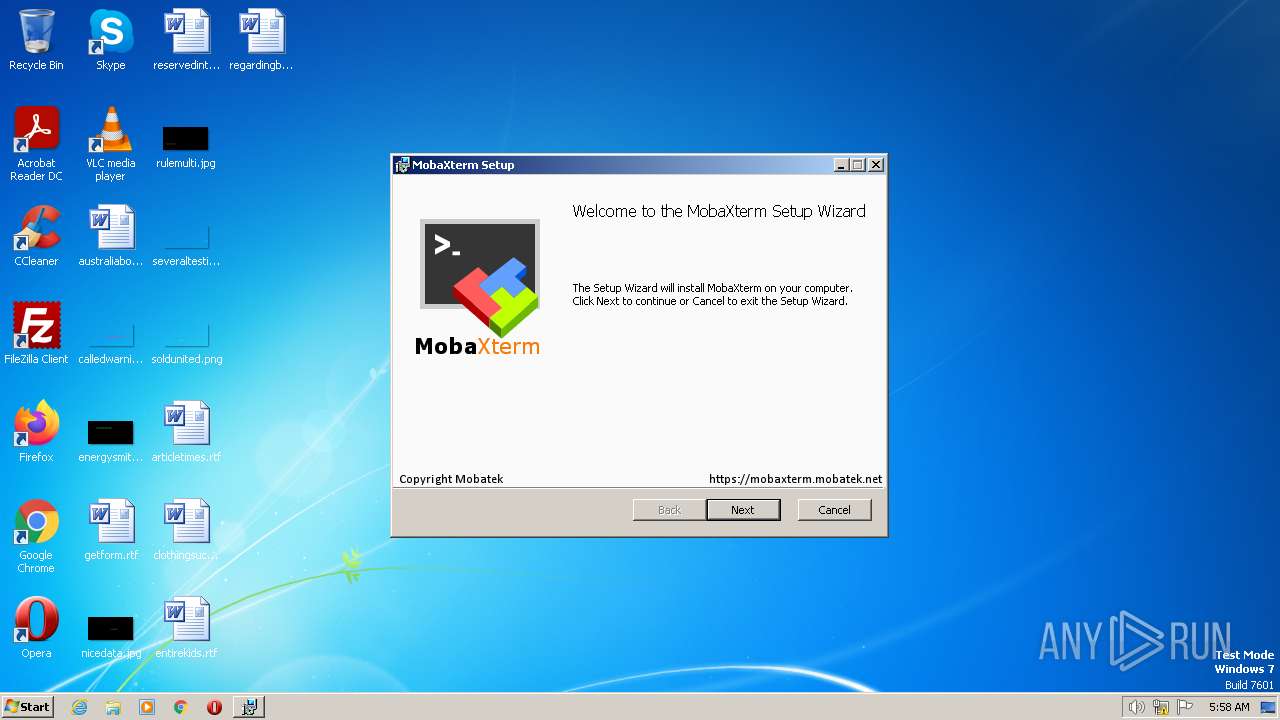
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Code page: 1252, Title: Installation Database, Subject: MobaXterm, Author: Mobatek, Keywords: Installer, Comments: This installer database contains the logic and data required to install MobaXterm., Template: Intel;1033, Revision Number: {CB9BD629-035F-4DA5-B84C-786DD2695428}, Create Time/Date: Wed Jun 7 19:41:26 2023, Last Saved Time/Date: Wed Jun 7 19:41:26 2023, Number of Pages: 100, Number of Words: 2, Name of Creating Application: Windows Installer XML (3.0.5419.0), Security: 2 |
| MD5: | B15EA815052427883CFD21E07633A00F |
| SHA1: | A507F5FB3F5537288494E8B1DCB229B3841B877B |
| SHA256: | 6A57452B5E8C01E2097AE0DAEFD2A350F4C3075E42EC7DA246F89EB2E1A40124 |
| SSDEEP: | 393216:06lU+V34SHjBwLVmkPgg7yREYH9qpuZ5:VV34SHjSXUEYIpuZ5 |
MALICIOUS
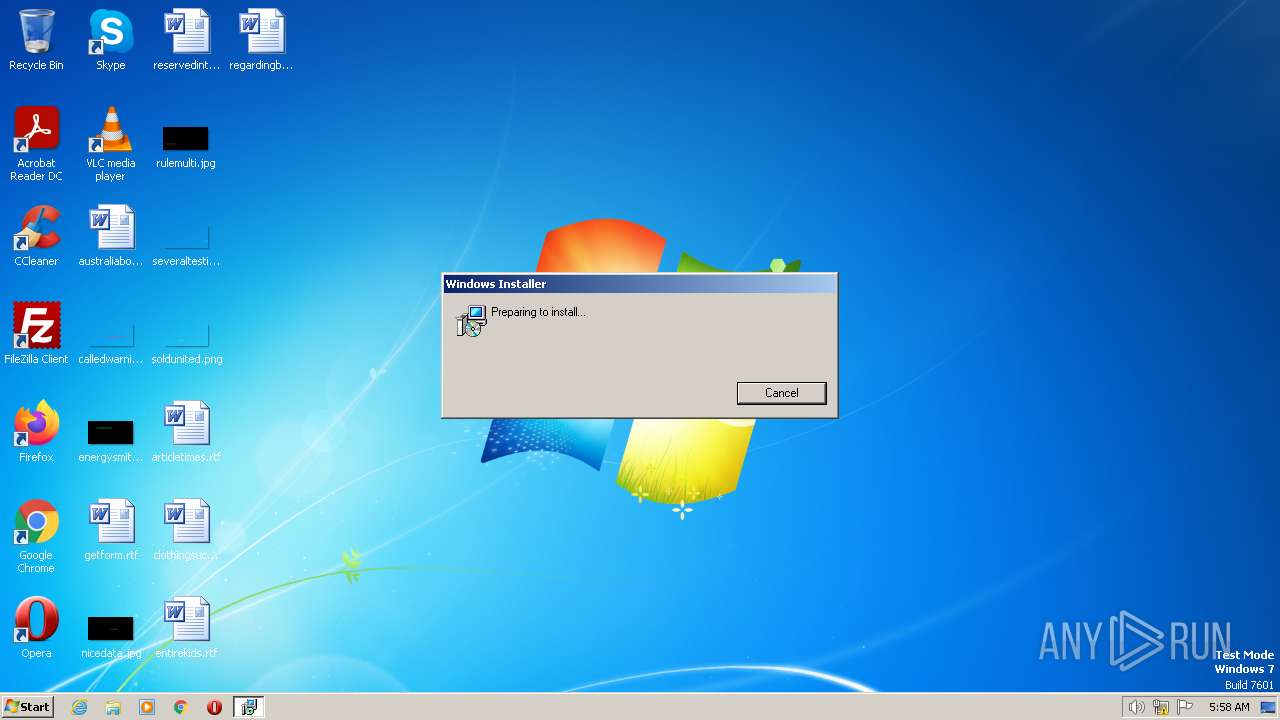
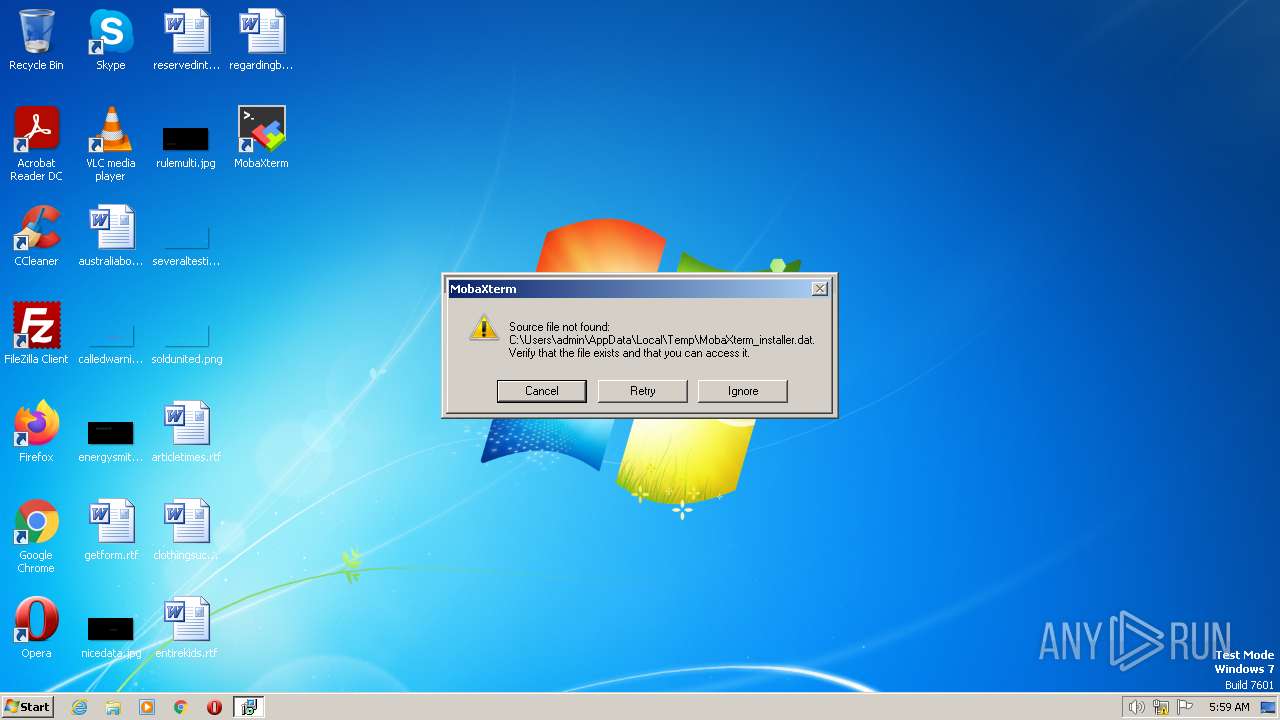
Loads dropped or rewritten executable
- msiexec.exe (PID: 3344)
- msiexec.exe (PID: 3676)
- msiexec.exe (PID: 3688)
Application was dropped or rewritten from another process
- MobaXterm.exe (PID: 2056)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 528)
Checks Windows Trust Settings
- msiexec.exe (PID: 3404)
Executable content was dropped or overwritten
- MobaXterm.exe (PID: 2056)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 3404)
INFO
The process checks LSA protection
- msiexec.exe (PID: 3008)
- msiexec.exe (PID: 3404)
- msiexec.exe (PID: 4048)
- VSSVC.exe (PID: 528)
- msiexec.exe (PID: 3344)
- msiexec.exe (PID: 3676)
- msiexec.exe (PID: 3688)
Reads the computer name
- msiexec.exe (PID: 3404)
- msiexec.exe (PID: 4048)
- msiexec.exe (PID: 3344)
- msiexec.exe (PID: 3676)
- MobaXterm.exe (PID: 2056)
- msiexec.exe (PID: 3688)
Checks supported languages
- msiexec.exe (PID: 3404)
- msiexec.exe (PID: 4048)
- msiexec.exe (PID: 3344)
- msiexec.exe (PID: 3676)
- MobaXterm.exe (PID: 2056)
- msiexec.exe (PID: 3688)
Reads the machine GUID from the registry
- msiexec.exe (PID: 3404)
- msiexec.exe (PID: 4048)
- msiexec.exe (PID: 3344)
- msiexec.exe (PID: 3676)
- msiexec.exe (PID: 3688)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3008)
- msiexec.exe (PID: 3404)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 3008)
Application launched itself
- msiexec.exe (PID: 3404)
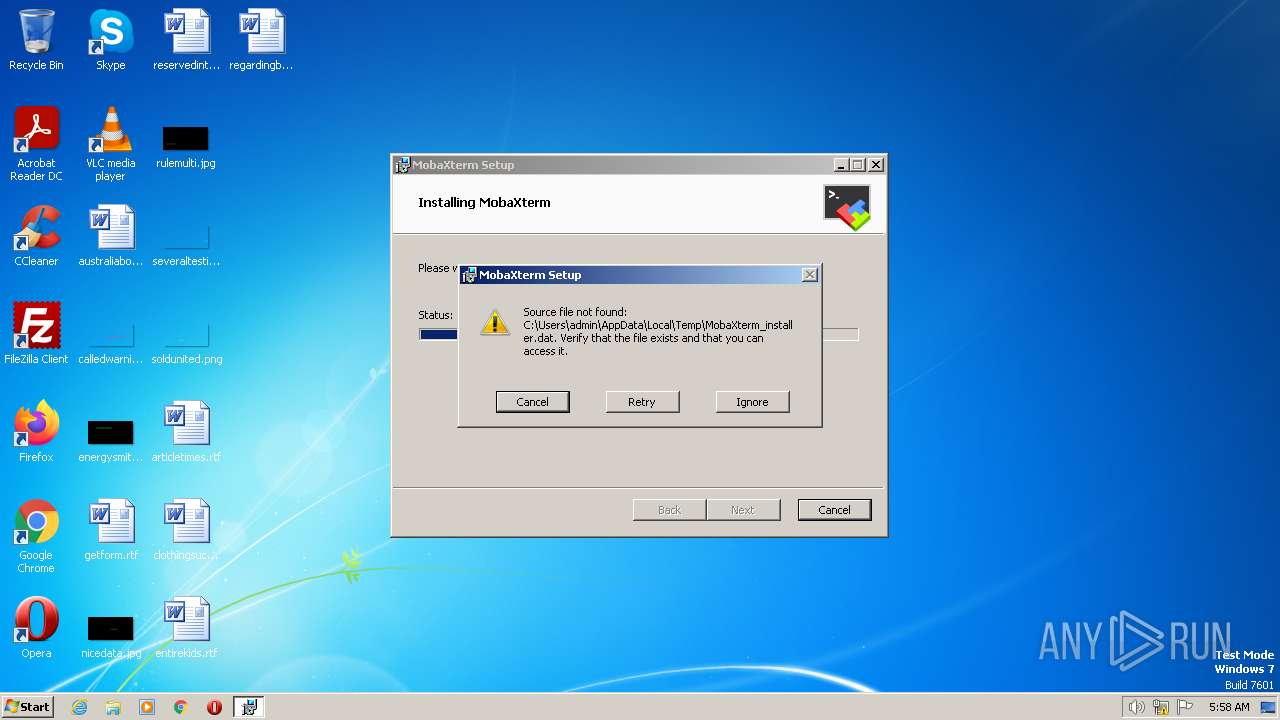
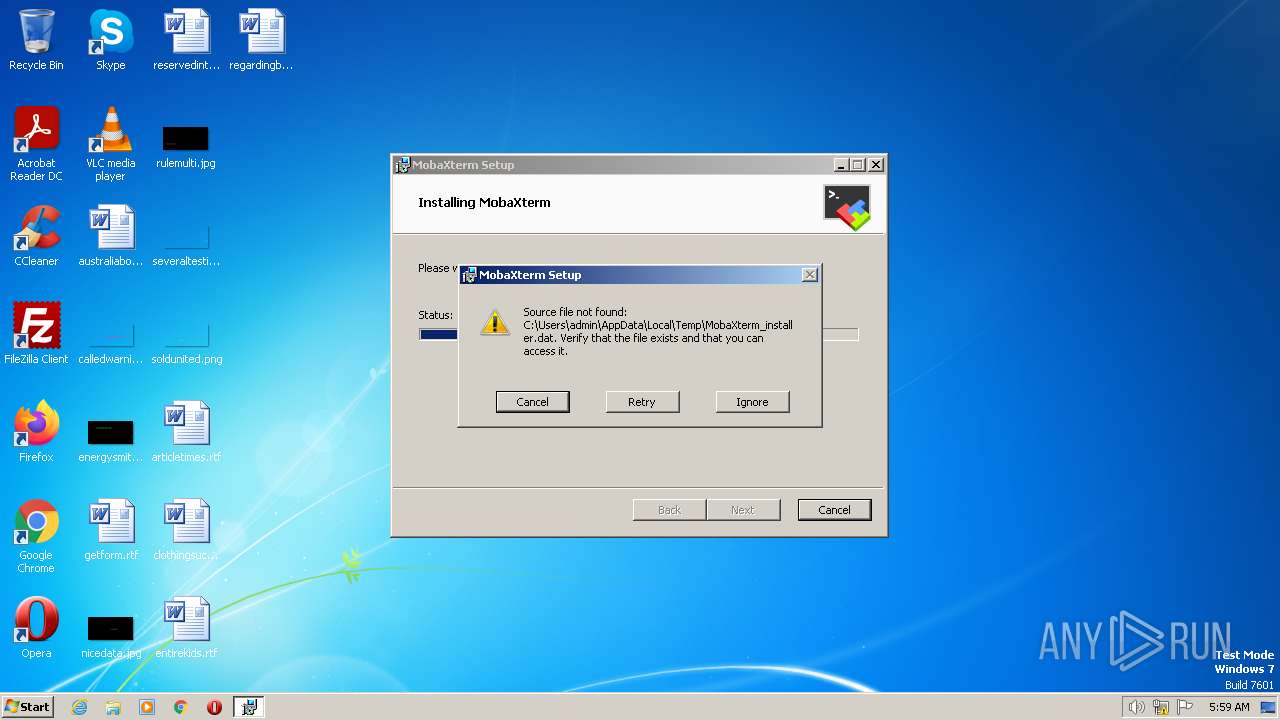
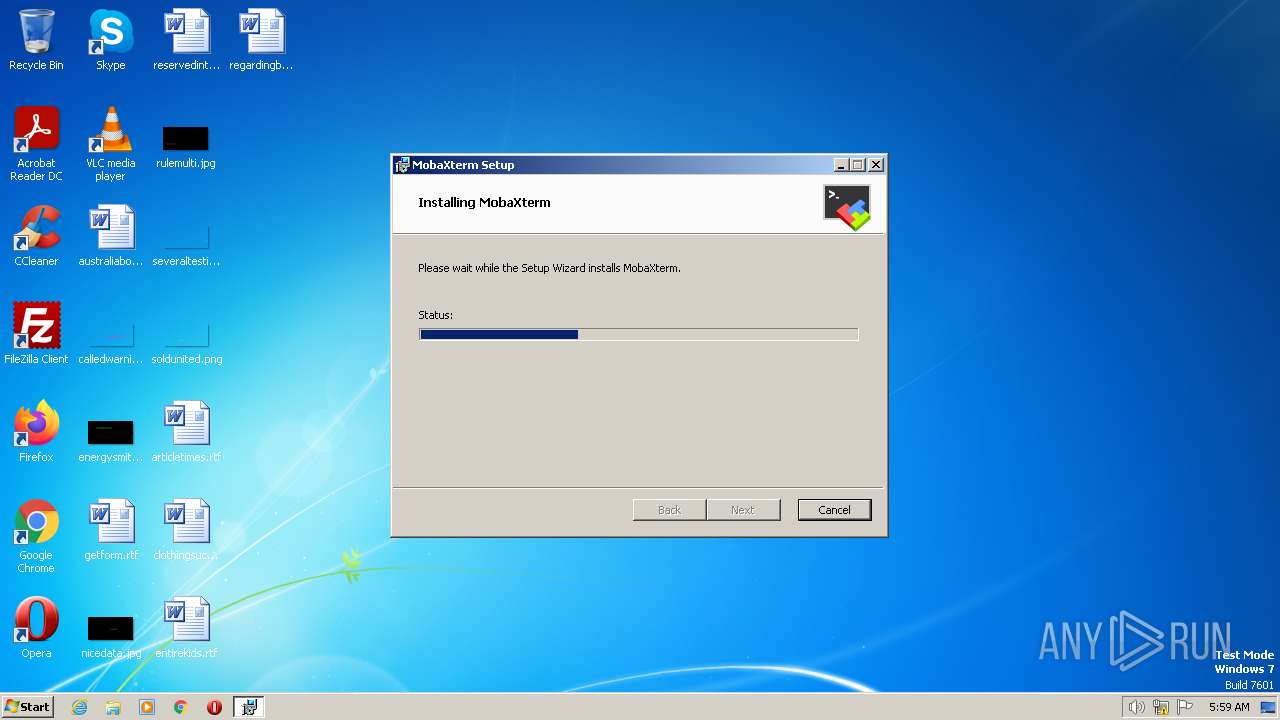
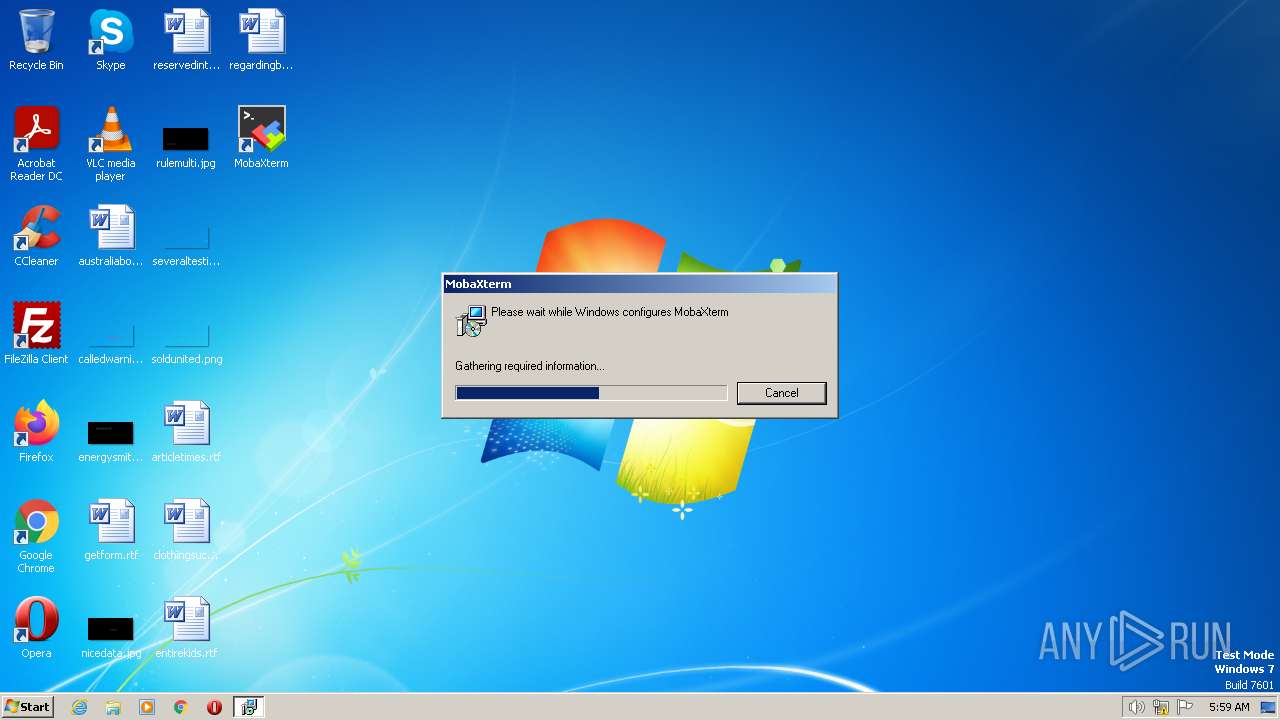
Create files in a temporary directory
- msiexec.exe (PID: 3404)
- msiexec.exe (PID: 3008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Security: | Read-only recommended |
|---|---|
| Software: | Windows Installer XML (3.0.5419.0) |
| Words: | 2 |
| Pages: | 100 |
| ModifyDate: | 2023:06:07 19:41:26 |
| CreateDate: | 2023:06:07 19:41:26 |
| RevisionNumber: | {CB9BD629-035F-4DA5-B84C-786DD2695428} |
| Template: | Intel;1033 |
| Comments: | This installer database contains the logic and data required to install MobaXterm. |
| Keywords: | Installer |
| Author: | Mobatek |
| Subject: | MobaXterm |
| Title: | Installation Database |
| CodePage: | Windows Latin 1 (Western European) |
Total processes
47
Monitored processes
8
Malicious processes
1
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 528 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2056 | "C:\Program Files\Mobatek\MobaXterm\MobaXterm.exe" -instunpack -msipath C:\Users\admin\AppData\Local\Temp\MobaXterm_installer_23.2.msi | C:\Program Files\Mobatek\MobaXterm\MobaXterm.exe | msiexec.exe | ||||||||||||
User: admin Company: Mobatek Integrity Level: MEDIUM Description: MobaXterm Exit code: 0 Version: 23.2.0.5082 Modules
| |||||||||||||||
| 3008 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\MobaXterm_installer_23.2.msi" | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3344 | C:\Windows\system32\MsiExec.exe -Embedding D0C0B25F0F3ADEDBDCCA03711276494D | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3404 | C:\Windows\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3676 | C:\Windows\system32\MsiExec.exe -Embedding 81DFD02E493124C0547D858CA0F4DC99 E Global\MSI0000 | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3688 | C:\Windows\system32\MsiExec.exe -Embedding FBB6748524DDDF9CF4C4D85717B2DDF4 | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4048 | C:\Windows\system32\MsiExec.exe -Embedding 4353965EBB2729D04D8191B69F63A41C C | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
10 349
Read events
10 275
Write events
53
Delete events
21
Modification events
| (PID) Process: | (3008) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3404) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 400000000000000011460B5E93FAD801F40E00002C040000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3404) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 400000000000000011460B5E93FAD801F40E00002C040000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3404) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 69 | |||
| (PID) Process: | (3404) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000F965AD5E93FAD801F40E00002C040000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3404) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Leave) |
Value: 4000000000000000B533446193FAD801F40E00002C040000D3070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3404) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppAddInterestingComponents (Enter) |
Value: 4000000000000000B533446193FAD801F40E00002C040000D4070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3404) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppAddInterestingComponents (Leave) |
Value: 40000000000000001745766193FAD801F40E00002C040000D4070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3404) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Leave) |
Value: 4000000000000000050A216393FAD801F40E00002C040000D0070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3404) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Leave) |
Value: 4000000000000000050A216393FAD801F40E00002C040000D5070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
6
Suspicious files
19
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3404 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3404 | msiexec.exe | C:\Windows\Installer\123a42.msi | — | |
MD5:— | SHA256:— | |||
| 3404 | msiexec.exe | C:\Windows\Installer\123a45.msi | — | |
MD5:— | SHA256:— | |||
| 3404 | msiexec.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\MobaXterm\MobaTextEditor.lnk | lnk | |
MD5:9F2594430CF3E40B6746FA21343909F9 | SHA256:83CD68B91EBC204682905EFE4A19CE5D47868CD34C39354C844725A40209AC6B | |||
| 2056 | MobaXterm.exe | C:\PROGRA~1\Mobatek\MOBAXT~1\version.dat | text | |
MD5:4503677F93CD0FFC50A11CF37EB12B38 | SHA256:44385A678A5C8D68A9AF74685AD8ABE57BDAEE64CBBB6020629F3CA2FB3EAA47 | |||
| 3676 | msiexec.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\MobaXterm\Visit MobaXterm Website.lnk | binary | |
MD5:8BBF32B2B0077A90D2F76FE50254CD2E | SHA256:1919064B1EC312A178641063C03A28A56E42649FE17D32CA6A98E7A6E1C7EEFC | |||
| 3404 | msiexec.exe | C:\Config.Msi\123a44.rbs | binary | |
MD5:C7650E5652DA9C072406D55393C38420 | SHA256:CD9A2B73E6A8A30492DD07F3FA551B91EB295FE0E391C38A7EA8E214771FFF5B | |||
| 2056 | MobaXterm.exe | C:\PROGRA~1\Mobatek\MOBAXT~1\MobaRTE.exe | executable | |
MD5:F05FC7AF70D81A183CD392905CE262B0 | SHA256:DBC859287E2CA0D7D3EB5D7F540B304858097416F019C15A78AC95C006C99908 | |||
| 3008 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI1881.tmp | executable | |
MD5:5EA7455A71A9B481D0D9402C4E4E19D7 | SHA256:428C16FAD8A8190A6090FA940C2EF2D5C13168F721D958750A874FF8C13C5A85 | |||
| 3404 | msiexec.exe | C:\Windows\Installer\MSI42AE.tmp | binary | |
MD5:4B4015BFEE2EE94CFAC120C4DDF7D86A | SHA256:6BC7251E7AE4E57D6B8D35F374A0832FC4B863C34FC24664D9CC80EE7911A228 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
292 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |