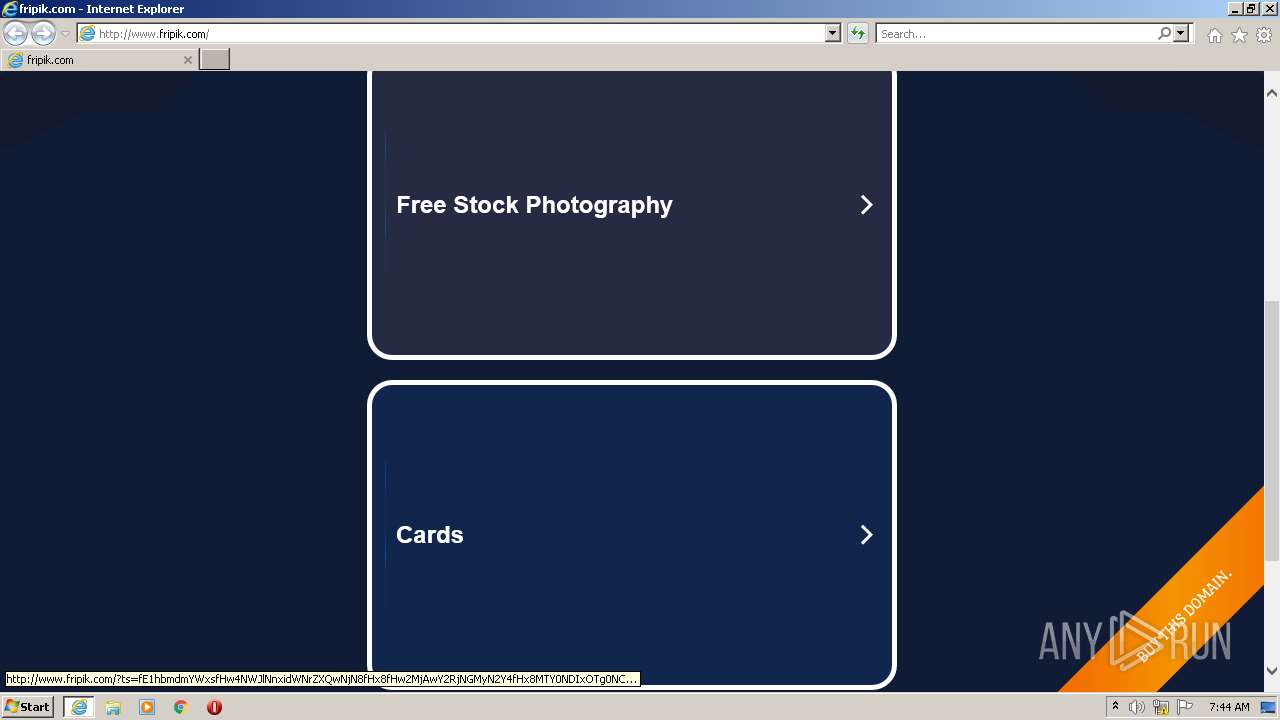
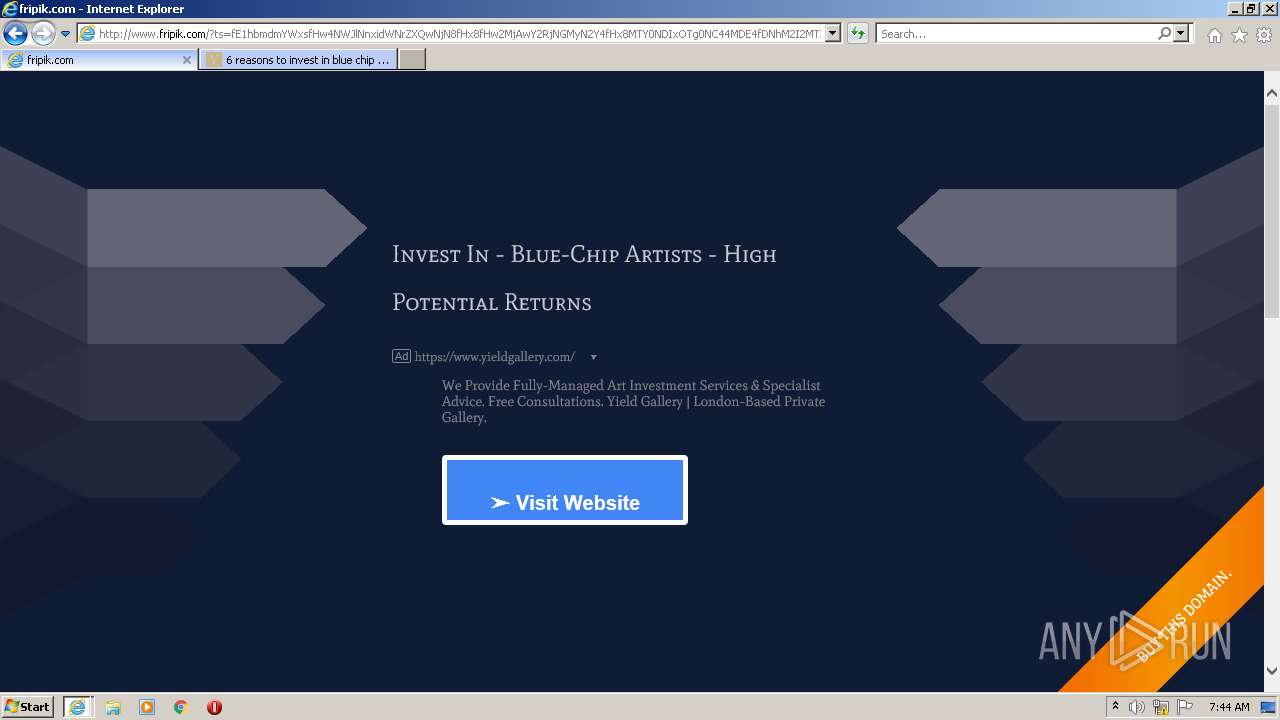
| URL: | http://www.fripik.com |
| Full analysis: | https://app.any.run/tasks/0b6d92b5-1510-41bf-af27-3a92502b84a0 |
| Verdict: | Malicious activity |
| Analysis date: | February 07, 2022, 07:44:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F11B238E7C88D3AB11D39FFE56BA6B0D |
| SHA1: | 3C05B0FC9C51283A32EB207A901905685882CD75 |
| SHA256: | 69B38E82DB44B6A6E3DE364805671A88243B73FF23498DD53133A179F592D240 |
| SSDEEP: | 3:N1KJS4LkyTn:Cc4YyTn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 532)
- iexplore.exe (PID: 3444)
- iexplore.exe (PID: 2920)
INFO
Checks supported languages
- iexplore.exe (PID: 1408)
- iexplore.exe (PID: 532)
- iexplore.exe (PID: 3444)
- iexplore.exe (PID: 2920)
Reads settings of System Certificates
- iexplore.exe (PID: 3444)
- iexplore.exe (PID: 532)
- iexplore.exe (PID: 1408)
- iexplore.exe (PID: 2920)
Reads the computer name
- iexplore.exe (PID: 1408)
- iexplore.exe (PID: 532)
- iexplore.exe (PID: 3444)
- iexplore.exe (PID: 2920)
Changes internet zones settings
- iexplore.exe (PID: 1408)
Application launched itself
- iexplore.exe (PID: 1408)
Reads internet explorer settings
- iexplore.exe (PID: 532)
- iexplore.exe (PID: 3444)
- iexplore.exe (PID: 2920)
Creates files in the user directory
- iexplore.exe (PID: 532)
- iexplore.exe (PID: 3444)
- iexplore.exe (PID: 2920)
Checks Windows Trust Settings
- iexplore.exe (PID: 532)
- iexplore.exe (PID: 1408)
- iexplore.exe (PID: 3444)
- iexplore.exe (PID: 2920)
Changes settings of System certificates
- iexplore.exe (PID: 1408)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1408 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1408 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://www.fripik.com" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2920 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1408 CREDAT:2954523 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3444 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1408 CREDAT:660753 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
37 001
Read events
36 792
Write events
207
Delete events
2
Modification events
| (PID) Process: | (1408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30940150 | |||
| (PID) Process: | (1408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30940150 | |||
| (PID) Process: | (1408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
34
Text files
151
Unknown types
54
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 532 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\js3caf[1].js | text | |
MD5:CCE7F943EC8E7B4BA13BE4ABA6B463D9 | SHA256:BA5B7354353B0EEC1637564DAE072FEE662A5B9862F6BF7ED5E60A5A76F2EF44 | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:0D029B83564CC3E2C7E3EEFF357CD56F | SHA256:80162FF00221C0A074B36EF8A8F38E4847920D08BEA9336AFC34E8E38A26CB36 | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:03C9994CEDC2C4AF0983FB17AC969B44 | SHA256:D23028DF9D38A9BBED765BF5375B5B2FBA4D7803BF70A7DE84028C5DF6D07B31 | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\style[1].css | text | |
MD5:96F84D0985AF87B4D4F6AE8816F9C5C5 | SHA256:93A1109ADA0CD55DEDEAF7E9C4251A7F91AC3C3E1AB85E25E37B6CD4E47D504B | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\style[1].css | text | |
MD5:46207BE7CBD5A4A547EE2DF4DD20A65B | SHA256:55B7102FC641DA51DBCB8FCB65E722D07DFED736EF0D1269640A8DB4E0F55AA4 | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:5BBA5F7F9490DE9800058EC7D03B768F | SHA256:AC9BFD7920062416F2C0C52B02159E6B88EA5FC247AF65335D2CF567529CD47E | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\css[1].css | text | |
MD5:E257A43F12A7E3A5D715839841C6E046 | SHA256:E7DF41ABA61AD3DA0891A3A76E6832AE5C96A3DD8150BE793124018CCB01BF8A | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\HJ0G948S.htm | html | |
MD5:8F2D088BAFB118E8220637B0F927962A | SHA256:CE40C4B5CADBAEA661705D2B86808C5B83C4C6EAD6446AB5FA6F89B12044B24E | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F07644E38ED7C9F37D11EEC6D4335E02_2B2BCCF5DEF5DB0836949F960BC55B50 | der | |
MD5:D56461A40DFA3932FED5FA2AE930AA63 | SHA256:1488C888AC6A4D4210D489362250F0D68C6F7418DFA4CC1C22C99C659755AC19 | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | der | |
MD5:64E9B8BB98E2303717538CE259BEC57D | SHA256:76BD459EC8E467EFC3E3FB94CB21B9C77A2AA73C9D4C0F3FAF823677BE756331 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
55
TCP/UDP connections
167
DNS requests
43
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
532 | iexplore.exe | GET | 200 | 185.53.178.50:80 | http://www.fripik.com/ | DE | html | 5.24 Kb | malicious |
532 | iexplore.exe | GET | 200 | 23.32.238.178:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c6b966393682f9ed | US | compressed | 4.70 Kb | whitelisted |
532 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
532 | iexplore.exe | GET | 200 | 65.9.58.42:80 | http://d1lxhc4jvstzrp.cloudfront.net/scripts/js3caf.js | US | text | 6.84 Kb | shared |
532 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDIRy5Lqyj5dAoAAAABLgV%2F | US | der | 472 b | whitelisted |
532 | iexplore.exe | GET | 200 | 65.9.58.42:80 | http://d1lxhc4jvstzrp.cloudfront.net/themes/mangfall_51416fbdb/img/arrows.png | US | image | 11.1 Kb | shared |
532 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://fonts.gstatic.com/s/portlligatslab/v19/LDIpaoiQNgArA8kR7ulhZ8P_NYOsg70R8A.woff | US | woff | 14.5 Kb | whitelisted |
532 | iexplore.exe | GET | 200 | 185.53.178.50:80 | http://www.fripik.com/track.php?domain=fripik.com&toggle=browserjs&uid=MTY0NDIxOTg0NC43OTY3OjcyNzkwYmUwZWU5YmRjMDRjNjQzNGE0YmM2MGMwMGI3YjY0MzVkZmNhMDI1NTE3ZGU3MTU3NGY5NGIxZDVhZTA6NjIwMGNkYzRjMjgxOA%3D%3D | DE | binary | 20 b | malicious |
1408 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
532 | iexplore.exe | GET | 200 | 142.250.186.106:80 | http://fonts.googleapis.com/css?family=Port+Lligat+Slab | US | text | 192 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
532 | iexplore.exe | 185.53.178.50:80 | www.fripik.com | Team Internet AG | DE | malicious |
532 | iexplore.exe | 172.217.16.132:80 | www.google.com | Google Inc. | US | whitelisted |
532 | iexplore.exe | 142.250.186.106:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
532 | iexplore.exe | 23.32.238.178:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
532 | iexplore.exe | 172.217.18.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
532 | iexplore.exe | 142.250.184.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
532 | iexplore.exe | 142.250.184.202:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
— | — | 172.217.18.99:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
— | — | 142.250.184.202:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
532 | iexplore.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.fripik.com |
| malicious |
www.google.com |
| malicious |
d1lxhc4jvstzrp.cloudfront.net |
| shared |
fonts.googleapis.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |