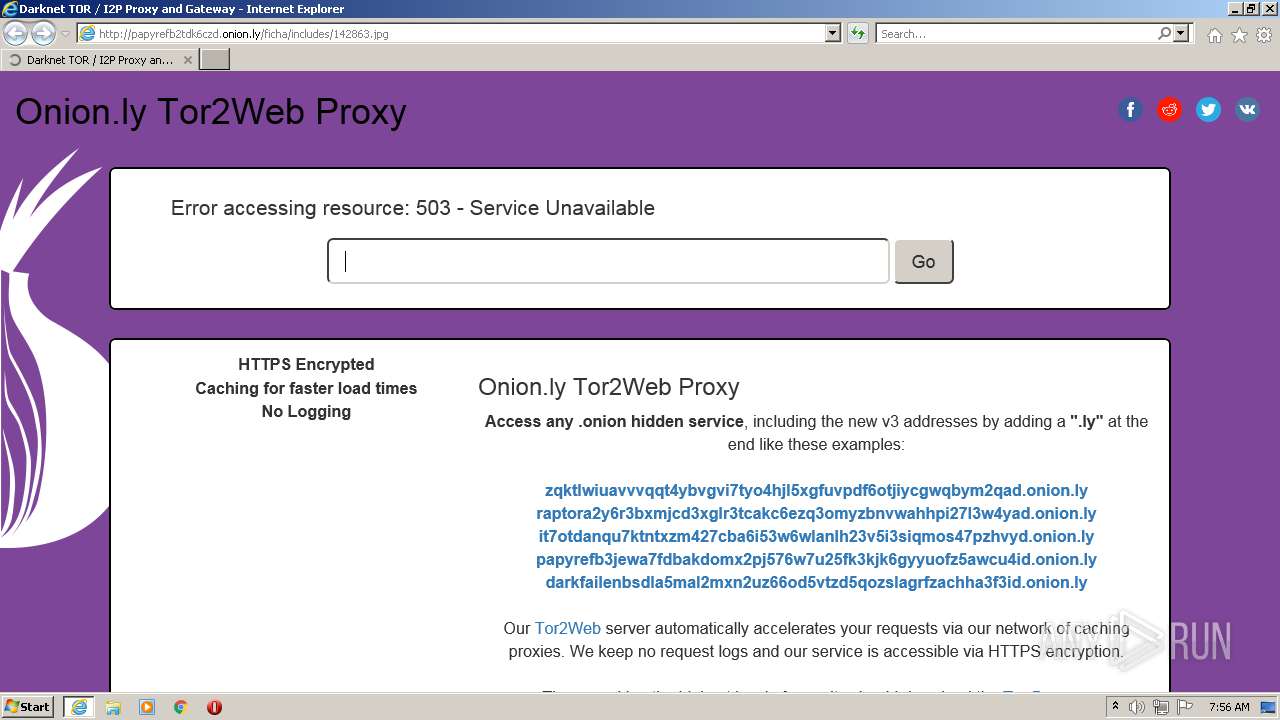
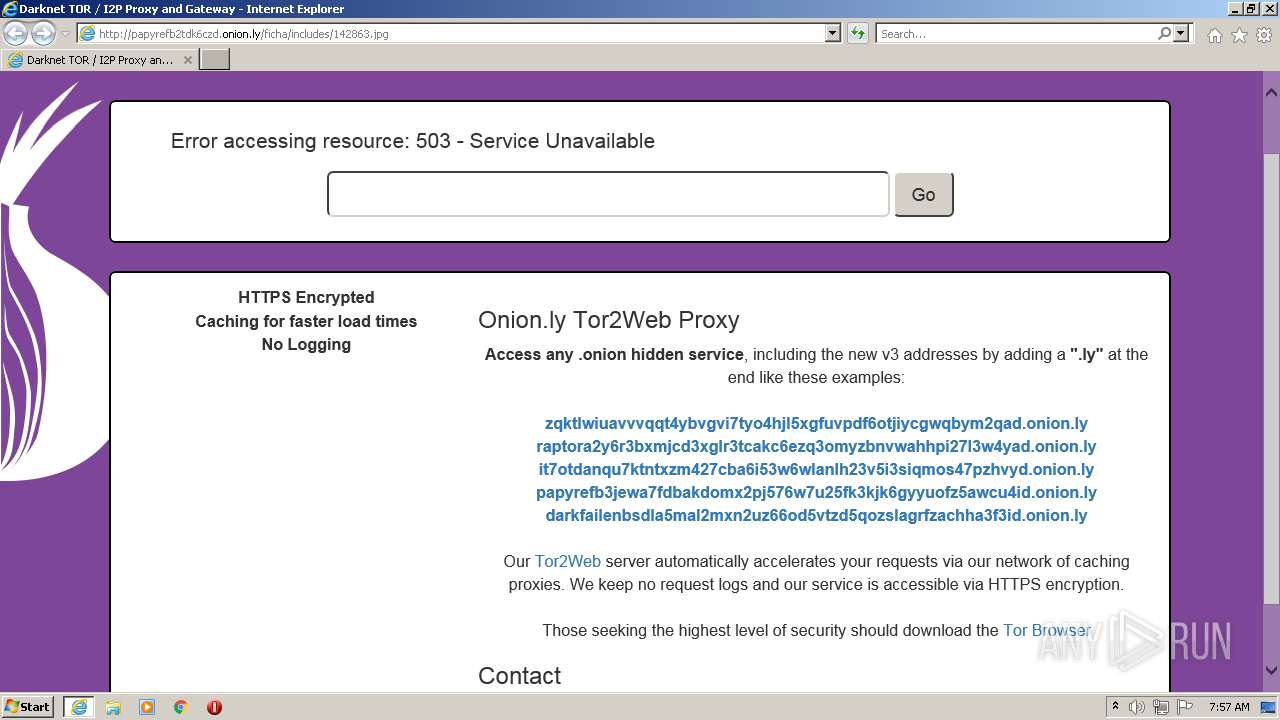
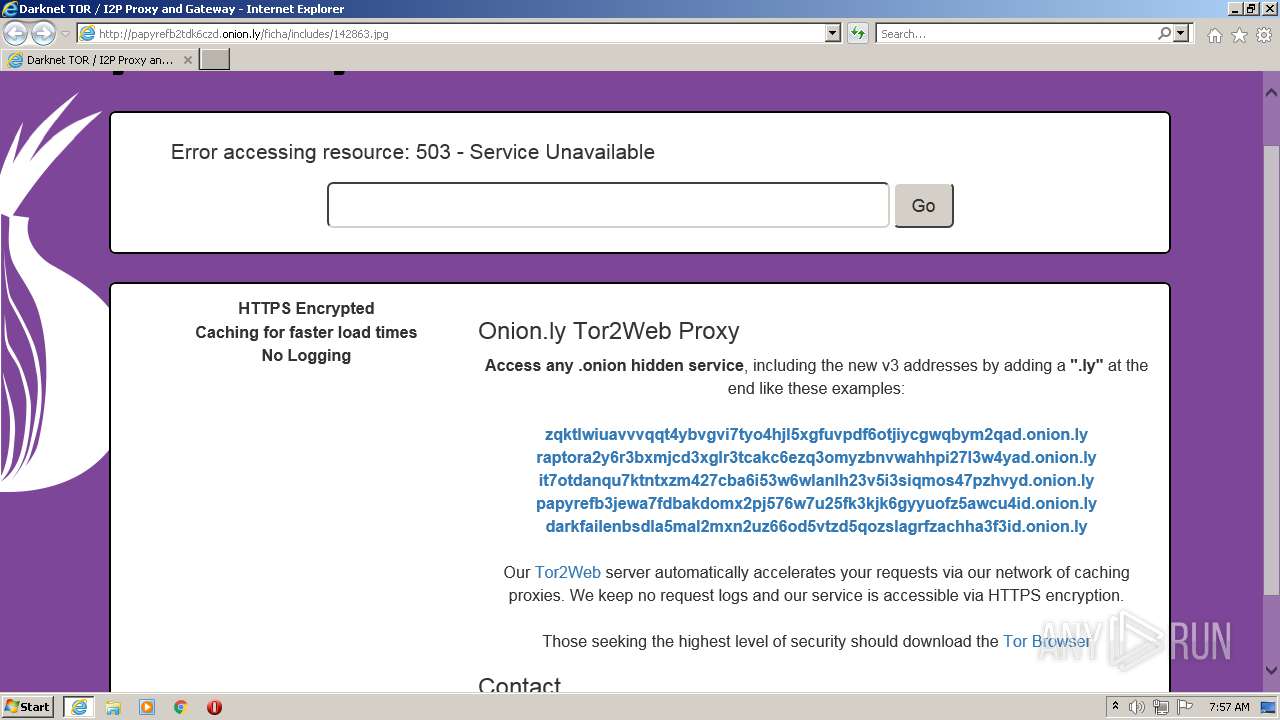
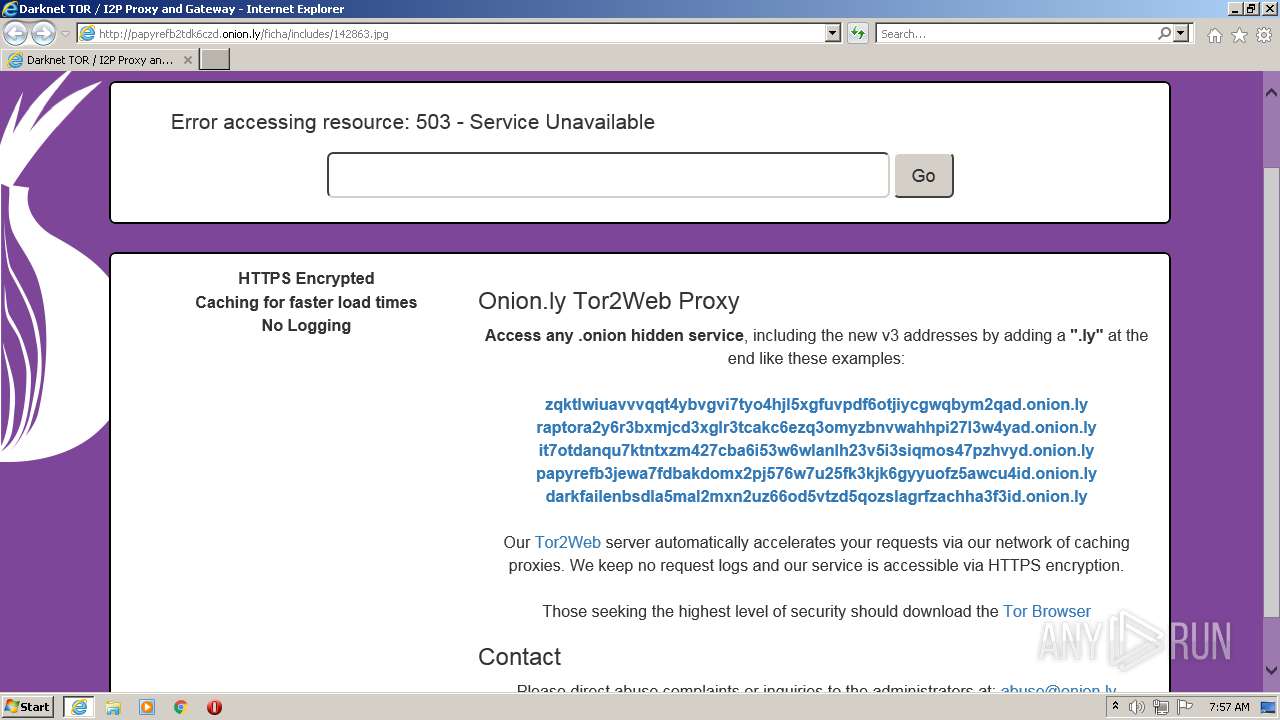
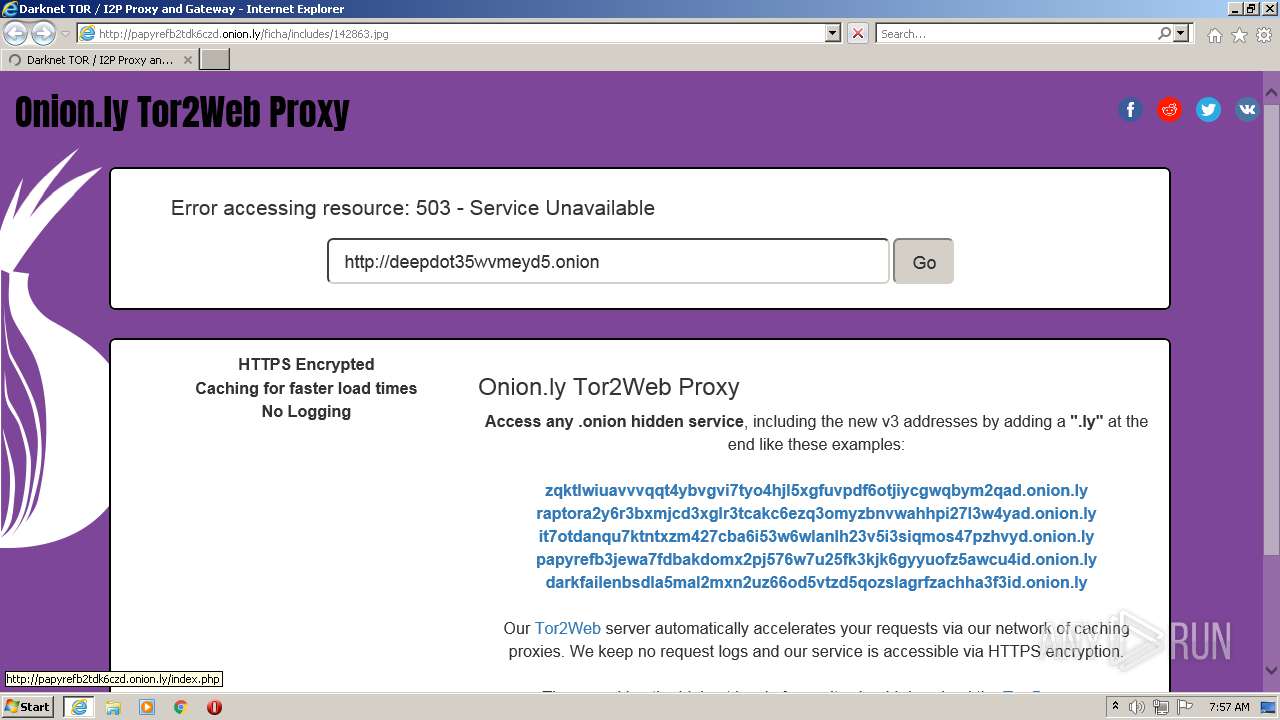
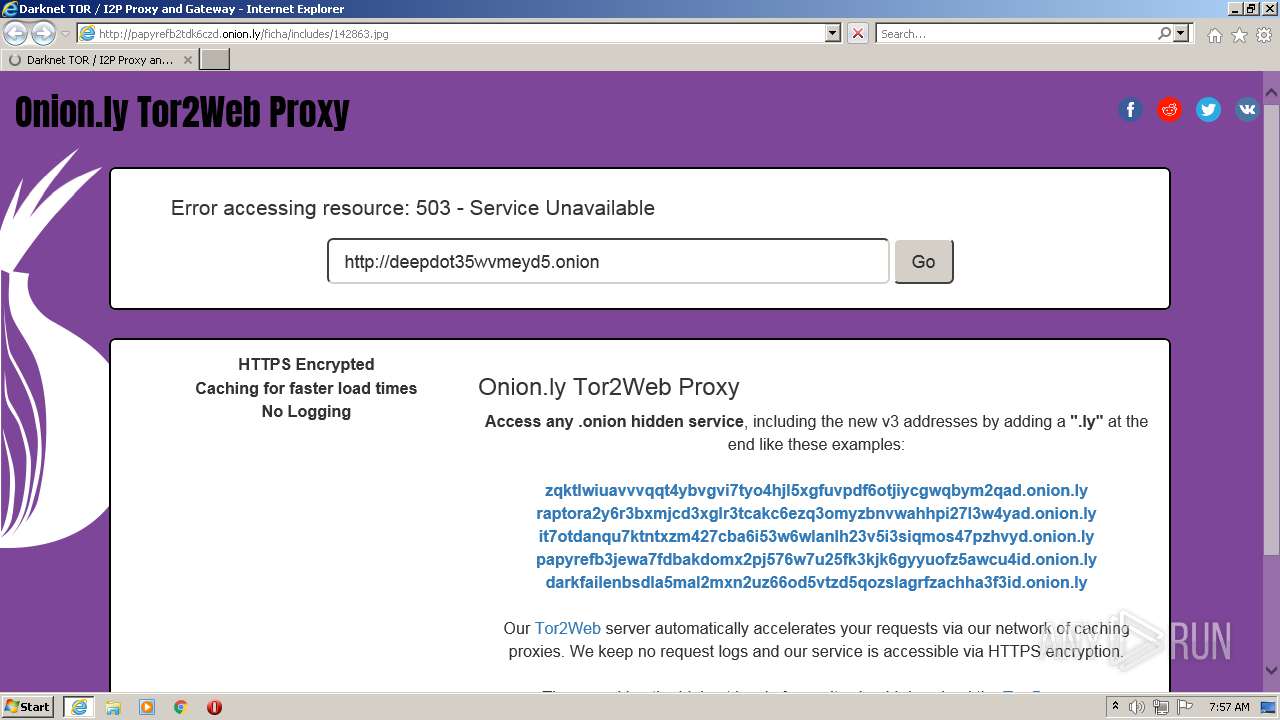
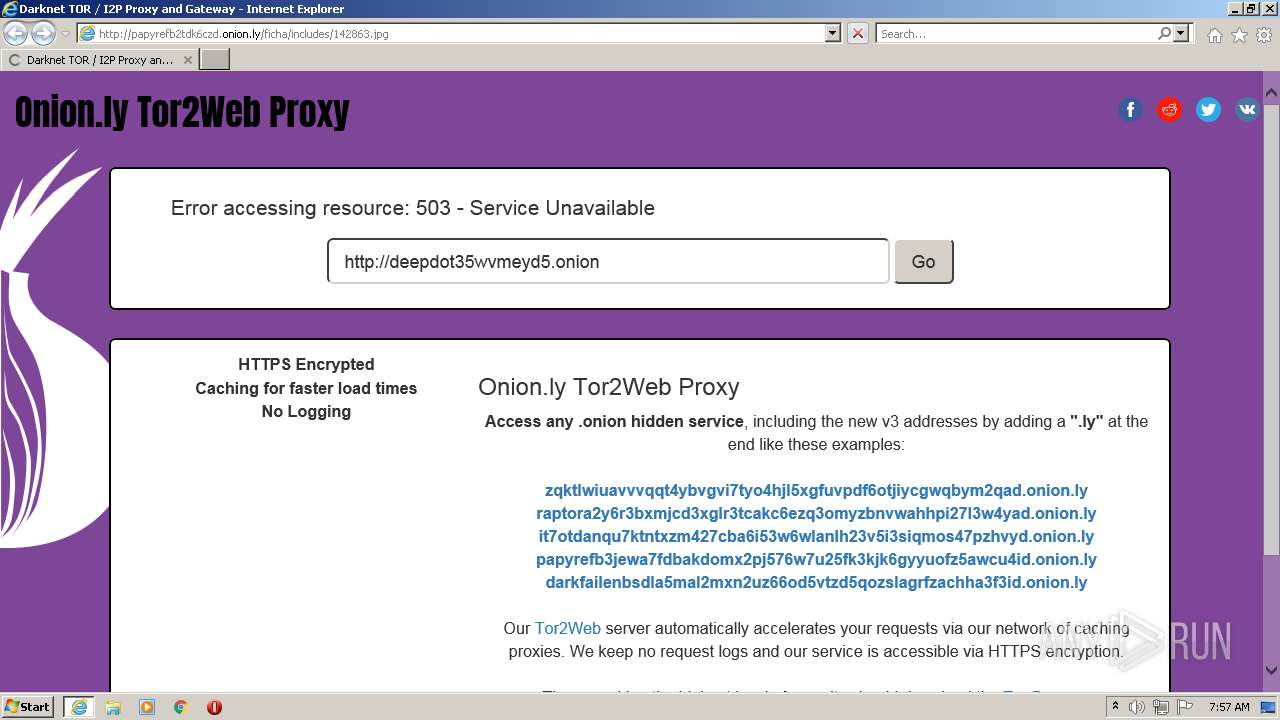
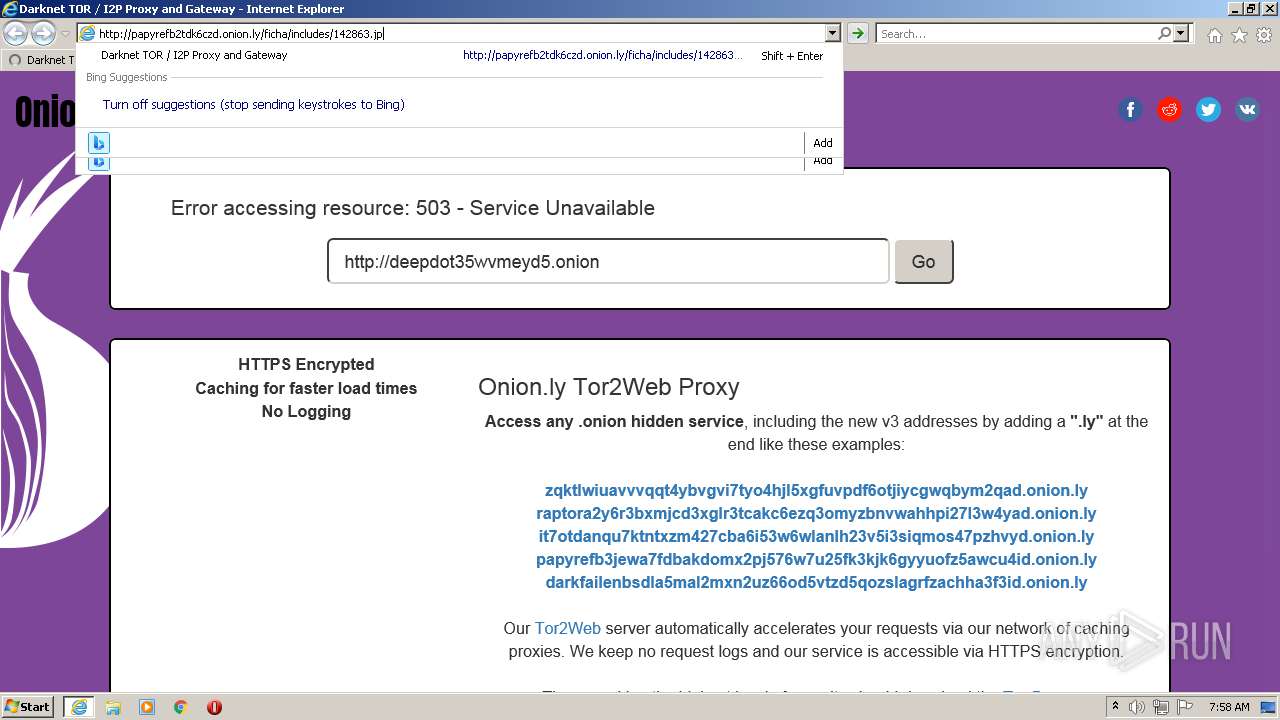
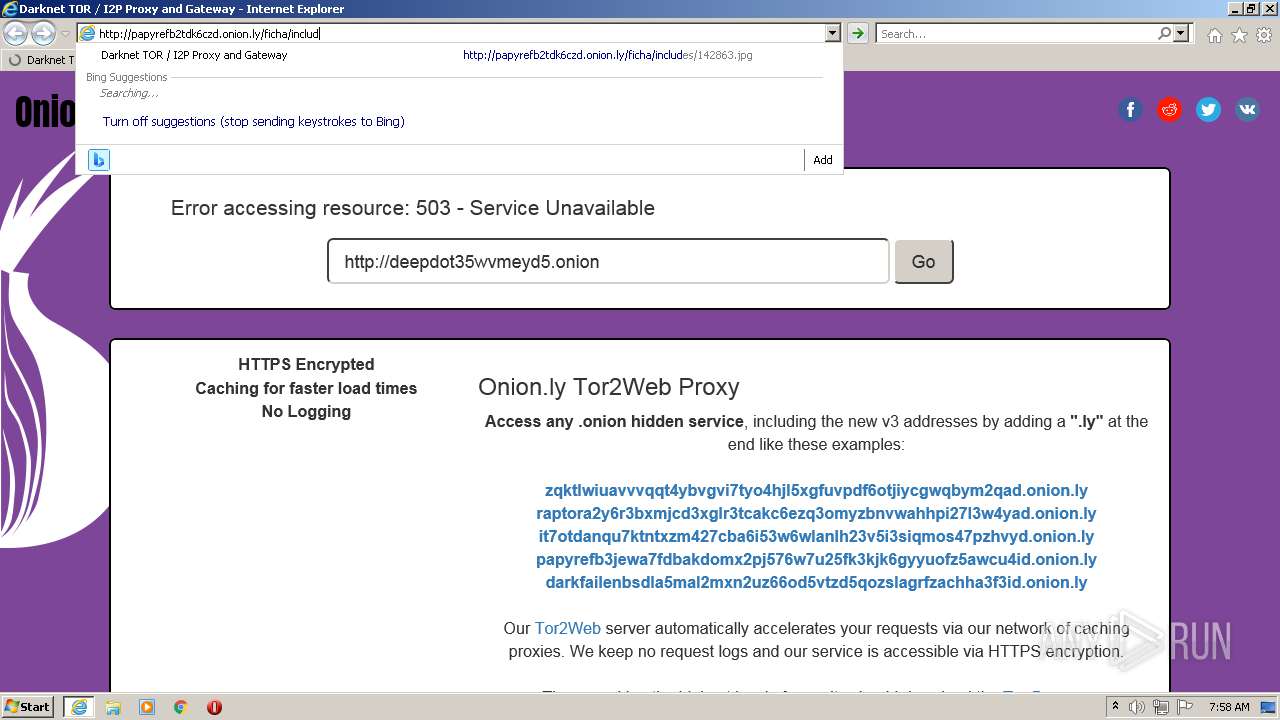
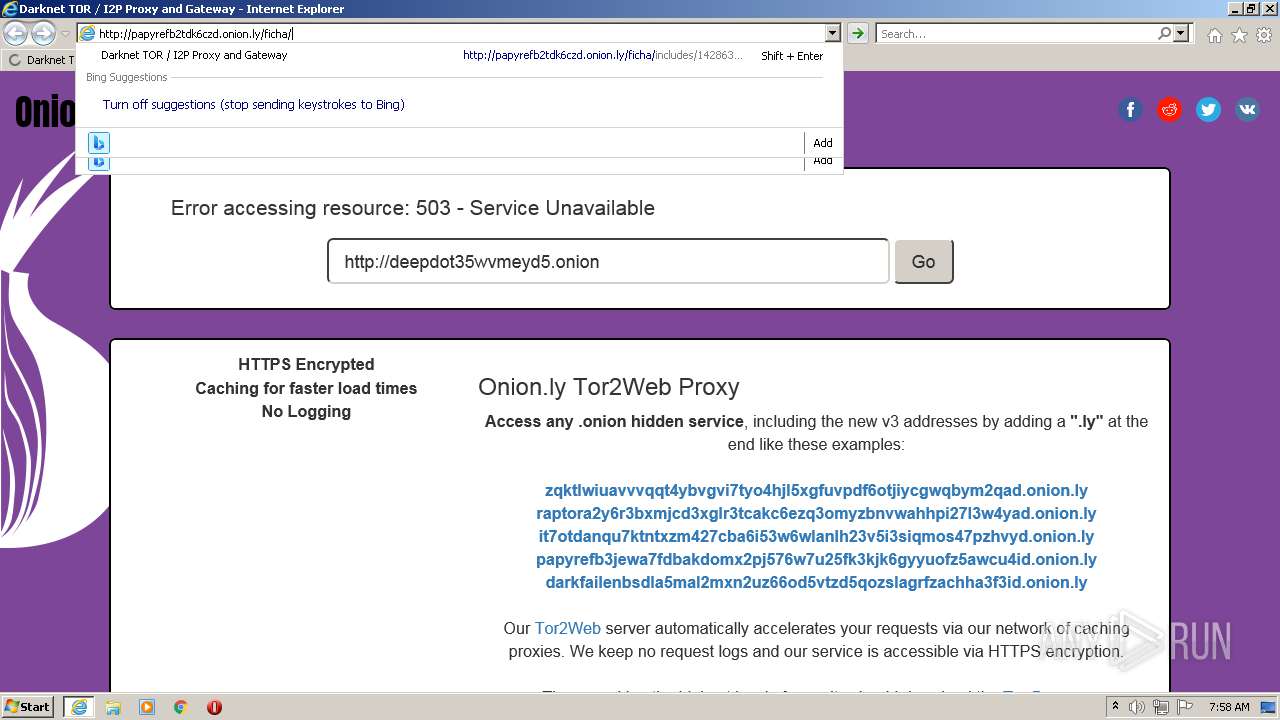
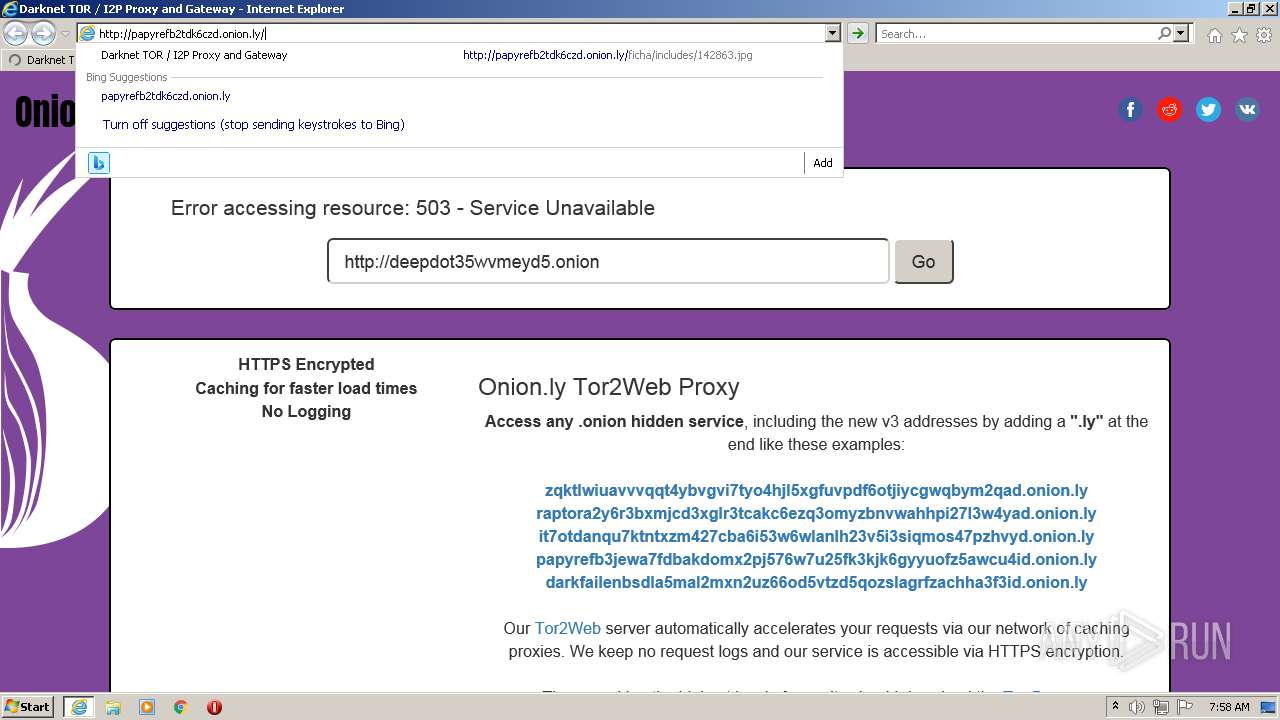
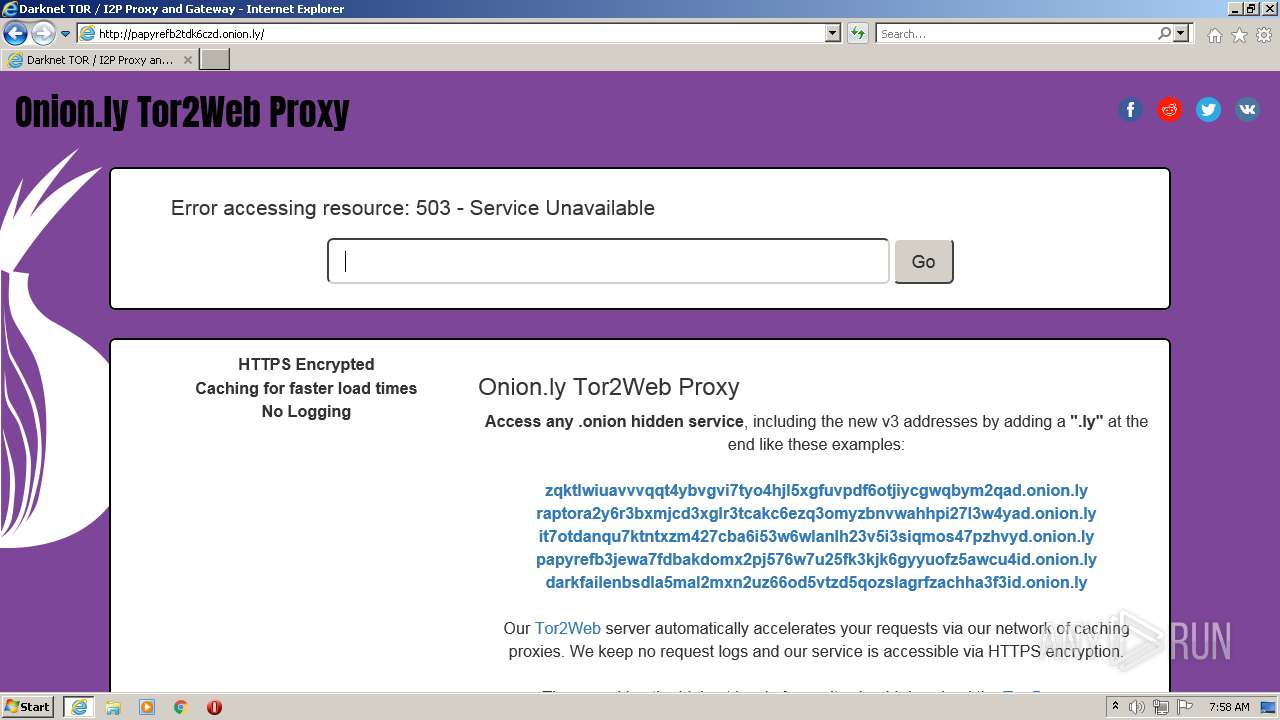
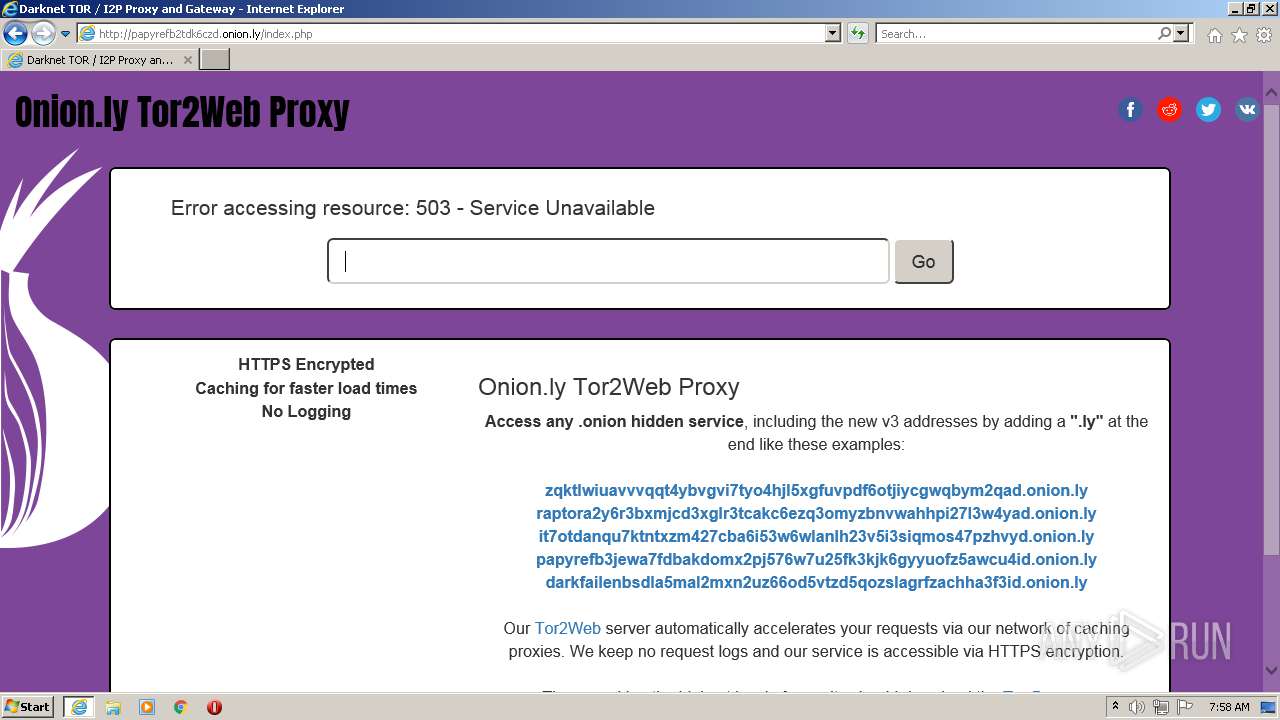
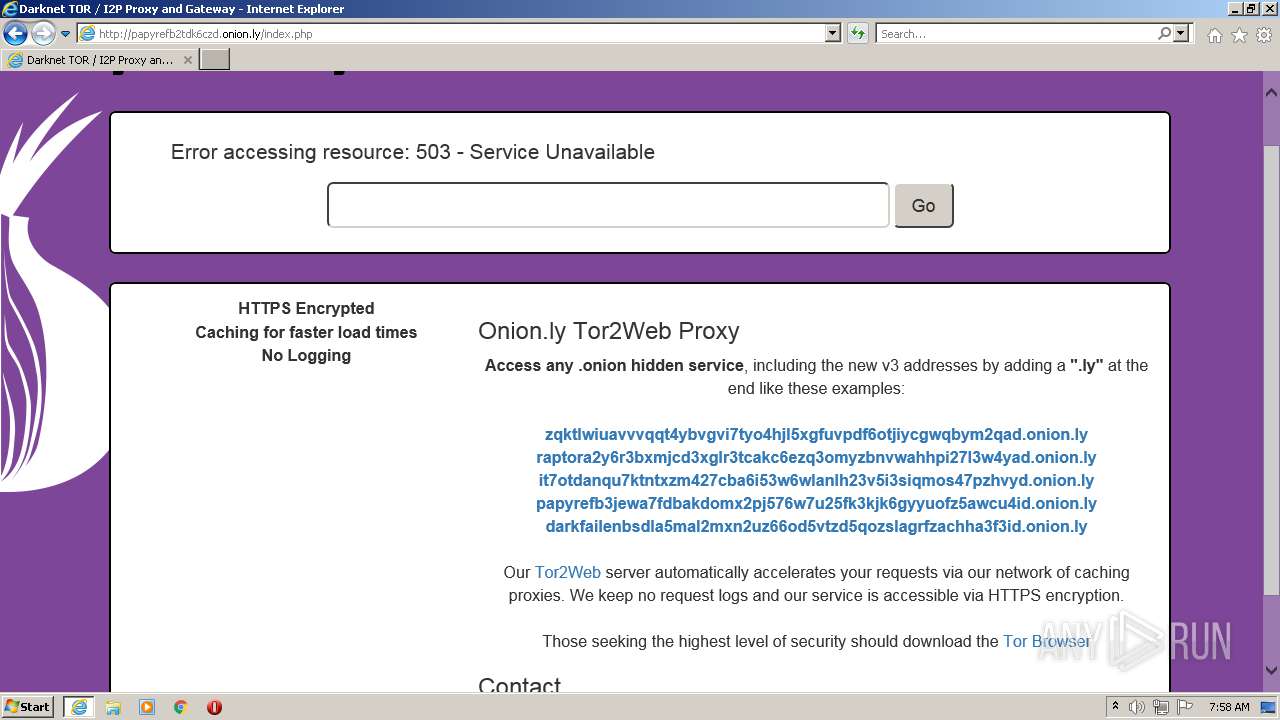
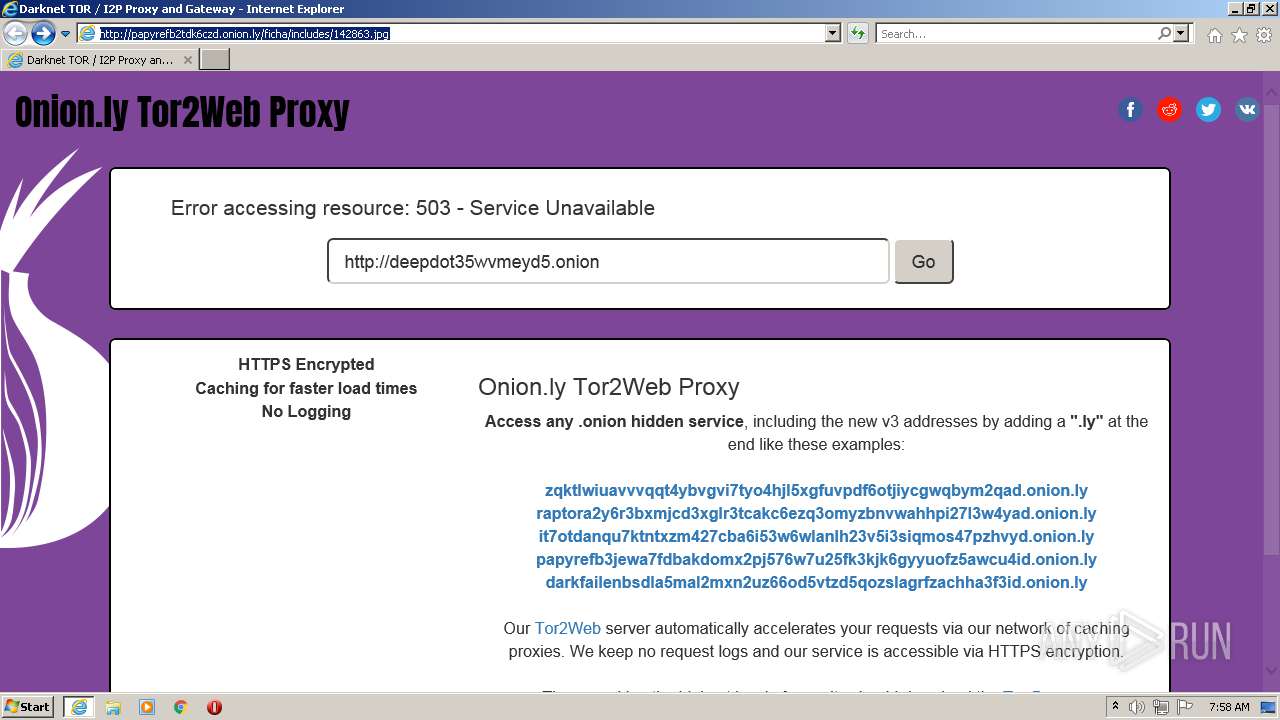
| URL: | http://papyrefb2tdk6czd.onion.ly/ficha/includes/142863.jpg |
| Full analysis: | https://app.any.run/tasks/7c6ae5ab-3f62-4bb5-90e6-2f4dec9437ec |
| Verdict: | Malicious activity |
| Analysis date: | August 24, 2021, 06:56:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1C87E24CDB47AE31B79952678C714C60 |
| SHA1: | 820E6F6DDB20D996A515CE66EED72B797D08EA36 |
| SHA256: | 6A4EACAF95385CA6CBD3089F247A53B26D9F9C9828196DA01FBD427F0274466C |
| SSDEEP: | 3:N1KOEVcXwXRZf9KLL/9eAGX+w:COFAQHgAFw |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1684)
- iexplore.exe (PID: 2968)
INFO
Checks supported languages
- iexplore.exe (PID: 2968)
- iexplore.exe (PID: 1684)
Reads the computer name
- iexplore.exe (PID: 1684)
- iexplore.exe (PID: 2968)
Application launched itself
- iexplore.exe (PID: 2968)
Reads settings of System Certificates
- iexplore.exe (PID: 2968)
- iexplore.exe (PID: 1684)
Changes internet zones settings
- iexplore.exe (PID: 2968)
Changes settings of System certificates
- iexplore.exe (PID: 2968)
Dropped object may contain URL to Tor Browser
- iexplore.exe (PID: 2968)
- iexplore.exe (PID: 1684)
Checks Windows Trust Settings
- iexplore.exe (PID: 2968)
- iexplore.exe (PID: 1684)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2968)
Creates files in the user directory
- iexplore.exe (PID: 1684)
- iexplore.exe (PID: 2968)
Reads internet explorer settings
- iexplore.exe (PID: 1684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1684 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2968 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2968 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://papyrefb2tdk6czd.onion.ly/ficha/includes/142863.jpg" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
24 430
Read events
24 040
Write events
388
Delete events
2
Modification events
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 813318496 | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30906549 | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30906549 | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
23
Text files
71
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1684 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 1684 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CC197601BE0898B7B0FCC91FA15D8A69_2C8690802F945687CBA0B739D6AA9E63 | binary | |
MD5:BAF9A317DBDB62A65C2D87B3C0DBF755 | SHA256:254EBE2A473D615D59A4DF24D8A14B7DF379D0489E2A61E22F08289531225D84 | |||
| 1684 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:33FAE2A16086927ACCC98A1BFD3432AD | SHA256:F3A29D972EF0E9CC6A555879B02B6B3B1E528F1A6DE8E80C23122BB8825949D0 | |||
| 1684 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | der | |
MD5:4F914D6A12B48374677859978D3DEF97 | SHA256:EB9AC8C88C0857B9588076073491EEC79F4725AA32BC7AF00C20EF31095D1D68 | |||
| 1684 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CC197601BE0898B7B0FCC91FA15D8A69_2C8690802F945687CBA0B739D6AA9E63 | der | |
MD5:BEB201037A7D30081B59F151BE63EED2 | SHA256:8DE3F096F16D9C94C54781685F0061C095DAD054E1B34D4798EDBFF5DA15791C | |||
| 1684 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\142863[1].htm | html | |
MD5:5ECA4F7835D788145DCA1B267EB4208F | SHA256:0B530B77CA10C94F6363D133668189EDC96DA100ECAA2170DE7BFF5D4788D14D | |||
| 1684 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | binary | |
MD5:BD1910F38408A094E797F478B246EA1D | SHA256:546E3E20246AD3798EC551777F40716A348103B35B18E655AF92E594CDC6ED29 | |||
| 1684 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\css[1].css | text | |
MD5:36D855A2C39C3FADC4FA7AAF6EB0D094 | SHA256:56ADE41635CED170D7DFE1697AC8C335614650D2F4DFBA2224A5C5342AF954F1 | |||
| 1684 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\82CB34DD3343FE727DF8890D352E0D8F | der | |
MD5:3248339A5C0CCB747287755B27EE2E9F | SHA256:B8E2A737FEA3E69A4008844262BA8FF43375DB297AFA3624C9B640C74534AE80 | |||
| 1684 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:5EFB06CAA58AFE50D93E5FD5FD67EC4C | SHA256:7D5B56681154C208CB02005C2C8D05189FC4AAB755B1F1DBCC7B9A049622459F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
52
DNS requests
24
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1684 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?fe21318f17eaf9c8 | US | compressed | 4.70 Kb | whitelisted |
1684 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b6e986b8a7ffeedb | US | compressed | 4.70 Kb | whitelisted |
1684 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?56469ab7a07bf22b | US | compressed | 4.70 Kb | whitelisted |
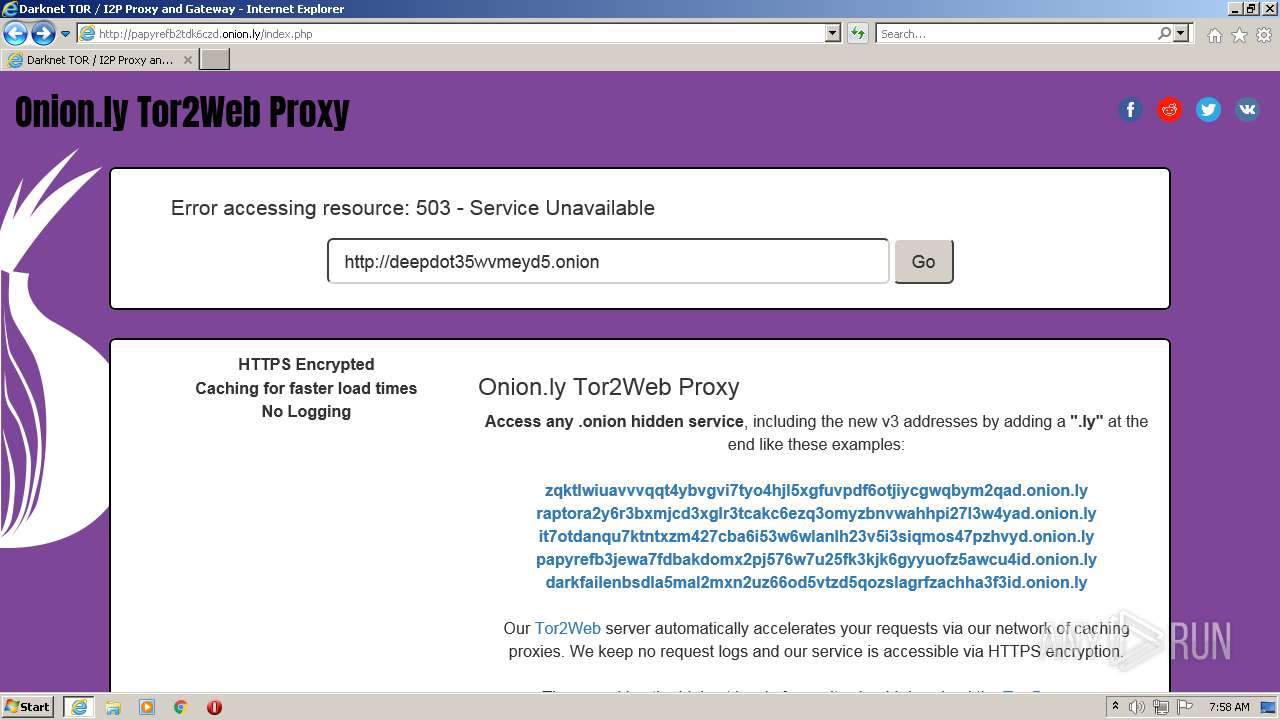
1684 | iexplore.exe | GET | 200 | 198.251.89.118:80 | http://papyrefb2tdk6czd.onion.ly/ficha/includes/142863.jpg | US | html | 22.0 Kb | malicious |
1684 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.68 Kb | whitelisted |
1684 | iexplore.exe | GET | 200 | 104.89.32.83:80 | http://x1.c.lencr.org/ | NL | der | 717 b | whitelisted |
1684 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCeFMaRQ3SNqAUAAAAAiBGe | US | der | 472 b | whitelisted |
1684 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
1684 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2968 | iexplore.exe | GET | 200 | 198.251.89.118:80 | http://papyrefb2tdk6czd.onion.ly/favicon.ico | US | html | 22.0 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2968 | iexplore.exe | 198.251.89.118:80 | papyrefb2tdk6czd.onion.ly | FranTech Solutions | US | malicious |
2968 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2968 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1672 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2968 | iexplore.exe | 104.89.38.104:443 | go.microsoft.com | Akamai Technologies, Inc. | NL | malicious |
2968 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2968 | iexplore.exe | 131.253.33.203:443 | www.msn.com | Microsoft Corporation | US | malicious |
2968 | iexplore.exe | 13.92.246.37:443 | query.prod.cms.msn.com | Microsoft Corporation | US | whitelisted |
1684 | iexplore.exe | 104.18.11.207:443 | maxcdn.bootstrapcdn.com | Cloudflare Inc | US | suspicious |
1684 | iexplore.exe | 198.251.89.118:80 | papyrefb2tdk6czd.onion.ly | FranTech Solutions | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
papyrefb2tdk6czd.onion.ly |
| malicious |
maxcdn.bootstrapcdn.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
simplesharebuttons.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.identrust.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query to .onion proxy Domain (onion . ly) |