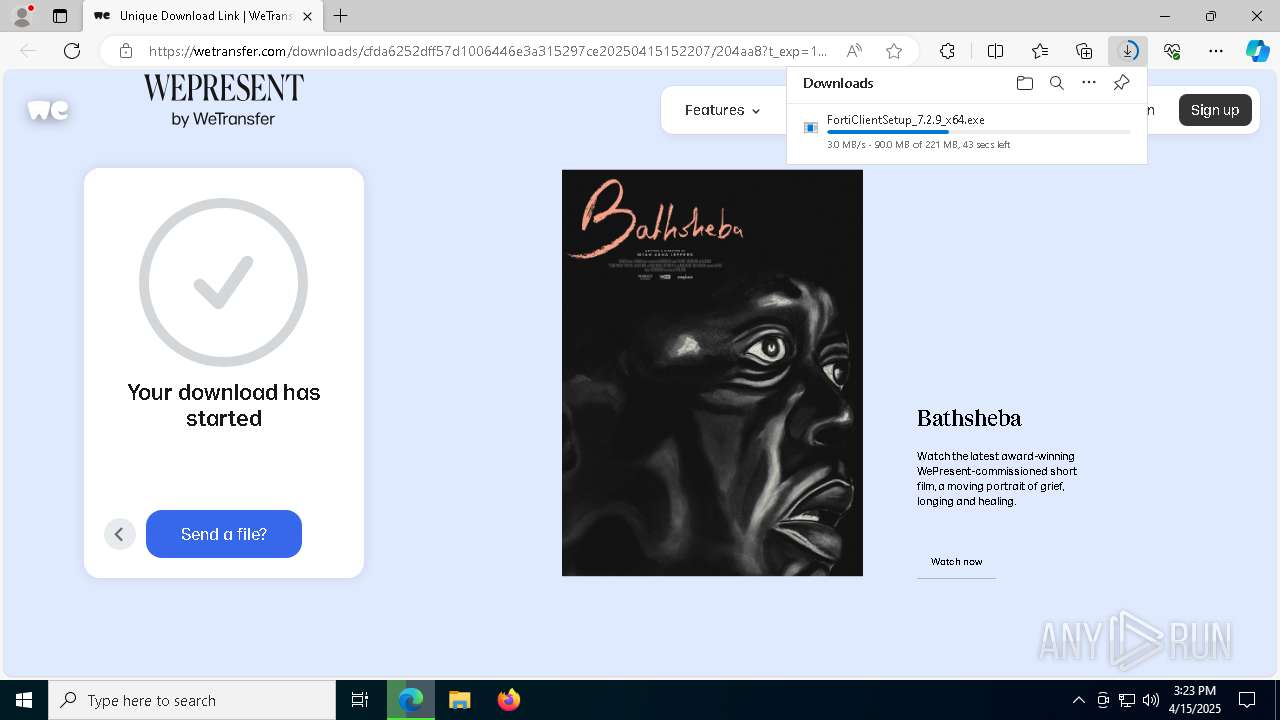
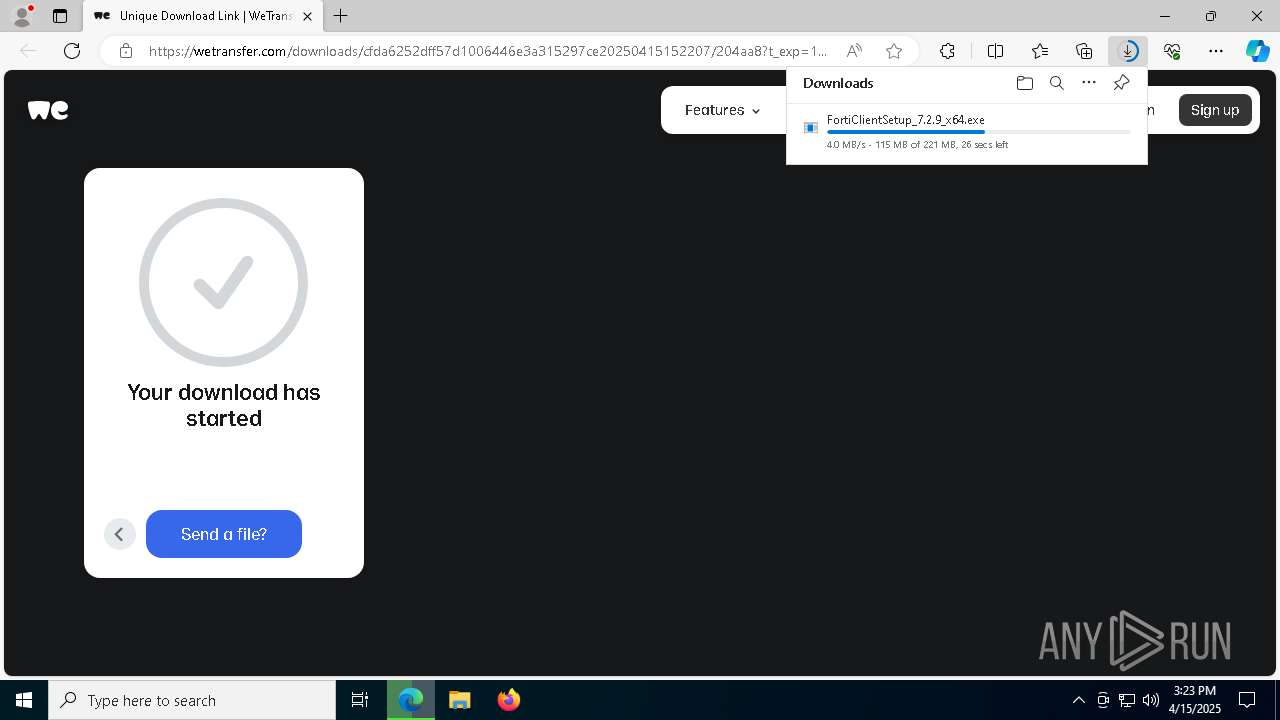
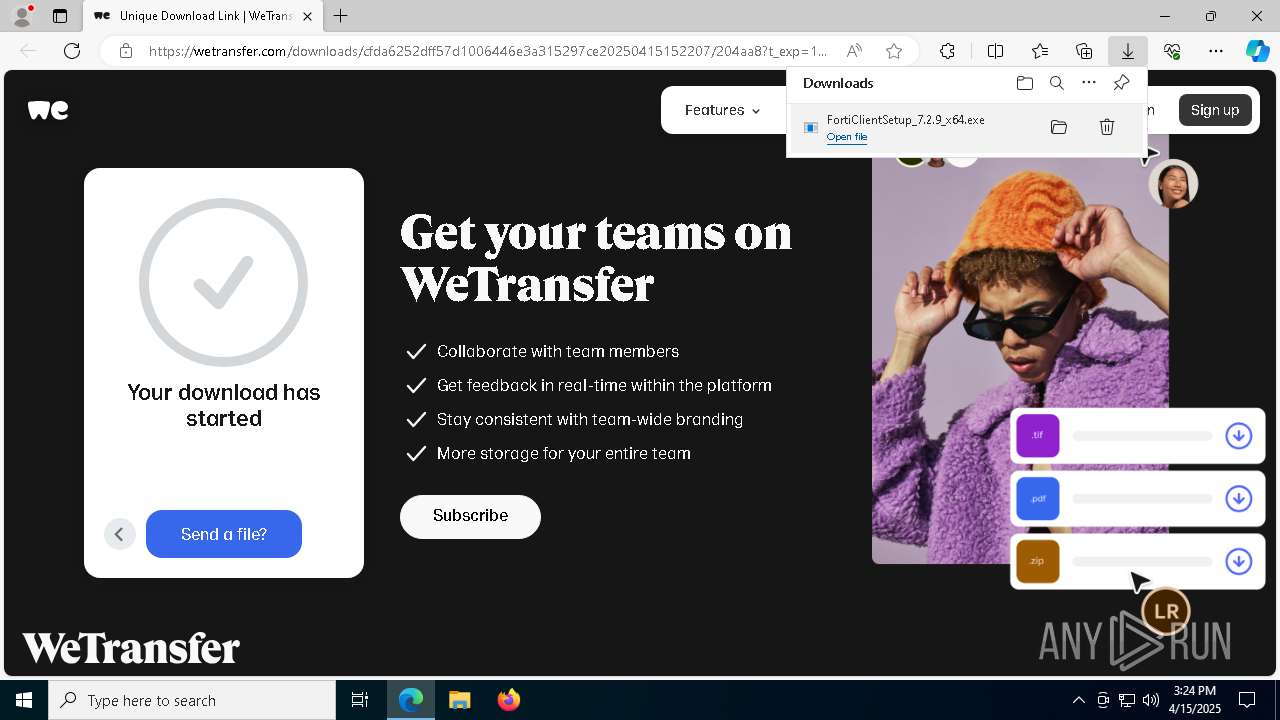
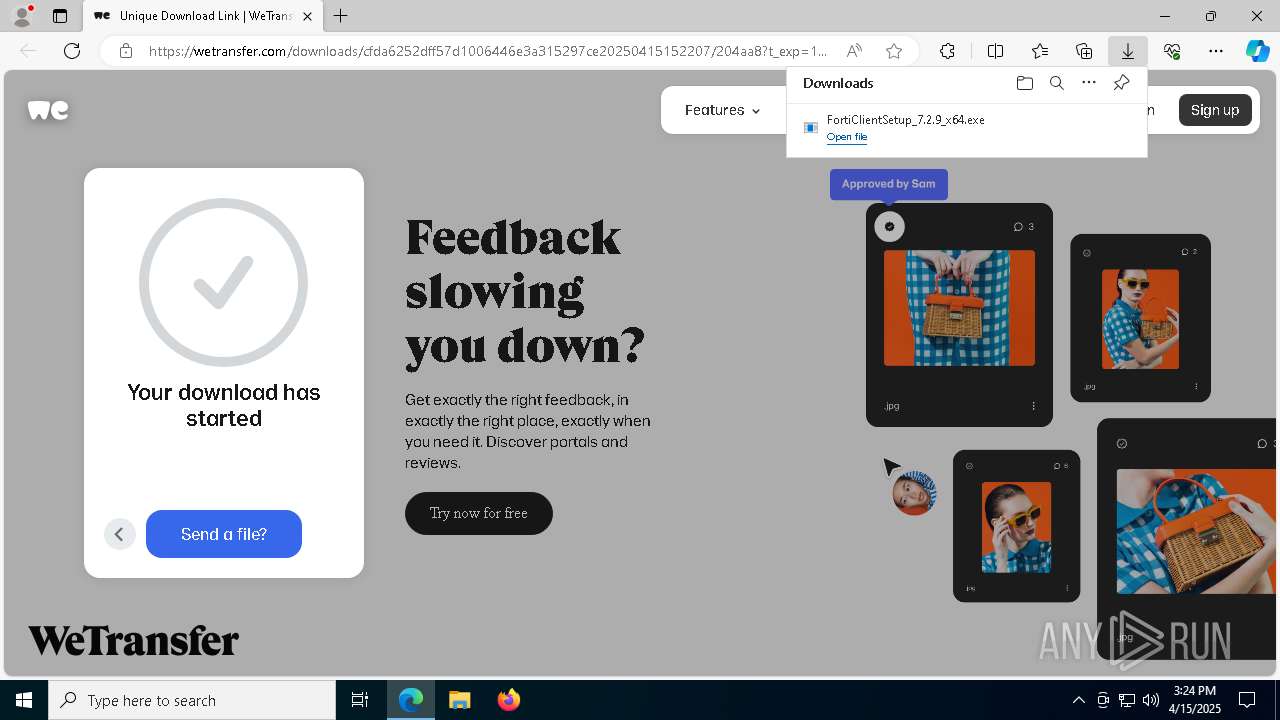
| URL: | https://we.tl/t-lWq3USMIqd |
| Full analysis: | https://app.any.run/tasks/781d6b2e-35d6-44e7-9e93-42404c0b26ac |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2025, 15:22:47 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 83018AF89C7478F48572C3C08AEB0462 |
| SHA1: | 52B4FE3AE02D93F88F21B2B296FEFBB406D1594C |
| SHA256: | 69EA58912B76917721A72175F1F6155D114DFA7C25B470AD7787902A761C0687 |
| SSDEEP: | 3:N8RlJKlPDoL:2KLy |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- msiexec.exe (PID: 5796)
- scheduler.exe (PID: 1012)
The DLL Hijacking
- regsvr32.exe (PID: 4376)
- regsvr32.exe (PID: 6892)
Starts NET.EXE for service management
- FortiSSLVPNdaemon.exe (PID: 4348)
- net.exe (PID: 7572)
SUSPICIOUS
Reads the Windows owner or organization settings
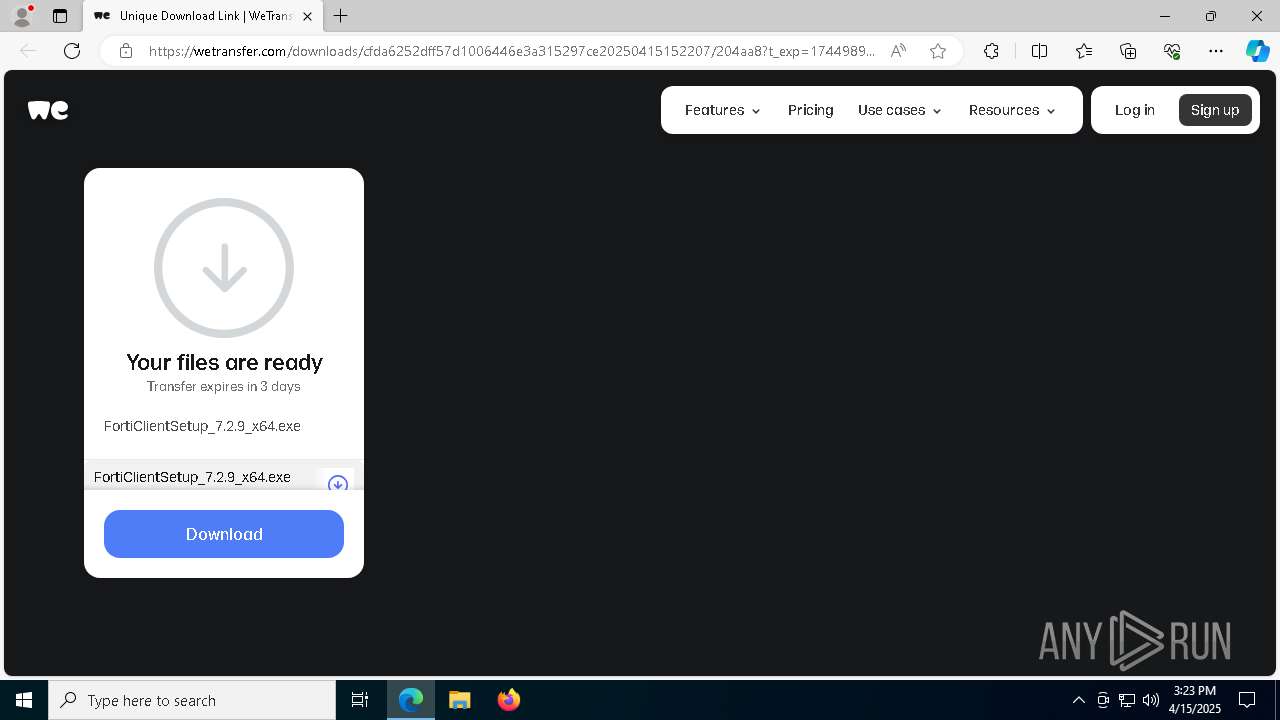
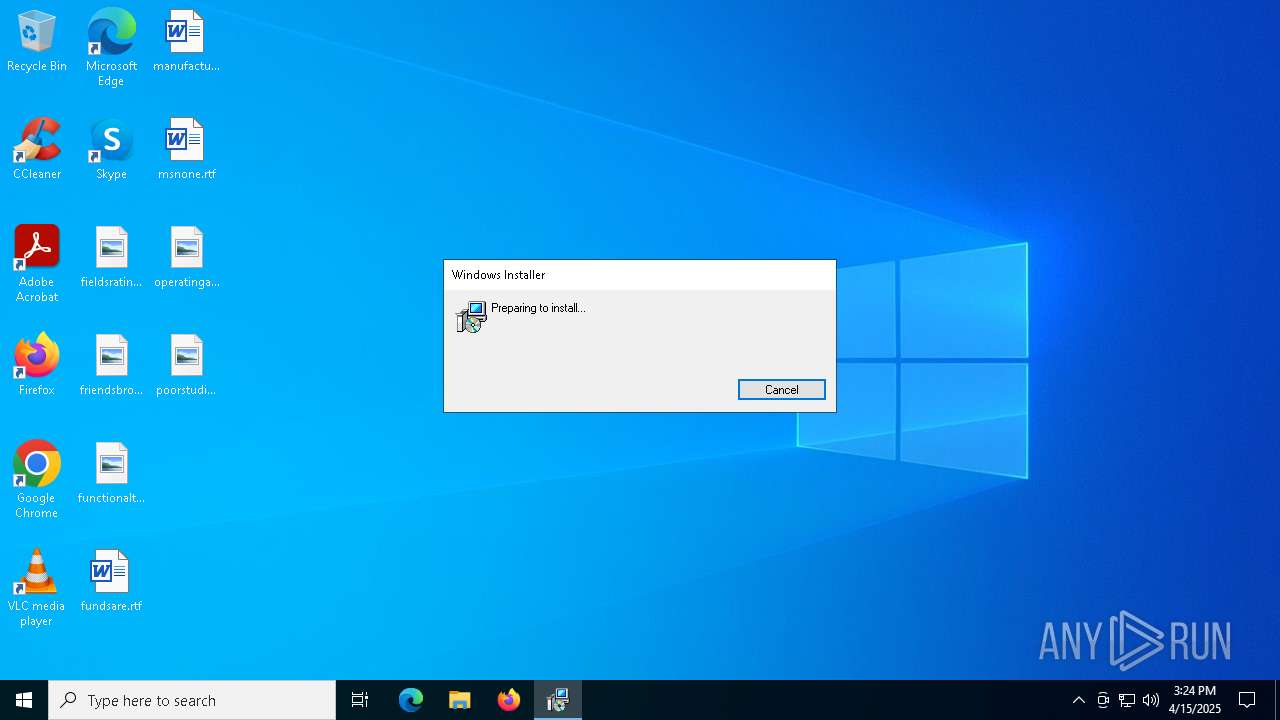
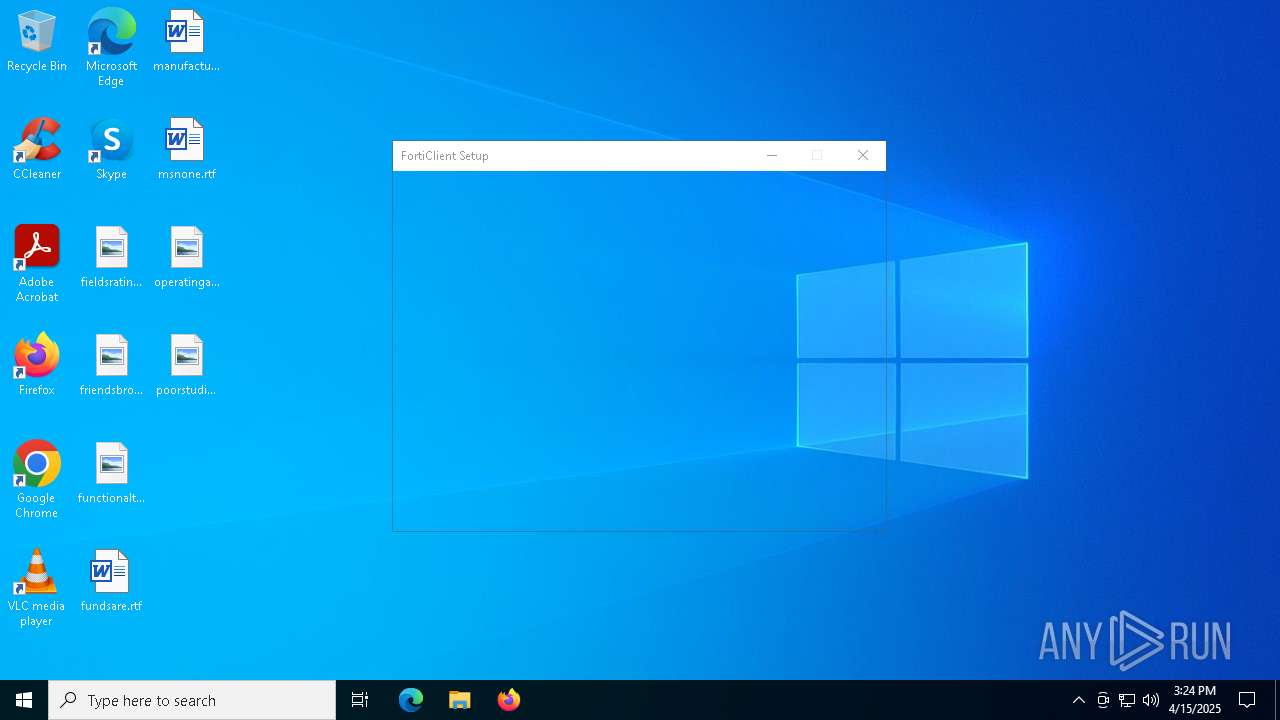
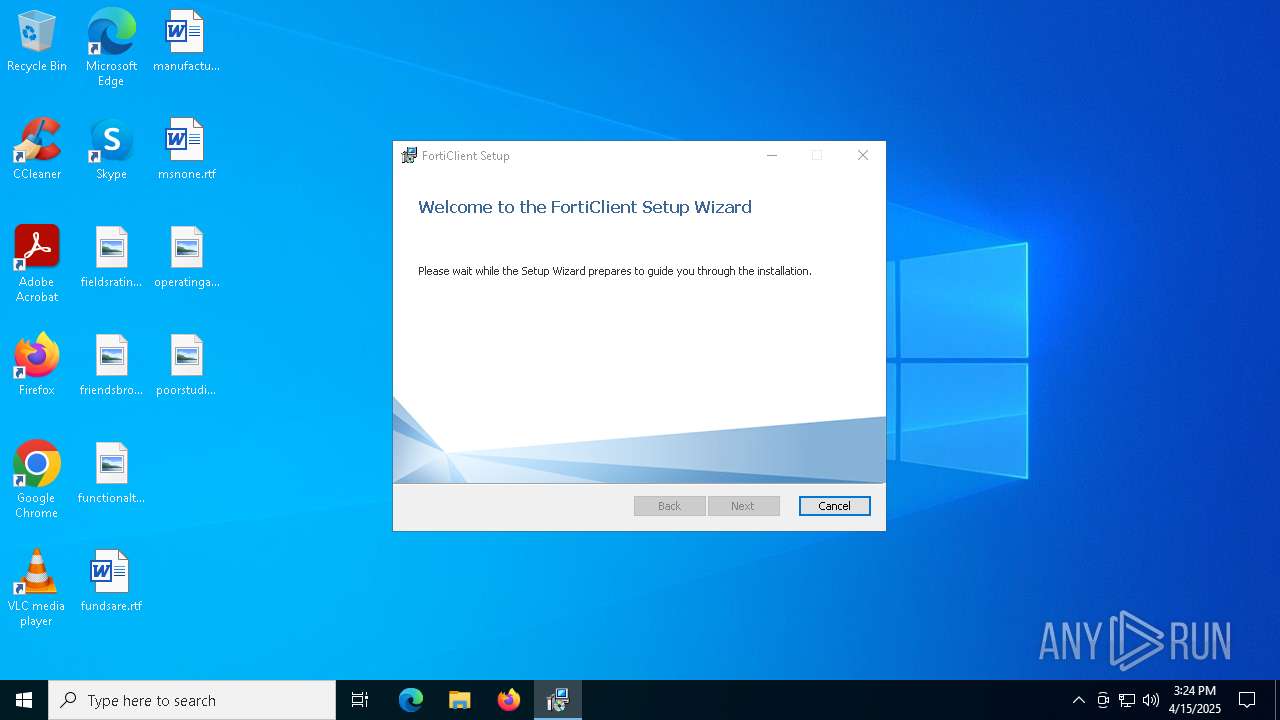
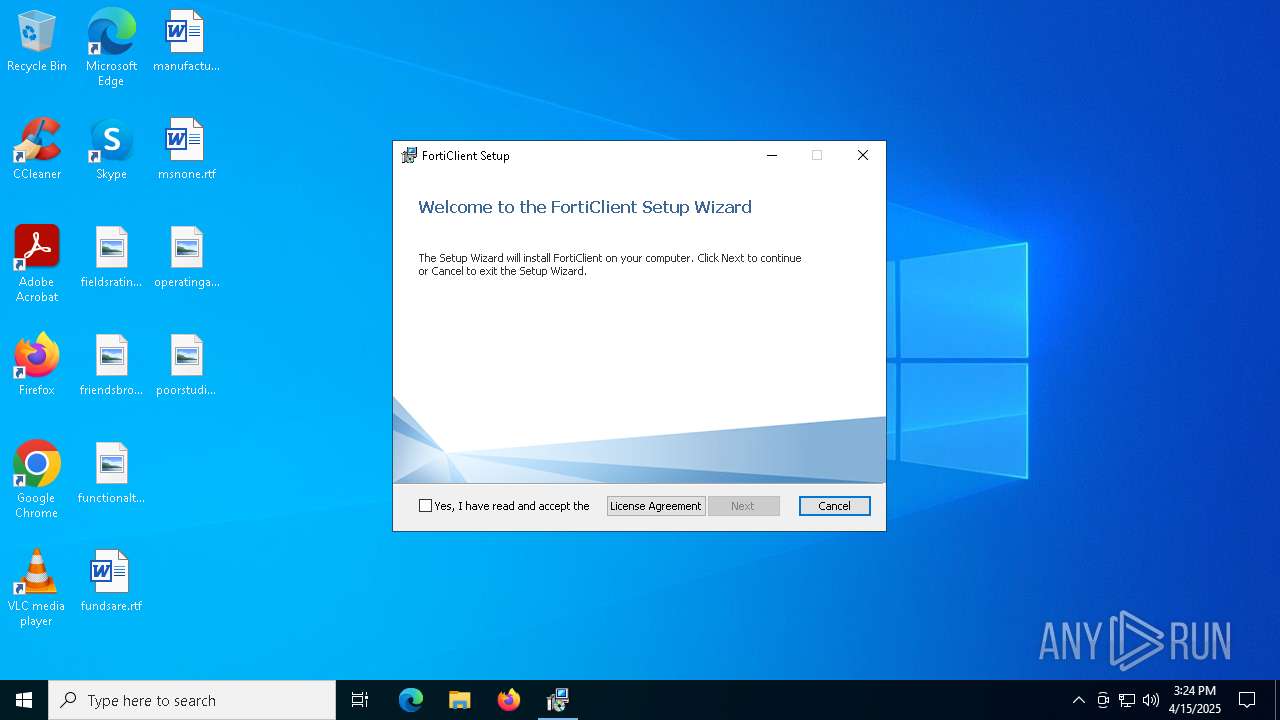
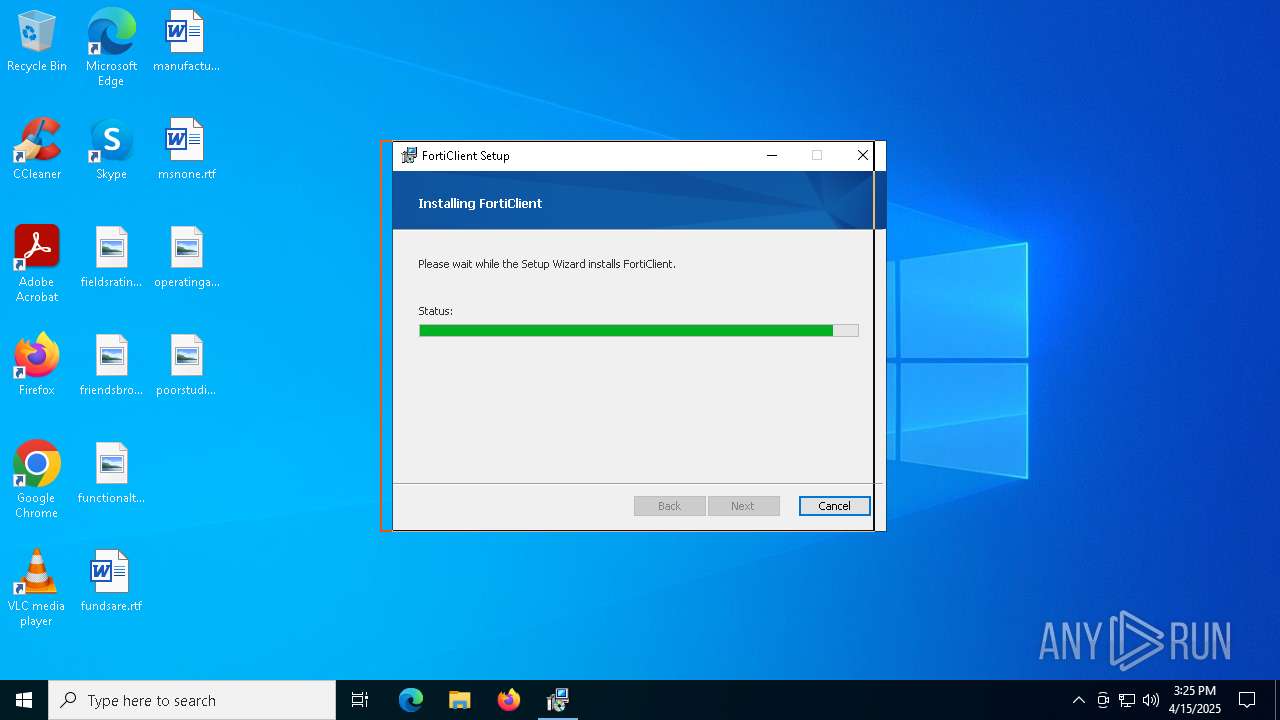
- FortiClientSetup_7.2.9_x64.exe (PID: 8432)
- msiexec.exe (PID: 2596)
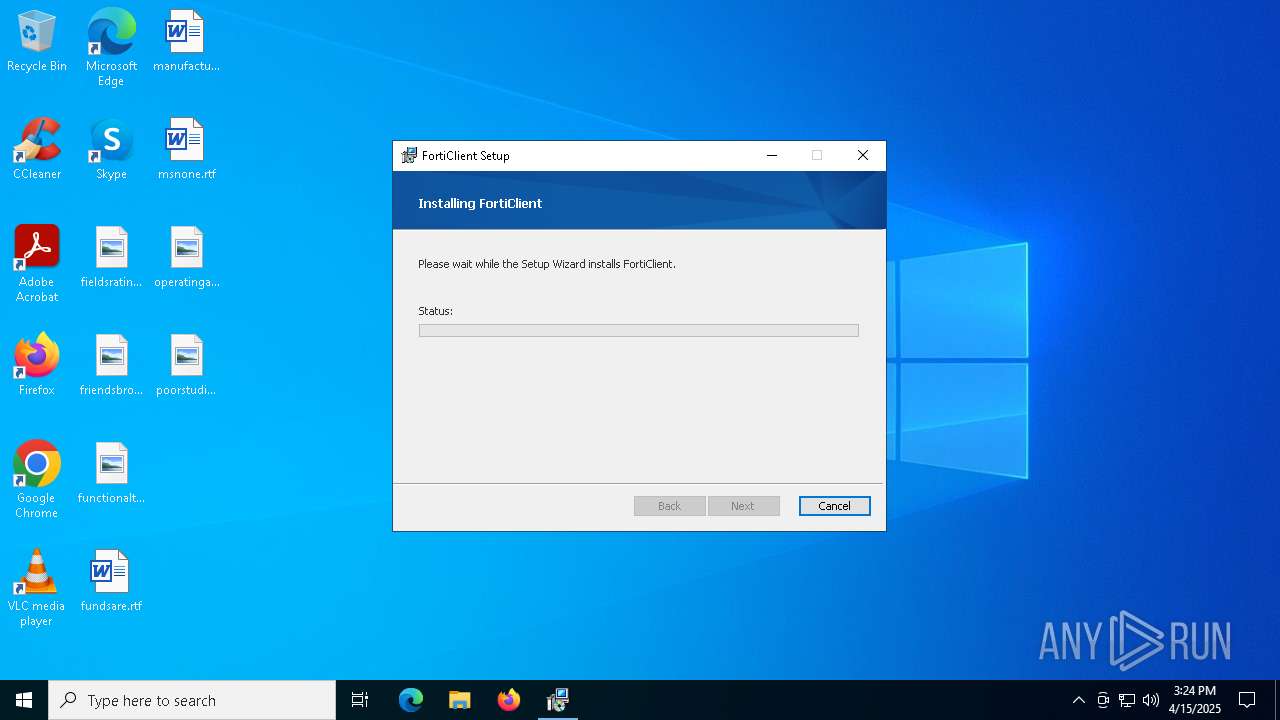
Executable content was dropped or overwritten
- FortiClientSetup_7.2.9_x64.exe (PID: 8432)
- drvinst.exe (PID: 8580)
- drvinst.exe (PID: 4892)
- drvinst.exe (PID: 8152)
- drvinst.exe (PID: 7656)
- drvinst.exe (PID: 7488)
- drvinst.exe (PID: 6512)
- drvinst.exe (PID: 9176)
- update_task.exe (PID: 5452)
Reads security settings of Internet Explorer
- FortiClientSetup_7.2.9_x64.exe (PID: 8432)
- scheduler.exe (PID: 1012)
- msiexec.exe (PID: 5796)
- FCDBLog.exe (PID: 2960)
- update_task.exe (PID: 5452)
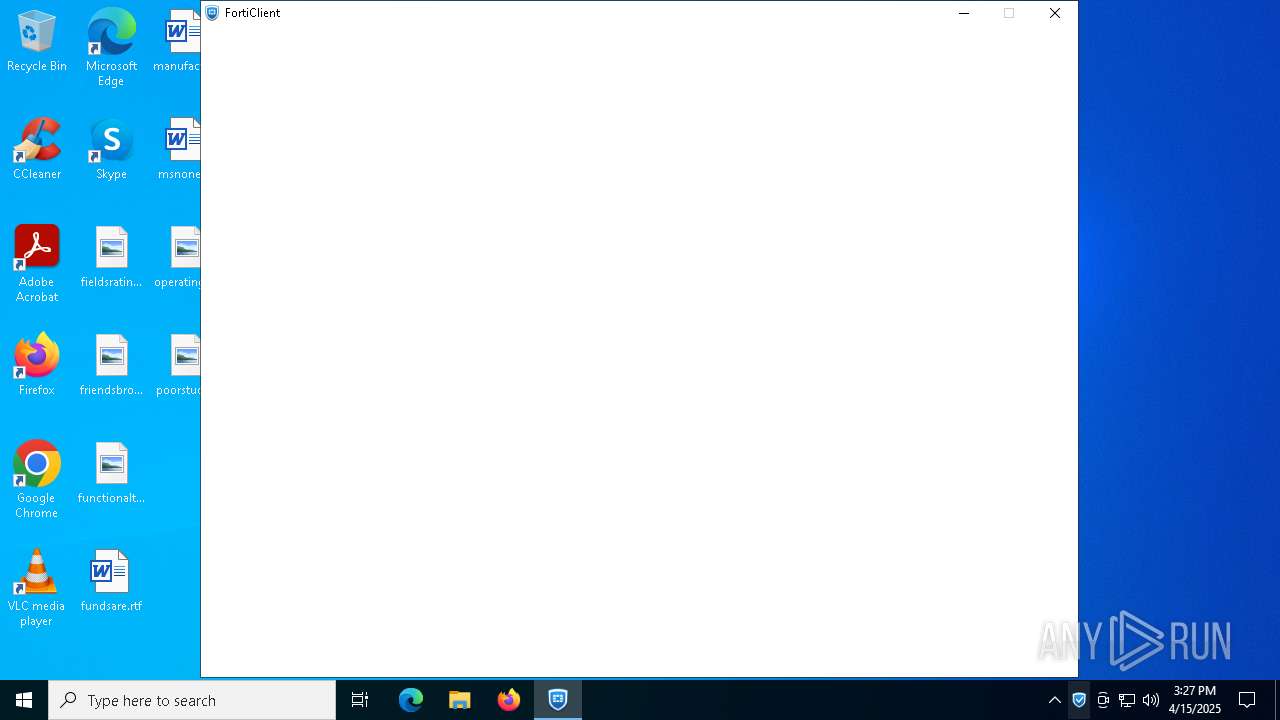
Application launched itself
- msiexec.exe (PID: 2596)
- FortiClient.exe (PID: 5640)
- FortiClient.exe (PID: 2104)
Process drops legitimate windows executable
- msiexec.exe (PID: 2596)
- update_task.exe (PID: 5452)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 2596)
- drvinst.exe (PID: 8580)
- drvinst.exe (PID: 4892)
- drvinst.exe (PID: 7488)
- drvinst.exe (PID: 6512)
- msiexec.exe (PID: 5796)
Creates files in the driver directory
- msiexec.exe (PID: 2596)
- drvinst.exe (PID: 8580)
- msiexec.exe (PID: 5796)
- drvinst.exe (PID: 4892)
- drvinst.exe (PID: 7656)
- drvinst.exe (PID: 7488)
- drvinst.exe (PID: 6512)
The process drops C-runtime libraries
- msiexec.exe (PID: 2596)
The process creates files with name similar to system file names
- msiexec.exe (PID: 2596)
Creates or modifies Windows services
- drvinst.exe (PID: 8152)
- drvinst.exe (PID: 7656)
- drvinst.exe (PID: 9176)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 2596)
- regsvr32.exe (PID: 4376)
- regsvr32.exe (PID: 6892)
- regsvr32.exe (PID: 8688)
- regsvr32.exe (PID: 7716)
- FCDBLog.exe (PID: 2960)
Executes as Windows Service
- FctSecSvr.exe (PID: 8384)
- scheduler.exe (PID: 1012)
Modifies hosts file to alter network resolution
- FCDBLog.exe (PID: 2960)
Reads the date of Windows installation
- scheduler.exe (PID: 1012)
Checks for external IP
- FortiESNAC.exe (PID: 7516)
Creates a software uninstall entry
- FortiESNAC.exe (PID: 7516)
Searches for installed software
- update_task.exe (PID: 5452)
Process uses IPCONFIG to clear DNS cache
- FortiTcs.exe (PID: 1664)
Adds/modifies Windows certificates
- certutil.exe (PID: 8288)
INFO
Reads Environment values
- identity_helper.exe (PID: 8172)
- identity_helper.exe (PID: 872)
- msiexec.exe (PID: 8048)
- msiexec.exe (PID: 7828)
- FctSecSvr.exe (PID: 8384)
- FCDBLog.exe (PID: 2960)
- FortiTray.exe (PID: 8624)
- FortiESNAC.exe (PID: 7516)
- FortiSSLVPNdaemon.exe (PID: 4348)
- EPCUserAvatar.exe (PID: 7880)
- FortiClient.exe (PID: 5640)
- FortiVPN.exe (PID: 8804)
- update_task.exe (PID: 5452)
- FortiClient.exe (PID: 1228)
- FortiClient.exe (PID: 2104)
Executable content was dropped or overwritten
- msedge.exe (PID: 7364)
- msiexec.exe (PID: 2596)
- msiexec.exe (PID: 5796)
- msedge.exe (PID: 5640)
Checks supported languages
- identity_helper.exe (PID: 8172)
- FortiClientSetup_7.2.9_x64.exe (PID: 8432)
- msiexec.exe (PID: 2596)
- identity_helper.exe (PID: 872)
- msiexec.exe (PID: 8048)
- msiexec.exe (PID: 7828)
- msiexec.exe (PID: 5796)
- drvinst.exe (PID: 8580)
- drvinst.exe (PID: 8152)
- drvinst.exe (PID: 4892)
- drvinst.exe (PID: 7488)
- drvinst.exe (PID: 7656)
- drvinst.exe (PID: 6512)
- drvinst.exe (PID: 9176)
- FCConfig.exe (PID: 4776)
- FctSecSvr.exe (PID: 8384)
- FCCOMInt.exe (PID: 4696)
- FCConfig.exe (PID: 7104)
- FortiTray.exe (PID: 8624)
- FortiESNAC.exe (PID: 7516)
- FortiSSLVPNdaemon.exe (PID: 4348)
- FortiVPN.exe (PID: 8804)
- fcappdb.exe (PID: 3884)
- FCDBLog.exe (PID: 2960)
- EPCUserAvatar.exe (PID: 7880)
- FortiClient.exe (PID: 8020)
- FortiClient.exe (PID: 5640)
- FortiClient.exe (PID: 1228)
- FortiClient.exe (PID: 2104)
- FortiClient.exe (PID: 4976)
- FortiClient.exe (PID: 8288)
- FortiClient.exe (PID: 6300)
- FortiClient.exe (PID: 7236)
- FortiClient.exe (PID: 8440)
- update_task.exe (PID: 5452)
- FortiClient.exe (PID: 1096)
- FortiClient.exe (PID: 720)
- FortiTcs.exe (PID: 1664)
- FCConfig.exe (PID: 5484)
- FCConfig.exe (PID: 4980)
Reads the computer name
- identity_helper.exe (PID: 8172)
- msiexec.exe (PID: 2596)
- FortiClientSetup_7.2.9_x64.exe (PID: 8432)
- identity_helper.exe (PID: 872)
- msiexec.exe (PID: 5796)
- msiexec.exe (PID: 7828)
- drvinst.exe (PID: 8580)
- drvinst.exe (PID: 8152)
- msiexec.exe (PID: 8048)
- drvinst.exe (PID: 4892)
- drvinst.exe (PID: 7656)
- drvinst.exe (PID: 7488)
- drvinst.exe (PID: 6512)
- drvinst.exe (PID: 9176)
- FCConfig.exe (PID: 4776)
- FCDBLog.exe (PID: 2960)
- fcappdb.exe (PID: 3884)
- FortiTray.exe (PID: 8624)
- FortiESNAC.exe (PID: 7516)
- FortiSSLVPNdaemon.exe (PID: 4348)
- FortiVPN.exe (PID: 8804)
- EPCUserAvatar.exe (PID: 7880)
- FortiClient.exe (PID: 5640)
- FortiSettings.exe (PID: 7740)
- update_task.exe (PID: 5452)
- FortiClient.exe (PID: 8020)
- FortiClient.exe (PID: 8288)
- FortiClient.exe (PID: 720)
- FortiClient.exe (PID: 1228)
- FortiTcs.exe (PID: 1664)
- FCConfig.exe (PID: 4980)
Application launched itself
- msedge.exe (PID: 1272)
- msedge.exe (PID: 4528)
Reads the machine GUID from the registry
- FortiClientSetup_7.2.9_x64.exe (PID: 8432)
- msiexec.exe (PID: 2596)
- drvinst.exe (PID: 8580)
- drvinst.exe (PID: 4892)
- drvinst.exe (PID: 7488)
- msiexec.exe (PID: 5796)
- drvinst.exe (PID: 6512)
- FortiClient.exe (PID: 5640)
Reads the software policy settings
- slui.exe (PID: 7832)
- FortiClientSetup_7.2.9_x64.exe (PID: 8432)
- msiexec.exe (PID: 2596)
- slui.exe (PID: 5408)
- drvinst.exe (PID: 8580)
- drvinst.exe (PID: 4892)
- drvinst.exe (PID: 7488)
- msiexec.exe (PID: 5796)
- FortiESNAC.exe (PID: 7516)
Creates files or folders in the user directory
- FortiClientSetup_7.2.9_x64.exe (PID: 8432)
- FortiTray.exe (PID: 8624)
- EPCUserAvatar.exe (PID: 7880)
- FortiClient.exe (PID: 5640)
- FortiClient.exe (PID: 2104)
- FortiClient.exe (PID: 8020)
Checks proxy server information
- FortiClientSetup_7.2.9_x64.exe (PID: 8432)
- slui.exe (PID: 5408)
- FortiClient.exe (PID: 5640)
- FortiClient.exe (PID: 2104)
- FortiESNAC.exe (PID: 7516)
Create files in a temporary directory
- FortiClientSetup_7.2.9_x64.exe (PID: 8432)
- FCConfig.exe (PID: 4776)
- FCConfig.exe (PID: 7104)
- EPCUserAvatar.exe (PID: 7880)
Creates files in the program directory
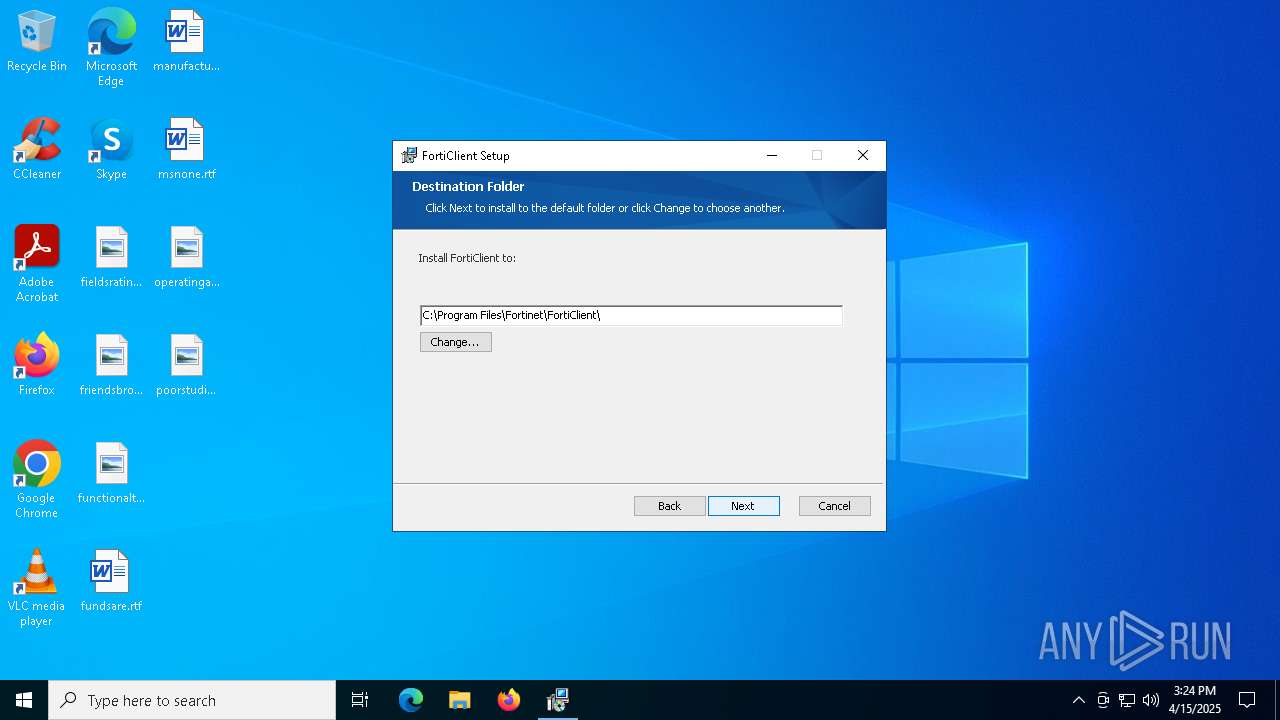
- FortiClientSetup_7.2.9_x64.exe (PID: 8432)
- FCDBLog.exe (PID: 2960)
- fcappdb.exe (PID: 3884)
- FortiVPN.exe (PID: 8804)
- FortiSSLVPNdaemon.exe (PID: 4348)
- update_task.exe (PID: 5452)
- FortiESNAC.exe (PID: 7516)
The sample compiled with english language support
- FortiClientSetup_7.2.9_x64.exe (PID: 8432)
- msiexec.exe (PID: 2596)
- msiexec.exe (PID: 5796)
- msedge.exe (PID: 5640)
- update_task.exe (PID: 5452)
Creates or modifies Windows services
- msiexec.exe (PID: 5796)
Creates a software uninstall entry
- msiexec.exe (PID: 5796)
Process checks computer location settings
- FCDBLog.exe (PID: 2960)
- FortiClient.exe (PID: 5640)
- update_task.exe (PID: 5452)
Reads product name
- FortiClient.exe (PID: 2104)
- FortiClient.exe (PID: 5640)
- FortiClient.exe (PID: 1228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
289
Monitored processes
143
Malicious processes
11
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 720 | "C:\Program Files\Fortinet\FortiClient\FortiClient.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\FortiClient" --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAABgAAAAAAAAAGAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=3204 --field-trial-handle=2024,i,2533453298803692098,10160894213089056418,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Program Files\Fortinet\FortiClient\FortiClient.exe | — | FortiClient.exe | |||||||||||
User: admin Company: Fortinet Inc. Integrity Level: LOW Description: FortiClient Console Exit code: 0 Version: 7.2.9.1185 Modules
| |||||||||||||||
| 872 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4300 --field-trial-handle=2260,i,8135313119993076461,10502892559813687602,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 968 | "C:\Windows\System32\regsvr32.exe" /s "C:\Program Files\Fortinet\FortiClient\x86\FortiAmsi.dll" | C:\Windows\System32\regsvr32.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Fortinet\FortiClient\scheduler.exe" | C:\Program Files\Fortinet\FortiClient\scheduler.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Fortinet Inc. Integrity Level: SYSTEM Description: FortiClient Scheduler Version: 7.2.9.1185 Modules
| |||||||||||||||
| 1096 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5168 --field-trial-handle=2260,i,8135313119993076461,10502892559813687602,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1096 | "C:\Program Files\Fortinet\FortiClient\FortiClient.exe" --type=crashpad-handler --user-data-dir=C:\Users\admin\AppData\Roaming\FortiClient /prefetch:7 --no-rate-limit --monitor-self-annotation=ptype=crashpad-handler --database=C:\Users\admin\AppData\Local\FortiClient\logs\trace --annotation=_productName=FortiClient --annotation=_version=7.0.0 --annotation=plat=Win64 --annotation=prod=Electron --annotation=ver=24.8.3 --initial-client-data=0x594,0x598,0x59c,0x590,0x5a0,0x7ff724a0dcb0,0x7ff724a0dcc0,0x7ff724a0dcd0 | C:\Program Files\Fortinet\FortiClient\FortiClient.exe | — | FortiClient.exe | |||||||||||
User: admin Company: Fortinet Inc. Integrity Level: MEDIUM Description: FortiClient Console Exit code: 0 Version: 7.2.9.1185 Modules
| |||||||||||||||
| 1116 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=5116 --field-trial-handle=2260,i,8135313119993076461,10502892559813687602,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1228 | "C:\Program Files\Fortinet\FortiClient\FortiClient.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\FortiClient" --app-user-model-id=FortiClient --app-path="C:\Program Files\Fortinet\FortiClient\resources\app.asar" --no-sandbox --no-zygote --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --mojo-platform-channel-handle=2972 --field-trial-handle=2024,i,2533453298803692098,10160894213089056418,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:1 | C:\Program Files\Fortinet\FortiClient\FortiClient.exe | — | FortiClient.exe | |||||||||||
User: admin Company: Fortinet Inc. Integrity Level: MEDIUM Description: FortiClient Console Exit code: 0 Version: 7.2.9.1185 Modules
| |||||||||||||||
| 1272 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://we.tl/t-lWq3USMIqd" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1664 | FortiTcs.exe -s FC_{73EFB30F-1CAD-4a7a-AE2E-150282B6CE25}_000029 | C:\Program Files\Fortinet\FortiClient\FortiTcs.exe | — | scheduler.exe | |||||||||||
User: SYSTEM Company: Fortinet Inc. Integrity Level: SYSTEM Description: FortiClient ZTNA Service Version: 7.2.9.1185 Modules
| |||||||||||||||
Total events
124 471
Read events
118 993
Write events
5 178
Delete events
300
Modification events
| (PID) Process: | (1272) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1272) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1272) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1272) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1272) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 5DC0BF0669912F00 | |||
| (PID) Process: | (1272) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 5E4ED30669912F00 | |||
| (PID) Process: | (1272) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328332 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {8B958B87-6C18-4D0B-866C-1CE5114D3727} | |||
| (PID) Process: | (1272) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328332 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {01150A04-5806-40D5-9FF8-DDED5FC64853} | |||
| (PID) Process: | (1272) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328332 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {DFC7F3A1-312E-4788-A610-978054C5B54A} | |||
| (PID) Process: | (1272) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328332 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {895DAFA3-35DA-4D36-8058-78414F6FC47A} | |||
Executable files
331
Suspicious files
1 255
Text files
181
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10cab4.TMP | — | |
MD5:— | SHA256:— | |||
| 1272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10cb12.TMP | — | |
MD5:— | SHA256:— | |||
| 1272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10cb12.TMP | — | |
MD5:— | SHA256:— | |||
| 1272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10cb12.TMP | — | |
MD5:— | SHA256:— | |||
| 1272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10cb9f.TMP | — | |
MD5:— | SHA256:— | |||
| 1272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
187
DNS requests
227
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6080 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1744954464&P2=404&P3=2&P4=VpvgJC14fYZ7%2bMV%2bByY5sCjdZcrQL6S64DrWeiCihNZNCHi21vMlBxRur5TDTkOpBEq4g6QeFyEKgECMHRZhEA%3d%3d | unknown | — | — | whitelisted |
6080 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5d32607d-eea9-44fc-ac55-77800b9862a5?P1=1744954464&P2=404&P3=2&P4=ZsbhnOj5fANiWygfd4Gtz0QqnxlQ9JZWFKHXAfaJ%2fi5cfsgG88sR2ehQrsXC4r4LuH2y%2bGe9L%2fA7adjYviZioA%3d%3d | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.161:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8432 | FortiClientSetup_7.2.9_x64.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
8432 | FortiClientSetup_7.2.9_x64.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
6080 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4a14e89f-4126-4b0a-8347-8c40c8e643a4?P1=1744954466&P2=404&P3=2&P4=CSNSlYT6zrfJ%2bijE6pyQ5x7vBwTYgrKN8aNpfx%2bNOgXCVa3AibWG0ND2C%2b70jBGMrhNuikymg8jpzzVW1QasGQ%3d%3d | unknown | — | — | whitelisted |
8636 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6080 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/cd4e6fbf-c0e9-4dc2-9e3d-7f538bc7435a?P1=1744950975&P2=404&P3=2&P4=fyxEY06hHoNVLwMJiY9DZc8w%2bPL7EzBPIMFLrLdwwQRSgN5AOjy%2fCEPXhLCf7EjO6JC4Gy1OzXvmWZgEQ3IL%2bg%3d%3d | unknown | — | — | whitelisted |
6080 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4a14e89f-4126-4b0a-8347-8c40c8e643a4?P1=1744954466&P2=404&P3=2&P4=CSNSlYT6zrfJ%2bijE6pyQ5x7vBwTYgrKN8aNpfx%2bNOgXCVa3AibWG0ND2C%2b70jBGMrhNuikymg8jpzzVW1QasGQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.161:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
1272 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7364 | msedge.exe | 143.204.98.71:443 | wetransfer.com | — | — | whitelisted |
7364 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7364 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7364 | msedge.exe | 18.66.147.26:443 | we.tl | AMAZON-02 | US | whitelisted |
7364 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
we.tl |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
wetransfer.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7364 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (wetransfer .com) |
7364 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (wetransfer .com) |
7364 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (wetransfer .com) |
7364 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7364 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7364 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7364 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7364 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (wetransfer .com) |
7364 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (wetransfer .com) |
7364 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (wetransfer .com) |
Process | Message |
|---|---|
FctSecSvr.exe | {FCT}"C:\Program Files\Fortinet\FortiClient\FctSecSvr.exe"
|
FctSecSvr.exe | {FCT}C:\Program Files\Fortinet\FortiClient\FctSecSvr.exe
|
FctSecSvr.exe | {FCT}WscRegisterAvProduct(), Register() returned 0x0, err=2, bstrRemediationExePath=C:\Program Files\Fortinet\FortiClient\FortiClientConsole.exe, strDisplayName=FortiClient
|