| File name: | DeltaInstaller (1).exe |
| Full analysis: | https://app.any.run/tasks/90bd688c-6365-4769-960e-aecf06c1306c |
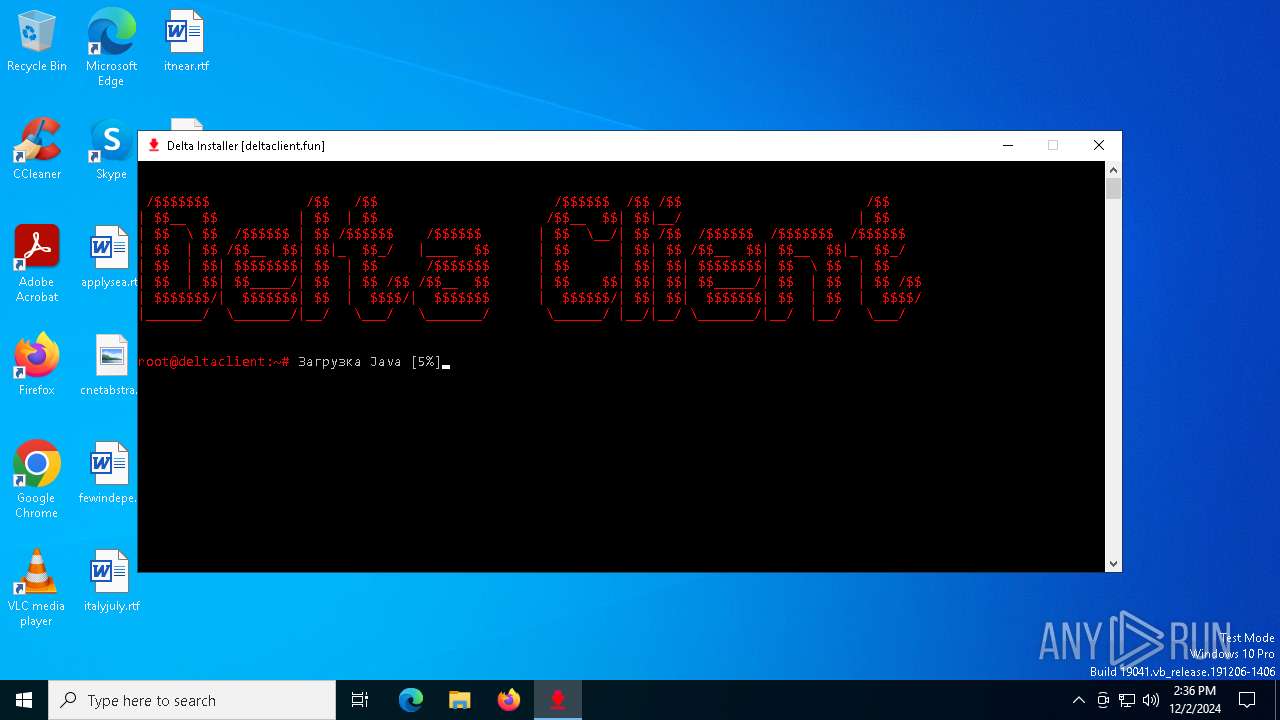
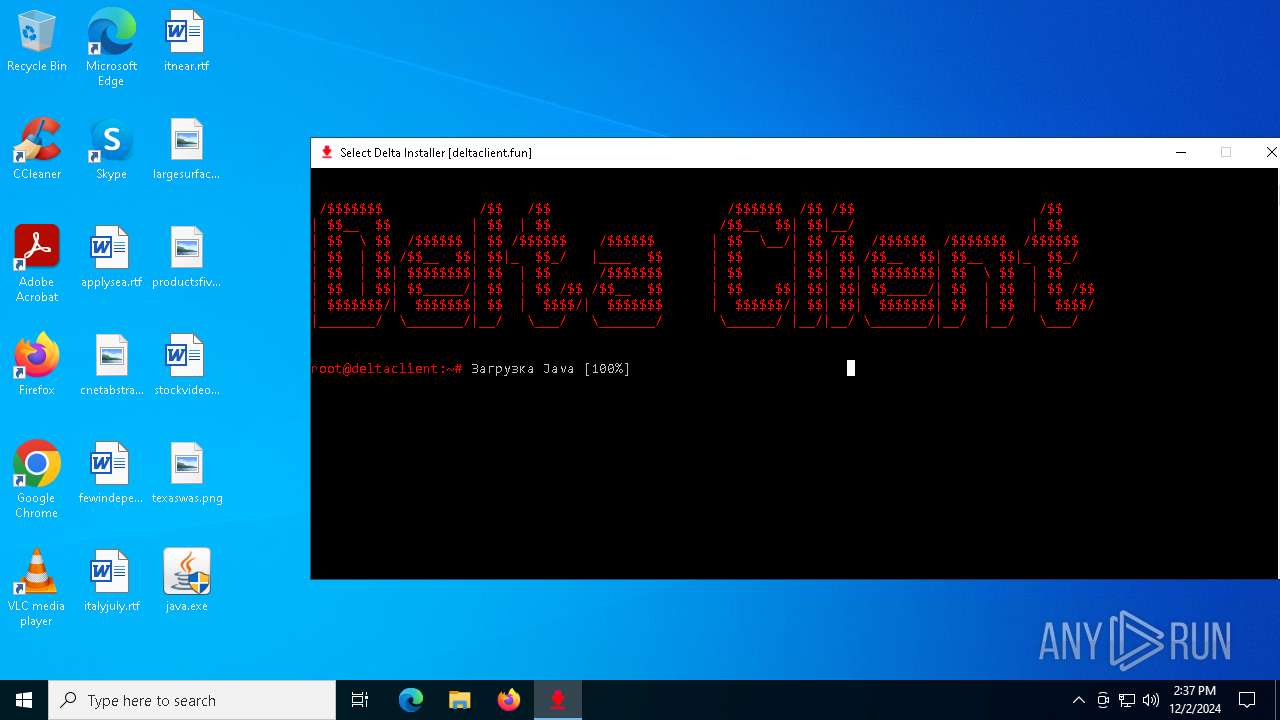
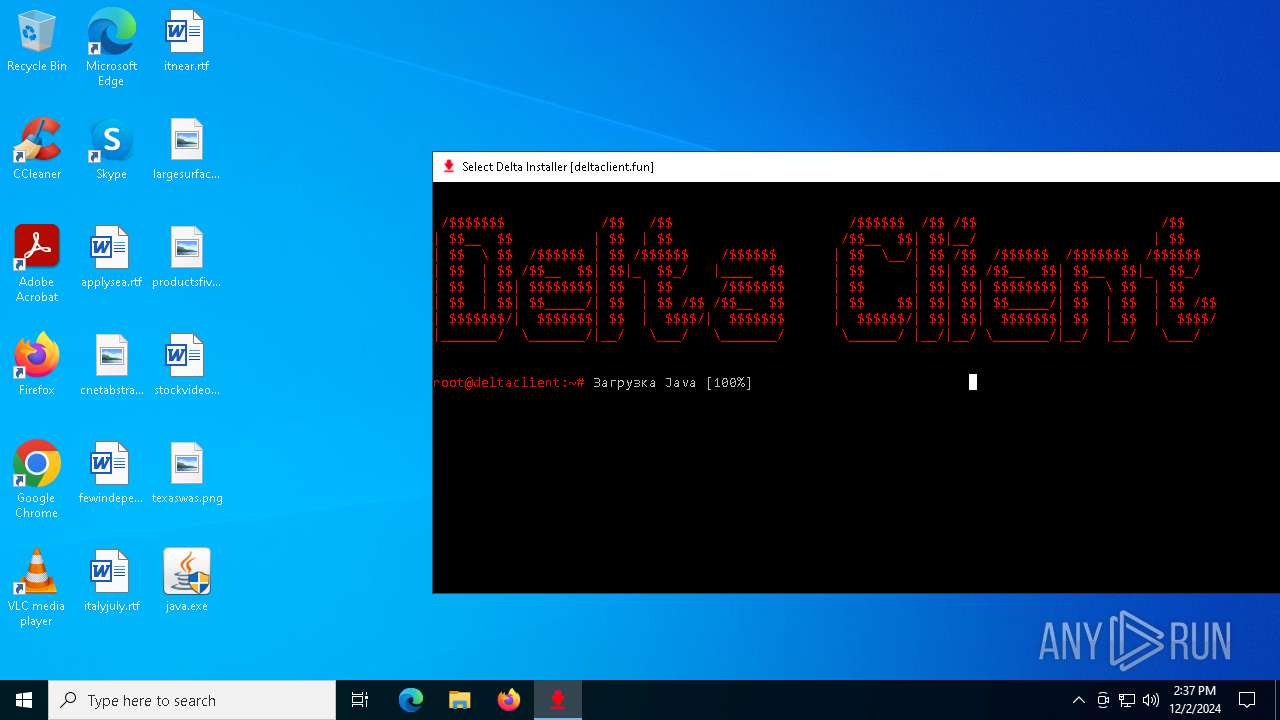
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2024, 14:36:30 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | 971DBD4B02CC39845EA6D7CE6A281286 |
| SHA1: | 6D93C9EF5BE73E2370973D79AB738132CCEC94B5 |
| SHA256: | 6A3FE369012DFC13E2232C316DCBAC74A2D92893B0D4CB656535307F99153B13 |
| SSDEEP: | 24576:wFhhEkiB8nbAy4Cuh3tp/AYLMzShNWg3/UoSDJo:i8vB8n0Ouh3tp/fLMzShNWQUoSDJo |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- msiexec.exe (PID: 4944)
Executable content was dropped or overwritten
- java.exe (PID: 5560)
- installer.exe (PID: 1916)
- javaw.exe (PID: 5888)
The process drops C-runtime libraries
- msiexec.exe (PID: 4944)
INFO
Executable content was dropped or overwritten
- msiexec.exe (PID: 4944)
Checks supported languages
- DeltaInstaller (1).exe (PID: 6276)
Application launched itself
- msiexec.exe (PID: 4944)
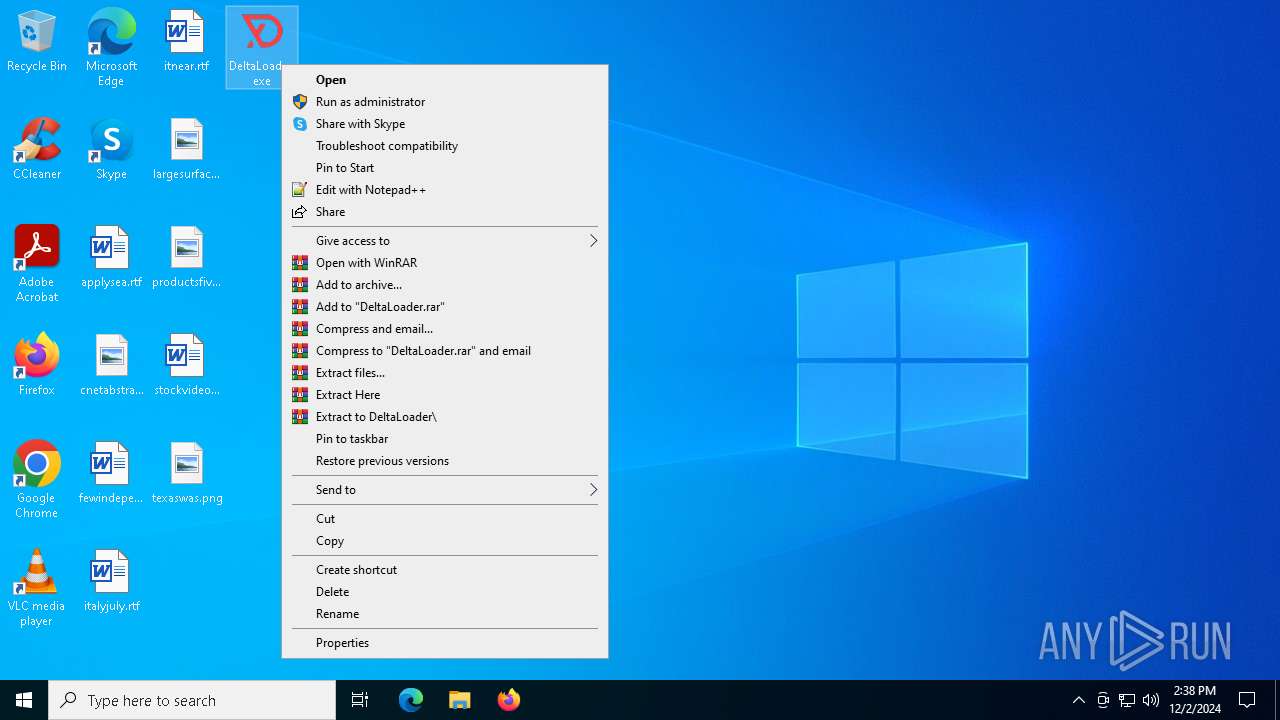
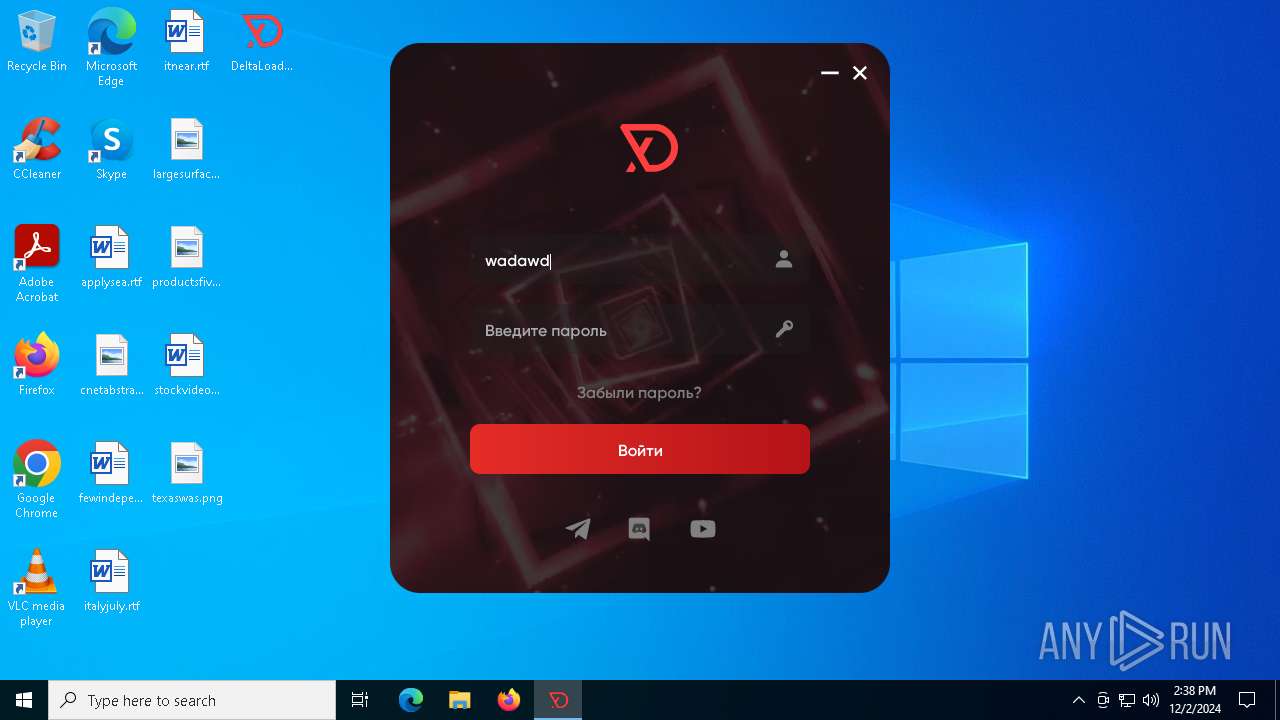
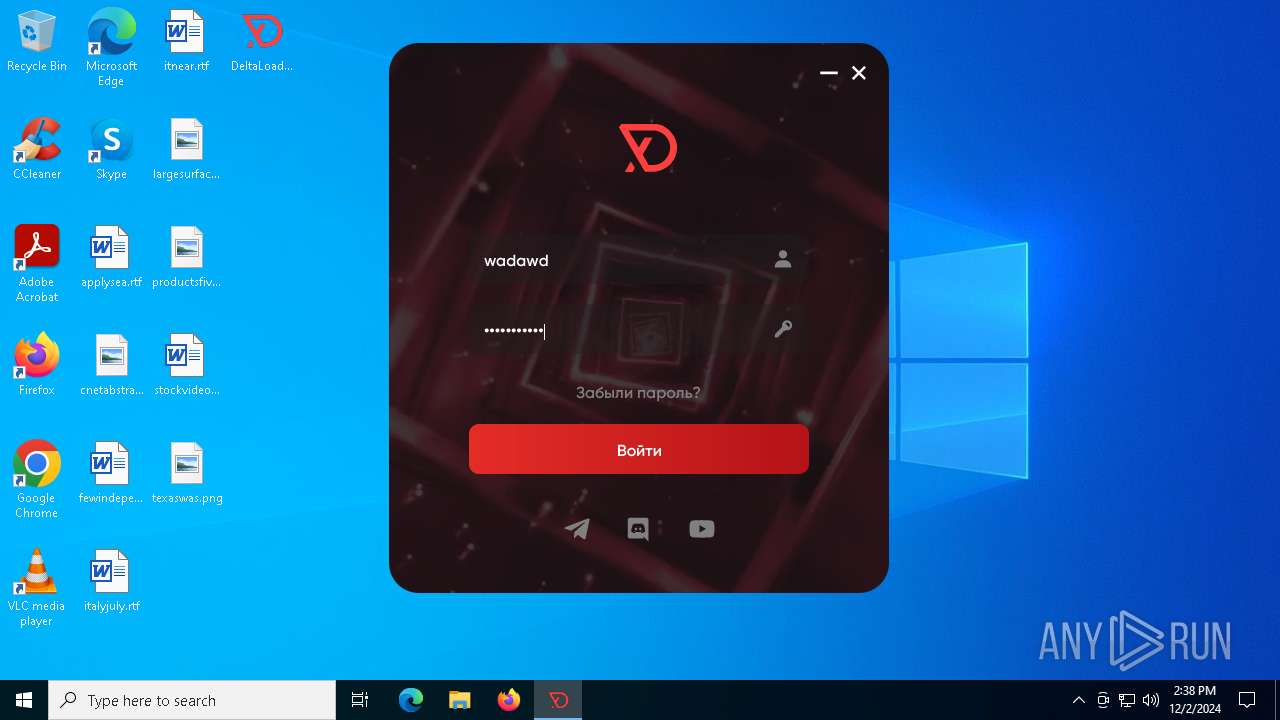
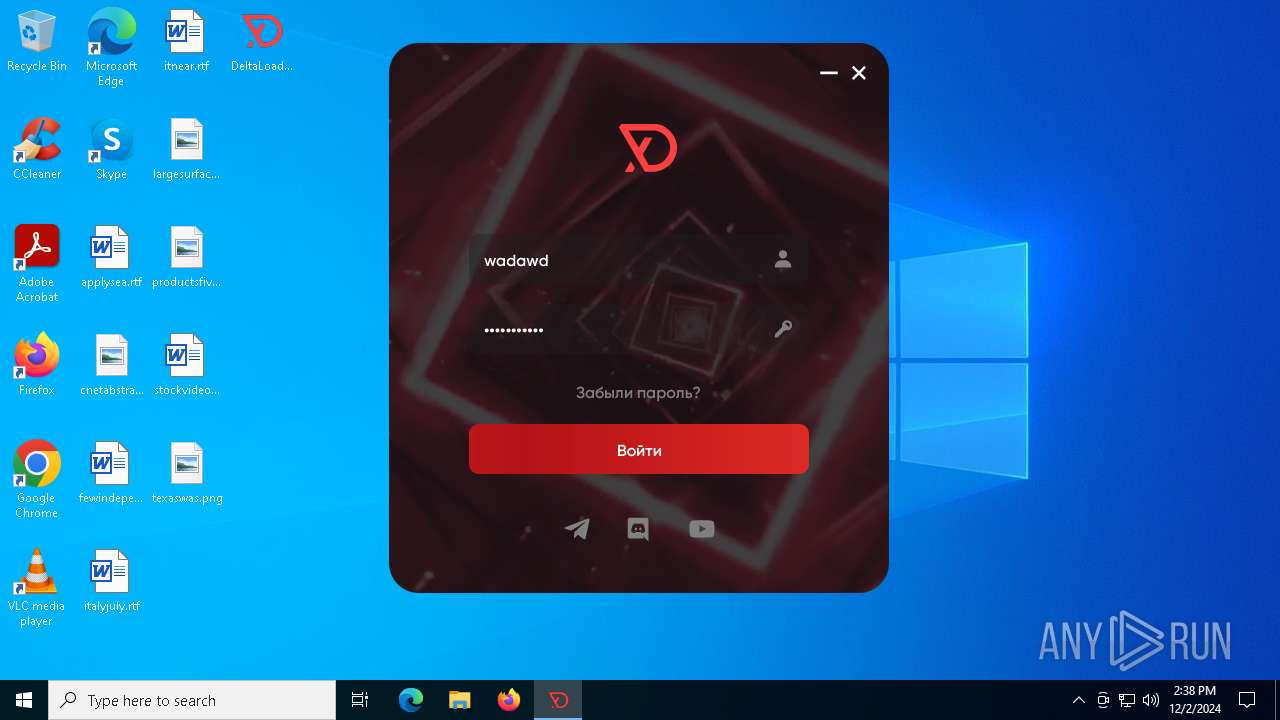
Manual execution by a user
- DeltaLoader.exe (PID: 5240)
Starts application with an unusual extension
- msiexec.exe (PID: 4944)
Application based on Java
- javaw.exe (PID: 5888)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:09:10 00:54:58+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.41 |
| CodeSize: | 525312 |
| InitializedDataSize: | 365056 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x528f8 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
159
Monitored processes
28
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 628 | "C:\Program Files\Java\jre1.8.0_421\bin\jp2launcher.exe" -secure -javaws -jre "C:\Program Files\Java\jre1.8.0_421" -vma LWNsYXNzcGF0aABDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfNDIxXGxpYlxkZXBsb3kuamFyAC1EamF2YS5zZWN1cml0eS5wb2xpY3k9ZmlsZTpDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfNDIxXGxpYlxzZWN1cml0eVxqYXZhd3MucG9saWN5AC1EdHJ1c3RQcm94eT10cnVlAC1YdmVyaWZ5OnJlbW90ZQAtRGpubHB4LmhvbWU9QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzQyMVxiaW4ALURqYXZhLnNlY3VyaXR5Lm1hbmFnZXIALURzdW4uYXd0Lndhcm11cD10cnVlAC1YYm9vdGNsYXNzcGF0aC9hOkM6XFByb2dyYW0gRmlsZXNcSmF2YVxqcmUxLjguMF80MjFcbGliXGphdmF3cy5qYXI7QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzQyMVxsaWJcZGVwbG95LmphcjtDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfNDIxXGxpYlxwbHVnaW4uamFyAC1EamF2YS5hd3QuaGVhZGxlc3M9dHJ1ZQAtRGpubHB4Lmp2bT1DOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfNDIxXGJpblxqYXZhdy5leGU= -ma LXdhaXQALWZpeAAtc2hvcnRjdXQALXNpbGVudAAtbm90V2ViSmF2YQ== | C:\Program Files\Java\jre1.8.0_421\bin\jp2launcher.exe | — | javaws.exe | |||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Web Launcher Exit code: 0 Version: 11.421.2.09 Modules
| |||||||||||||||
| 1300 | "C:\Users\admin\AppData\Local\Temp\DeltaInstaller (1).exe" | C:\Users\admin\AppData\Local\Temp\DeltaInstaller (1).exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1876 | "C:\Windows\SysWOW64\msiexec.exe" /x {4A03706F-666A-4037-7777-5F2748764D10} /qn | C:\Windows\SysWOW64\msiexec.exe | — | jaureg.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 1605 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1916 | "C:\Program Files\Java\jre1.8.0_421\installer.exe" /s INSTALLDIR="C:\Program Files\Java\jre1.8.0_421\\" INSTALL_SILENT=1 AUTO_UPDATE=0 SPONSORS=0 REPAIRMODE=0 ProductCode={77924AE4-039E-4CA4-87B4-2F64180421F0} | C:\Program Files\Java\jre1.8.0_421\installer.exe | msiexec.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java Platform SE binary Exit code: 0 Version: 8.0.4210.9 Modules
| |||||||||||||||
| 2380 | C:\Windows\syswow64\MsiExec.exe -Embedding 6C90C1948848F67184F890E89DA9763A E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2512 | "C:\Program Files\Java\jre1.8.0_421\bin\javaws.exe" -wait -fix -shortcut -silent | C:\Program Files\Java\jre1.8.0_421\bin\javaws.exe | installer.exe | ||||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Web Start Launcher Exit code: 0 Version: 11.421.2.09 Modules
| |||||||||||||||
| 2956 | C:\Windows\syswow64\MsiExec.exe -Embedding 9EAD9E17B48FBAF7CFF4B8B35000804C E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3420 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | jaureg.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3688 | C:\Windows\syswow64\MsiExec.exe -Embedding 85CE0361CAE280FB58E838BBA71F59A3 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4076 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | icacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
39 927
Read events
12 932
Write events
12 521
Delete events
14 474
Modification events
| (PID) Process: | (5560) java.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\JavaSoft |
| Operation: | delete value | Name: | InstallStatus |
Value: | |||
| (PID) Process: | (5560) java.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5560) java.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5560) java.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5560) java.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\JavaSoft\Java Update\Policy |
| Operation: | write | Name: | Country |
Value: DE | |||
| (PID) Process: | (5560) java.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\JavaSoft\Java Update\Policy |
| Operation: | write | Name: | PostStatusUrl |
Value: https://sjremetrics.java.com/b/ss//6 | |||
| (PID) Process: | (5560) java.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\JavaSoft\Java Update\Policy |
| Operation: | write | Name: | Method |
Value: joff | |||
| (PID) Process: | (4944) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 50130000B7E49DC0C744DB01 | |||
| (PID) Process: | (4944) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 4D8C7A06C5007D315A5206F9C97B4AF724F88C2EE1F88A3BA8B1B093B7D008C7 | |||
| (PID) Process: | (4944) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
Executable files
360
Suspicious files
94
Text files
214
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4652 | java.exe | C:\Users\admin\AppData\Local\Temp\jds1333156.tmp\jds1333156.tmp | — | |
MD5:— | SHA256:— | |||
| 4652 | java.exe | C:\Users\admin\AppData\Local\Temp\jds1333156.tmp\java.exe | — | |
MD5:— | SHA256:— | |||
| 5560 | java.exe | C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_421_x64\jre1.8.0_42164.msi | — | |
MD5:— | SHA256:— | |||
| 4944 | msiexec.exe | C:\Windows\Installer\146753.msi | — | |
MD5:— | SHA256:— | |||
| 4944 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | der | |
MD5:B6102B47F3D2450F02C1167E5B337E9B | SHA256:E0C2D57C8661D444666AE009725EE84CD33A29AC48738277EA37BFD56B3CF8C4 | |||
| 4944 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8EC9B1D0ABBD7F98B401D425828828CE_D2F6556190F7B1A25A117FFB5467EEBD | binary | |
MD5:A8A1047A91EFD4F5C5AC613BB3590C60 | SHA256:1C53F270547FD3C7DB6D9FADA4EB6A19F3AE09EE805FC0C3BA6EE6477450B7DF | |||
| 4652 | java.exe | C:\Users\admin\AppData\Local\Temp\jusched.log | text | |
MD5:6E58BD8B049B1B32901AF72C7A579C2E | SHA256:1CCB31741929517C1A648C725EED02C726AD50166EEFA5883BCC6B8E3668508E | |||
| 4944 | msiexec.exe | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\ngen.log | text | |
MD5:6FFEDE39A9A1AF35466FE449D7A24A33 | SHA256:3080AEC18B8E378AF23CB0EF710BDCC814358FC30B46A11AEC39B205FD0799C0 | |||
| 4944 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8EC9B1D0ABBD7F98B401D425828828CE_D2F6556190F7B1A25A117FFB5467EEBD | der | |
MD5:EEBFDB0CA57400191DB10580AD845CB3 | SHA256:49A1F12D020258604C8EE3C128AB6D591553181B9411ADBD3B7ED7FC9CF69FE6 | |||
| 4944 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:77595D315C43E57C7030AD792277055B | SHA256:6CB84920CAC327925200A2BFF877979D19E31A2041E344D424EE6C5B86DB8D6D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
48
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
760 | lsass.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7084 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7084 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
760 | lsass.exe | GET | 200 | 142.250.184.195:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
6400 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.179:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1176 | svchost.exe | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
javadl.oracle.com |
| whitelisted |
sdlc-esd.oracle.com |
| whitelisted |