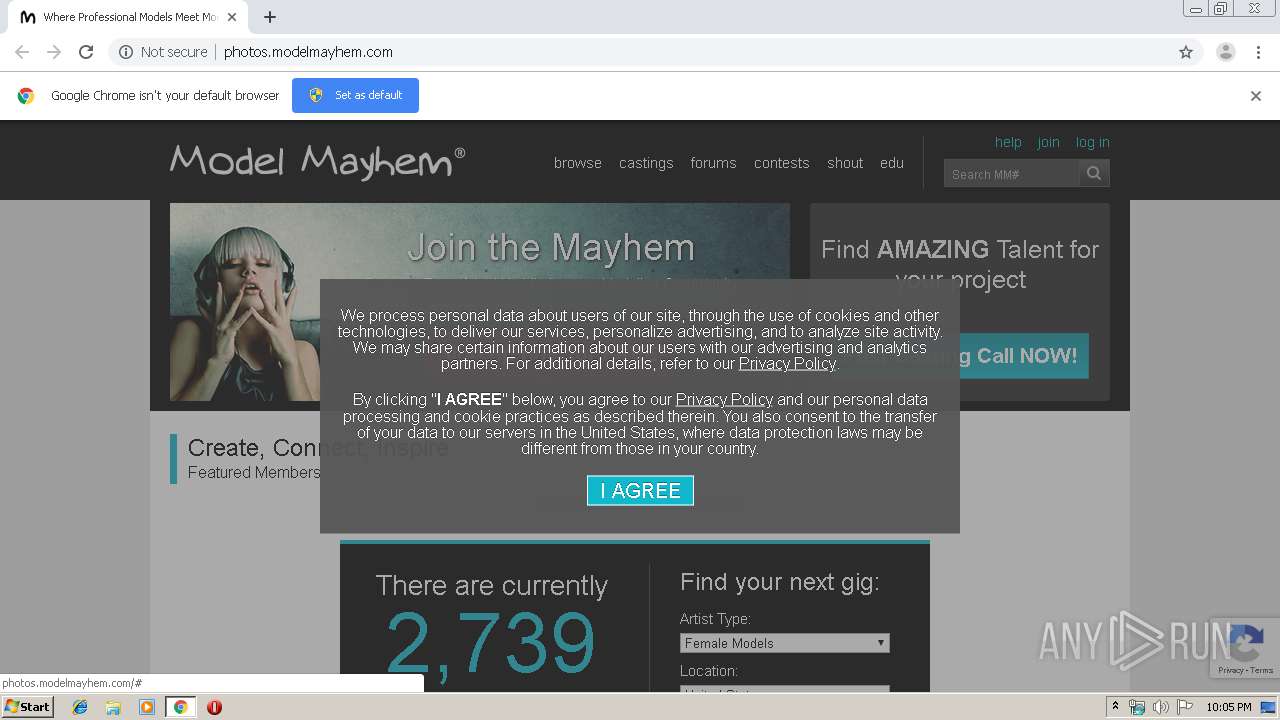
| URL: | http://photos.modelmayhem.com/ |
| Full analysis: | https://app.any.run/tasks/b2b0837a-845e-49ed-8bb3-3cd545b3e785 |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2019, 22:04:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 732CEE9056F17EA84E78571DC9802740 |
| SHA1: | 24481C7860B1BE1F54CEED4B3D63999D411BED95 |
| SHA256: | 6A1637DD25054A07378468D78D573272C7E9621DB5DC5CA05820140B503FBC15 |
| SSDEEP: | 3:N1KONK2aAG1SIt:CON3Ly |
MALICIOUS
Runs injected code in another process
- chrome.exe (PID: 2152)
Application was injected by another process
- dllhost.exe (PID: 3680)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2152)
INFO
Application launched itself
- chrome.exe (PID: 2152)
Reads the hosts file
- chrome.exe (PID: 2152)
- chrome.exe (PID: 1780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
68
Monitored processes
33
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,13071746730612695572,7689963453770484172,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2090413521416810608 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,13071746730612695572,7689963453770484172,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17076106831596315071 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4632 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,13071746730612695572,7689963453770484172,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3527317823882009112 --mojo-platform-channel-handle=4444 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,13071746730612695572,7689963453770484172,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13294584312335955936 --mojo-platform-channel-handle=4924 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,13071746730612695572,7689963453770484172,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15986295804134914363 --mojo-platform-channel-handle=4952 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,13071746730612695572,7689963453770484172,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5779590675641728818 --mojo-platform-channel-handle=4844 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,13071746730612695572,7689963453770484172,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16763467642391757826 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3540 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,13071746730612695572,7689963453770484172,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13341139612979399201 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2980 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,13071746730612695572,7689963453770484172,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=47633100384988833 --mojo-platform-channel-handle=5164 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,13071746730612695572,7689963453770484172,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=5735001402279667087 --mojo-platform-channel-handle=1540 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
226
Read events
133
Write events
88
Delete events
5
Modification events
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2128) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2152-13219797899932750 |
Value: 259 | |||
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
98
Text files
269
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4122def9-1129-4847-b915-9d492195f420.tmp | — | |
MD5:— | SHA256:— | |||
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39a62d.TMP | text | |
MD5:— | SHA256:— | |||
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a61e.TMP | text | |
MD5:— | SHA256:— | |||
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
61
DNS requests
43
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1780 | chrome.exe | GET | 200 | 104.27.136.158:80 | http://photos.modelmayhem.com/ | US | html | 11.7 Kb | malicious |
1780 | chrome.exe | GET | 200 | 104.27.136.158:80 | http://assets.modelmayhem.com/includes/css/gdpr.css?201911060935 | US | text | 74 b | malicious |
1780 | chrome.exe | GET | 200 | 104.27.136.158:80 | http://assets.modelmayhem.com/includes/css/homepage/all.css?201911060935 | US | text | 7.12 Kb | malicious |
1780 | chrome.exe | GET | 200 | 104.27.136.158:80 | http://assets.modelmayhem.com/includes/js/callgdpr.js?201911060935 | US | text | 427 b | malicious |
1780 | chrome.exe | GET | 200 | 104.27.136.158:80 | http://assets.modelmayhem.com/includes/css/groups_colors.css?201911060935 | US | text | 234 b | malicious |
1780 | chrome.exe | GET | 200 | 104.27.136.158:80 | http://photos.modelmayhem.com/images/loadingAnimation.gif | US | image | 5.75 Kb | malicious |
1780 | chrome.exe | GET | 200 | 104.27.136.158:80 | http://photos.modelmayhem.com/cdn-cgi/scripts/5c5dd728/cloudflare-static/email-decode.min.js | US | html | 655 b | malicious |
1780 | chrome.exe | GET | 200 | 104.27.136.158:80 | http://photos.modelmayhem.com/includes/css/newHomePageMessage.css | US | text | 228 b | malicious |
1780 | chrome.exe | GET | 200 | 104.27.136.158:80 | http://assets.modelmayhem.com/images/homepage/sprite_v2.png | US | image | 11.6 Kb | malicious |
1780 | chrome.exe | GET | 200 | 104.27.136.158:80 | http://assets.modelmayhem.com/includes/css/site_messages.css?201911060935 | US | text | 682 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1780 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1780 | chrome.exe | 104.27.136.158:80 | photos.modelmayhem.com | Cloudflare Inc | US | suspicious |
1780 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
1780 | chrome.exe | 216.58.208.36:443 | www.google.com | Google Inc. | US | whitelisted |
1780 | chrome.exe | 216.58.205.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1780 | chrome.exe | 104.17.65.4:443 | ajax.cloudflare.com | Cloudflare Inc | US | unknown |
1780 | chrome.exe | 172.217.21.206:443 | www.youtube.com | Google Inc. | US | whitelisted |
1780 | chrome.exe | 99.81.183.143:443 | modelmayhem.t.domdex.com | AT&T Services, Inc. | US | unknown |
1780 | chrome.exe | 104.27.164.211:443 | www.internetbrands.com | Cloudflare Inc | US | shared |
1780 | chrome.exe | 195.181.174.6:443 | load77.exelator.com | Datacamp Limited | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
photos.modelmayhem.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
assets.modelmayhem.com |
| malicious |
www.google.com |
| malicious |
ajax.cloudflare.com |
| whitelisted |
modelmayhem.t.domdex.com |
| unknown |
www.gstatic.com |
| whitelisted |
www.youtube.com |
| whitelisted |
plus.google.com |
| whitelisted |