| File name: | invoice_2318362983713_823931342io.pdf.exe |
| Full analysis: | https://app.any.run/tasks/471c18cc-86bb-41fc-abe8-bf0cd613eade |
| Verdict: | Malicious activity |
| Analysis date: | November 11, 2024, 13:56:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | EA039A854D20D7734C5ADD48F1A51C34 |
| SHA1: | 9615DCA4C0E46B8A39DE5428AF7DB060399230B2 |
| SHA256: | 69E966E730557FDE8FD84317CDEF1ECE00A8BB3470C0B58F3231E170168AF169 |
| SSDEEP: | 6144:tg+buboEf6ZsYxQWzMTohPdrDdkyRcpD7r:GmubXyQWQToDrDnED7r |
MALICIOUS
Runs injected code in another process
- invoice_2318362983713_823931342io.pdf.exe (PID: 3744)
- InstallFlashPlayer.exe (PID: 2828)
Application was injected by another process
- explorer.exe (PID: 1296)
- services.exe (PID: 472)
ZEROACCESS has been detected (SURICATA)
- invoice_2318362983713_823931342io.pdf.exe (PID: 3744)
- InstallFlashPlayer.exe (PID: 2828)
Changes the autorun value in the registry
- invoice_2318362983713_823931342io.pdf.exe (PID: 3744)
ZEROACCESS has been detected
- invoice_2318362983713_823931342io.pdf.exe (PID: 3744)
SUSPICIOUS
Reads the date of Windows installation
- invoice_2318362983713_823931342io.pdf.exe (PID: 3744)
Reads the Internet Settings
- invoice_2318362983713_823931342io.pdf.exe (PID: 3744)
- InstallFlashPlayer.exe (PID: 2828)
Detected use of alternative data streams (AltDS)
- InstallFlashPlayer.exe (PID: 2828)
Reads security settings of Internet Explorer
- invoice_2318362983713_823931342io.pdf.exe (PID: 3744)
Starts CMD.EXE for commands execution
- invoice_2318362983713_823931342io.pdf.exe (PID: 3744)
There is functionality for lookup Geolocation (YARA)
- InstallFlashPlayer.exe (PID: 2828)
Executable content was dropped or overwritten
- InstallFlashPlayer.exe (PID: 2828)
- invoice_2318362983713_823931342io.pdf.exe (PID: 3744)
INFO
Checks supported languages
- invoice_2318362983713_823931342io.pdf.exe (PID: 3744)
- InstallFlashPlayer.exe (PID: 2828)
Creates files or folders in the user directory
- invoice_2318362983713_823931342io.pdf.exe (PID: 3744)
Reads the machine GUID from the registry
- invoice_2318362983713_823931342io.pdf.exe (PID: 3744)
Reads the computer name
- invoice_2318362983713_823931342io.pdf.exe (PID: 3744)
- InstallFlashPlayer.exe (PID: 2828)
The process uses the downloaded file
- invoice_2318362983713_823931342io.pdf.exe (PID: 3744)
Creates files in the program directory
- InstallFlashPlayer.exe (PID: 2828)
Manual execution by a user
- wmpnscfg.exe (PID: 1572)
Create files in a temporary directory
- invoice_2318362983713_823931342io.pdf.exe (PID: 3744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:11:25 10:32:03+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 144384 |
| InitializedDataSize: | 107520 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa3b6 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
42
Monitored processes
6
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 472 | C:\Windows\system32\services.exe | C:\Windows\System32\services.exe | wininit.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Services and Controller app Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 976 | "C:\Windows\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | invoice_2318362983713_823931342io.pdf.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 4294967295 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1296 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1572 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
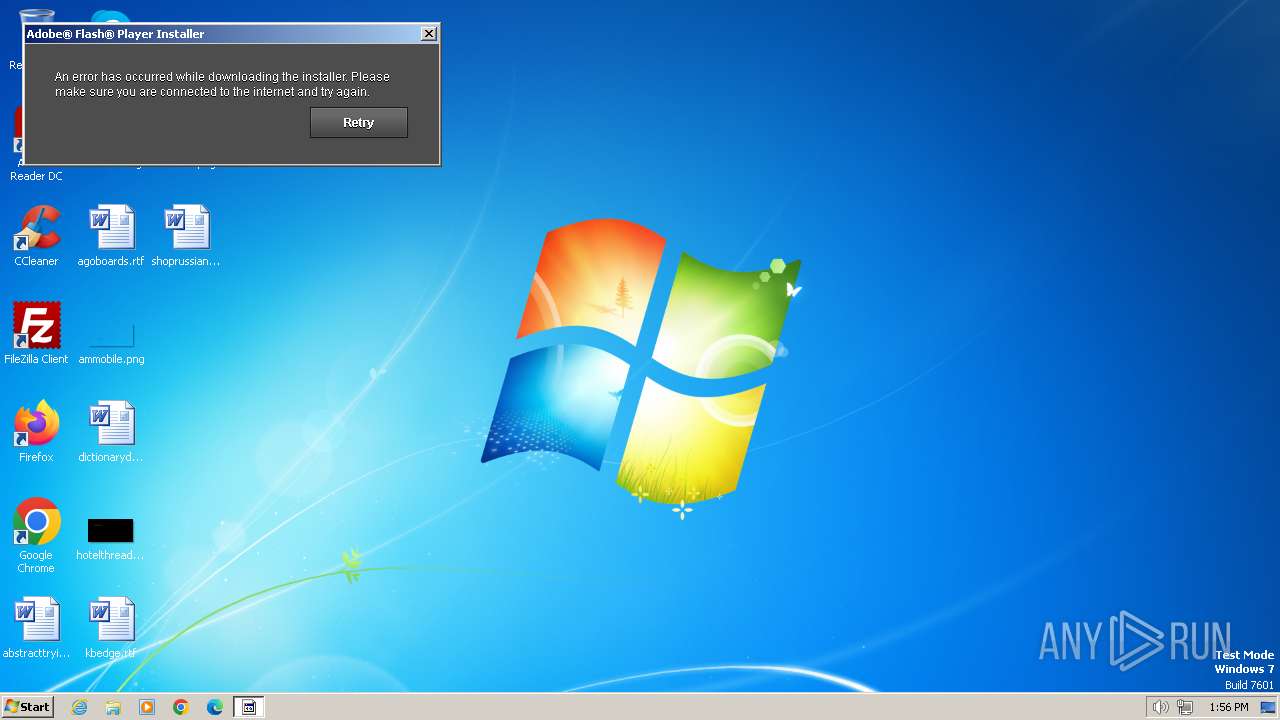
| 2828 | "C:\Users\admin\AppData\Local\Temp\InstallFlashPlayer.exe" | C:\Users\admin\AppData\Local\Temp\InstallFlashPlayer.exe | invoice_2318362983713_823931342io.pdf.exe | ||||||||||||
User: admin Company: Adobe Systems, Inc. Integrity Level: HIGH Description: Adobe® Flash® Player Installer/Uninstaller 11.0 r1 Version: 11,0,1,152 Modules
| |||||||||||||||
| 3744 | "C:\Users\admin\AppData\Local\Temp\invoice_2318362983713_823931342io.pdf.exe" | C:\Users\admin\AppData\Local\Temp\invoice_2318362983713_823931342io.pdf.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 034
Read events
1 015
Write events
12
Delete events
7
Modification events
| (PID) Process: | (1296) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Action Center\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB010000008226EE969B80BE4D824A2079D0A500DD00000000020000000000106600000001000020000000F8870E32D26D7047AC58F9524267FFB2522B88FA73D0CBE3D054C68767972118000000000E8000000002000020000000D55D5716554F0DD50C032B33A4D0799D1B25027F289069589AC223BF4004E61330000000B0C10AF16AF946ACE05A5AF512B3387F411E64810F5EF29B0E30B5846B245BB0C33B994AED52B7BF4E84DFE7FEF8433E4000000046BDE043B5BD8E85C48C01738FCB10045AE685105B8699FFAD00B1D6F17EF7144DDB4136DBA04E4FD262BD936638143E054E0E357D3CEAC494AD942EF527A360 | |||
| (PID) Process: | (3744) invoice_2318362983713_823931342io.pdf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Google Update |
Value: "C:\Users\admin\AppData\Local\Google\Desktop\Install\{6c5bc945-ecdc-d004-f972-a3d5e5911bb1}\❤≸⋙\Ⱒ☠⍨\ﯹ๛\{6c5bc945-ecdc-d004-f972-a3d5e5911bb1}\GoogleUpdate.exe" > | |||
| (PID) Process: | (3744) invoice_2318362983713_823931342io.pdf.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3744) invoice_2318362983713_823931342io.pdf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3744) invoice_2318362983713_823931342io.pdf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3744) invoice_2318362983713_823931342io.pdf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3744) invoice_2318362983713_823931342io.pdf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2828) InstallFlashPlayer.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WinDefend\Parameters |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2828) InstallFlashPlayer.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WinDefend\Security |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2828) InstallFlashPlayer.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WinDefend\TriggerInfo\0 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
5
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3744 | invoice_2318362983713_823931342io.pdf.exe | C:\Users\admin\AppData\Local\Temp\InstallFlashPlayer.exe | executable | |
MD5:2FF9B590342C62748885D459D082295F | SHA256:672EC8DCEAFD429C1A09CFAFBC4951968953E2081E0D97243040DB16EDB24429 | |||
| 3744 | invoice_2318362983713_823931342io.pdf.exe | C:\Users\admin\AppData\Local\Google\Desktop\Install\{6c5bc945-ecdc-d004-f972-a3d5e5911bb1}\❤≸⋙\Ⱒ☠⍨\ﯹ๛\{6c5bc945-ecdc-d004-f972-a3d5e5911bb1}\GoogleUpdate.exe | executable | |
MD5:EA039A854D20D7734C5ADD48F1A51C34 | SHA256:69E966E730557FDE8FD84317CDEF1ECE00A8BB3470C0B58F3231E170168AF169 | |||
| 2828 | InstallFlashPlayer.exe | C:\Program Files\Google\Desktop\Install\{6c5bc945-ecdc-d004-f972-a3d5e5911bb1}\ \...\ﯹ๛\{6c5bc945-ecdc-d004-f972-a3d5e5911bb1}\GoogleUpdate.exe | executable | |
MD5:EA039A854D20D7734C5ADD48F1A51C34 | SHA256:69E966E730557FDE8FD84317CDEF1ECE00A8BB3470C0B58F3231E170168AF169 | |||
| 472 | services.exe | C:\Windows\assembly\GAC\Desktop.ini | executable | |
MD5:D1A909DB8D6F6A6DA32050F077BE630C | SHA256:315387A3E83AAE9A667B82635B26A4D8576887887732239422D63E0F964CA17B | |||
| 3744 | invoice_2318362983713_823931342io.pdf.exe | C:\Users\admin\AppData\Local\Google\Desktop\Install\{6c5bc945-ecdc-d004-f972-a3d5e5911bb1}\❤≸⋙\Ⱒ☠⍨\ﯹ๛\{6c5bc945-ecdc-d004-f972-a3d5e5911bb1}\@ | binary | |
MD5:5D249256C4720087CBA1D4440FF2E4A5 | SHA256:F50445531AE32C0802E2299DED9BB609C6CA08AFD61AE1B9466EC2D3E6854C3C | |||
| 3744 | invoice_2318362983713_823931342io.pdf.exe | C:\Users\admin\AppData\Local\Temp\msimg32.dll | executable | |
MD5:E051308C2F0C1B280514C99AABD36E34 | SHA256:DDF7CCAB32E8C0EE6294DF2591EFAC632C27C61D073B86B97DE62311F9379212 | |||
| 2828 | InstallFlashPlayer.exe | C:\Program Files\Google\Desktop\Install\{6c5bc945-ecdc-d004-f972-a3d5e5911bb1}\ \...\ﯹ๛\{6c5bc945-ecdc-d004-f972-a3d5e5911bb1}\@ | binary | |
MD5:E927DBD8047A820F0B69BE63CFA0081F | SHA256:C0590D9BBFA15AFE3DBAC669E91809095F2C579B28FE346EE6EB1E03AA64B02F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
49
DNS requests
3
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 404 | 23.197.153.202:80 | http://fpdownload.macromedia.com/get/flashplayer/update/current/install/install_all_win_cab_ax_sgn.z | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
3744 | invoice_2318362983713_823931342io.pdf.exe | 85.114.128.127:53 | — | — | — | malicious |
2828 | InstallFlashPlayer.exe | 85.114.128.127:53 | — | — | — | malicious |
— | — | 85.114.128.127:53 | — | — | — | malicious |
— | — | 239.255.255.250:3702 | — | — | — | whitelisted |
— | — | 23.197.153.202:80 | fpdownload.macromedia.com | AKAMAI-AS | US | whitelisted |
— | — | 207.191.243.130:16471 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
j.maxmind.com |
| shared |
fpdownload.macromedia.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3744 | invoice_2318362983713_823931342io.pdf.exe | A Network Trojan was detected | ET MALWARE ZeroAccess udp traffic detected |
3744 | invoice_2318362983713_823931342io.pdf.exe | A Network Trojan was detected | ET MALWARE ZeroAccess udp traffic detected |
3744 | invoice_2318362983713_823931342io.pdf.exe | A Network Trojan was detected | ET MALWARE ZeroAccess udp traffic detected |
3744 | invoice_2318362983713_823931342io.pdf.exe | A Network Trojan was detected | ET MALWARE ZeroAccess udp traffic detected |
3744 | invoice_2318362983713_823931342io.pdf.exe | A Network Trojan was detected | ET MALWARE ZeroAccess udp traffic detected |
3744 | invoice_2318362983713_823931342io.pdf.exe | A Network Trojan was detected | ET MALWARE ZeroAccess udp traffic detected |
3744 | invoice_2318362983713_823931342io.pdf.exe | A Network Trojan was detected | ET MALWARE ZeroAccess udp traffic detected |
3744 | invoice_2318362983713_823931342io.pdf.exe | A Network Trojan was detected | ET MALWARE ZeroAccess udp traffic detected |
— | — | A Network Trojan was detected | ET MALWARE ZeroAccess udp traffic detected |
— | — | A Network Trojan was detected | ET MALWARE ZeroAccess udp traffic detected |