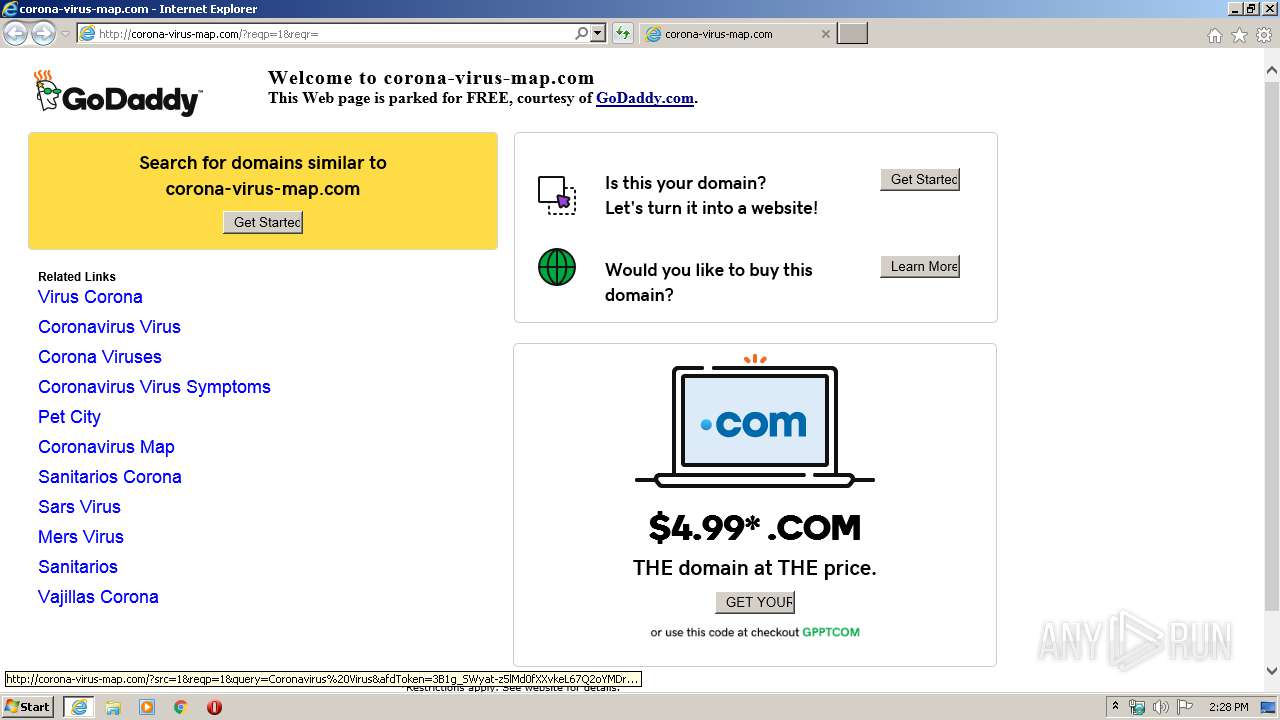
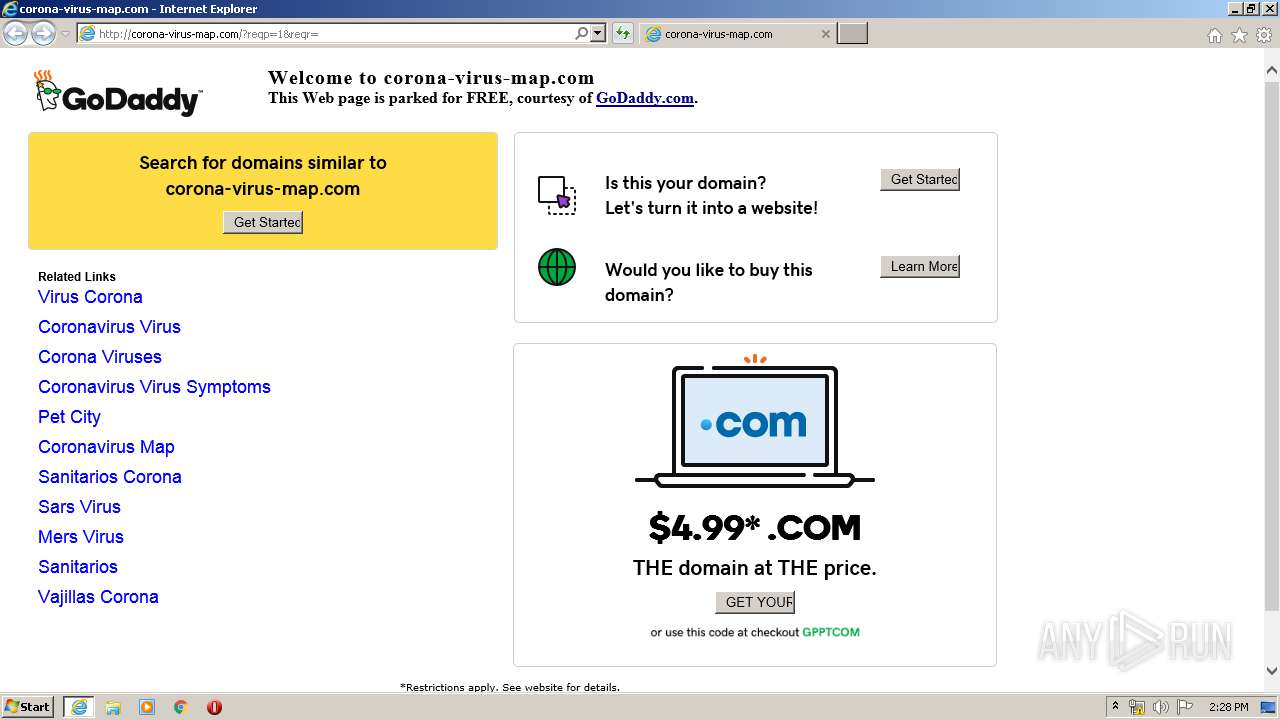
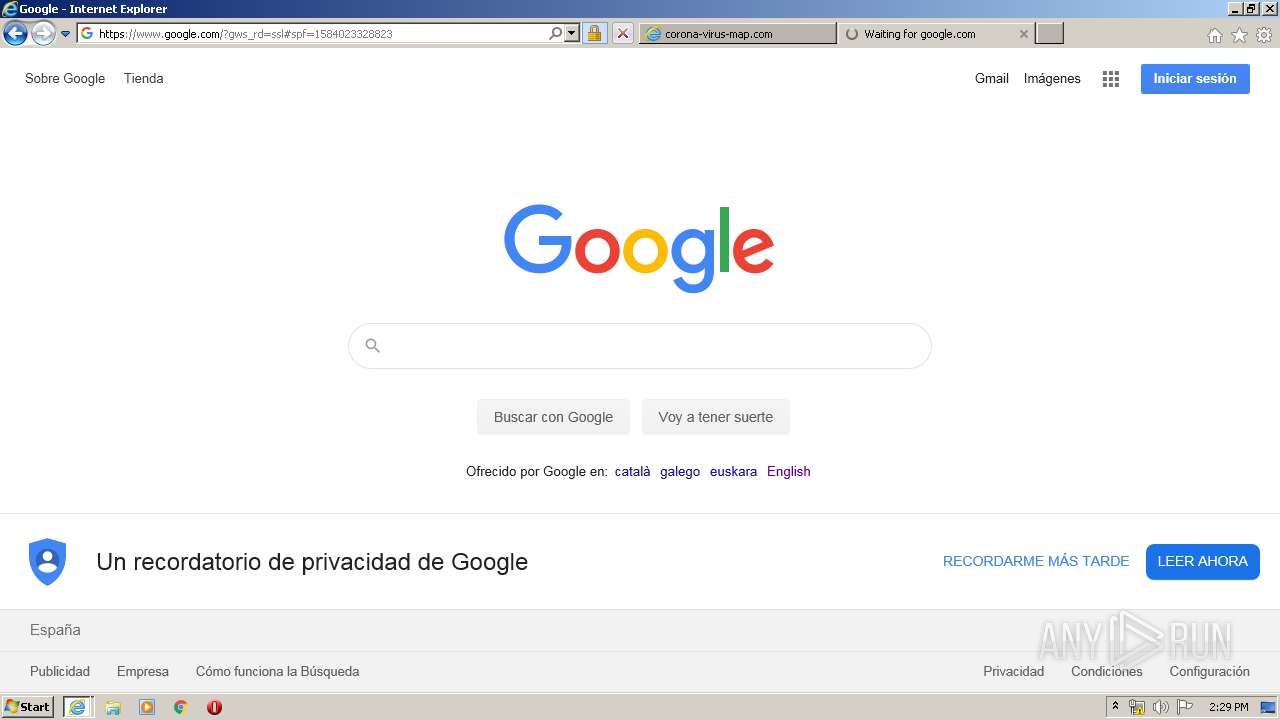
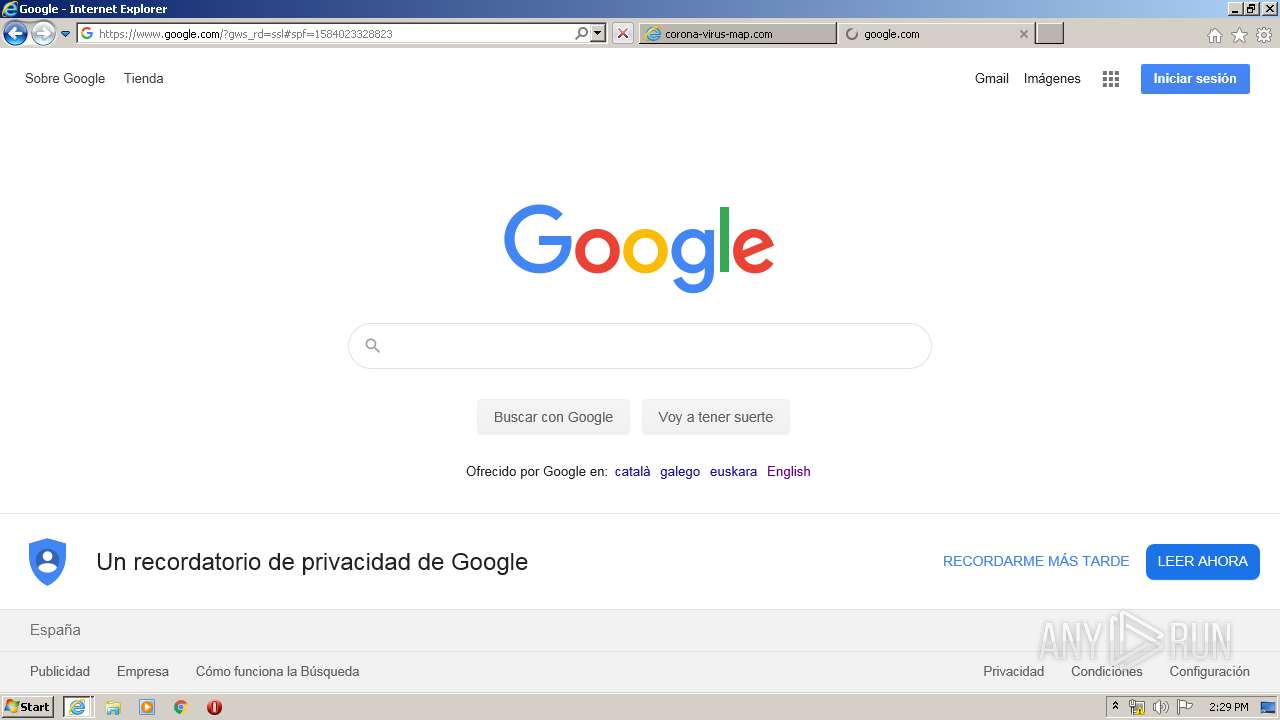
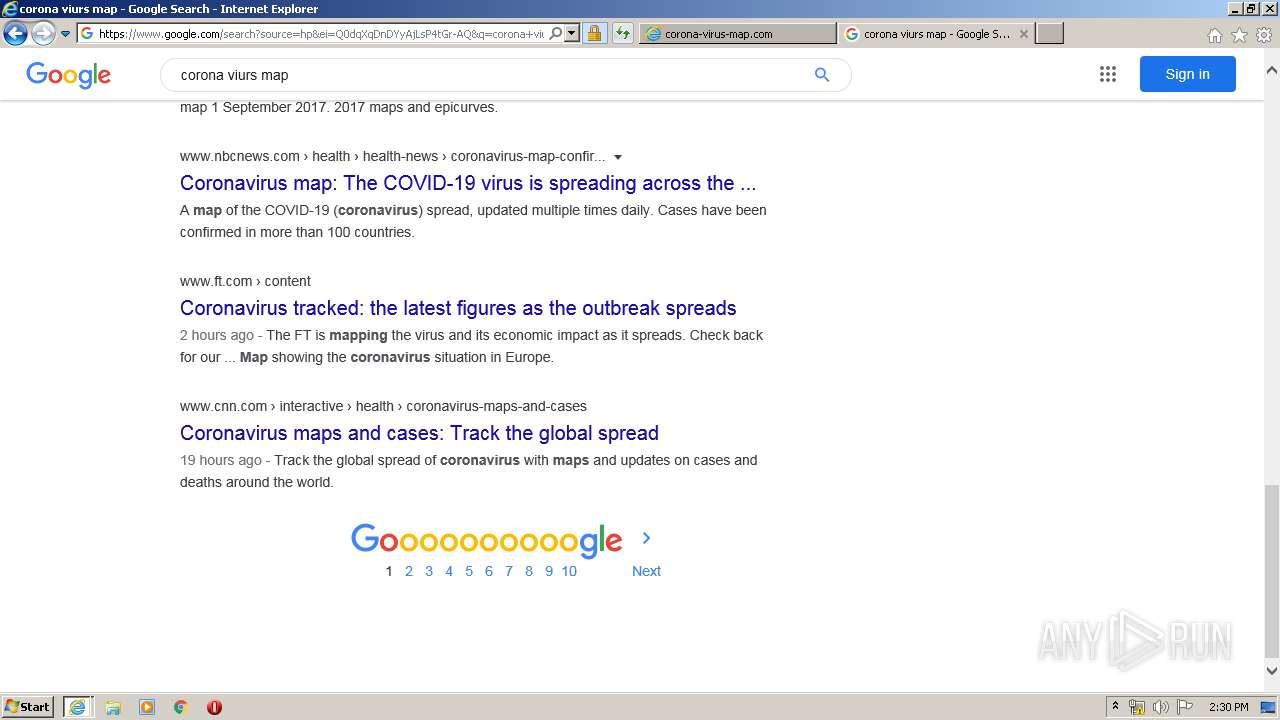
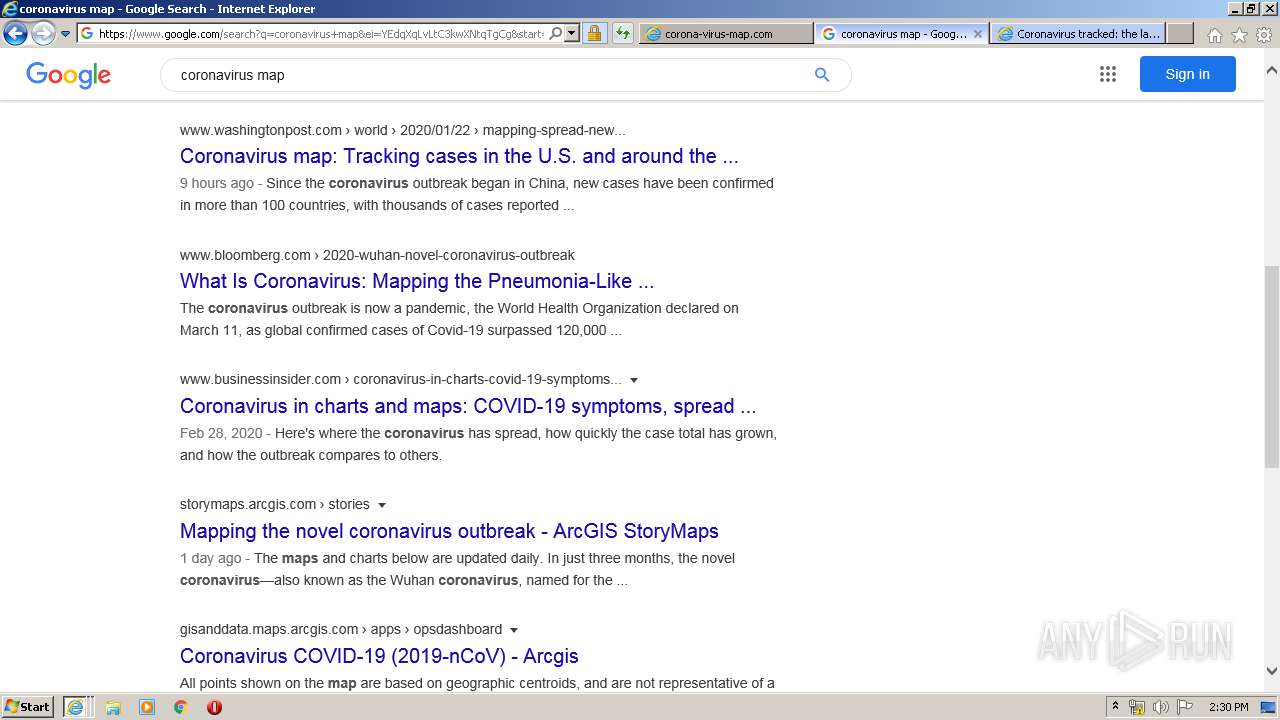
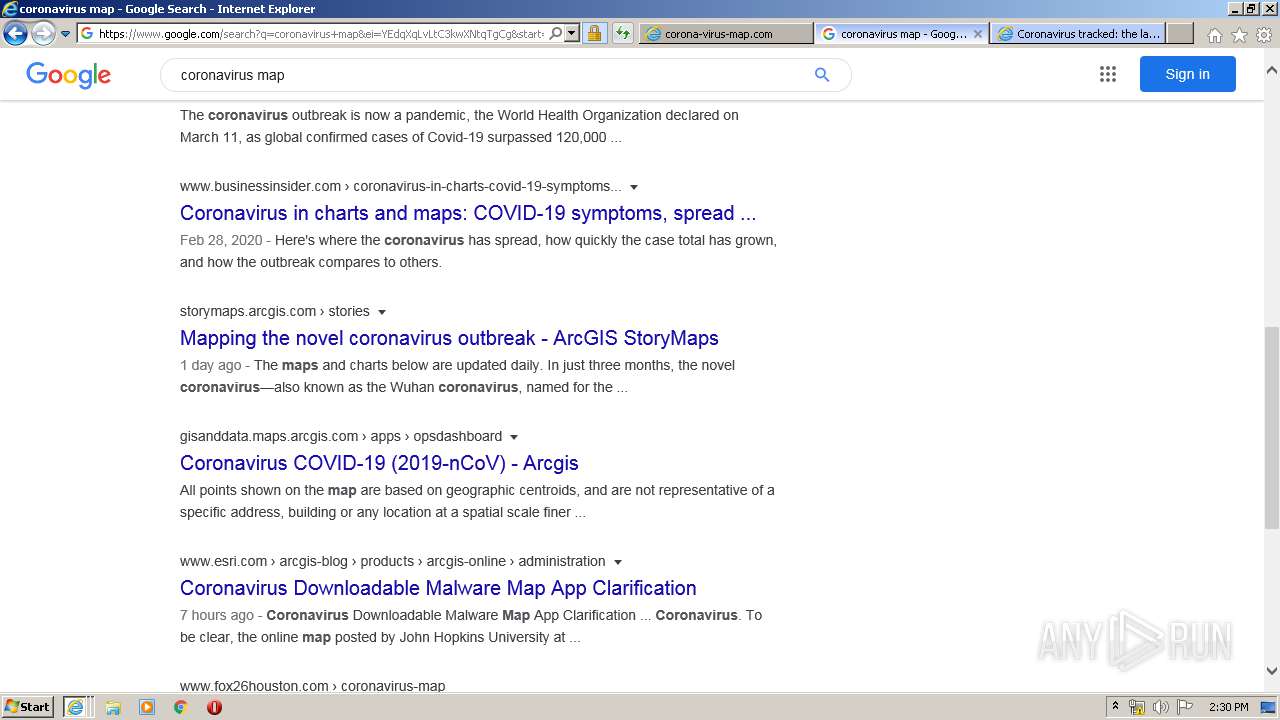
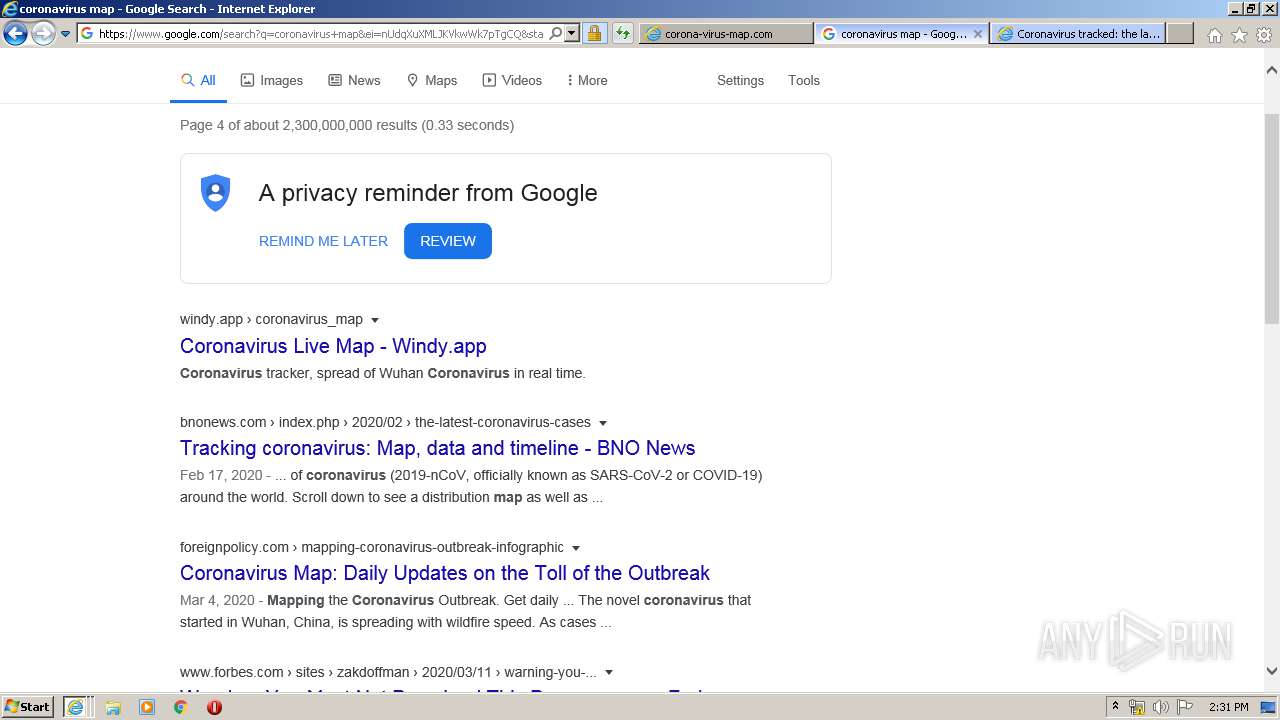
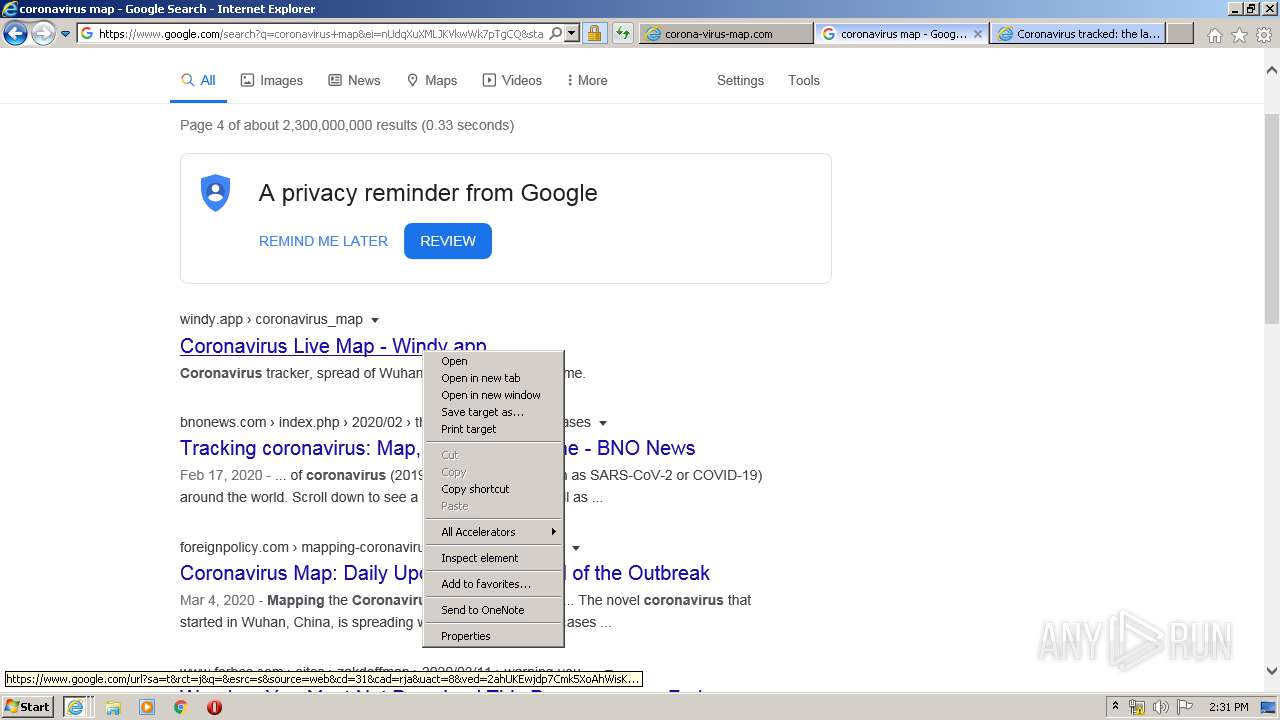
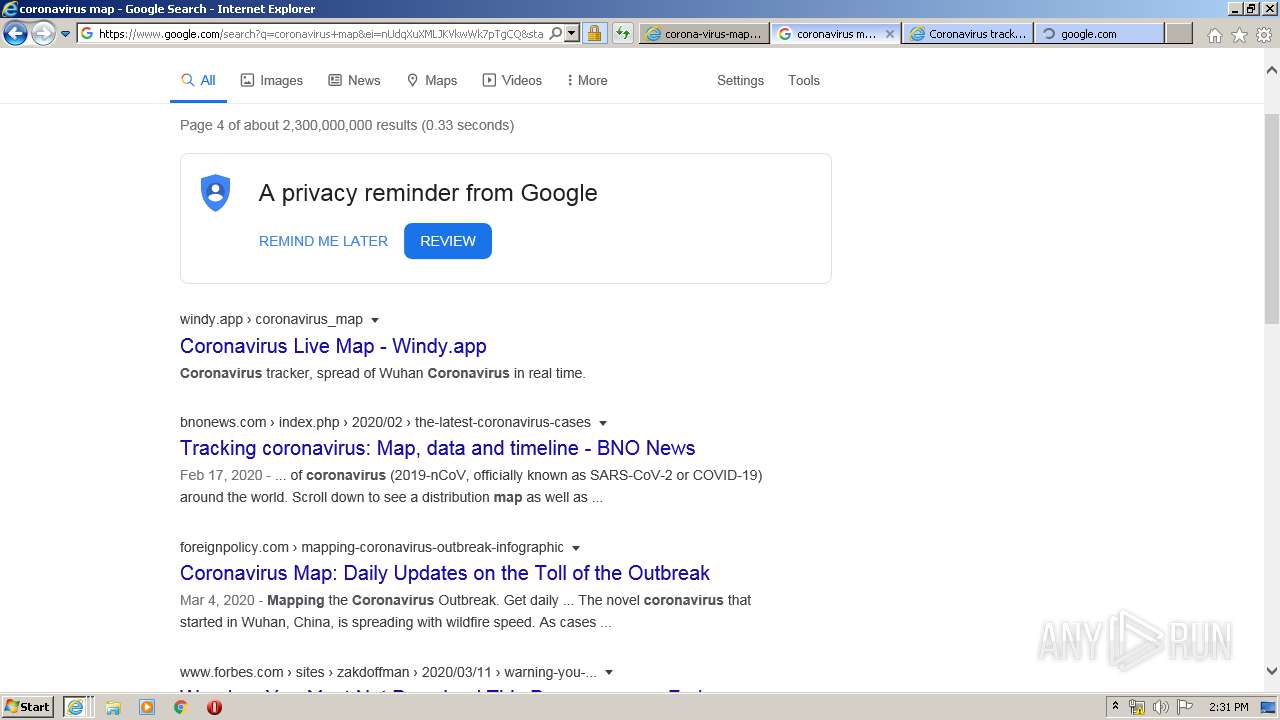
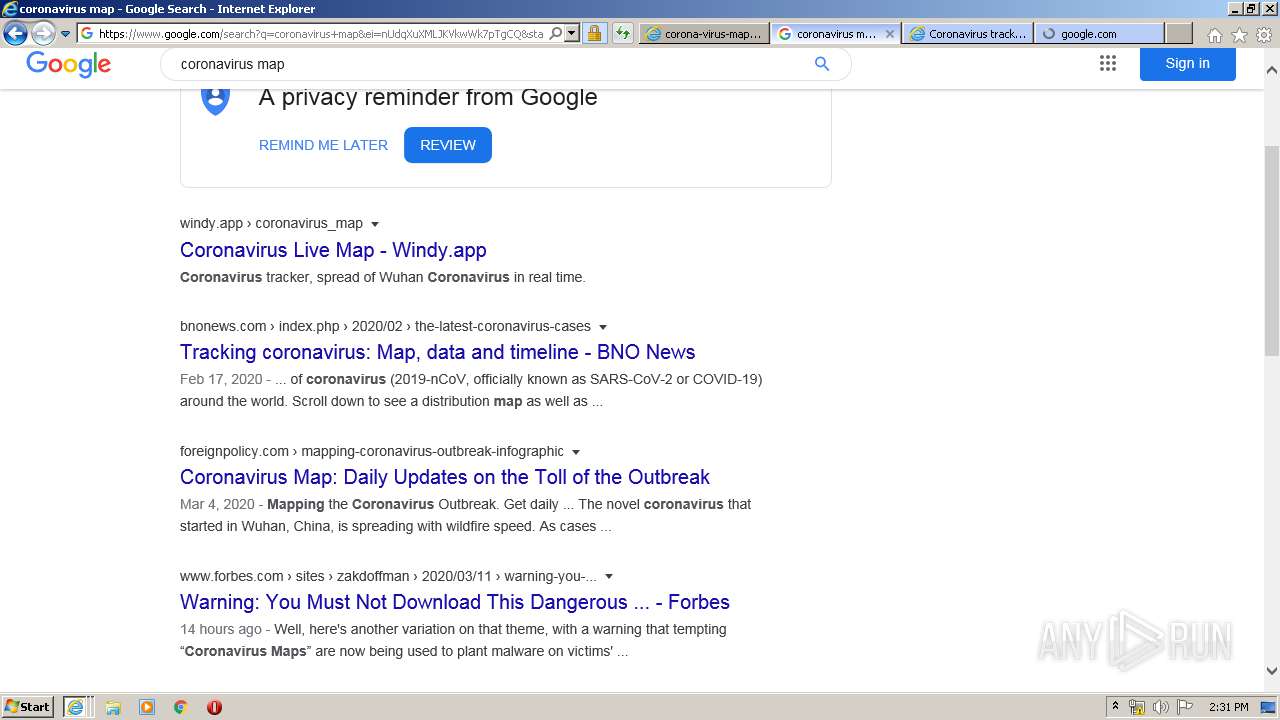
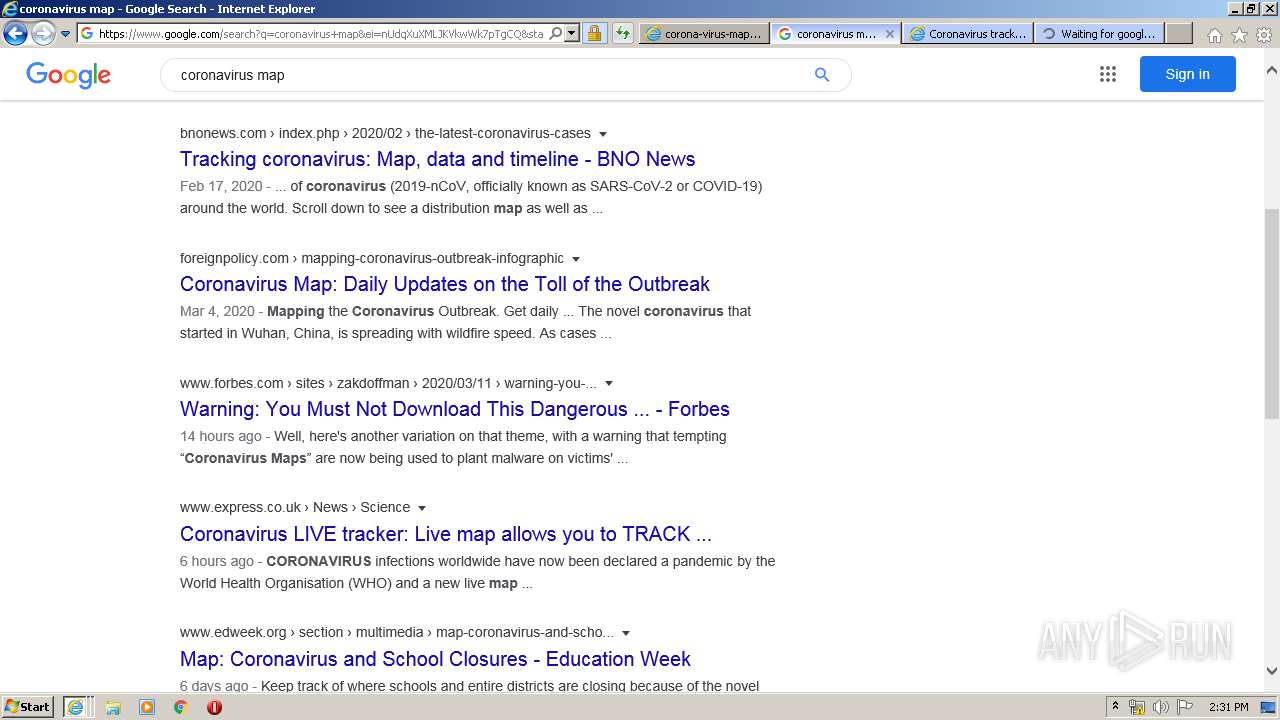
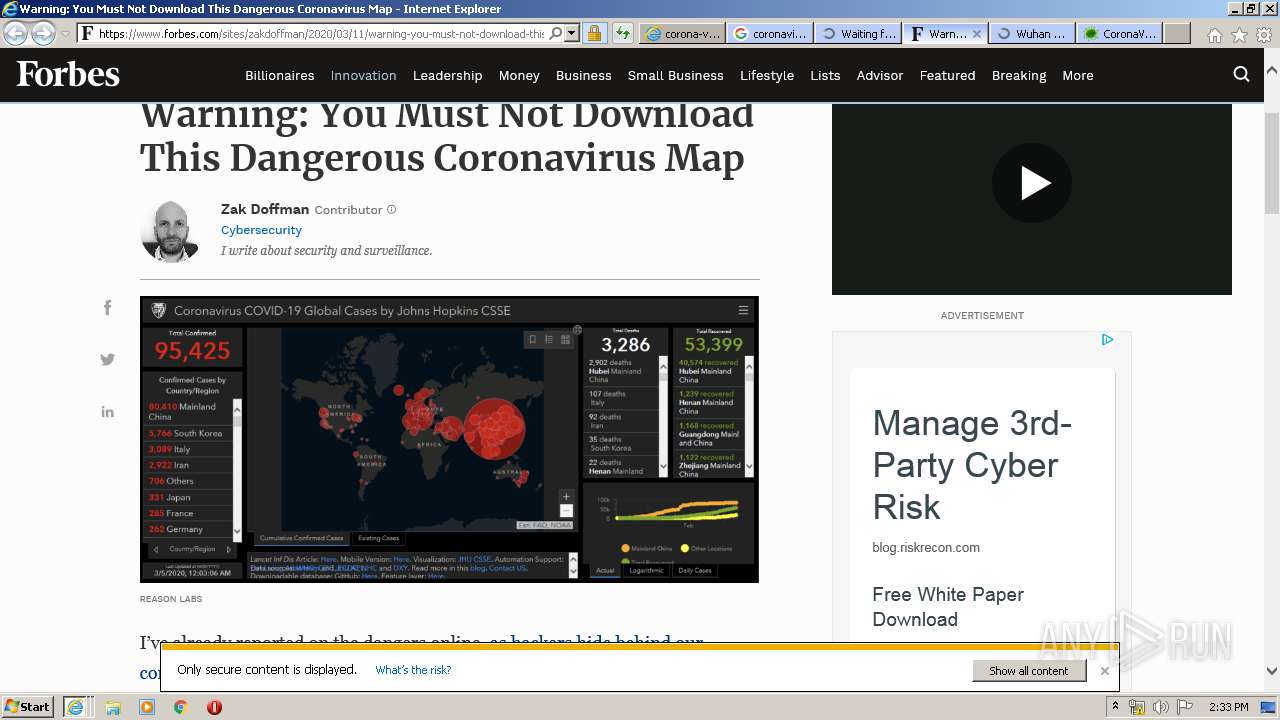
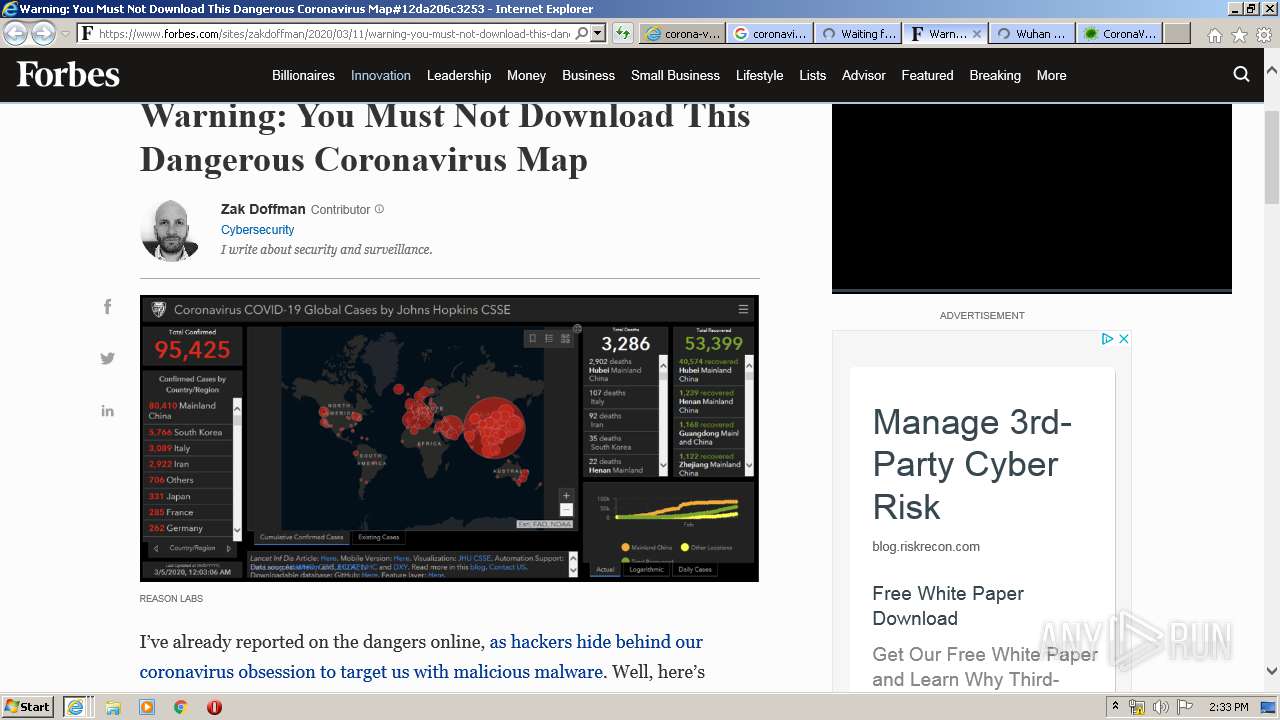
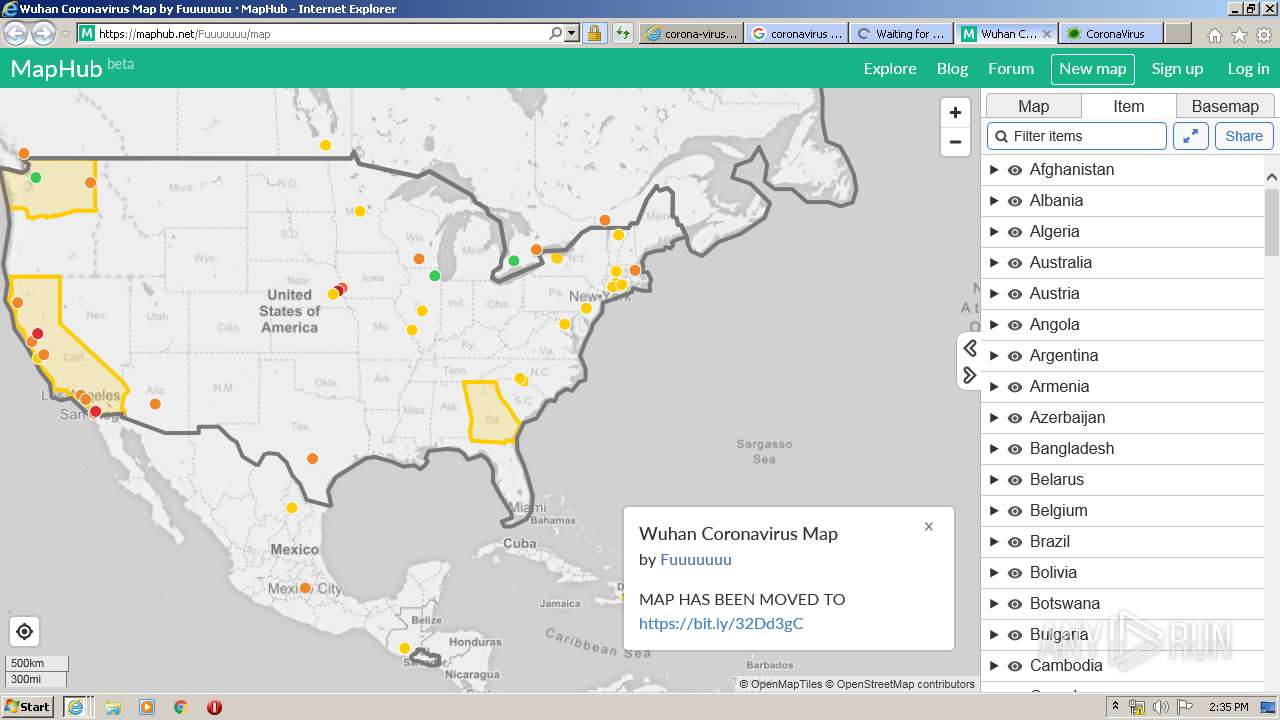
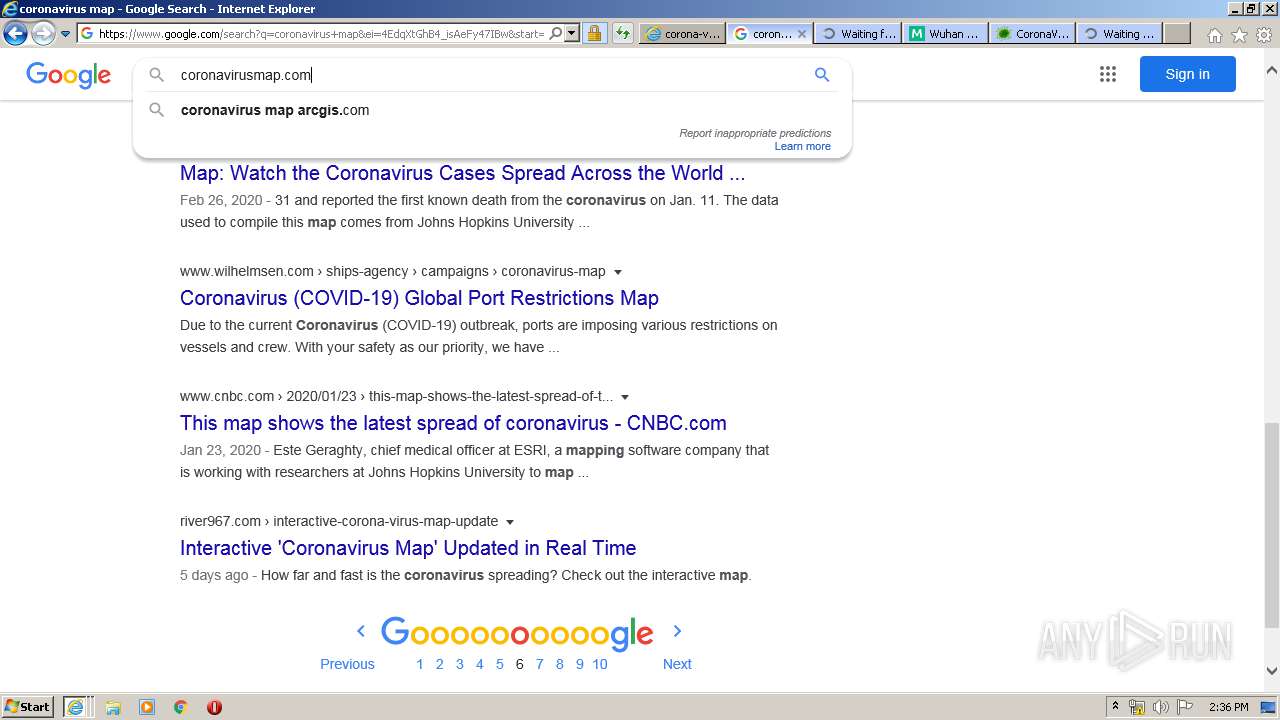
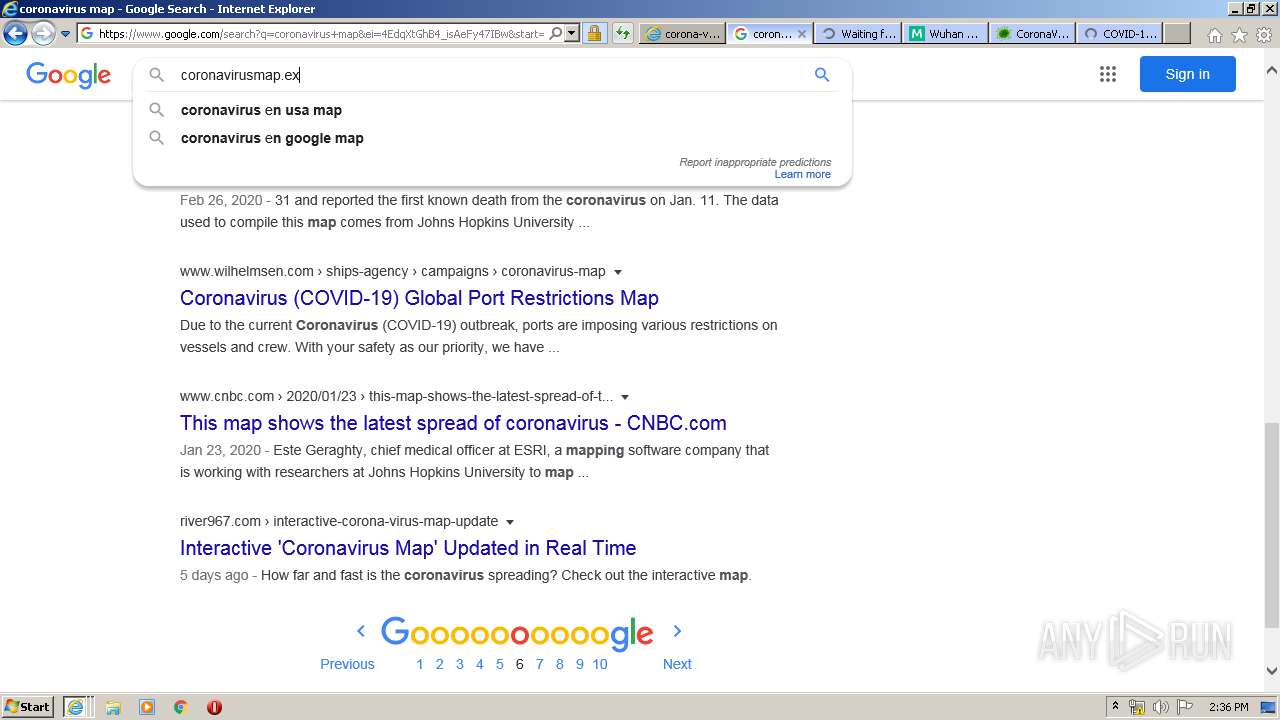
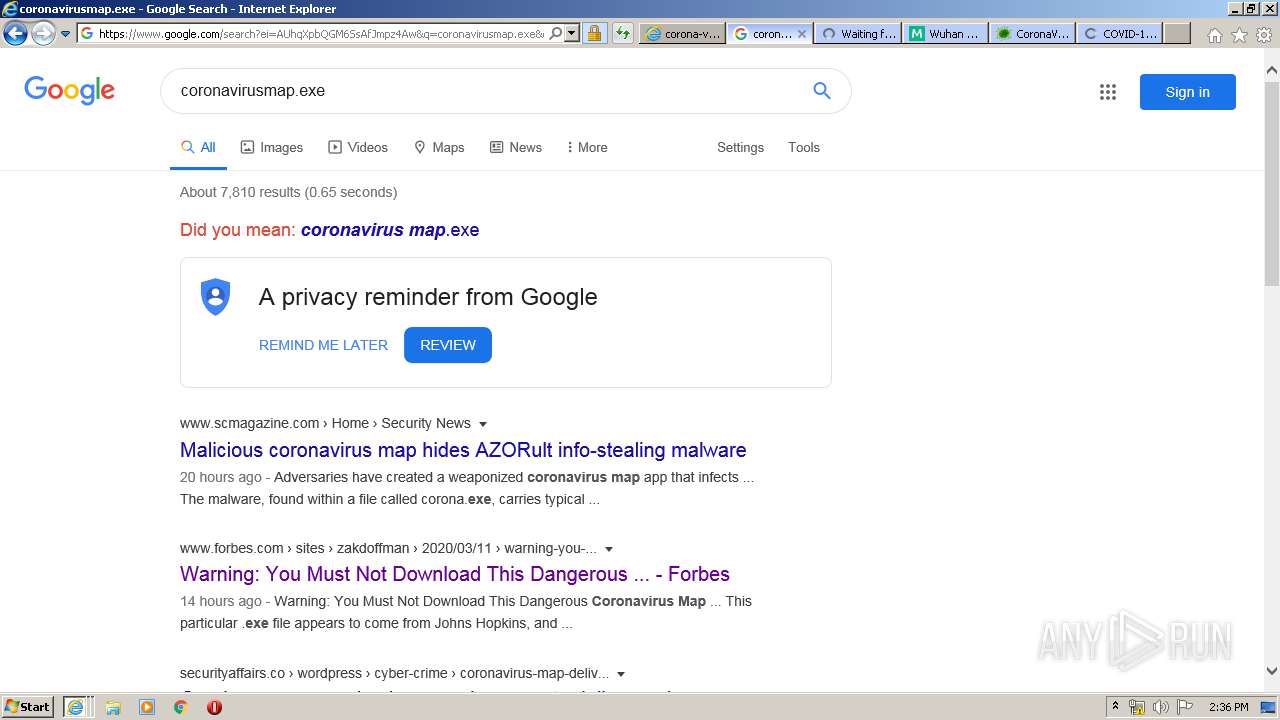
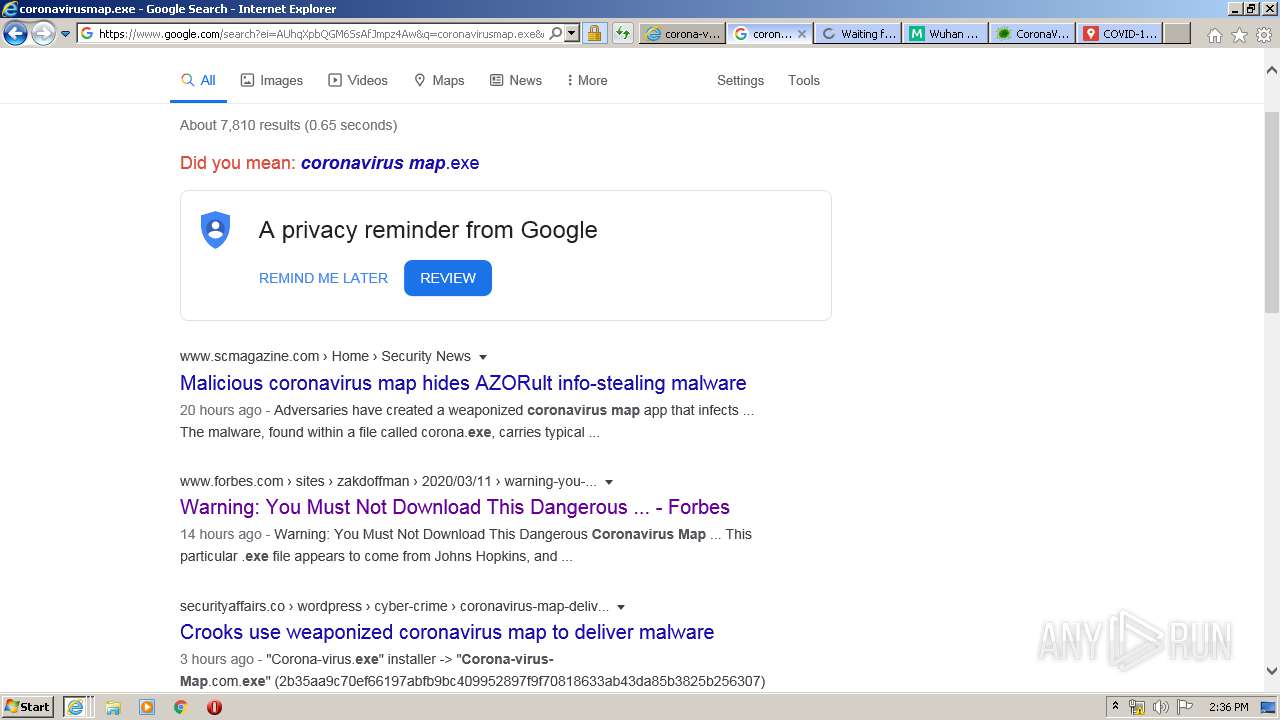
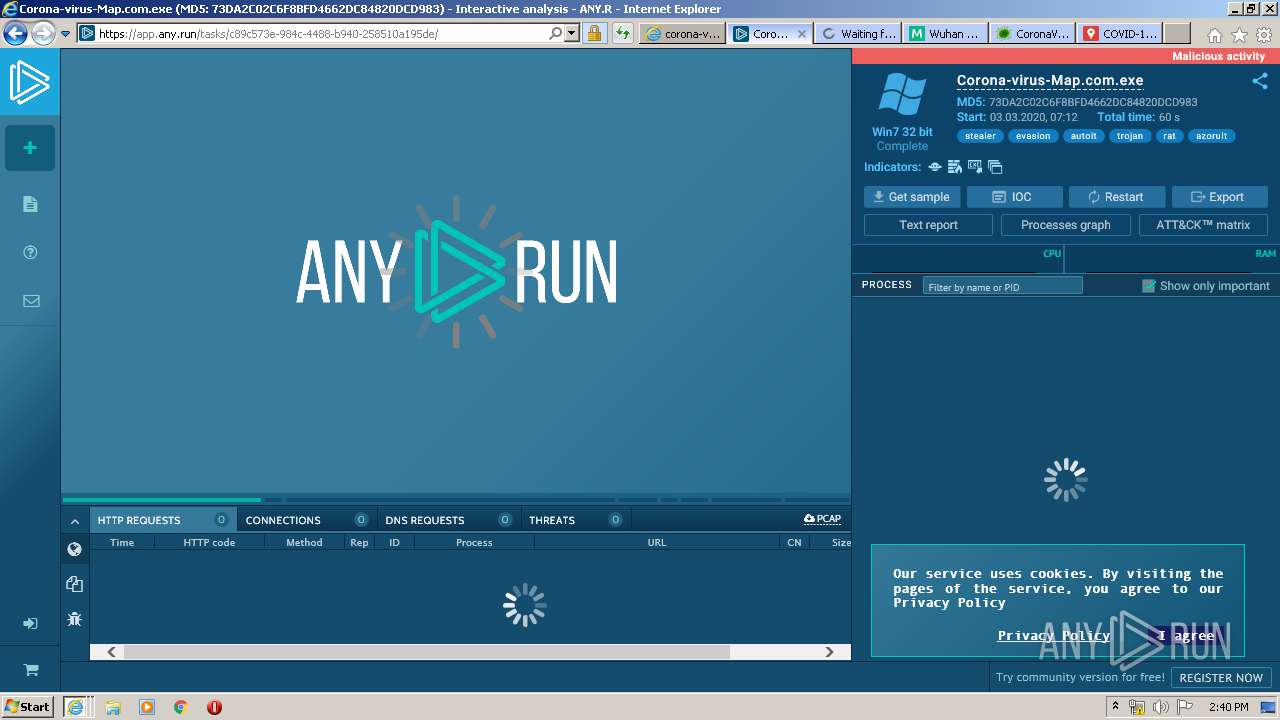
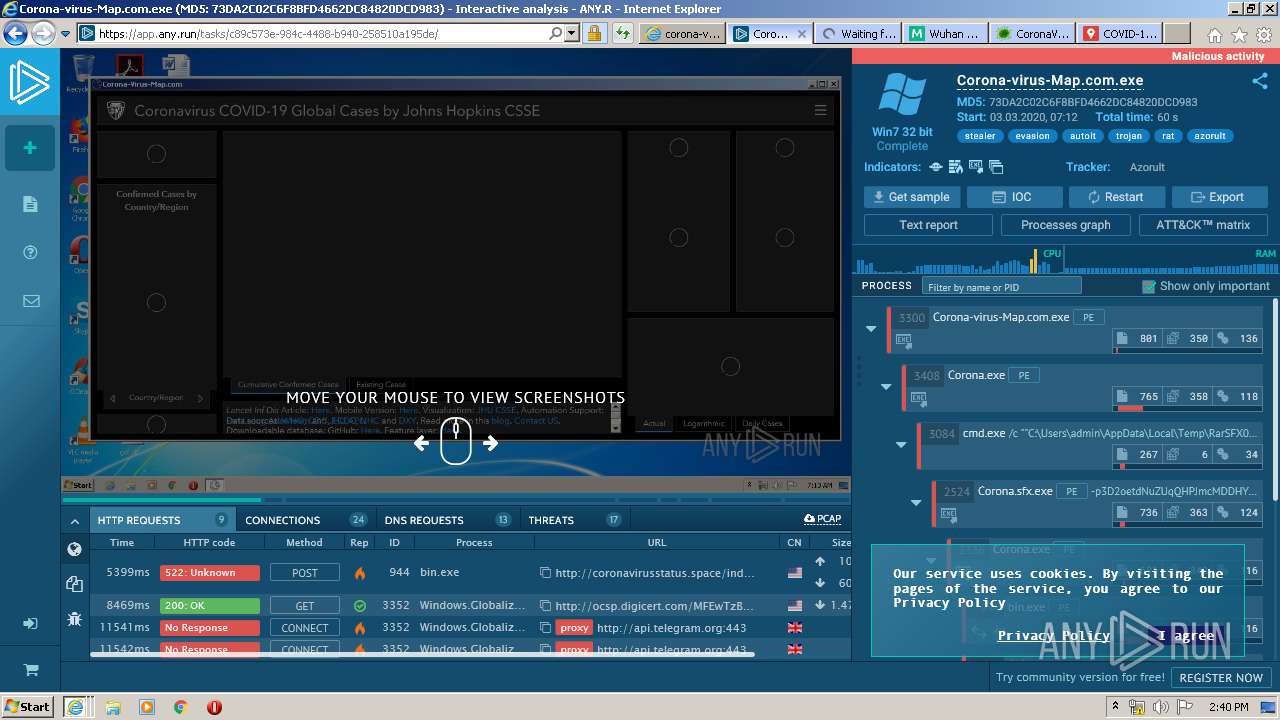
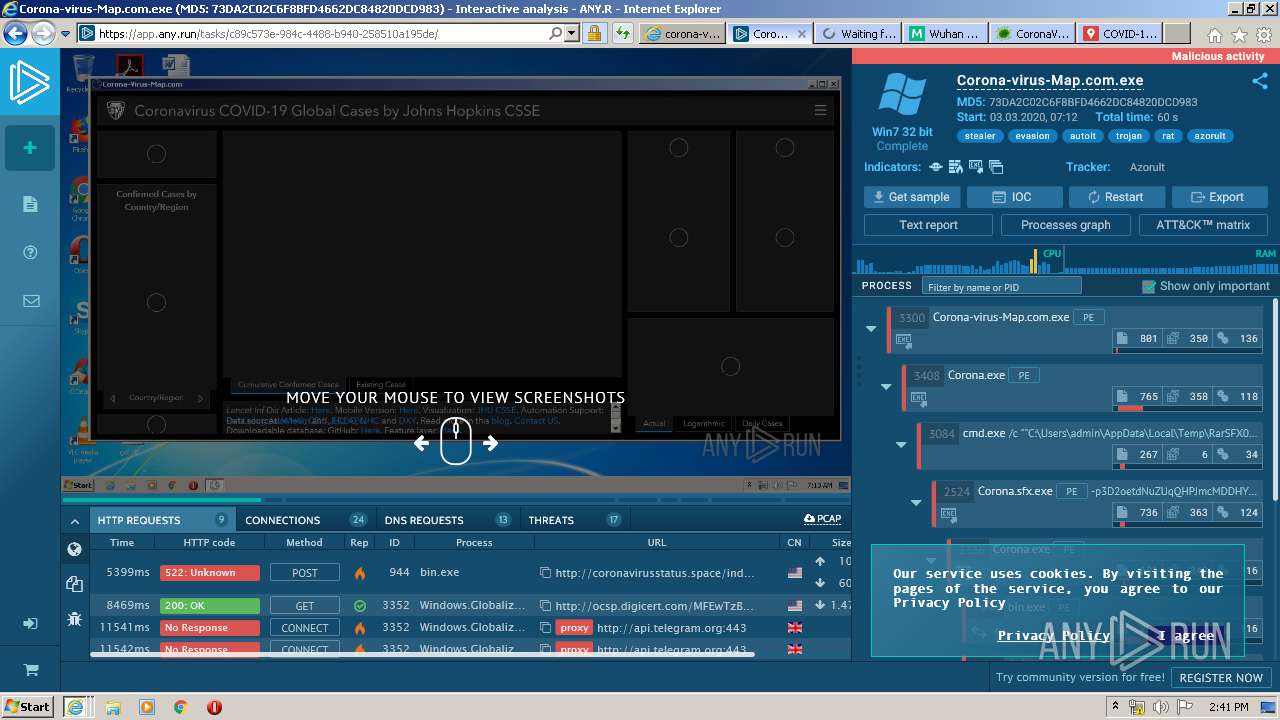
| URL: | http://www.Corona-Virus-Map.com |
| Full analysis: | https://app.any.run/tasks/f3a039c4-c81d-423b-8c6c-4cdebc188141 |
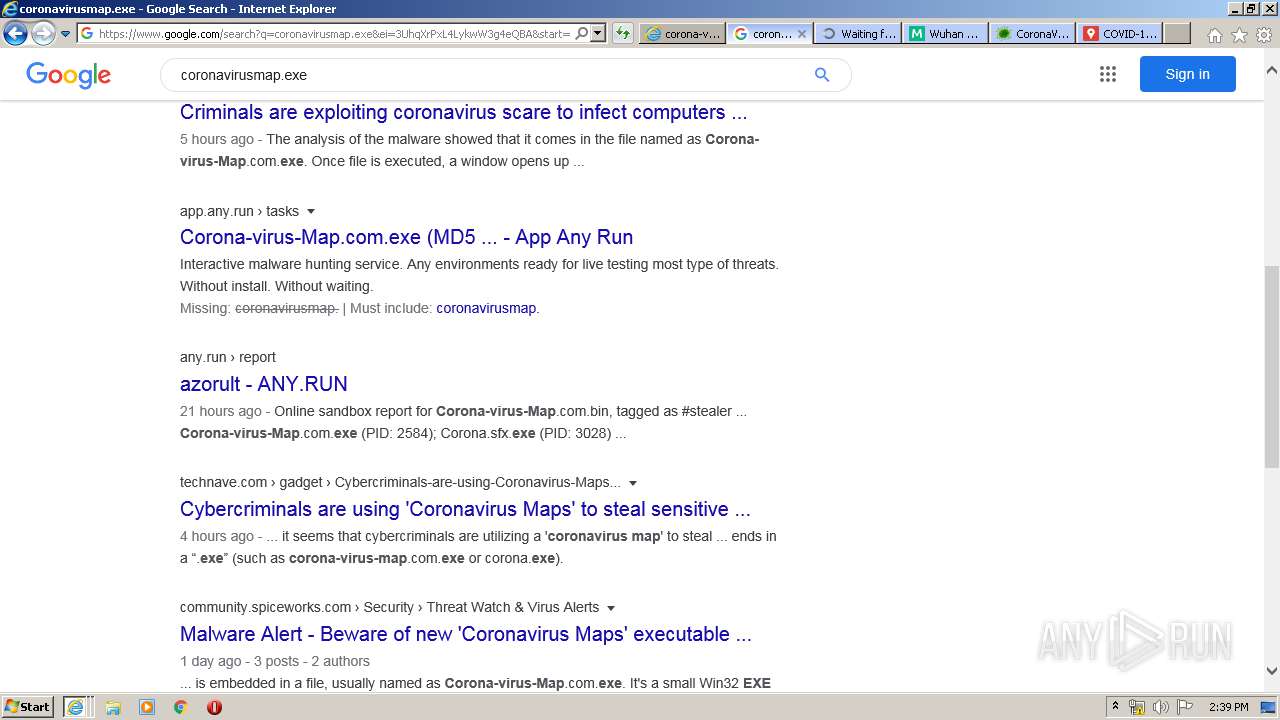
| Verdict: | Malicious activity |
| Analysis date: | March 12, 2020, 14:27:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 65653664F056C7BE7DA9F461B3964D2F |
| SHA1: | 49846B1E93B274659A66DCACA6FEEB0D4B33336E |
| SHA256: | 69ABE529136F8AAF8133651BF8BE53311CBB260E33C3D34B3F5E5423DED475EF |
| SSDEEP: | 3:N1KJS4vXQPrZIn:Cc4vmZIn |
MALICIOUS
No malicious indicators.SUSPICIOUS
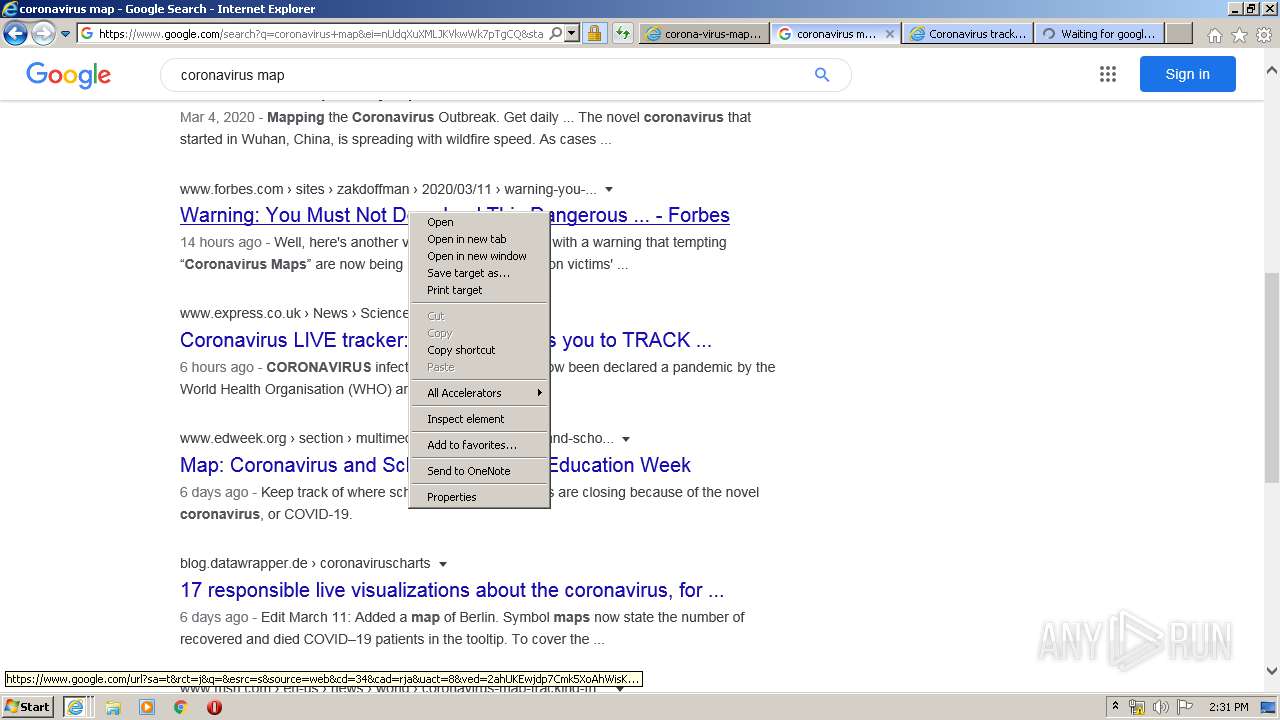
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 5652)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3556)
- iexplore.exe (PID: 2952)
- iexplore.exe (PID: 2412)
- iexplore.exe (PID: 2620)
- iexplore.exe (PID: 3084)
- iexplore.exe (PID: 1392)
- iexplore.exe (PID: 2716)
Changes internet zones settings
- iexplore.exe (PID: 2952)
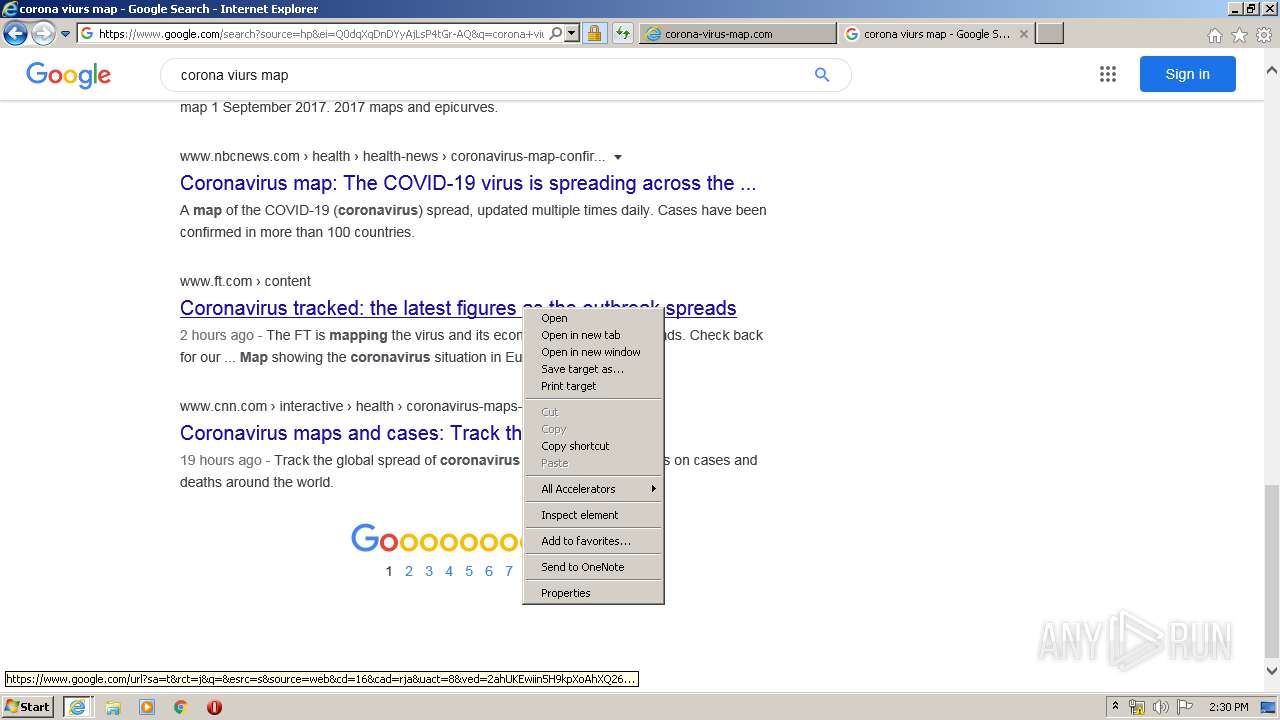
Application launched itself
- iexplore.exe (PID: 2952)
Reads settings of System Certificates
- iexplore.exe (PID: 2412)
- iexplore.exe (PID: 1392)
- iexplore.exe (PID: 3084)
- iexplore.exe (PID: 2620)
- iexplore.exe (PID: 2952)
- iexplore.exe (PID: 2716)
- iexplore.exe (PID: 3556)
Reads internet explorer settings
- iexplore.exe (PID: 3556)
- iexplore.exe (PID: 2620)
- iexplore.exe (PID: 2412)
- iexplore.exe (PID: 3084)
- iexplore.exe (PID: 1392)
- iexplore.exe (PID: 2716)
Creates files in the user directory
- iexplore.exe (PID: 2620)
- iexplore.exe (PID: 2952)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 5652)
- iexplore.exe (PID: 1392)
- iexplore.exe (PID: 2716)
- iexplore.exe (PID: 3556)
- iexplore.exe (PID: 2412)
Changes settings of System certificates
- iexplore.exe (PID: 2952)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
8
Malicious processes
0
Suspicious processes
0
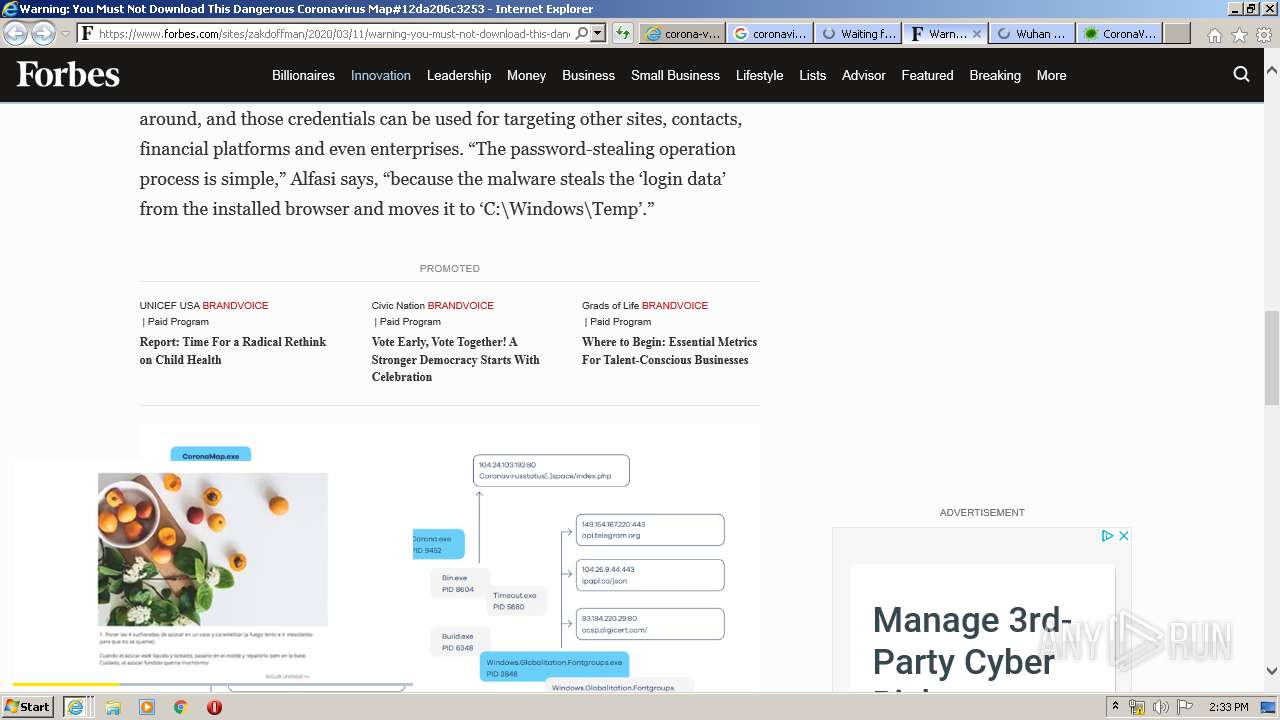
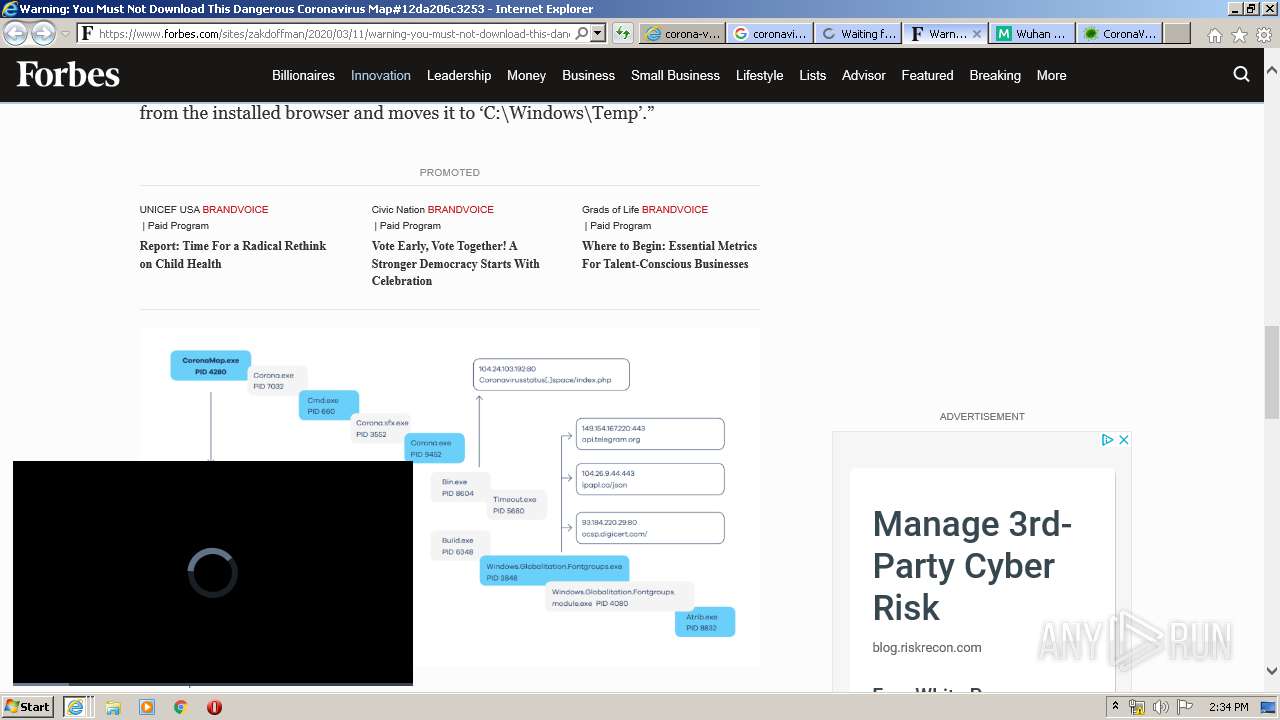
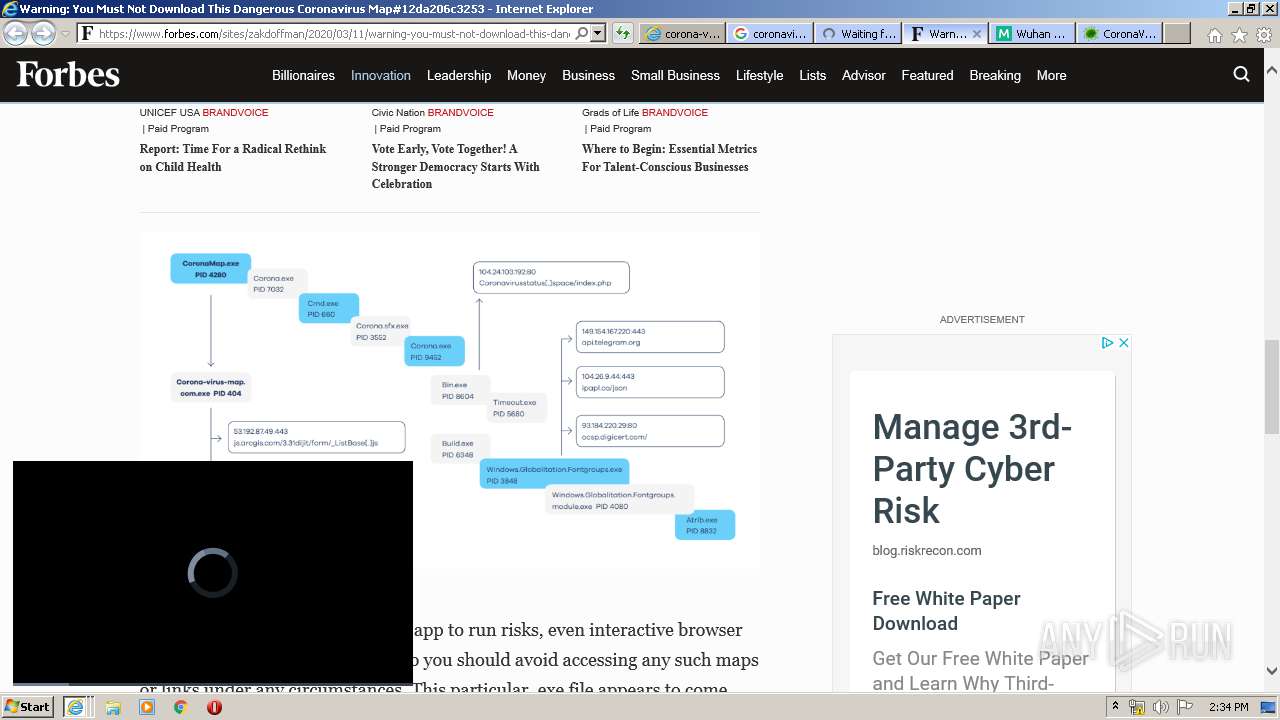
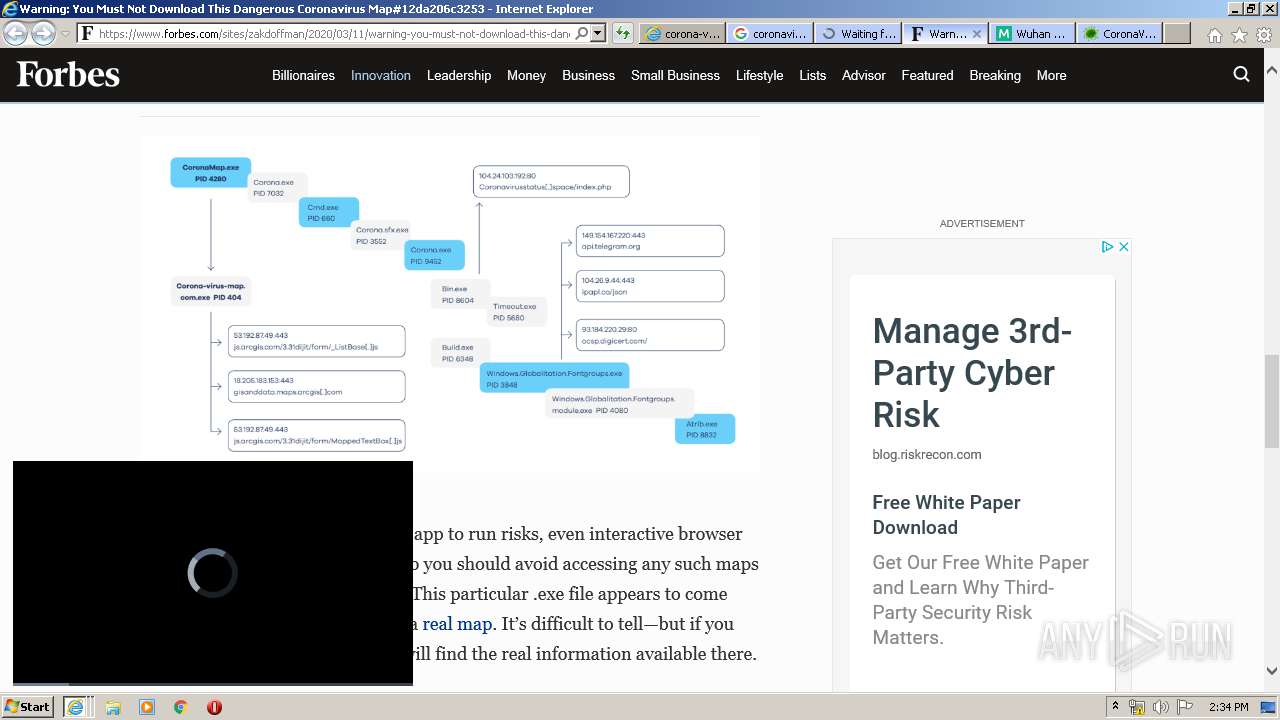
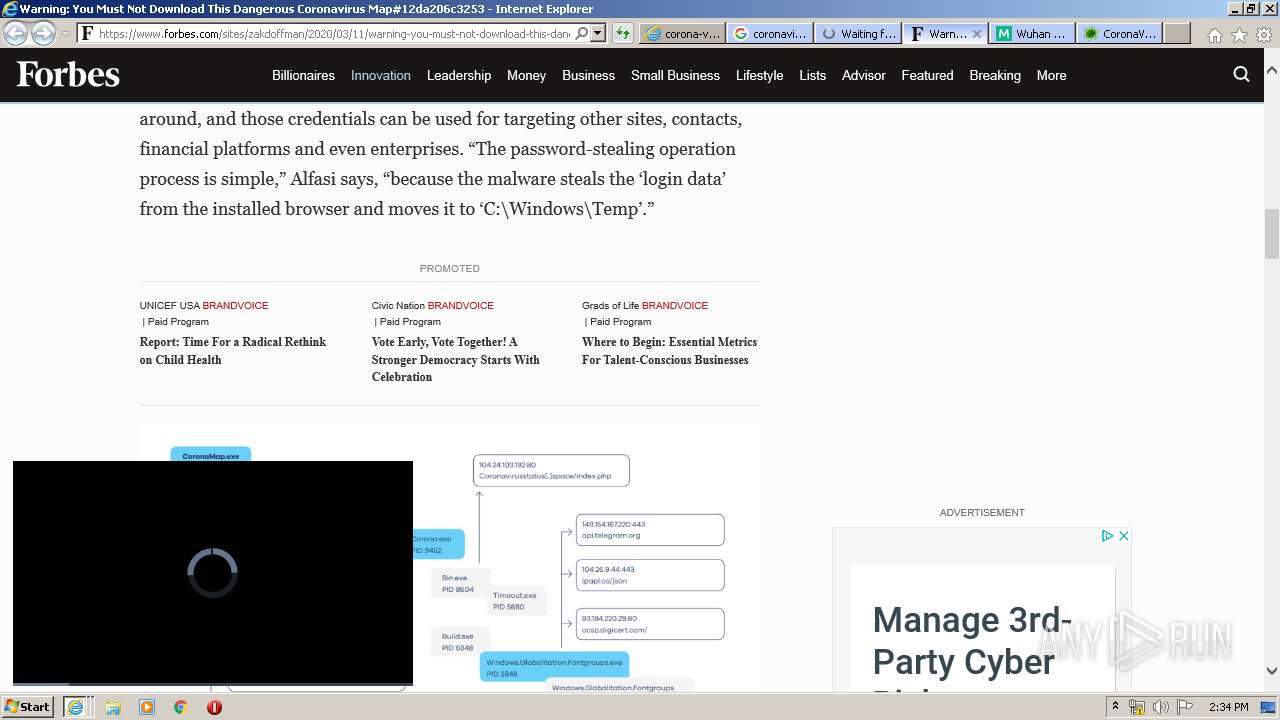
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1392 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2952 CREDAT:2889015 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2412 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2952 CREDAT:2037025 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2952 CREDAT:1578259 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2716 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2952 CREDAT:3609994 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
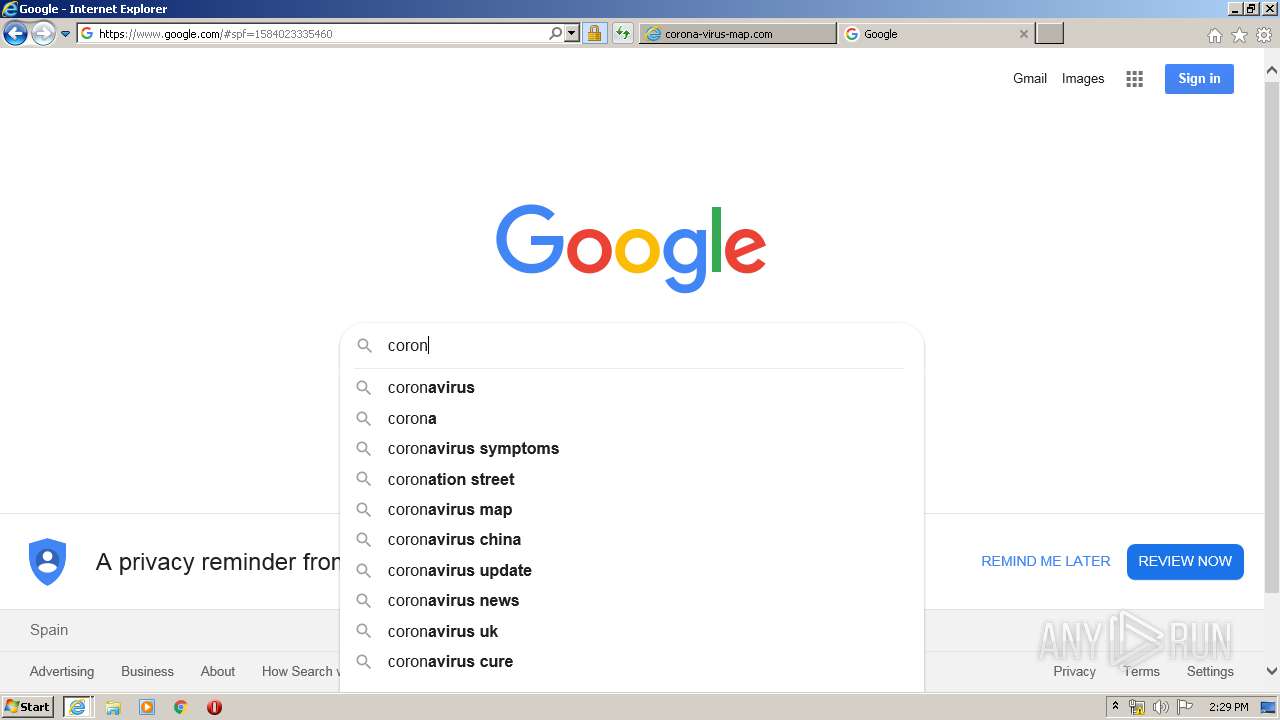
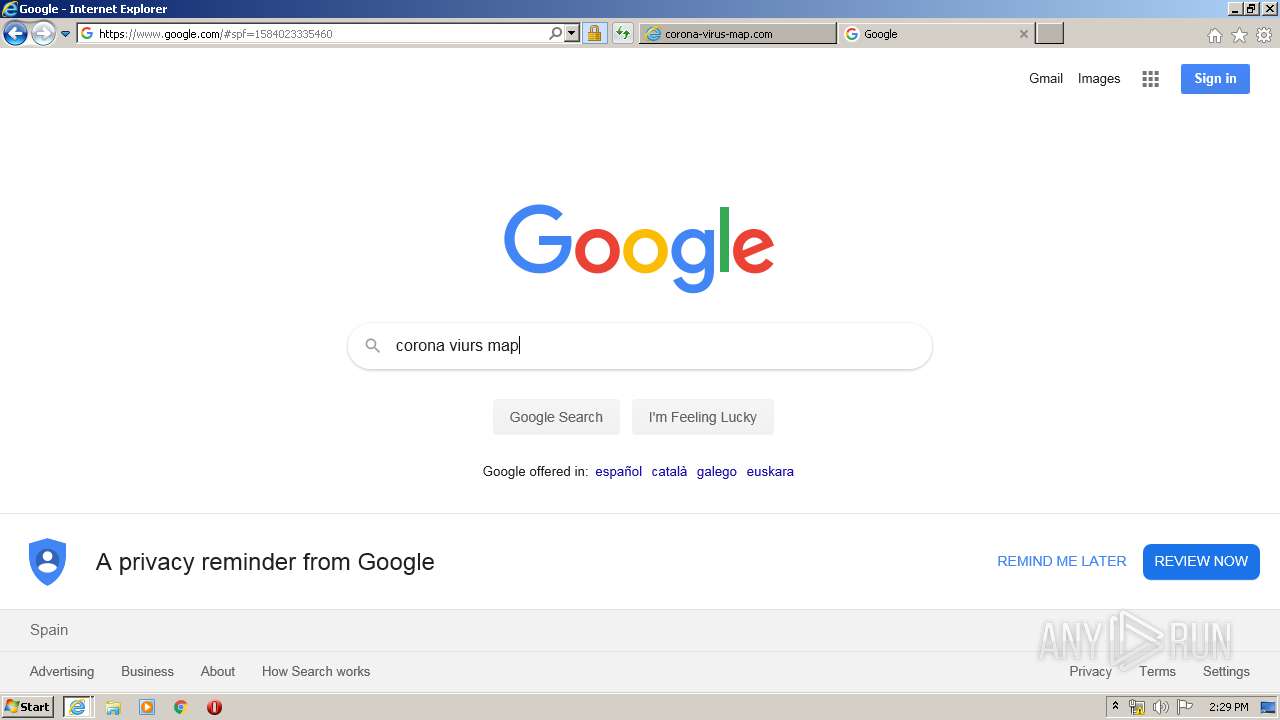
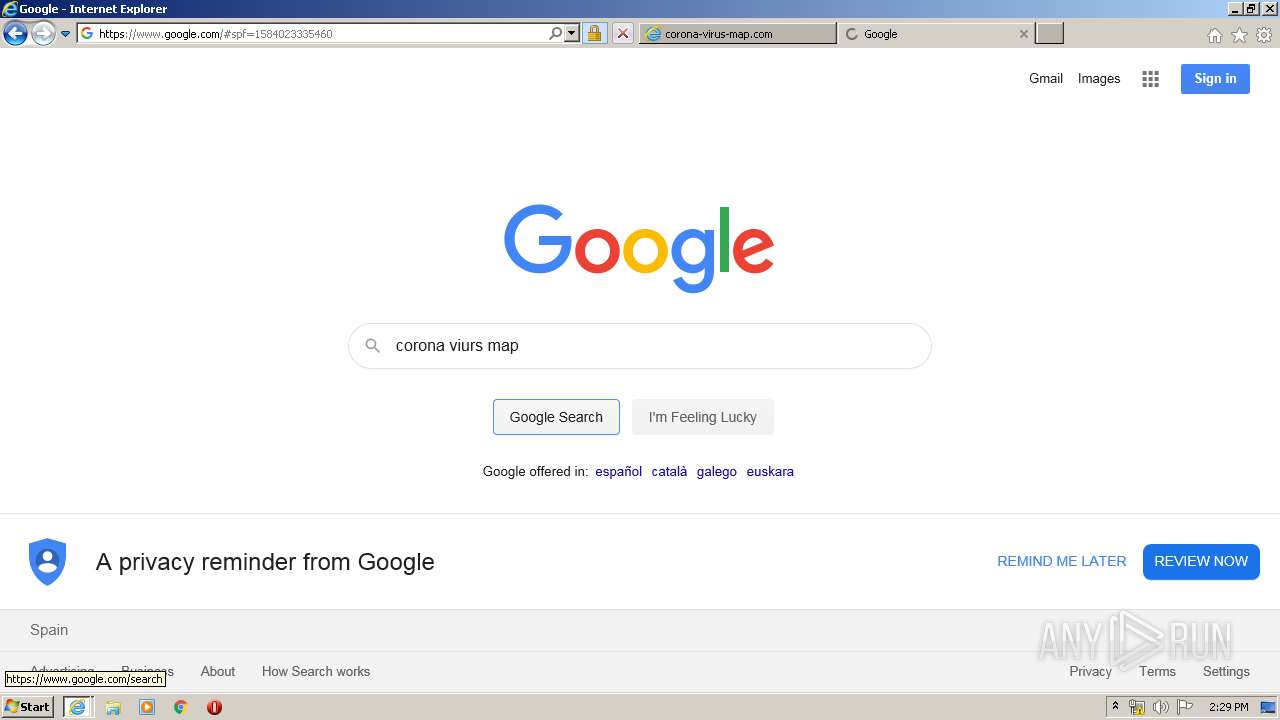
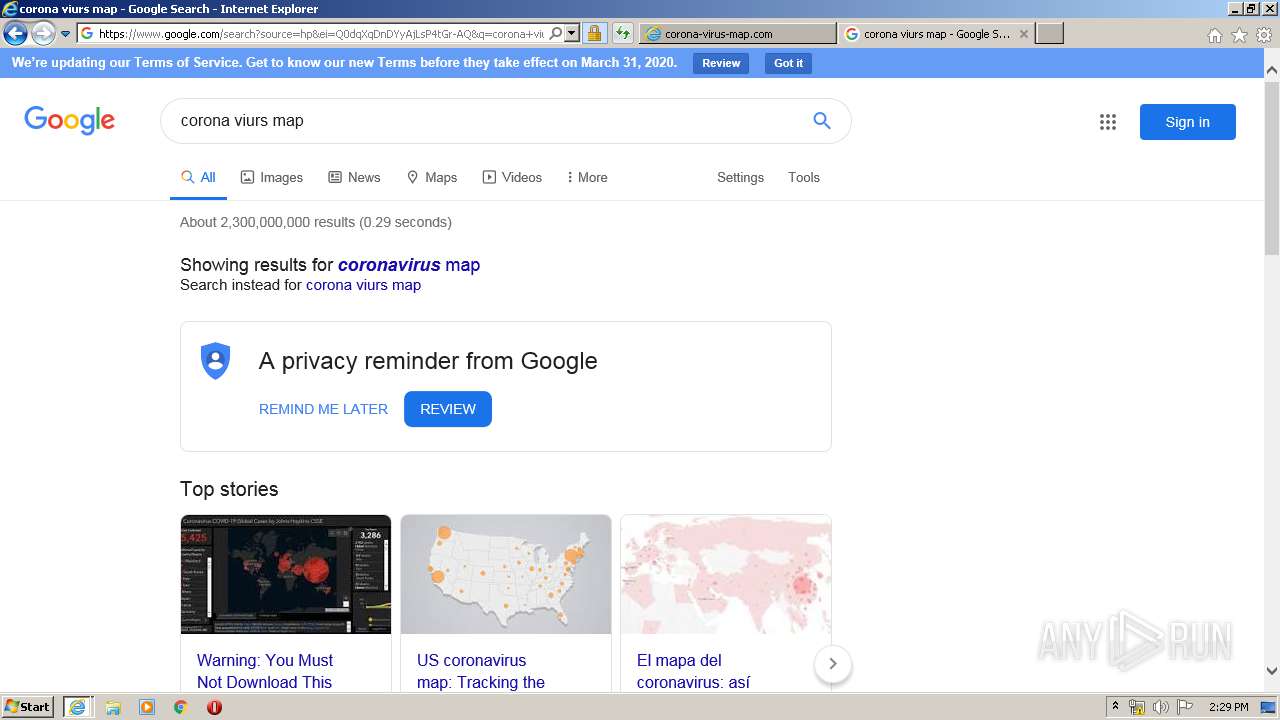
| 2952 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://www.Corona-Virus-Map.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3084 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2952 CREDAT:3740957 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3556 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2952 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 5652 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
Total events
13 550
Read events
3 555
Write events
7 752
Delete events
2 243
Modification events
| (PID) Process: | (3556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1811270026 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30799994 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
0
Suspicious files
38
Text files
1 177
Unknown types
81
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2952 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3556 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabE269.tmp | — | |
MD5:— | SHA256:— | |||
| 3556 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabE26A.tmp | — | |
MD5:— | SHA256:— | |||
| 3556 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarE27B.tmp | — | |
MD5:— | SHA256:— | |||
| 3556 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarE27C.tmp | — | |
MD5:— | SHA256:— | |||
| 3556 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\3Z6FHGM4.txt | — | |
MD5:— | SHA256:— | |||
| 3556 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\J7OWZ9AF.txt | — | |
MD5:— | SHA256:— | |||
| 3556 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\new_logo_GDTrans[1].png | image | |
MD5:— | SHA256:— | |||
| 2952 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab30B9.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab30B8.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1 499
TCP/UDP connections
702
DNS requests
191
Threats
1
HTTP requests
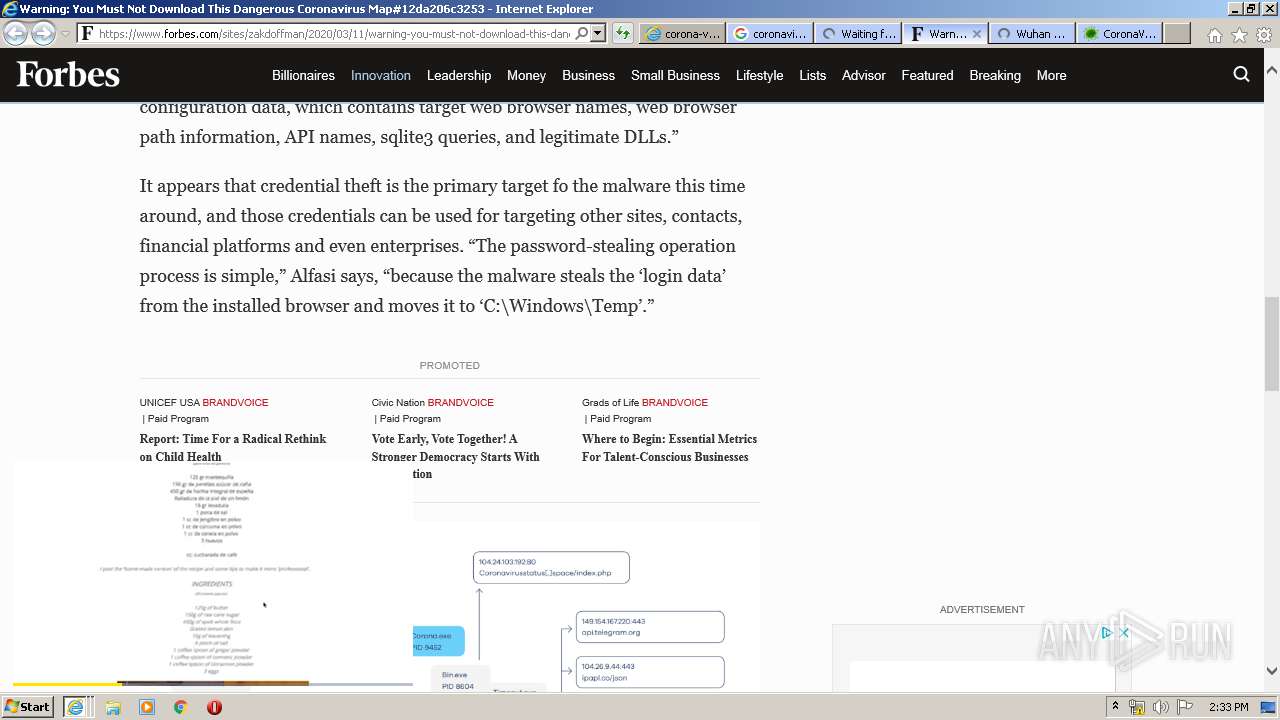
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3556 | iexplore.exe | GET | 200 | 152.199.19.161:443 | https://r20swj13mr.microsoft.com/ieblocklist/v1/urlblocklist.bin | US | — | — | whitelisted |
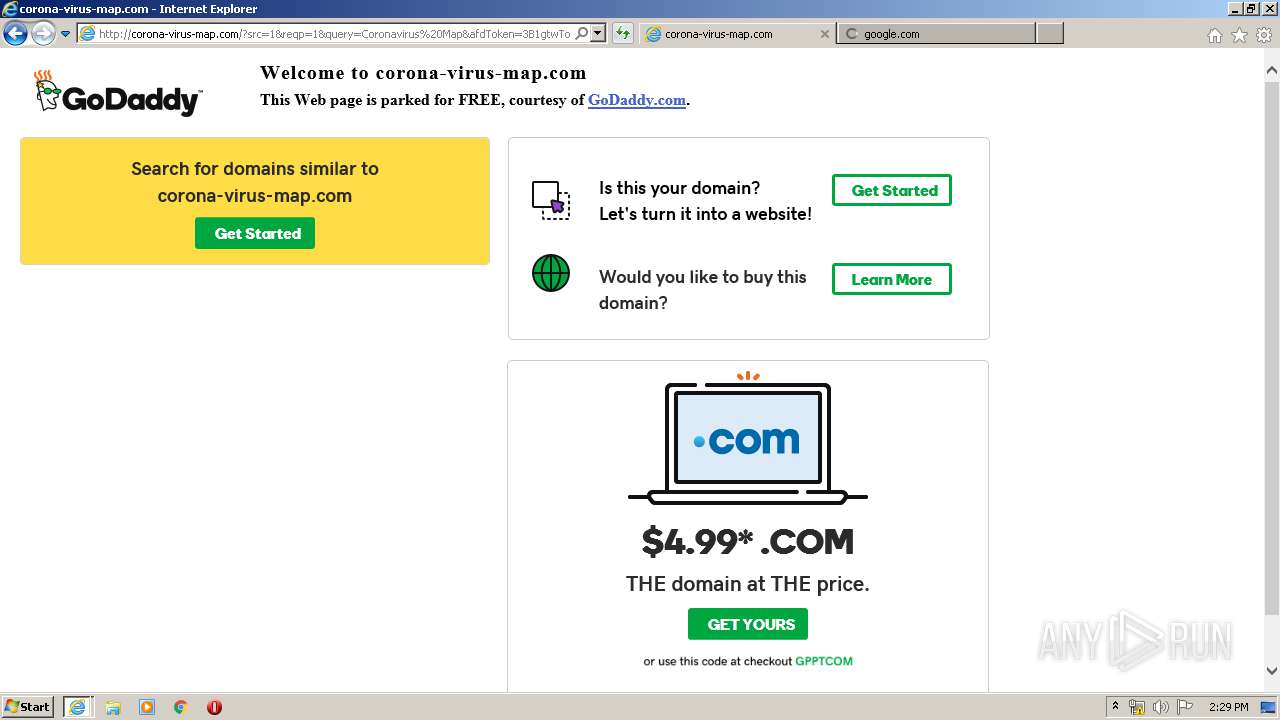
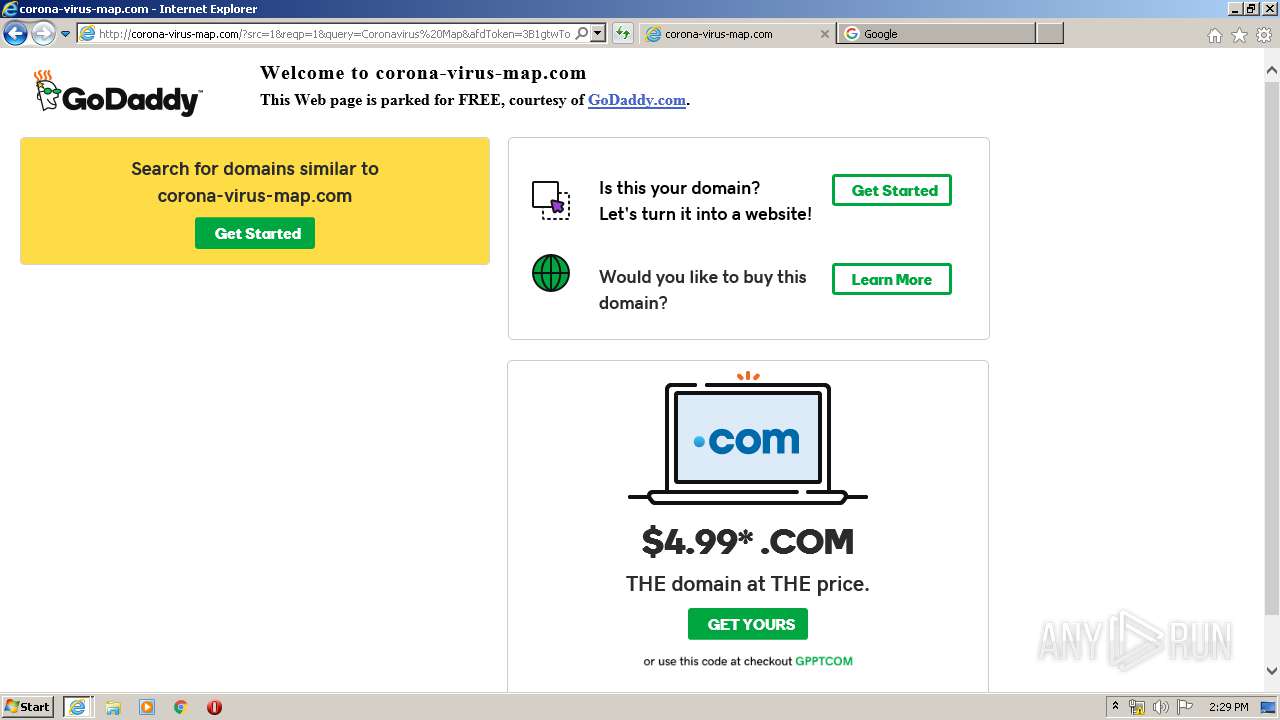
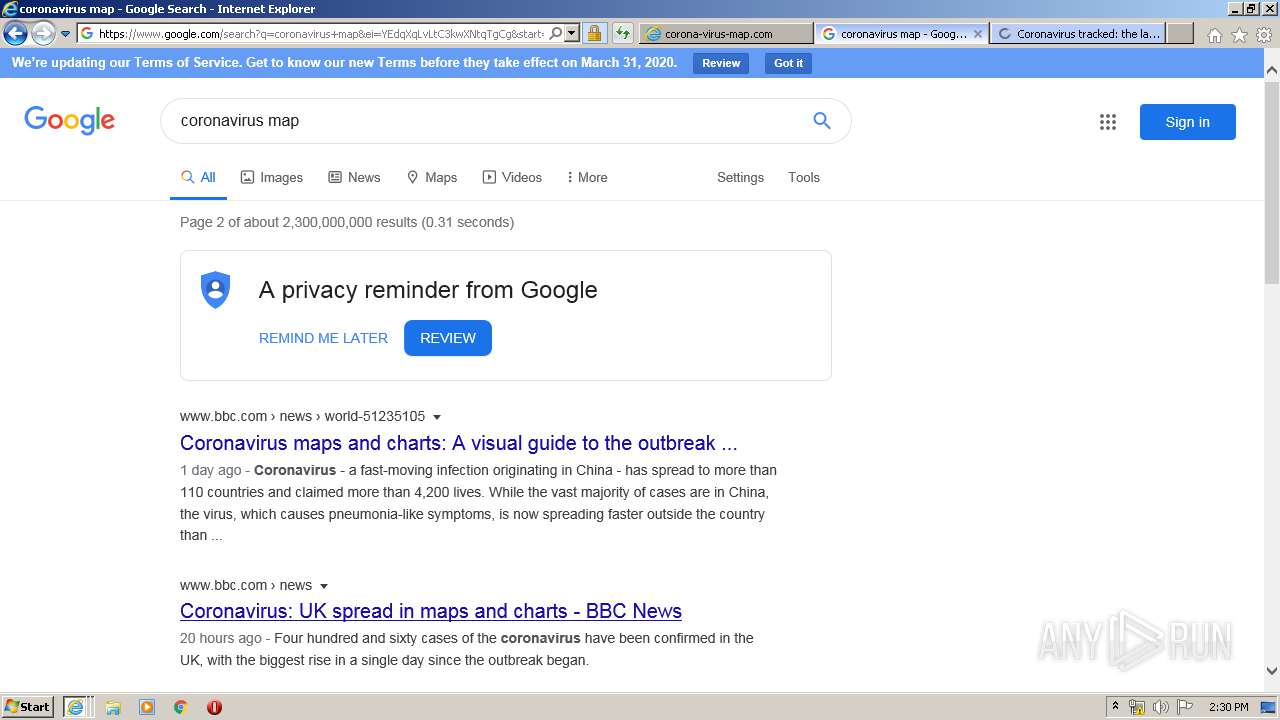
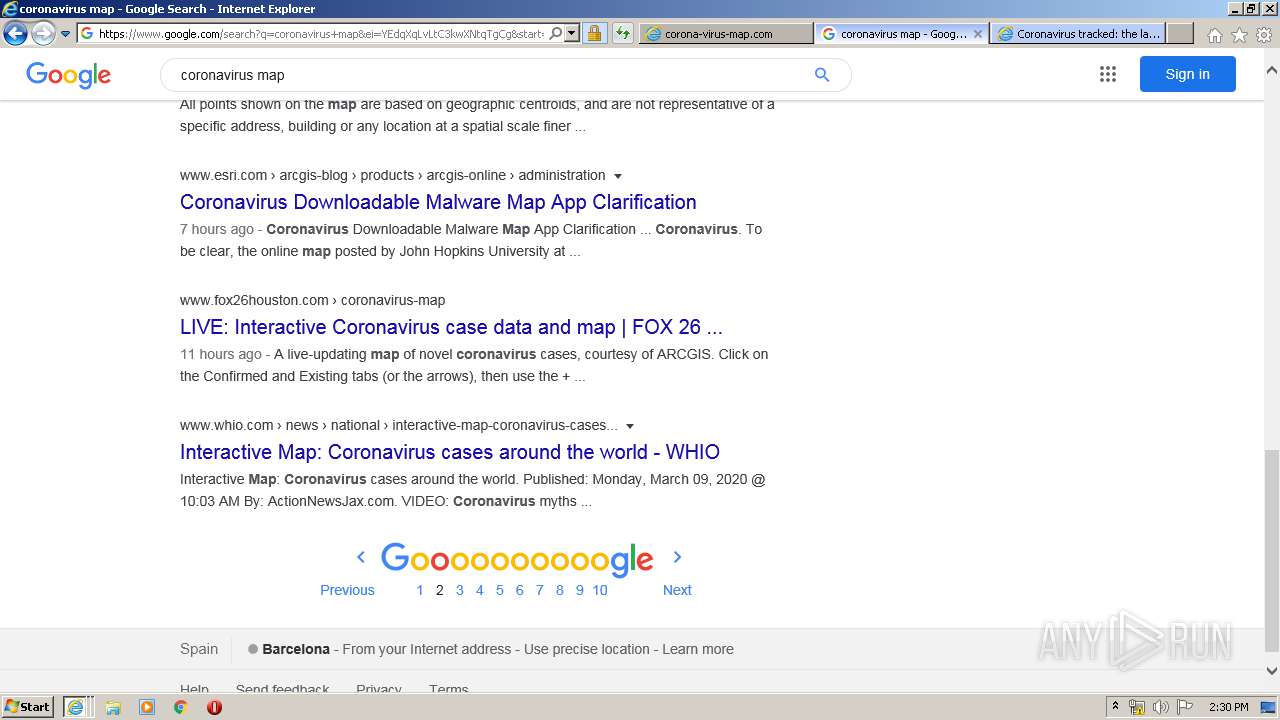
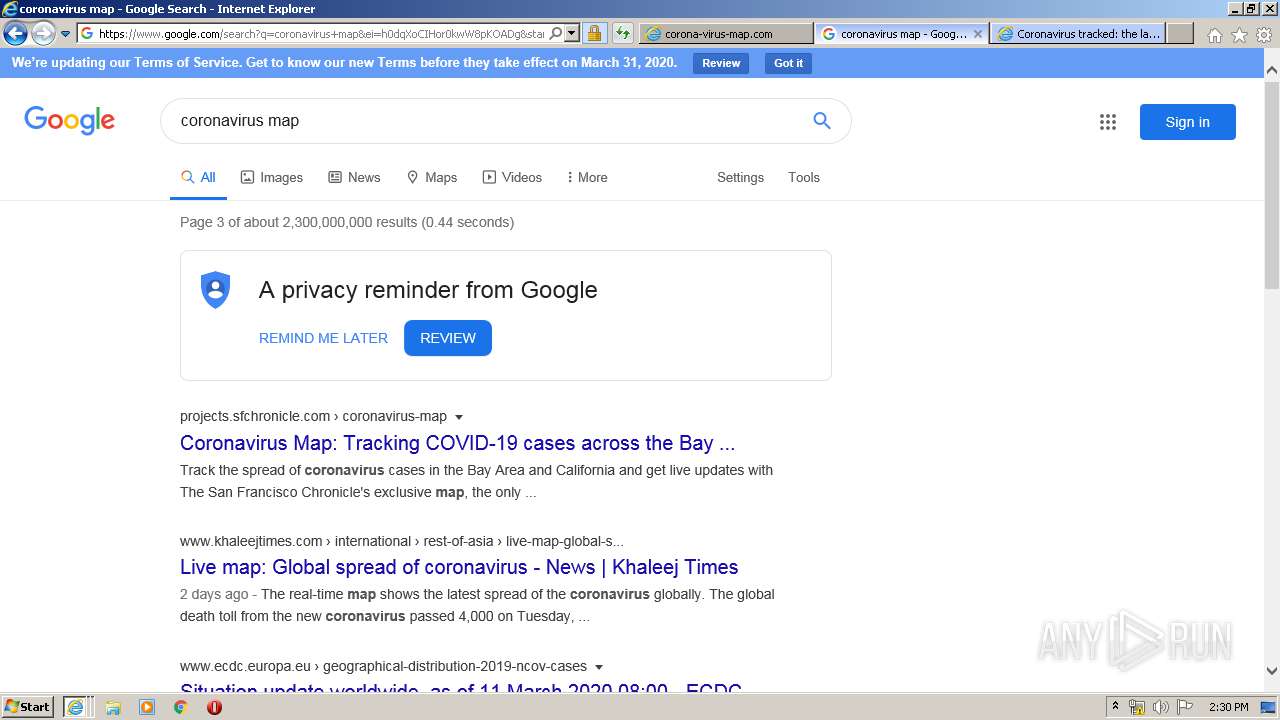
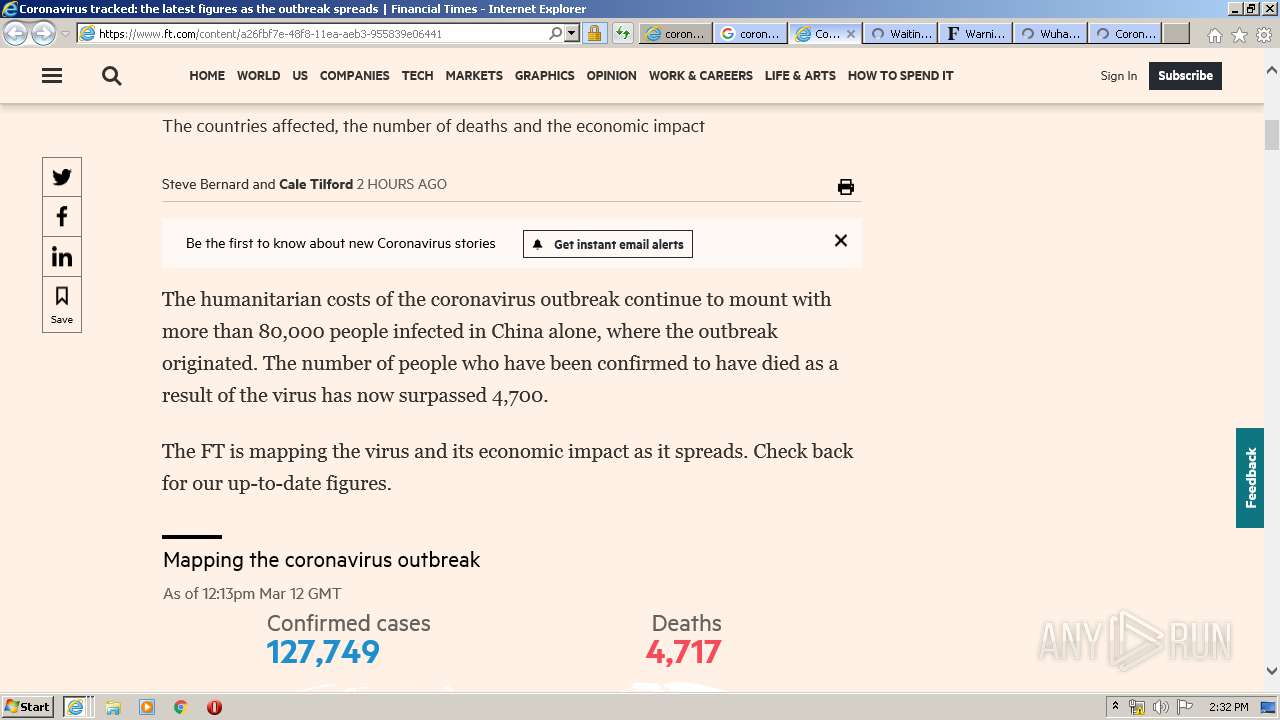
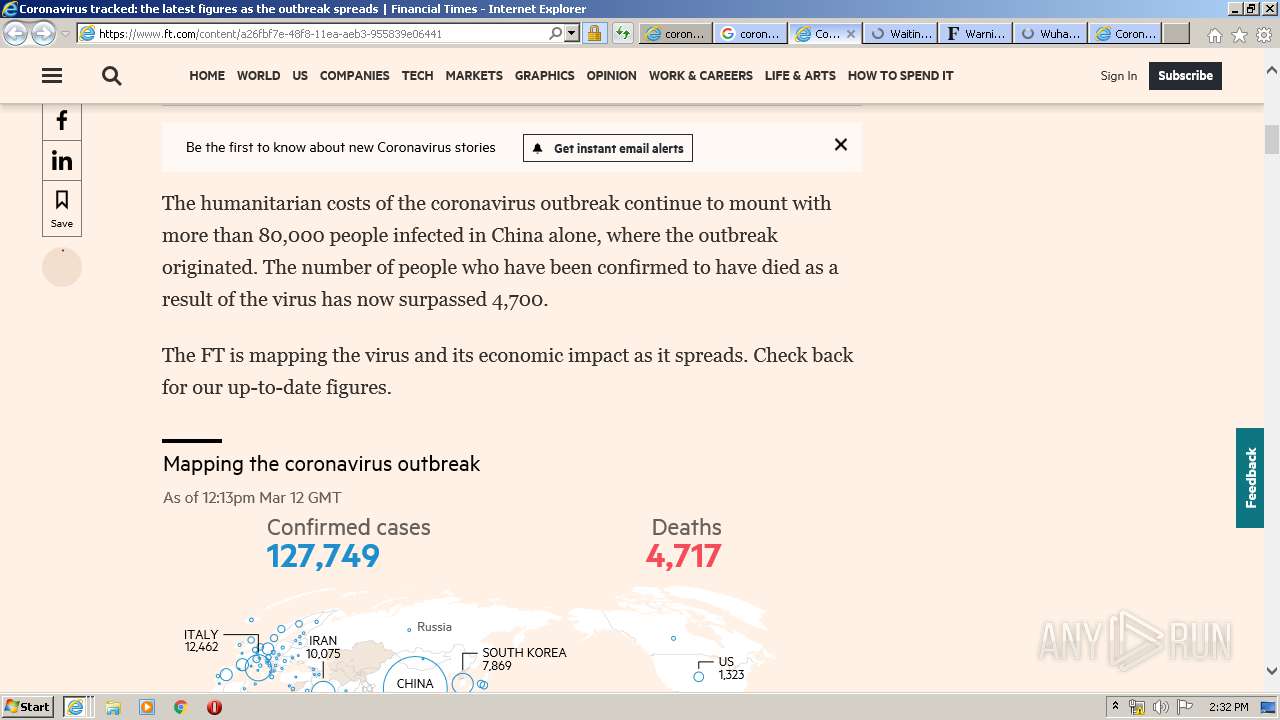
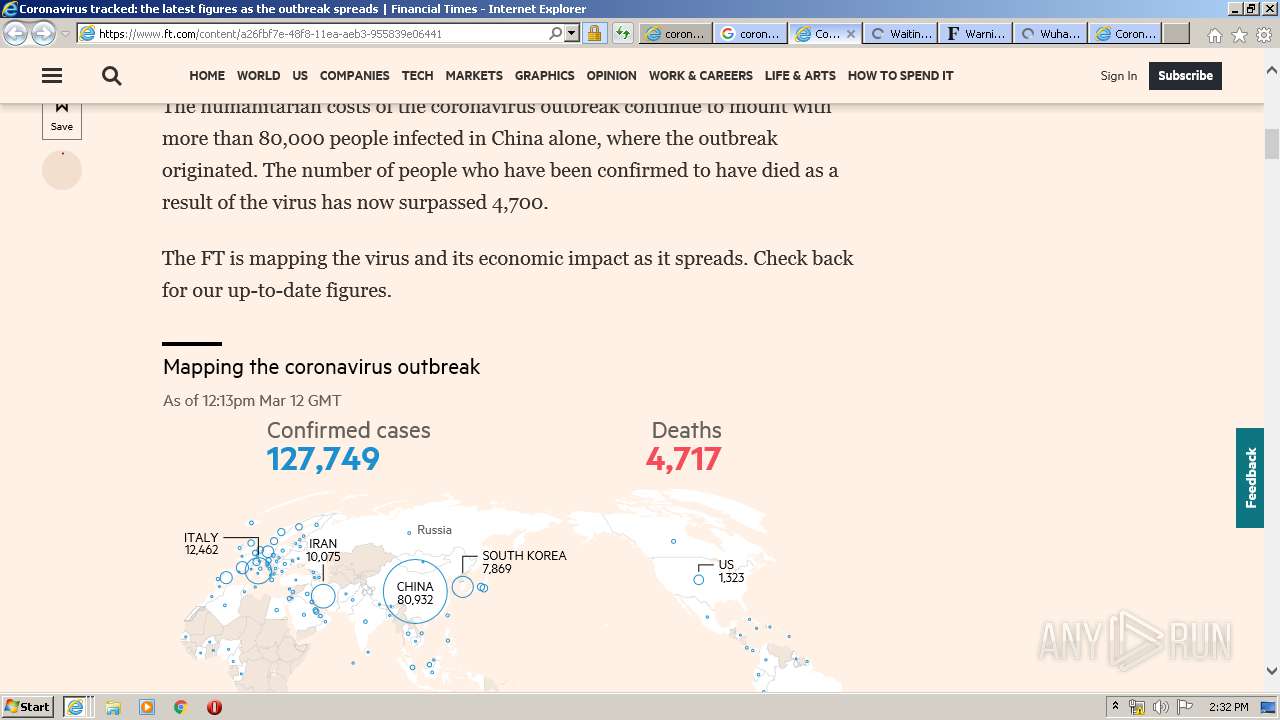
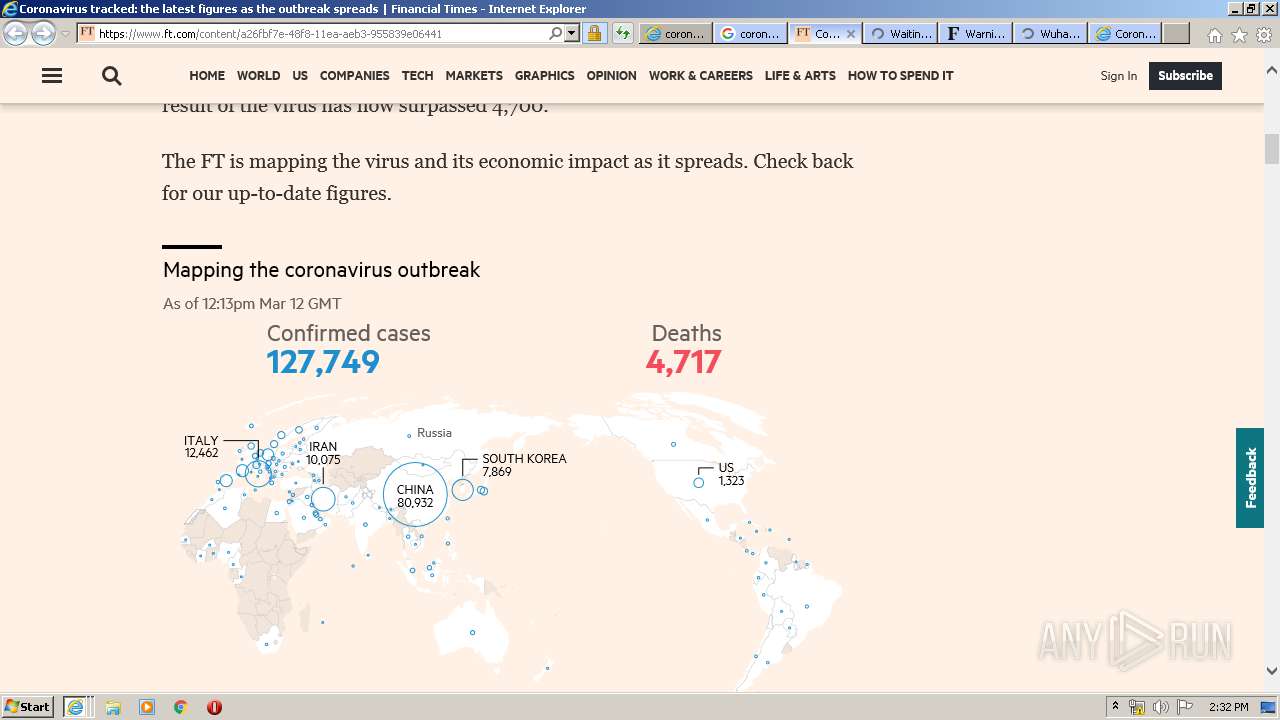
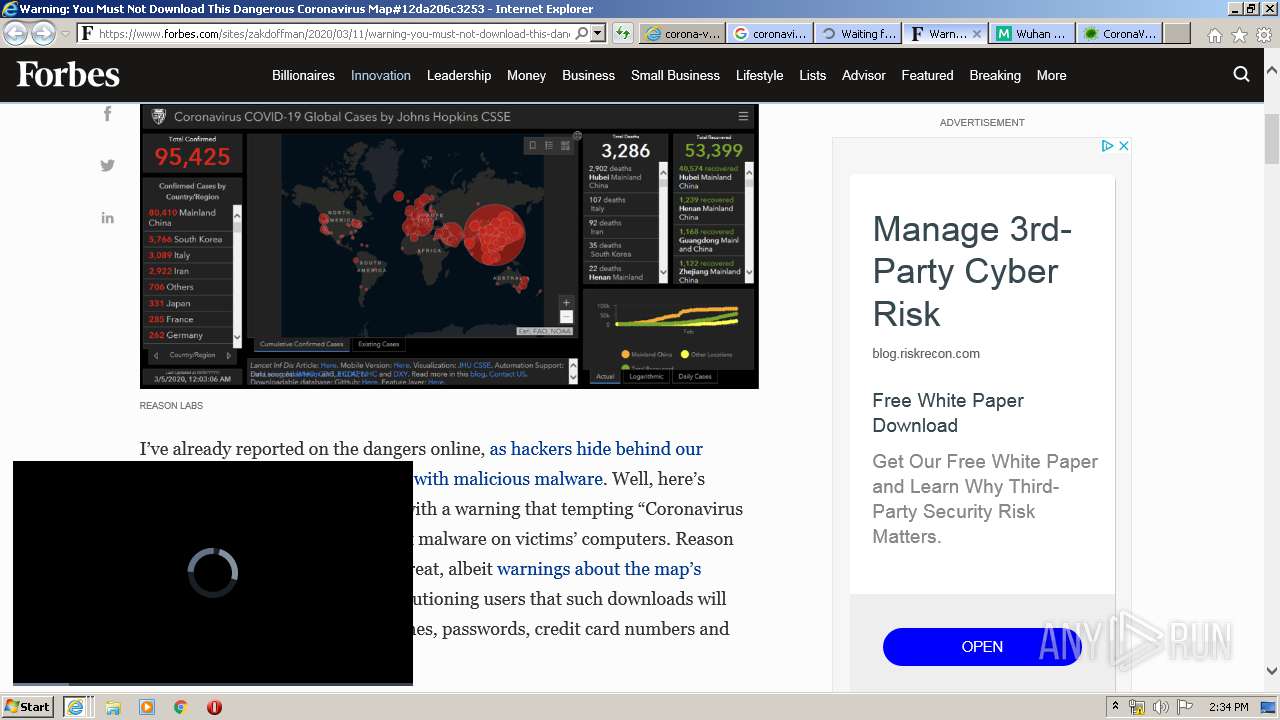
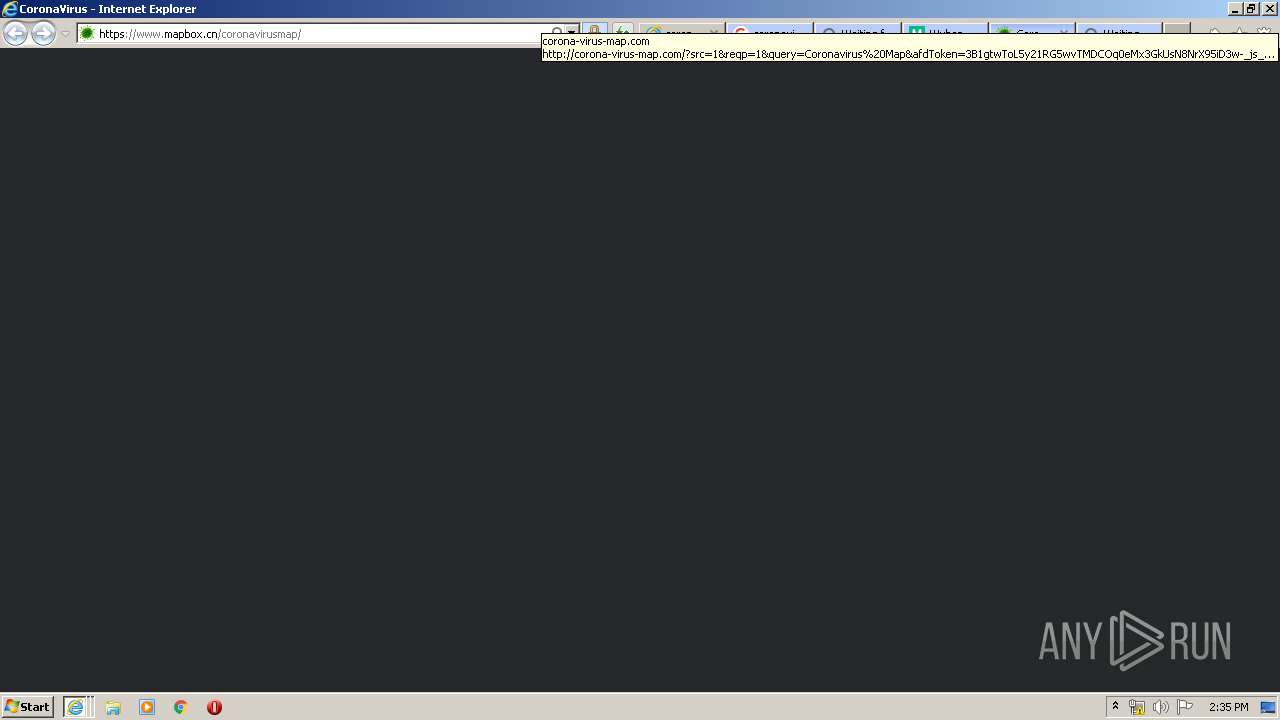
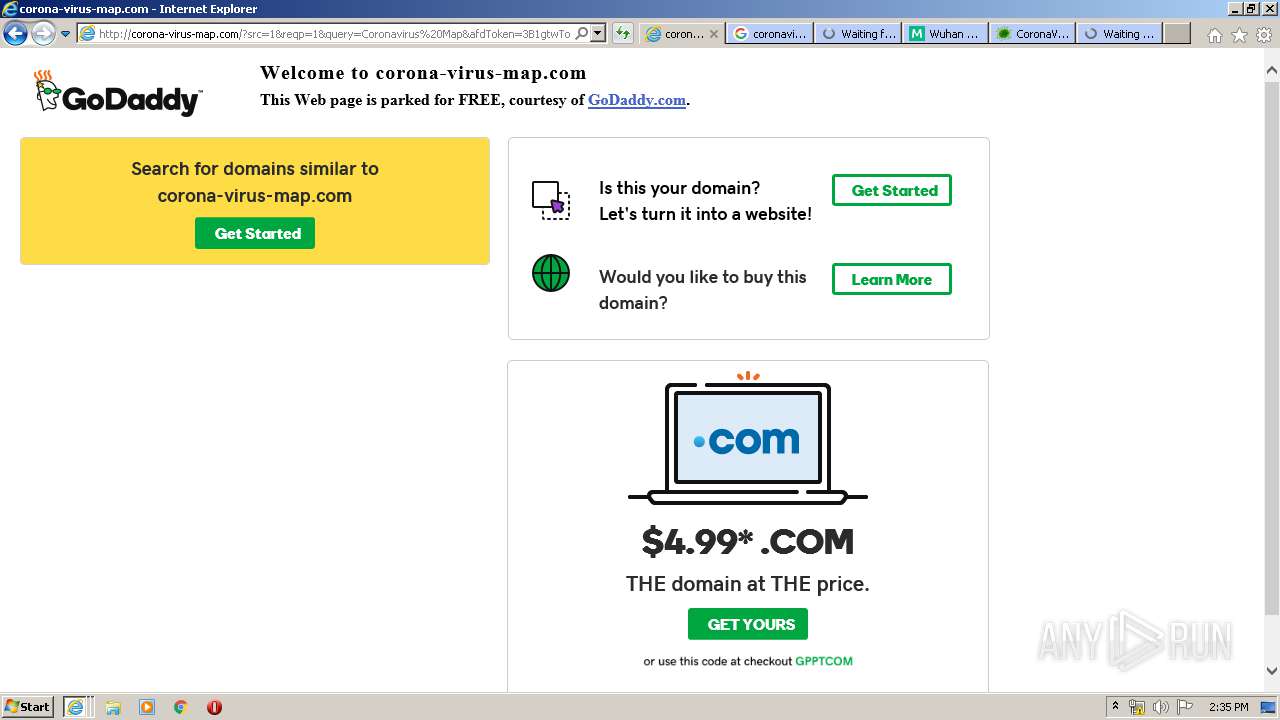
3556 | iexplore.exe | GET | 200 | 184.168.221.46:80 | http://www.corona-virus-map.com/ | US | html | 451 b | whitelisted |
3556 | iexplore.exe | GET | 200 | 92.123.28.58:443 | https://img1.wsimg.com/ux/fonts/sherpa/1.0/gdsherpa-bold.woff | FR | woff | 31.9 Kb | whitelisted |
3556 | iexplore.exe | GET | 200 | 184.168.221.46:80 | http://corona-virus-map.com/?reqp=1&reqr= | US | html | 6.29 Kb | whitelisted |
3556 | iexplore.exe | GET | 200 | 104.109.73.120:80 | http://parked-content.godaddy.com/images/99C_code.png | NL | image | 7.42 Kb | whitelisted |
3556 | iexplore.exe | GET | 200 | 104.109.73.120:80 | http://parked-content.godaddy.com/park/pTWyLzShYJy2MJuzYKchLl5jLab= | NL | html | 262 b | whitelisted |
3556 | iexplore.exe | GET | 200 | 2.16.186.96:80 | http://ak2.imgaft.com/images/new_logo_GDTrans.png | unknown | image | 3.72 Kb | shared |
3556 | iexplore.exe | GET | 200 | 172.217.18.164:80 | http://www.google.com/adsense/domains/caf.js | US | text | 55.6 Kb | malicious |
3556 | iexplore.exe | GET | 200 | 2.16.186.96:80 | http://ak2.imgaft.com/script/jquery-1.3.1.min.js | unknown | text | 23.7 Kb | shared |
3556 | iexplore.exe | GET | 200 | 2.16.186.96:80 | http://ak2.imgaft.com/images/feature-illu-dot-com-domain.png | unknown | image | 1.42 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
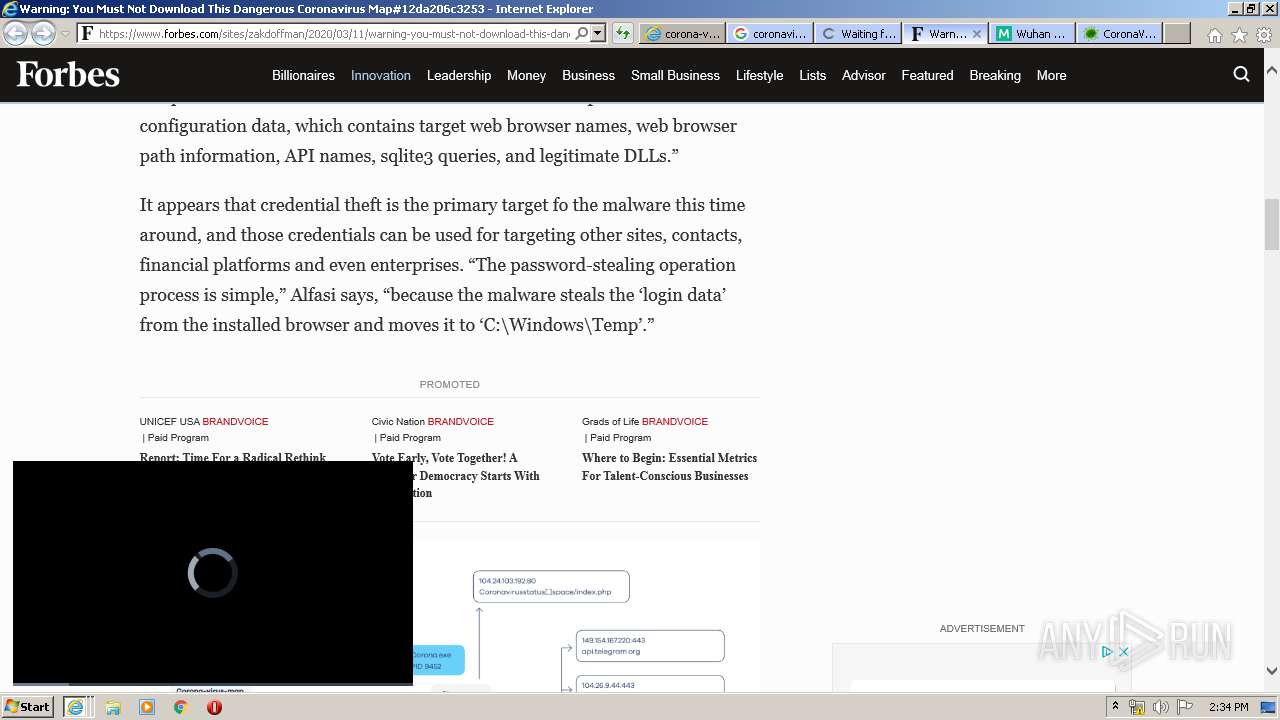
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3556 | iexplore.exe | 184.168.221.46:80 | corona-virus-map.com | GoDaddy.com, LLC | US | malicious |
2952 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3556 | iexplore.exe | 104.109.73.120:80 | parked-content.godaddy.com | Akamai International B.V. | NL | whitelisted |
3556 | iexplore.exe | 172.217.18.164:80 | www.corona-virus-map.com | Google Inc. | US | whitelisted |
3556 | iexplore.exe | 23.45.106.78:443 | www.godaddy.com | Akamai International B.V. | NL | unknown |
3556 | iexplore.exe | 2.16.186.96:80 | ak2.imgaft.com | Akamai International B.V. | — | whitelisted |
2952 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3556 | iexplore.exe | 172.217.18.164:443 | www.corona-virus-map.com | Google Inc. | US | whitelisted |
3556 | iexplore.exe | 92.123.28.58:443 | img1.wsimg.com | Telia Company AB | FR | unknown |
2412 | iexplore.exe | 172.217.18.164:80 | www.corona-virus-map.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.corona-virus-map.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
parked-content.godaddy.com |
| whitelisted |
corona-virus-map.com |
| whitelisted |
www.google.com |
| malicious |
www.godaddy.com |
| whitelisted |
ak2.imgaft.com |
| shared |
img1.wsimg.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3556 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |