| File name: | 69e834be4264dab45e393e63952ae3b65f4e027a5928509c013b16175a43504b.exe |
| Full analysis: | https://app.any.run/tasks/5dbae726-9810-456f-8567-3f6c410f07f1 |
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2025, 19:35:25 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 7ACF6527EF4BEF7F7325A94C4D92C1F9 |
| SHA1: | 8C39212F127DFE4C04B05F05B9E6759566ED207A |
| SHA256: | 69E834BE4264DAB45E393E63952AE3B65F4E027A5928509C013B16175A43504B |
| SSDEEP: | 1536:Euf6eOOaYLJgceVTuD8SIY2vn7JibiwCrdGgPQECYq9J9wng:5fVOOaYLX0orIY2f7JimwCrdGgPQE9g |
MALICIOUS
BDAEJEC has been found (auto)
- 69e834be4264dab45e393e63952ae3b65f4e027a5928509c013b16175a43504b.exe (PID: 3220)
SUSPICIOUS
Executable content was dropped or overwritten
- 69e834be4264dab45e393e63952ae3b65f4e027a5928509c013b16175a43504b.exe (PID: 3220)
Reads security settings of Internet Explorer
- sgKbPm.exe (PID: 5968)
Connects to unusual port
- sgKbPm.exe (PID: 5968)
Starts CMD.EXE for commands execution
- sgKbPm.exe (PID: 5968)
Executing commands from a ".bat" file
- sgKbPm.exe (PID: 5968)
INFO
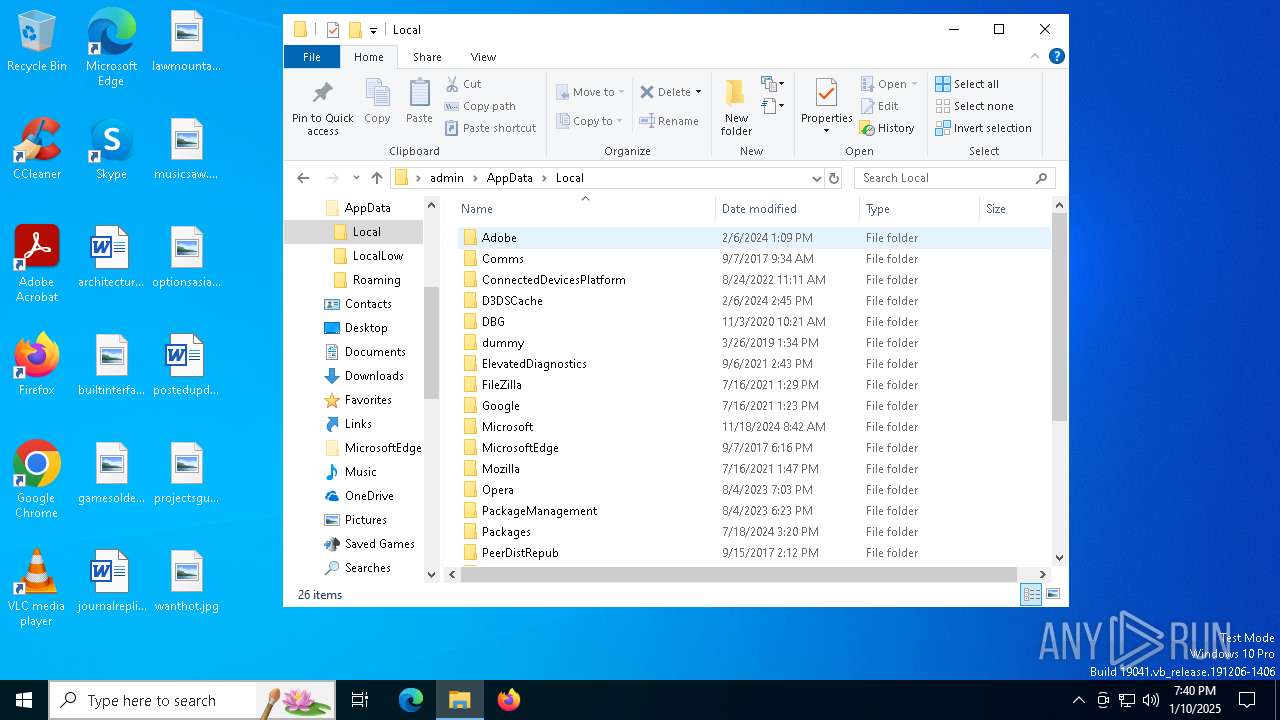
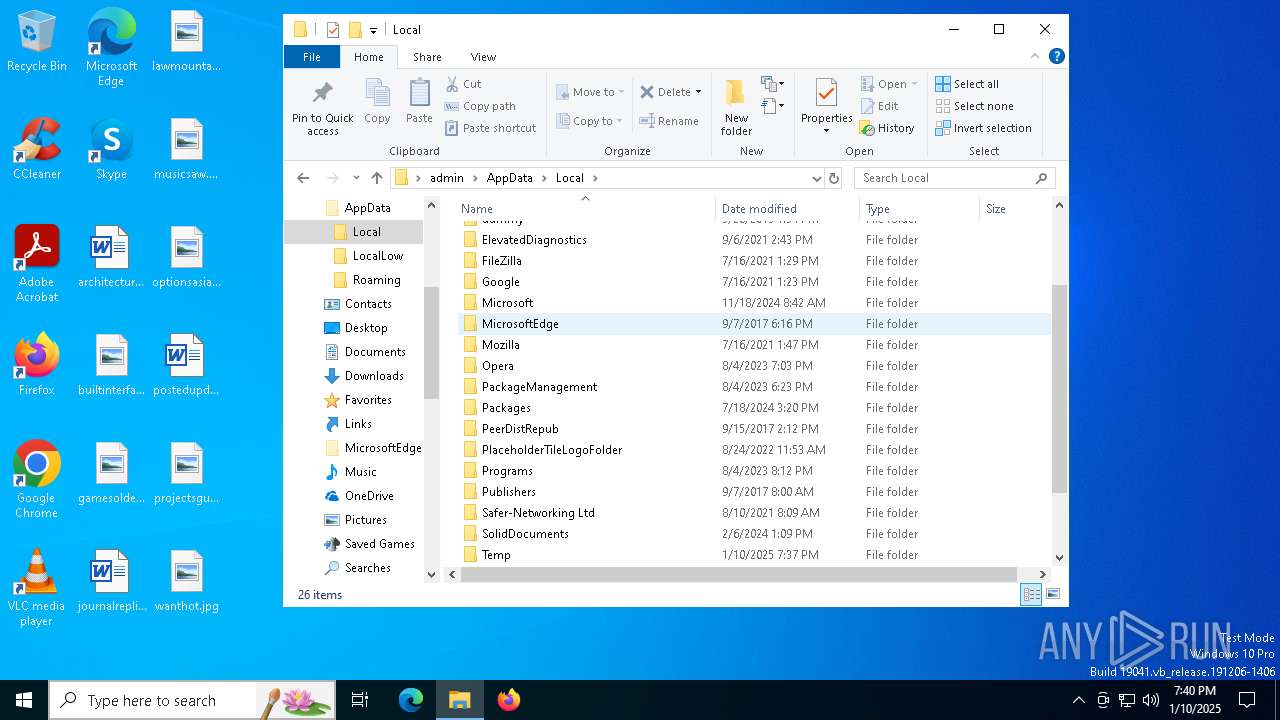
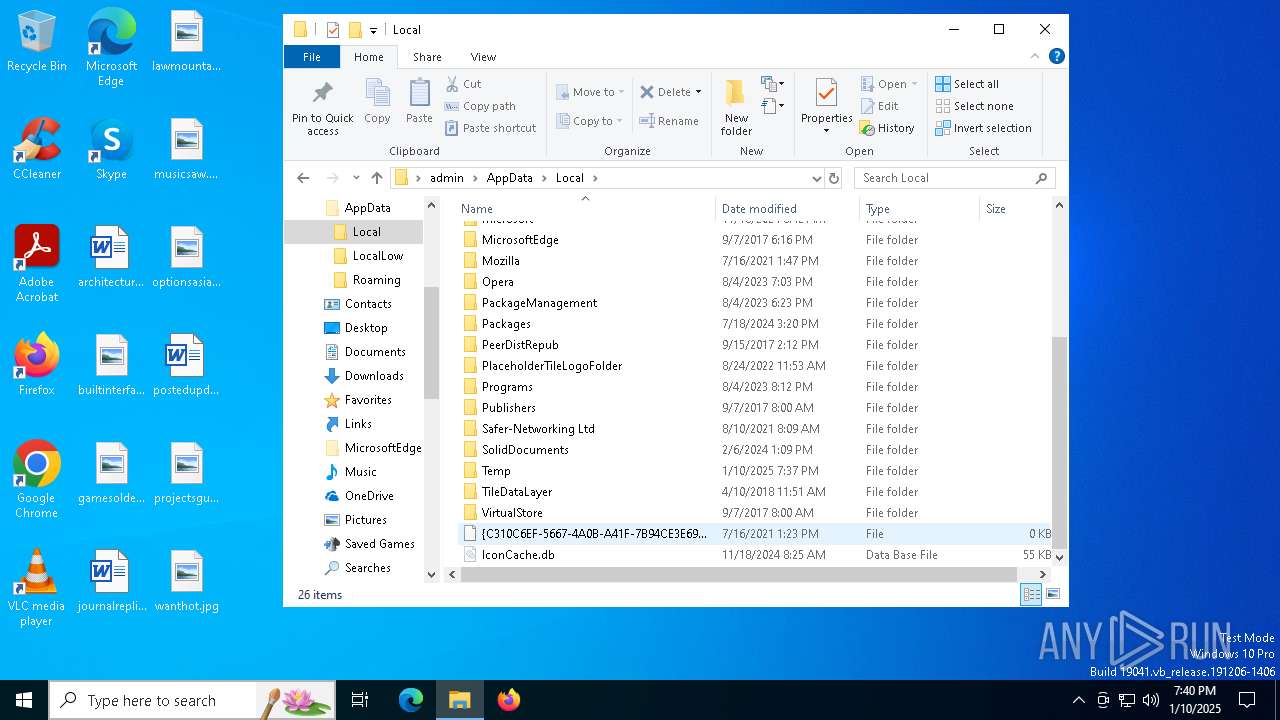
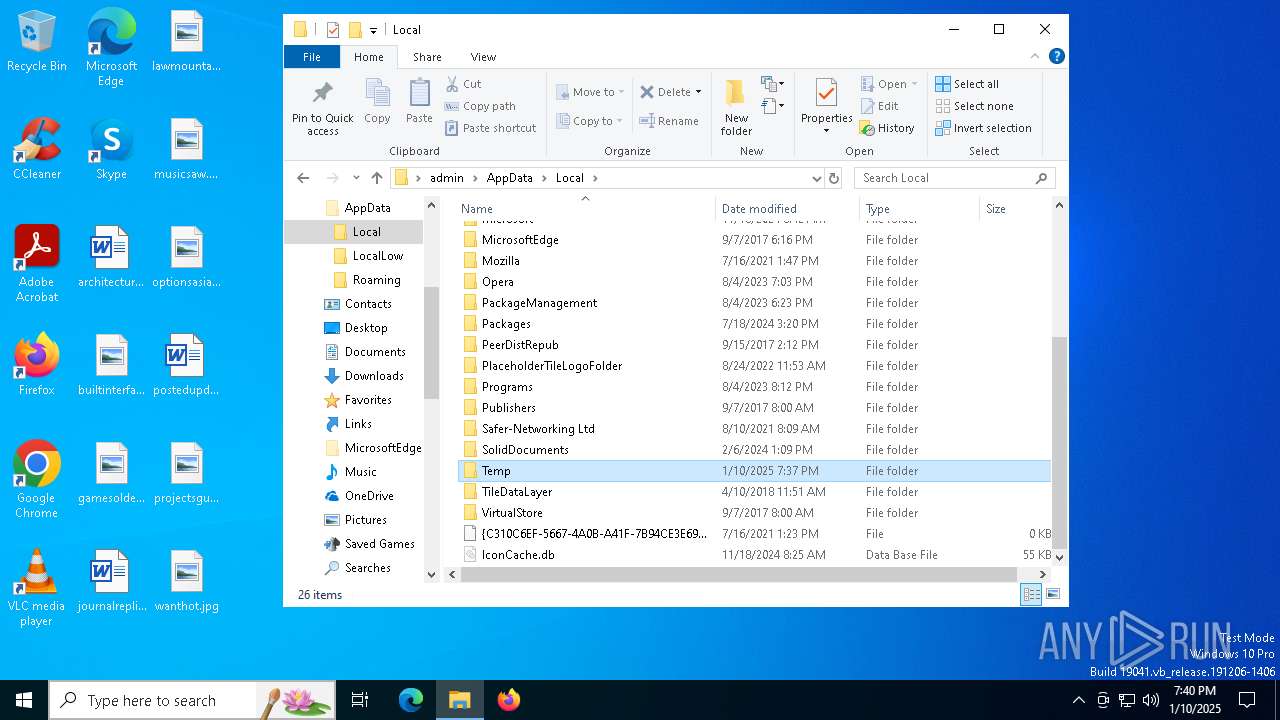
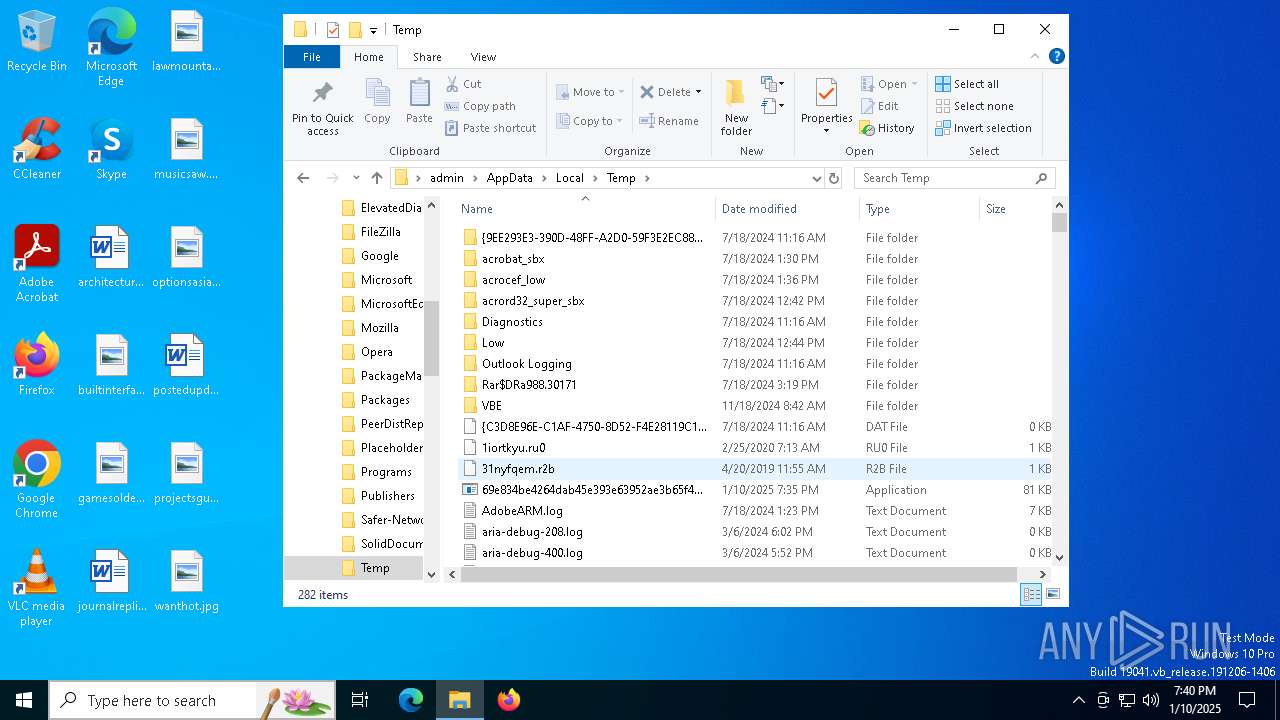
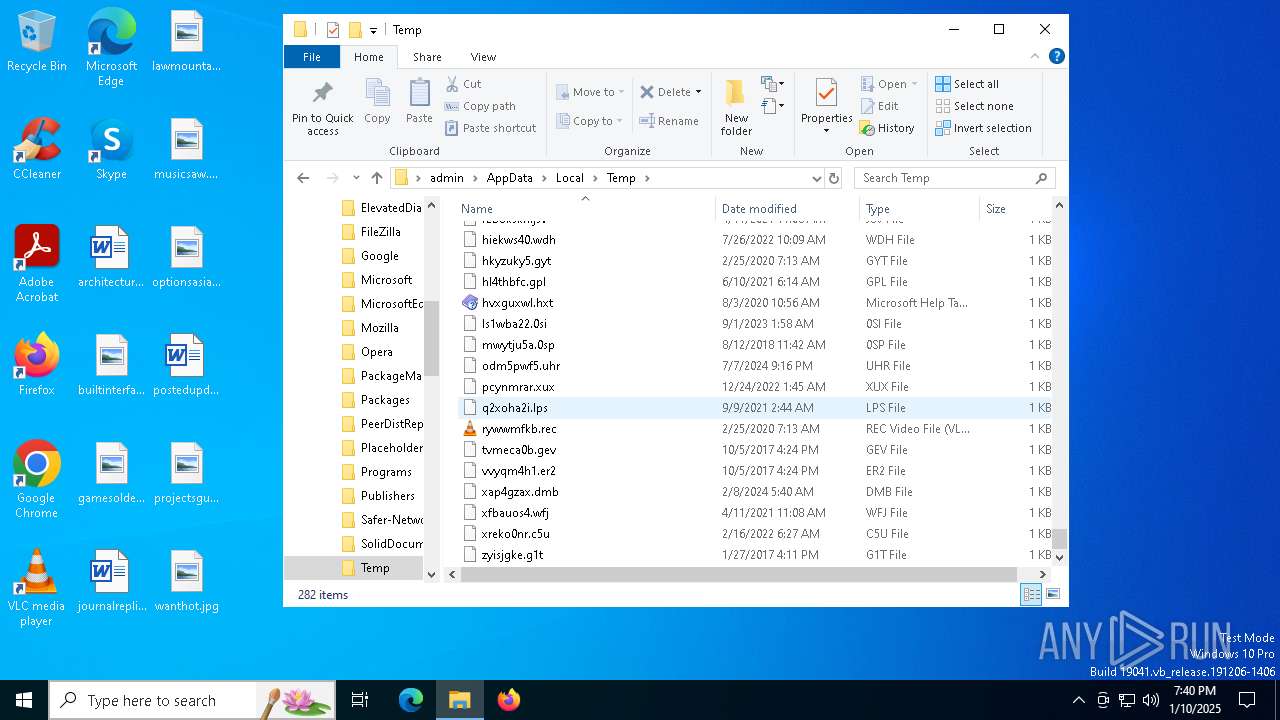
Create files in a temporary directory
- 69e834be4264dab45e393e63952ae3b65f4e027a5928509c013b16175a43504b.exe (PID: 3220)
- sgKbPm.exe (PID: 5968)
Checks supported languages
- sgKbPm.exe (PID: 5968)
- 69e834be4264dab45e393e63952ae3b65f4e027a5928509c013b16175a43504b.exe (PID: 3220)
Reads the computer name
- sgKbPm.exe (PID: 5968)
Checks proxy server information
- sgKbPm.exe (PID: 5968)
Process checks computer location settings
- sgKbPm.exe (PID: 5968)
The process uses the downloaded file
- sgKbPm.exe (PID: 5968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:05:09 14:21:53+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 68608 |
| InitializedDataSize: | 19968 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x14000 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Total processes
129
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
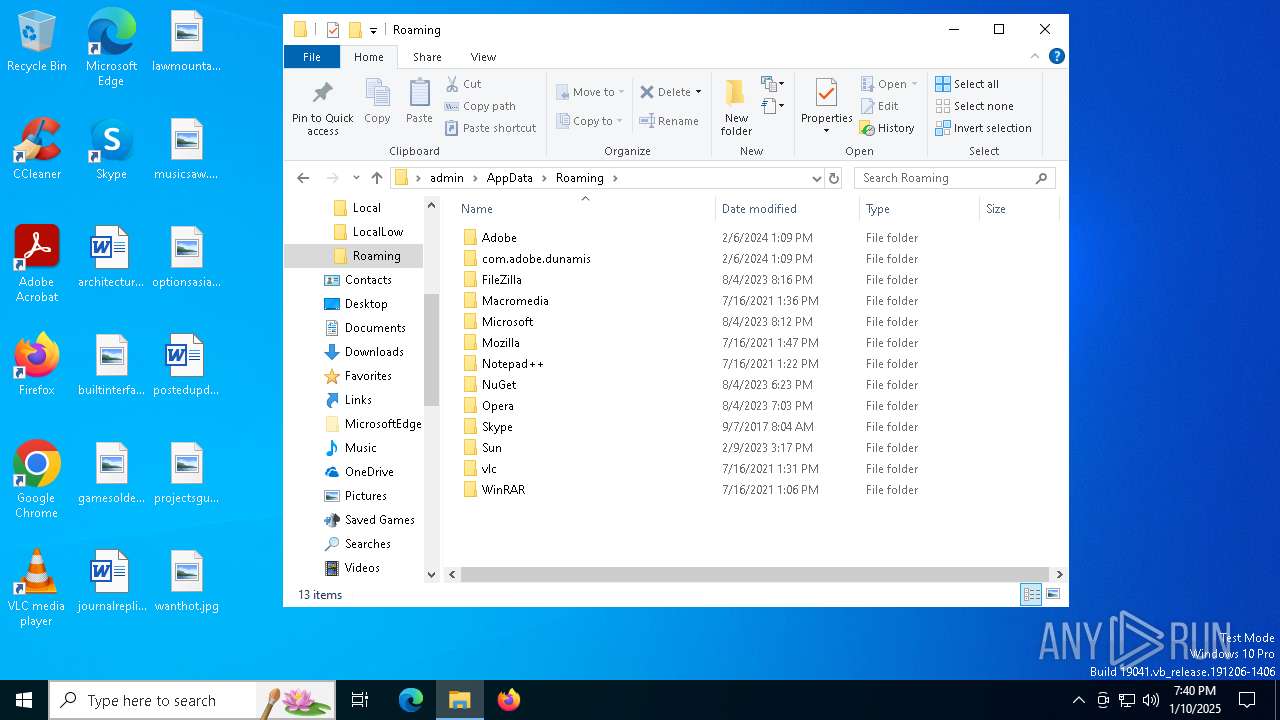
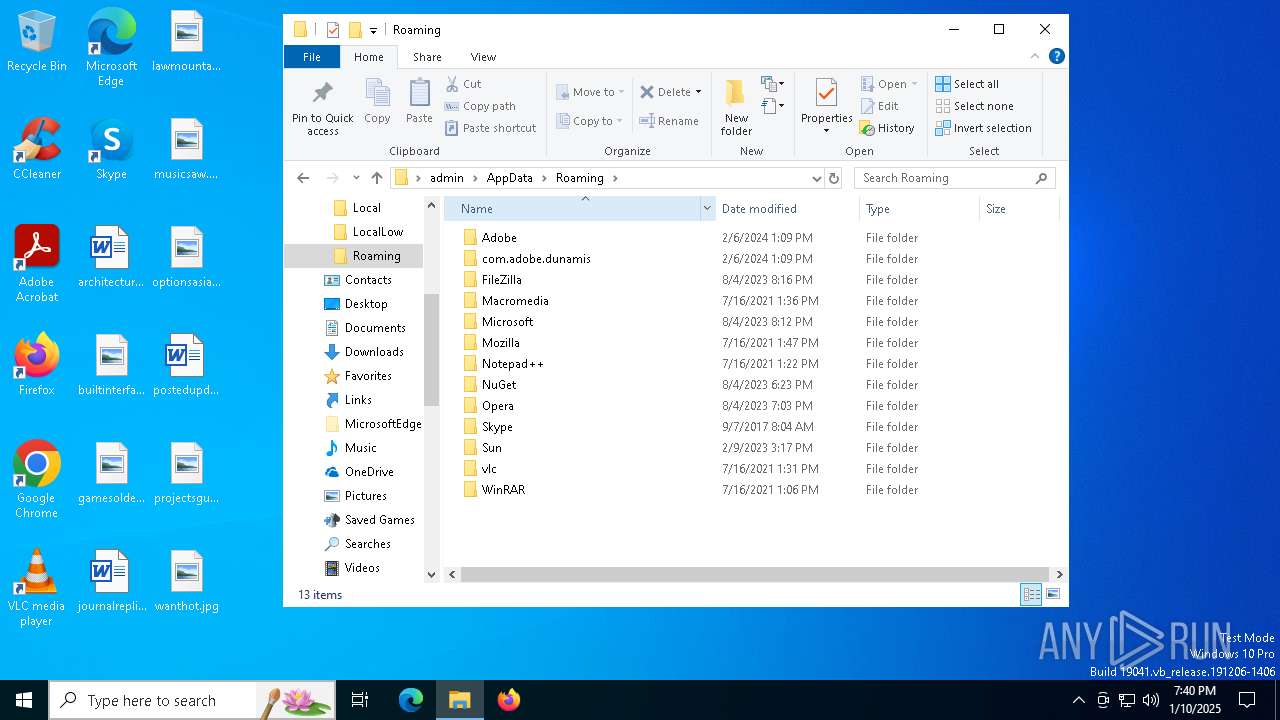
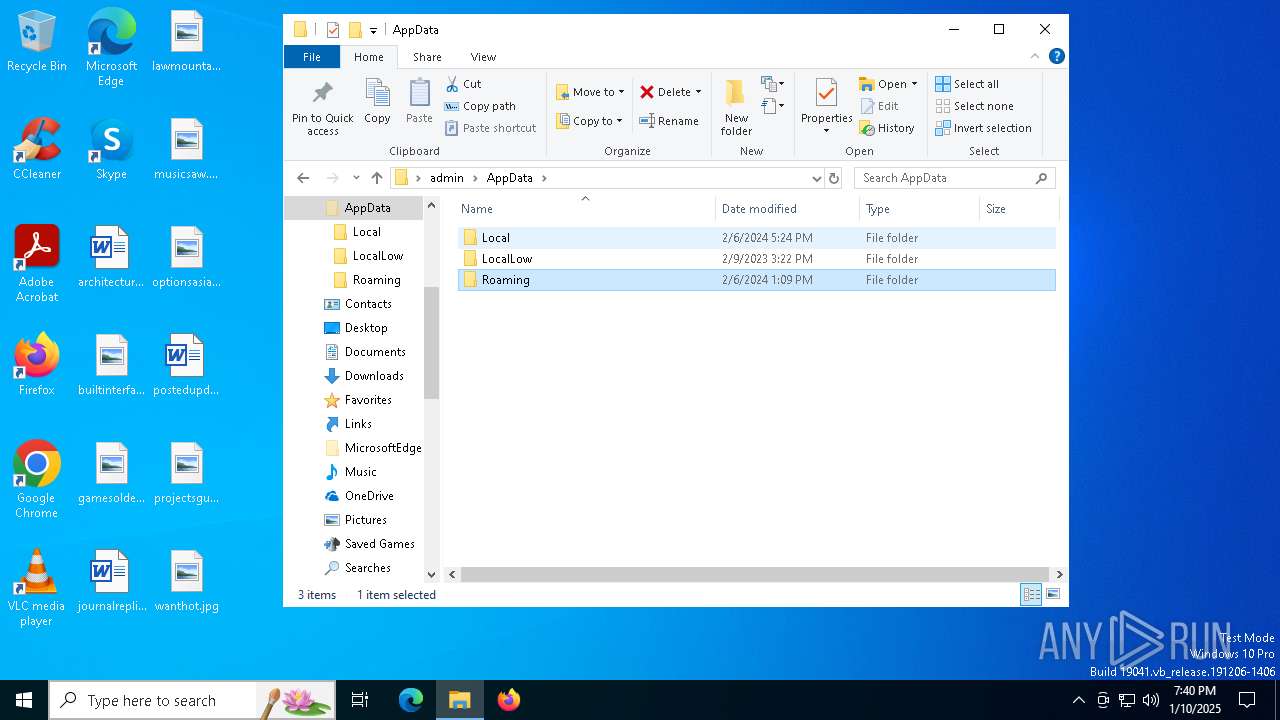
| 3220 | "C:\Users\admin\AppData\Local\Temp\69e834be4264dab45e393e63952ae3b65f4e027a5928509c013b16175a43504b.exe" | C:\Users\admin\AppData\Local\Temp\69e834be4264dab45e393e63952ae3b65f4e027a5928509c013b16175a43504b.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 2 Modules
| |||||||||||||||
| 5968 | C:\Users\admin\AppData\Local\Temp\sgKbPm.exe | C:\Users\admin\AppData\Local\Temp\sgKbPm.exe | 69e834be4264dab45e393e63952ae3b65f4e027a5928509c013b16175a43504b.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6628 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\20e750d9.bat" " | C:\Windows\SysWOW64\cmd.exe | — | sgKbPm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6640 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6936 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
748
Read events
744
Write events
4
Delete events
0
Modification events
| (PID) Process: | (5968) sgKbPm.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5968) sgKbPm.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5968) sgKbPm.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5968) sgKbPm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\GTplus |
| Operation: | write | Name: | Time |
Value: 3A316F0E9763DB01 | |||
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5968 | sgKbPm.exe | C:\Users\admin\AppData\Local\Temp\20e750d9.bat | text | |
MD5:237D970FC830C294A09DE7F6D6977FE0 | SHA256:571C3C6CD3A50D36BFAE7FE8E9D814E340A8EC479052DF27BE9D306191FEF07B | |||
| 3220 | 69e834be4264dab45e393e63952ae3b65f4e027a5928509c013b16175a43504b.exe | C:\Users\admin\AppData\Local\Temp\sgKbPm.exe | executable | |
MD5:56B2C3810DBA2E939A8BB9FA36D3CF96 | SHA256:4354970CCC7CD6BB16318F132C34F6A1B3D5C2EA7FF53E1C9271905527F2DB07 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
34
DNS requests
18
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5968 | sgKbPm.exe | 44.221.84.105:799 | ddos.dnsnb8.net | AMAZON-AES | US | malicious |
3976 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
736 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7012 | SIHClient.exe | 20.12.23.50:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7012 | SIHClient.exe | 20.242.39.171:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ddos.dnsnb8.net |
| malicious |
dns.msftncsi.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
171.39.242.20.in-addr.arpa |
| unknown |
d.3.0.0.0.0.0.0.0.0.0.0.0.0.0.0.7.0.0.0.8.0.4.0.0.3.0.1.3.0.6.2.ip6.arpa |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Misc activity | SUSPICIOUS [ANY.RUN] Domain previously seen in multiple payload deliveries (ddos .dnsnb8 .net) |