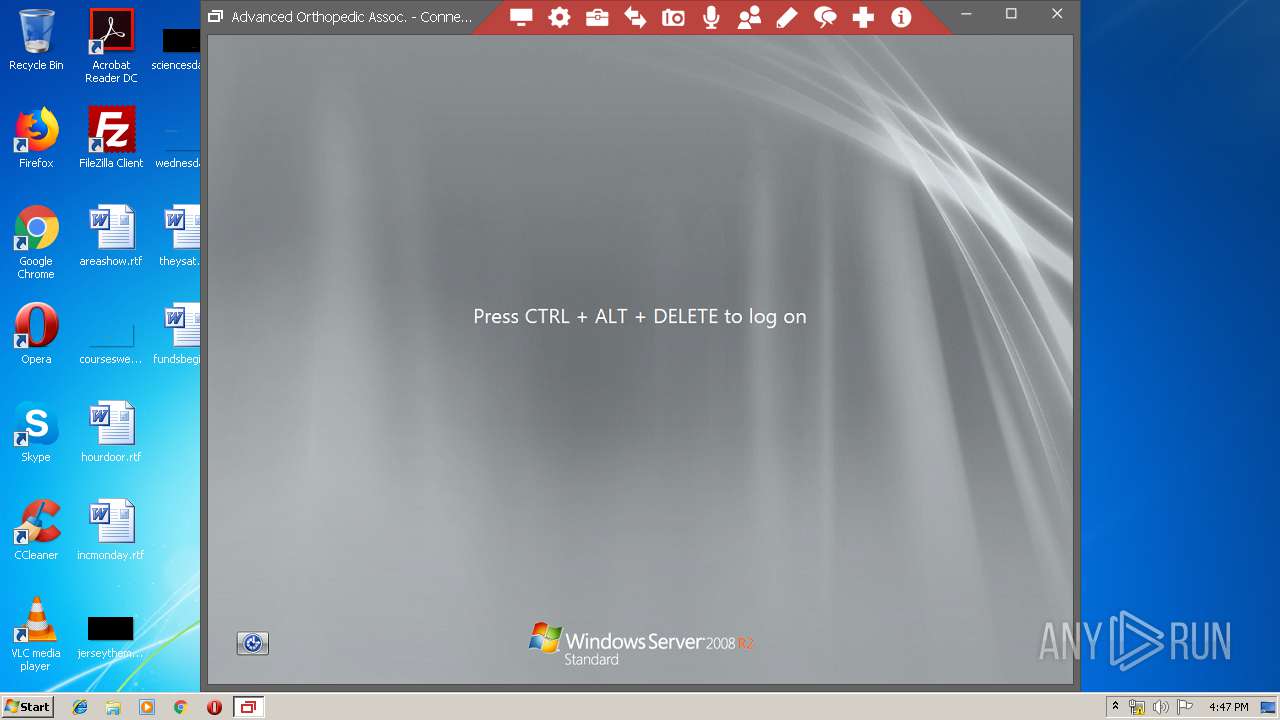
| File name: | ConnectWiseControl.ClientSetup (67).exe |
| Full analysis: | https://app.any.run/tasks/214f124c-aaca-477c-81ed-0805b86eadd0 |
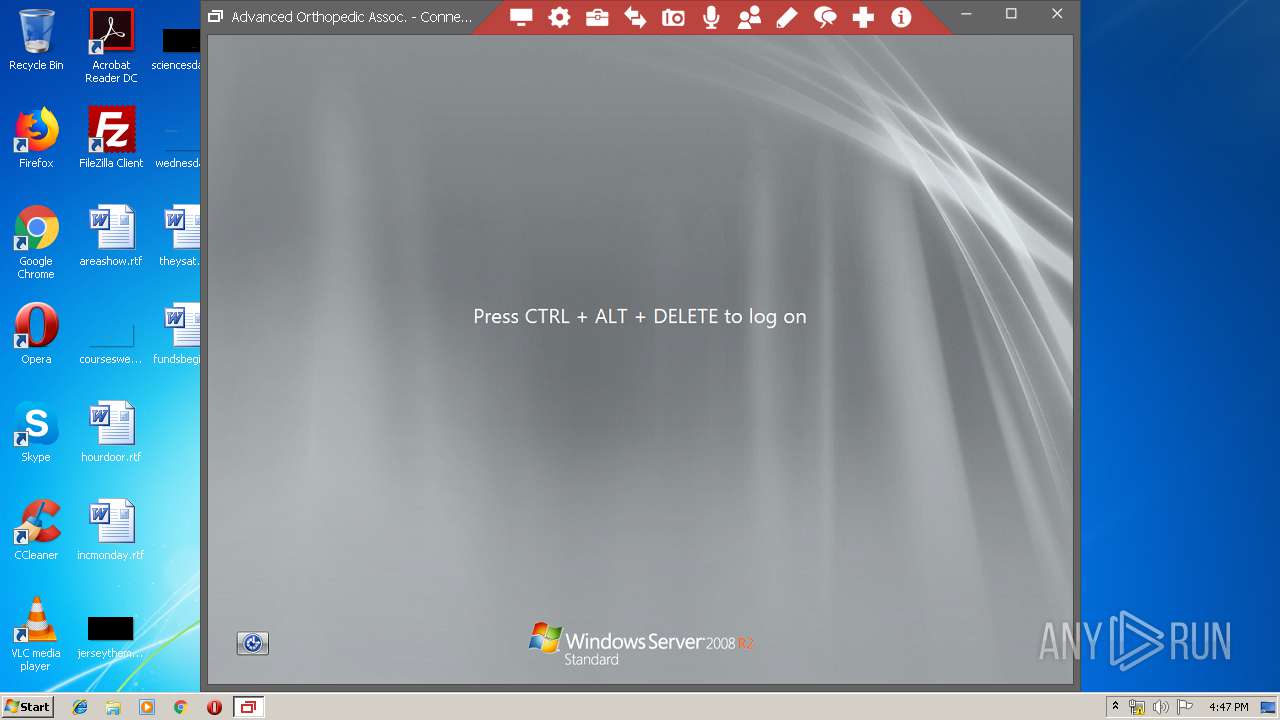
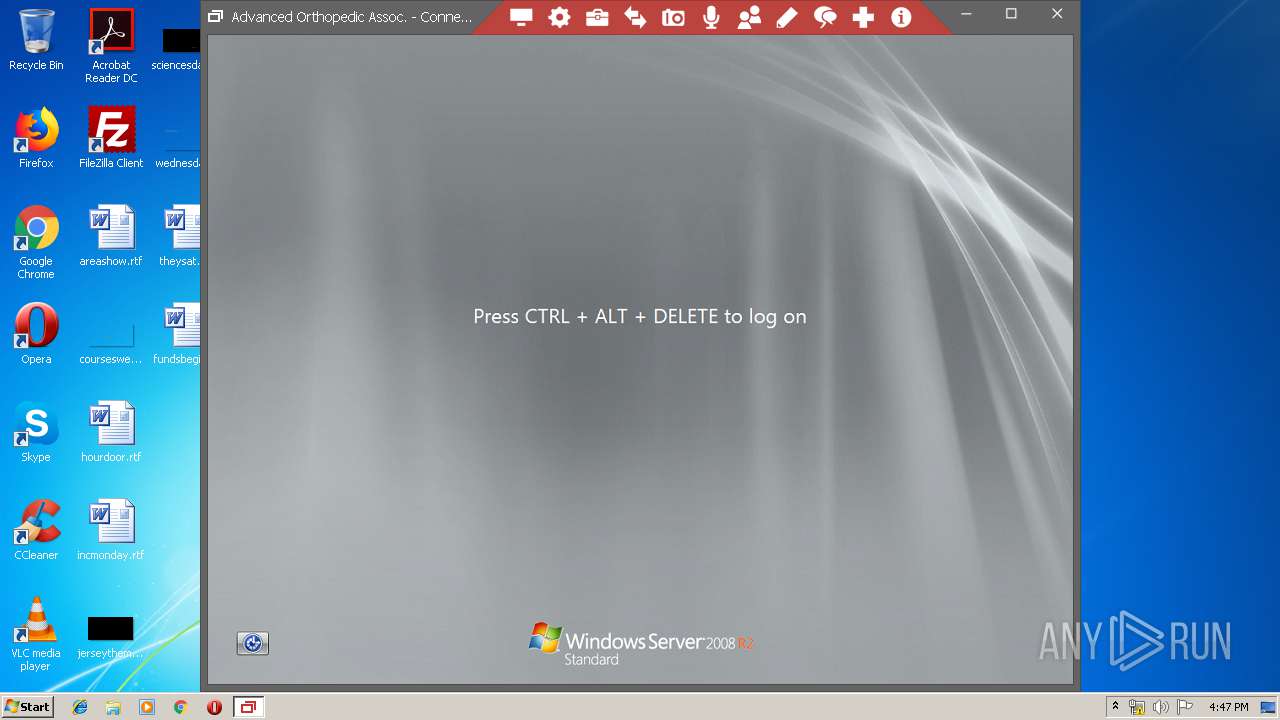
| Verdict: | Malicious activity |
| Analysis date: | April 05, 2019, 15:46:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | AC7906810423E0CB3AC96BF2F92A51A0 |
| SHA1: | 0DEC29E666CFF175D2B20703EA78C30C684F9743 |
| SHA256: | 6A0022FDC79647D4E4C1DE2A483DC80B63690290F6D074F944E98AC45C556E95 |
| SSDEEP: | 49152:y4N0MT0+TL3Z0Mi963PSuAIiiooByhajGDQCmfMPOH1IV1mpExvp+KIlGueufwpg:y42z16oHuB8awwBI/m2yGQocR |
MALICIOUS
Loads dropped or rewritten executable
- rundll32.exe (PID: 2360)
- ScreenConnect.WindowsClient.exe (PID: 3376)
- ScreenConnect.WindowsClient.exe (PID: 1516)
Application was dropped or rewritten from another process
- ScreenConnect.WindowsClient.exe (PID: 1516)
- ScreenConnect.WindowsClient.exe (PID: 3376)
Changes settings of System certificates
- ScreenConnect.WindowsClient.exe (PID: 1516)
SUSPICIOUS
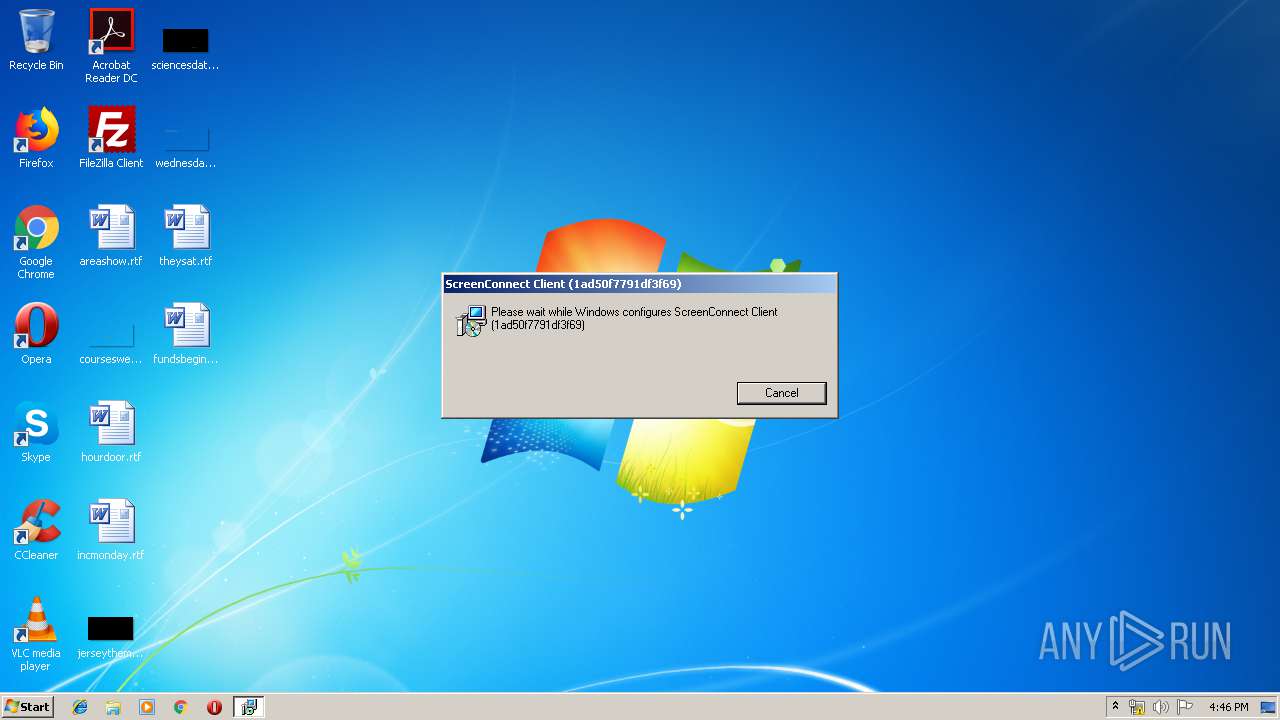
Starts Microsoft Installer
- ConnectWiseControl.ClientSetup (67).exe (PID: 3708)
Executable content was dropped or overwritten
- msiexec.exe (PID: 2364)
- ConnectWiseControl.ClientSetup (67).exe (PID: 3708)
- msiexec.exe (PID: 3976)
- rundll32.exe (PID: 2360)
Uses RUNDLL32.EXE to load library
- MsiExec.exe (PID: 3880)
Modifies the open verb of a shell class
- msiexec.exe (PID: 3976)
Reads internet explorer settings
- ScreenConnect.WindowsClient.exe (PID: 1516)
Adds / modifies Windows certificates
- ScreenConnect.WindowsClient.exe (PID: 1516)
Creates files in the user directory
- ScreenConnect.WindowsClient.exe (PID: 1516)
Application launched itself
- ScreenConnect.WindowsClient.exe (PID: 3376)
INFO
Application launched itself
- msiexec.exe (PID: 3976)
Searches for installed software
- msiexec.exe (PID: 3976)
Creates files in the program directory
- msiexec.exe (PID: 3976)
Changes settings of System certificates
- DrvInst.exe (PID: 3732)
Creates a software uninstall entry
- msiexec.exe (PID: 3976)
Reads settings of System Certificates
- ScreenConnect.WindowsClient.exe (PID: 1516)
Low-level read access rights to disk partition
- vssvc.exe (PID: 1440)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 3732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (47.3) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (35.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:06:20 19:09:26+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 32768 |
| InitializedDataSize: | 3590656 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x124b |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Jun-2018 17:09:26 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 20-Jun-2018 17:09:26 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00007EA6 | 0x00008000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54461 |
.rdata | 0x00009000 | 0x0000520A | 0x00005400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.62058 |
.data | 0x0000F000 | 0x00002C94 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.38535 |
.rsrc | 0x00012000 | 0x00363C7C | 0x00363E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.37958 |
.reloc | 0x00376000 | 0x000028D8 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 2.91982 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | Latin 1 / Western European | English - United States | RT_MANIFEST |
SCREENCONNECT.CORE, VERSION=6.9.21870.6964, CULTURE=NEUTRAL, PUBLICKEYTOKEN=4B14C015C87C1AD8 | 6.17357 | 350208 | Latin 1 / Western European | UNKNOWN | FILES |
SCREENCONNECT.WINDOWS, VERSION=6.9.21870.6964, CULTURE=NEUTRAL, PUBLICKEYTOKEN=4B14C015C87C1AD8 | 6.73756 | 1161216 | Latin 1 / Western European | UNKNOWN | FILES |
SCREENCONNECT.WINDOWSINSTALLER, VERSION=6.9.21870.6964, CULTURE=NEUTRAL, PUBLICKEYTOKEN=4B14C015C87C1AD8 | 5.68085 | 78336 | Latin 1 / Western European | UNKNOWN | FILES |
_ENTRYPOINT | 7.73918 | 1957656 | Latin 1 / Western European | UNKNOWN | FILES |
_RESOLVER | 3.86896 | 5632 | Latin 1 / Western European | UNKNOWN | FILES |
Imports
KERNEL32.dll |
OLEAUT32.dll |
mscoree.dll |
Total processes
44
Monitored processes
11
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1440 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
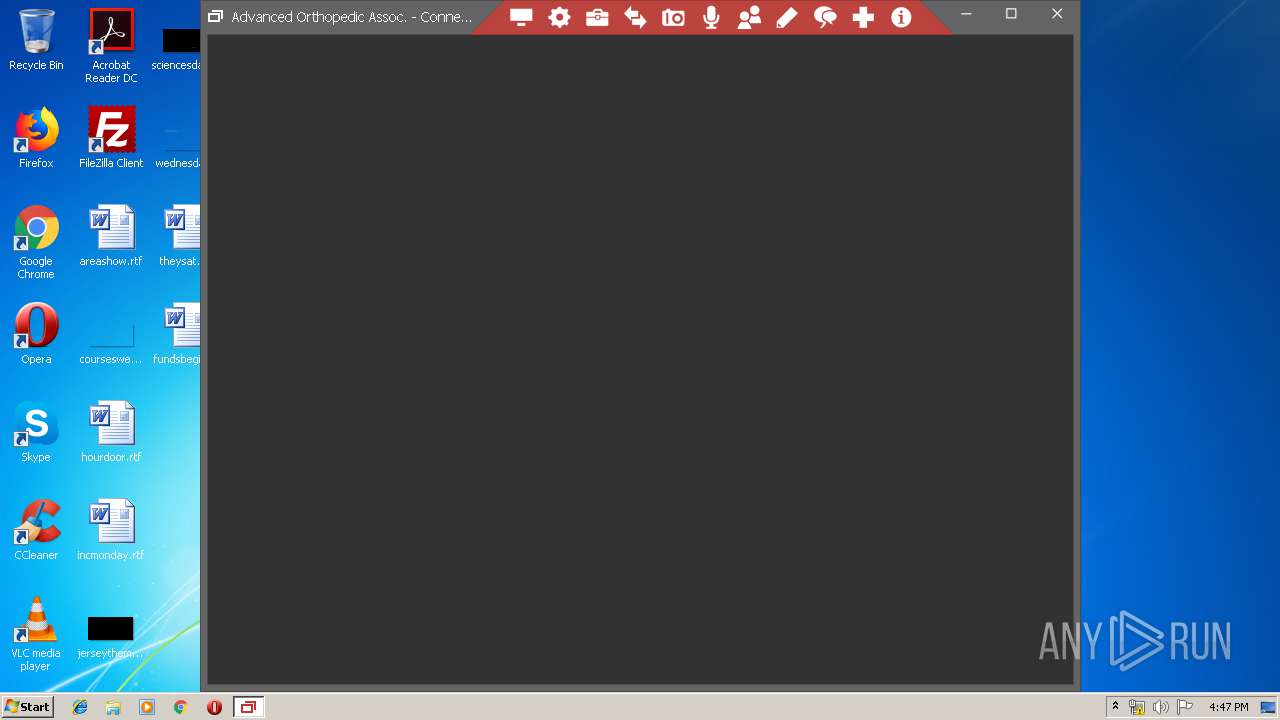
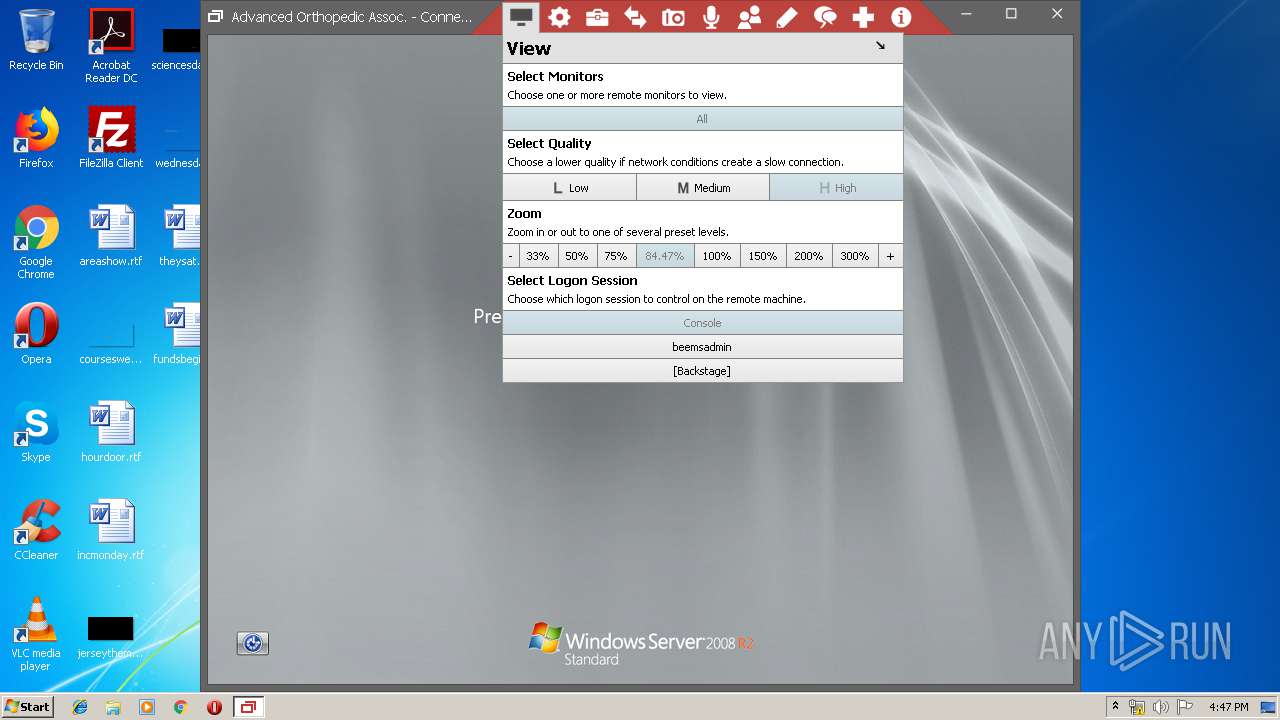
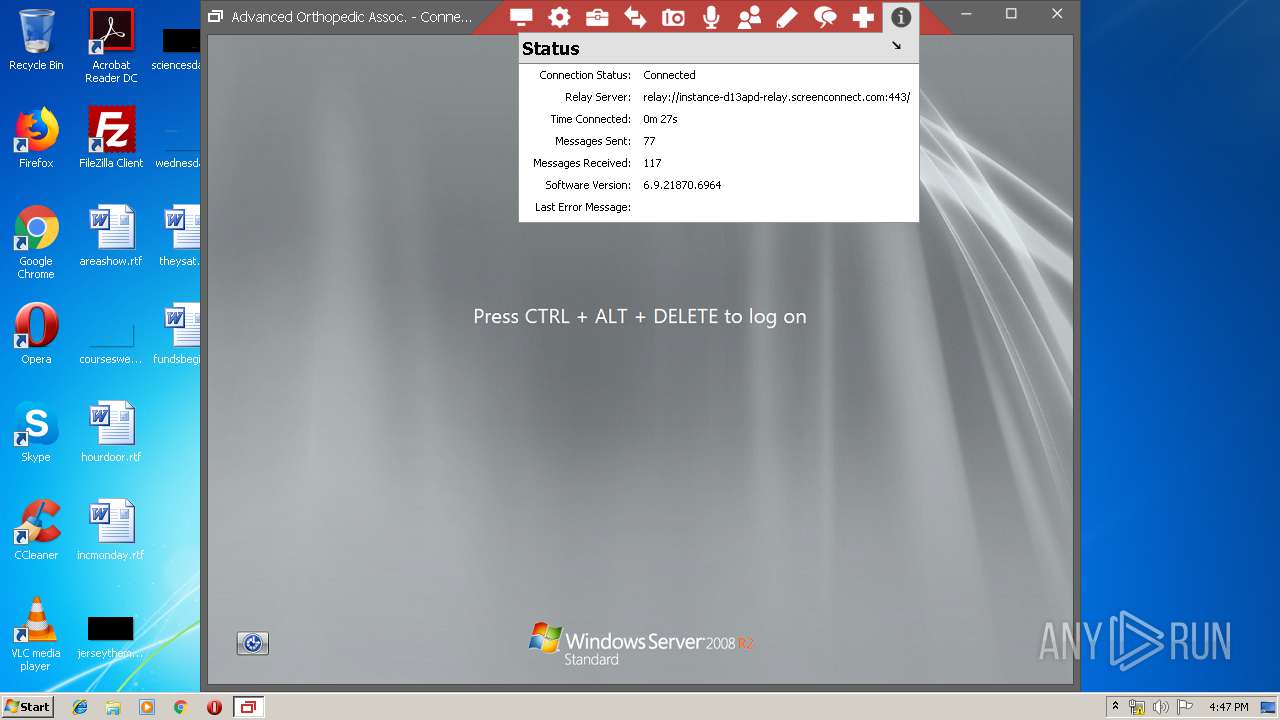
| 1516 | "C:\Program Files\ScreenConnect Client (1ad50f7791df3f69)\ScreenConnect.WindowsClient.exe" "?e=Access&y=Host&h=instance-d13apd-relay.screenconnect.com&p=443&s=28ff2184-1661-4147-901e-8b62c85cf219&k=BgIAAACkAABSU0ExAAgAAAEAAQATOi9v%2bW0%2bPR8%2fNjuZ3UaGJoiAIDcZNH3fhnePngdh42n3vy6MziIpEoVI0SbygjGRx2CF4ohWirVIZj5jHYZqL2pHO8rFDaGEjaGR6z1rMmGOX3329wkpnLDidW9R97DlK2VCgW6H5oM%2b%2fO%2bcxLuOEOb5KzQUB4EUGyZp6vXgXklGINddlCrOXb%2fuXbDrCY3y1i7h5bT2cCqzjHLtCmfO9NZ%2bYinUSFnSzLn6J061IliGI6EaKfWAT%2b69L8KrFn%2bLIepEKVEidM0Q2w1xi4efOpRU0eCtTNmP%2fpJT3mOUR%2b7NEym0Rt3%2fIvoAjMeNzmpcpQVniXRr0rVFv%2bSOKiOv&n=AQG4%2fOCh7QGAowUMRGViYmllIFRob21lid4dtRmP2c%2f1GMQnVd47EPieenhfclGXJ8pgrZas15OlcWc%3d&i=Advanced%20Orthopedic%20Assoc." | C:\Program Files\ScreenConnect Client (1ad50f7791df3f69)\ScreenConnect.WindowsClient.exe | ScreenConnect.WindowsClient.exe | ||||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: ScreenConnect Client Exit code: 0 Version: 6.9.21870.6964 Modules
| |||||||||||||||
| 1896 | C:\Windows\system32\MsiExec.exe -Embedding 0E1C34C45C0E27DFFCABDFD042C07CF8 M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2360 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\MSI681C.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_944390 1 ScreenConnect.InstallerActions!ScreenConnect.ClientInstallerActions.FixupServiceArguments | C:\Windows\system32\rundll32.exe | MsiExec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2364 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\setup.msi" | C:\Windows\System32\msiexec.exe | ConnectWiseControl.ClientSetup (67).exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3376 | "C:\Program Files\ScreenConnect Client (1ad50f7791df3f69)\ScreenConnect.WindowsClient.exe" "Rerun" "?e=Access&y=Host&h=instance-d13apd-relay.screenconnect.com&p=443&s=28ff2184-1661-4147-901e-8b62c85cf219&k=BgIAAACkAABSU0ExAAgAAAEAAQATOi9v%2bW0%2bPR8%2fNjuZ3UaGJoiAIDcZNH3fhnePngdh42n3vy6MziIpEoVI0SbygjGRx2CF4ohWirVIZj5jHYZqL2pHO8rFDaGEjaGR6z1rMmGOX3329wkpnLDidW9R97DlK2VCgW6H5oM%2b%2fO%2bcxLuOEOb5KzQUB4EUGyZp6vXgXklGINddlCrOXb%2fuXbDrCY3y1i7h5bT2cCqzjHLtCmfO9NZ%2bYinUSFnSzLn6J061IliGI6EaKfWAT%2b69L8KrFn%2bLIepEKVEidM0Q2w1xi4efOpRU0eCtTNmP%2fpJT3mOUR%2b7NEym0Rt3%2fIvoAjMeNzmpcpQVniXRr0rVFv%2bSOKiOv&n=AQG4%2fOCh7QGAowUMRGViYmllIFRob21lid4dtRmP2c%2f1GMQnVd47EPieenhfclGXJ8pgrZas15OlcWc%3d&i=Advanced%20Orthopedic%20Assoc." | C:\Program Files\ScreenConnect Client (1ad50f7791df3f69)\ScreenConnect.WindowsClient.exe | — | msiexec.exe | |||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: ScreenConnect Client Exit code: 0 Version: 6.9.21870.6964 Modules
| |||||||||||||||
| 3580 | C:\Windows\system32\MsiExec.exe -Embedding 380886A056C243E15FE971AFF52E26B7 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3708 | "C:\Users\admin\AppData\Local\Temp\ConnectWiseControl.ClientSetup (67).exe" | C:\Users\admin\AppData\Local\Temp\ConnectWiseControl.ClientSetup (67).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3732 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot18" "" "" "6792c44eb" "00000000" "000004C0" "000004AC" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3880 | C:\Windows\system32\MsiExec.exe -Embedding 81851BDC3231DB71FC4D33B220C95B47 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 181
Read events
878
Write events
288
Delete events
15
Modification events
| (PID) Process: | (3708) ConnectWiseControl.ClientSetup (67).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3708) ConnectWiseControl.ClientSetup (67).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3976) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 400000000000000090F5E5C9C6EBD401880F0000F80D0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3976) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000EA57E8C9C6EBD401880F0000F80D0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3976) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 20 | |||
| (PID) Process: | (3976) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000F43D70CAC6EBD401880F0000F80D0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3976) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000004EA072CAC6EBD401880F0000B8000000E8030000010000000000000000000000D217D350DC9CED4EA7C705CDD2367FB30000000000000000 | |||
| (PID) Process: | (1440) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000D2778ACAC6EBD401A0050000E40C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1440) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000D2778ACAC6EBD401A005000040010000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1440) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000D2778ACAC6EBD401A00500004C0C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
14
Suspicious files
8
Text files
134
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3976 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3976 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF1DB36B213A524C56.TMP | — | |
MD5:— | SHA256:— | |||
| 3976 | msiexec.exe | C:\Windows\Installer\MSIBF37.tmp | — | |
MD5:— | SHA256:— | |||
| 3976 | msiexec.exe | C:\Windows\Installer\MSIBF86.tmp | — | |
MD5:— | SHA256:— | |||
| 3708 | ConnectWiseControl.ClientSetup (67).exe | C:\Users\admin\AppData\Local\Temp\setup.msi | executable | |
MD5:— | SHA256:— | |||
| 3976 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{50d317d2-9cdc-4eed-a7c7-05cdd2367fb3}_OnDiskSnapshotProp | binary | |
MD5:— | SHA256:— | |||
| 3732 | DrvInst.exe | C:\Windows\INF\setupapi.ev3 | binary | |
MD5:— | SHA256:— | |||
| 3976 | msiexec.exe | C:\Windows\Installer\eb66b.msi | executable | |
MD5:— | SHA256:— | |||
| 3976 | msiexec.exe | C:\Windows\Installer\MSIBD31.tmp | binary | |
MD5:— | SHA256:— | |||
| 3976 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
3
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1516 | ScreenConnect.WindowsClient.exe | 18.205.123.62:443 | instance-d13apd-relay.screenconnect.com | — | US | unknown |
1516 | ScreenConnect.WindowsClient.exe | 216.58.210.14:443 | cse.google.com | Google Inc. | US | whitelisted |
1516 | ScreenConnect.WindowsClient.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
instance-d13apd-relay.screenconnect.com |
| unknown |
cse.google.com |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
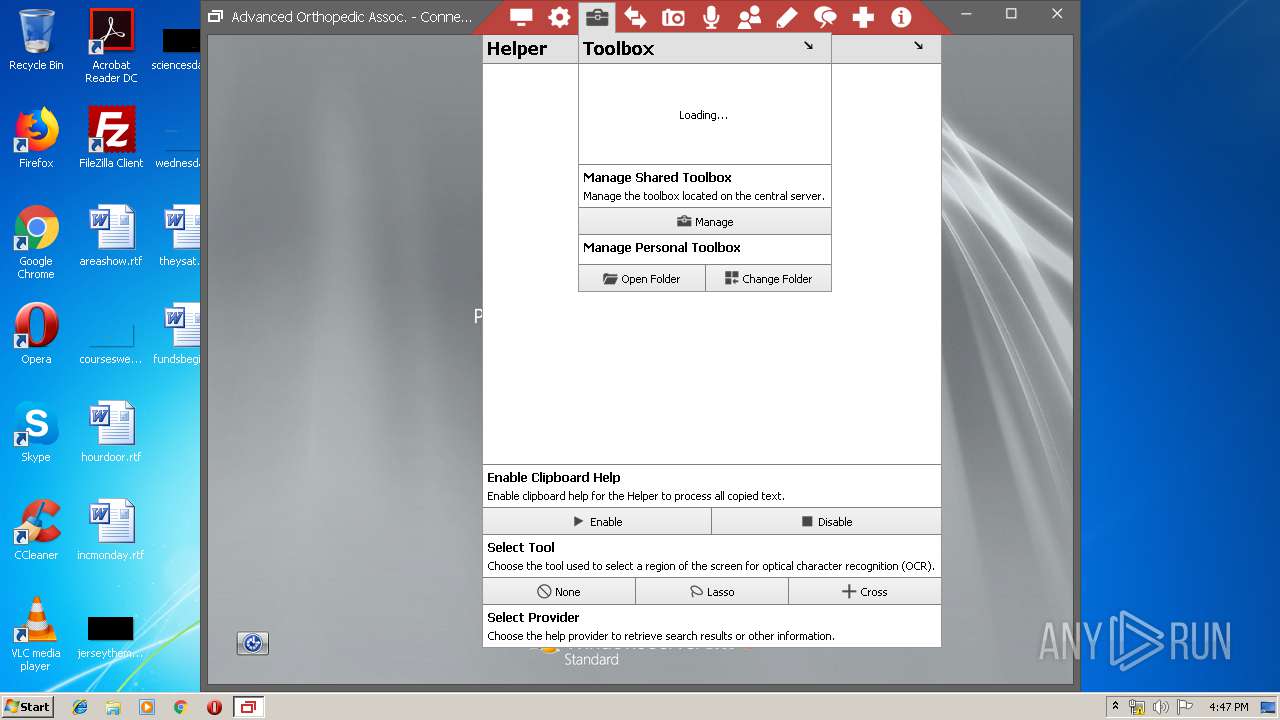
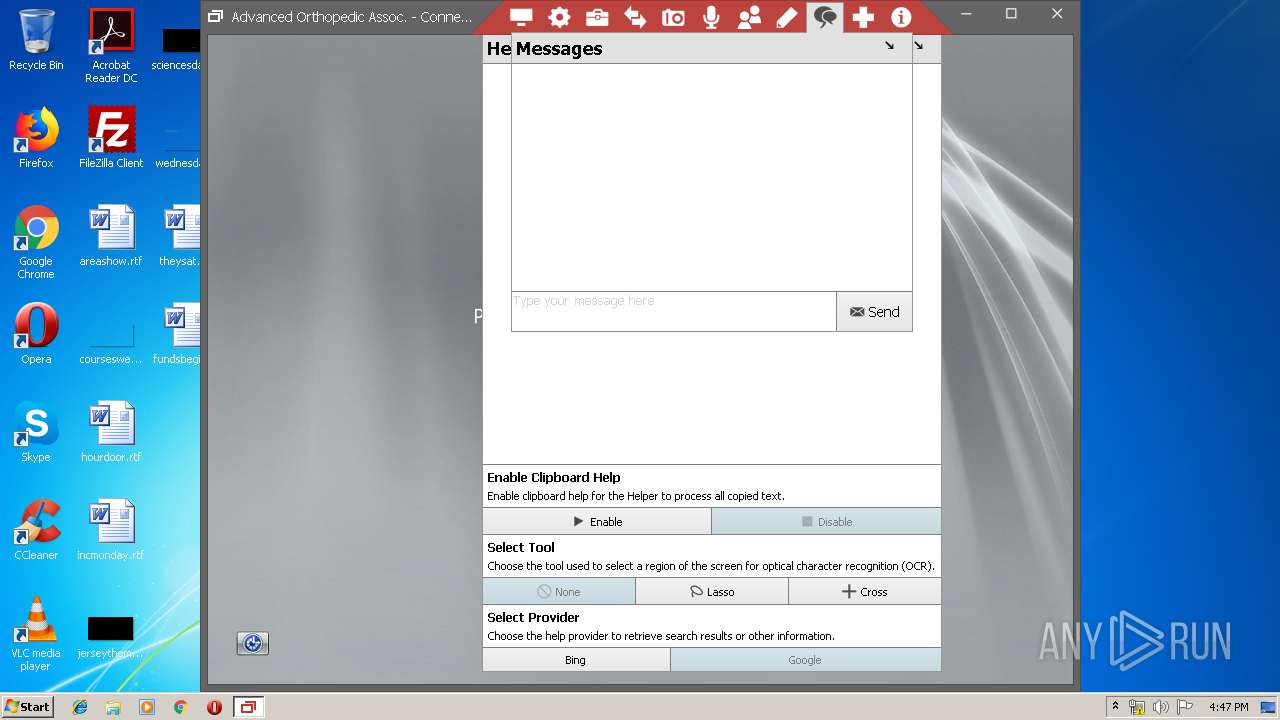
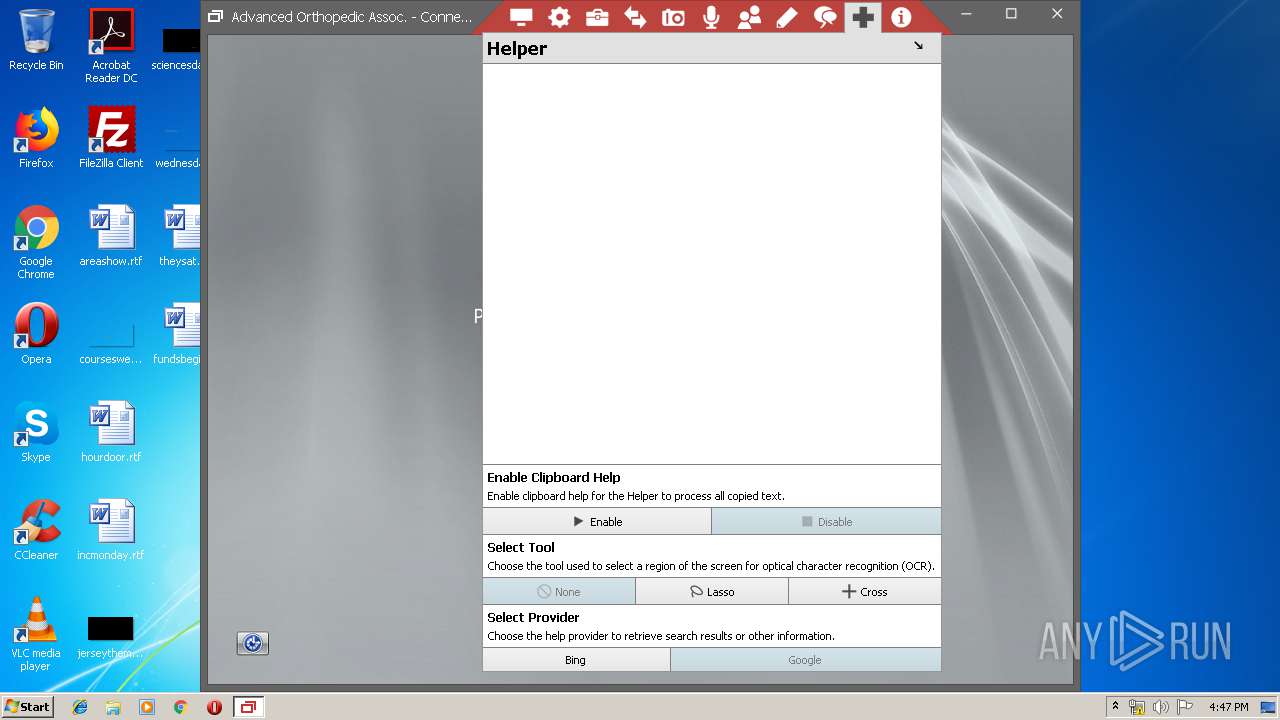
1516 | ScreenConnect.WindowsClient.exe | Misc activity | APP [PTsecurity] ScreenConnect |
1 ETPRO signatures available at the full report