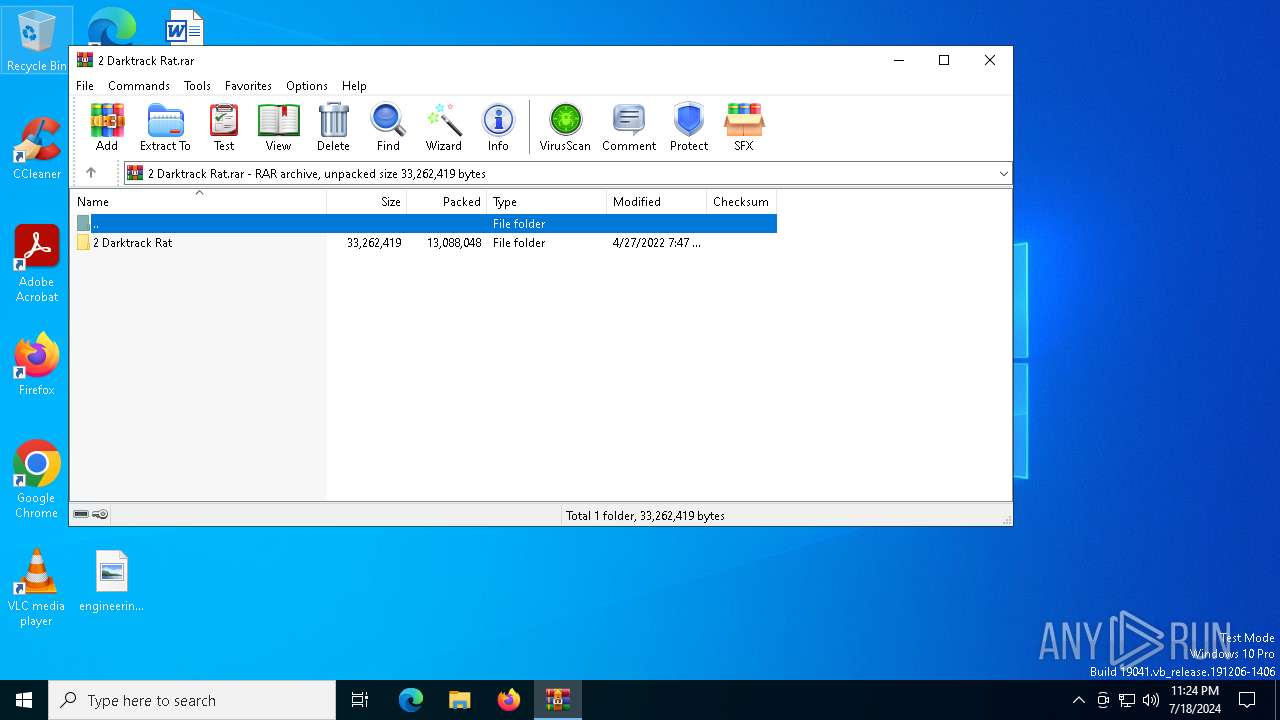
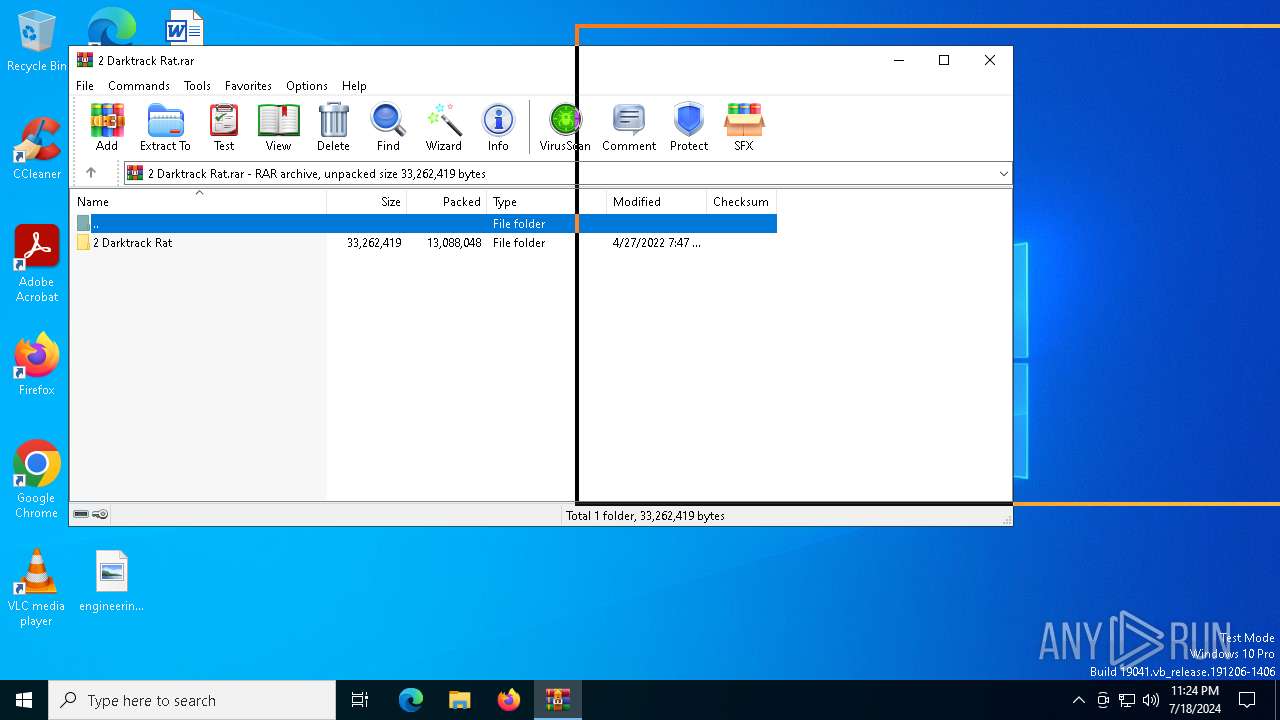
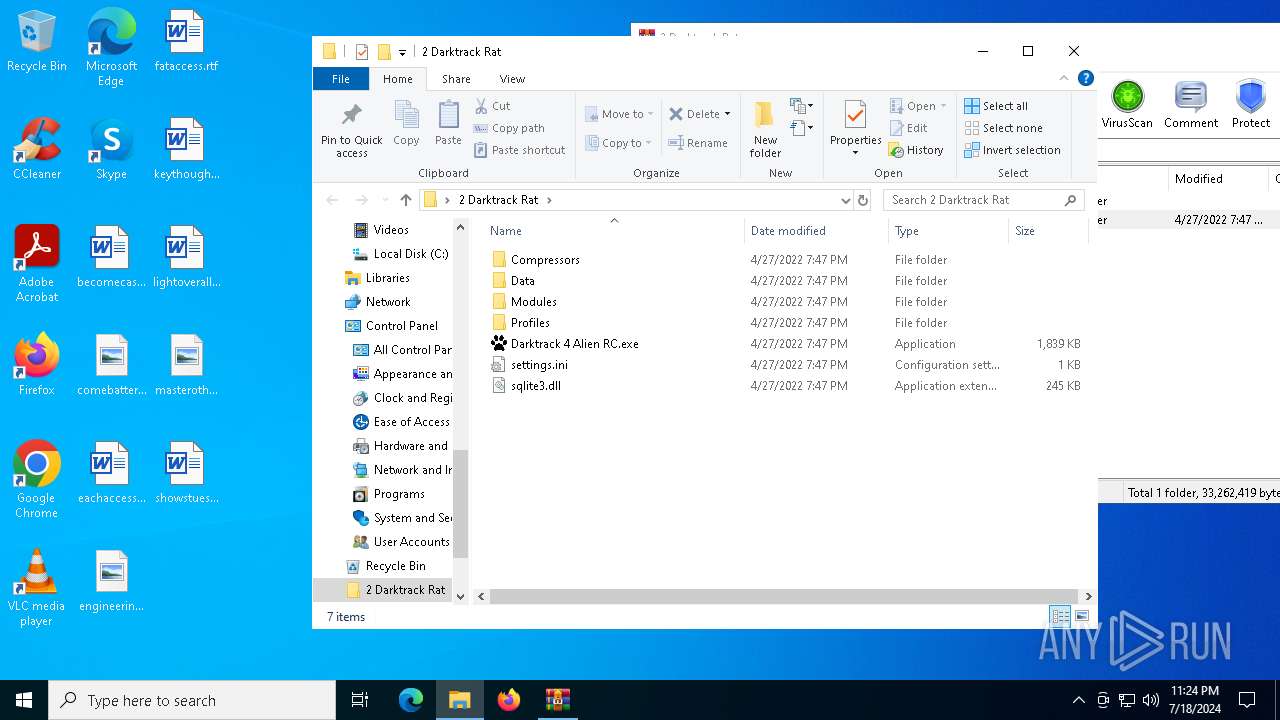
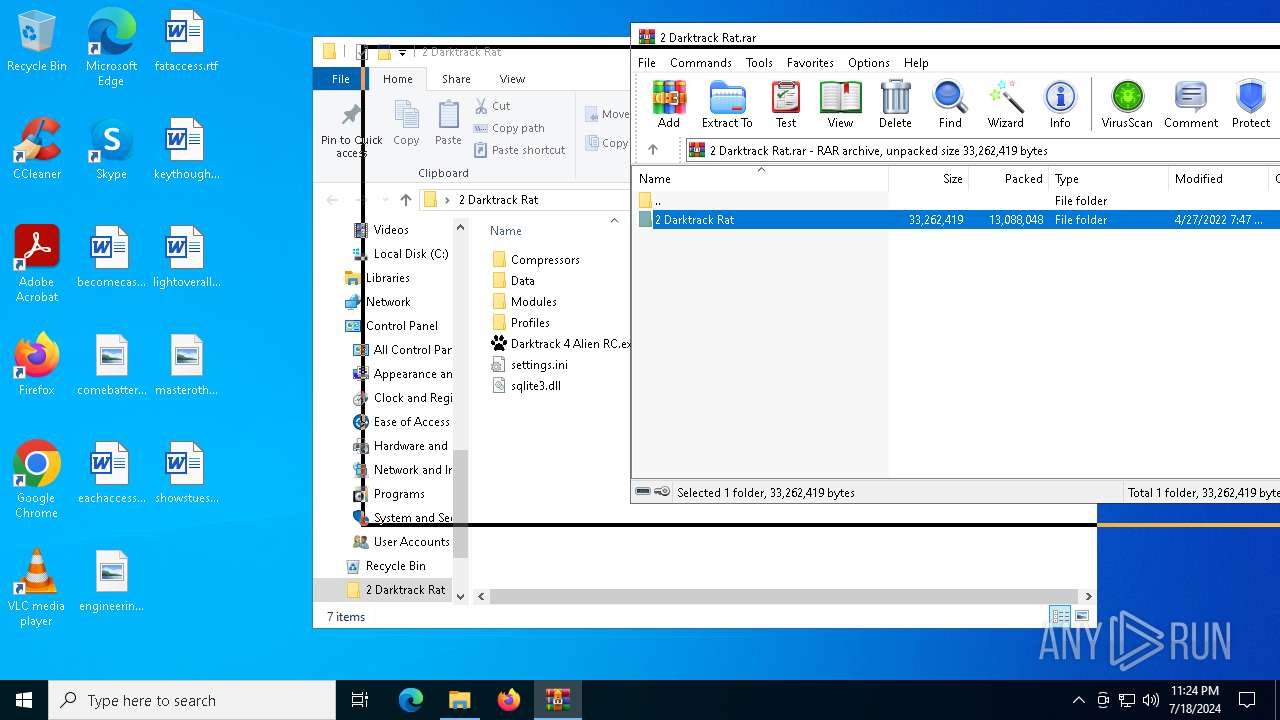
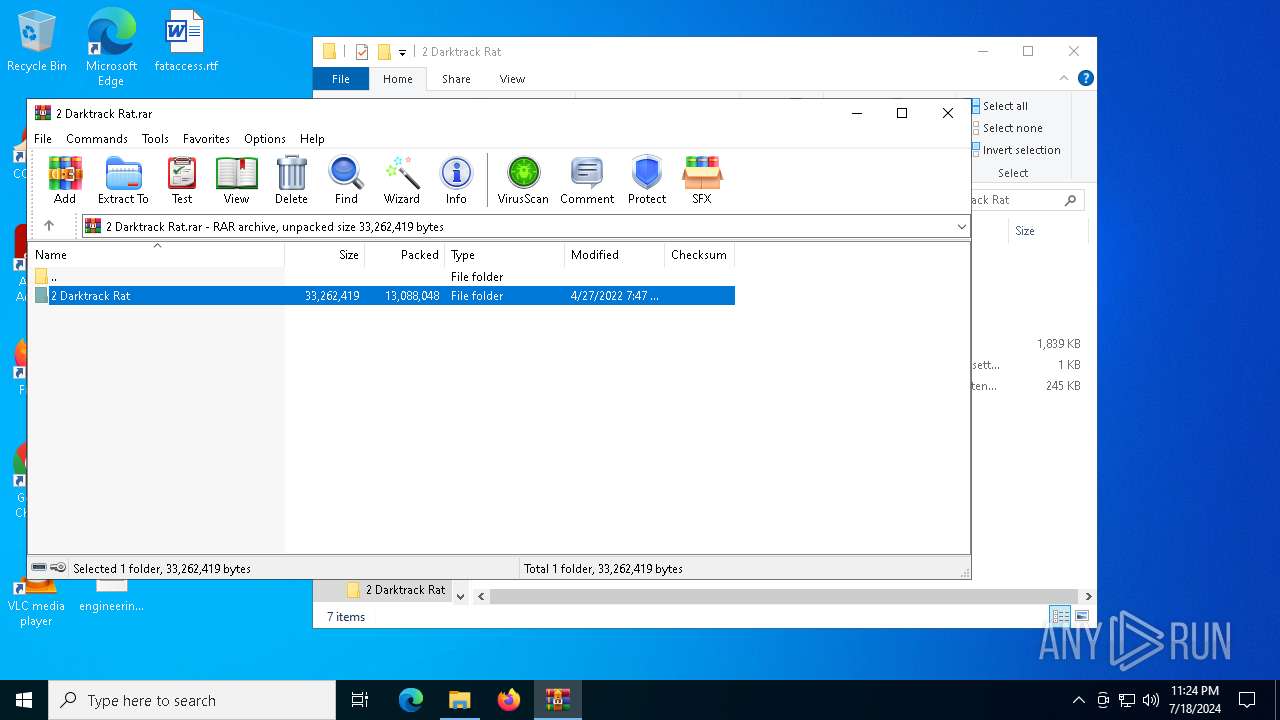
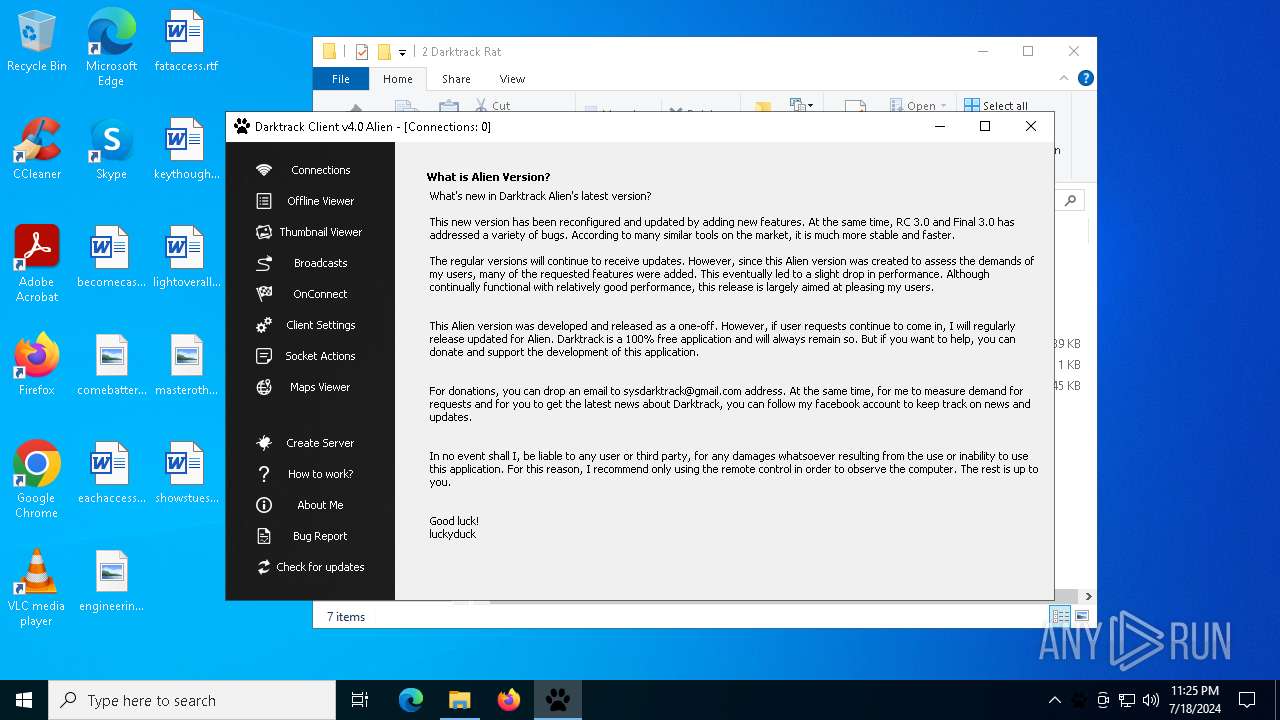
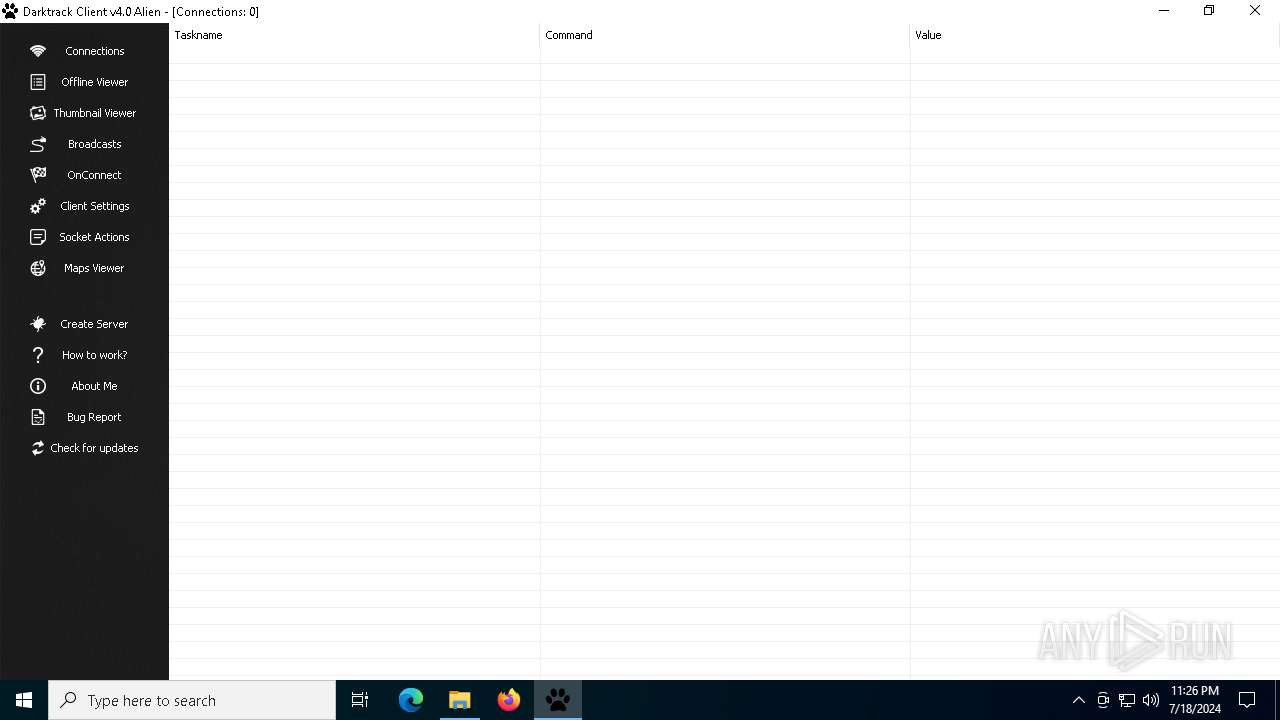
| File name: | 2 Darktrack Rat.rar |
| Full analysis: | https://app.any.run/tasks/78096359-6374-41bf-aed0-33edc8a805b6 |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2024, 23:24:22 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
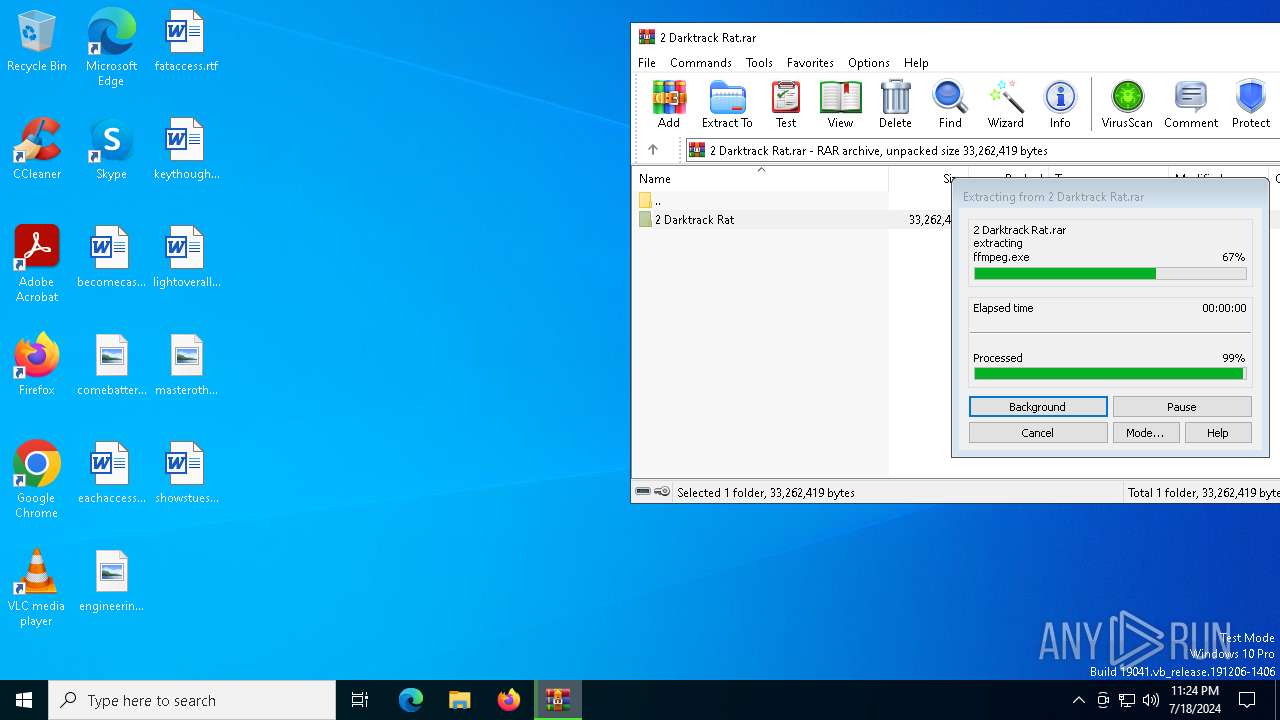
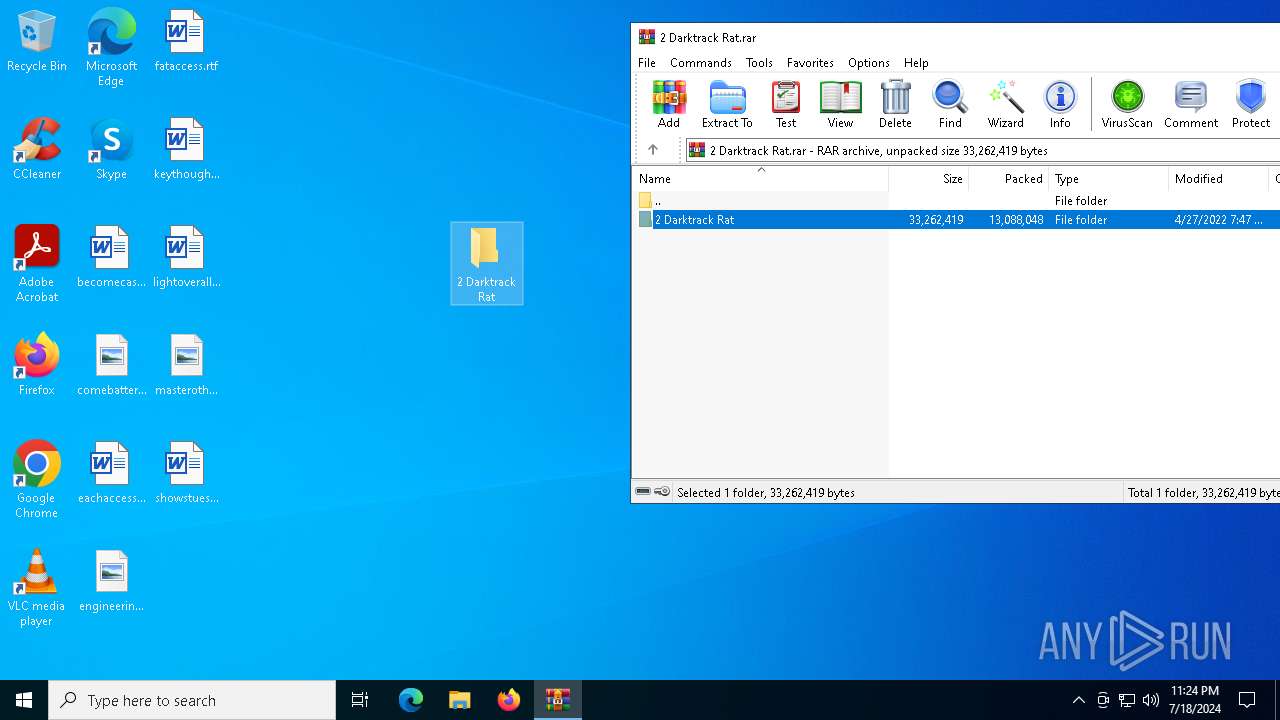
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | C120E5D923F5176CA110A342C6D8C233 |
| SHA1: | 439D3122860CC12532B54C577A08BB18FC851183 |
| SHA256: | 6A1E261BAA6948ADF079CDAE0D68FF0950A7EE288EA0FBC8191E5D0B8249E3B3 |
| SSDEEP: | 196608:L97sFgpZQVyJZUoasF0z6HYvH5I4nA7MN:xqgnQ4Zl70z6HYP5I4+k |
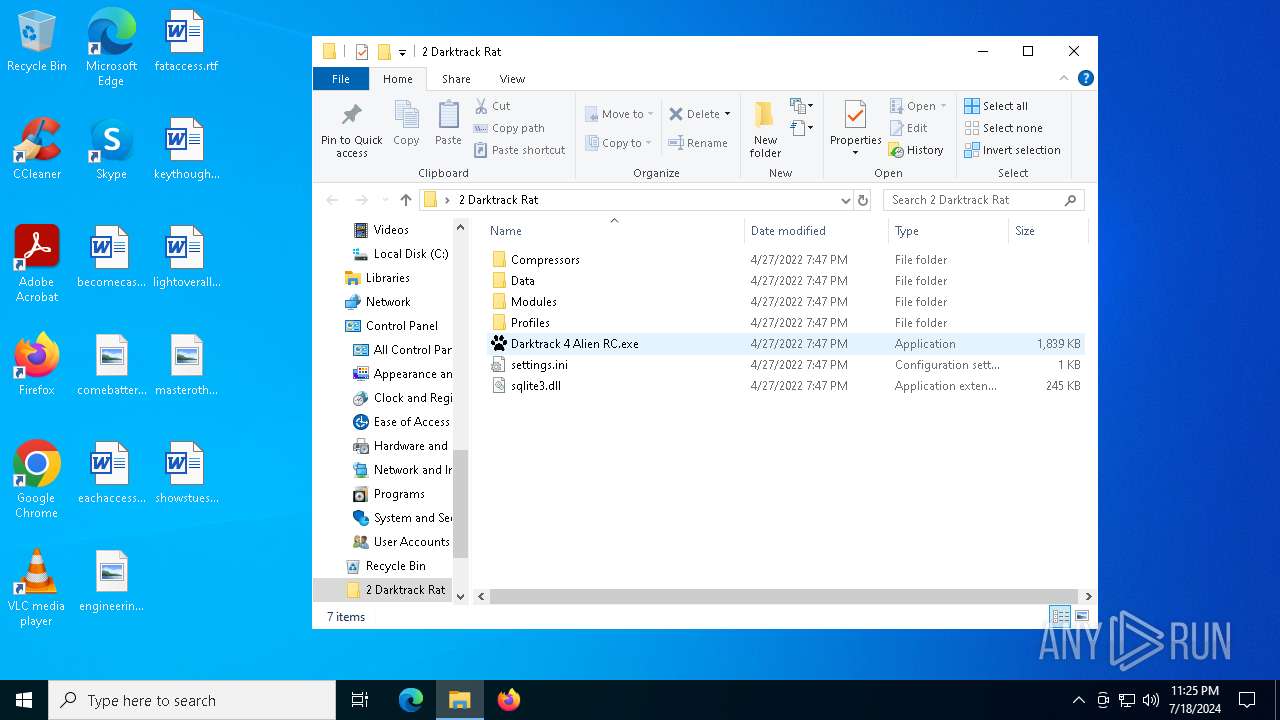
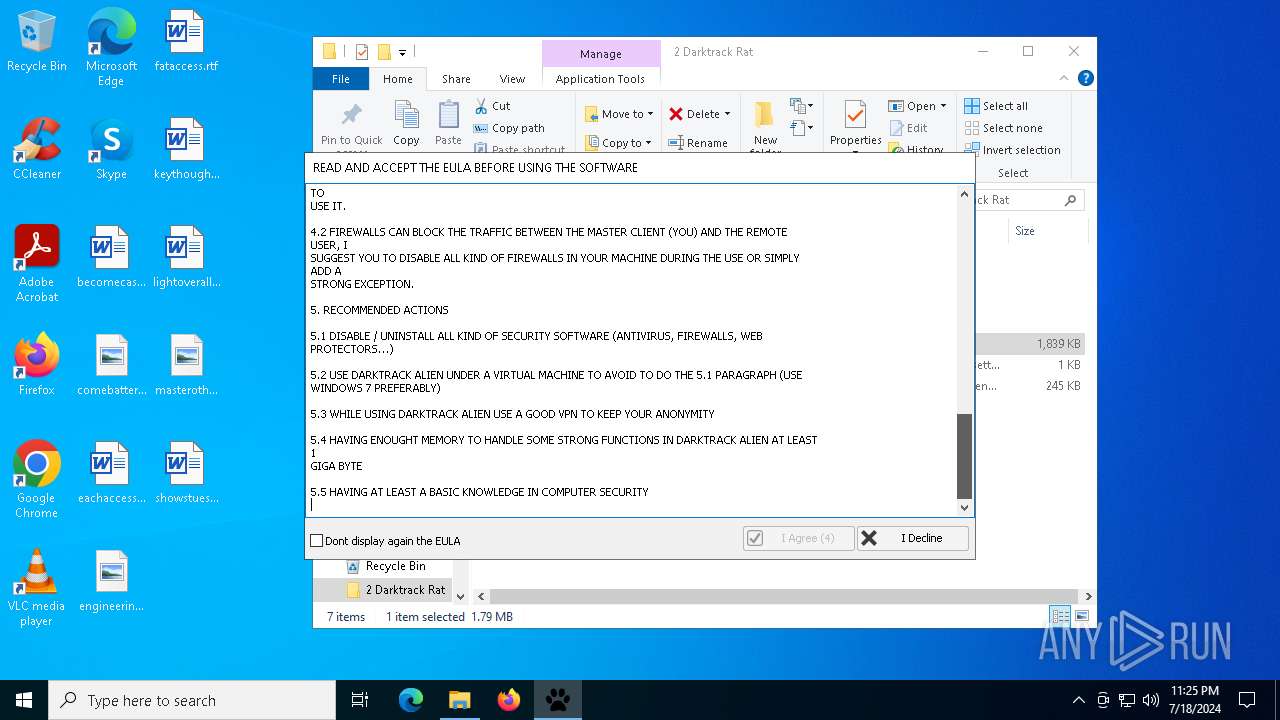
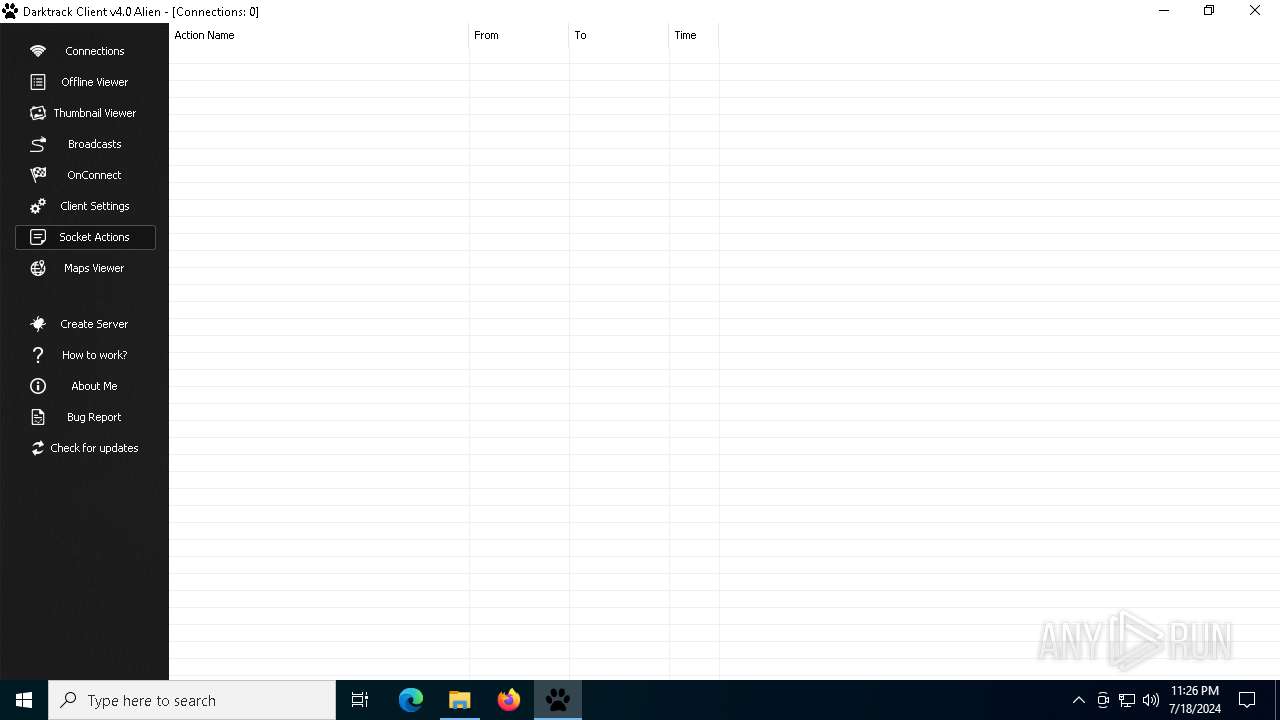
MALICIOUS
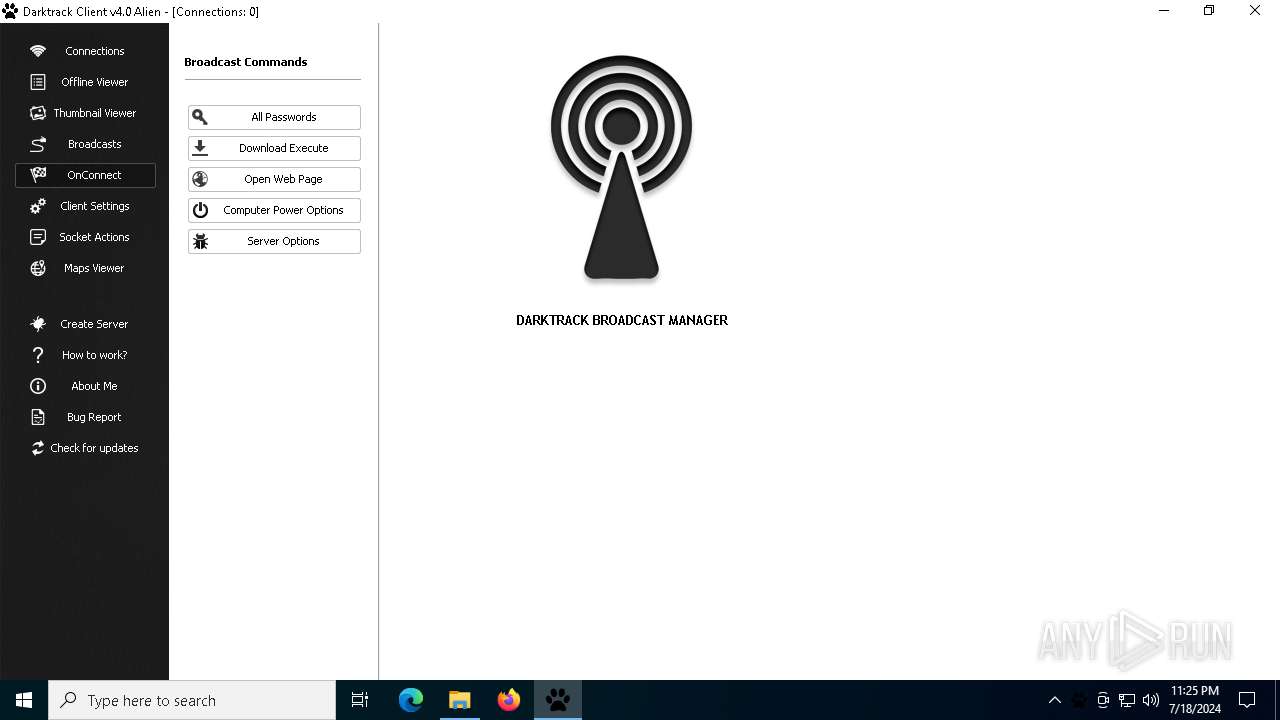
Scans artifacts that could help determine the target
- Darktrack 4 Alien RC.exe (PID: 1164)
SUSPICIOUS
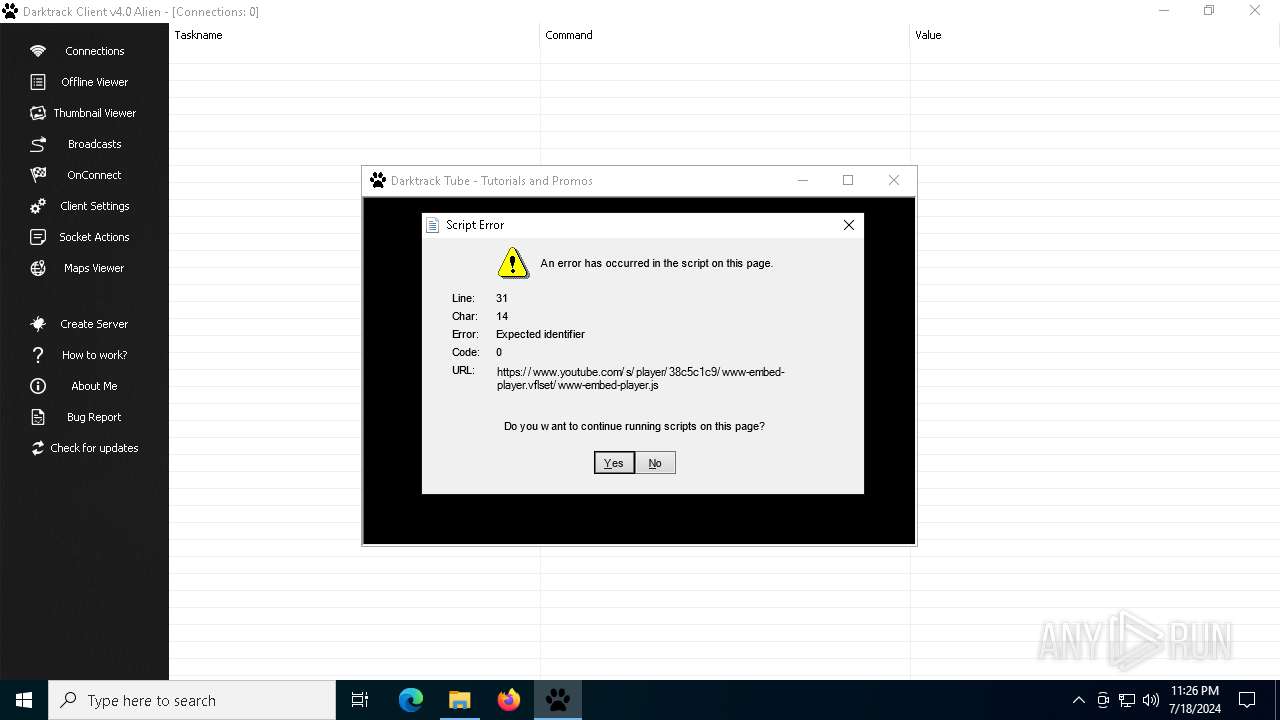
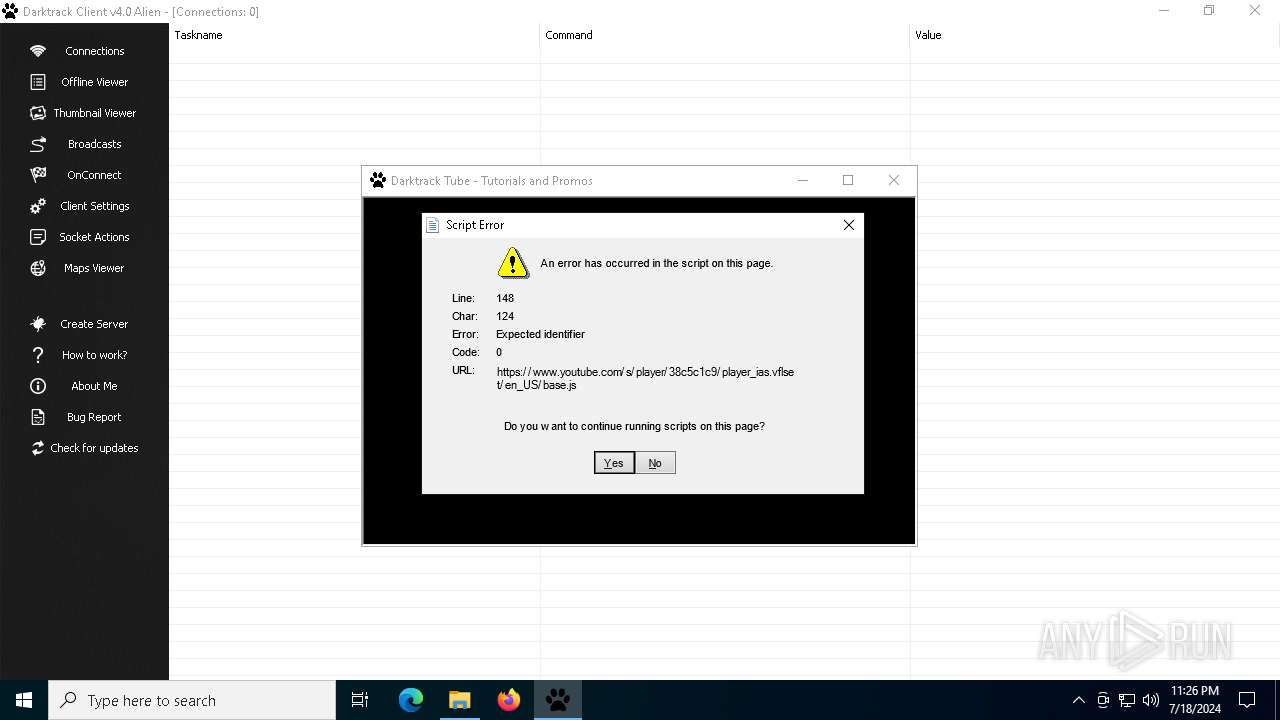
Reads security settings of Internet Explorer
- Darktrack 4 Alien RC.exe (PID: 1164)
There is functionality for communication over UDP network (YARA)
- Darktrack 4 Alien RC.exe (PID: 1164)
There is functionality for taking screenshot (YARA)
- Darktrack 4 Alien RC.exe (PID: 1164)
Reads Microsoft Outlook installation path
- Darktrack 4 Alien RC.exe (PID: 1164)
Checks Windows Trust Settings
- Darktrack 4 Alien RC.exe (PID: 1164)
Reads Internet Explorer settings
- Darktrack 4 Alien RC.exe (PID: 1164)
INFO
Checks supported languages
- Darktrack 4 Alien RC.exe (PID: 1164)
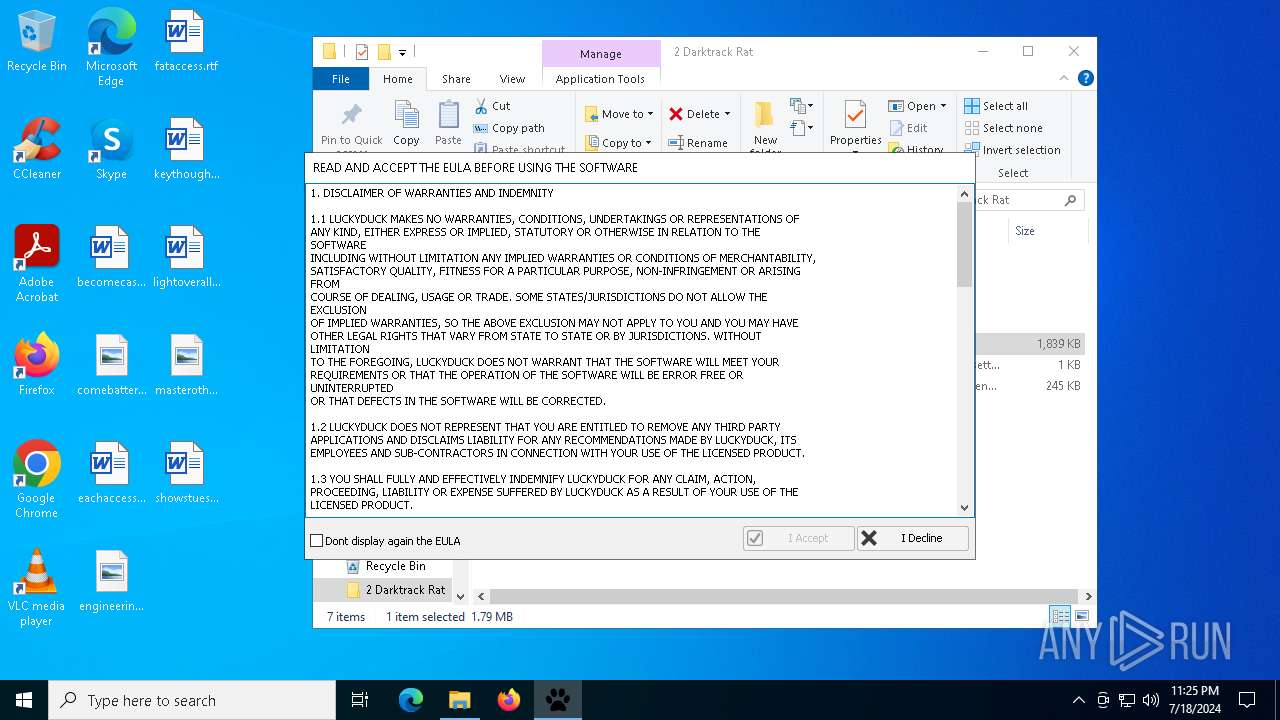
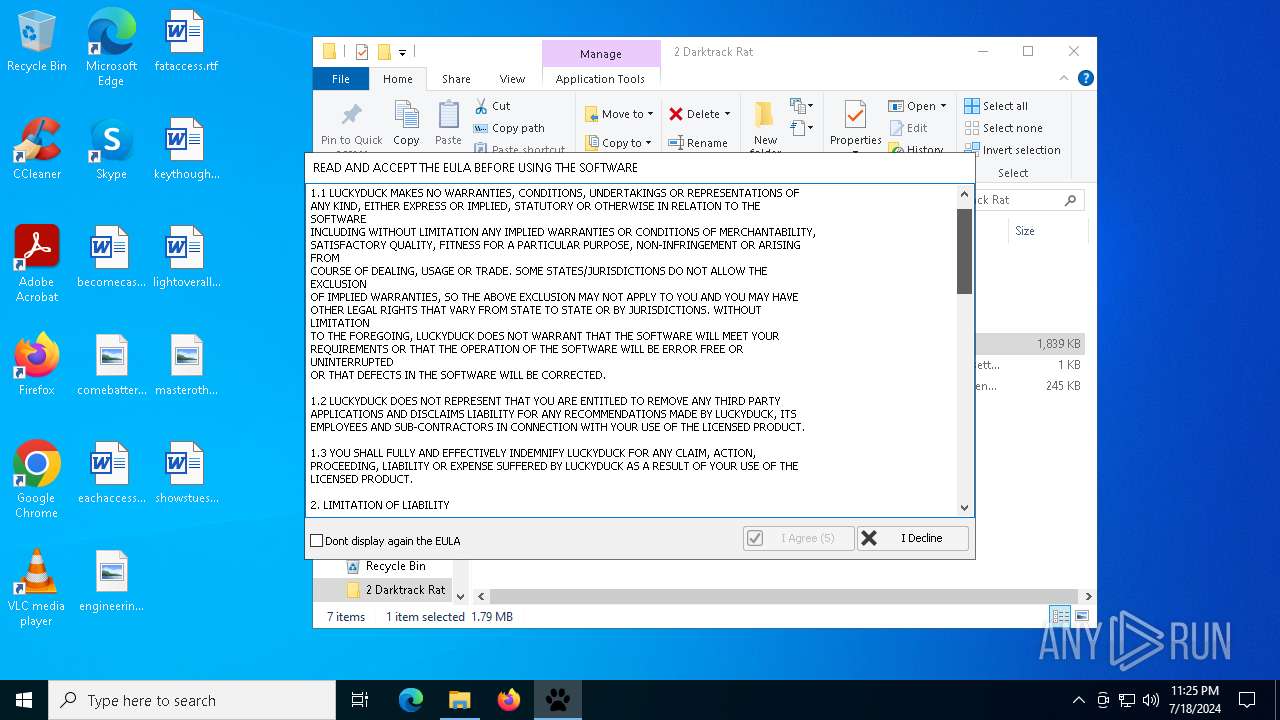
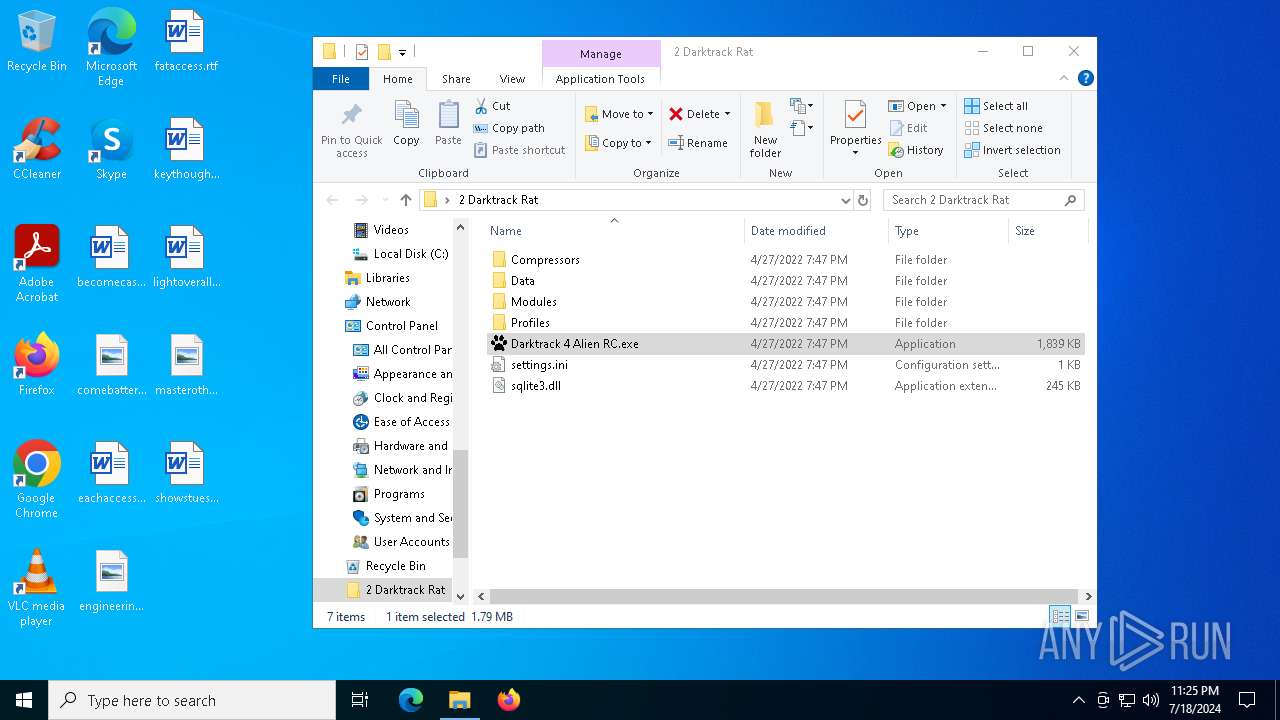
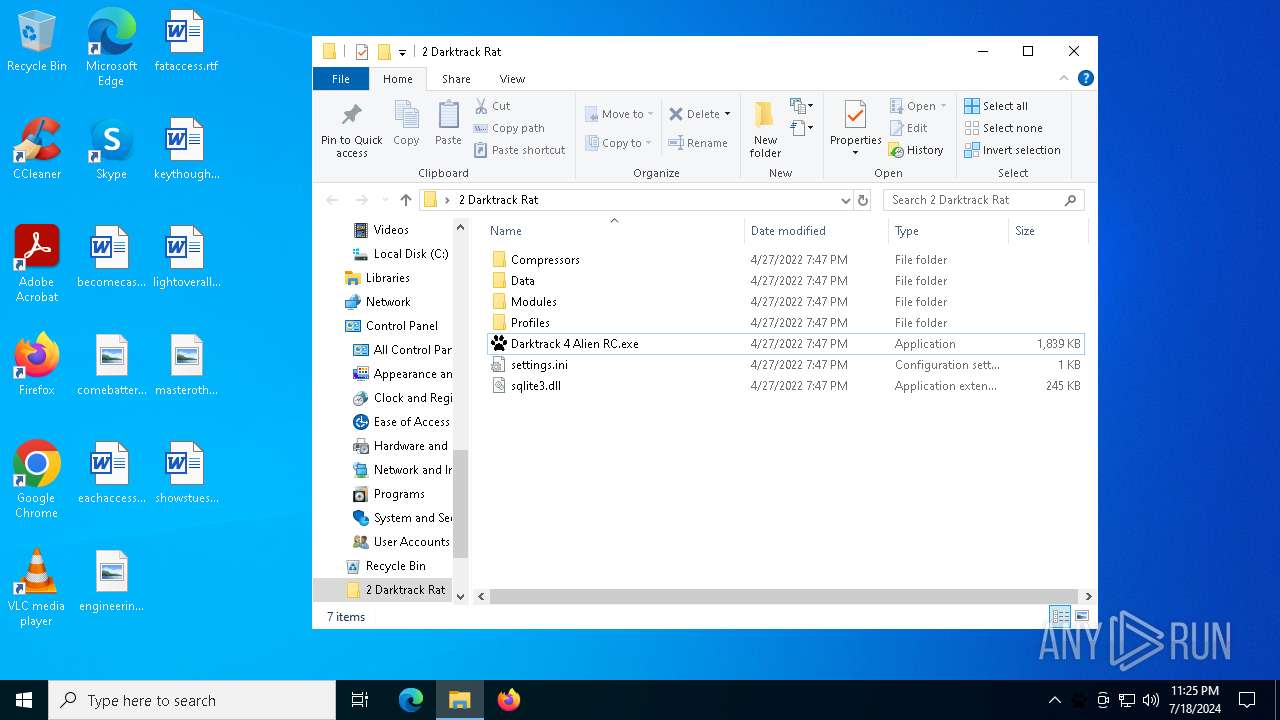
Manual execution by a user
- Darktrack 4 Alien RC.exe (PID: 1164)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7268)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 7268)
Reads the computer name
- Darktrack 4 Alien RC.exe (PID: 1164)
Checks proxy server information
- Darktrack 4 Alien RC.exe (PID: 1164)
Aspack has been detected
- Darktrack 4 Alien RC.exe (PID: 1164)
Reads the machine GUID from the registry
- Darktrack 4 Alien RC.exe (PID: 1164)
Creates files or folders in the user directory
- Darktrack 4 Alien RC.exe (PID: 1164)
Reads the software policy settings
- Darktrack 4 Alien RC.exe (PID: 1164)
Process checks Internet Explorer phishing filters
- Darktrack 4 Alien RC.exe (PID: 1164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
122
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
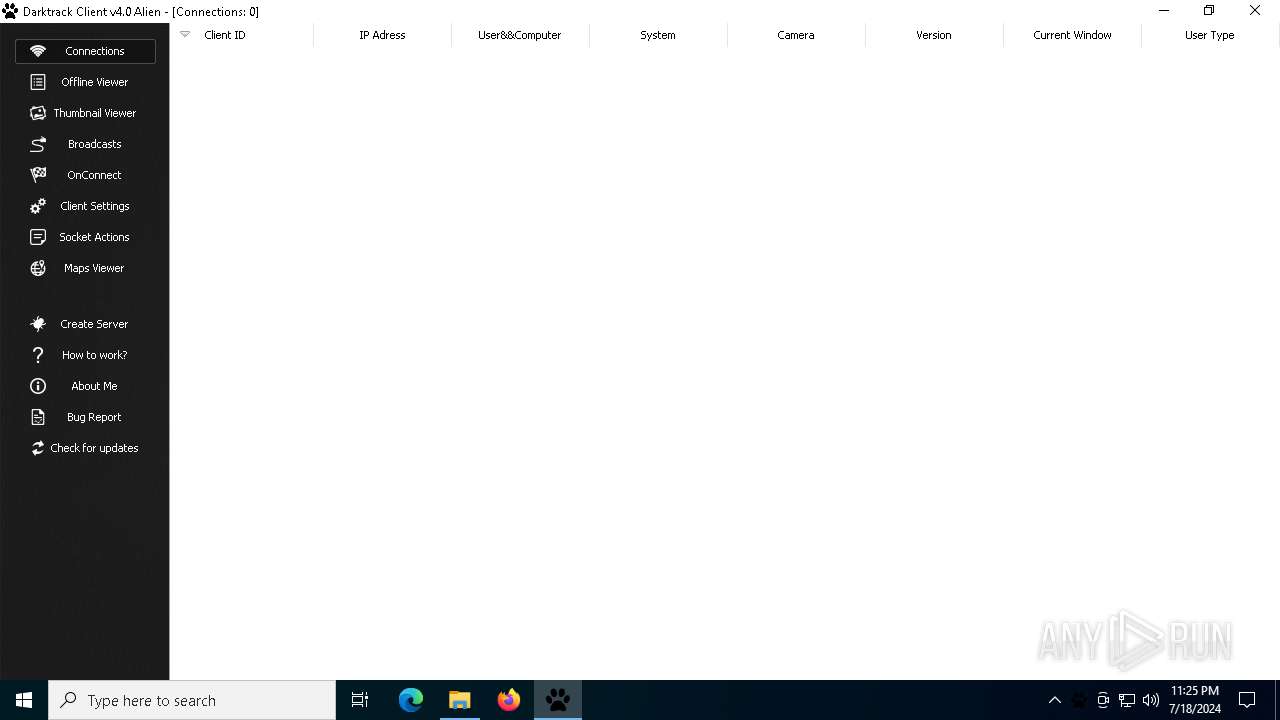
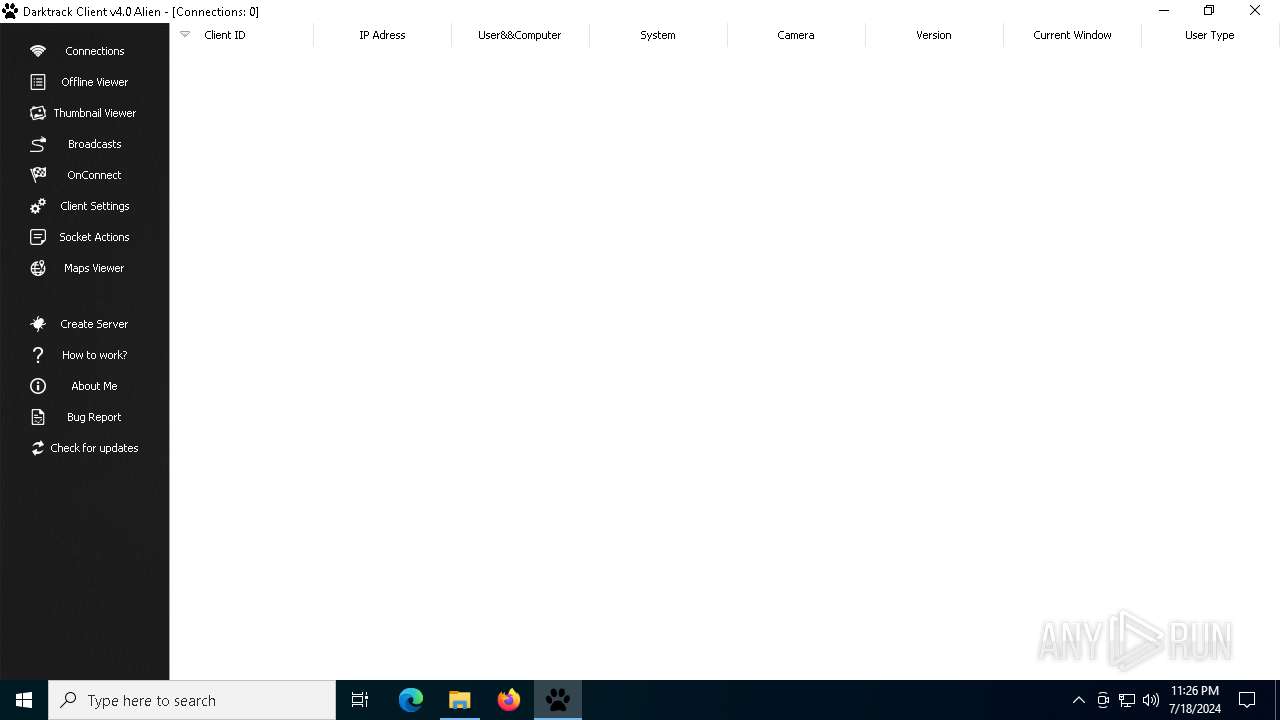
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
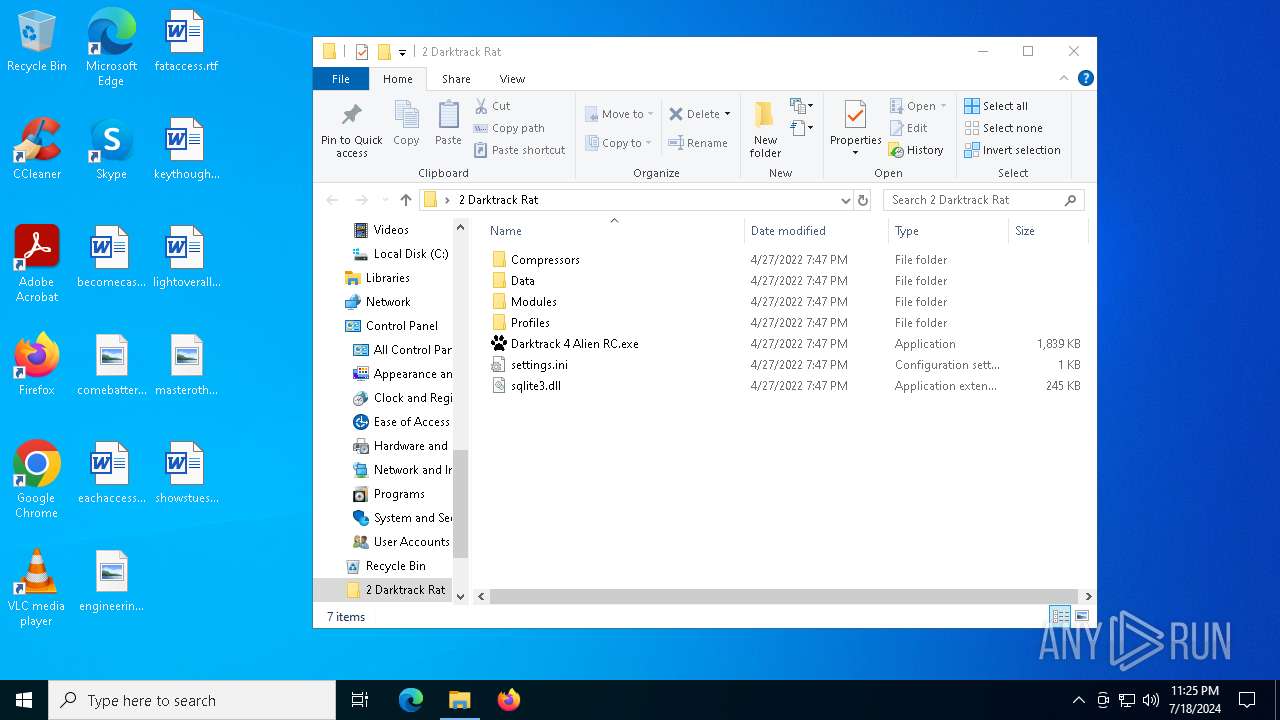
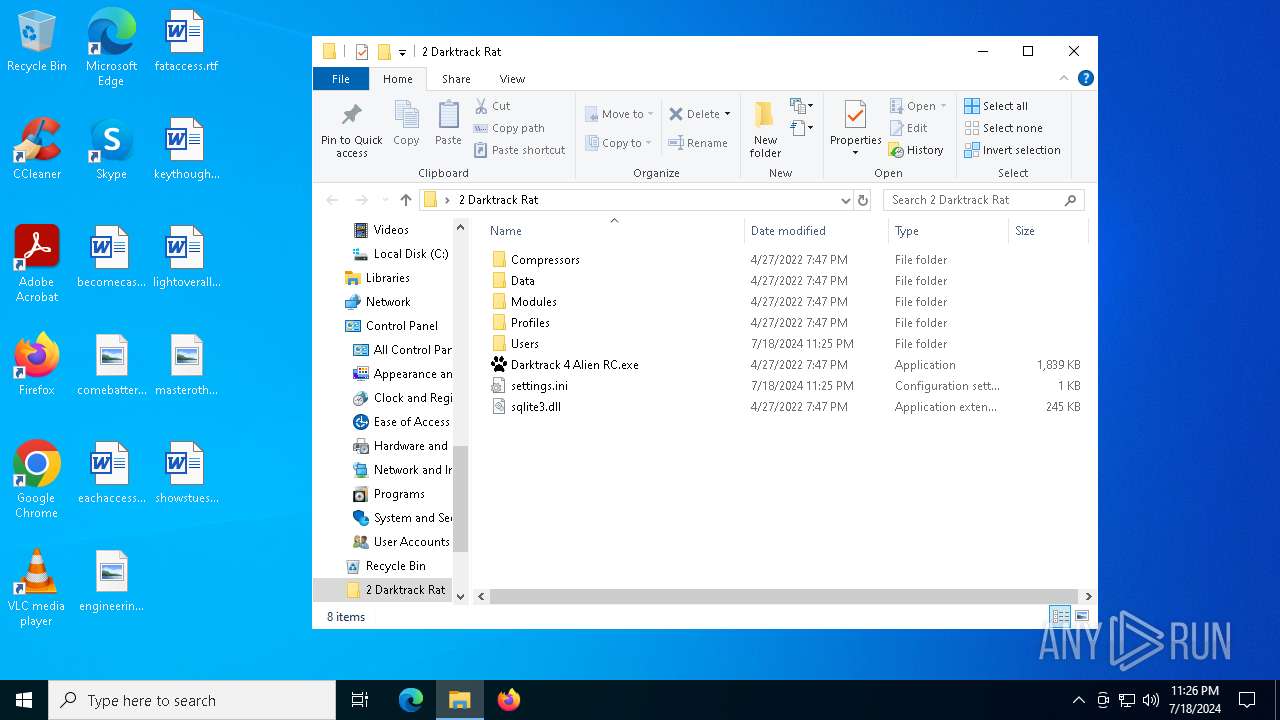
| 1164 | "C:\Users\admin\Desktop\2 Darktrack Rat\Darktrack 4 Alien RC.exe" | C:\Users\admin\Desktop\2 Darktrack Rat\Darktrack 4 Alien RC.exe | explorer.exe | ||||||||||||
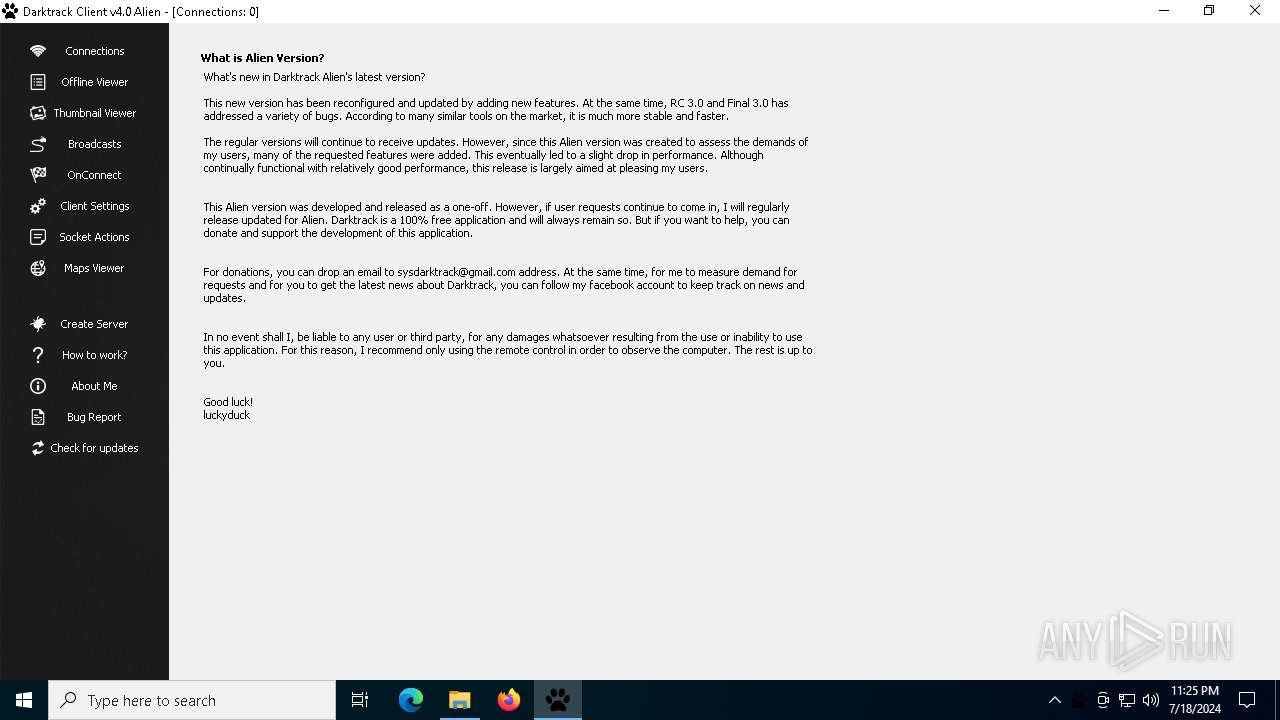
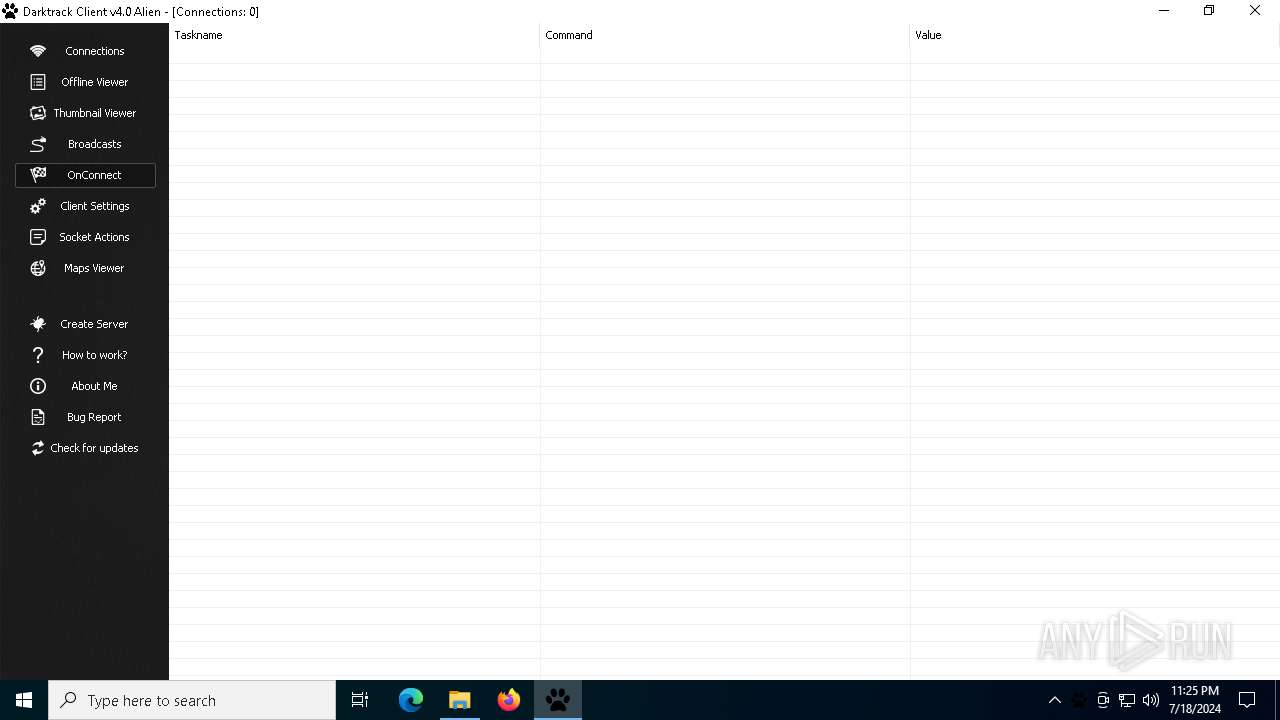
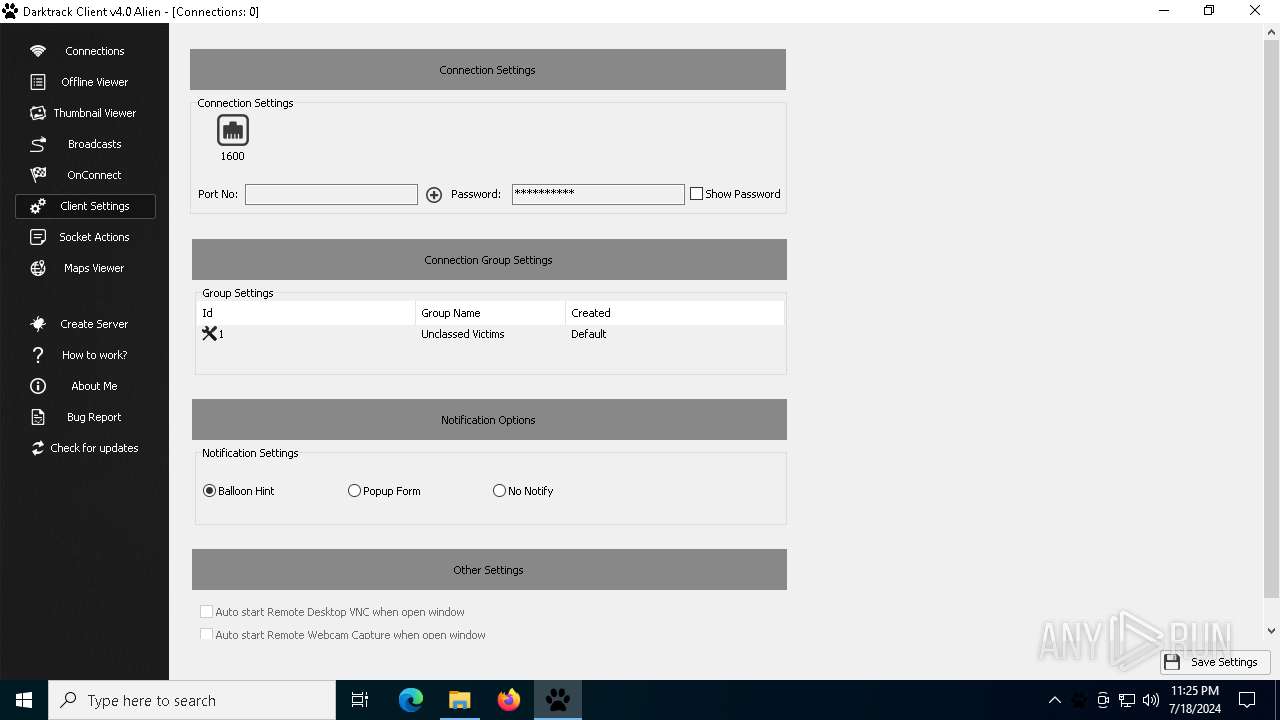
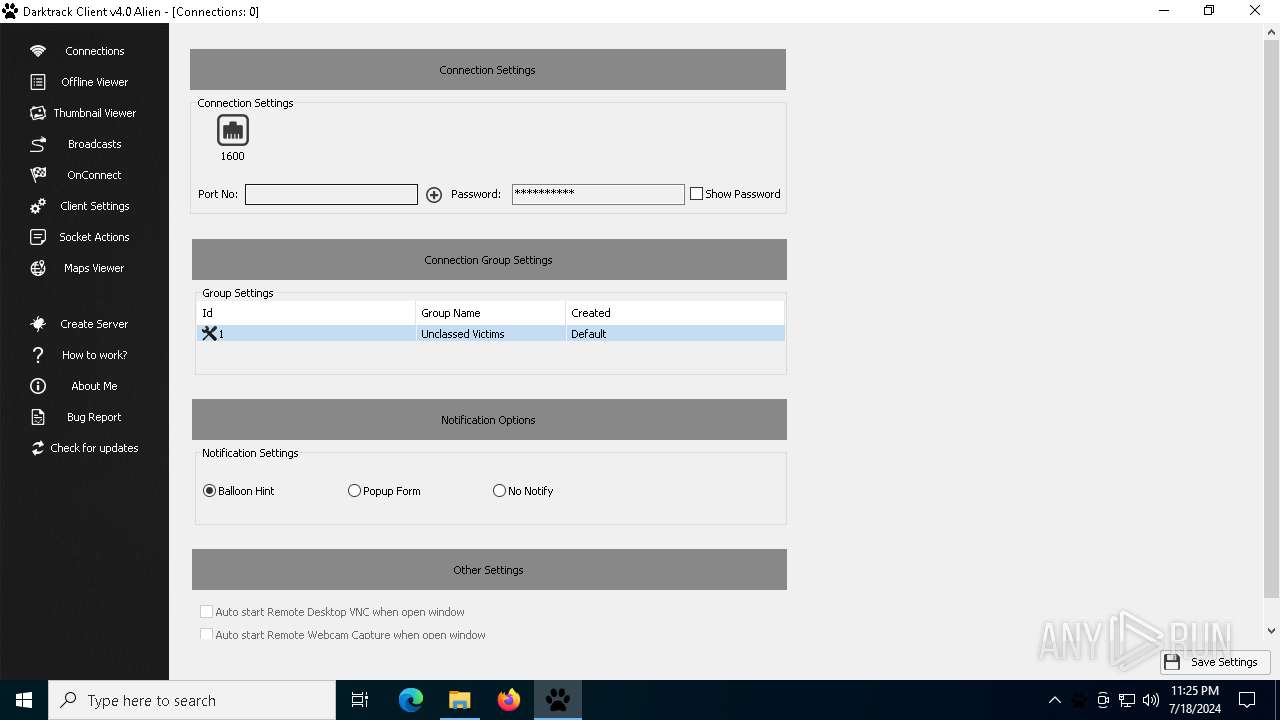
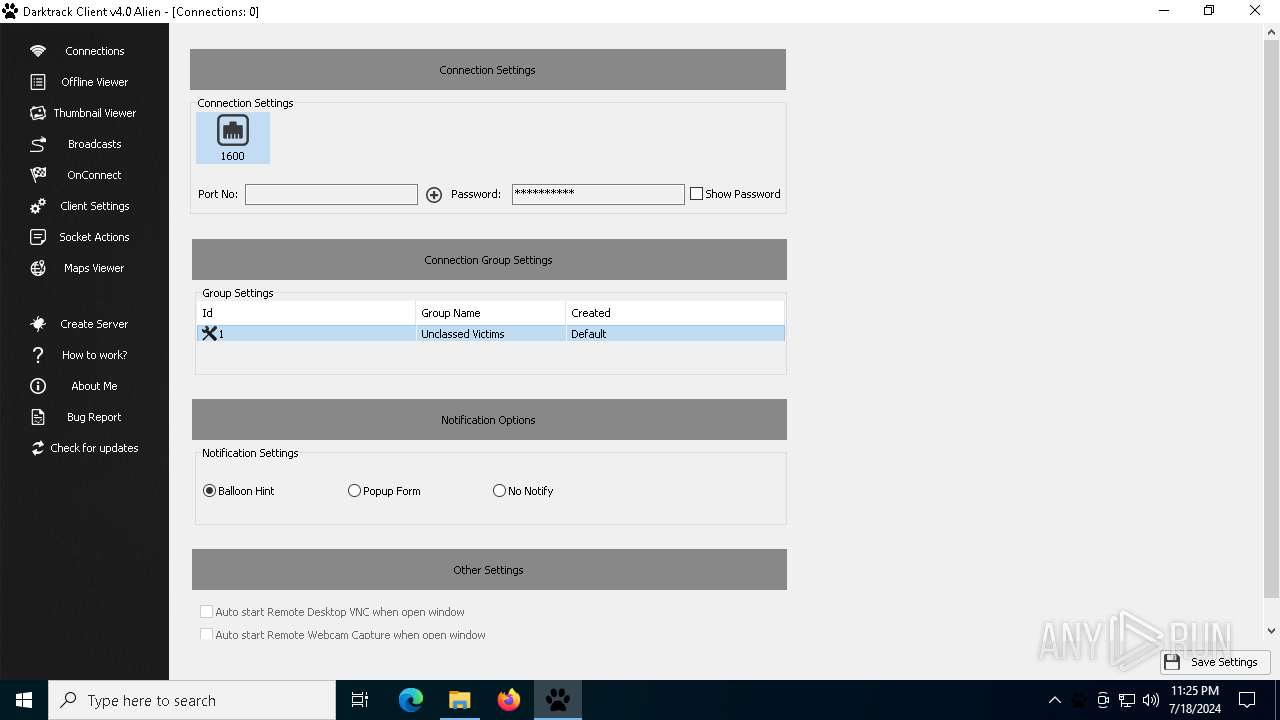
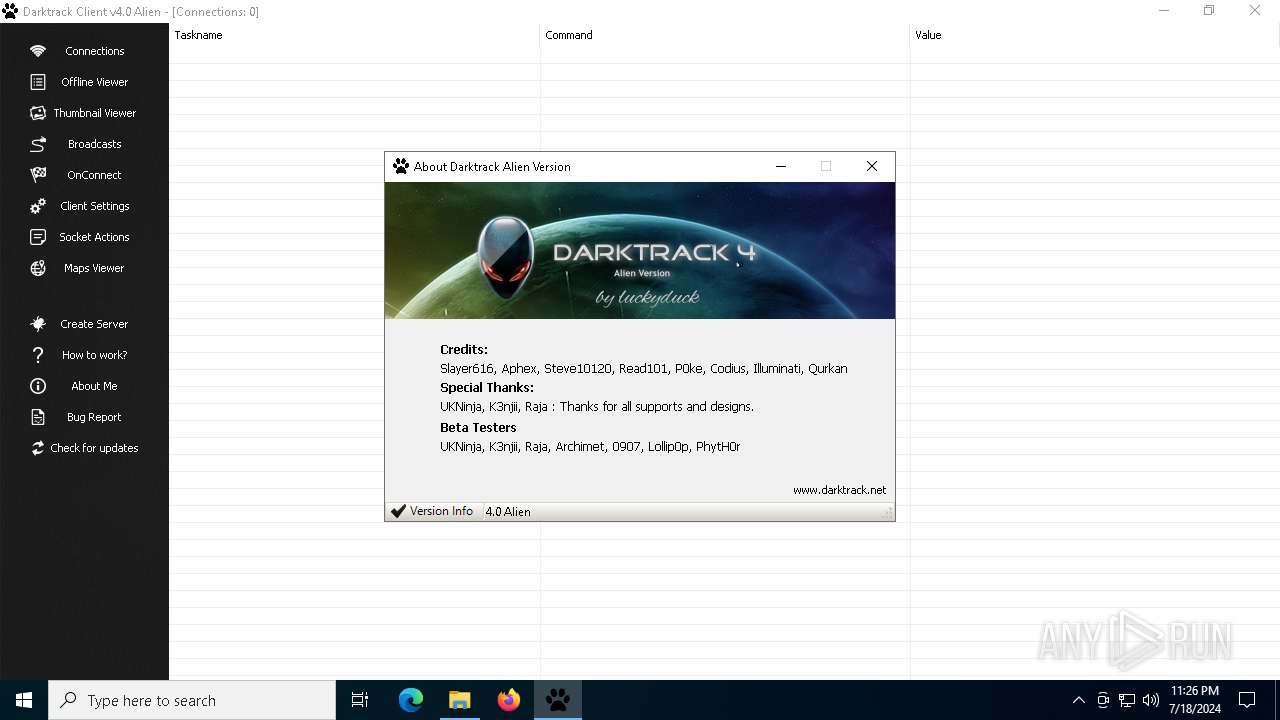
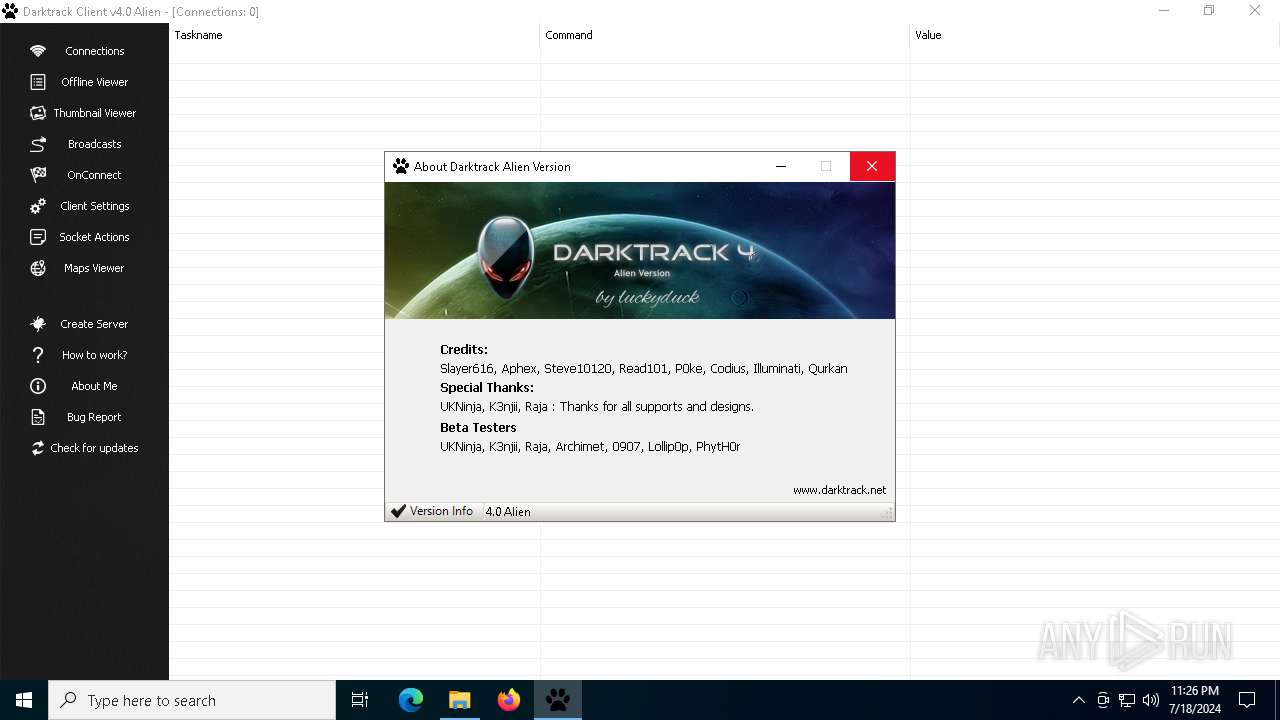
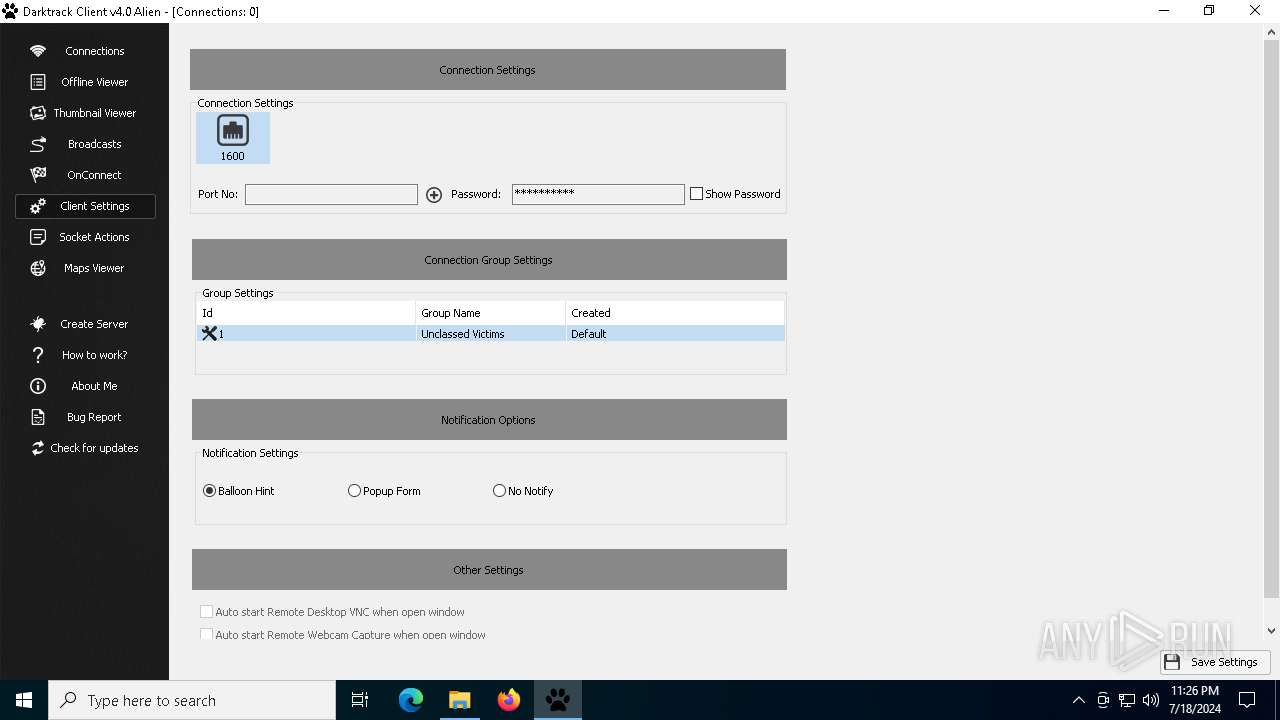
User: admin Company: Darktrack Integrity Level: MEDIUM Description: Remote Administration Tool Exit code: 0 Version: 4.0.0.0 Modules
| |||||||||||||||
| 1832 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
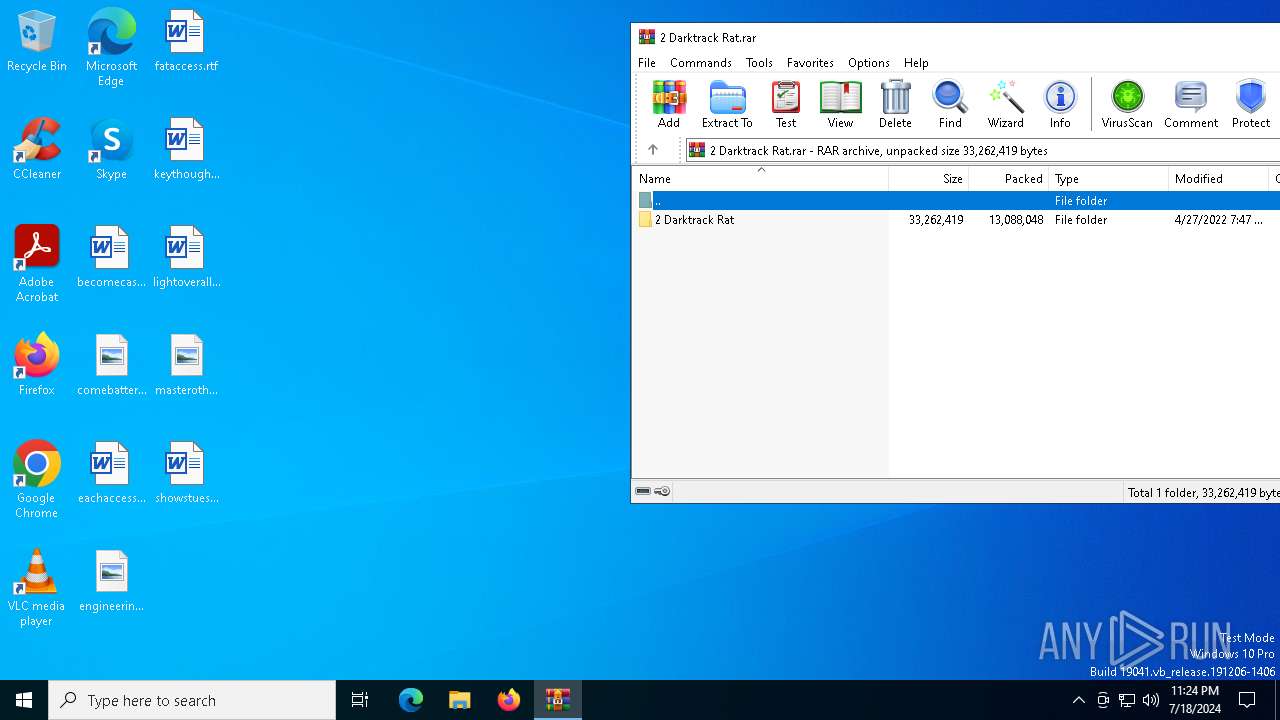
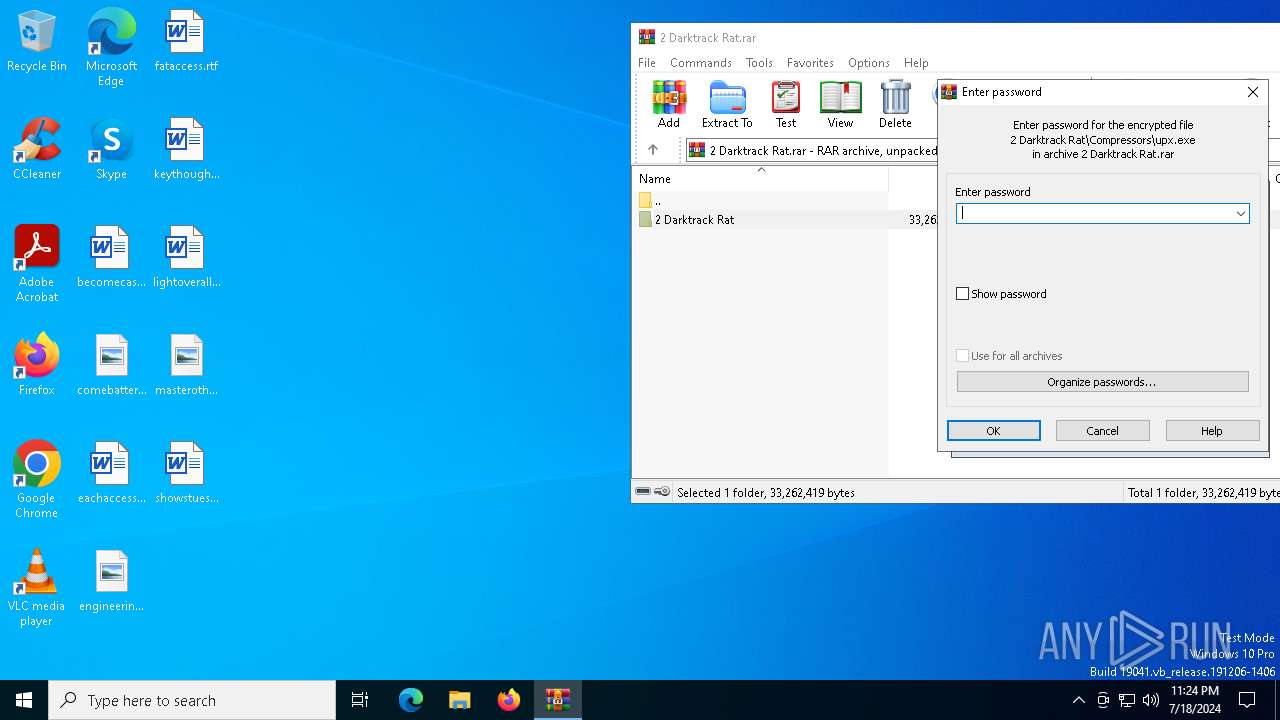
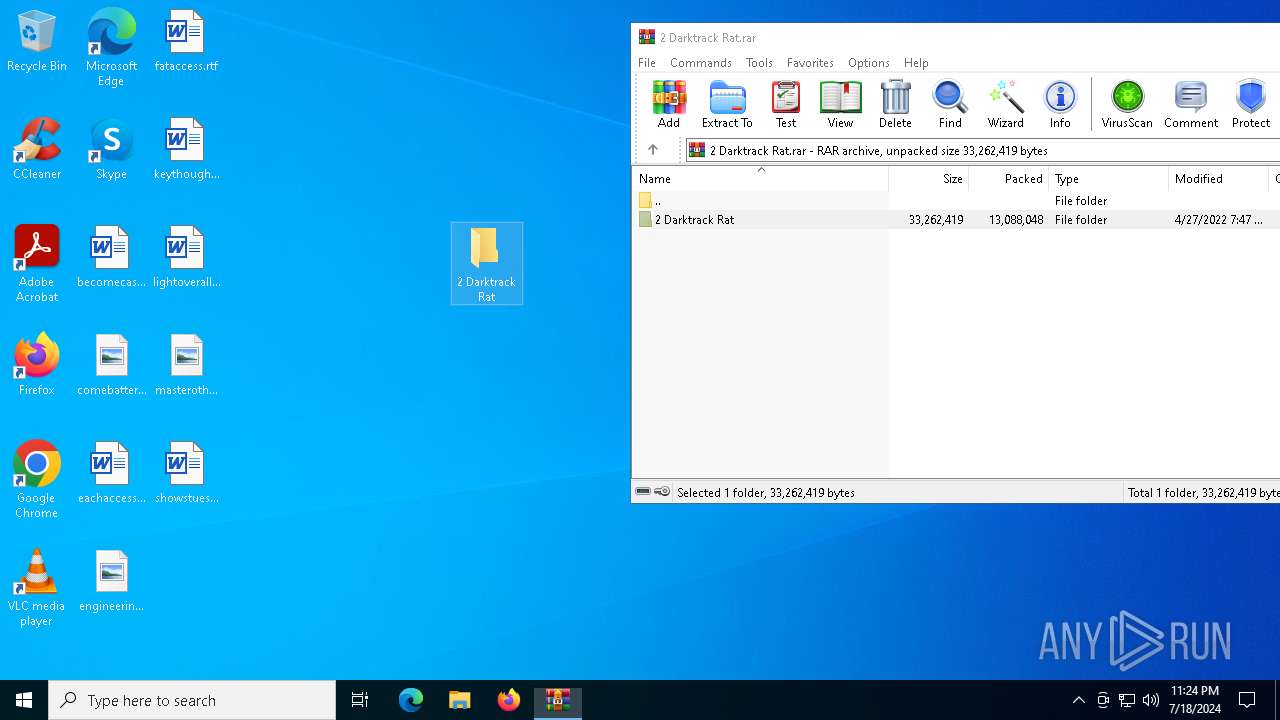
| 7268 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\2 Darktrack Rat.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 7320 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 319
Read events
8 285
Write events
34
Delete events
0
Modification events
| (PID) Process: | (7268) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (7268) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (7268) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (7268) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\2 Darktrack Rat.rar | |||
| (PID) Process: | (7268) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7268) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7268) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7268) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7268) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (7268) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF1300000062000000D30300004B020000 | |||
Executable files
7
Suspicious files
12
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7268 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7268.39613\2 Darktrack Rat\Compressors\upx.exe | executable | |
MD5:308F709A8F01371A6DD088A793E65A5F | SHA256:C0F9FAFFDF14AB2C853880457BE19A237B10F8986755F184ECFE21670076CB35 | |||
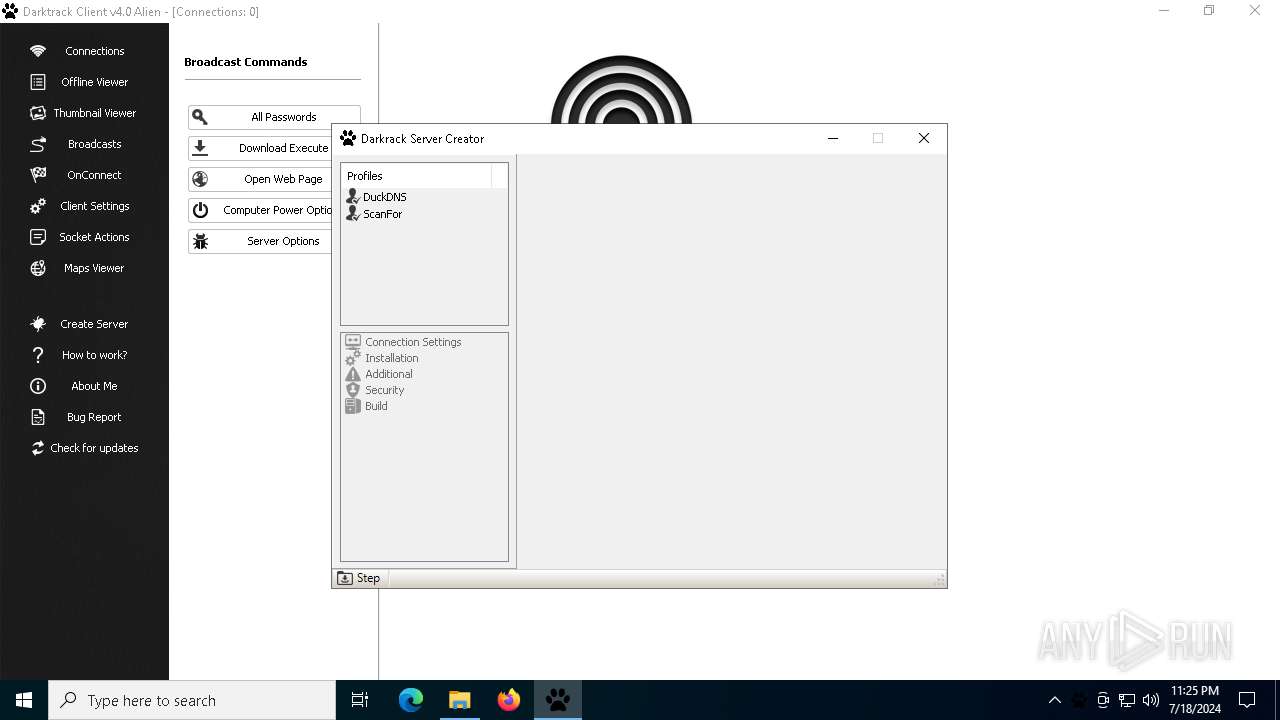
| 7268 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7268.39613\2 Darktrack Rat\Profiles\DuckDNS | text | |
MD5:8B005994814CEBA9A8C2F47DC683366F | SHA256:253EFC0D11B53266D966D43349BADF83AB97483F97A9F928792D701E892CD6CE | |||
| 7268 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7268.39613\2 Darktrack Rat\Profiles\ScanFor | text | |
MD5:0667371BB521CA441BFA5C54F6302832 | SHA256:527338896D53D202618FCBA40707A73B779BF3A417BA2237967F997D704AE229 | |||
| 7268 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7268.39613\2 Darktrack Rat\Darktrack 4 Alien RC.exe | executable | |
MD5:7AFC28B47371FA3488352CD8C3EA818F | SHA256:51C0BA723E062C9E65544B37DAFE7765BA0E56AA8F533915B3639E2649A81B65 | |||
| 7268 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7268.39613\2 Darktrack Rat\Modules\ffmpeg.exe | executable | |
MD5:F25EEF8A89531E8A78340B2A682D6047 | SHA256:1ABEE4A7DBE8F624290054C14EF7B58DB19E93DF976C2ADB8FF4BD20974C3A78 | |||
| 7268 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7268.39613\2 Darktrack Rat\Data\DataBase.db | sqlite | |
MD5:AFDA8CB7D24C955C6A9D283D03B21362 | SHA256:2BC07101CCBD9AED85C7BBADE188BBC1D2E32DA5A146D6D4A71E414DDCA8CFB2 | |||
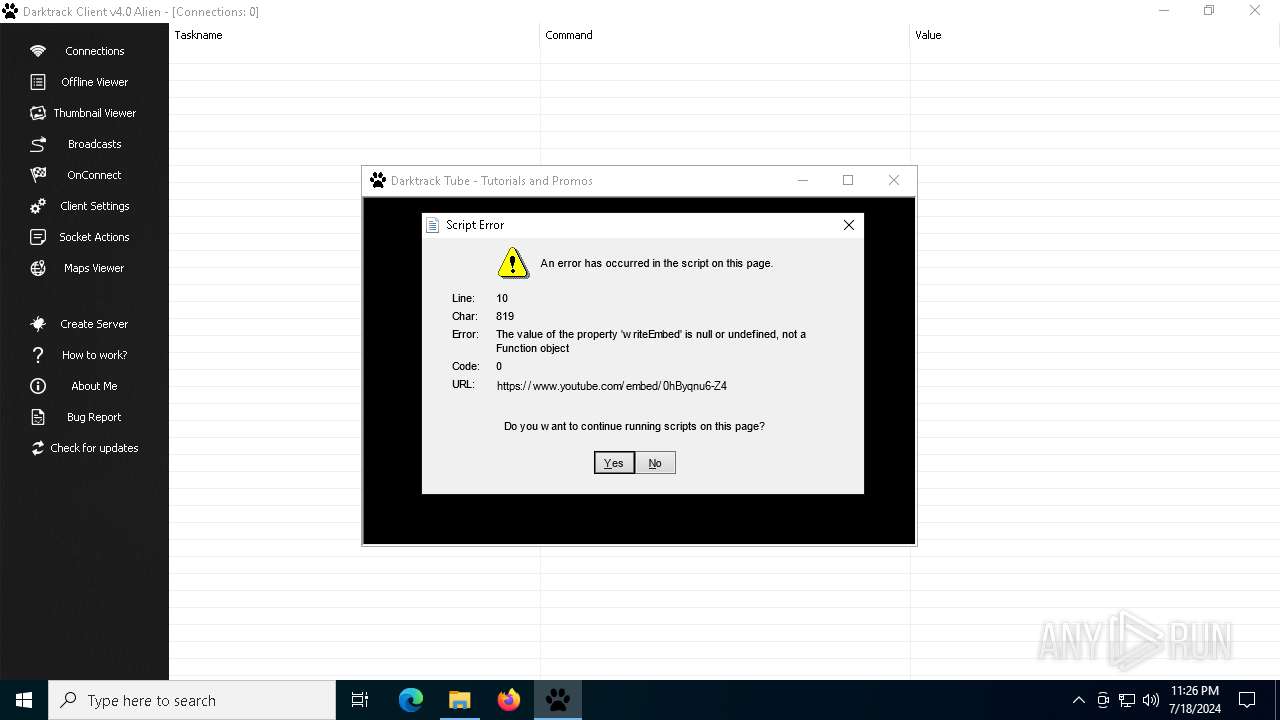
| 1164 | Darktrack 4 Alien RC.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\0hByqnu6-Z4[1].htm | html | |
MD5:4DA7ED98EE7C19CF15EEF24F50DF707B | SHA256:F5006B4C9BF67A074CF0EEBC2C21224D8A2E2475E4AD70D92D062719ACC65363 | |||
| 1164 | Darktrack 4 Alien RC.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\www-player[1].css | text | |
MD5:84BF70B8C21FC2EAB8065766C02CDCC2 | SHA256:07EAAD0272E7B43BB4B569A2BB7F934795913719CA799519B4C146EEE154A5D5 | |||
| 1164 | Darktrack 4 Alien RC.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\AH8CR9J5\www-embed-player[1].js | text | |
MD5:2283B7D03C3F8E247B27B432DA9E6765 | SHA256:DC051C8BBC25A459D27B76D264D8885C4DCABD211848E9ABAA6816767D9A4D0E | |||
| 1164 | Darktrack 4 Alien RC.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\AH8CR9J5\KFOmCnqEu92Fr1Mu4mxO[1].eot | binary | |
MD5:68889C246DA2739681C1065D15A1AB0B | SHA256:830D75BBF0E1F9289D787422F767B23F9D63FD79DBE75C091A119B6B7155D198 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
19
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1164 | Darktrack 4 Alien RC.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | whitelisted |
1164 | Darktrack 4 Alien RC.exe | GET | 200 | 172.217.16.131:80 | http://c.pki.goog/r/r1.crl | unknown | — | — | whitelisted |
1164 | Darktrack 4 Alien RC.exe | GET | 200 | 142.250.185.227:80 | http://o.pki.goog/wr2/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRTQtSEi8EX%2BbYUTXd8%2ByMxD3s1zQQU3hse7XkV1D43JMMhu%2Bw0OW1CsjACEQDJocJI3cuzOAqV4KAdwn94 | unknown | — | — | whitelisted |
— | — | GET | 200 | 142.250.185.227:80 | http://o.pki.goog/wr2/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTQtSEi8EX%2BbYUTXd8%2ByMxD3s1zQQU3hse7XkV1D43JMMhu%2Bw0OW1CsjACEHViWUaptL4MEEkSmq4OScg%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4716 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7856 | svchost.exe | 4.209.32.198:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5968 | backgroundTaskHost.exe | 20.31.169.57:443 | fd.api.iris.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
2760 | svchost.exe | 40.113.110.67:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3384 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7856 | svchost.exe | 4.209.33.156:443 | licensing.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
arc.msn.com |
| whitelisted |
login.live.com |
| whitelisted |
google.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
licensing.mp.microsoft.com |
| whitelisted |
www.youtube.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
c.pki.goog |
| whitelisted |
o.pki.goog |
| whitelisted |