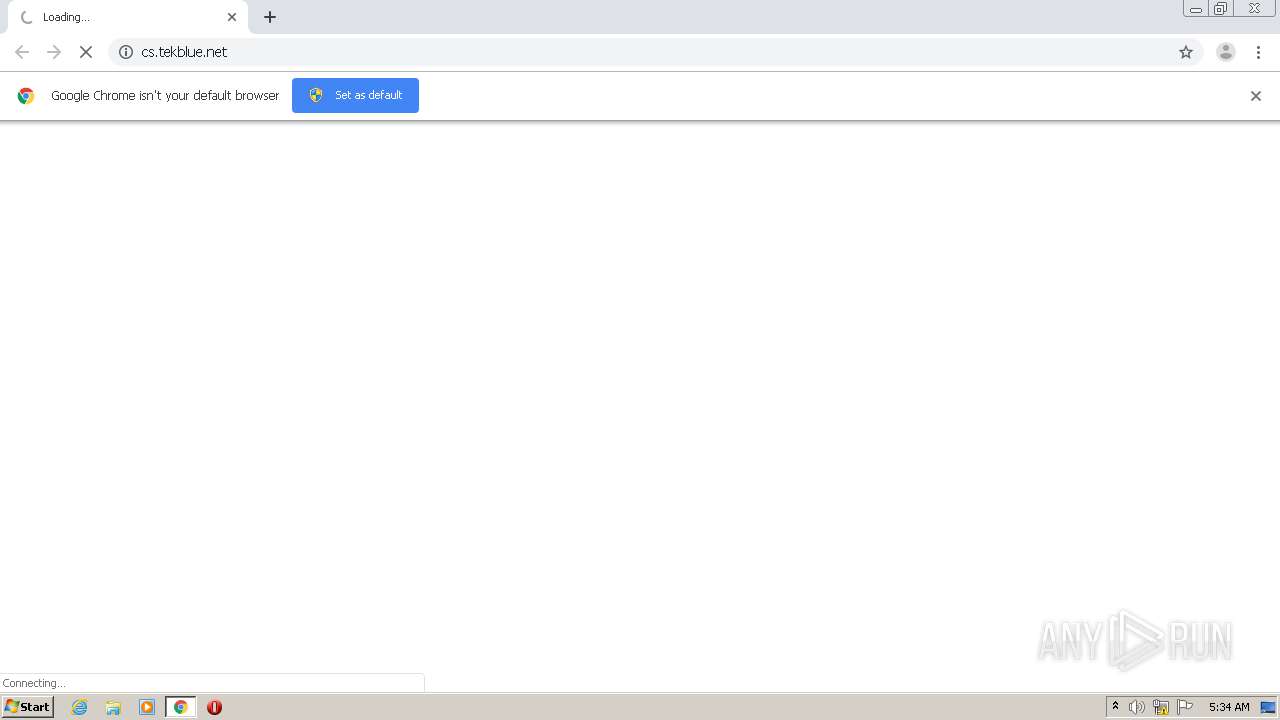
| URL: | http://cs.tekblue.net |
| Full analysis: | https://app.any.run/tasks/317f4c0f-e883-4c58-a972-068d70813eb2 |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 04:33:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | EB40AB8A5890E40F486A1C5F0C7A48BC |
| SHA1: | 02574CF81667812741EB2A3B4A0A1509A5765629 |
| SHA256: | 69C48AC4C829E0509FD915CE0D6BF471D3D1CB05555C298422BC09193192FA88 |
| SSDEEP: | 3:N1KdWlFCR:CUrS |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads settings of System Certificates
- chrome.exe (PID: 3764)
Reads the hosts file
- chrome.exe (PID: 3764)
- chrome.exe (PID: 300)
Application launched itself
- chrome.exe (PID: 300)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
15
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://cs.tekblue.net" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,16003018659970156517,7348505242233120808,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7311049579440036004 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2476 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,16003018659970156517,7348505242233120808,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16868540103290047480 --mojo-platform-channel-handle=1020 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,16003018659970156517,7348505242233120808,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8846201943817917153 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2120 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f15a9d0,0x6f15a9e0,0x6f15a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,16003018659970156517,7348505242233120808,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6057702767853897063 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2804 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,16003018659970156517,7348505242233120808,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=690675634073784028 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2536 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,16003018659970156517,7348505242233120808,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6735731836055397232 --mojo-platform-channel-handle=3080 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,16003018659970156517,7348505242233120808,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12818784420778582128 --mojo-platform-channel-handle=3436 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,16003018659970156517,7348505242233120808,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=7511691385053829526 --mojo-platform-channel-handle=884 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
638
Read events
572
Write events
62
Delete events
4
Modification events
| (PID) Process: | (3428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 300-13245914055418875 |
Value: 259 | |||
| (PID) Process: | (300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3228-13245745346152343 |
Value: 0 | |||
| (PID) Process: | (300) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
14
Text files
63
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F740AC7-12C.pma | — | |
MD5:— | SHA256:— | |||
| 300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c9115cab-6a79-4327-bafe-d4bd88ad562b.tmp | — | |
MD5:— | SHA256:— | |||
| 300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000046.dbtmp | — | |
MD5:— | SHA256:— | |||
| 300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF3bbc9a.TMP | text | |
MD5:— | SHA256:— | |||
| 300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | — | |
MD5:— | SHA256:— | |||
| 300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF3bbca9.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
15
DNS requests
11
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3764 | chrome.exe | GET | 200 | 199.59.242.155:80 | http://tracking.bodis.com/tlpv?d=eyJkb21haW5fbmFtZSI6InRla2JsdWUubmV0Iiwic2VydmVyIjo5MSwidGVybXMiOltdLCJVUkwiOiJodHRwOlwvXC93dzEudGVrYmx1ZS5uZXRcLyIsInJlZmVycmVyIjoiIiwiZHciOjEyODAsImRoIjo1NzIsInJ3IjoxMjgwLCJyaCI6NzIwfQ&t=1601440479&abp=0 | US | — | — | whitelisted |
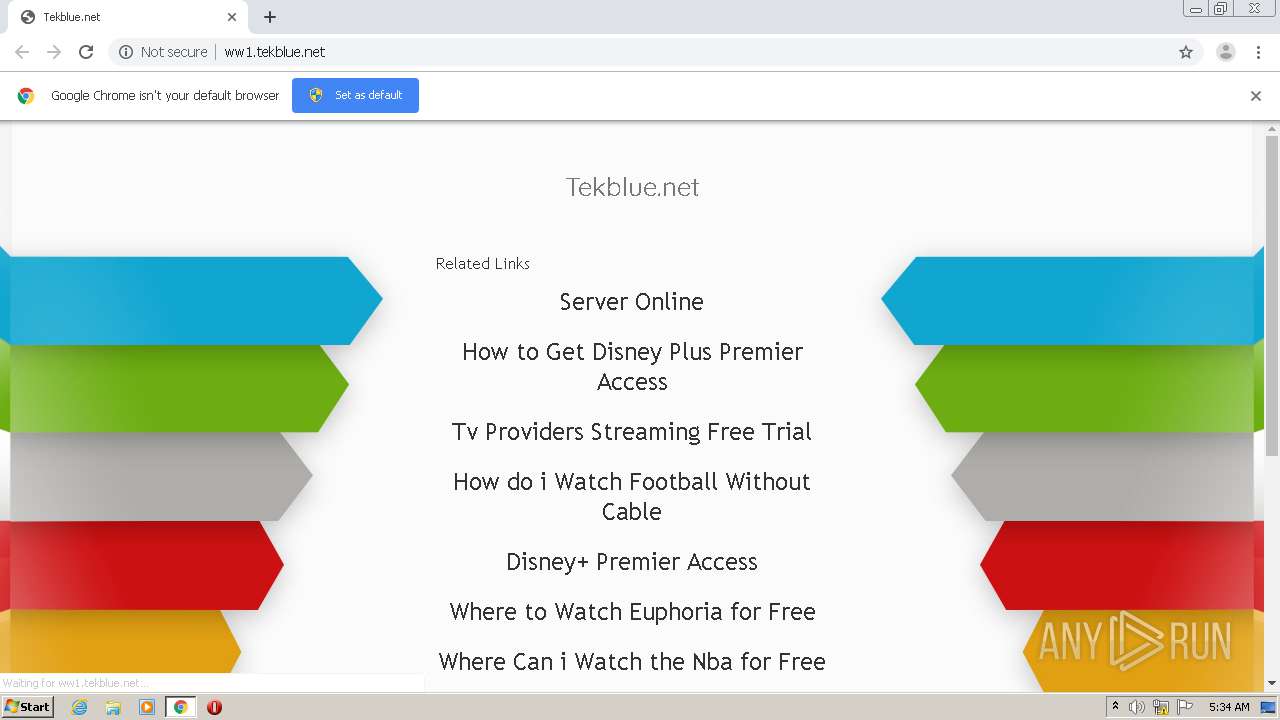
3764 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://ww1.tekblue.net/public/legacy/10352/resources/arrows-bg-ext.png | US | image | 1.12 Kb | malicious |
3764 | chrome.exe | GET | 404 | 199.59.242.153:80 | http://ww1.tekblue.net/favicon.ico | US | html | 3.93 Kb | malicious |
3764 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://ww1.tekblue.net/ | US | html | 3.93 Kb | malicious |
3764 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://ww1.tekblue.net/px.gif?ch=2&rn=1.826927901145229 | US | image | 42 b | malicious |
3764 | chrome.exe | GET | 302 | 94.229.72.116:80 | http://cs.tekblue.net/ | GB | text | 11 b | malicious |
3764 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://ww1.tekblue.net/public/legacy/10352/resources/arrows-bg.jpg | US | image | 93.6 Kb | malicious |
3764 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://ww1.tekblue.net/glp?r=&u=http%3A%2F%2Fww1.tekblue.net%2F&rw=1280&rh=720&ww=1280&wh=572 | US | text | 9.84 Kb | malicious |
3764 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://ww1.tekblue.net/px.gif?ch=1&rn=1.826927901145229 | US | image | 42 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3764 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3764 | chrome.exe | 94.229.72.116:80 | cs.tekblue.net | UK Dedicated Servers Limited | GB | malicious |
3764 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
3764 | chrome.exe | 199.59.242.153:80 | ww1.tekblue.net | Bodis, LLC | US | malicious |
3764 | chrome.exe | 216.58.208.36:443 | www.google.com | Google Inc. | US | whitelisted |
3764 | chrome.exe | 172.217.21.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
— | — | 216.58.208.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
— | — | 199.59.242.155:80 | tracking.bodis.com | Bodis, LLC | US | suspicious |
3764 | chrome.exe | 216.58.208.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
3764 | chrome.exe | 216.58.207.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
cs.tekblue.net |
| malicious |
accounts.google.com |
| shared |
ww1.tekblue.net |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
sedo.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
tracking.bodis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3764 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Drive-by Evil Redirector |