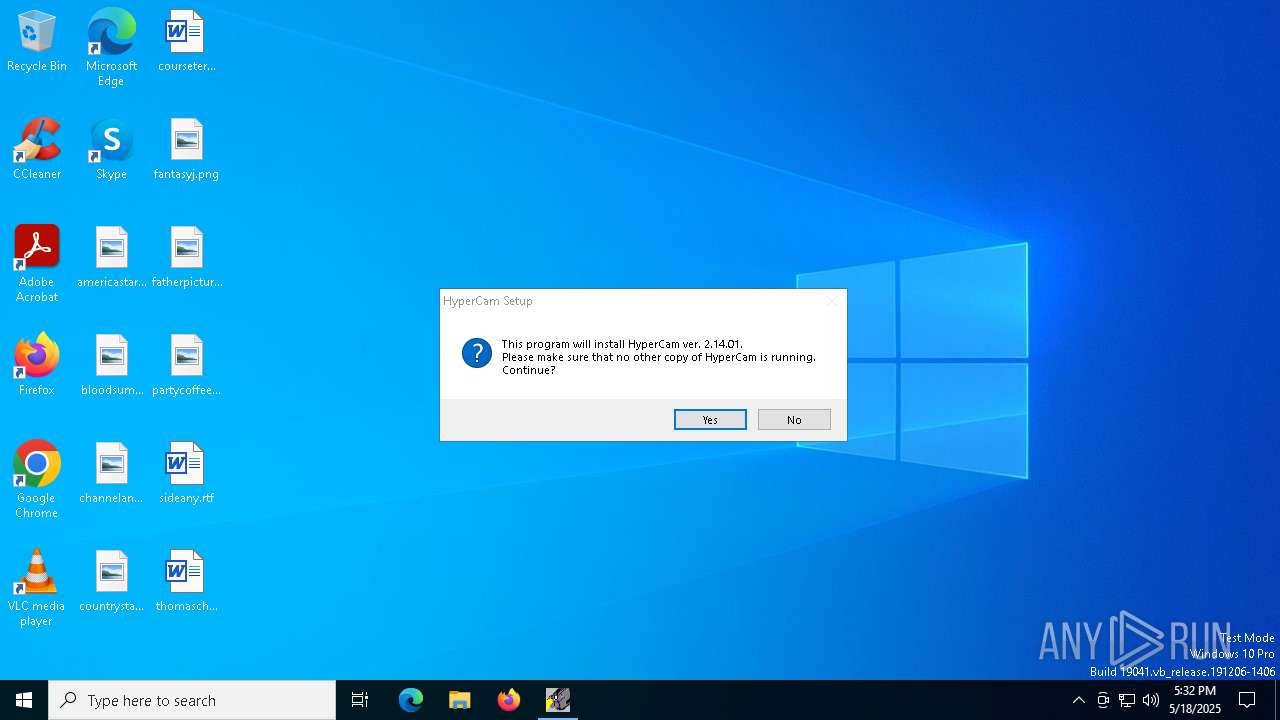
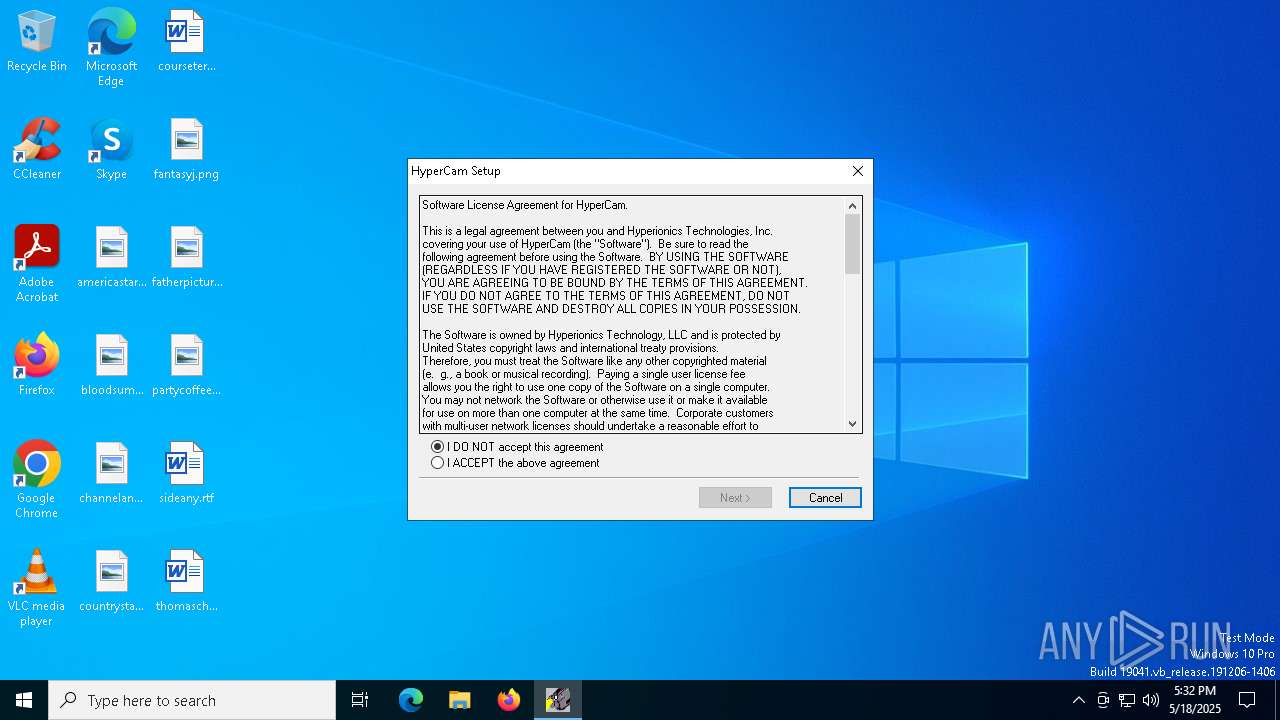
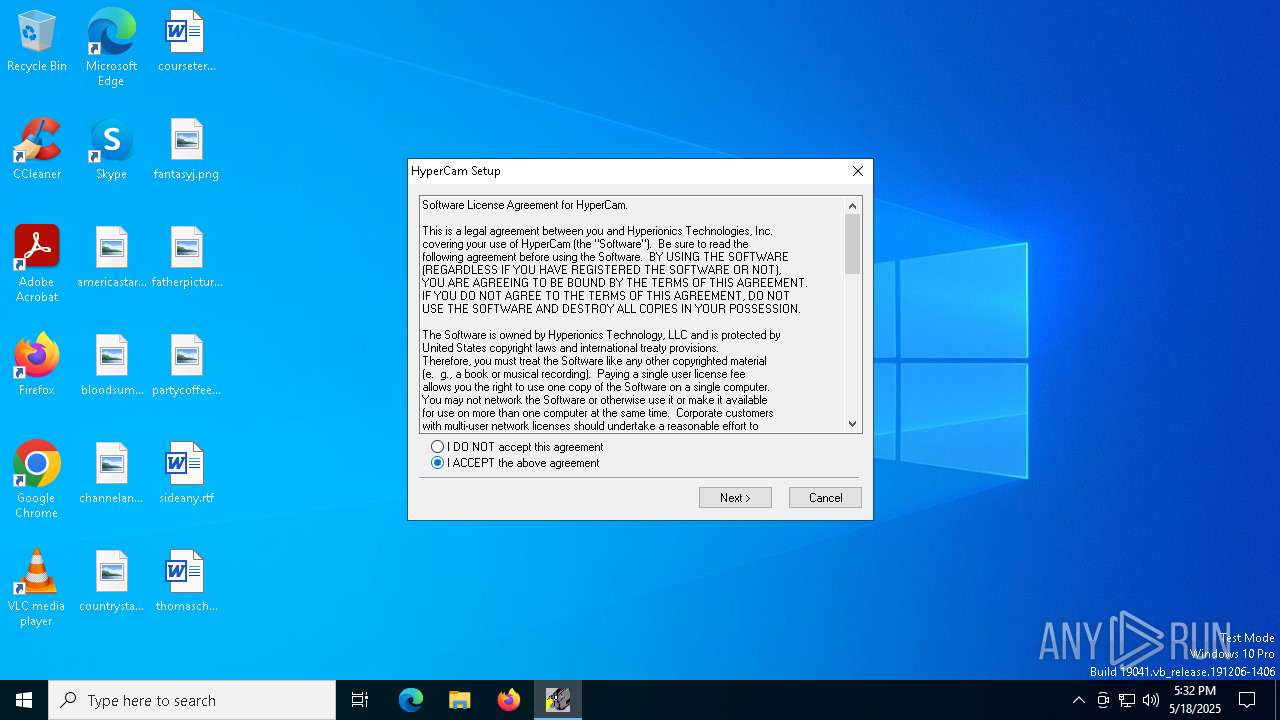
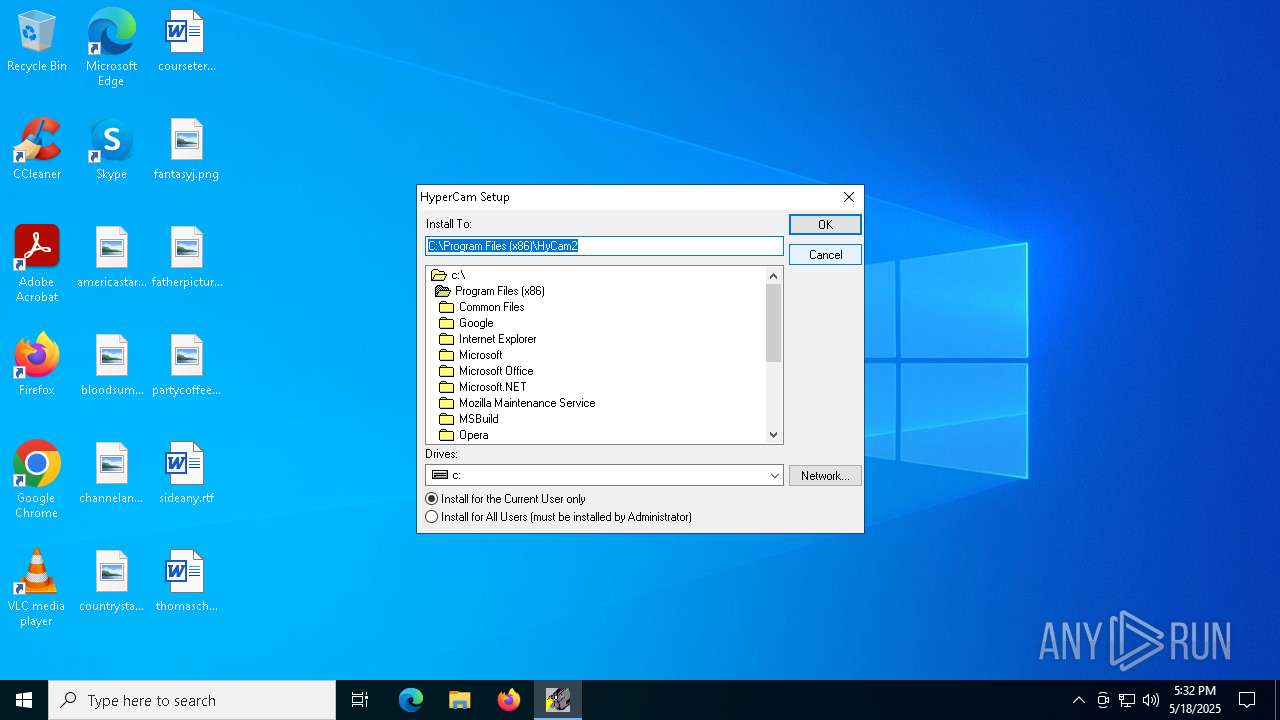
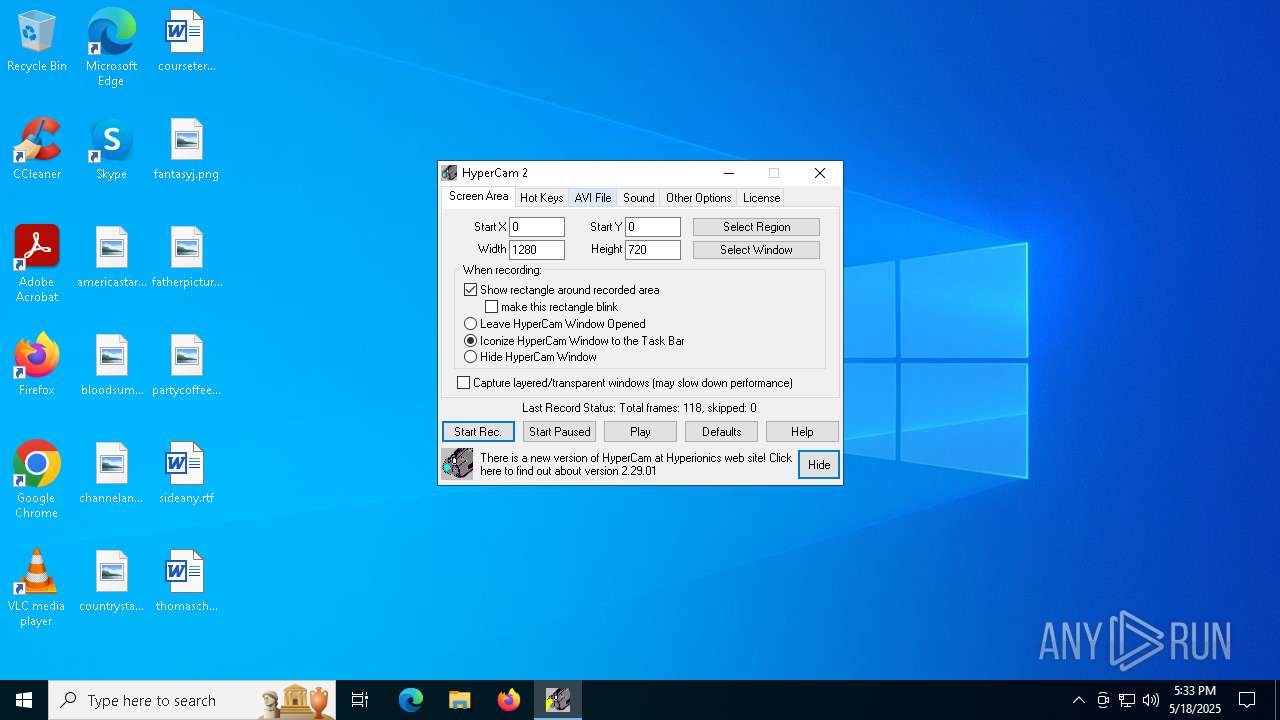
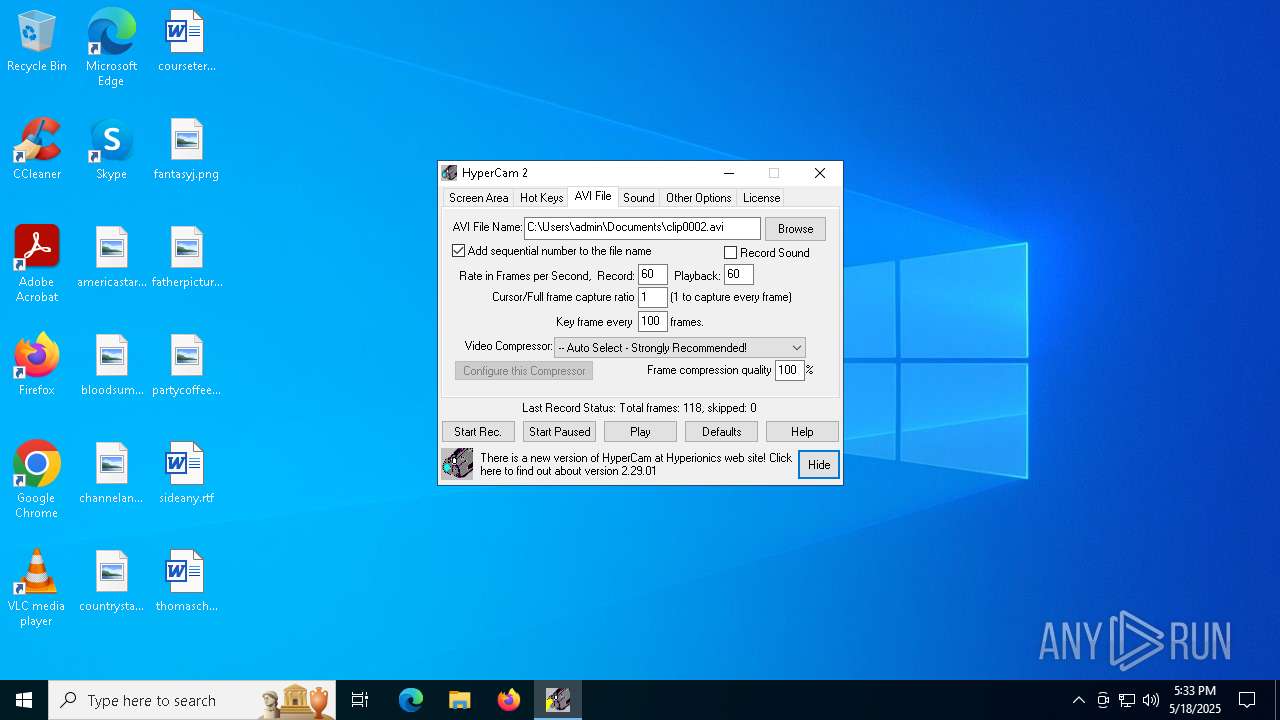
| download: | /download/UnregisteredHyperCam2/HC2Setup.exe |
| Full analysis: | https://app.any.run/tasks/ec933b78-d356-4743-ac0a-d683daaa1a85 |
| Verdict: | Malicious activity |
| Analysis date: | May 18, 2025, 17:32:13 |
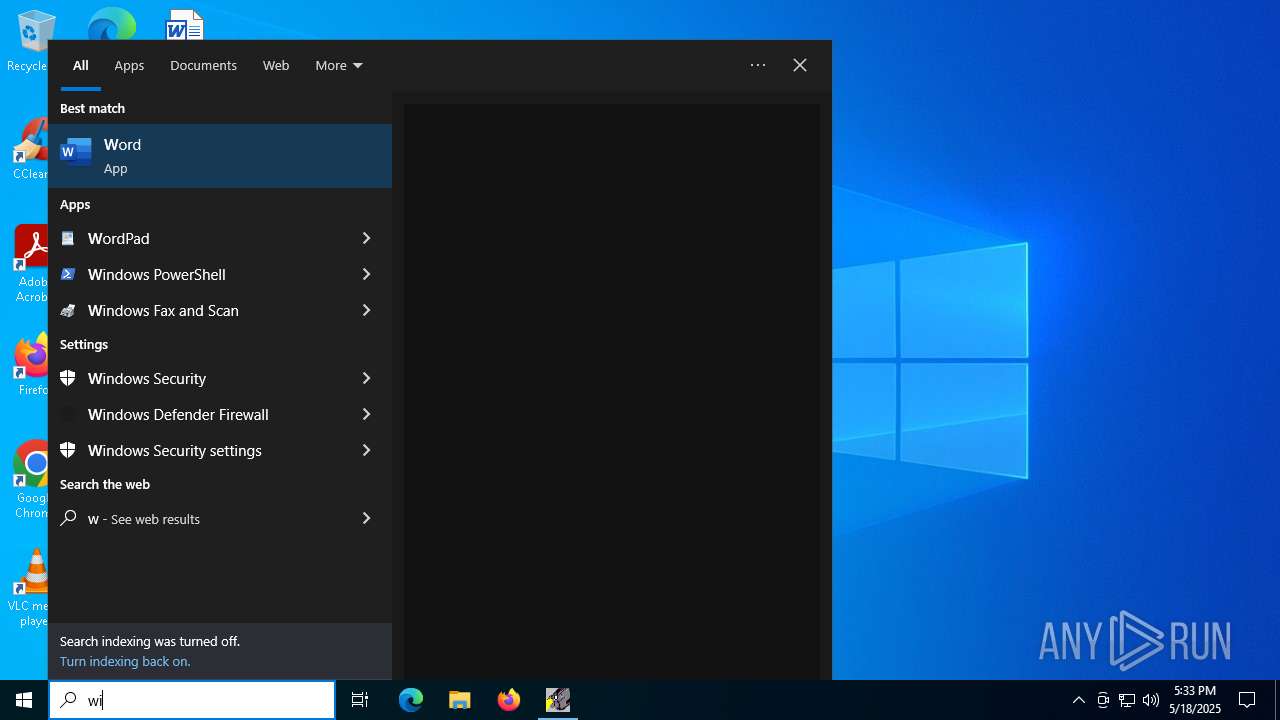
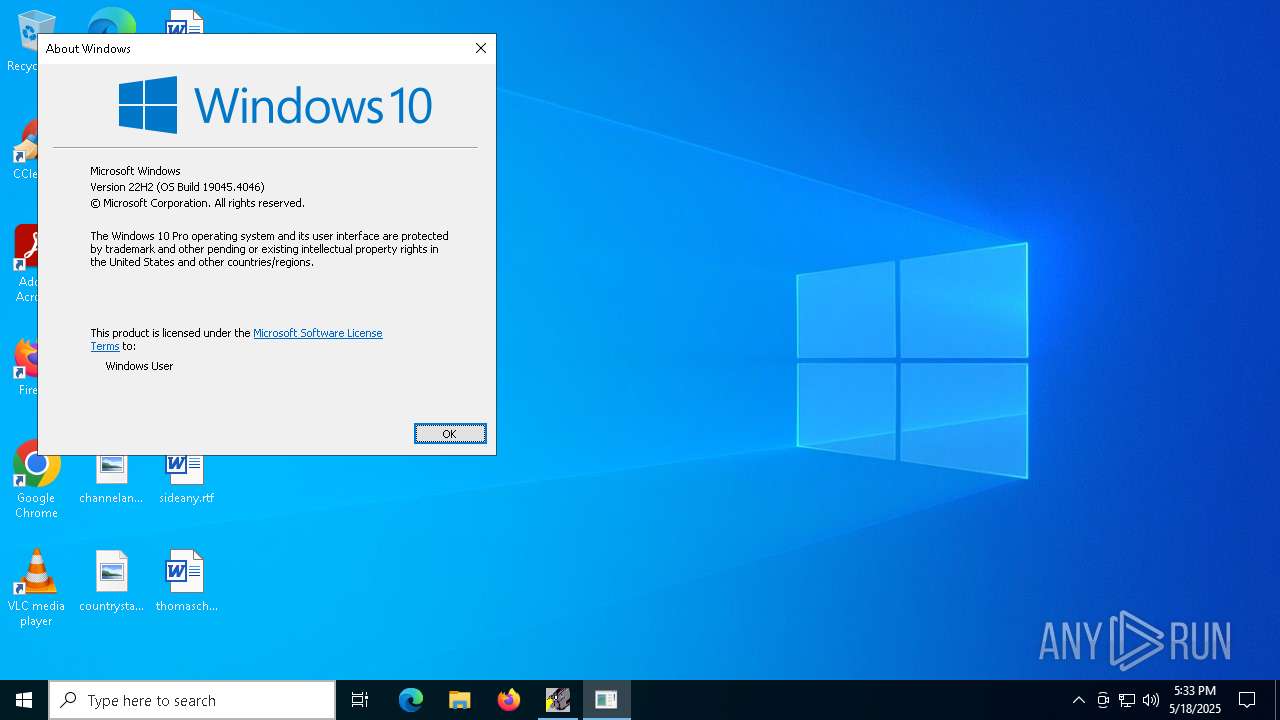
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive, 4 sections |
| MD5: | F96A73B23464366E4158620B10FA52C5 |
| SHA1: | 1B048D127670EA9C113C3582C7D2BFDE2BC4B32A |
| SHA256: | 6A06B2BA1A32B703D65F43D49DDAA8E74D8F5ADD21A8AB04AA0044937A5A50C5 |
| SSDEEP: | 24576:Lev+eq3WBaH4tnpWrcLkx0j6a0BkIgsgq4bSu2wU1DjsJMY9cLYelTgJORXs:a5BaYtnpWrcLkx0j6amkIgsgqASu2wU+ |
MALICIOUS
Executing a file with an untrusted certificate
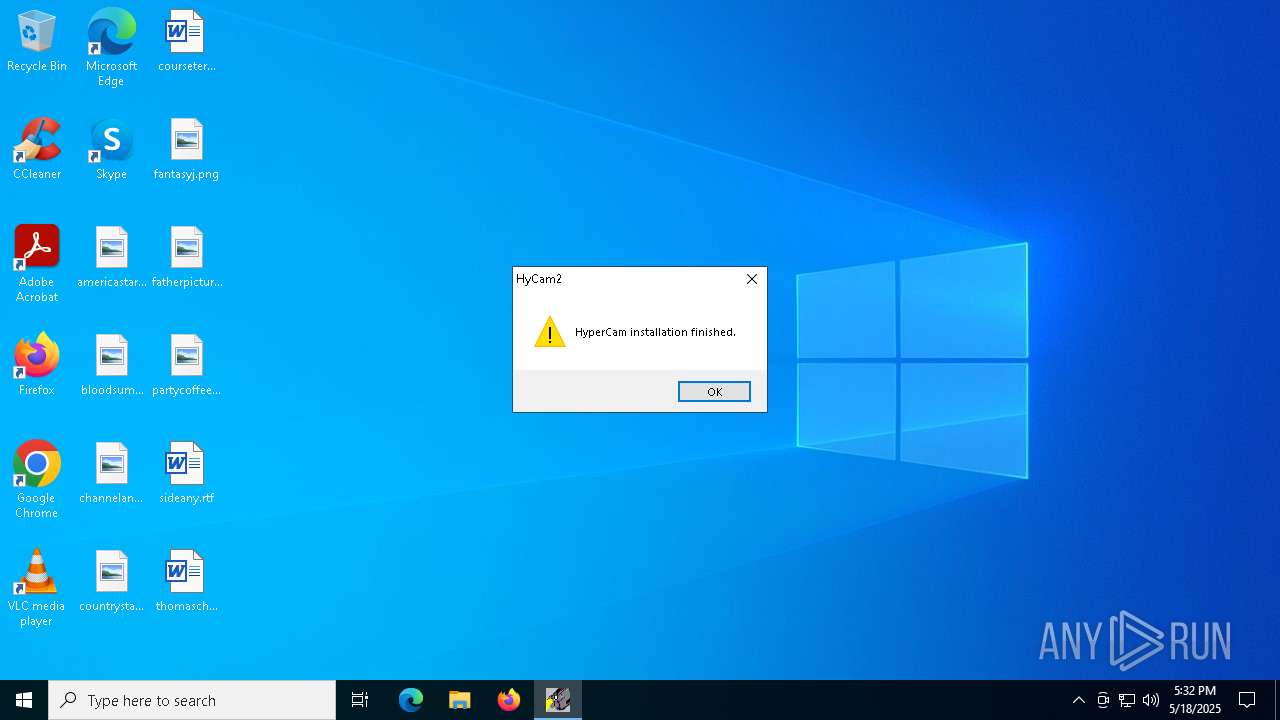
- HyCam2.exe (PID: 7904)
- HyCam2.exe (PID: 2852)
- HC2Setup.exe (PID: 4652)
SUSPICIOUS
Executable content was dropped or overwritten
- HyCam2.exe (PID: 2852)
- HC2Setup.exe (PID: 6040)
Reads security settings of Internet Explorer
- HC2Setup.exe (PID: 6040)
- HyCam2.exe (PID: 7904)
Creates a software uninstall entry
- HyCam2.exe (PID: 2852)
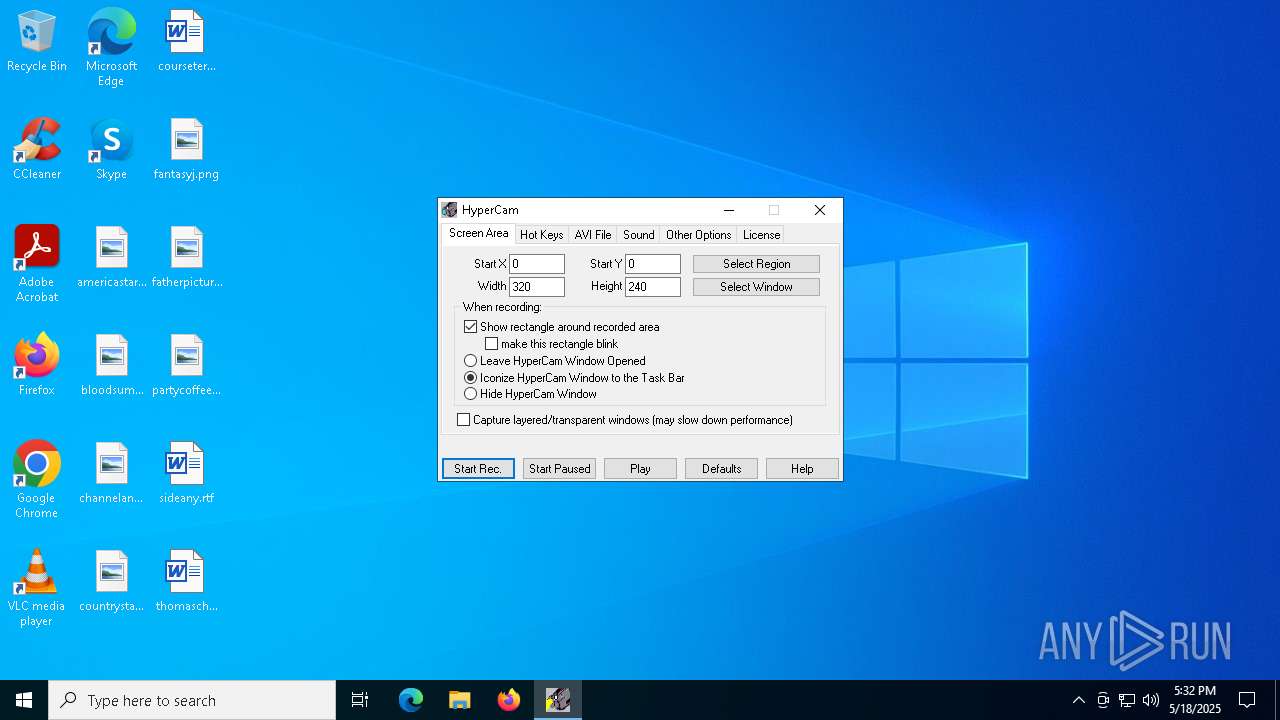
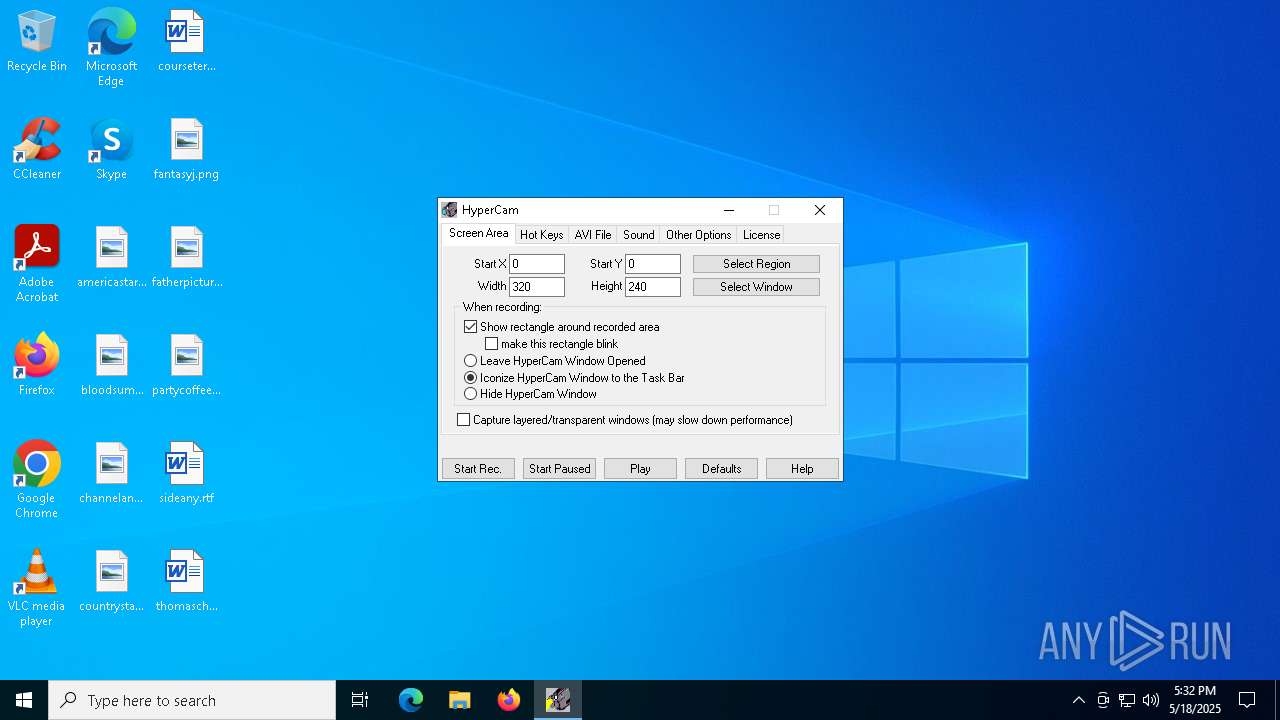
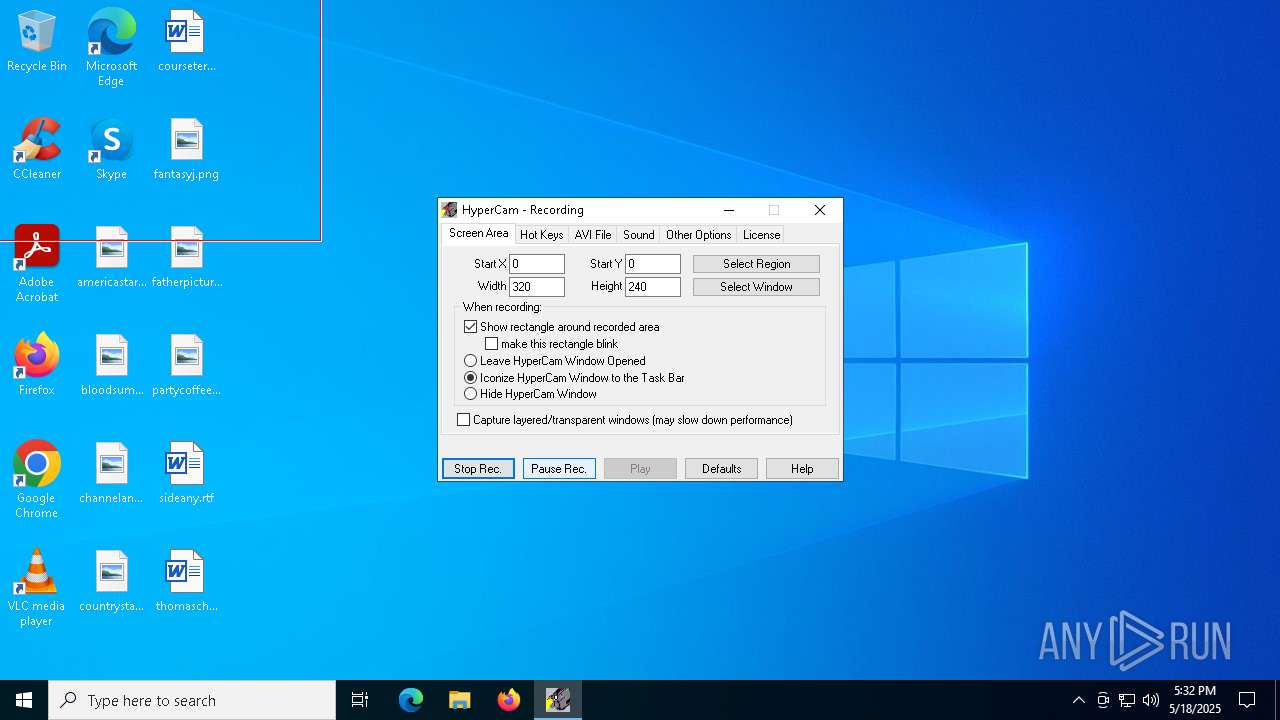
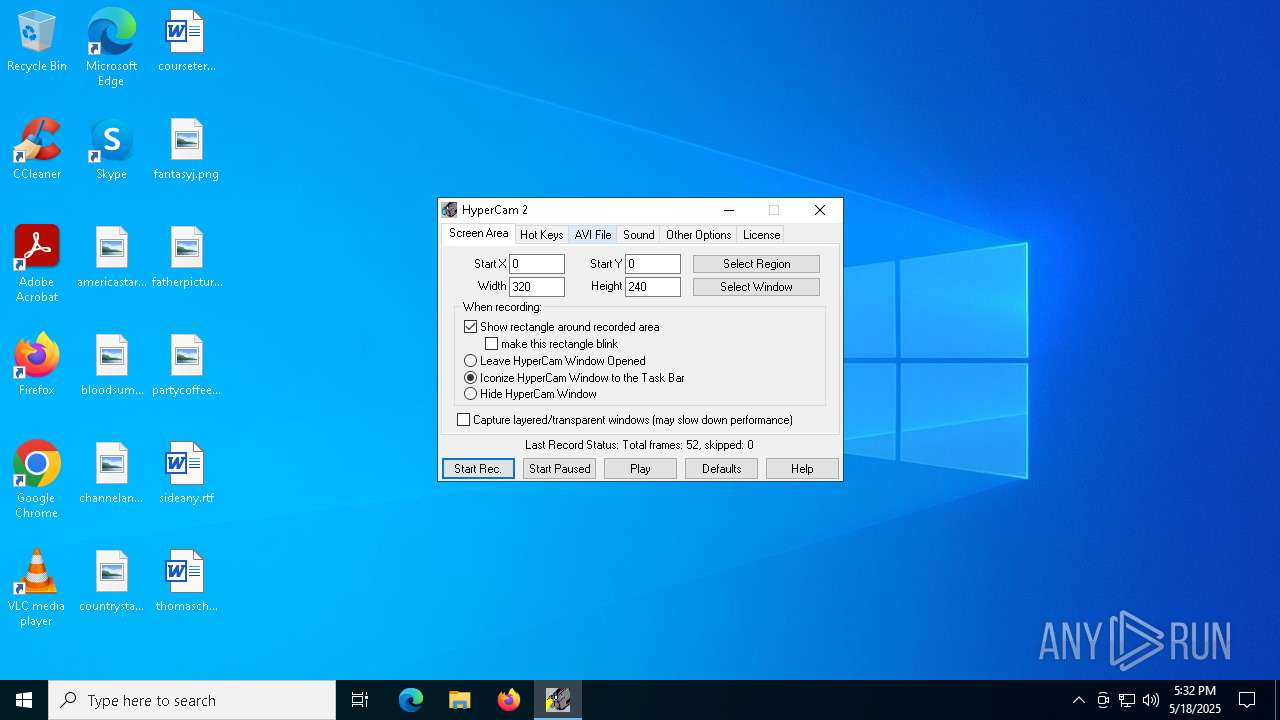
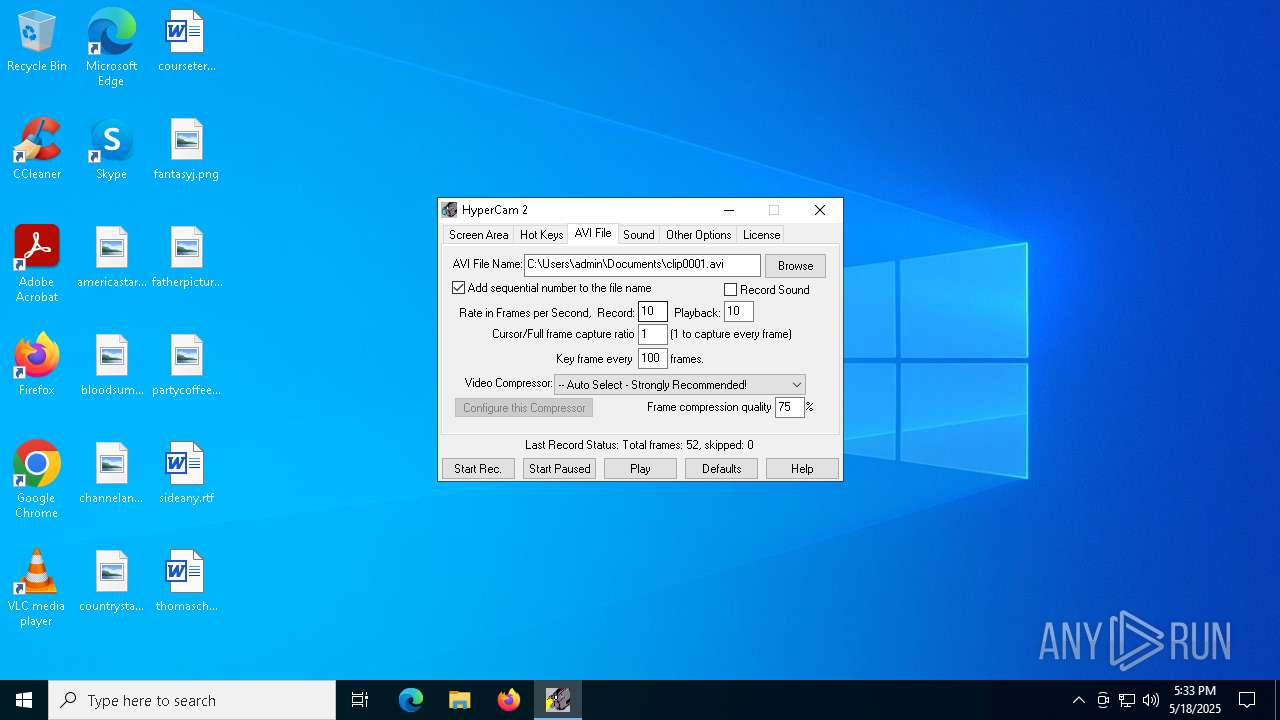
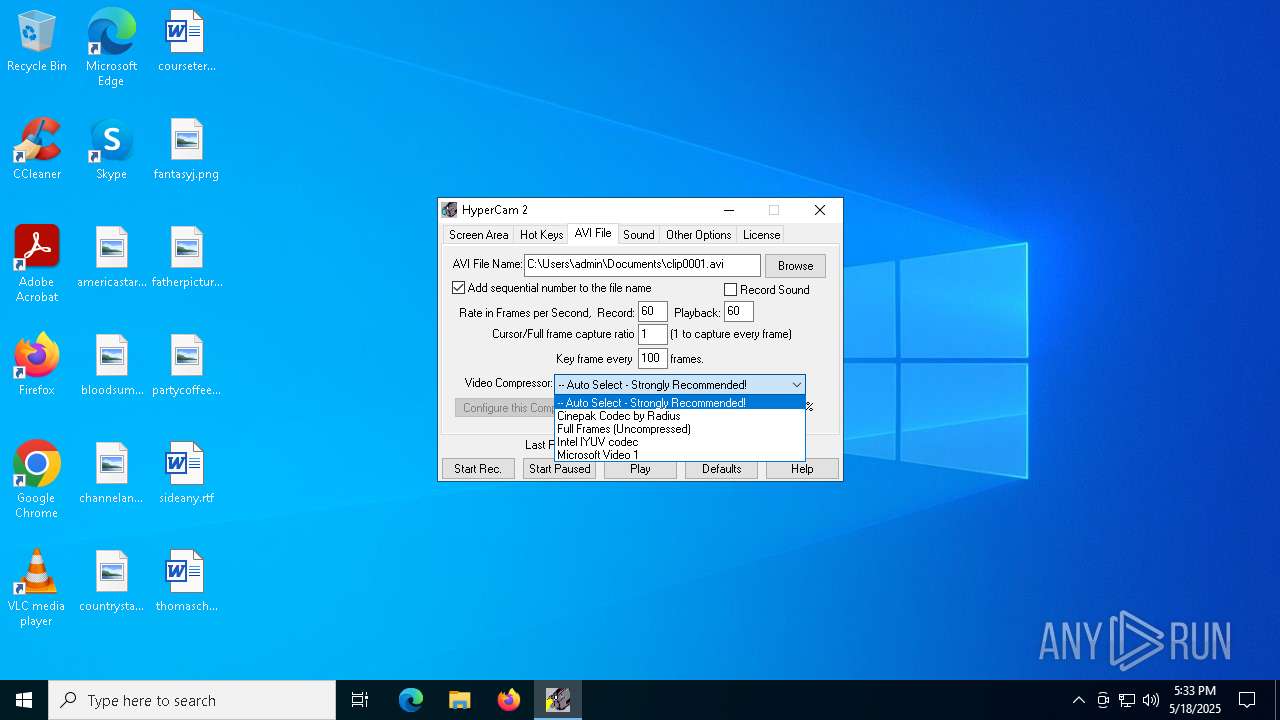
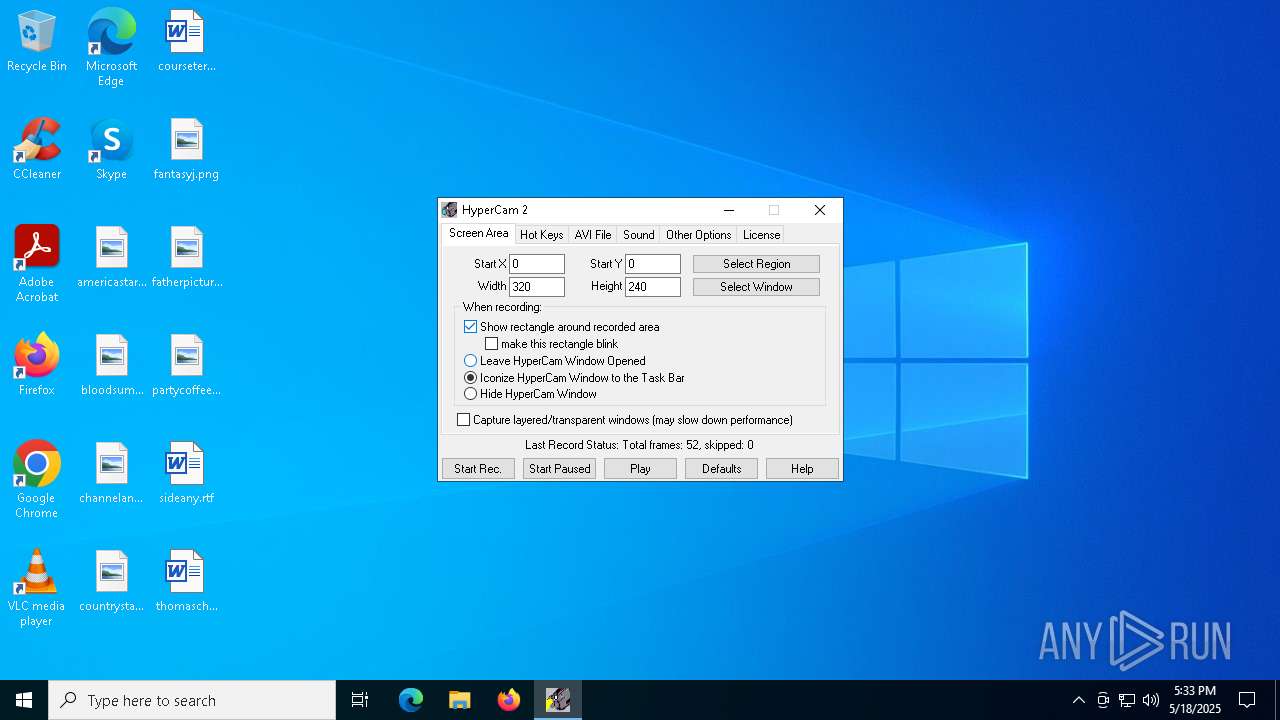
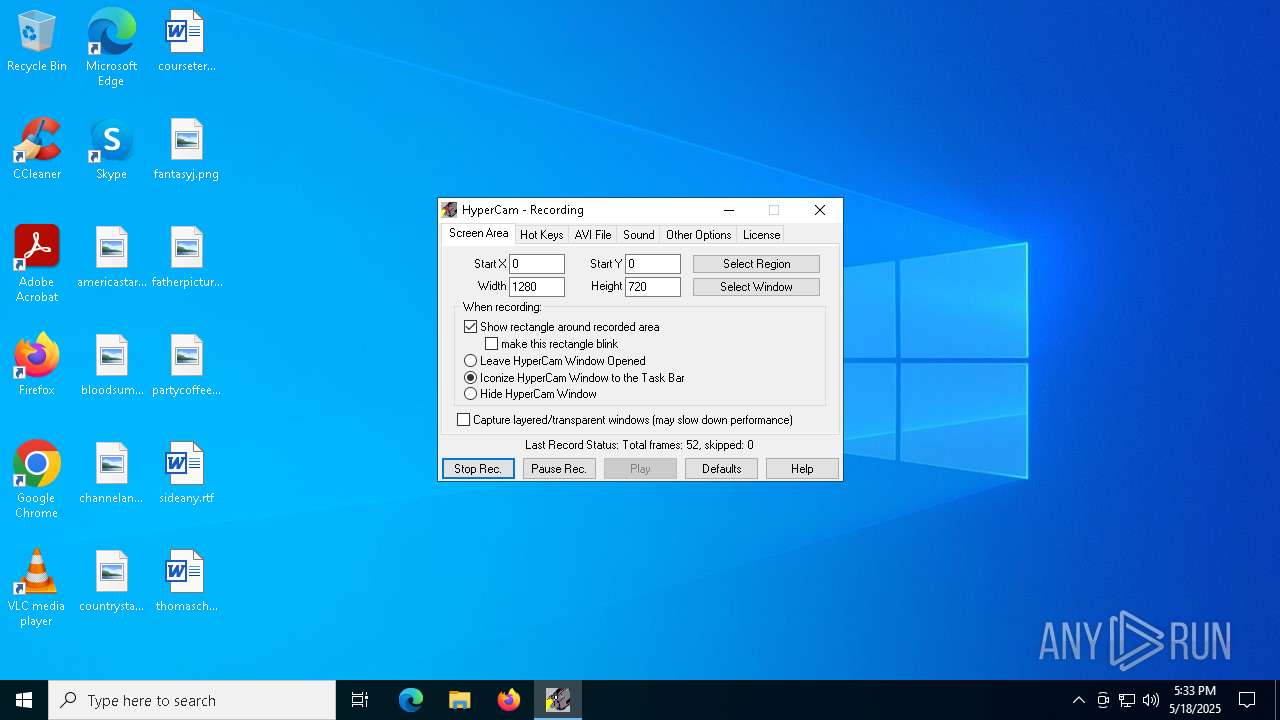
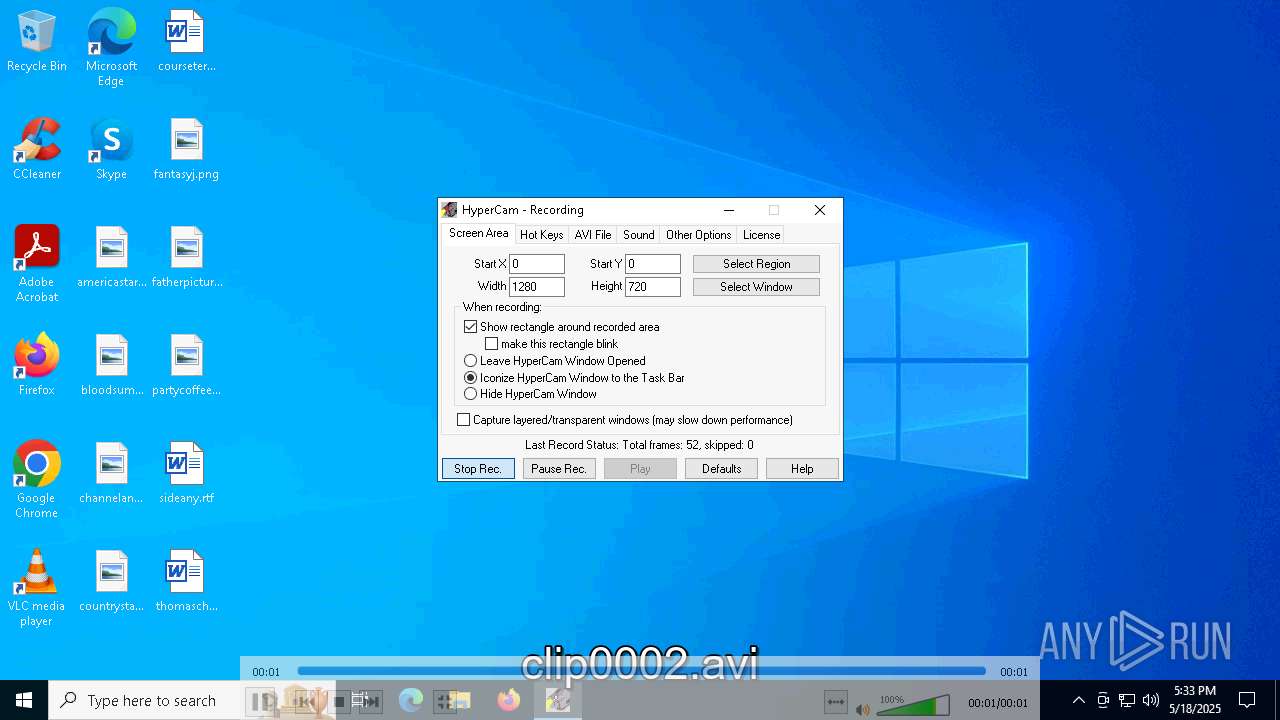
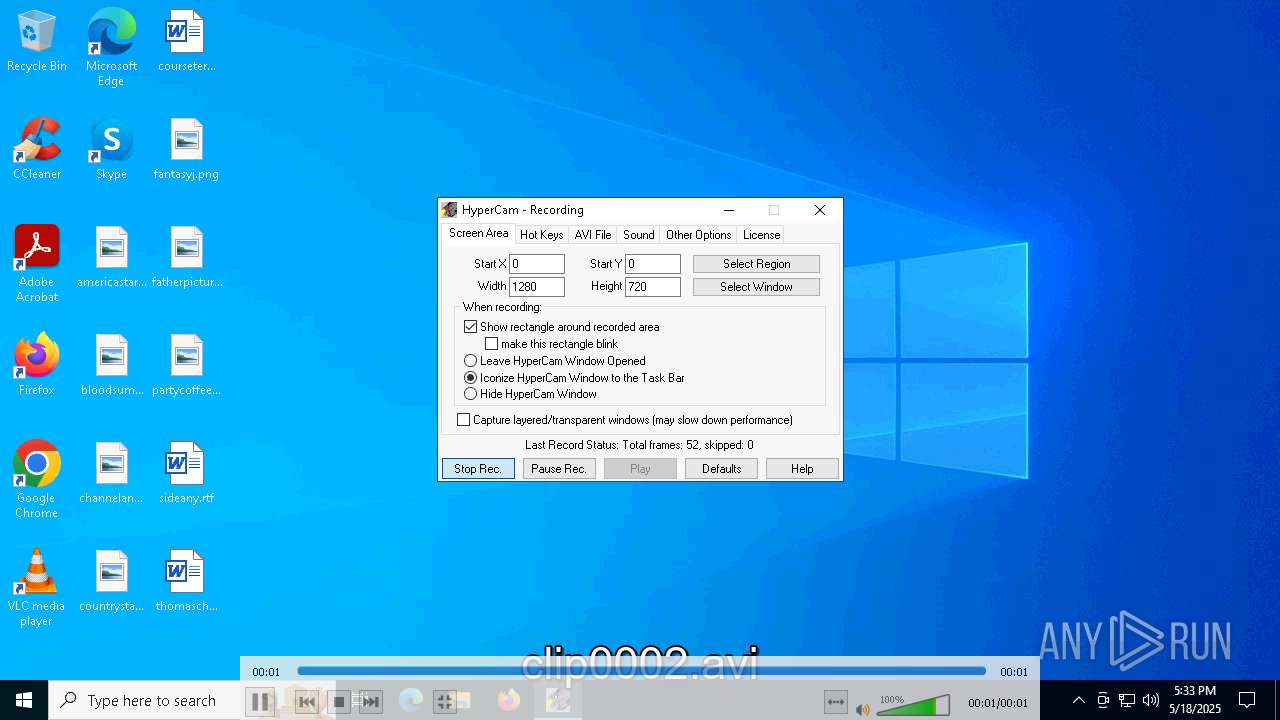
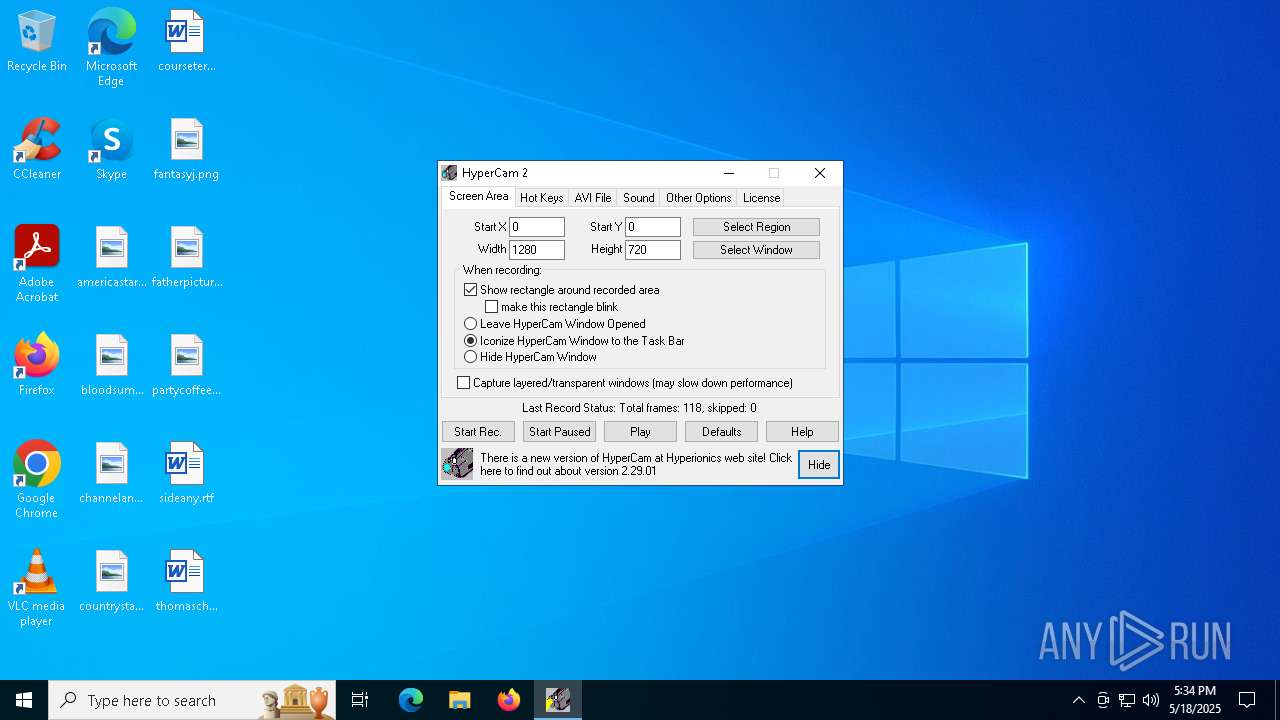
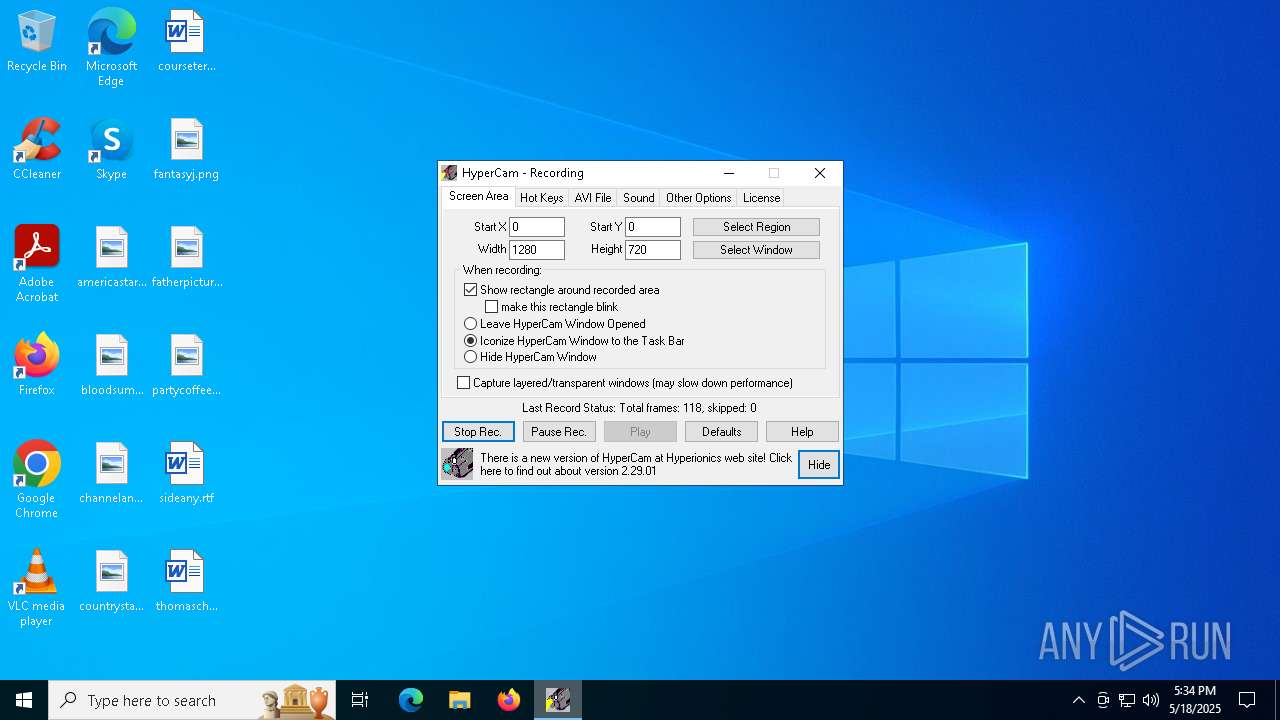
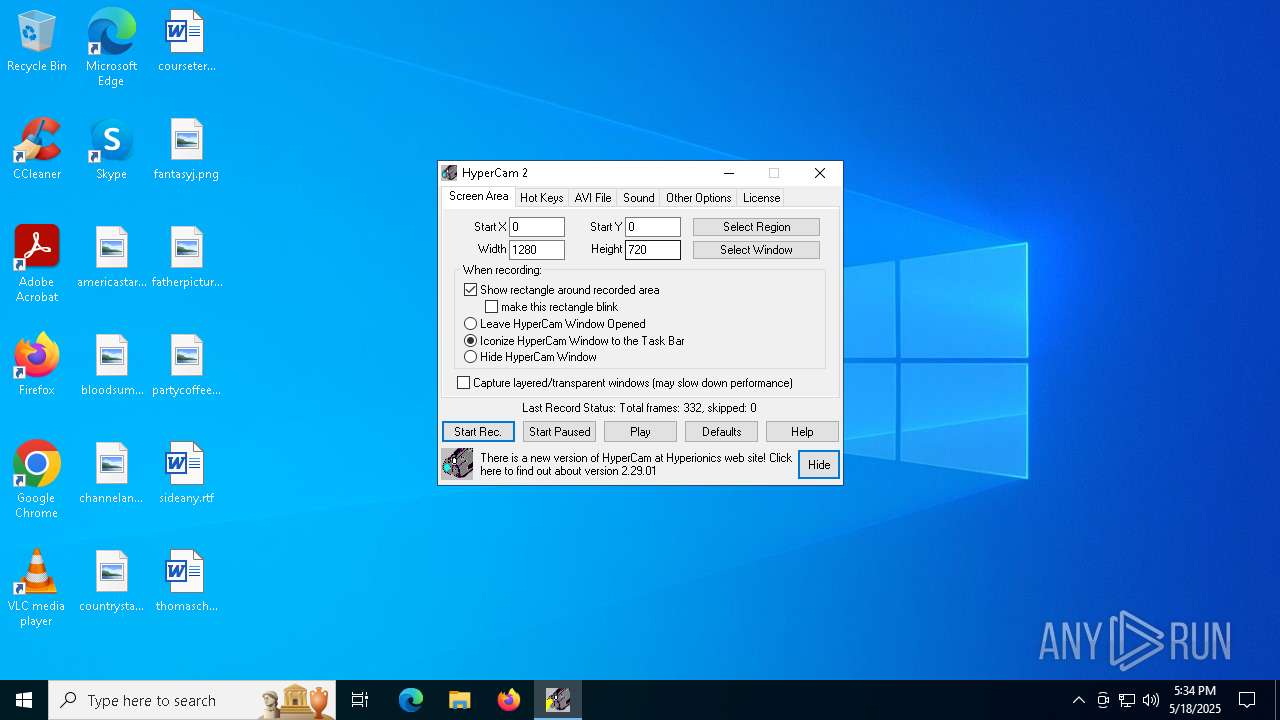
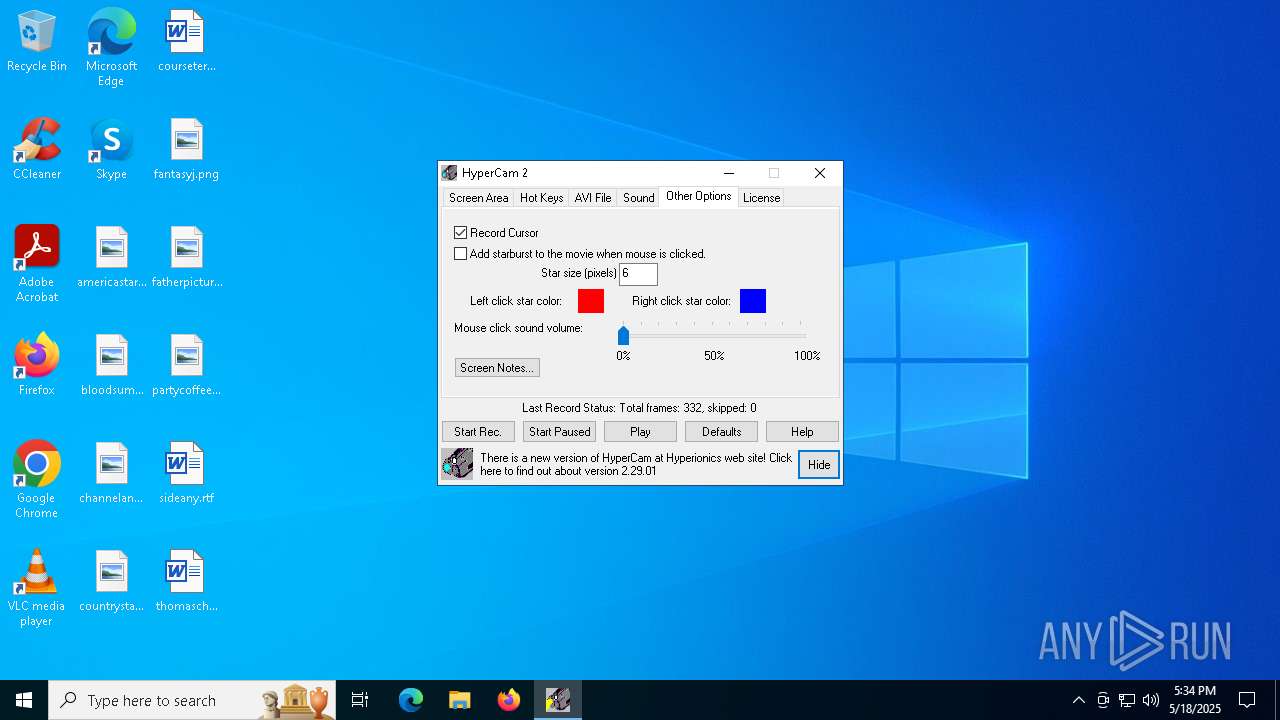
There is functionality for taking screenshot (YARA)
- HyCam2.exe (PID: 7904)
INFO
Checks supported languages
- HC2Setup.exe (PID: 6040)
- HyCam2.exe (PID: 2852)
- HyCam2.exe (PID: 7904)
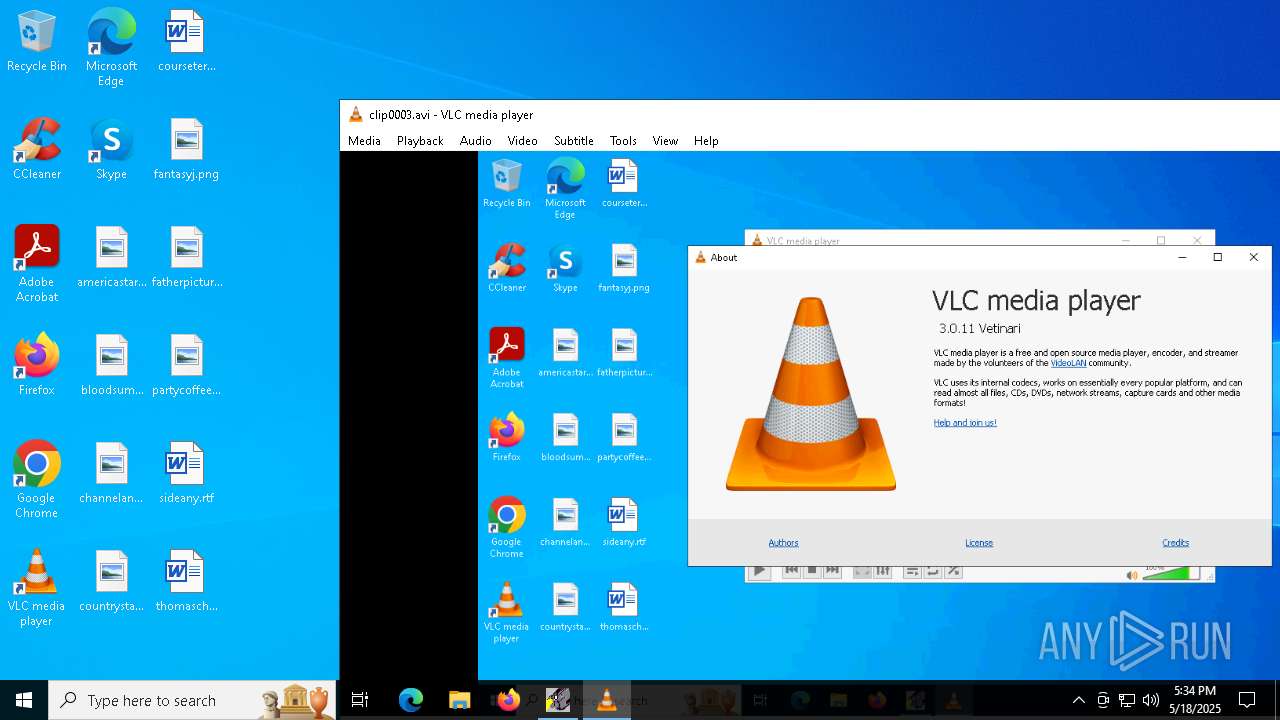
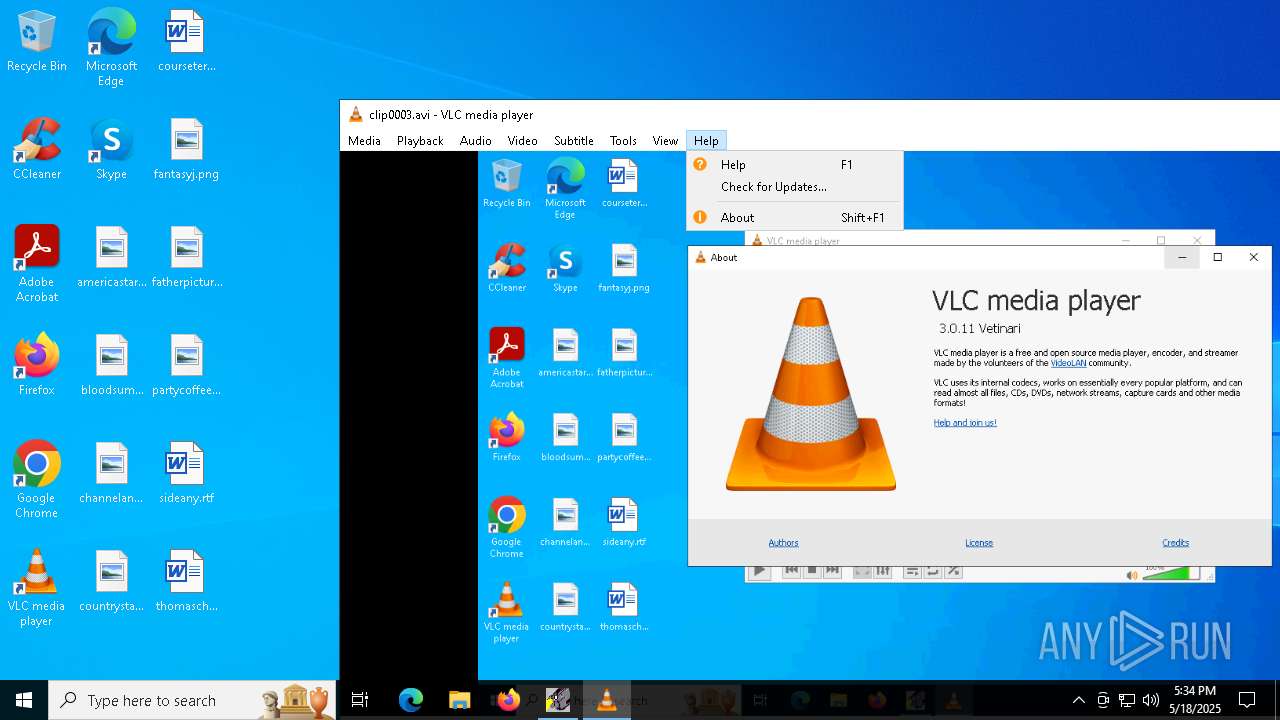
- vlc.exe (PID: 7480)
- vlc.exe (PID: 3020)
Create files in a temporary directory
- HC2Setup.exe (PID: 6040)
Creates files in the program directory
- HyCam2.exe (PID: 2852)
The sample compiled with english language support
- HC2Setup.exe (PID: 6040)
- HyCam2.exe (PID: 2852)
Reads the computer name
- HC2Setup.exe (PID: 6040)
- HyCam2.exe (PID: 2852)
- HyCam2.exe (PID: 7904)
- vlc.exe (PID: 7480)
- vlc.exe (PID: 3020)
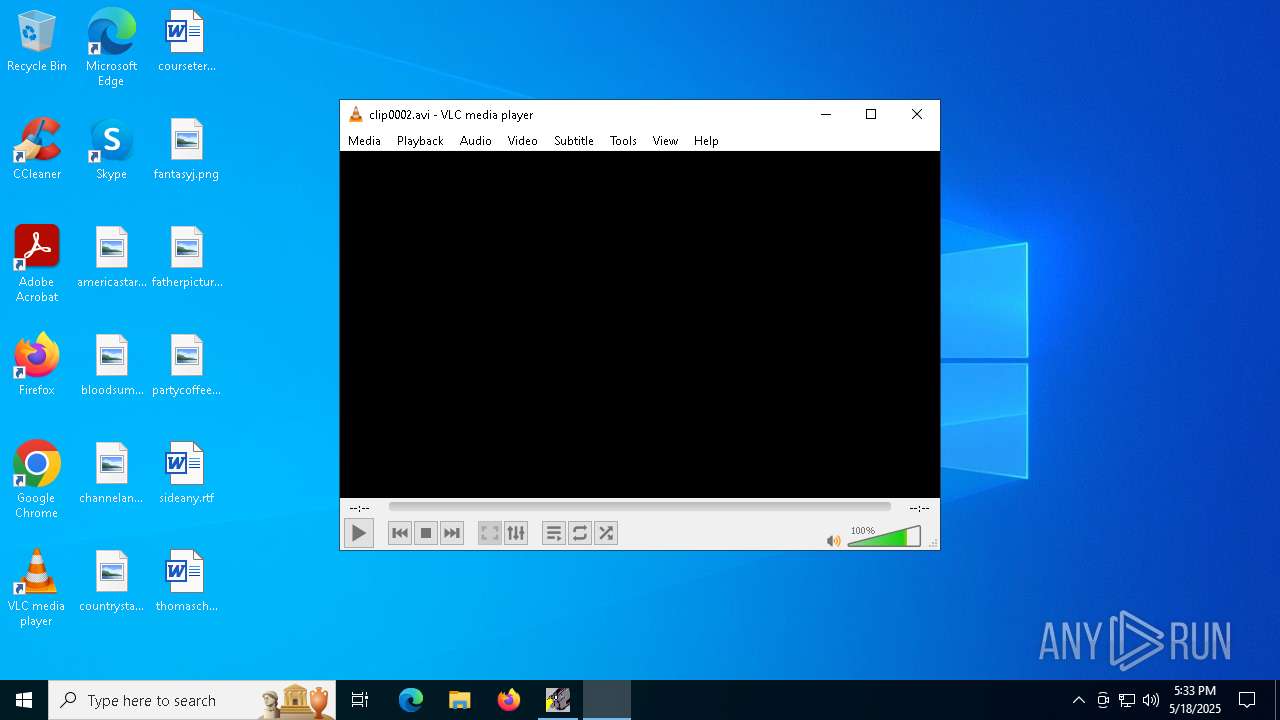
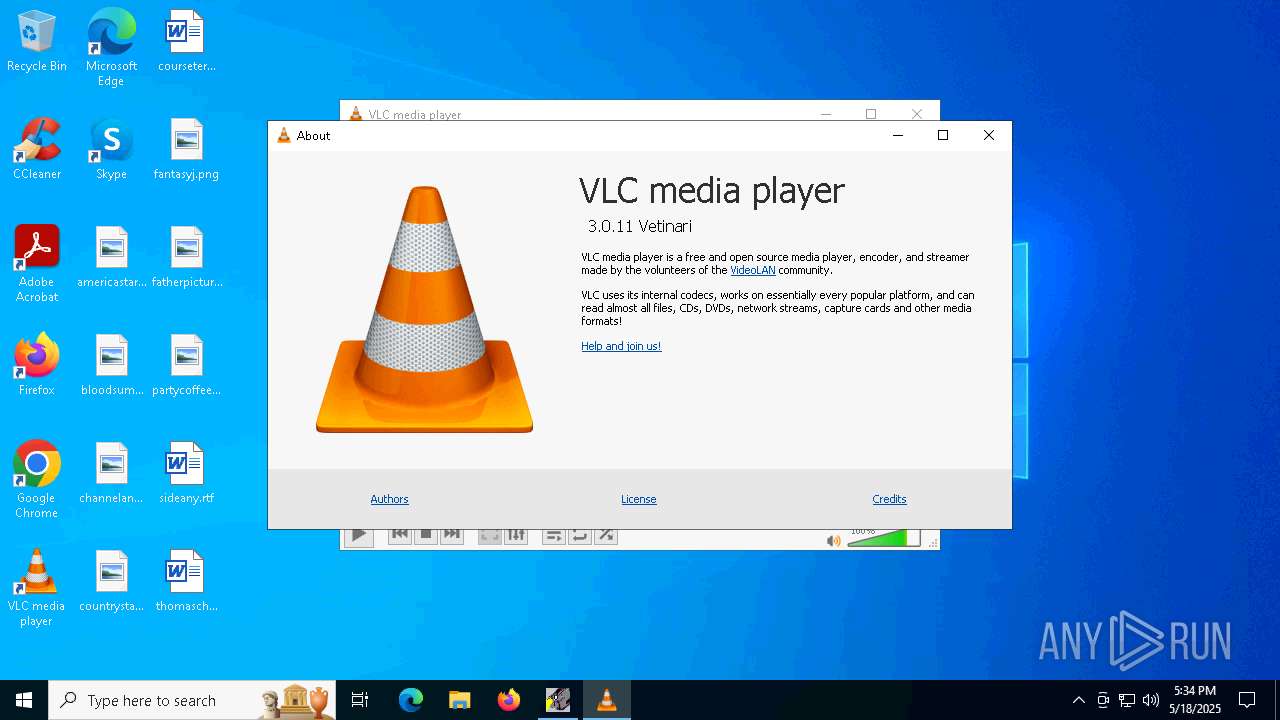
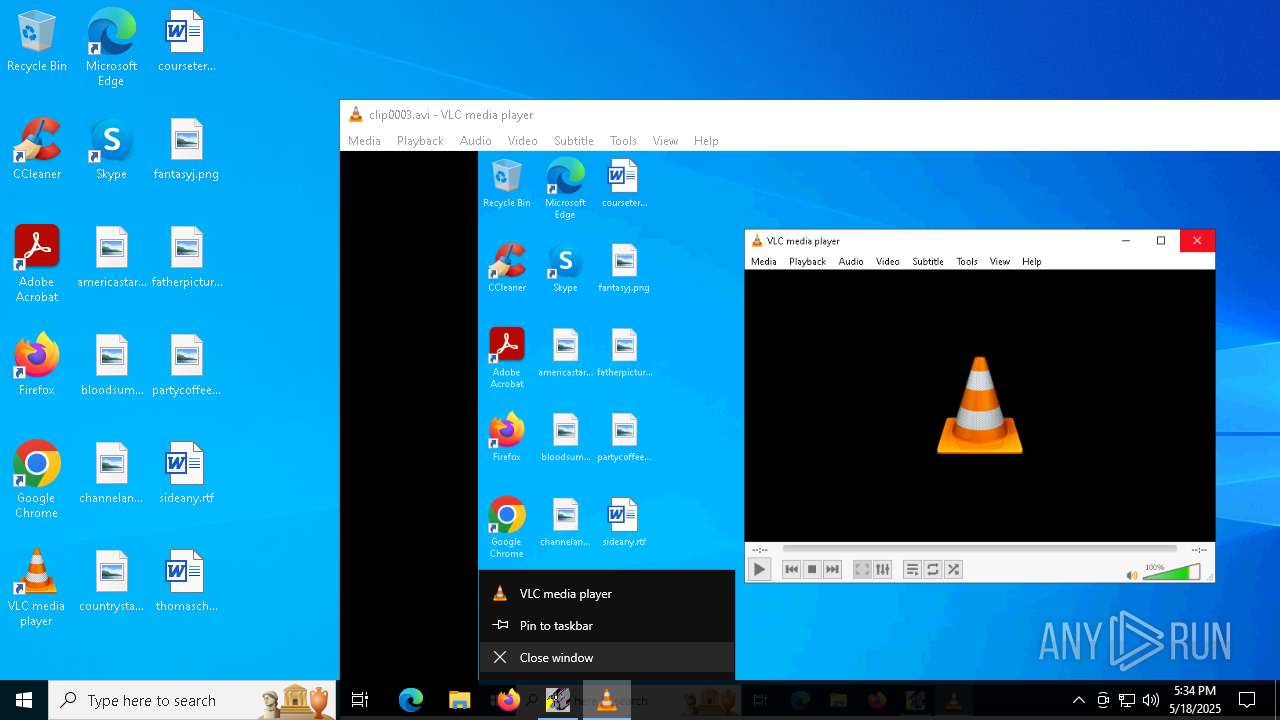
Manual execution by a user
- HyCam2.exe (PID: 7904)
- vlc.exe (PID: 4776)
Creates files or folders in the user directory
- HyCam2.exe (PID: 7904)
- HyCam2.exe (PID: 2852)
Reads the software policy settings
- slui.exe (PID: 7328)
Process checks computer location settings
- HyCam2.exe (PID: 7904)
- HC2Setup.exe (PID: 6040)
Checks proxy server information
- HyCam2.exe (PID: 7904)
Application launched itself
- msedge.exe (PID: 4008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | WinRAR Self Extracting archive (94.8) |
|---|---|---|
| .scr | | | Windows screen saver (2.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.2) |
| .exe | | | Win32 Executable (generic) (0.8) |
| .exe | | | Generic Win/DOS Executable (0.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2006:09:13 18:20:14+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 5 |
| CodeSize: | 77824 |
| InitializedDataSize: | 28672 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
178
Monitored processes
41
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 812 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5936 --field-trial-handle=2348,i,7433333761704631963,2520386758396676325,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5932 --field-trial-handle=2348,i,7433333761704631963,2520386758396676325,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=5240 --field-trial-handle=2348,i,7433333761704631963,2520386758396676325,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1116 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6232 --field-trial-handle=2348,i,7433333761704631963,2520386758396676325,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1128 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6068 --field-trial-handle=2348,i,7433333761704631963,2520386758396676325,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1512 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5512 --field-trial-handle=2348,i,7433333761704631963,2520386758396676325,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2244 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2344 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6068 --field-trial-handle=2348,i,7433333761704631963,2520386758396676325,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2416 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2508 --field-trial-handle=2348,i,7433333761704631963,2520386758396676325,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
12 611
Read events
12 355
Write events
256
Delete events
0
Modification events
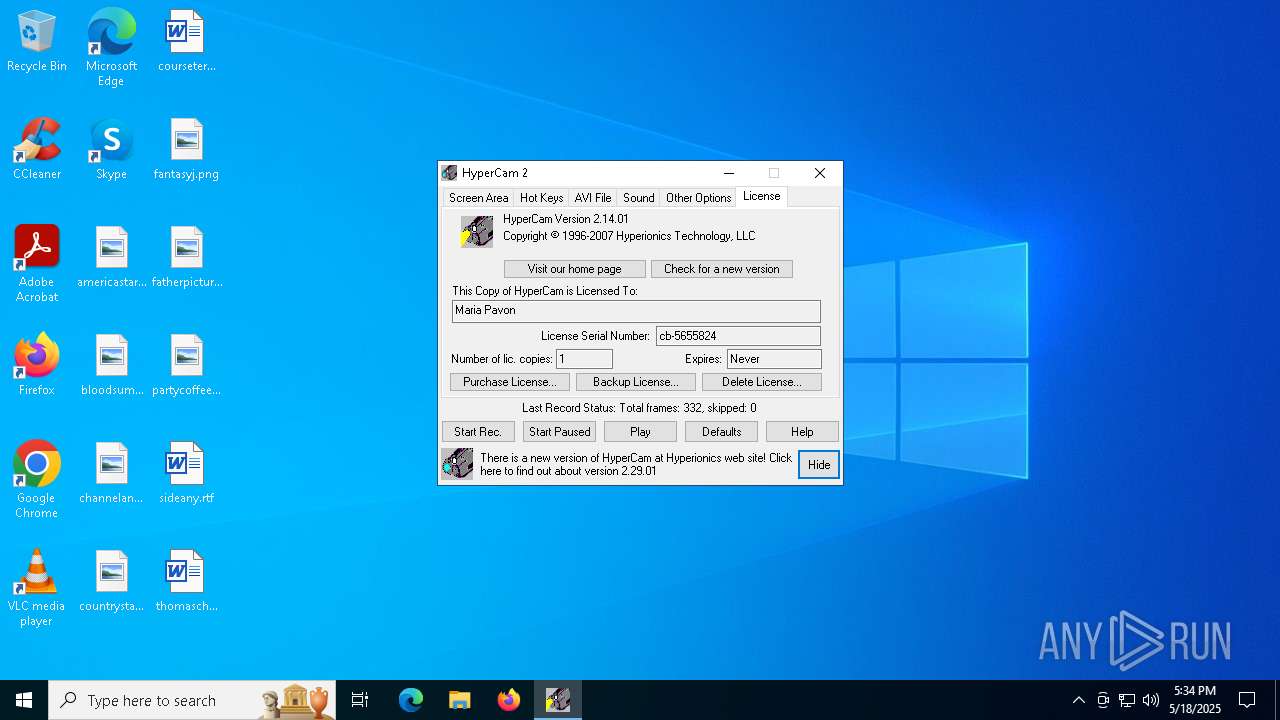
| (PID) Process: | (2852) HyCam2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\HyperCam 2 |
| Operation: | write | Name: | DisplayName |
Value: HyperCam 2 | |||
| (PID) Process: | (2852) HyCam2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\HyperCam 2 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files (x86)\HyCam2\UnHyCam2.exe" | |||
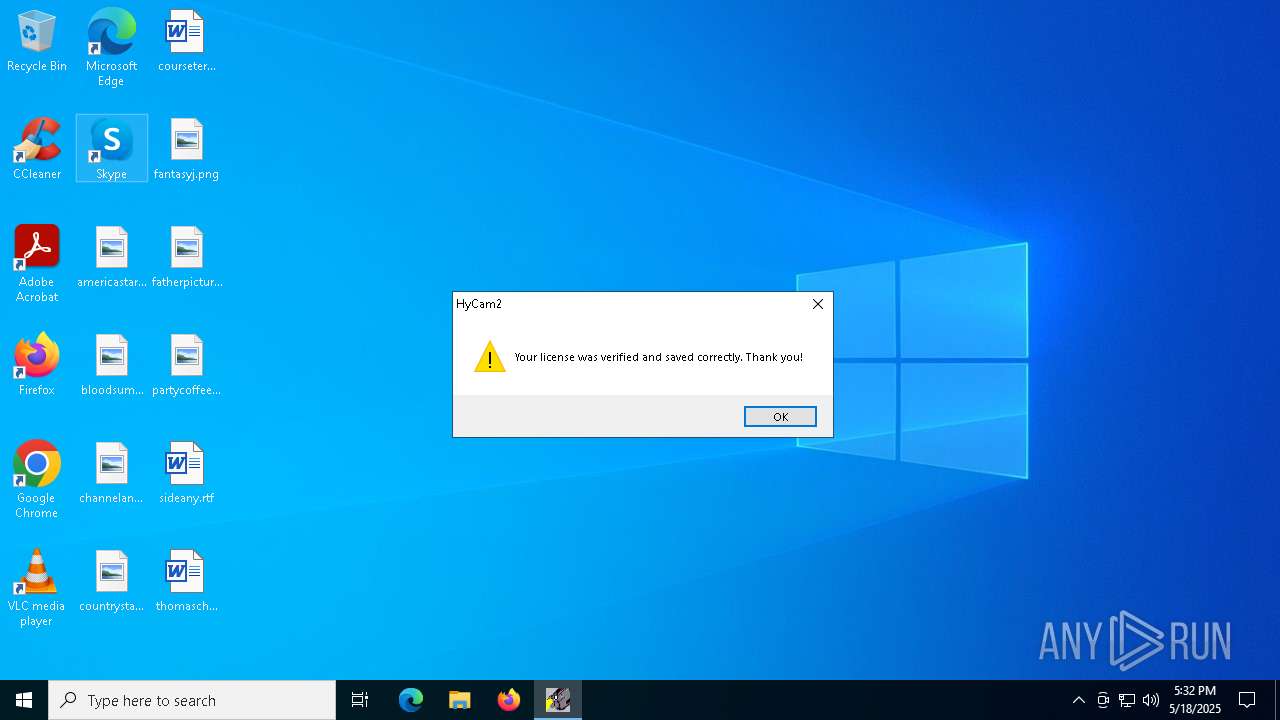
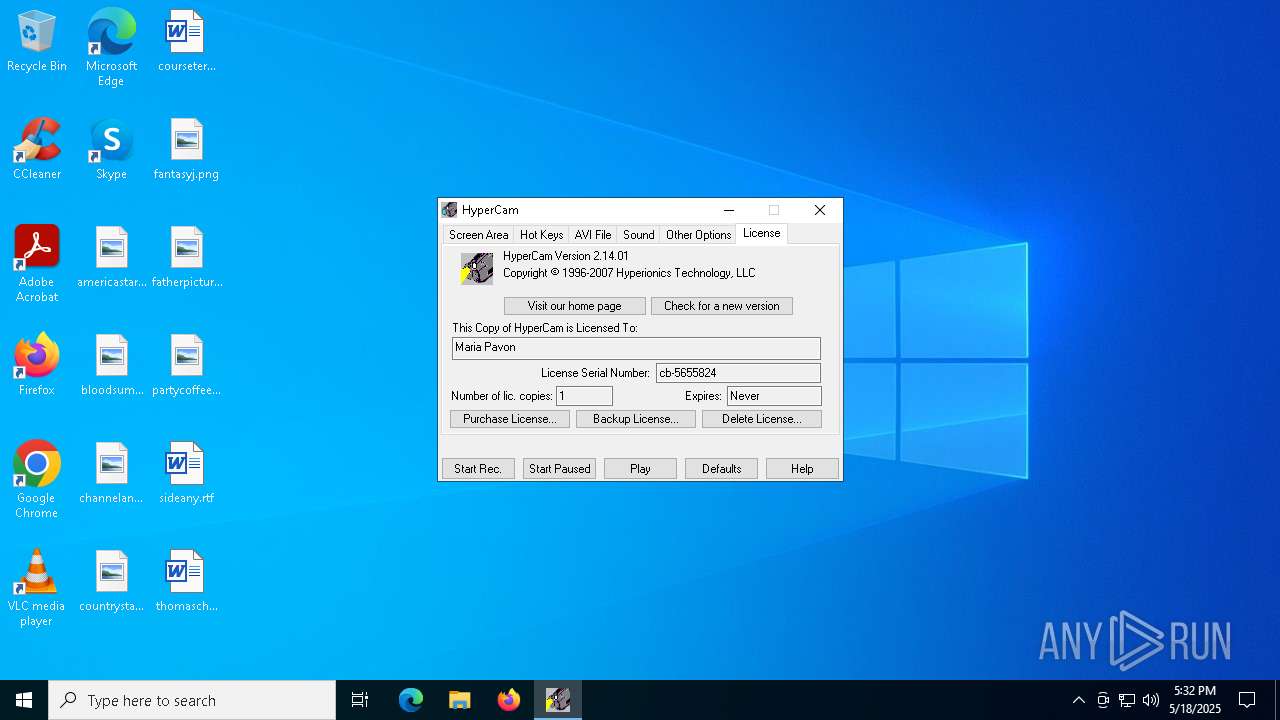
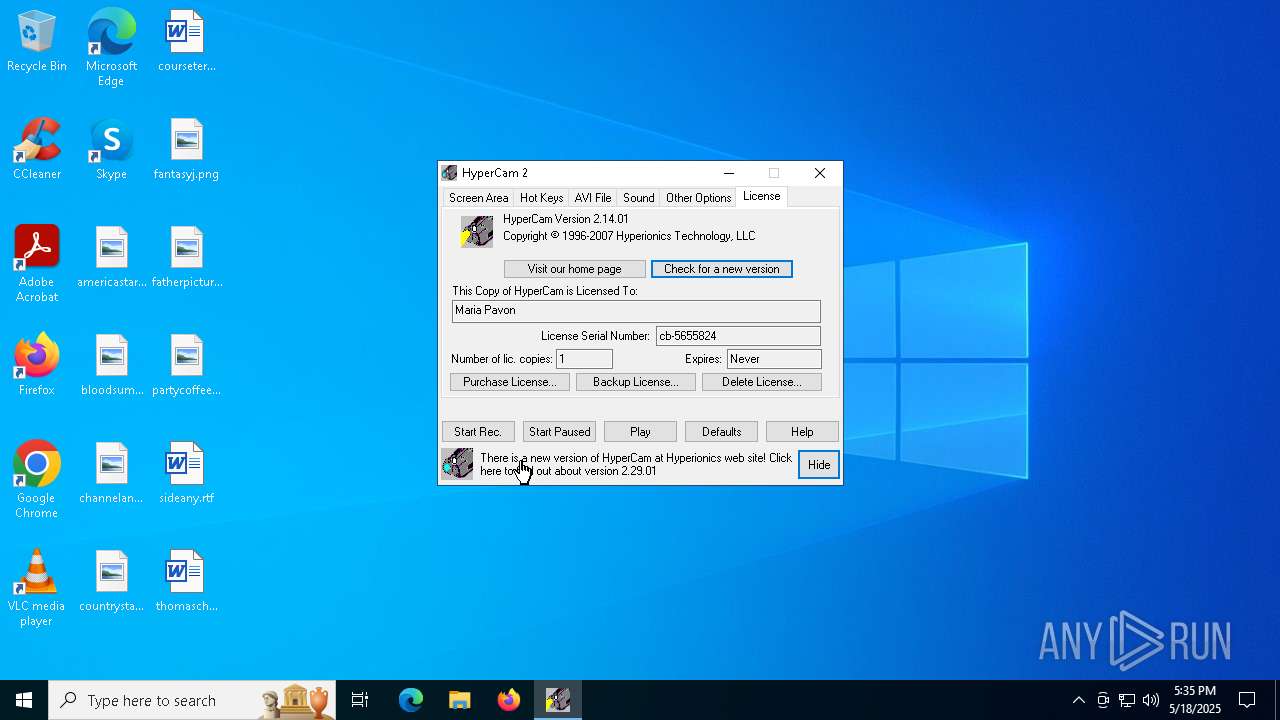
| (PID) Process: | (7904) HyCam2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Hyperionics\HyperCam 2 |
| Operation: | write | Name: | Key |
Value: 50443A7B487970657243616D20327D0A4C4F3A7B4D61726961205061766F6E7D0A534E3A7B63622D353635353832347D0A4E433A7B317D0A4C443A7B323030392E30342E32357D0A4B493A7B485048532D307D0A46533A7B317D0A4B443A7B3130300A303438203039382030303220303031203030332031323820303230203038380A303230203231382032313720313432203130312032333720313630203136370A313338203135362030343620303935203135332030393720323036203132340A313135203030312031323920303438203030392030303620303035203034330A303134203030332030303220303236203030352030303020303438203031310A303036203030372030343220313334203037322032303620303536203030340A303031203030352030303020303034203034372030343820303435203030320A303230203037332031333920323139203134342031383820303930203233360A313933203235312030343420313033203232362030323720313233203139380A313434203034332030333420323333203030392030303220303231203030300A313531203035312032313020303030203034382032323620323231203032330A323433203032392030373220303339203234342031373820323335203038390A3231392030393620313733203030340A454B3A7D | |||
| (PID) Process: | (7904) HyCam2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Hyperionics\HyperCam 2 |
| Operation: | write | Name: | Key |
Value: 50443A7B487970657243616D20327D0A4C4F3A7B4D61726961205061766F6E7D0A534E3A7B63622D353635353832347D0A4E433A7B317D0A4C443A7B323030392E30342E32357D0A4B493A7B485048532D307D0A46533A7B317D0A4B443A7B3130300A303438203039382030303220303031203030332031323820303230203038380A303230203231382032313720313432203130312032333720313630203136370A313338203135362030343620303935203135332030393720323036203132340A313135203030312031323920303438203030392030303620303035203034330A303134203030332030303220303236203030352030303020303438203031310A303036203030372030343220313334203037322032303620303536203030340A303031203030352030303020303034203034372030343820303435203030320A303230203037332031333920323139203134342031383820303930203233360A313933203235312030343420313033203232362030323720313233203139380A313434203034332030333420323333203030392030303220303231203030300A313531203035312032313020303030203034382032323620323231203032330A323433203032392030373220303339203234342031373820323335203038390A3231392030393620313733203030340A454B3A7D | |||
| (PID) Process: | (7904) HyCam2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.avi\OpenWithProgids |
| Operation: | write | Name: | VLC.avi |
Value: | |||
| (PID) Process: | (7904) HyCam2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7904) HyCam2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
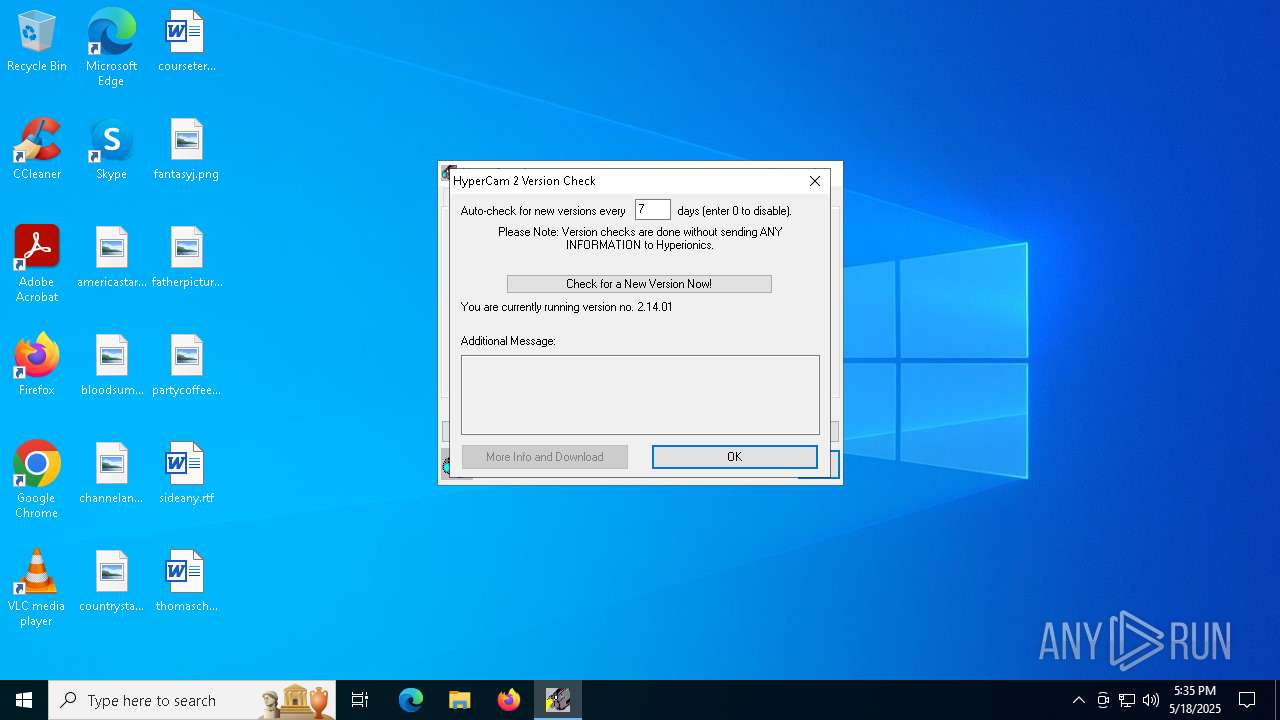
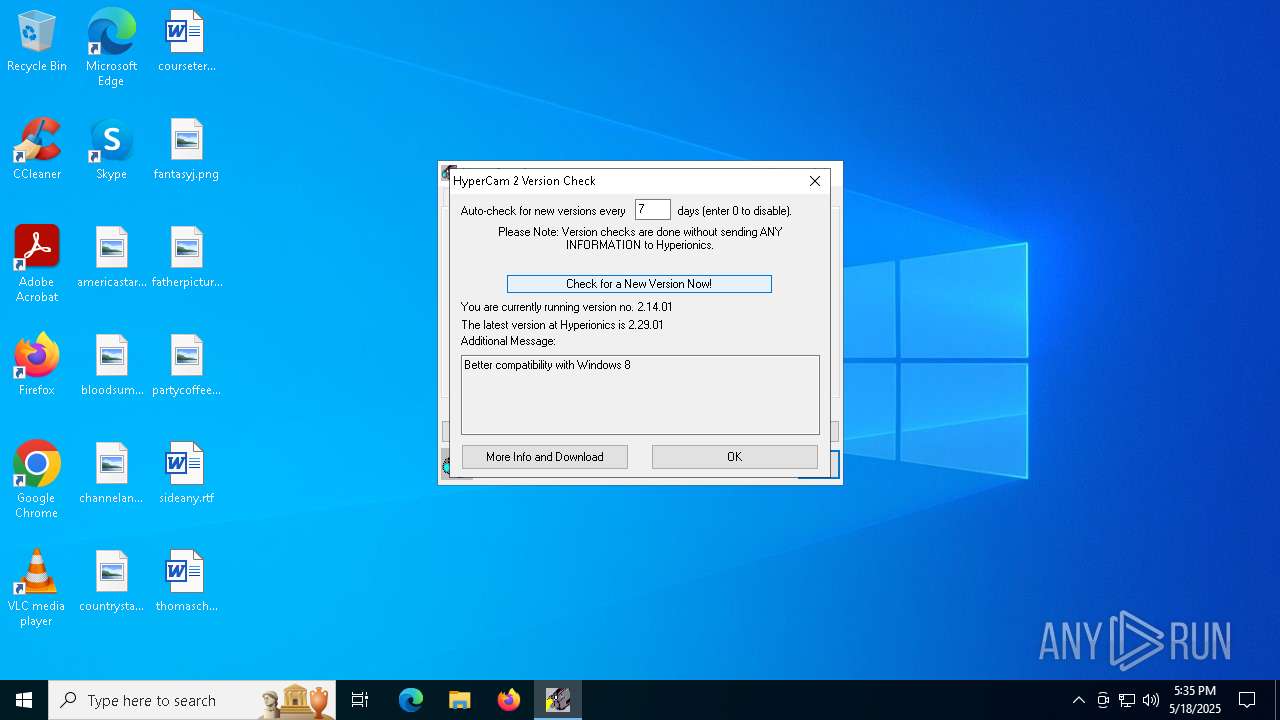
| (PID) Process: | (7904) HyCam2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Hyperionics\HyperCam 2\HyCam2\Vcheck |
| Operation: | write | Name: | lvAsked |
Value: 0 | |||
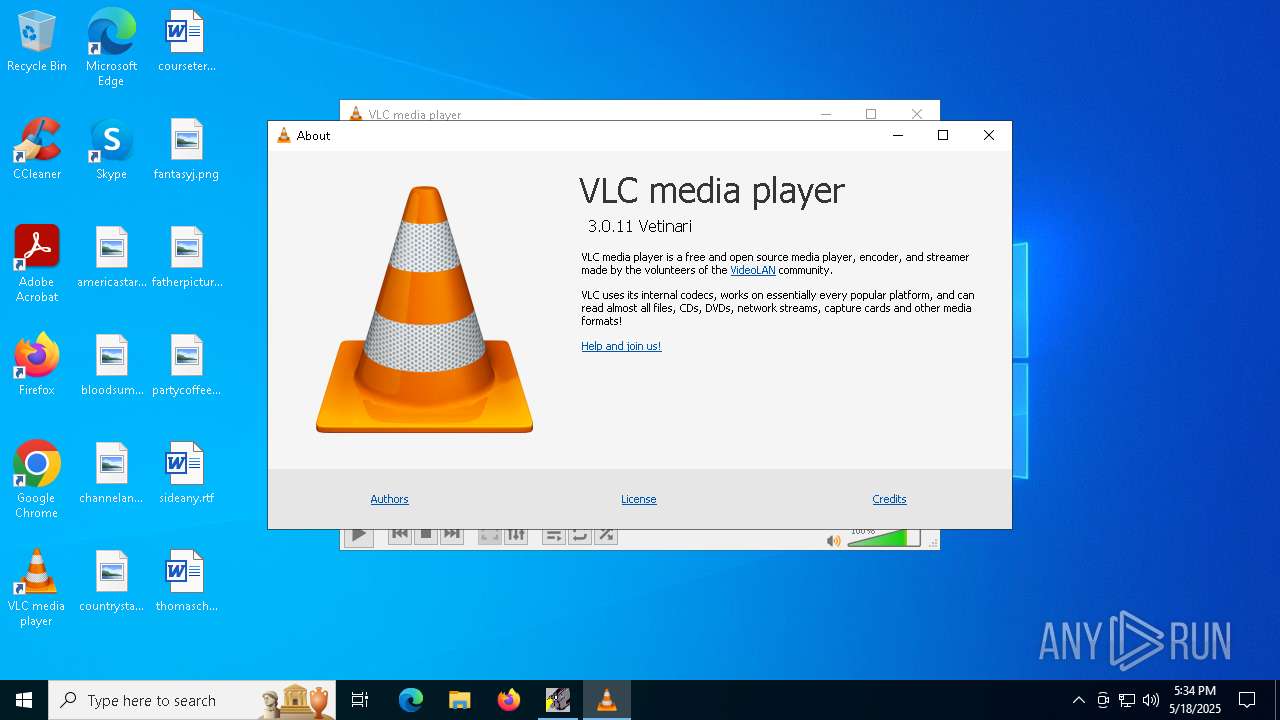
| (PID) Process: | (7904) HyCam2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Hyperionics\HyperCam 2\HyCam2\Vcheck |
| Operation: | write | Name: | lvMajor |
Value: 2 | |||
| (PID) Process: | (7904) HyCam2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Hyperionics\HyperCam 2\HyCam2\Vcheck |
| Operation: | write | Name: | lvMinor |
Value: 29 | |||
Executable files
29
Suspicious files
89
Text files
46
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6040 | HC2Setup.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\8-22050u.wav | binary | |
MD5:BF39380290ED50079B752A2593B9A50D | SHA256:C809DB4B1D49BB7F70A1E91FA8769563BD1E2BEFF8EC979B881713CD55FF99E9 | |||
| 6040 | HC2Setup.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\8-11025u.wav | binary | |
MD5:C928167AE840C4D092D2D11157458B72 | SHA256:C1D1F055679140D002EEADCD16FD2D72FA6BDC03E0649520E1CF4EEEA6182EF7 | |||
| 6040 | HC2Setup.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\8-44100u.wav | binary | |
MD5:FA7805635EFE3D2B2F1891274413731F | SHA256:9CBB2AD958F1CF1D8EB111CF8813C18596473679220B393C6689F745CD9FDEB3 | |||
| 6040 | HC2Setup.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\16-11025d.wav | binary | |
MD5:C61B97FDEA6DE3AC4EC0DCAB8EDA621C | SHA256:15F65320D89520A615CFDBF952742B3FB9E2466F84794A18433AFD743C3C8709 | |||
| 6040 | HC2Setup.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\8-8000d.wav | binary | |
MD5:1912519EA64D50843AE9084D37E8A0C1 | SHA256:5F8D2BDA27A1036902C82778FF4C947AC57D63D558C1D6F0AA4B168489774538 | |||
| 6040 | HC2Setup.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\16-22050d.wav | binary | |
MD5:E00C8AE722FD731A639F34571375ADB1 | SHA256:60C7BC95E033888F55022B12C9D9BAD16FC458B9E499515B2223FDF2D4F8E741 | |||
| 6040 | HC2Setup.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\16-22050u.wav | binary | |
MD5:76F42715F524FB2110CA845520E101D8 | SHA256:3B393414011D7CCF8A1EB588C3FFD627105EB33E9660D5BDC050455B3C7A215A | |||
| 6040 | HC2Setup.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\8-8000u.wav | binary | |
MD5:D6A10FFAB0437CB757CA0DD098B8B3A7 | SHA256:F3B90092A7F0313D5D0B97AD470CE6D68AA4F4780B18D39560A4988520F4C849 | |||
| 6040 | HC2Setup.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\8-44100d.wav | binary | |
MD5:38A775466B8DC0A1F2D7E04F34F72BD9 | SHA256:FF20BEF1BA7566685B22F5F92DD215178A312DB97DA4C6C743585405F5C040ED | |||
| 6040 | HC2Setup.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\16-8000u.wav | binary | |
MD5:0FCE94CFEC32E5D6084184A34DC60501 | SHA256:2A23479428FCD329D4025FB24C112466237B512A233828FA40B215276CCB84ED | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
61
DNS requests
52
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8068 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
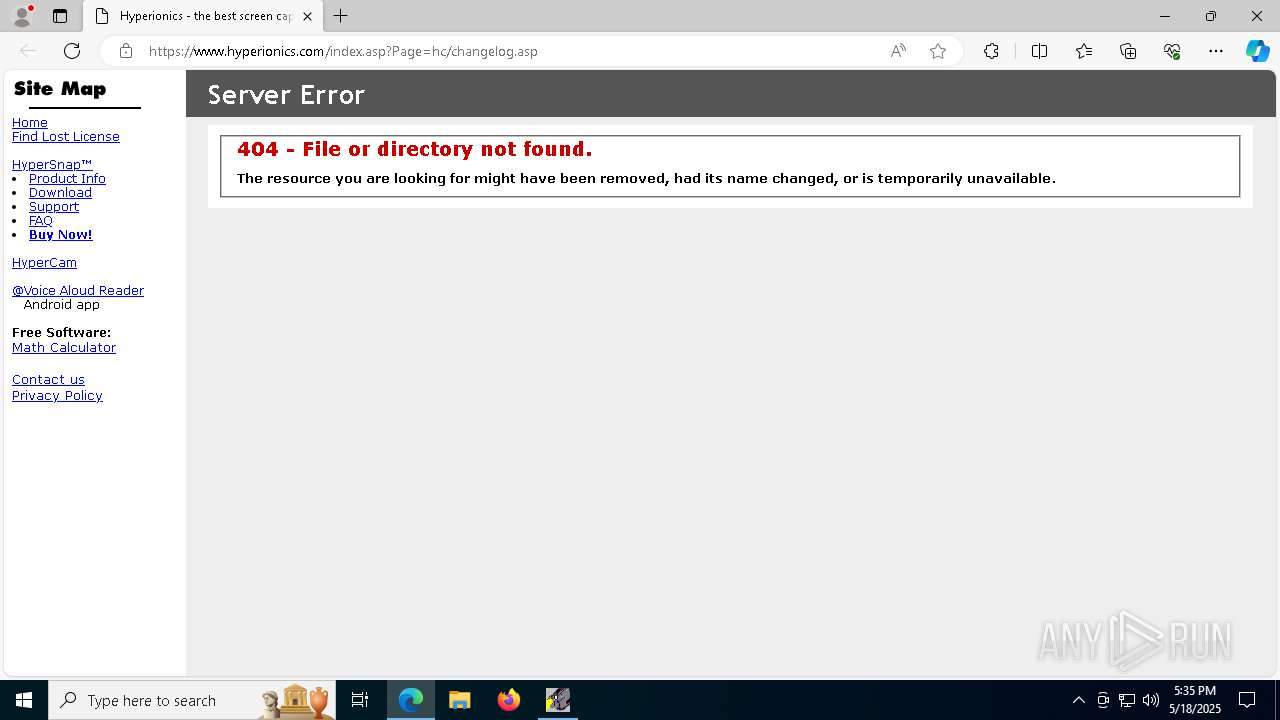
7904 | HyCam2.exe | GET | 200 | 66.135.60.154:80 | http://www.hyperionics.com/vers/hc2.txt | unknown | — | — | malicious |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
8068 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2924 | SearchApp.exe | 204.79.197.222:443 | fp.msedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2924 | SearchApp.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
dual-s-ring.msedge.net |
| whitelisted |
mcr-ring-fallback.msedge.net |
| unknown |