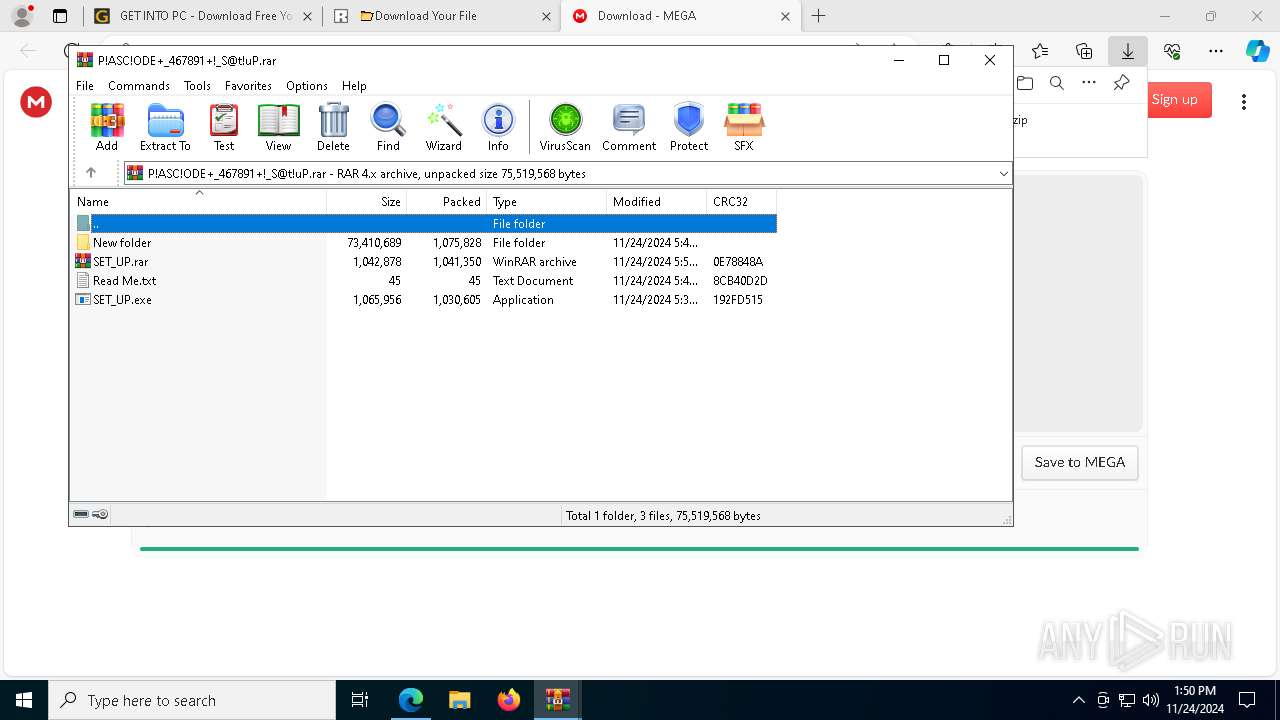
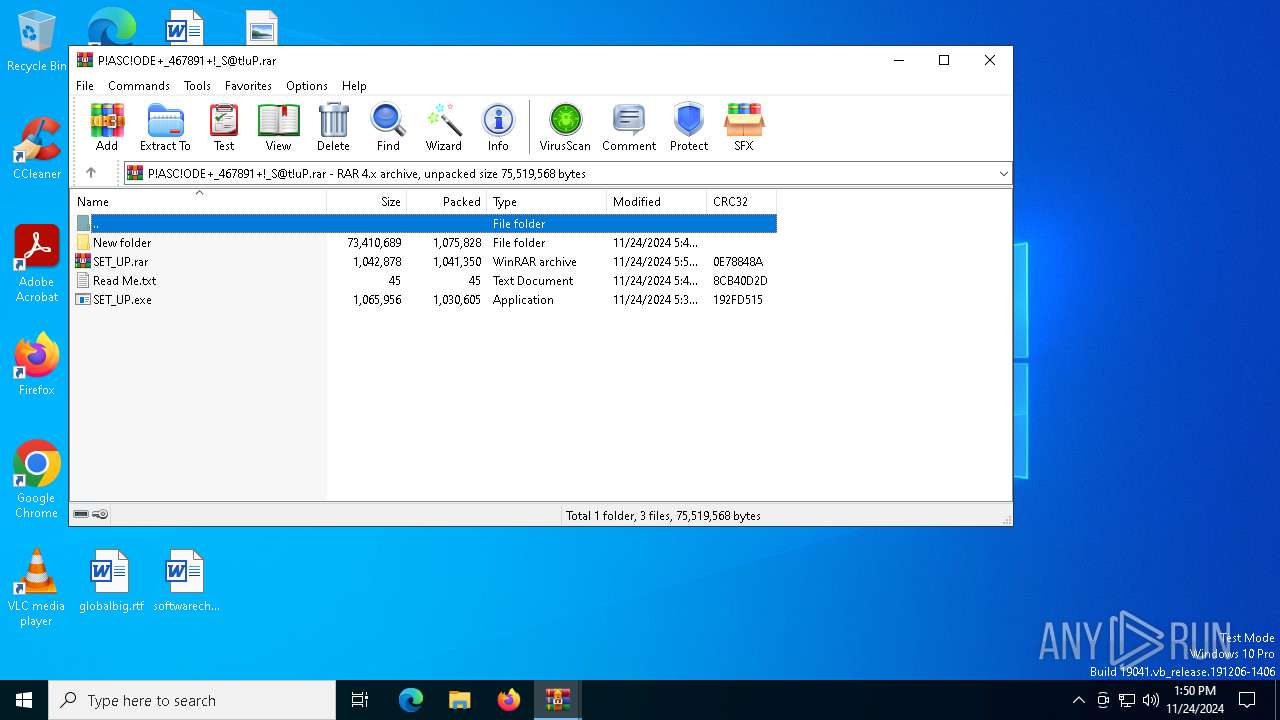
| URL: | https://kuyhaa-u.info/after-verification-click-go-to-download-page/ |
| Full analysis: | https://app.any.run/tasks/a352f3d7-1ae7-498b-b41e-20a5ec7f3925 |
| Verdict: | Malicious activity |
| Analysis date: | November 24, 2024, 13:49:42 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 44D77F9B9C9B21D0BBA42427FA88E674 |
| SHA1: | C6820BD225481206E34C586F4FD812377C59A2F6 |
| SHA256: | 69EA2317463C7DED122515D55C1A00E7393B955AE6655AB9DA63150051A75921 |
| SSDEEP: | 3:N8VVGLYZ+aeTTXJmVECv:2/tZ0Tc |
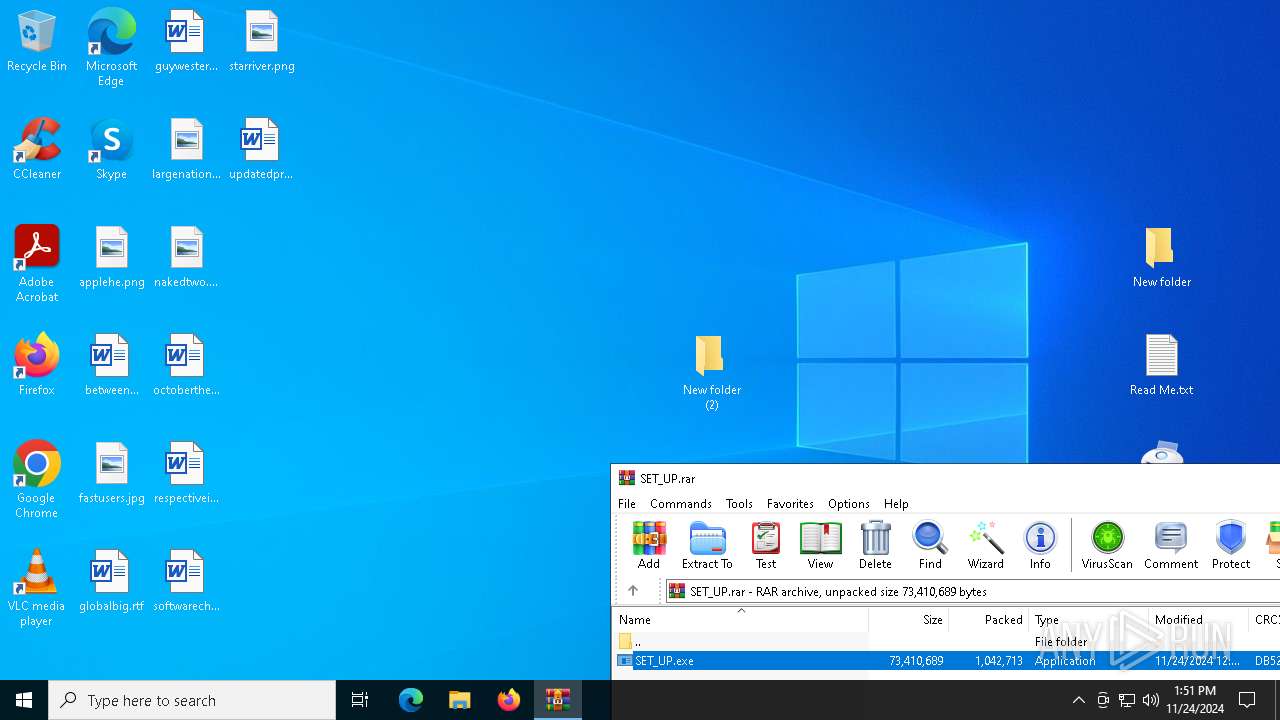
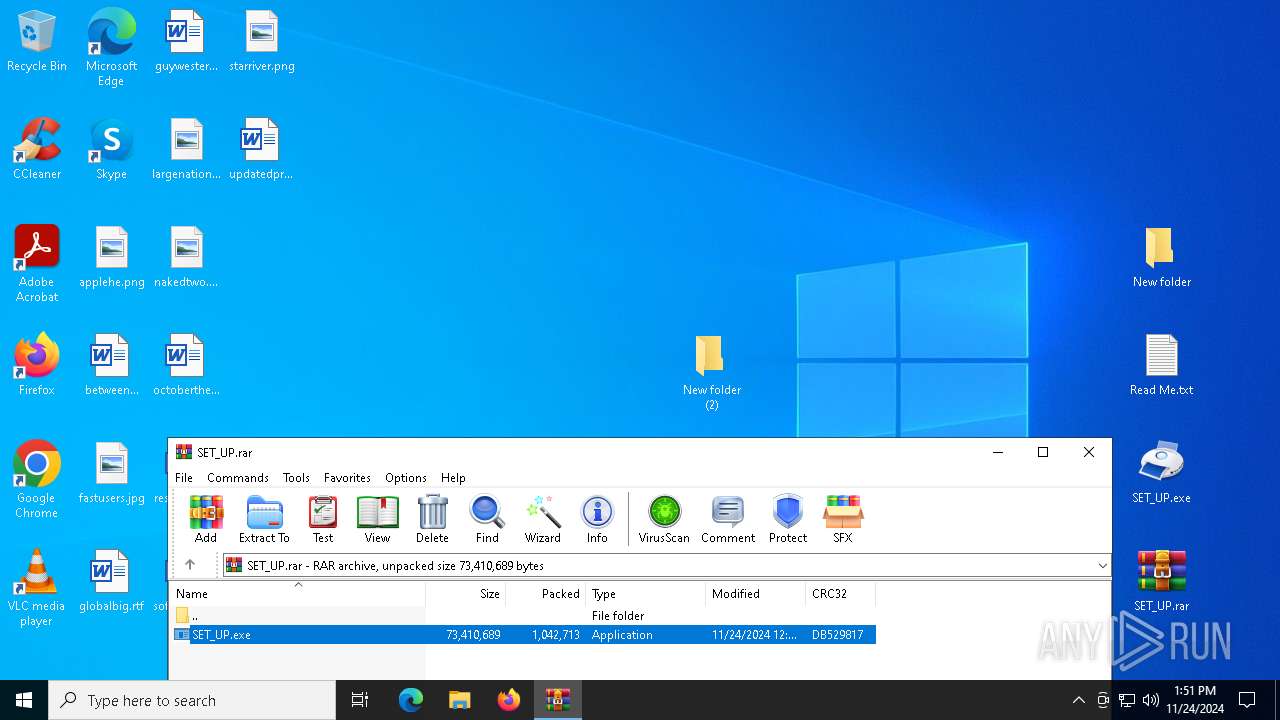
MALICIOUS
Executing a file with an untrusted certificate
- SET_UP.exe (PID: 6456)
- SET_UP.exe (PID: 1544)
- VCDDaemon.exe (PID: 440)
Bypass execution policy to execute commands
- powershell.exe (PID: 3768)
- powershell.exe (PID: 3080)
- powershell.exe (PID: 6712)
- powershell.exe (PID: 4360)
- powershell.exe (PID: 6804)
- powershell.exe (PID: 8004)
AutoIt loader has been detected (YARA)
- Hunt.com (PID: 7172)
- Hunt.com (PID: 6876)
Changes powershell execution policy (Bypass)
- Hunt.com (PID: 7172)
- Hunt.com (PID: 6876)
Known privilege escalation attack
- dllhost.exe (PID: 6484)
SUSPICIOUS
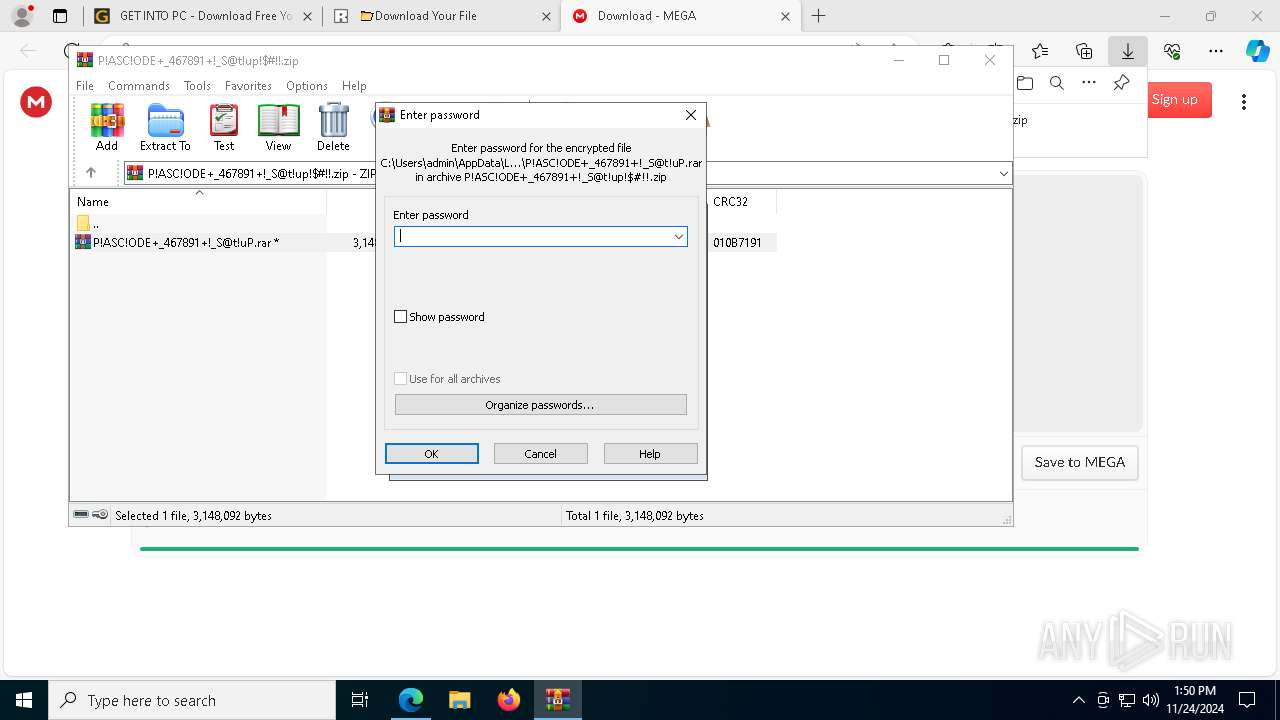
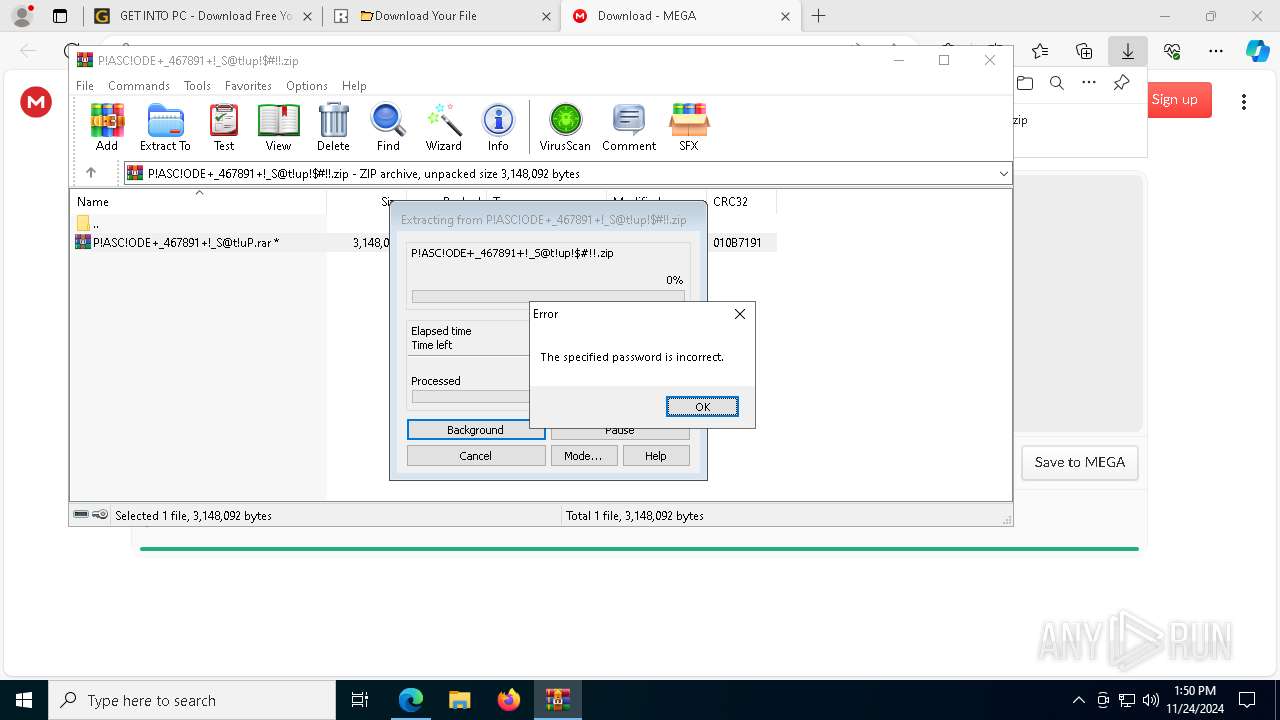
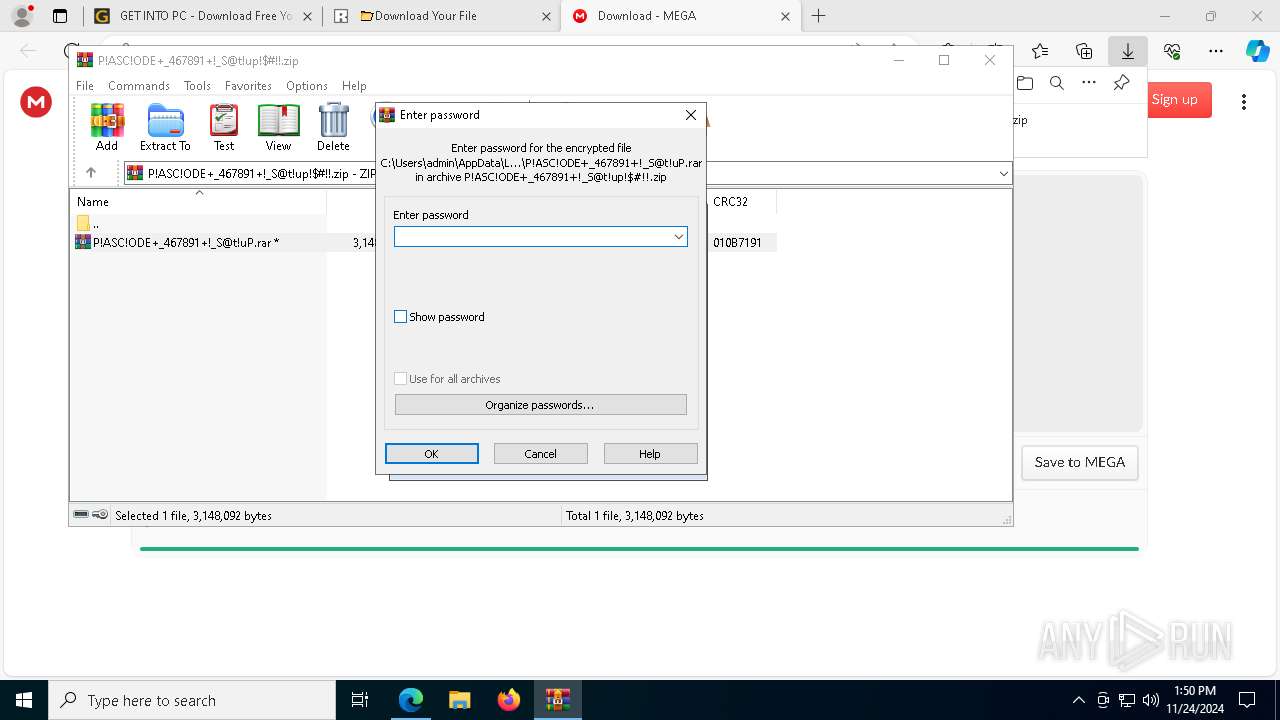
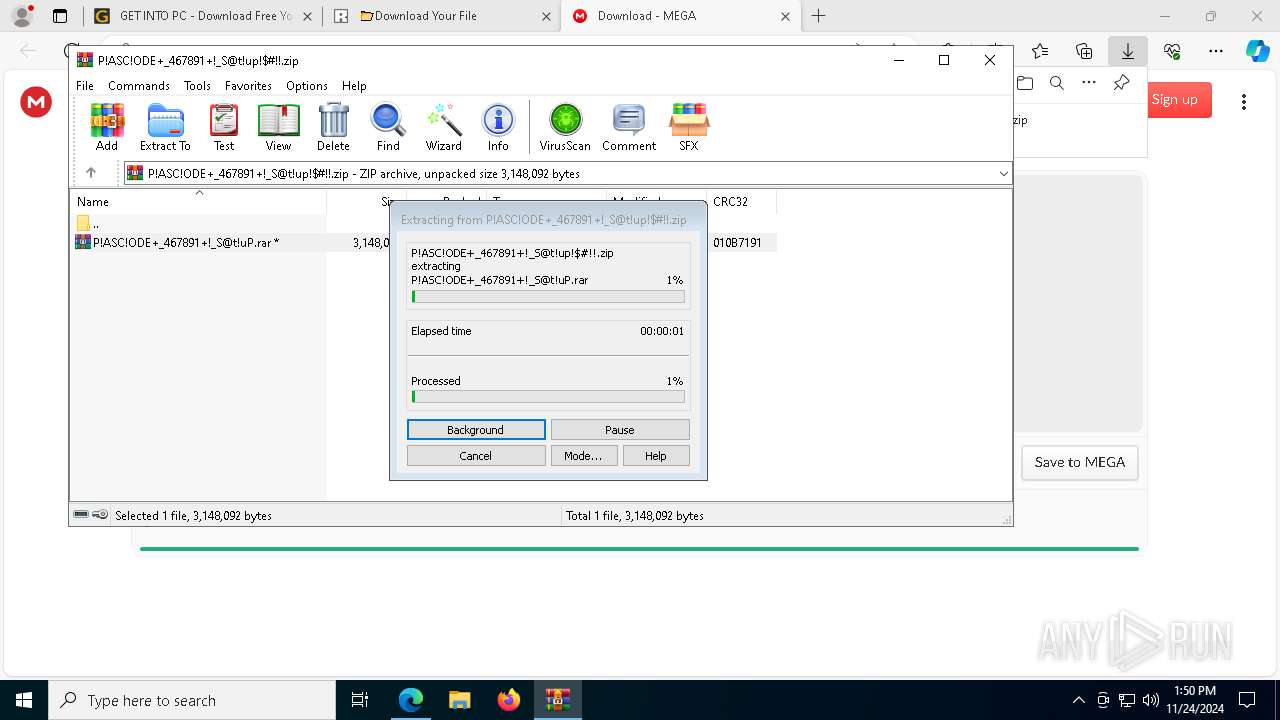
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7516)
Application launched itself
- WinRAR.exe (PID: 7516)
- cmd.exe (PID: 3820)
- cmd.exe (PID: 4388)
Starts application with an unusual extension
- cmd.exe (PID: 3820)
- cmd.exe (PID: 4388)
- VCDDaemon.exe (PID: 6368)
- VCDDaemon.exe (PID: 3628)
- VCDDaemon.exe (PID: 5316)
- VCDDaemon.exe (PID: 4724)
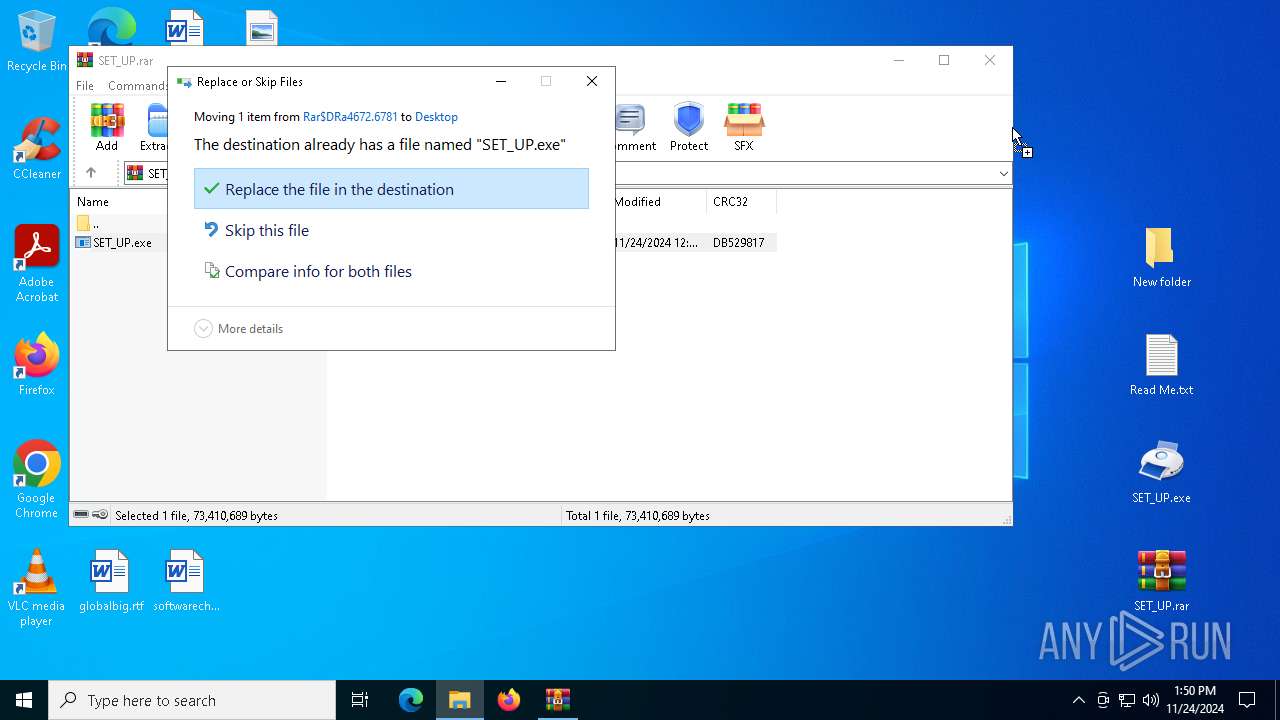
Executable content was dropped or overwritten
- cmd.exe (PID: 3820)
- SET_UP.exe (PID: 6456)
- powershell.exe (PID: 6712)
- powershell.exe (PID: 8004)
- VCDDaemon.exe (PID: 440)
The executable file from the user directory is run by the CMD process
- Hunt.com (PID: 7172)
- Hunt.com (PID: 6876)
Starts the AutoIt3 executable file
- cmd.exe (PID: 3820)
- cmd.exe (PID: 4388)
Executing commands from ".cmd" file
- SET_UP.exe (PID: 1544)
- SET_UP.exe (PID: 6456)
Starts CMD.EXE for commands execution
- SET_UP.exe (PID: 1544)
- cmd.exe (PID: 4388)
- SET_UP.exe (PID: 6456)
- cmd.exe (PID: 3820)
Get information on the list of running processes
- cmd.exe (PID: 4388)
- cmd.exe (PID: 3820)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 4388)
- cmd.exe (PID: 3820)
The process executes Powershell scripts
- Hunt.com (PID: 7172)
- Hunt.com (PID: 6876)
Starts POWERSHELL.EXE for commands execution
- Hunt.com (PID: 7172)
- Hunt.com (PID: 6876)
Base64-obfuscated command line is found
- Hunt.com (PID: 7172)
- Hunt.com (PID: 6876)
BASE64 encoded PowerShell command has been detected
- Hunt.com (PID: 7172)
- Hunt.com (PID: 6876)
Process drops legitimate windows executable
- powershell.exe (PID: 8004)
- powershell.exe (PID: 6712)
The process drops C-runtime libraries
- powershell.exe (PID: 6712)
- powershell.exe (PID: 8004)
Starts itself from another location
- VCDDaemon.exe (PID: 440)
- VCDDaemon.exe (PID: 6428)
INFO
Application launched itself
- msedge.exe (PID: 5712)
- msedge.exe (PID: 7220)
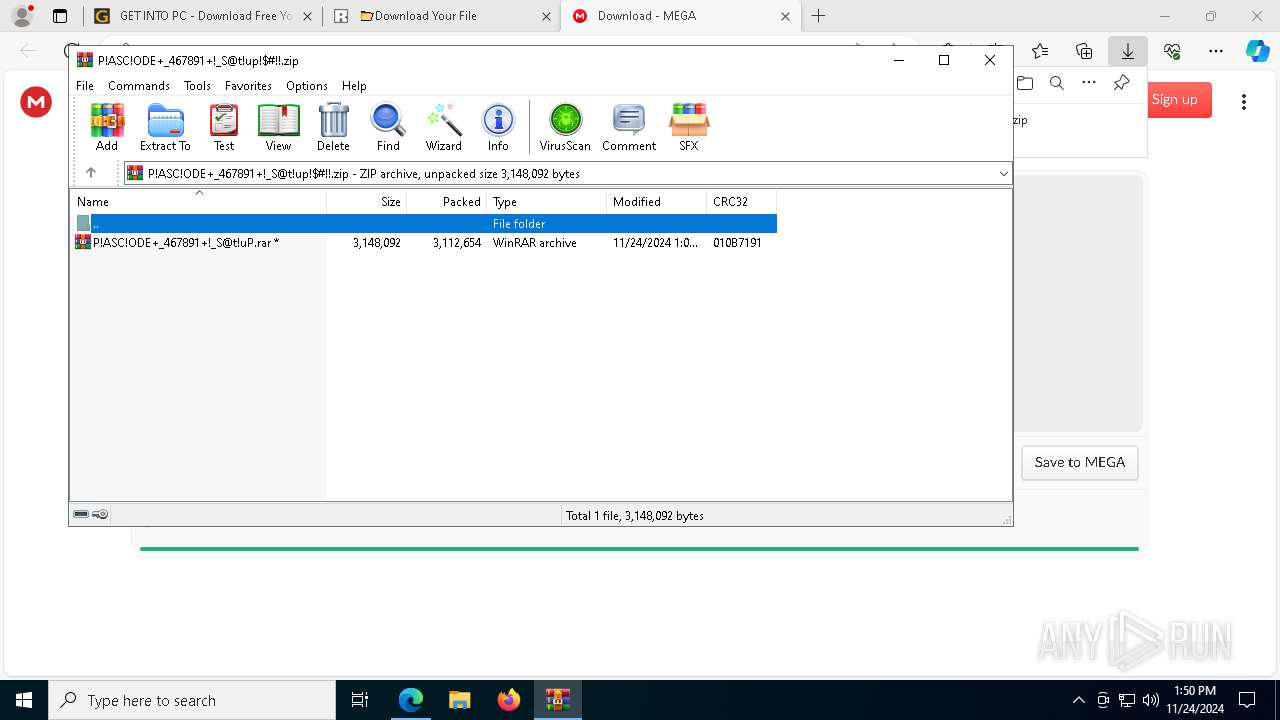
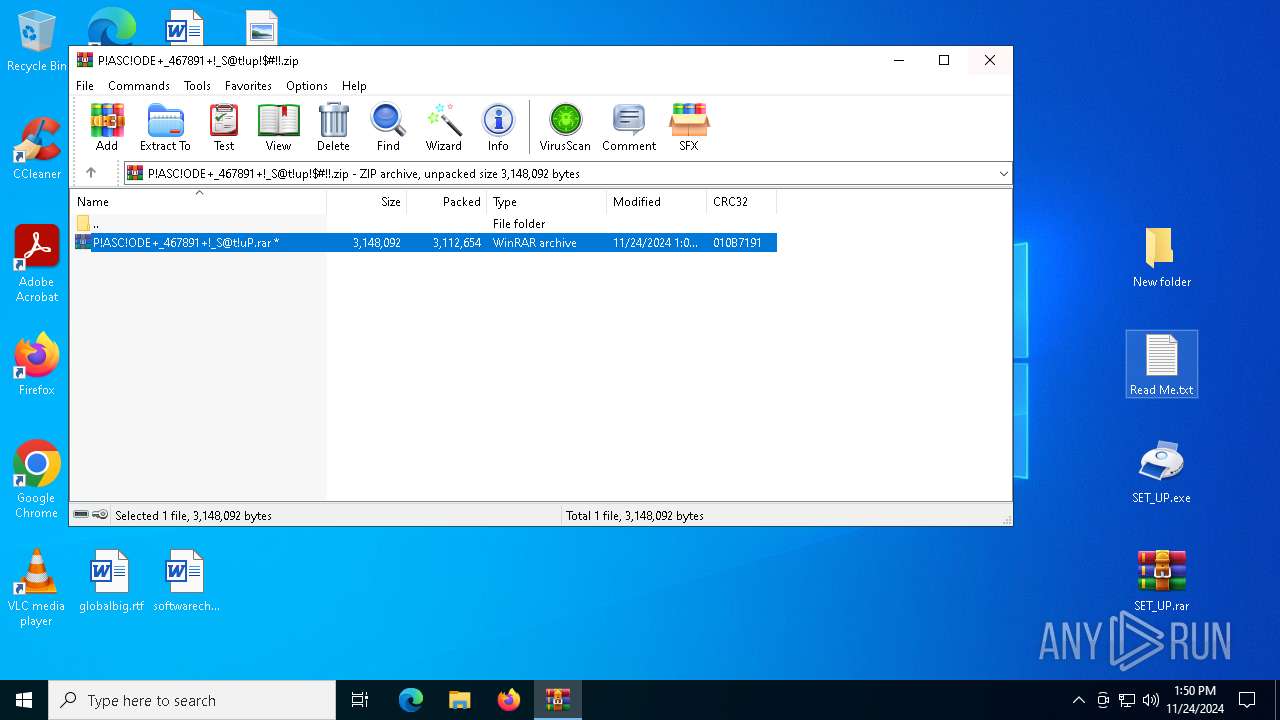
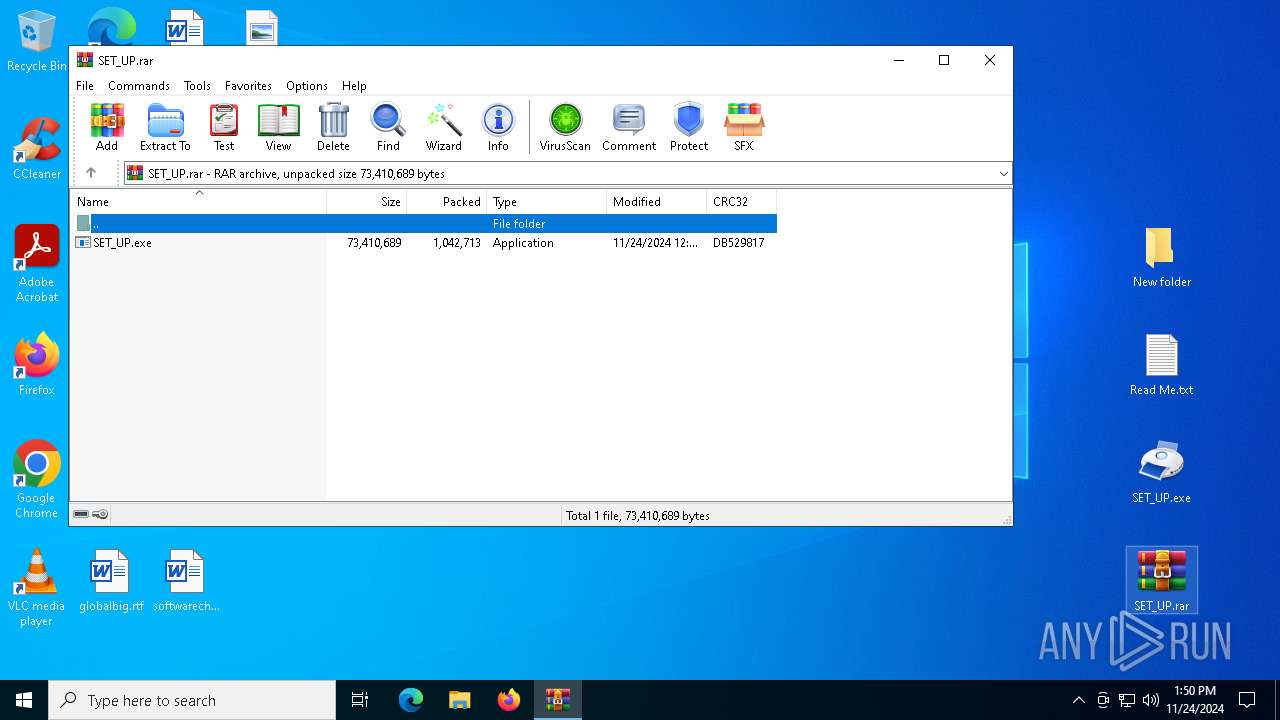
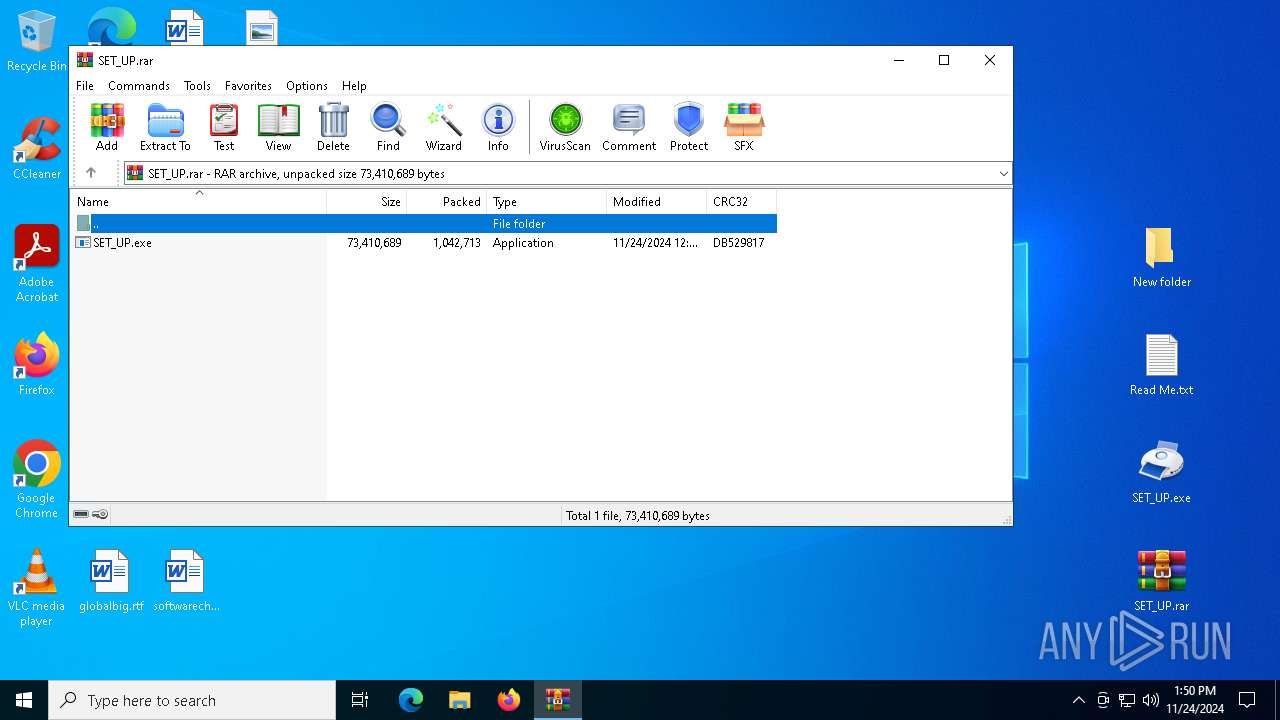
The process uses the downloaded file
- iexplore.exe (PID: 4952)
- msedge.exe (PID: 6380)
- WinRAR.exe (PID: 7516)
- msedge.exe (PID: 5712)
- WinRAR.exe (PID: 4512)
Checks supported languages
- identity_helper.exe (PID: 7156)
- identity_helper.exe (PID: 7148)
Reads the computer name
- identity_helper.exe (PID: 7156)
- identity_helper.exe (PID: 7148)
Reads Environment values
- identity_helper.exe (PID: 7156)
- identity_helper.exe (PID: 7148)
Reads Microsoft Office registry keys
- msedge.exe (PID: 5712)
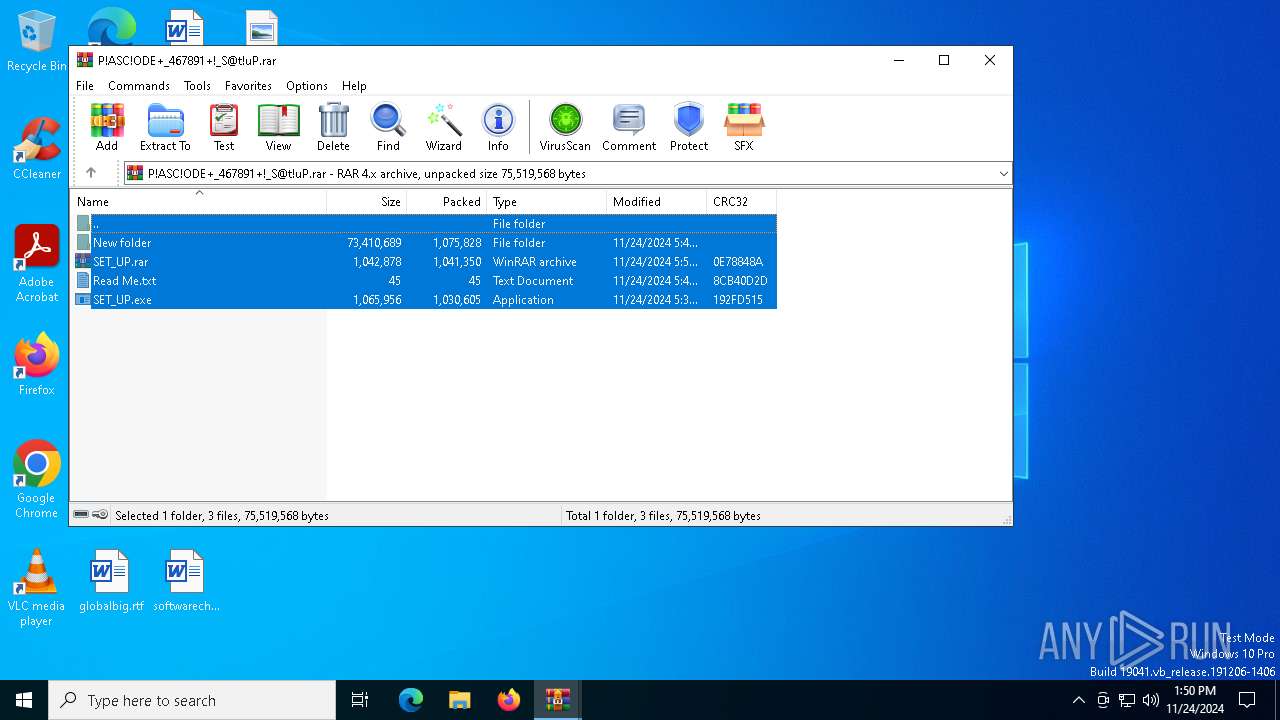
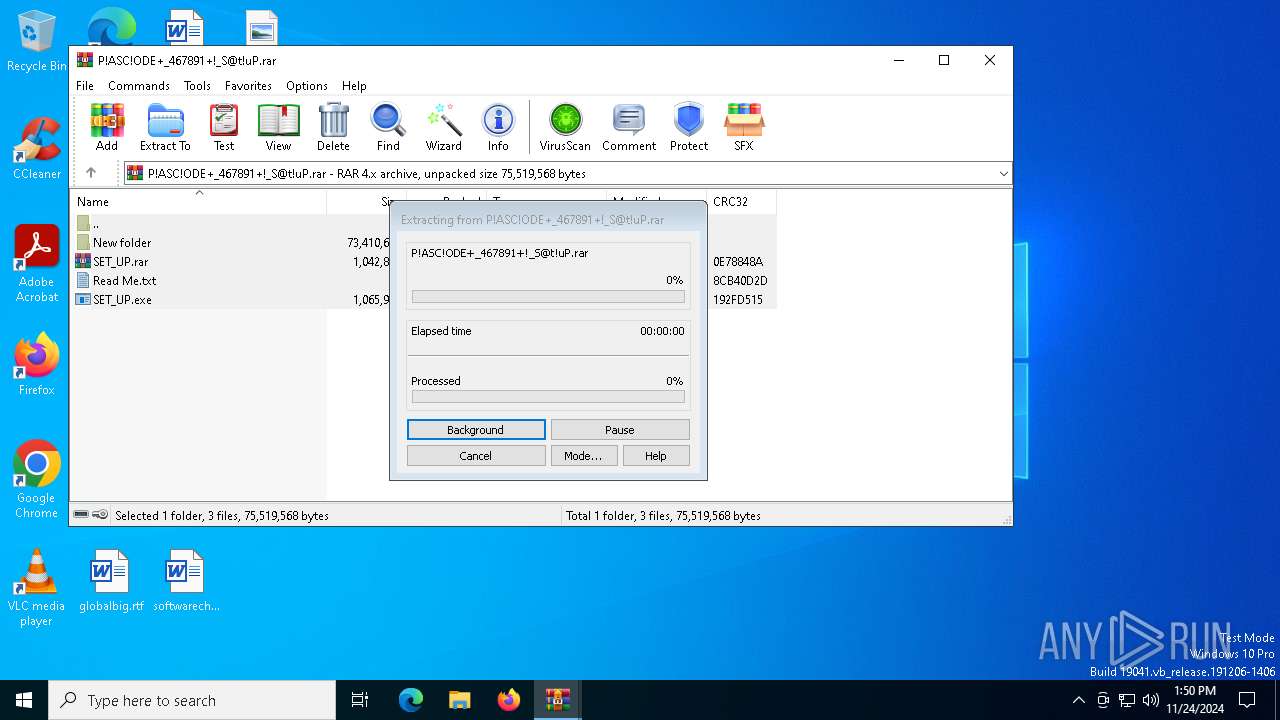
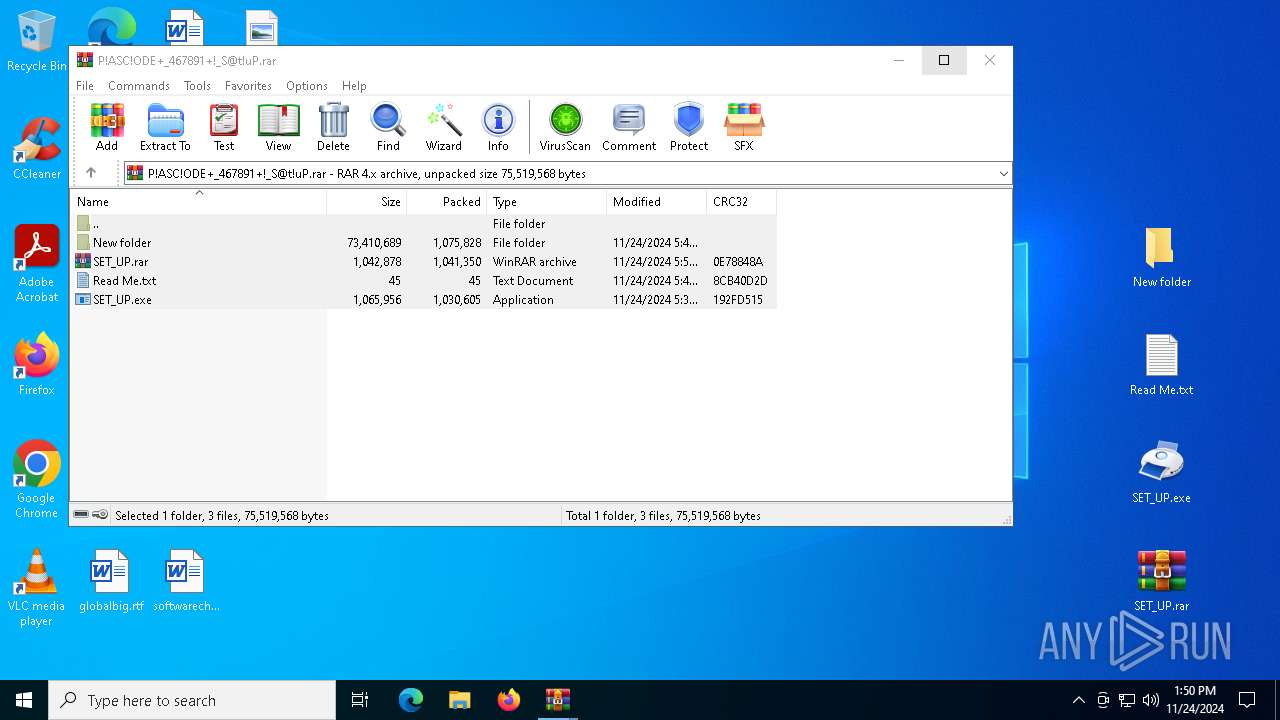
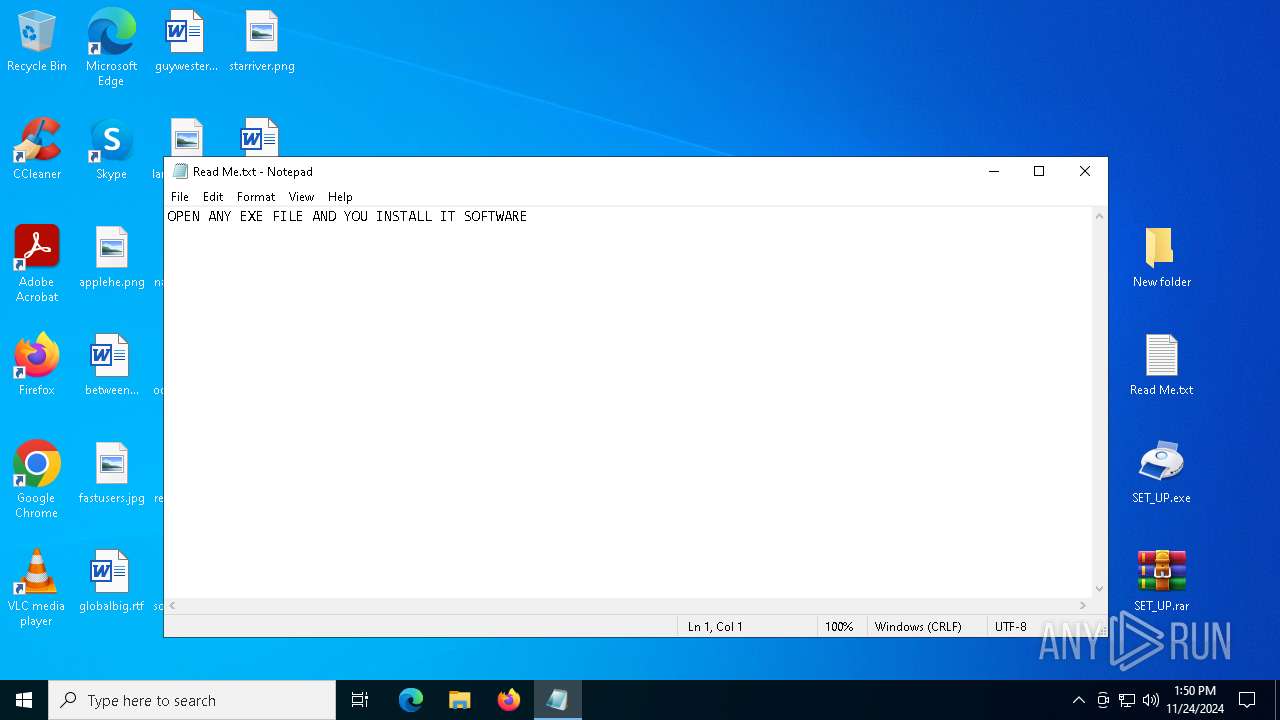
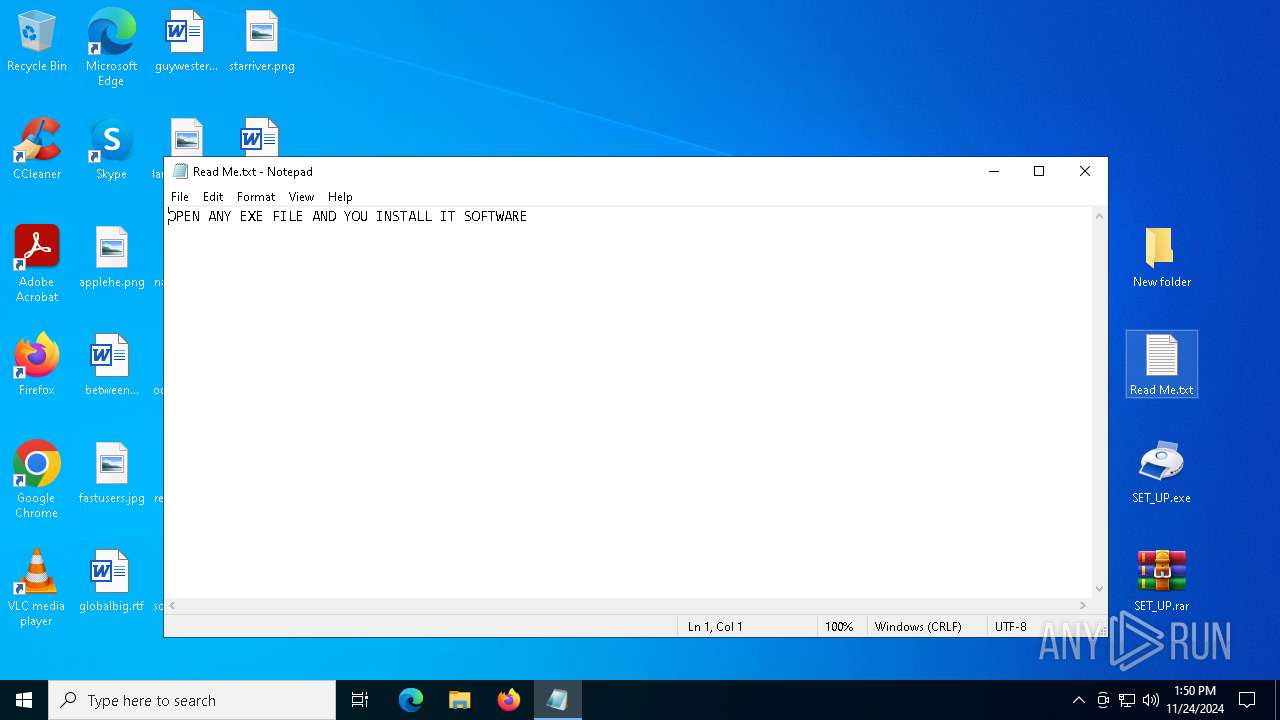
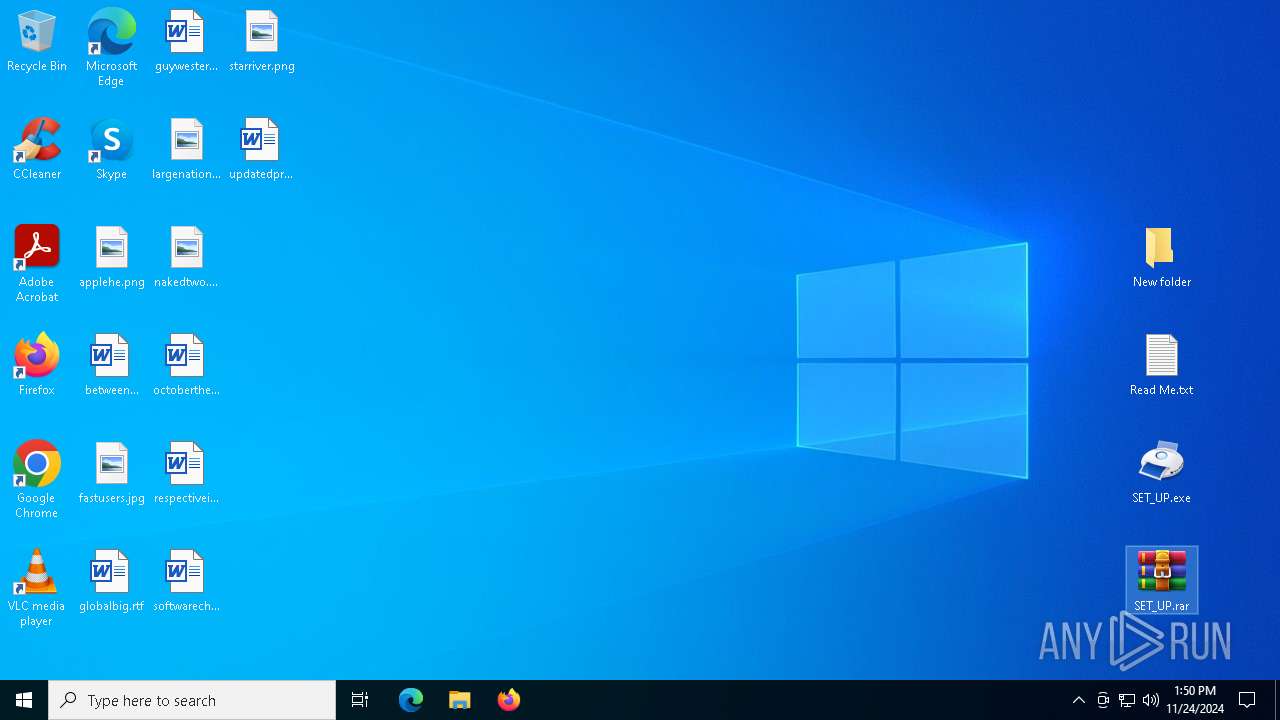
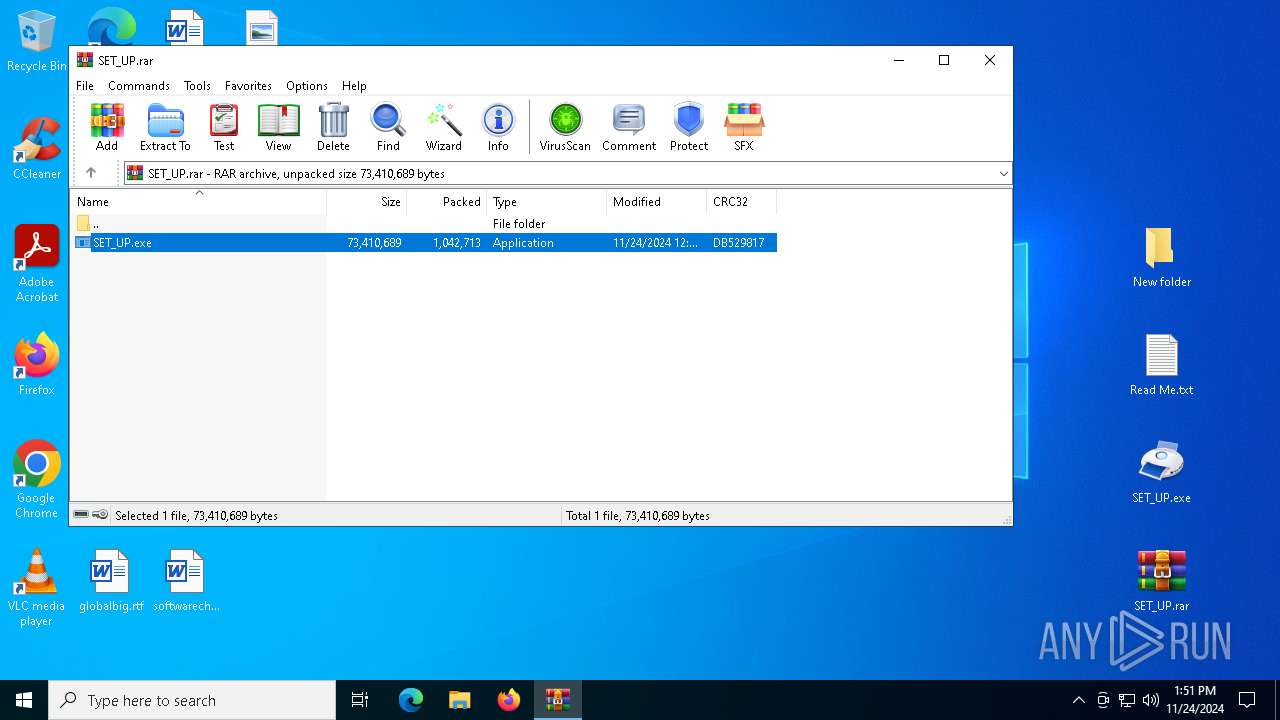
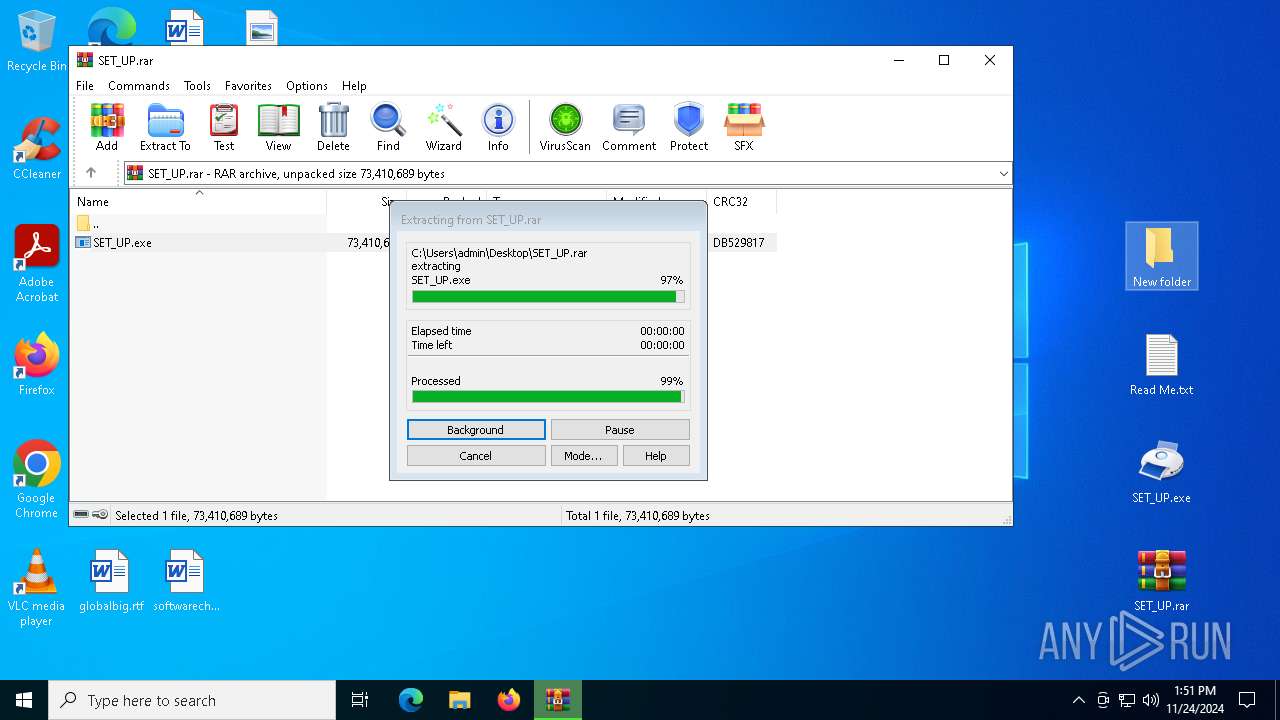
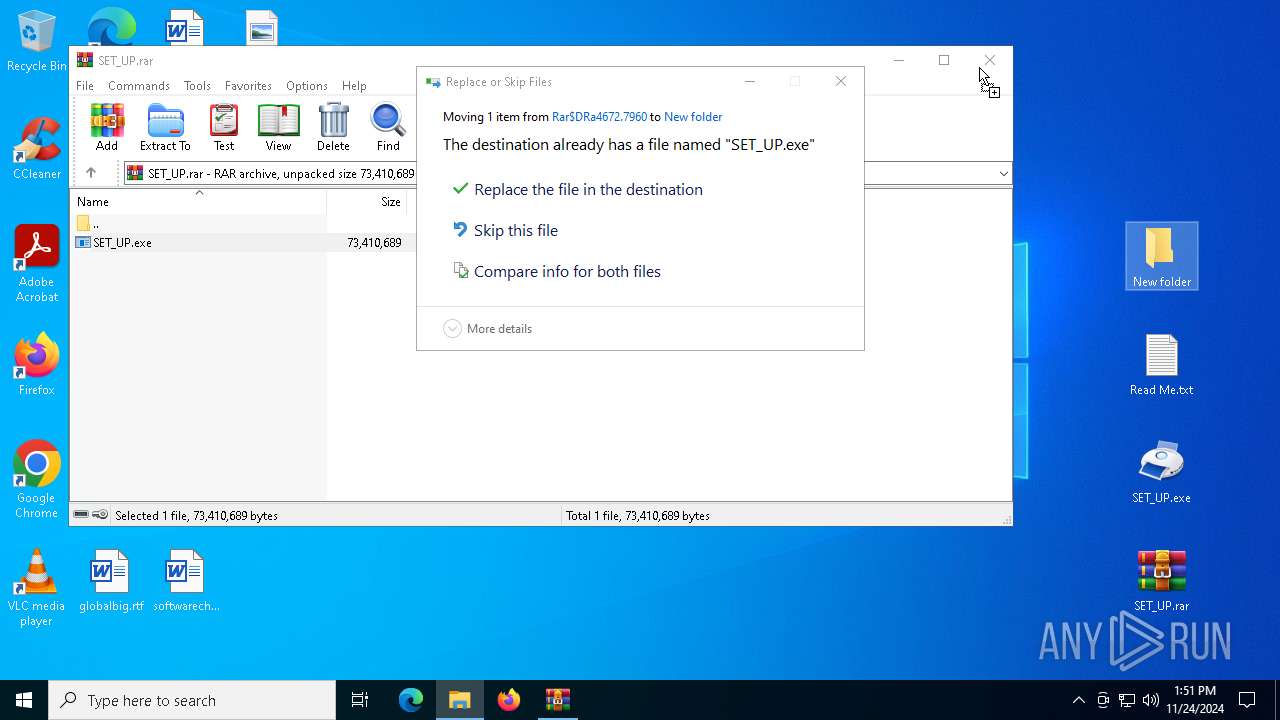
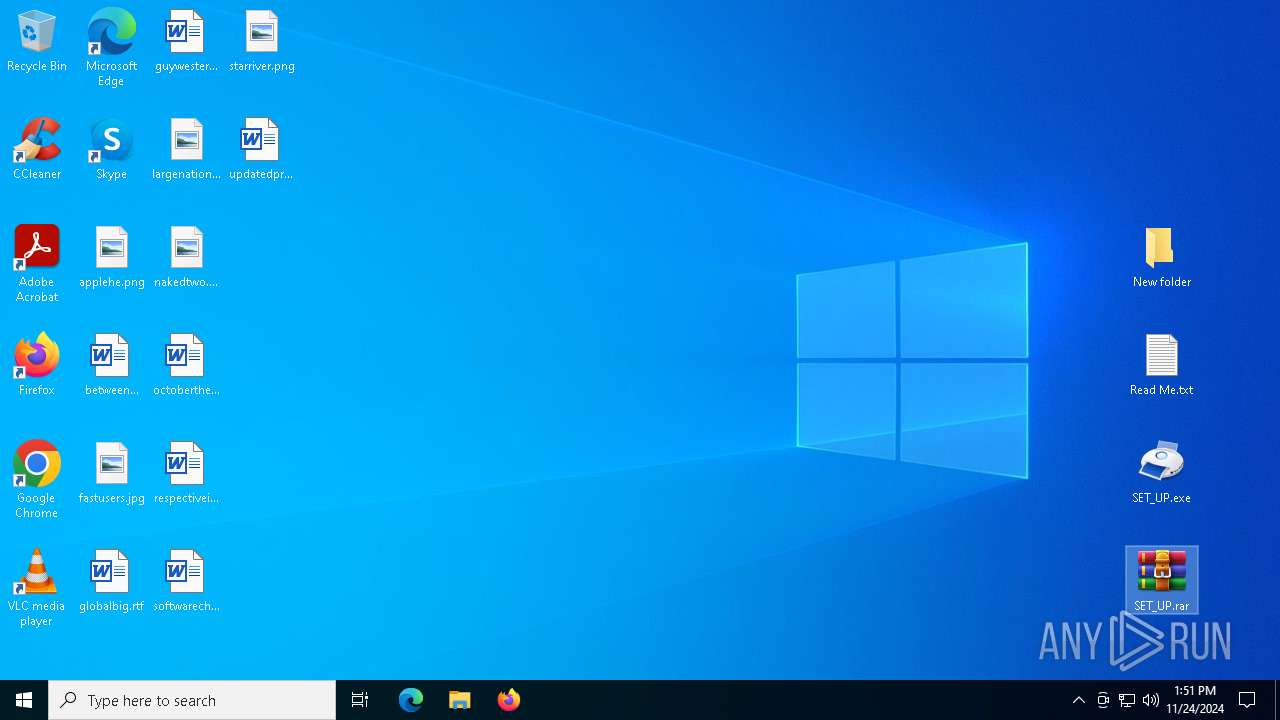
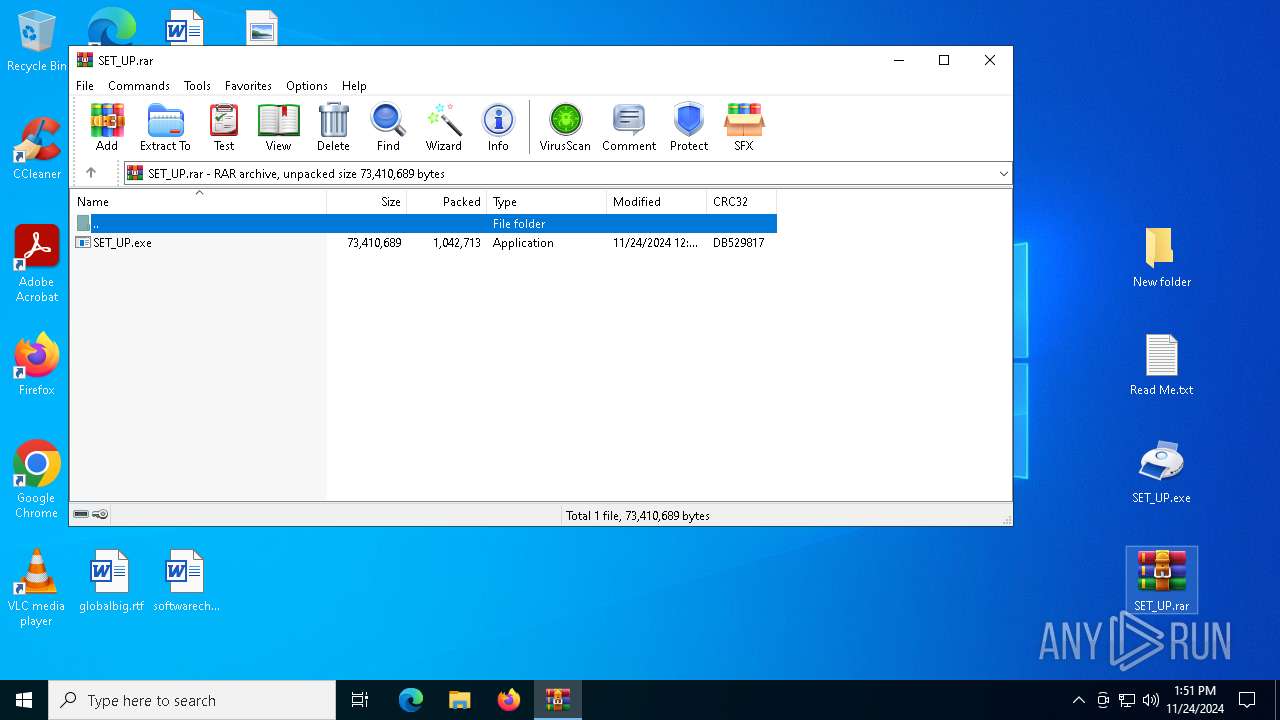
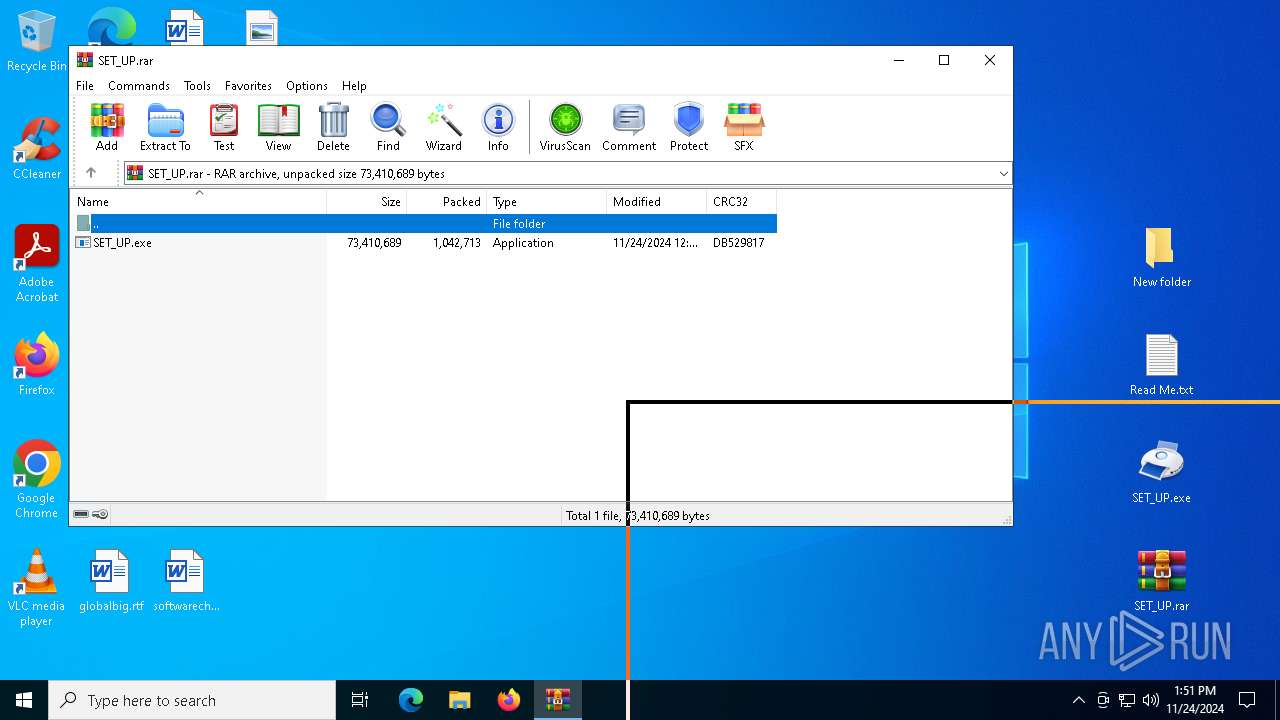
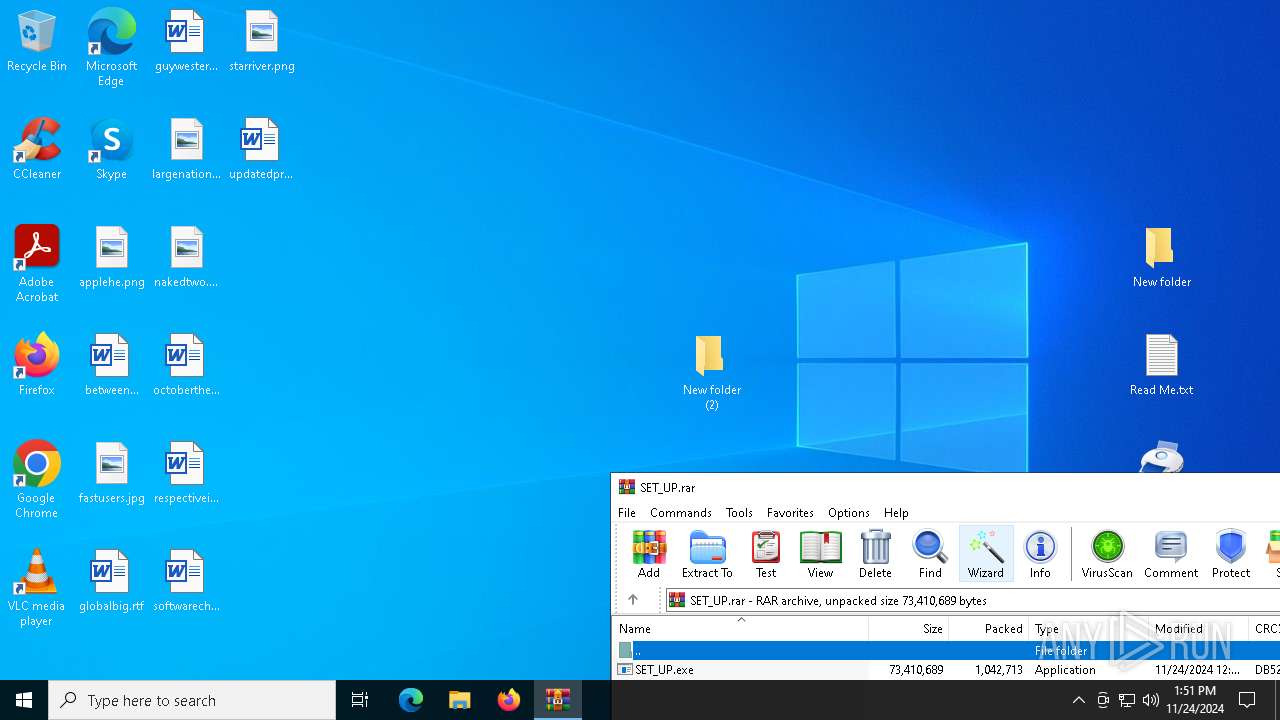
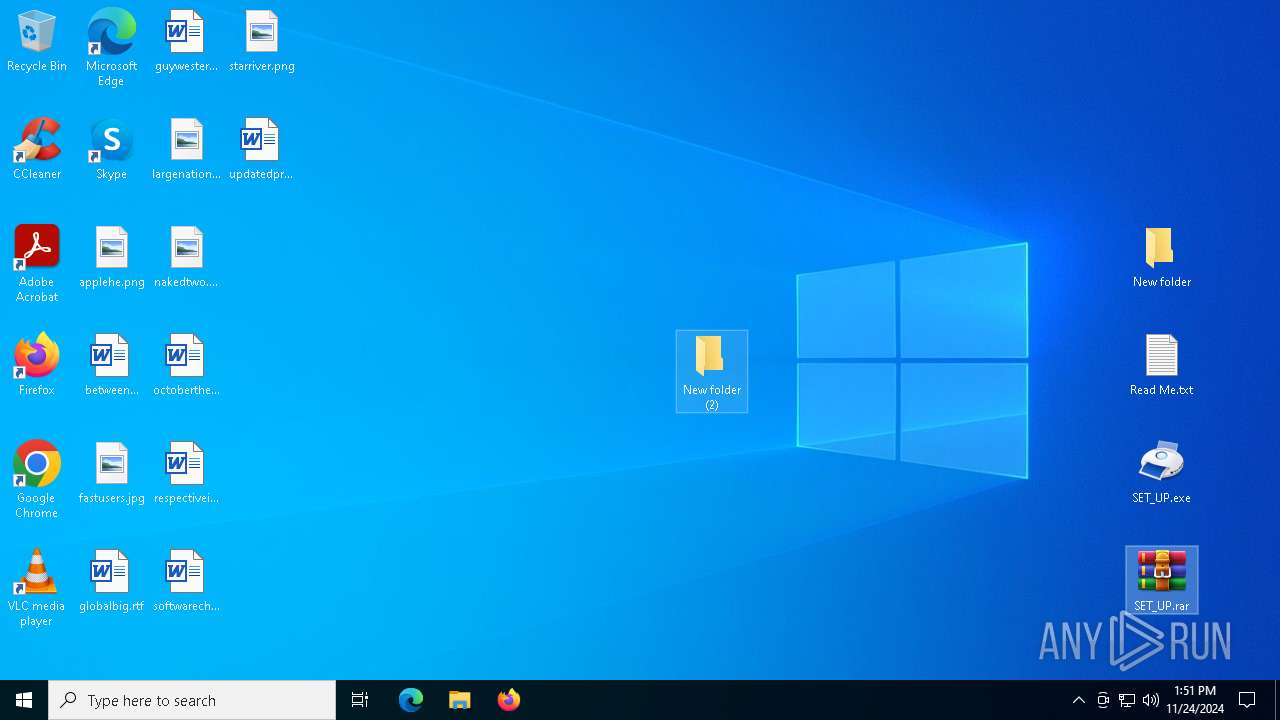
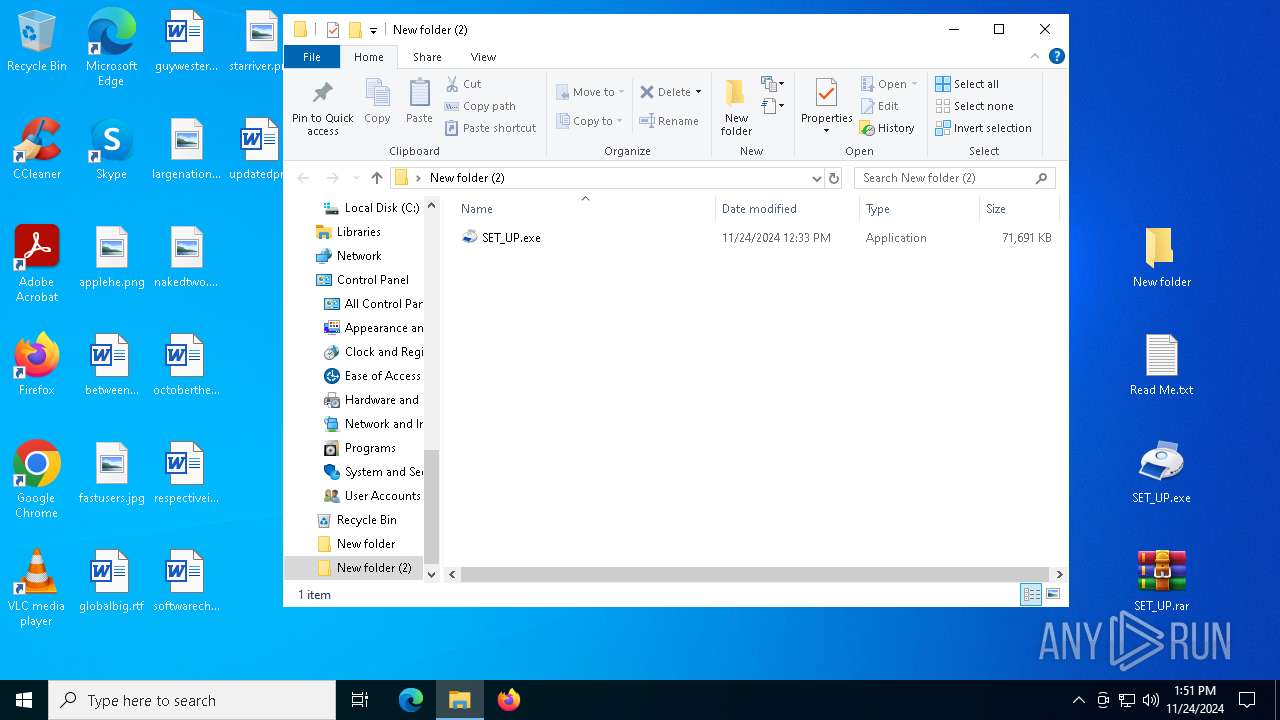
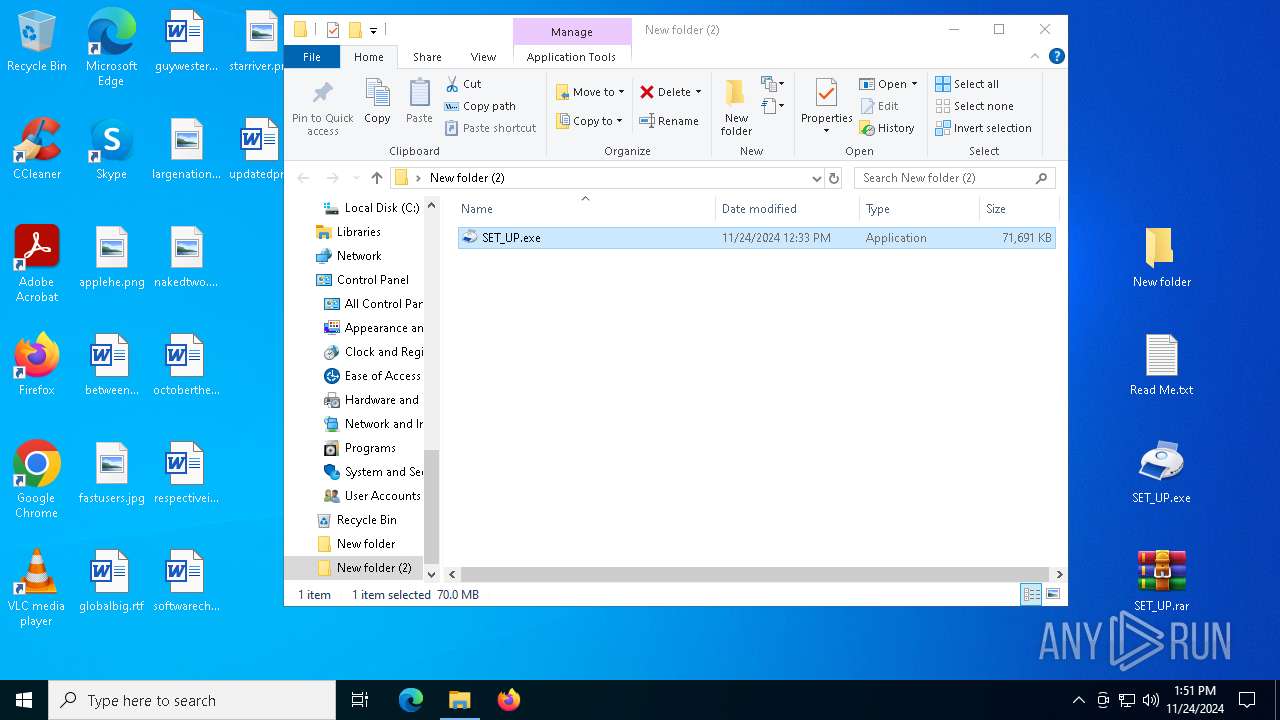
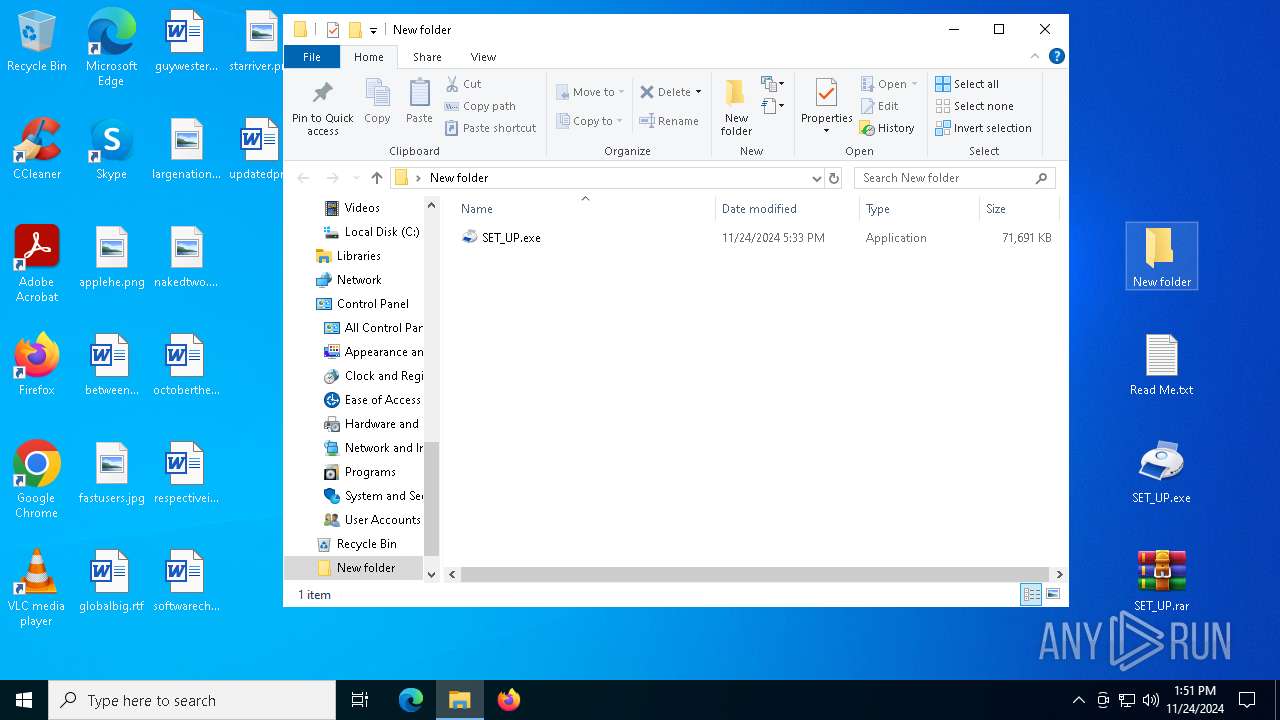
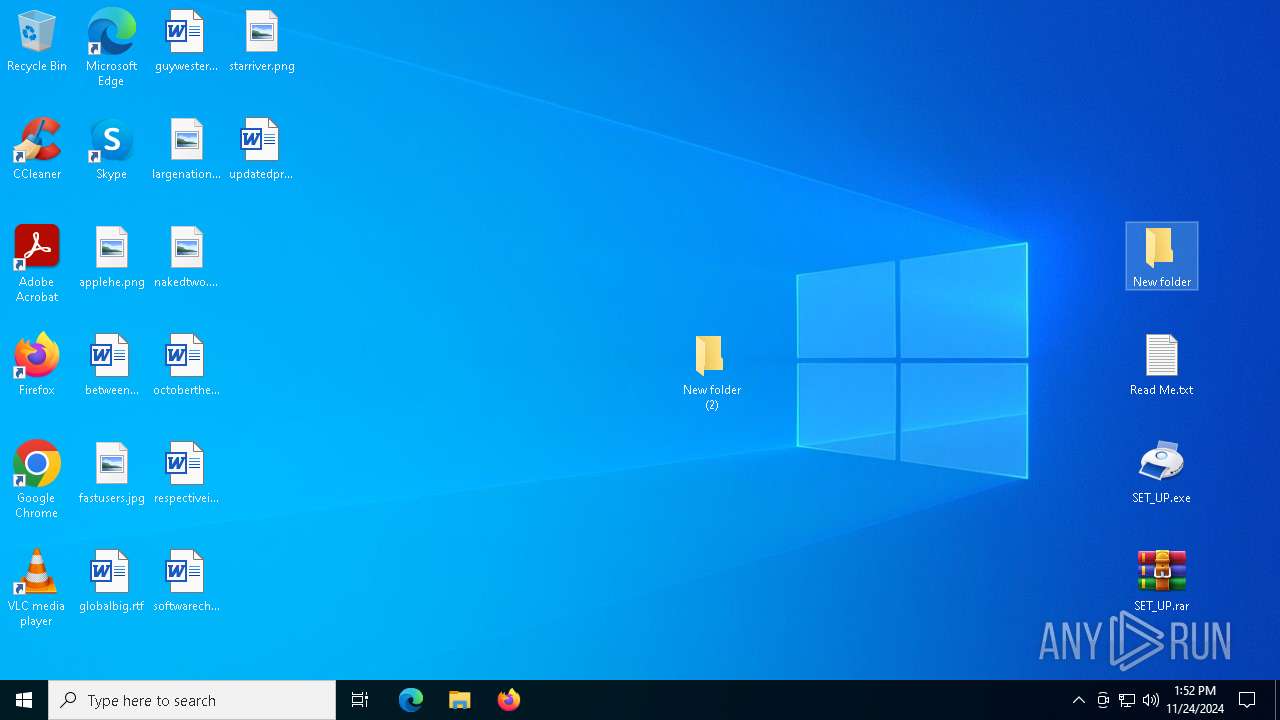
Manual execution by a user
- SET_UP.exe (PID: 6456)
- notepad.exe (PID: 1076)
- notepad.exe (PID: 6600)
- WinRAR.exe (PID: 4672)
- WinRAR.exe (PID: 7684)
- SET_UP.exe (PID: 1544)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4512)
- msedge.exe (PID: 6324)
Reads security settings of Internet Explorer
- notepad.exe (PID: 1076)
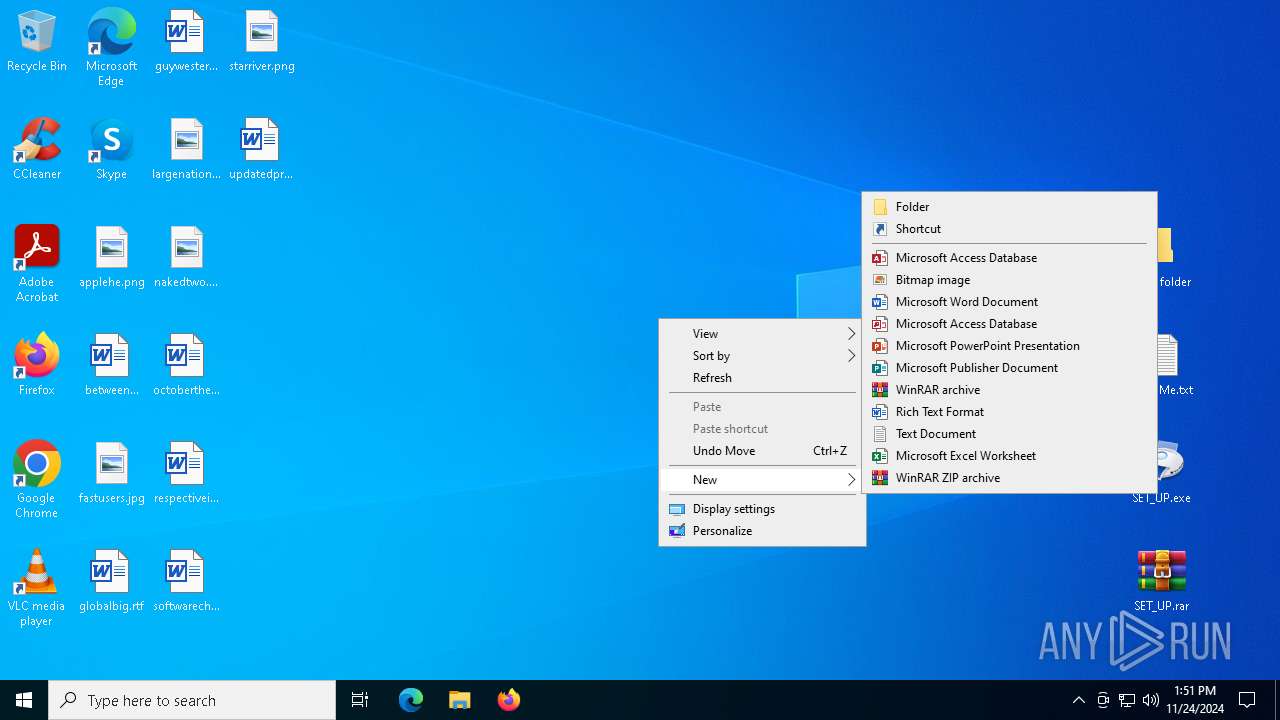
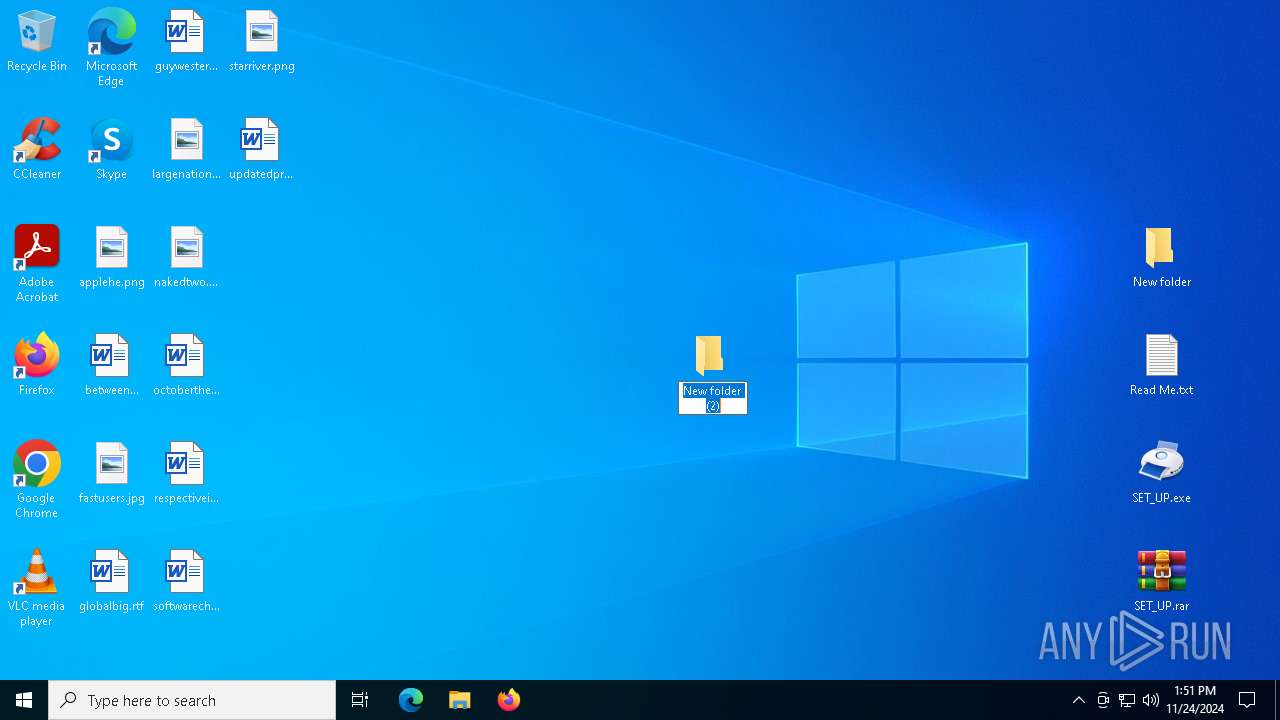
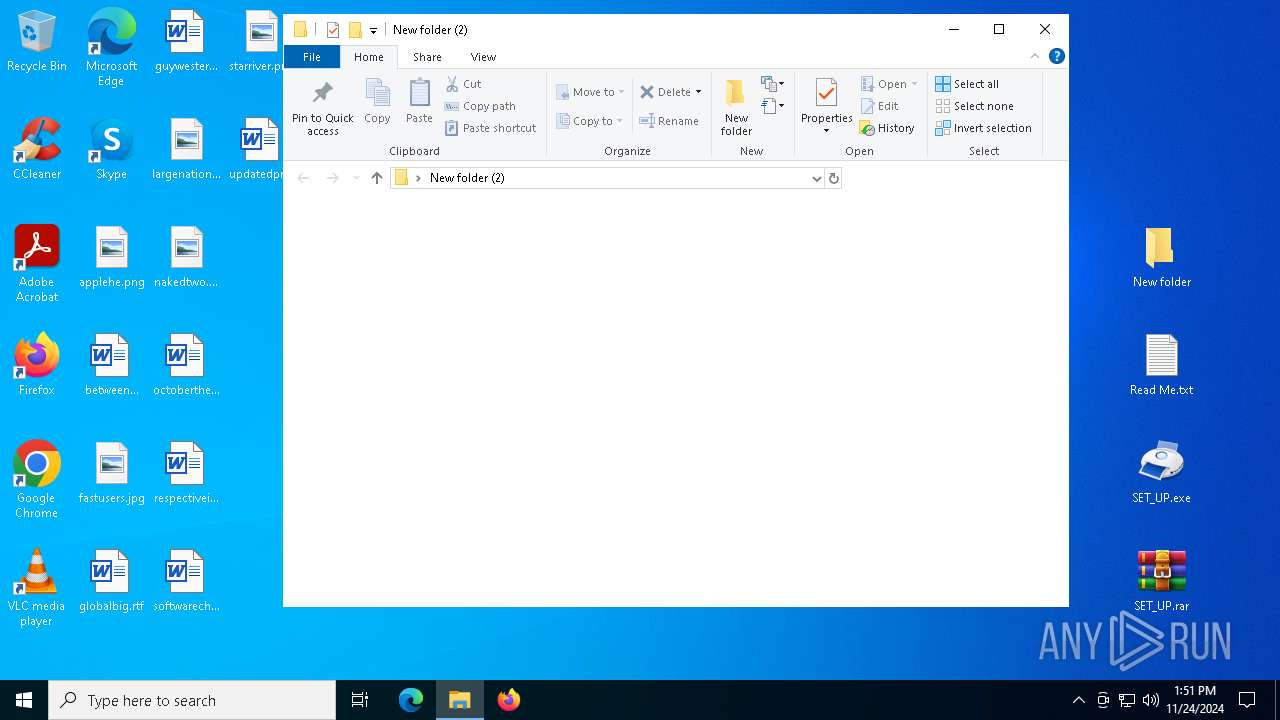
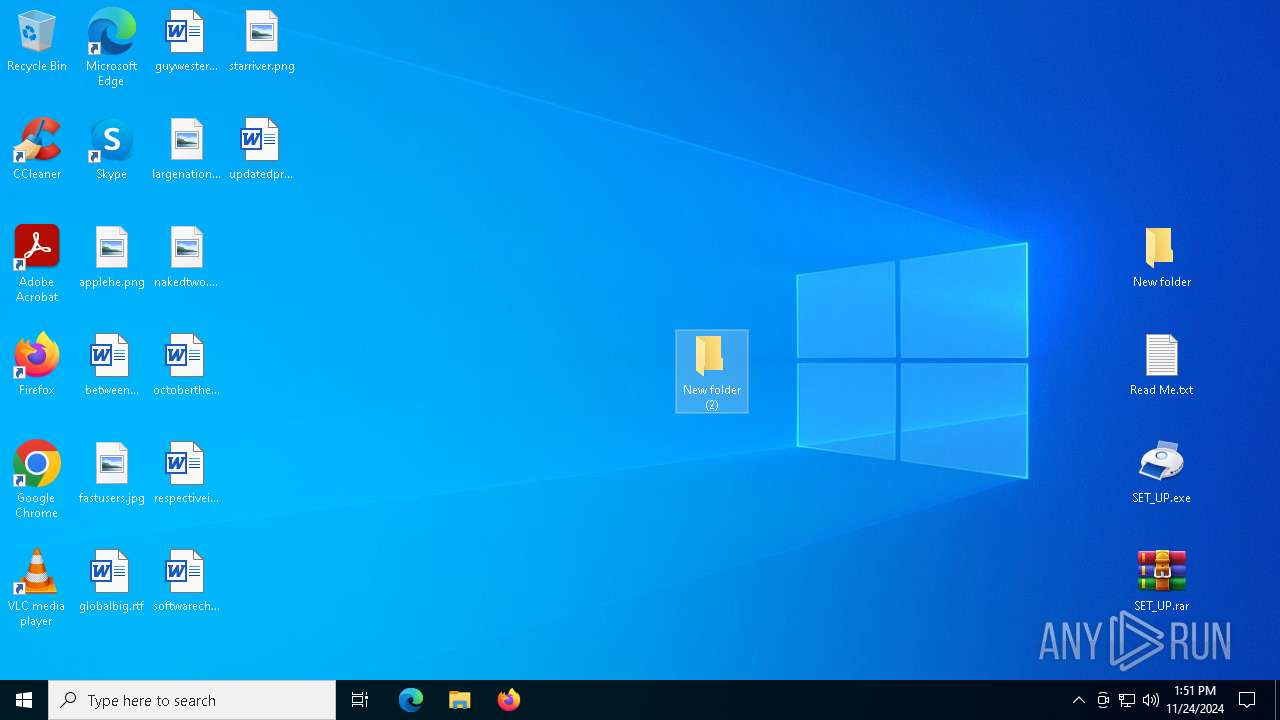
Creates a new folder
- cmd.exe (PID: 1520)
- cmd.exe (PID: 7252)
Found Base64 encoded network access via PowerShell (YARA)
- powershell.exe (PID: 6712)
- powershell.exe (PID: 8004)
Found Base64 encoded file access via PowerShell (YARA)
- powershell.exe (PID: 6712)
- powershell.exe (PID: 8004)
The executable file from the user directory is run by the Powershell process
- VCDDaemon.exe (PID: 440)
- VCDDaemon.exe (PID: 6428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
265
Monitored processes
127
Malicious processes
13
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 424 | C:\WINDOWS\SysWOW64\explorer.exe | C:\Windows\SysWOW64\explorer.exe | — | more.com | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 0 Version: 10.0.19041.3758 (WinBuild.160101.0800) | |||||||||||||||
| 440 | "C:\Users\admin\AppData\Local\b4fe9f24-5ea6-4bed-9cea-cd4da33ee23a\VCDDaemon.exe" | C:\Users\admin\AppData\Local\b4fe9f24-5ea6-4bed-9cea-cd4da33ee23a\VCDDaemon.exe | powershell.exe | ||||||||||||
User: admin Company: Elaborate Bytes AG Integrity Level: MEDIUM Description: Virtual CloneDrive Daemon Exit code: 0 Version: 5, 4, 5, 1 | |||||||||||||||
| 556 | choice /d y /t 5 | C:\Windows\SysWOW64\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 936 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | more.com | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1076 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Read Me.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1296 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=5832 --field-trial-handle=2532,i,2566251826497089783,8055198057904601005,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1416 | C:\WINDOWS\SysWOW64\more.com | C:\Windows\SysWOW64\more.com | — | VCDDaemon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1480 | choice /d y /t 5 | C:\Windows\SysWOW64\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1520 | cmd /c md 714312 | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1544 | "C:\Users\admin\Desktop\New folder (2)\SET_UP.exe" | C:\Users\admin\Desktop\New folder (2)\SET_UP.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
48 947
Read events
48 810
Write events
137
Delete events
0
Modification events
| (PID) Process: | (4952) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4952) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4952) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4952) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (4952) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (4952) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (5712) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5712) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5712) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5712) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
170
Suspicious files
531
Text files
186
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5712 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135547.TMP | — | |
MD5:— | SHA256:— | |||
| 5712 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135547.TMP | — | |
MD5:— | SHA256:— | |||
| 5712 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135547.TMP | — | |
MD5:— | SHA256:— | |||
| 5712 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5712 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5712 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5712 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135547.TMP | — | |
MD5:— | SHA256:— | |||
| 5712 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5712 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135566.TMP | — | |
MD5:— | SHA256:— | |||
| 5712 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
58
TCP/UDP connections
203
DNS requests
180
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.21.20.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4300 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4300 | svchost.exe | GET | 200 | 2.21.20.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6240 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1732462810&P2=404&P3=2&P4=RCYR0hPovjtd%2bkHT23hqA%2bvDMdtuhr1nK%2fOr6TdAQE8VSbU7qkbYGZI5yLTTIXyyYzl3JKuVS7b%2blETLZta1iA%3d%3d | unknown | — | — | whitelisted |
624 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7300 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7300 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.21.20.137:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.21.20.137:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4300 | svchost.exe | 2.21.20.137:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4300 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 104.126.37.153:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
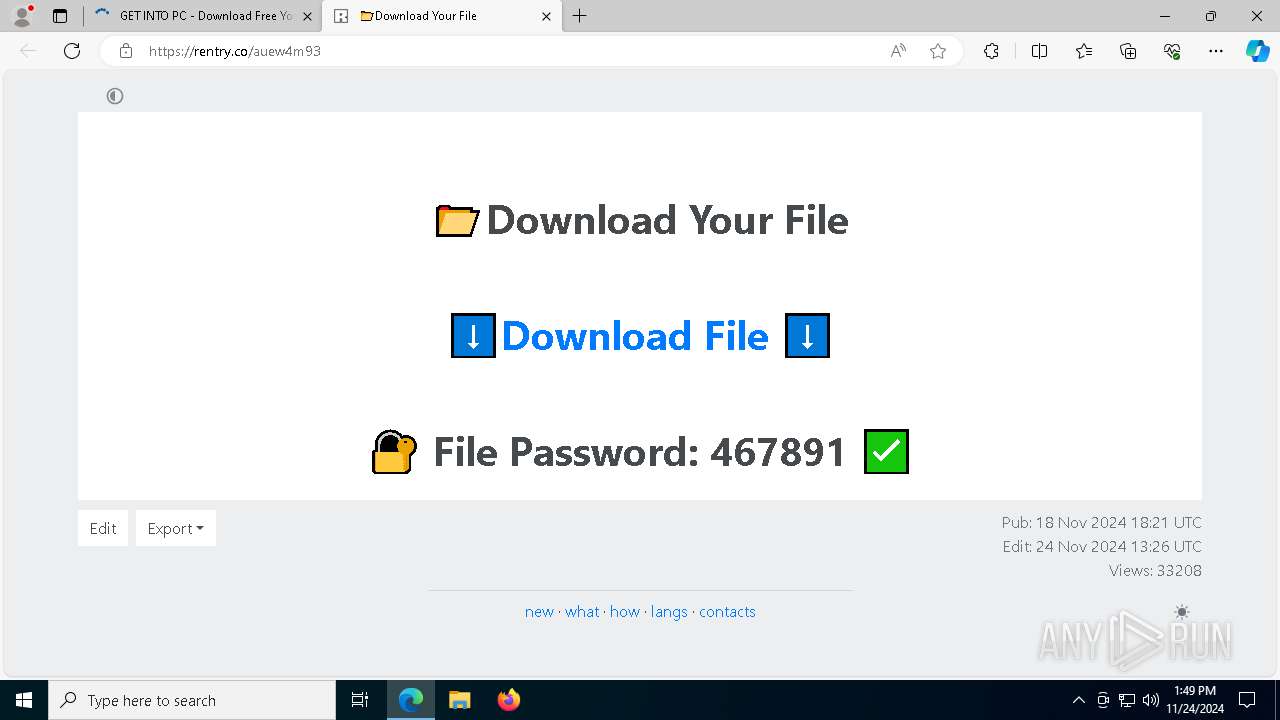
kuyhaa-u.info |
| unknown |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6176 | msedge.exe | Misc activity | ET INFO Pastebin Service Domain in DNS Lookup (rentry .co) |
6176 | msedge.exe | Misc activity | ET INFO Pastebin Service Domain in DNS Lookup (rentry .co) |
6176 | msedge.exe | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |
6176 | msedge.exe | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |
6176 | msedge.exe | Misc activity | ET INFO Pastebin Service Domain in DNS Lookup (rentry .co) |
6176 | msedge.exe | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |
6176 | msedge.exe | Misc activity | ET INFO Pastebin Service Domain in DNS Lookup (rentry .co) |
6176 | msedge.exe | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |
6176 | msedge.exe | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |
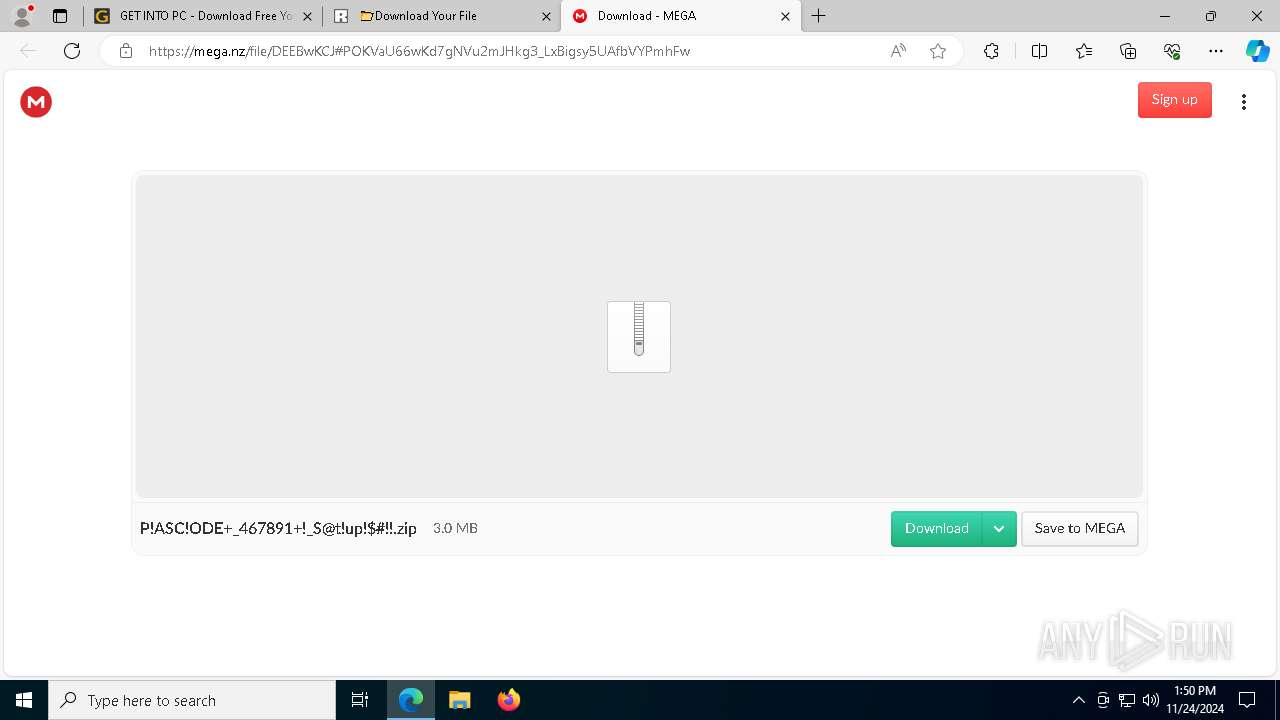
6176 | msedge.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |