| File name: | Setup_GCPSuite.exe |
| Full analysis: | https://app.any.run/tasks/b4f4a660-34fd-4820-871e-48d5f855158c |
| Verdict: | Malicious activity |
| Analysis date: | December 29, 2021, 04:58:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 37791A87B1092E7679B6C362266B4871 |
| SHA1: | 0755F1E6CDBAA42A5B8D3E8E0D46981E8CDF0074 |
| SHA256: | 69C4D91CA5ADBDDA695AF52A73975936E68311BB82E36DB0C9AAE9DB8B76B3B8 |
| SSDEEP: | 24576:GT3b4M3Cuv6wLvnAcWgWjjakTUtuv8brj0RKbsXVumSi54RSAgtYpOyf:YMMyq8cWzjekTJvgroRKSVum04Amk |
MALICIOUS
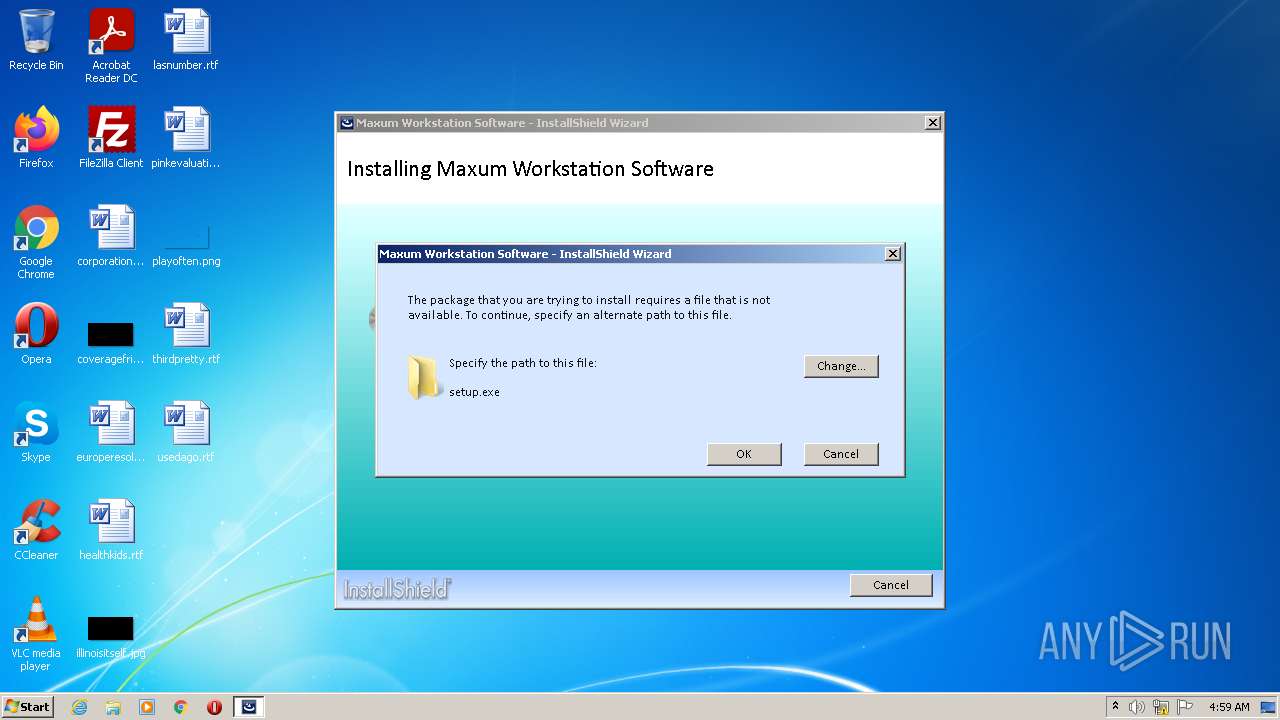
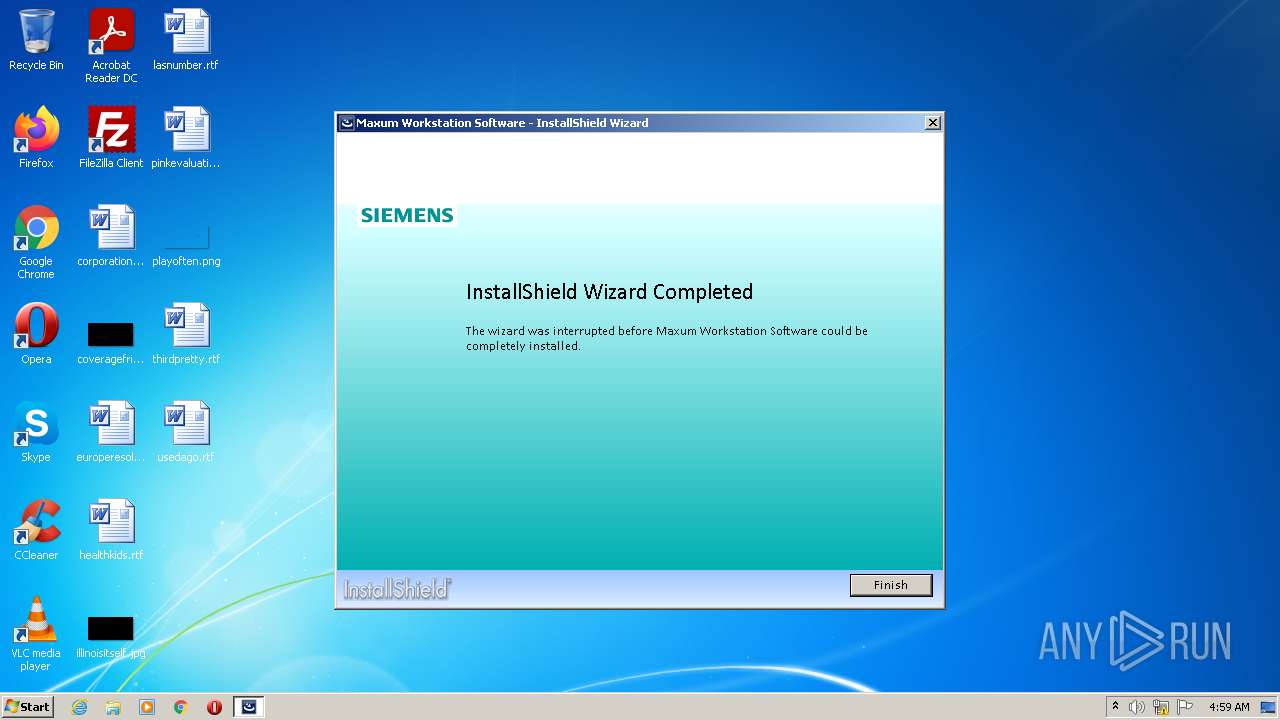
Loads dropped or rewritten executable
- Setup_GCPSuite.exe (PID: 596)
Changes the autorun value in the registry
- Setup_GCPSuite.exe (PID: 596)
Drops executable file immediately after starts
- Setup_GCPSuite.exe (PID: 596)
SUSPICIOUS
Checks supported languages
- Setup_GCPSuite.exe (PID: 596)
Reads the computer name
- Setup_GCPSuite.exe (PID: 596)
Executable content was dropped or overwritten
- Setup_GCPSuite.exe (PID: 596)
Drops a file that was compiled in debug mode
- Setup_GCPSuite.exe (PID: 596)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (17.3) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (4.1) |
| .exe | | | Win32 Executable (generic) (2.8) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
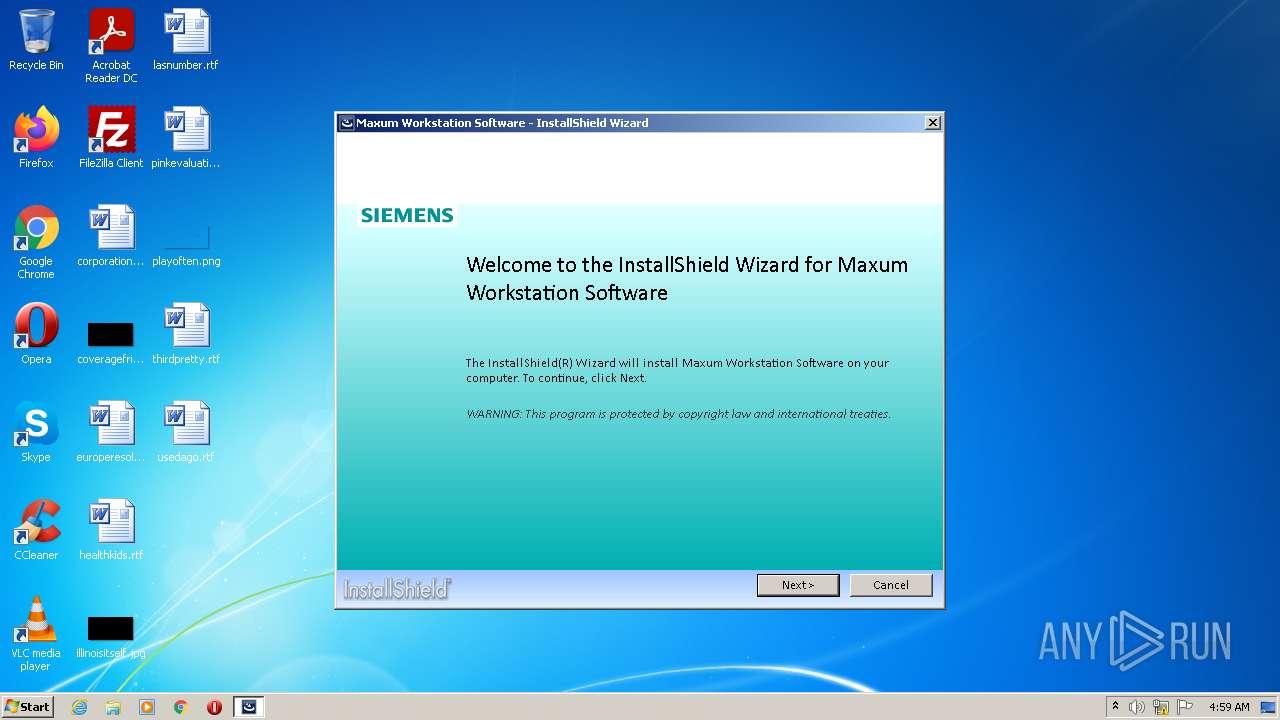
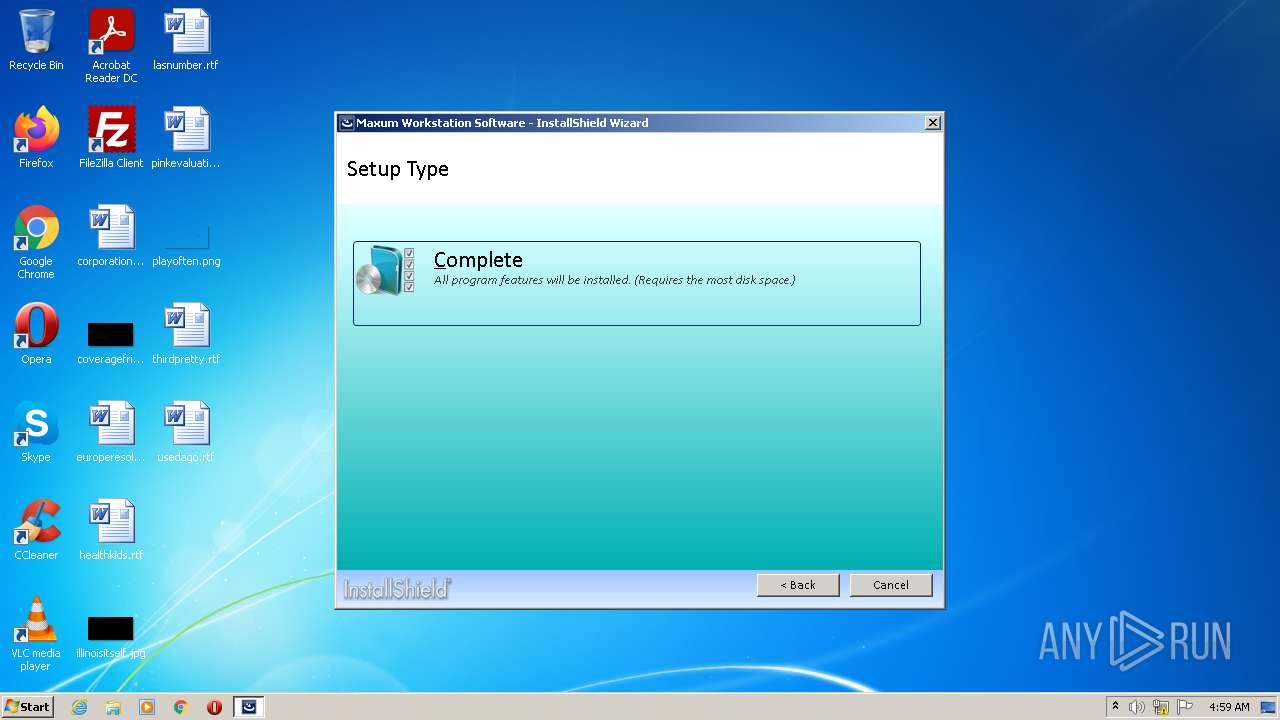
| ISInternalDescription: | Setup Suite Launcher Unicode |
|---|---|
| ISInternalVersion: | 20.0.496 |
| InternalBuildNumber: | 133442 |
| ProductVersion: | 5.20.05.0280 |
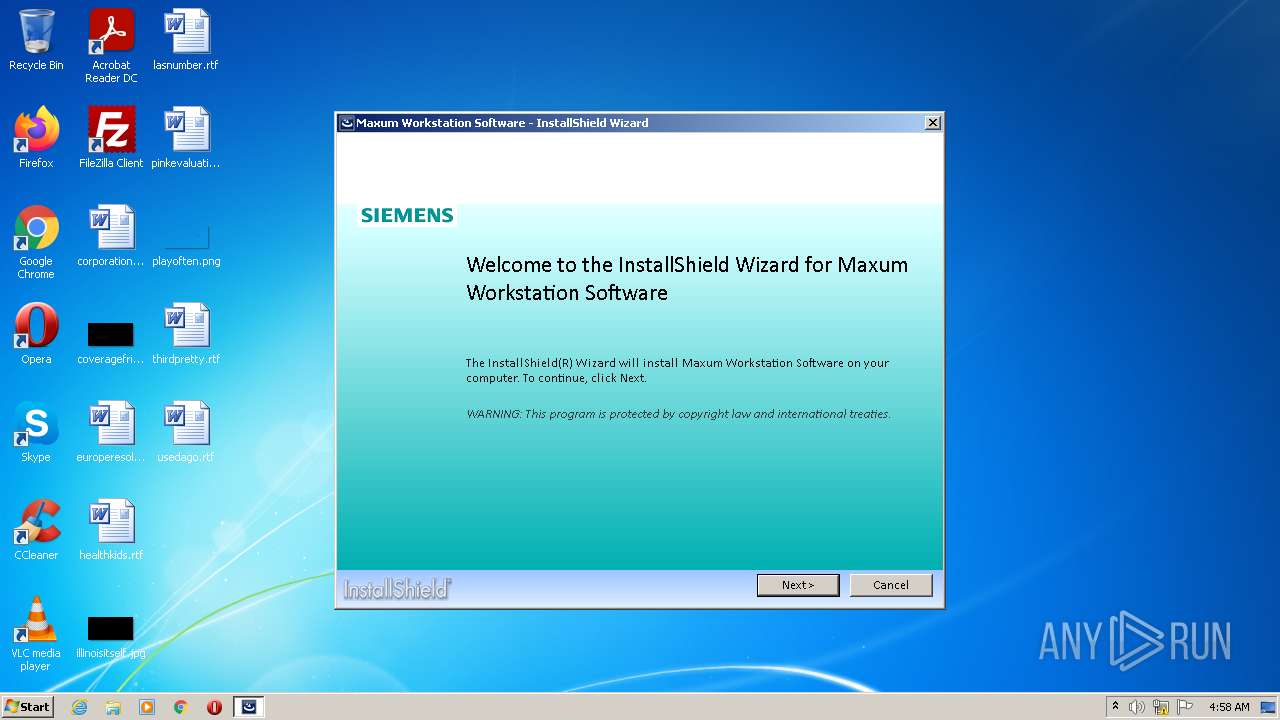
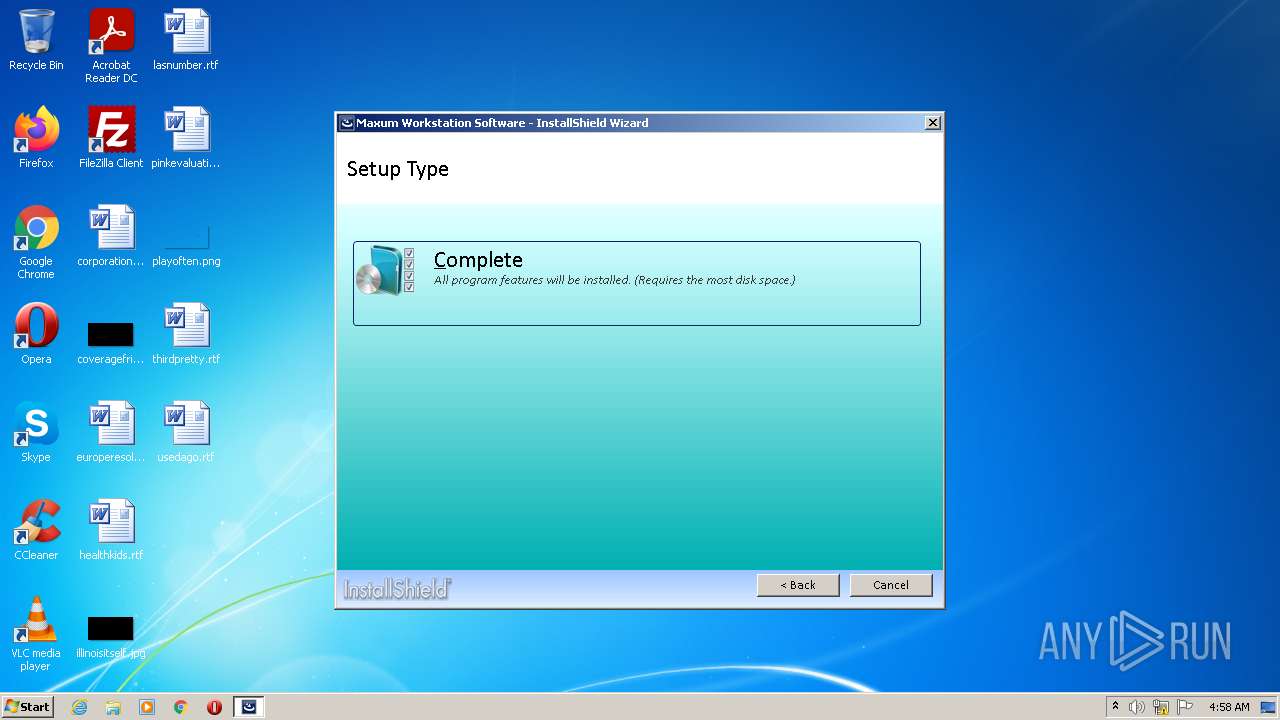
| ProductName: | Maxum Workstation Software |
| OriginalFileName: | InstallShield SetupSuite.exe |
| LegalCopyright: | Copyright © 2014 Siemens Industry, Inc. |
| InternalName: | SetupSuite |
| FileVersion: | 5.20.05.0280 |
| FileDescription: | Suite setup launcher |
| CompanyName: | Siemens Industry, Inc. |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Dynamic link library |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 5.20.5.280 |
| FileVersionNumber: | 5.20.5.280 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x80e16 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 354816 |
| CodeSize: | 635392 |
| LinkerVersion: | 11 |
| PEType: | PE32 |
| TimeStamp: | 2013:10:02 06:50:58+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Oct-2013 04:50:58 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Flexera Software LLC |
| FileDescription: | Setup Suite Launcher Unicode |
| FileVersion: | 20.0.496 |
| InternalName: | SetupSuite |
| LegalCopyright: | Copyright (c) 2013 Flexera Software LLC. All Rights Reserved. |
| OriginalFilename: | InstallShield SetupSuite.exe |
| ProductName: | InstallShield |
| ProductVersion: | 20.0 |
| Internal Build Number: | 133442 |
| ISInternalVersion: | 20.0.496 |
| ISInternalDescription: | Setup Suite Launcher Unicode |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 02-Oct-2013 04:50:58 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0009AE1C | 0x0009B000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47571 |
.orpc | 0x0009C000 | 0x00000163 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.31288 |
.rdata | 0x0009D000 | 0x0002FA76 | 0x0002FC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.53541 |
.data | 0x000CD000 | 0x0000782C | 0x00005400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.86513 |
.rsrc | 0x000D5000 | 0x0000C730 | 0x0000C800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.73563 |
.reloc | 0x000E2000 | 0x000151A8 | 0x00015200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.37218 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.02666 | 888 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.835 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.35696 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 6.14965 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 6.18448 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 4.85842 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 1.94502 | 72 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 5.81004 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 6.06596 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
100 | 2.89097 | 132 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
CRYPT32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
VERSION.dll |
WINTRUST.dll |
Total processes
38
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 596 | "C:\Users\admin\AppData\Local\Temp\Setup_GCPSuite.exe" | C:\Users\admin\AppData\Local\Temp\Setup_GCPSuite.exe | Explorer.EXE | ||||||||||||
User: admin Company: Siemens Industry, Inc. Integrity Level: HIGH Description: Suite setup launcher Exit code: 2 Version: 5.20.05.0280 Modules
| |||||||||||||||
| 1012 | "C:\Users\admin\AppData\Local\Temp\Setup_GCPSuite.exe" | C:\Users\admin\AppData\Local\Temp\Setup_GCPSuite.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Siemens Industry, Inc. Integrity Level: MEDIUM Description: Suite setup launcher Exit code: 3221226540 Version: 5.20.05.0280 Modules
| |||||||||||||||
Total events
107
Read events
100
Write events
3
Delete events
4
Modification events
| (PID) Process: | (596) Setup_GCPSuite.exe | Key: | HKEY_CURRENT_USER\Software\InstallShield\SuiteInstallers\{842D3FBA-EE54-4283-872A-DF315C1A4BCC} |
| Operation: | write | Name: | InfoPath |
Value: C:\Users\admin\AppData\Local\Temp\{211C5685-1DE1-430E-BED3-1F364F1E16F3}\_is50AD | |||
| (PID) Process: | (596) Setup_GCPSuite.exe | Key: | HKEY_CURRENT_USER\Software\InstallShield\SuiteInstallers\{842D3FBA-EE54-4283-872A-DF315C1A4BCC} |
| Operation: | write | Name: | Reboot |
Value: 1 | |||
| (PID) Process: | (596) Setup_GCPSuite.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | {842D3FBA-EE54-4283-872A-DF315C1A4BCC} |
Value: "C:\Users\admin\AppData\Local\Temp\Setup_GCPSuite.exe" | |||
| (PID) Process: | (596) Setup_GCPSuite.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | delete value | Name: | {842D3FBA-EE54-4283-872A-DF315C1A4BCC} |
Value: "C:\Users\admin\AppData\Local\Temp\Setup_GCPSuite.exe" | |||
| (PID) Process: | (596) Setup_GCPSuite.exe | Key: | HKEY_CURRENT_USER\Software\InstallShield\SuiteInstallers\{842D3FBA-EE54-4283-872A-DF315C1A4BCC} |
| Operation: | delete value | Name: | Reboot |
Value: 1 | |||
| (PID) Process: | (596) Setup_GCPSuite.exe | Key: | HKEY_CURRENT_USER\Software\InstallShield\SuiteInstallers\{842D3FBA-EE54-4283-872A-DF315C1A4BCC} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (596) Setup_GCPSuite.exe | Key: | HKEY_CURRENT_USER\Software\InstallShield\SuiteInstallers |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
1
Suspicious files
0
Text files
18
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 596 | Setup_GCPSuite.exe | C:\Users\admin\AppData\Local\Temp\{211C5685-1DE1-430E-BED3-1F364F1E16F3}\setup.xml | xml | |
MD5:— | SHA256:— | |||
| 596 | Setup_GCPSuite.exe | C:\Users\admin\AppData\Local\Temp\{211C5685-1DE1-430E-BED3-1F364F1E16F3}\Setup_UI.dll | executable | |
MD5:— | SHA256:— | |||
| 596 | Setup_GCPSuite.exe | C:\Users\admin\AppData\Local\Temp\{211C5685-1DE1-430E-BED3-1F364F1E16F3}\Repair.png | image | |
MD5:937F2BFFFC27212329296A1D3E43A9C9 | SHA256:CC119589CA28D424A3561572F2C00784ED080E9412F42B0770F2D475F346D762 | |||
| 596 | Setup_GCPSuite.exe | C:\Users\admin\AppData\Local\Temp\{211C5685-1DE1-430E-BED3-1F364F1E16F3}\Custom.png | image | |
MD5:1D120A56EC5AF89EA087D13346E3C10A | SHA256:CDB5FD13AE58F93741FB7CCAB6C1AB74552B3880ADA692075B12DB140A9572D4 | |||
| 596 | Setup_GCPSuite.exe | C:\Users\admin\AppData\Local\Temp\{211C5685-1DE1-430E-BED3-1F364F1E16F3}\Remove.png | image | |
MD5:974078A6F927F6F91B1BCCB7C75CECD4 | SHA256:CC46733D81399047DDC6FD4D24E10D0ED6E2AFCB4D959B4F6821B0C370C0BA78 | |||
| 596 | Setup_GCPSuite.exe | C:\Users\admin\AppData\Local\Temp\{211C5685-1DE1-430E-BED3-1F364F1E16F3}\1034\License.txt | text | |
MD5:— | SHA256:— | |||
| 596 | Setup_GCPSuite.exe | C:\Users\admin\AppData\Local\Temp\{211C5685-1DE1-430E-BED3-1F364F1E16F3}\Folder.png | image | |
MD5:7B526924A8A5E6579896165E902F2587 | SHA256:32B2198A0223283C4A6C135A5EA3453F9F4D45BBD8BC11EEF973FA8BCA88ACDD | |||
| 596 | Setup_GCPSuite.exe | C:\Users\admin\AppData\Local\Temp\{211C5685-1DE1-430E-BED3-1F364F1E16F3}\1031\License.txt | text | |
MD5:— | SHA256:— | |||
| 596 | Setup_GCPSuite.exe | C:\Users\admin\AppData\Local\Temp\{211C5685-1DE1-430E-BED3-1F364F1E16F3}\1036\License.txt | text | |
MD5:— | SHA256:— | |||
| 596 | Setup_GCPSuite.exe | C:\Users\admin\AppData\Local\Temp\{211C5685-1DE1-430E-BED3-1F364F1E16F3}\1033\License.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report