| File name: | ZENINDLC.exe |
| Full analysis: | https://app.any.run/tasks/ba39d4f9-15b1-43c5-b9fe-21d60ce51e8a |
| Verdict: | Malicious activity |
| Analysis date: | March 13, 2026, 13:10:49 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | C53E0C5C63D8759F71612B09A86EF3EB |
| SHA1: | 0DAFE1D9AE6A87D569CE15B6E9C16476348A95C3 |
| SHA256: | 69D128A105512E63A9DC7B3E0F1E92CACB68958CC0332A17AEA5F07C2DA58BC8 |
| SSDEEP: | 24576:wYjmIirluEIcRC58V90zD80PJEeYjmIirluEIcRC58V90zD80PJEDjHLK:wmmIirluEI8C58V9KD80PJEemmIirlu1 |
MALICIOUS
Bypass User Account Control (Modify registry)
- ZENINDLC.exe (PID: 5752)
- ZENINDLC.exe (PID: 1424)
Bypass User Account Control (ComputerDefaults)
- ComputerDefaults.exe (PID: 8708)
- ComputerDefaults.exe (PID: 8392)
Changes powershell execution policy (Bypass)
- ZENINDLC.exe (PID: 9160)
- ZENINDLC.exe (PID: 8488)
Adds path to the Windows Defender exclusion list
- ZENINDLC.exe (PID: 9160)
- ZENINDLC.exe (PID: 8488)
Changes Windows Defender settings
- ZENINDLC.exe (PID: 9160)
- ZENINDLC.exe (PID: 8488)
Changes the autorun value in the registry
- ZENINDLC.exe (PID: 9160)
- ZENINDLC.exe (PID: 8488)
SUSPICIOUS
Delegate execute modification
- ZENINDLC.exe (PID: 5752)
- ZENINDLC.exe (PID: 1424)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2456)
- cmd.exe (PID: 1960)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2456)
- ZENINDLC.exe (PID: 9160)
- cmd.exe (PID: 1960)
- ZENINDLC.exe (PID: 8488)
Removes files via Powershell
- powershell.exe (PID: 7868)
- powershell.exe (PID: 4304)
Reads the date of Windows installation
- ZENINDLC.exe (PID: 9160)
- ZENINDLC.exe (PID: 8488)
Bypass execution policy to execute commands
- powershell.exe (PID: 4144)
- powershell.exe (PID: 7780)
- powershell.exe (PID: 2688)
- powershell.exe (PID: 9048)
- powershell.exe (PID: 476)
- powershell.exe (PID: 4876)
Adds exclusion path to Windows Defender (POWERSHELL)
- ZENINDLC.exe (PID: 9160)
- ZENINDLC.exe (PID: 8488)
Checks for external IP
- ZENINDLC.exe (PID: 9160)
- svchost.exe (PID: 2292)
- ZENINDLC.exe (PID: 5752)
- ZENINDLC.exe (PID: 1424)
- ZENINDLC.exe (PID: 8488)
Executable content was dropped or overwritten
- ZENINDLC.exe (PID: 9160)
INFO
Checks supported languages
- ZENINDLC.exe (PID: 5752)
- ZENINDLC.exe (PID: 9160)
- Nursultan.exe (PID: 5160)
- Nursultan (3).exe (PID: 3508)
- ZENINDLC.exe (PID: 8488)
- ZENINDLC.exe (PID: 1424)
- Nursultan.exe (PID: 5608)
- Nursultan (3).exe (PID: 1904)
Reads the computer name
- ZENINDLC.exe (PID: 5752)
- ZENINDLC.exe (PID: 9160)
- Nursultan.exe (PID: 5160)
- Nursultan (3).exe (PID: 3508)
- ZENINDLC.exe (PID: 8488)
- ZENINDLC.exe (PID: 1424)
- Nursultan.exe (PID: 5608)
- Nursultan (3).exe (PID: 1904)
Disables trace logs
- ZENINDLC.exe (PID: 5752)
- ZENINDLC.exe (PID: 9160)
- ZENINDLC.exe (PID: 1424)
- ZENINDLC.exe (PID: 8488)
Reads the machine GUID from the registry
- ZENINDLC.exe (PID: 5752)
- ZENINDLC.exe (PID: 9160)
- ZENINDLC.exe (PID: 1424)
- ZENINDLC.exe (PID: 8488)
Reads Environment values
- ZENINDLC.exe (PID: 5752)
- ZENINDLC.exe (PID: 9160)
- ZENINDLC.exe (PID: 1424)
- ZENINDLC.exe (PID: 8488)
Reads security settings of Internet Explorer
- ComputerDefaults.exe (PID: 8708)
- ZENINDLC.exe (PID: 9160)
- ComputerDefaults.exe (PID: 8392)
- ZENINDLC.exe (PID: 8488)
Process checks computer location settings
- ZENINDLC.exe (PID: 9160)
- ZENINDLC.exe (PID: 8488)
Launching a file from a Registry key
- ZENINDLC.exe (PID: 9160)
- ZENINDLC.exe (PID: 8488)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7780)
- powershell.exe (PID: 2688)
- powershell.exe (PID: 4144)
- powershell.exe (PID: 9048)
- powershell.exe (PID: 476)
- powershell.exe (PID: 4876)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7780)
- powershell.exe (PID: 2688)
- powershell.exe (PID: 4144)
- powershell.exe (PID: 9048)
- powershell.exe (PID: 476)
- powershell.exe (PID: 4876)
Reads Microsoft Office registry keys
- ZENINDLC.exe (PID: 9160)
- ZENINDLC.exe (PID: 8488)
Create files in a temporary directory
- ZENINDLC.exe (PID: 9160)
- ZENINDLC.exe (PID: 8488)
Manual execution by a user
- ZENINDLC.exe (PID: 1424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2026:03:12 09:35:53+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 720384 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb1cfe |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 1.0.0.0 |
| InternalName: | NURSULTAN.exe |
| LegalCopyright: | |
| OriginalFileName: | NURSULTAN.exe |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
183
Monitored processes
36
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 476 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Local\Temp\Nursultan (3).exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | ZENINDLC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1424 | "C:\Users\admin\Desktop\ZENINDLC.exe" | C:\Users\admin\Desktop\ZENINDLC.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1432 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1612 | "C:\WINDOWS\system32\ComputerDefaults.exe" | C:\Windows\System32\ComputerDefaults.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Set Program Access and Computer Defaults Control Panel Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1904 | "C:\Users\admin\AppData\Local\Temp\Nursultan (3).exe" | C:\Users\admin\AppData\Local\Temp\Nursultan (3).exe | — | ZENINDLC.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Client Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1956 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1960 | "cmd.exe" /c start computerdefaults.exe && powershell.exe Remove-Item -Path HKCU:\Software\Classes\ms-settings\shell -Recurse | C:\Windows\System32\cmd.exe | — | ZENINDLC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2212 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2292 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2456 | "cmd.exe" /c start computerdefaults.exe && powershell.exe Remove-Item -Path HKCU:\Software\Classes\ms-settings\shell -Recurse | C:\Windows\System32\cmd.exe | — | ZENINDLC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
59 043
Read events
58 947
Write events
88
Delete events
8
Modification events
| (PID) Process: | (5752) ZENINDLC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ZENINDLC_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5752) ZENINDLC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ZENINDLC_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5752) ZENINDLC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ZENINDLC_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (5752) ZENINDLC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ZENINDLC_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (5752) ZENINDLC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ZENINDLC_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (5752) ZENINDLC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ZENINDLC_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (5752) ZENINDLC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ZENINDLC_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (5752) ZENINDLC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ZENINDLC_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5752) ZENINDLC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ZENINDLC_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5752) ZENINDLC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\ZENINDLC_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
2
Suspicious files
1
Text files
30
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6568 | mspaint.exe | C:\Windows\debug\WIA\wiatrace.log | text | |
MD5:D297ADE25601B7F4EEC289124F071E0A | SHA256:262EE5BC0C46D8DCE75876871DA4F07BFE07C8F9CA6EF6966429CA238791DCA2 | |||
| 7780 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1xeplnc4.w0x.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7868 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_w3z0wm3f.fp5.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7868 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:C3F966C303B8C39A3743F1F89B9A6899 | SHA256:702B1FA1AE5F81091BEF5E0BFC49F286A26ECCCE39E89C6DD093E1E62E8185EB | |||
| 4144 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5jtrylxr.2kt.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4144 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0a4hzast.iqy.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4144 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fw3xvyl5.u52.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4144 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2bokrk3p.akd.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7780 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_kectacgs.5cp.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
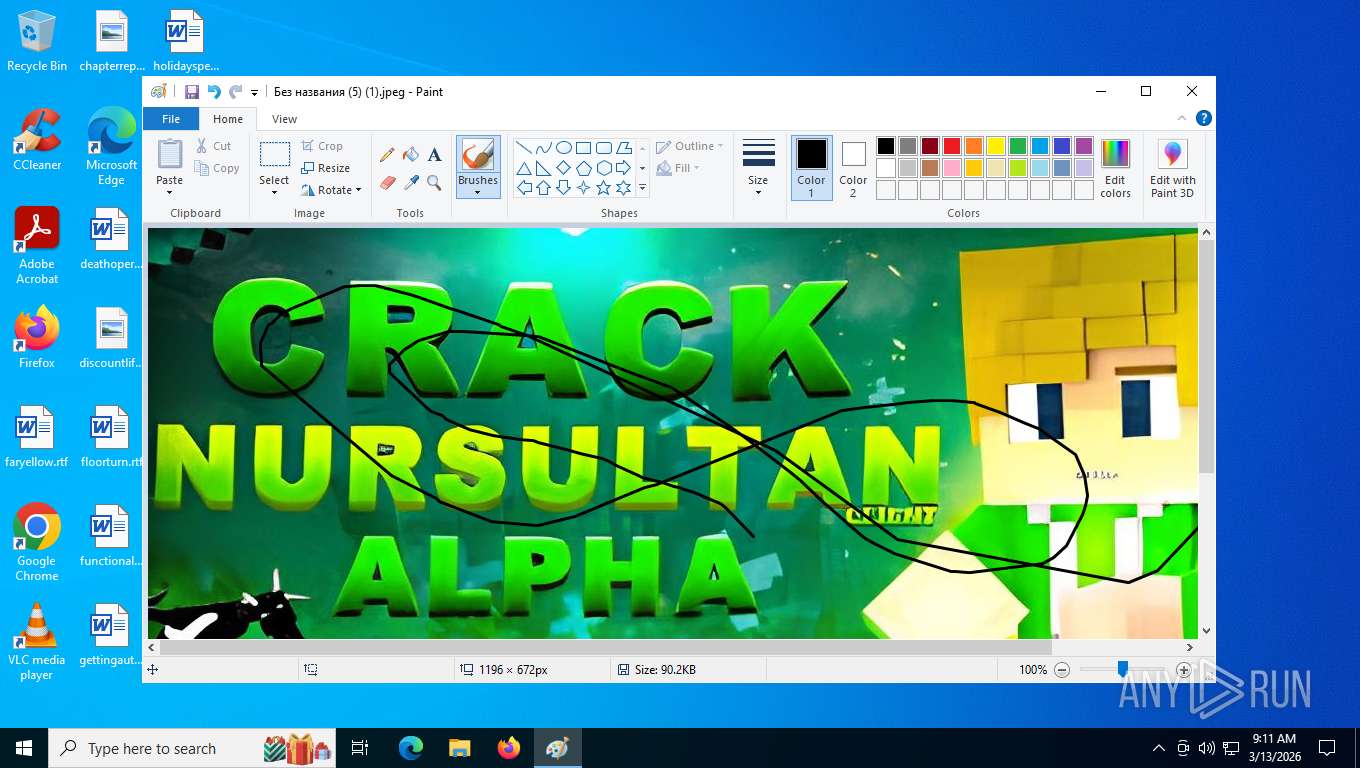
| 9160 | ZENINDLC.exe | C:\Users\admin\AppData\Local\Temp\Без названия (5) (1).jpeg | image | |
MD5:1094836305A40B26A41BBE4F11162107 | SHA256:C4CE7974BCBEB38C5660885A93FE38037AAEC95A9F5F5FDBB936E3741BC0B654 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
27
DNS requests
19
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | unknown | — | — | whitelisted |
9088 | svchost.exe | GET | 304 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | unknown | — | — | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | unknown | — | — | whitelisted |
5752 | ZENINDLC.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | malicious |
9160 | ZENINDLC.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | malicious |
524 | SIHClient.exe | GET | 304 | 74.178.240.61:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
356 | svchost.exe | POST | 200 | 20.190.160.132:443 | https://login.live.com/RST2.srf | unknown | xml | 1.24 Kb | whitelisted |
524 | SIHClient.exe | GET | 200 | 74.178.240.51:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | whitelisted |
524 | SIHClient.exe | GET | 200 | 74.178.240.61:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
9088 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8628 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 2.16.241.212:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3412 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
5752 | ZENINDLC.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
ip-api.com |
| whitelisted |
login.live.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2292 | svchost.exe | Misc activity | INFO [ANY.RUN] External IP Check (ip-api .com) |
5752 | ZENINDLC.exe | A Network Trojan was detected | ET MALWARE Common Stealer Behavior - Source IP Associated with Hosting Provider Check via ip.api .com |
5752 | ZENINDLC.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
2292 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
9160 | ZENINDLC.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
1424 | ZENINDLC.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
8488 | ZENINDLC.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |