| File name: | KMSAuto Net.exe |
| Full analysis: | https://app.any.run/tasks/cc657f14-5624-400f-9378-a52c63c01da4 |
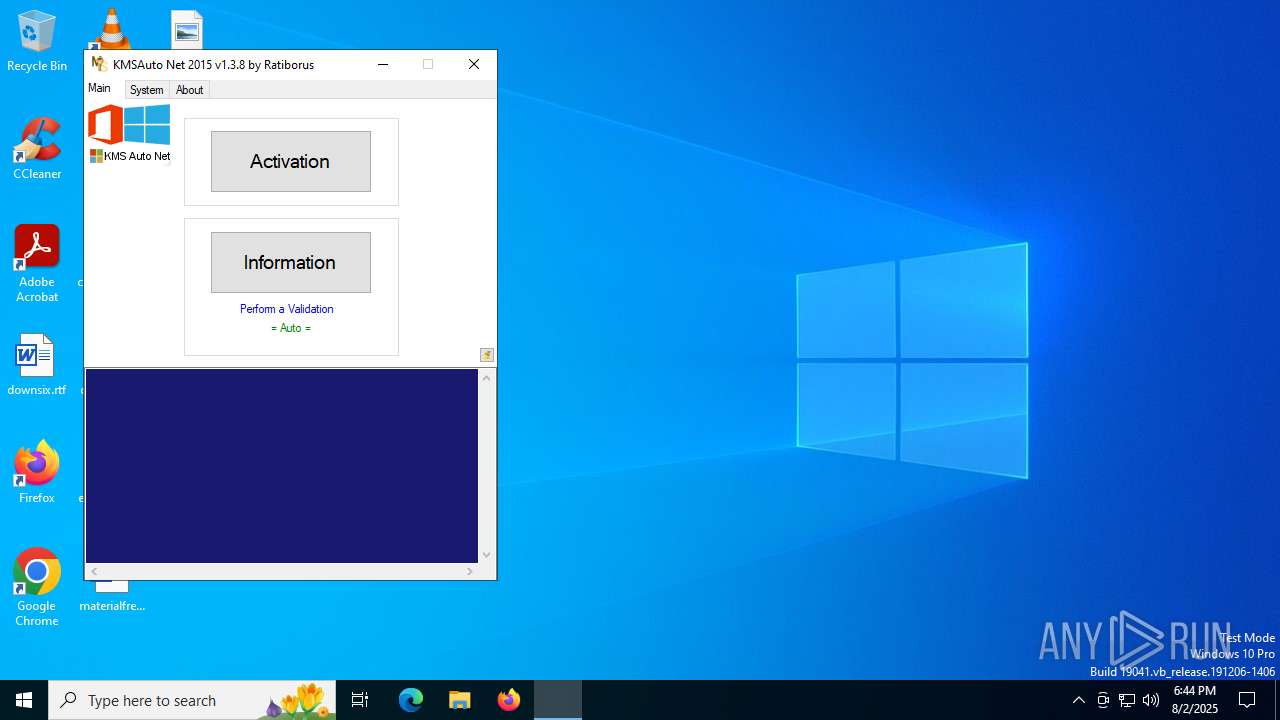
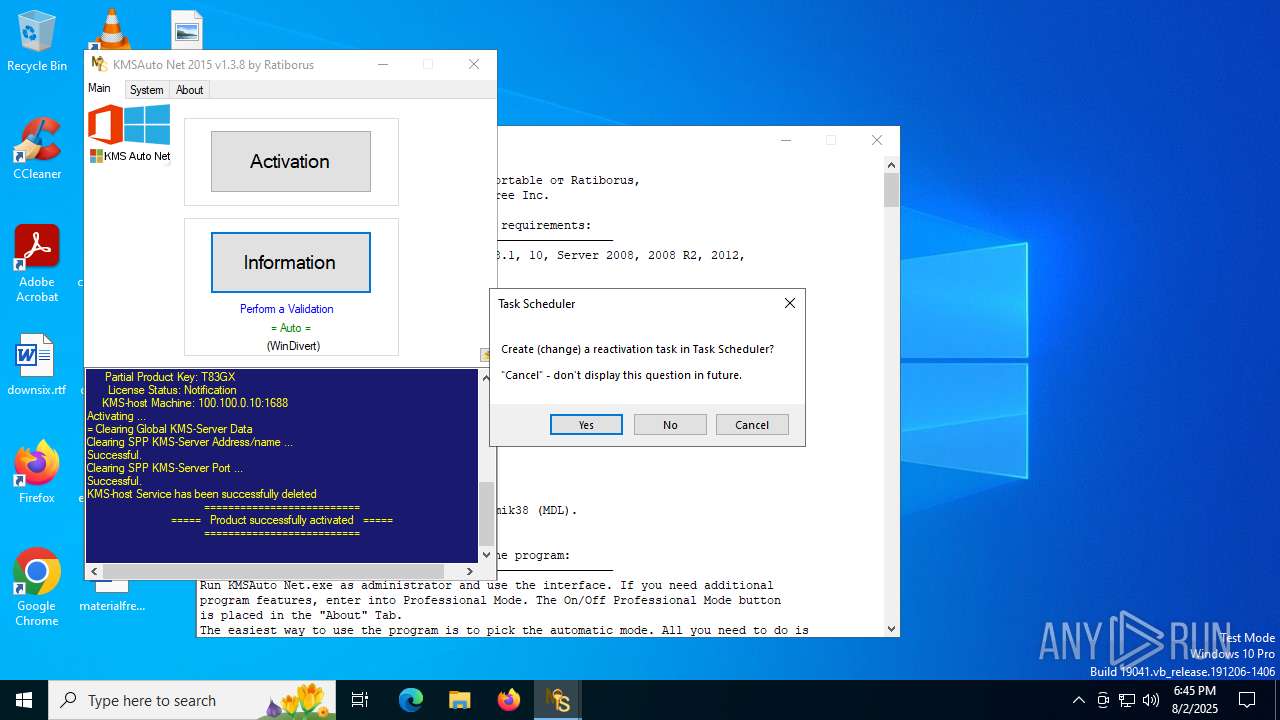
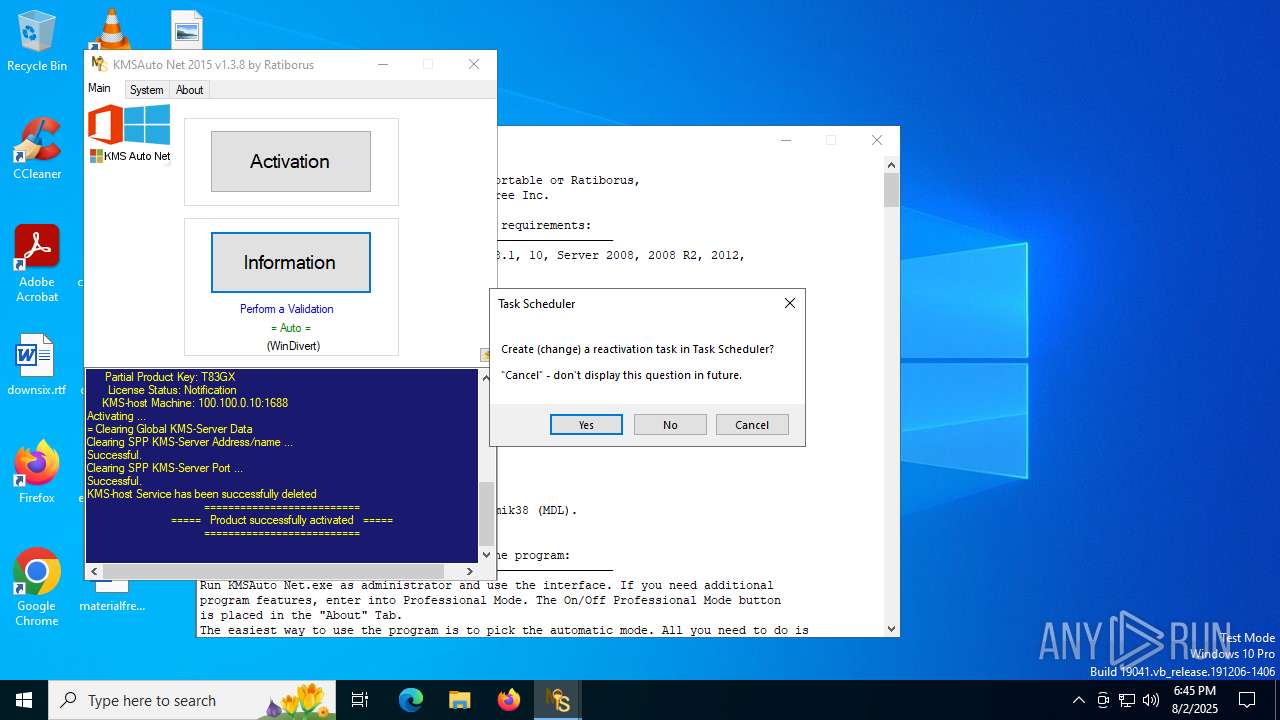
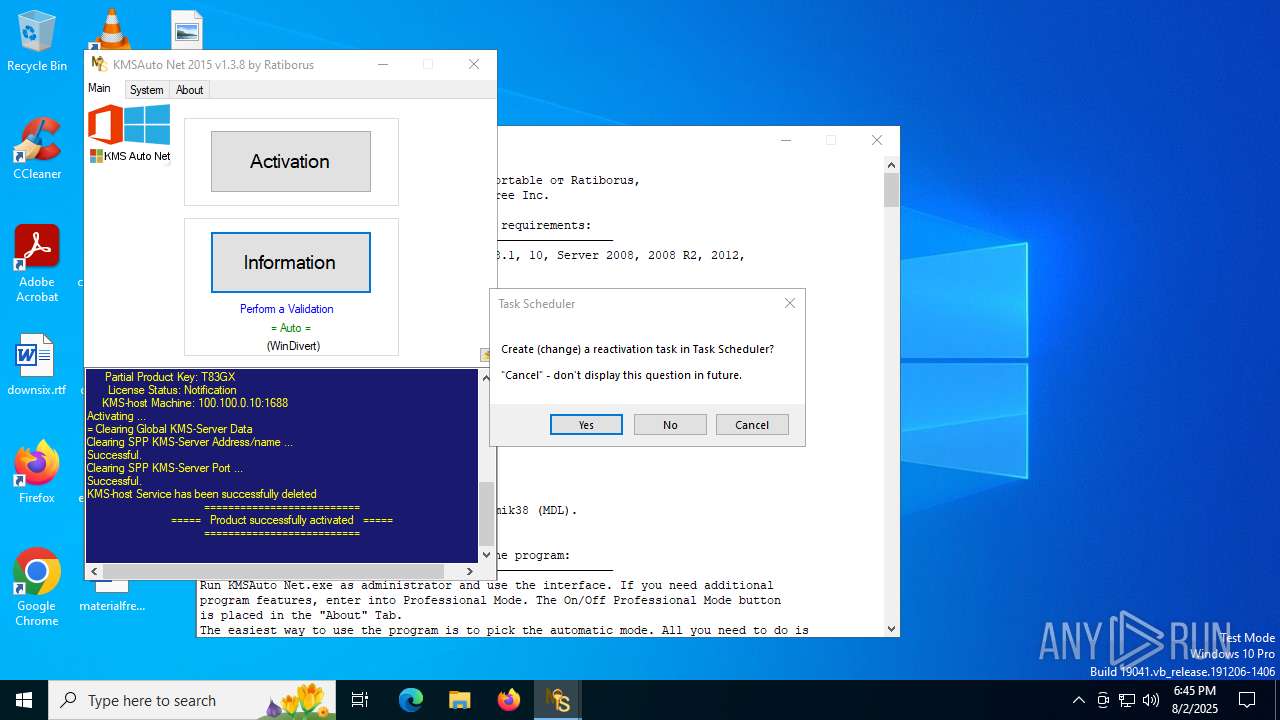
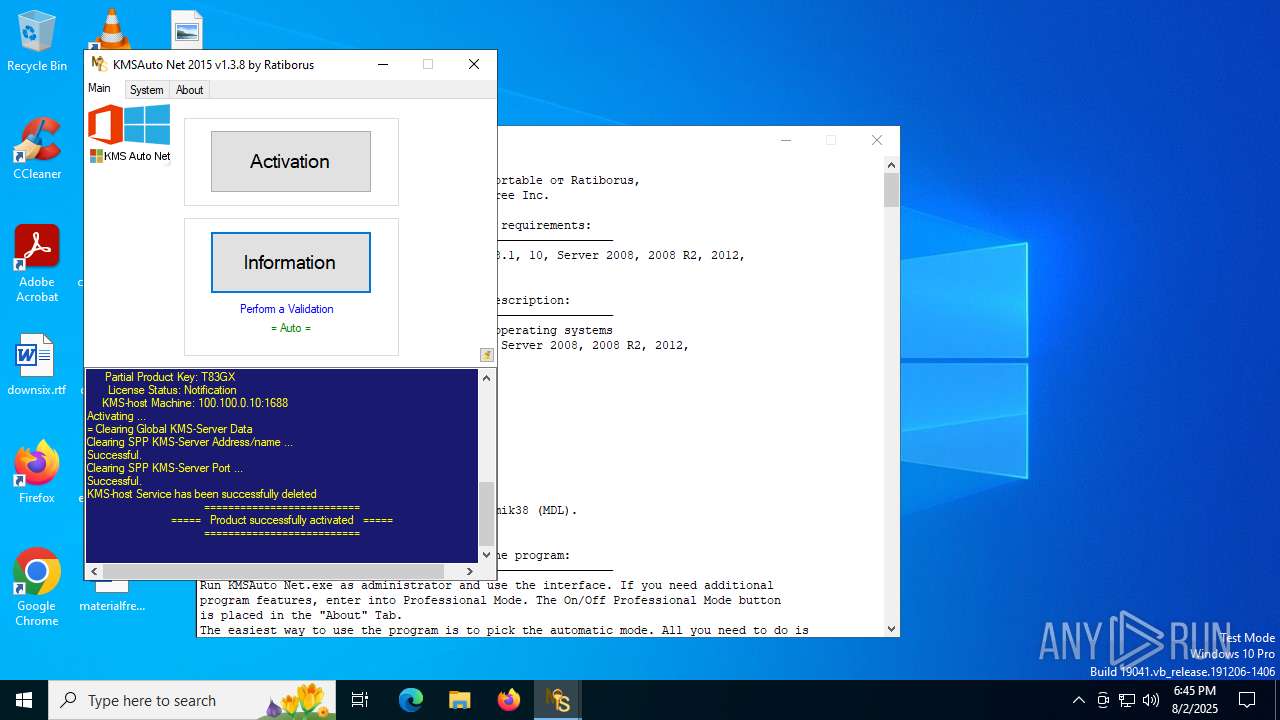
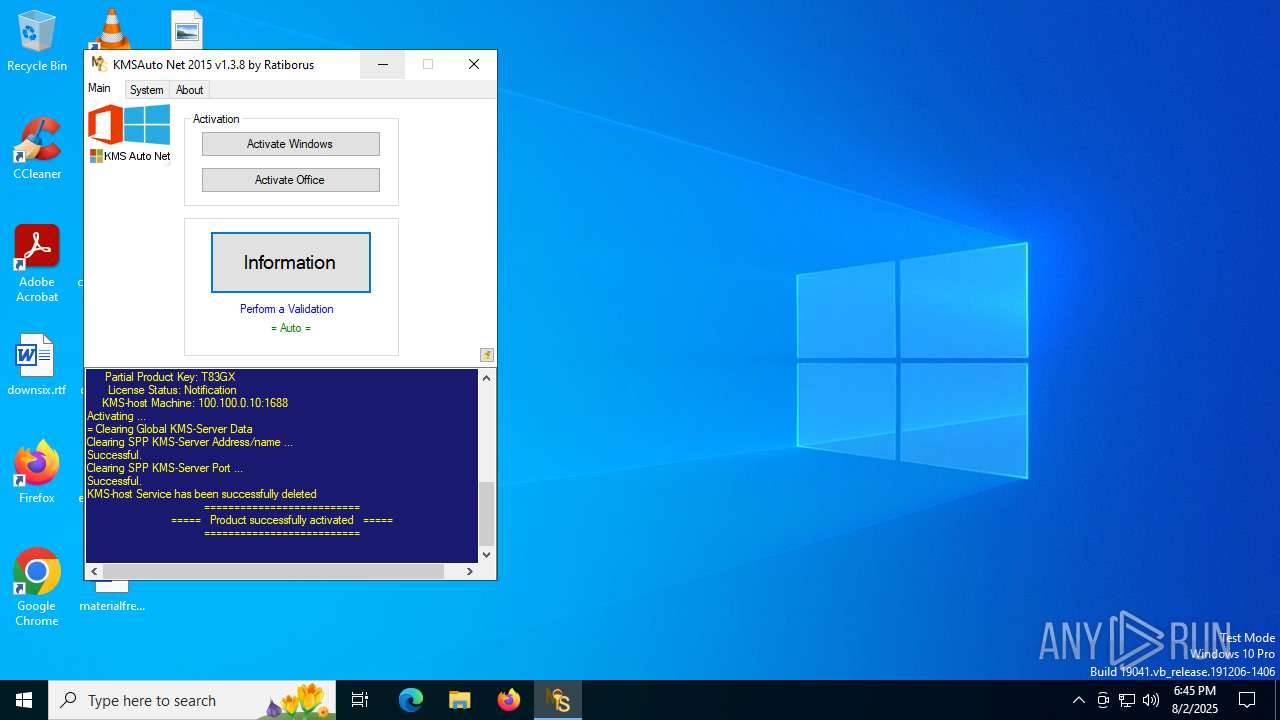
| Verdict: | Malicious activity |
| Analysis date: | August 02, 2025, 18:44:50 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 6EE7F3ECD5111CD5306792FD3141515D |
| SHA1: | 45C92D0E691175A39A8C61228F526F80A7CA94FC |
| SHA256: | 69A8AE6352CFFD366409DF8E566E84315B4BFFCF5865A4B8079C446123BA1D26 |
| SSDEEP: | 196608:0eywBGqyw1lT3ywuywQyw1ywlywaywTyw9lywfywEyw1ywHywwywmIBywyywsywv:IwBGnw1l+wjwNw4wIw3w2w9IwqwJw4w4 |
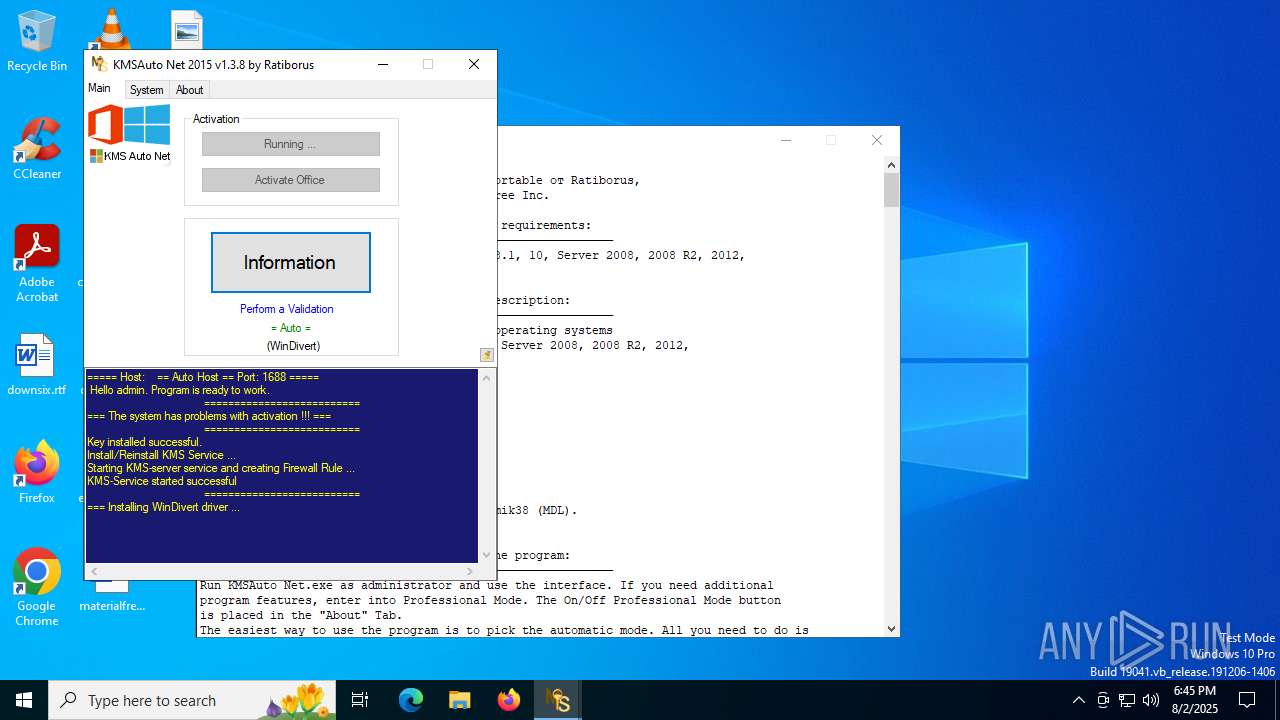
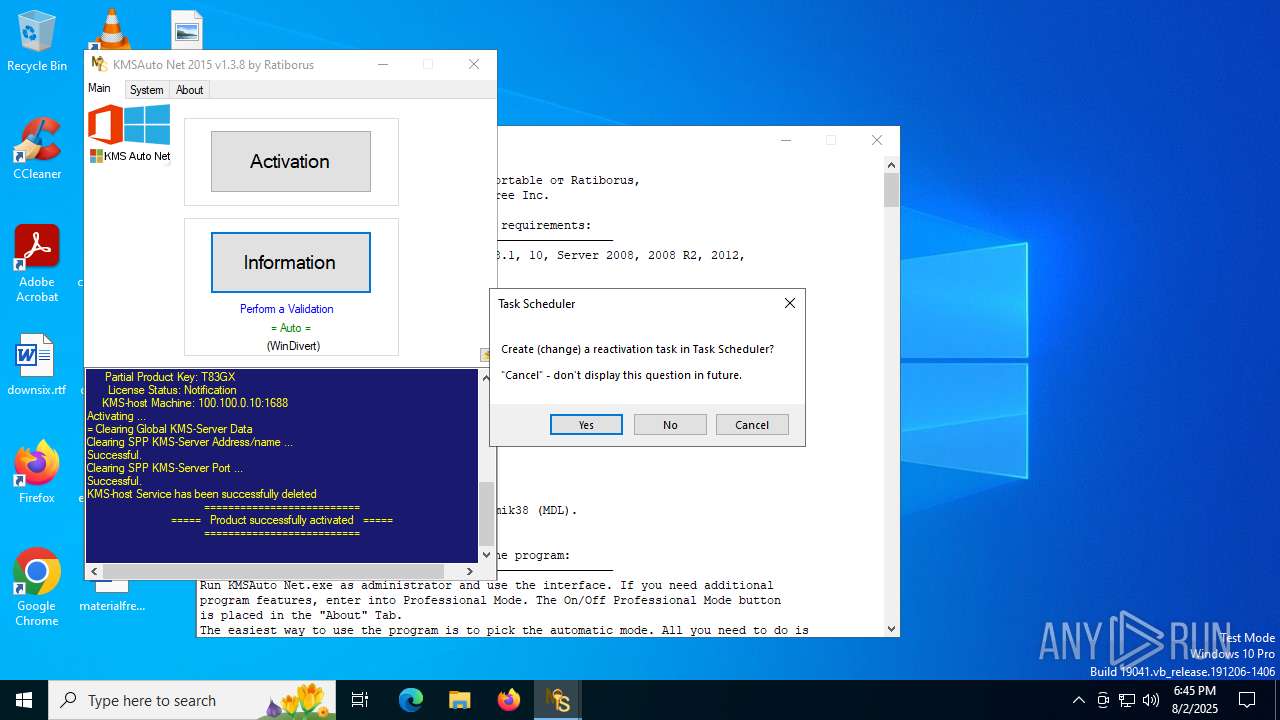
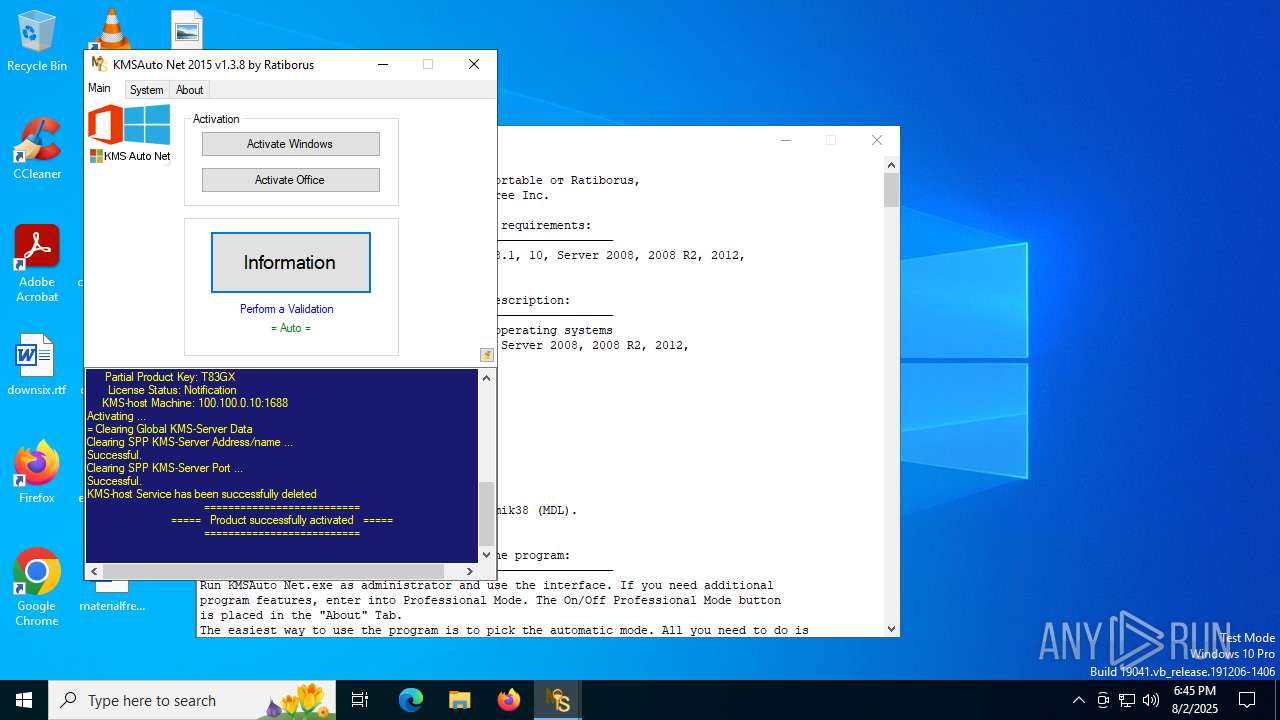
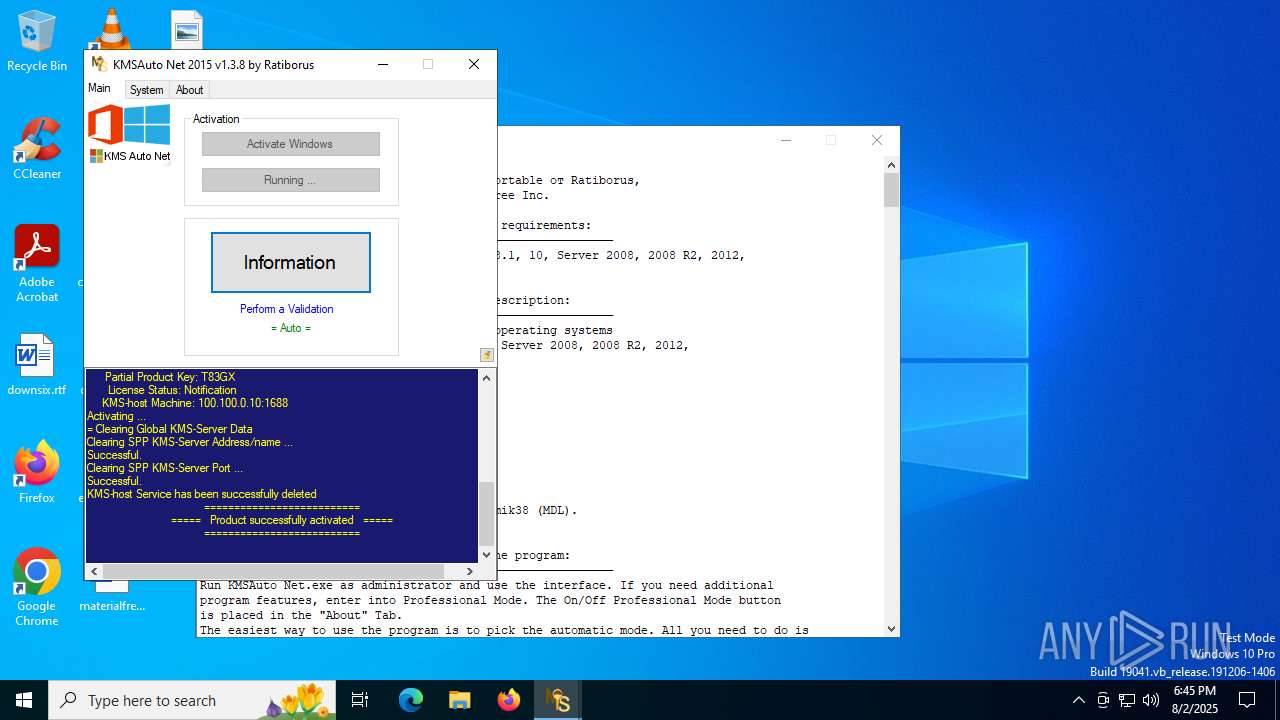
MALICIOUS
Opens a text file (SCRIPT)
- cscript.exe (PID: 3148)
- cscript.exe (PID: 1216)
SUSPICIOUS
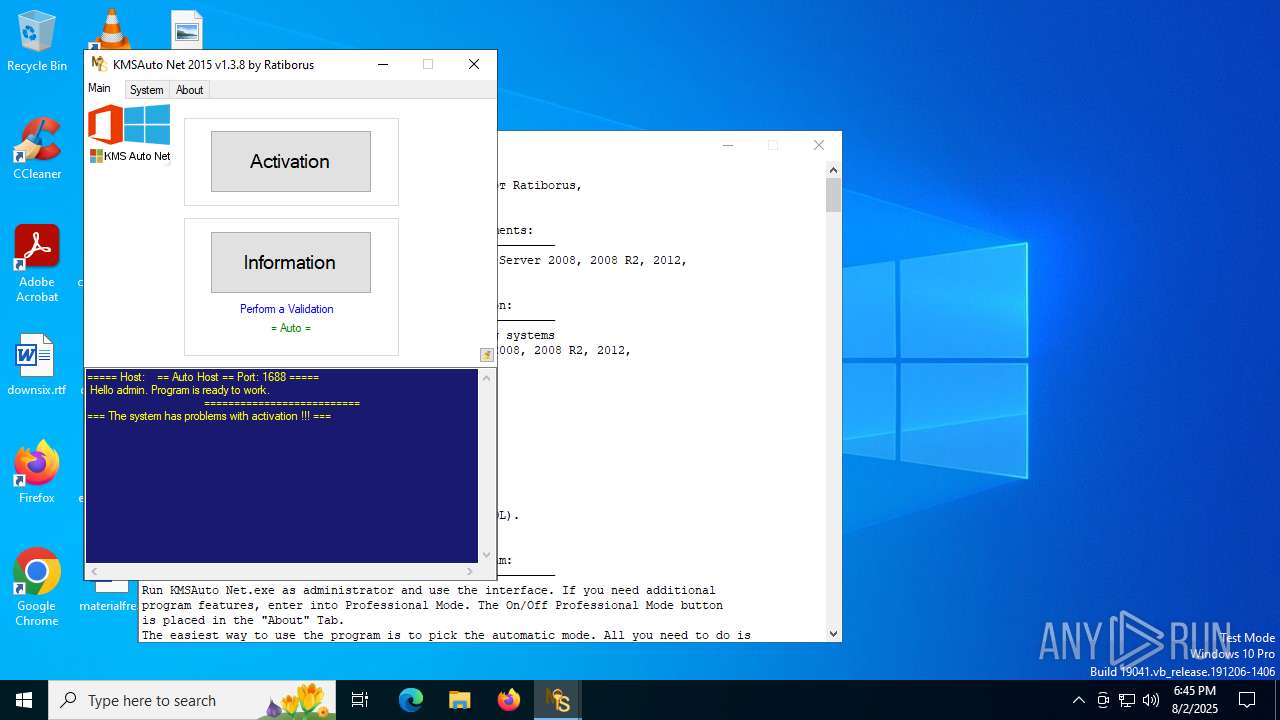
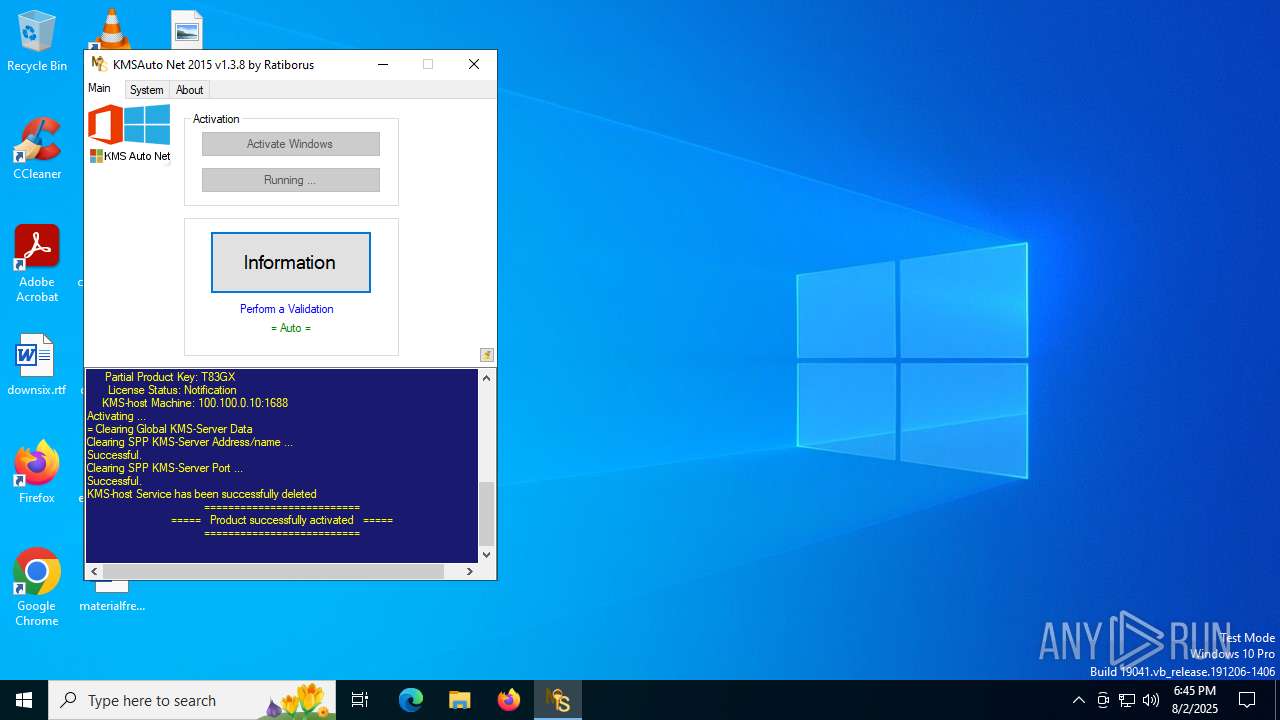
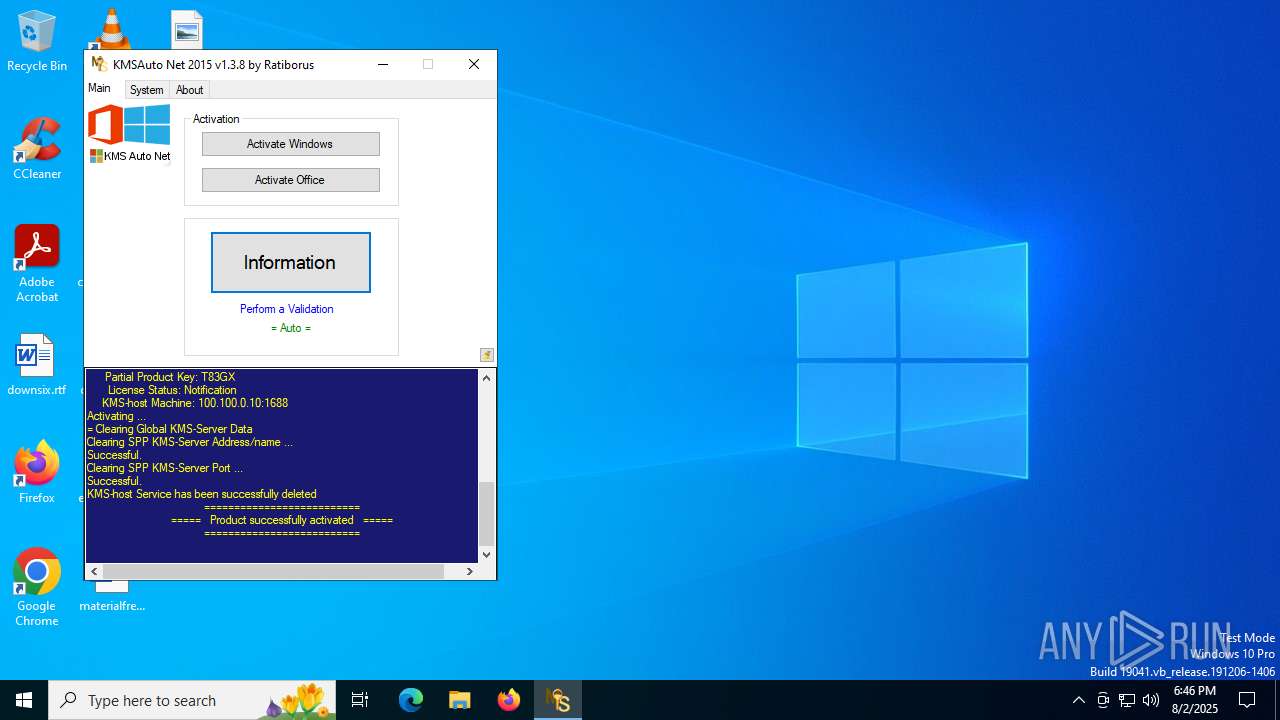
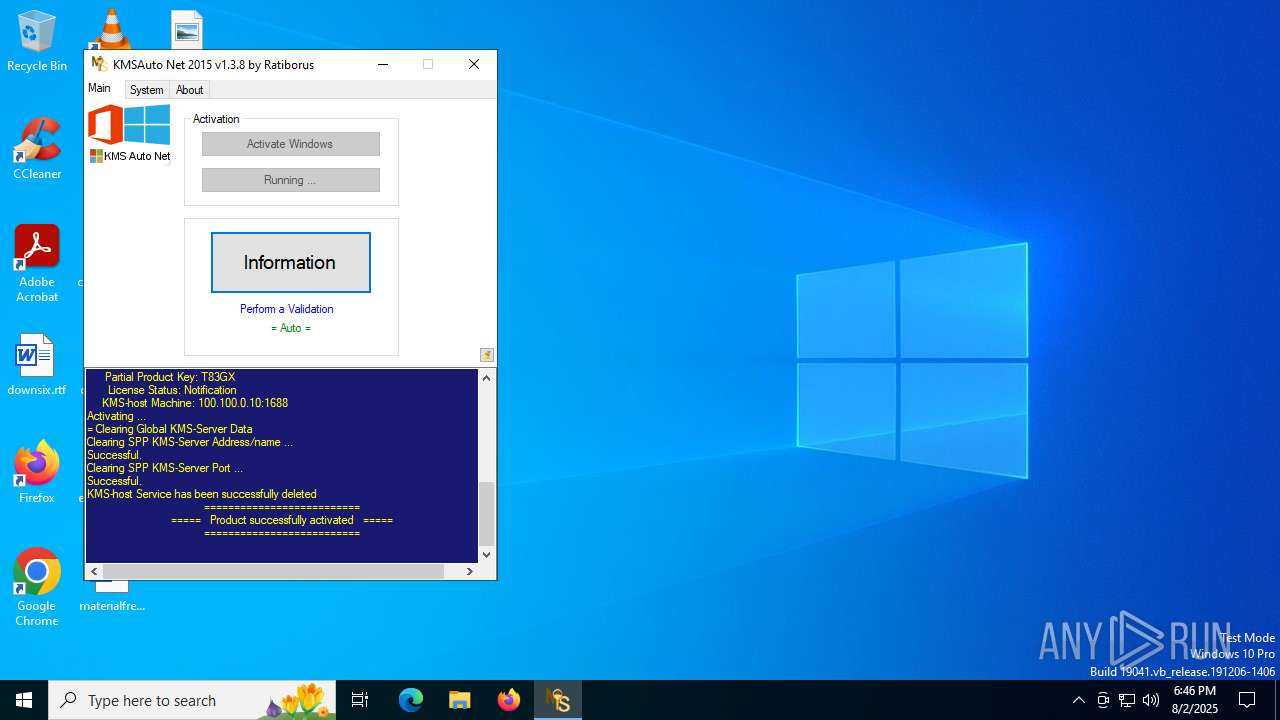
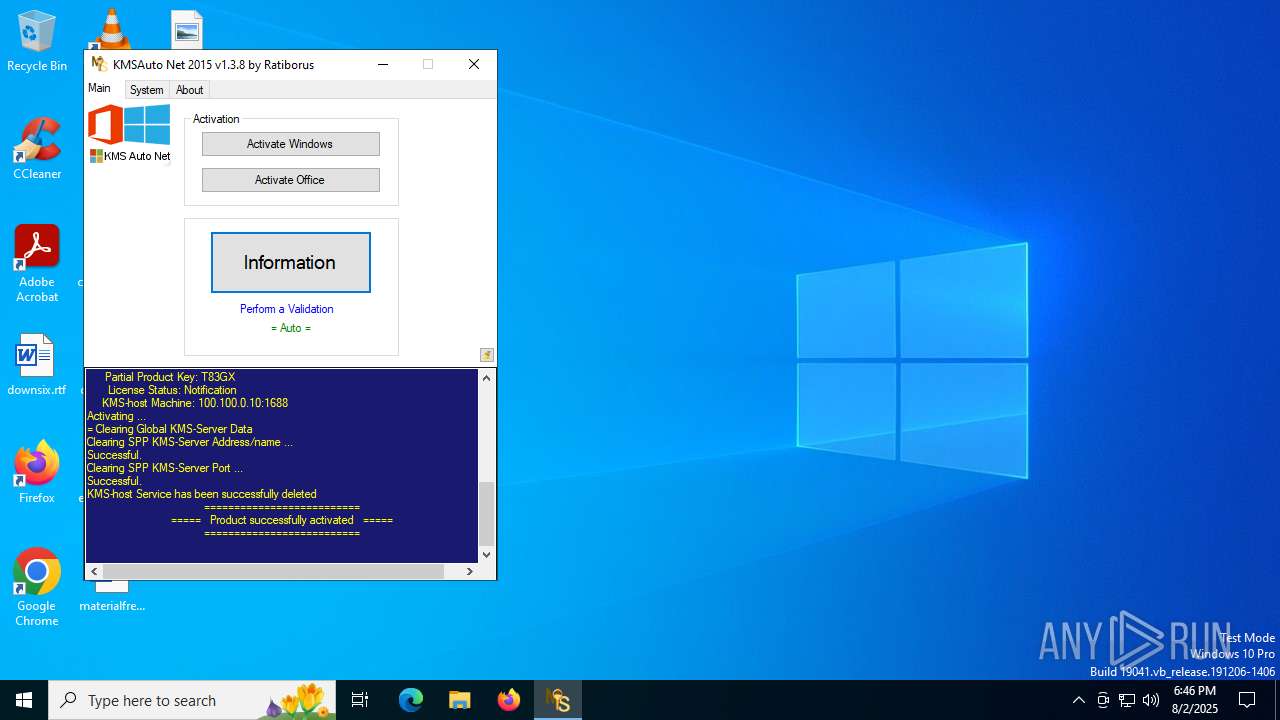
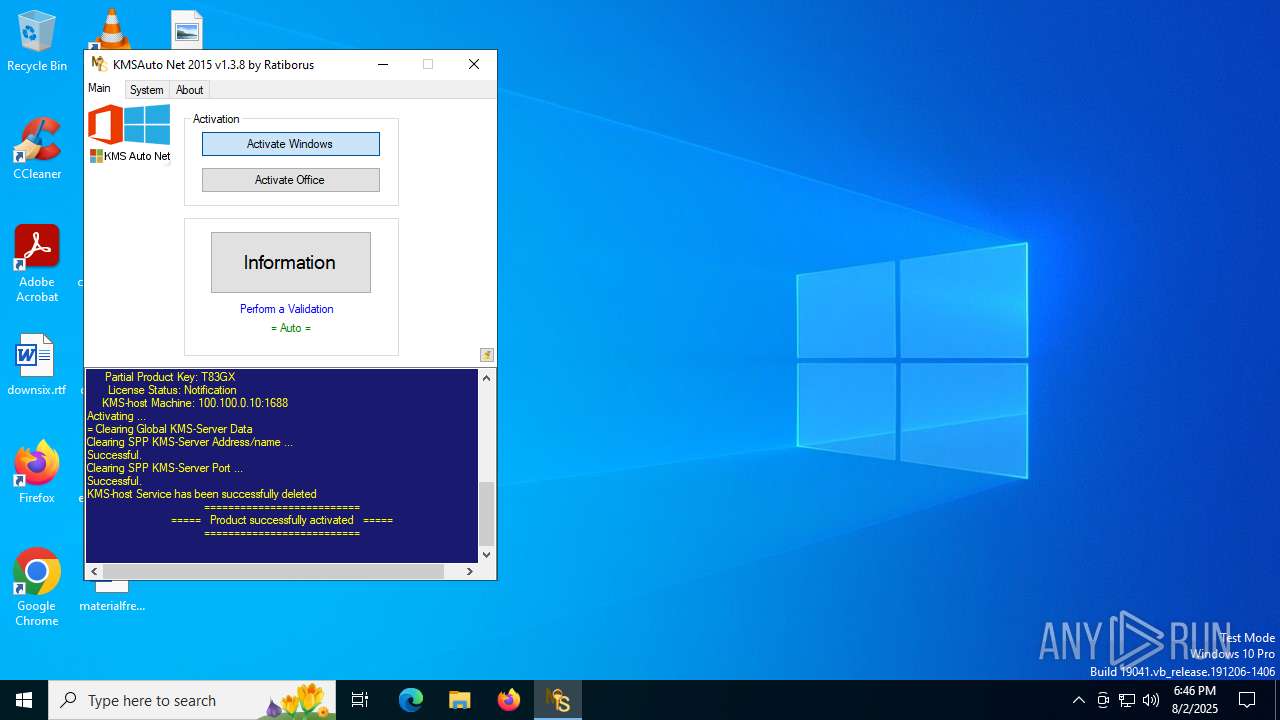
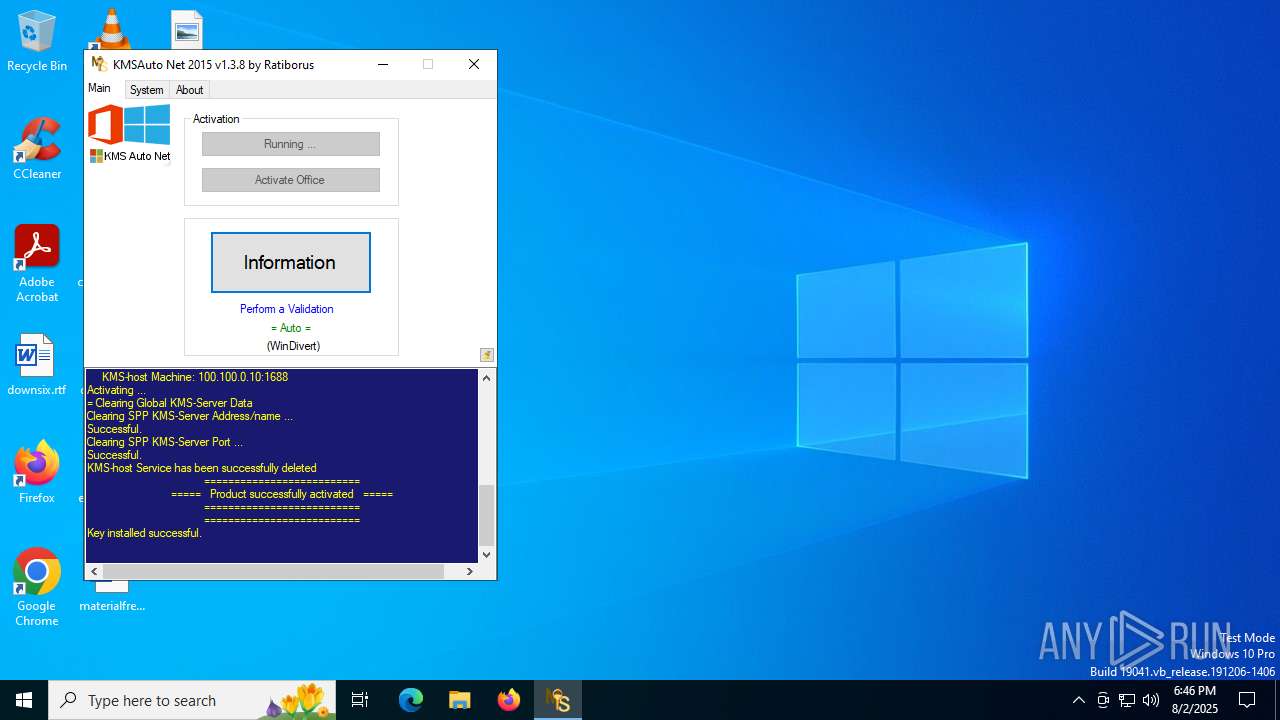
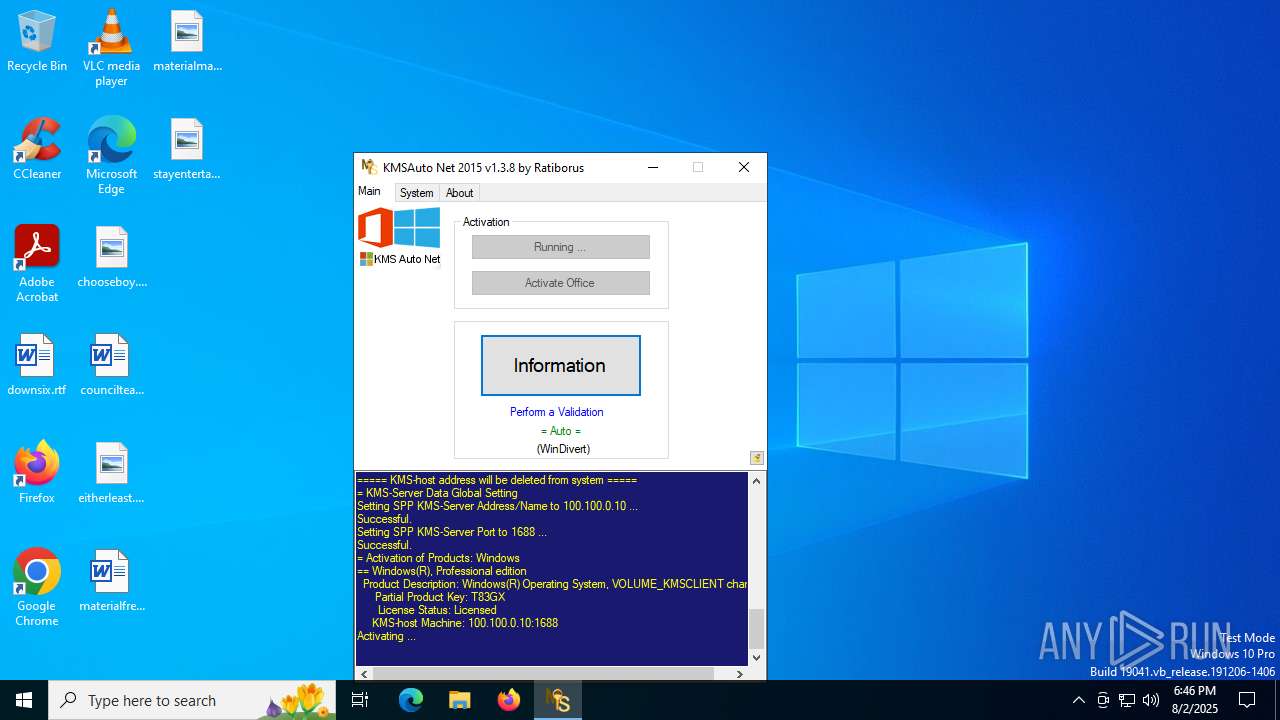
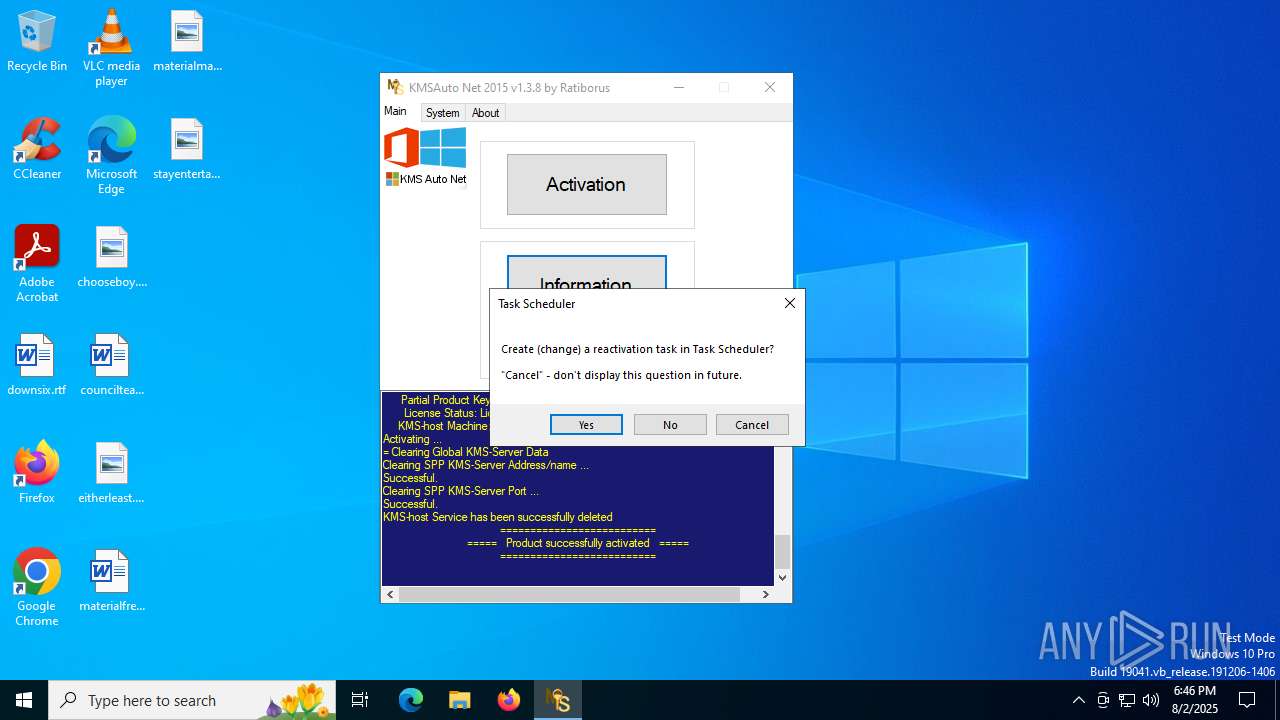
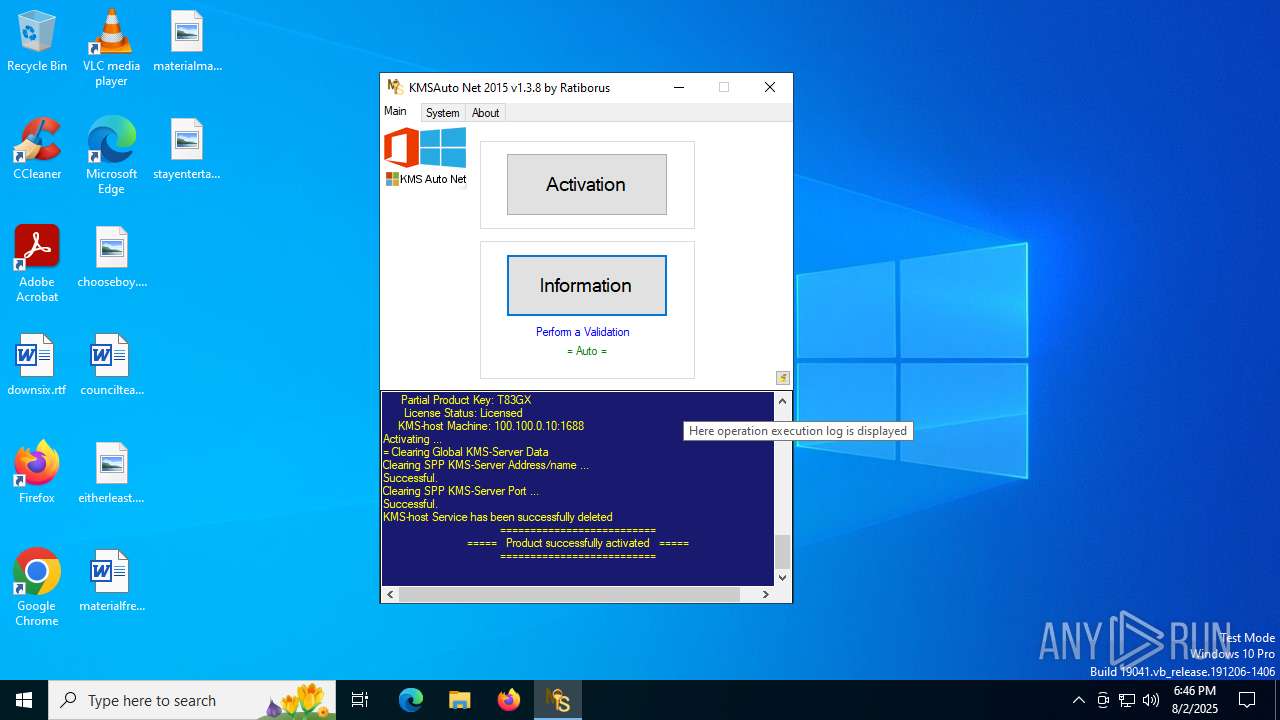
KMS tool has been detected
- KMSAuto Net.exe (PID: 4888)
- KMSAuto Net.exe (PID: 1948)
- KMSAuto Net.exe (PID: 1948)
Reads Internet Explorer settings
- KMSAuto Net.exe (PID: 1948)
There is functionality for taking screenshot (YARA)
- KMSAuto Net.exe (PID: 1948)
The process executes VB scripts
- KMSAuto Net.exe (PID: 1948)
Starts CMD.EXE for commands execution
- KMSAuto Net.exe (PID: 1948)
- cmd.exe (PID: 5780)
- cmd.exe (PID: 304)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- cscript.exe (PID: 3148)
- cscript.exe (PID: 1216)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 3148)
- cscript.exe (PID: 1216)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 3148)
- cscript.exe (PID: 1216)
Checks whether a specific file exists (SCRIPT)
- cscript.exe (PID: 3148)
- cscript.exe (PID: 1216)
Reads data from a binary Stream object (SCRIPT)
- cscript.exe (PID: 3148)
- cscript.exe (PID: 1216)
Executes WMI query (SCRIPT)
- cscript.exe (PID: 3148)
- cscript.exe (PID: 1216)
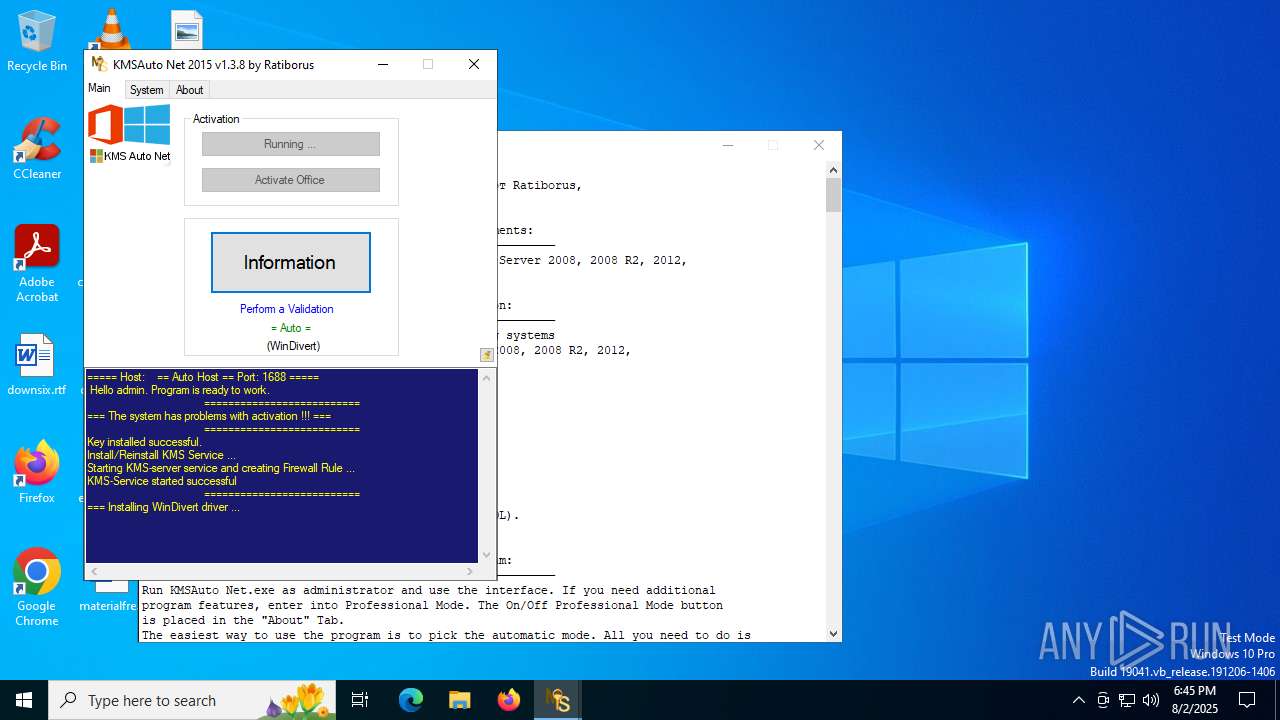
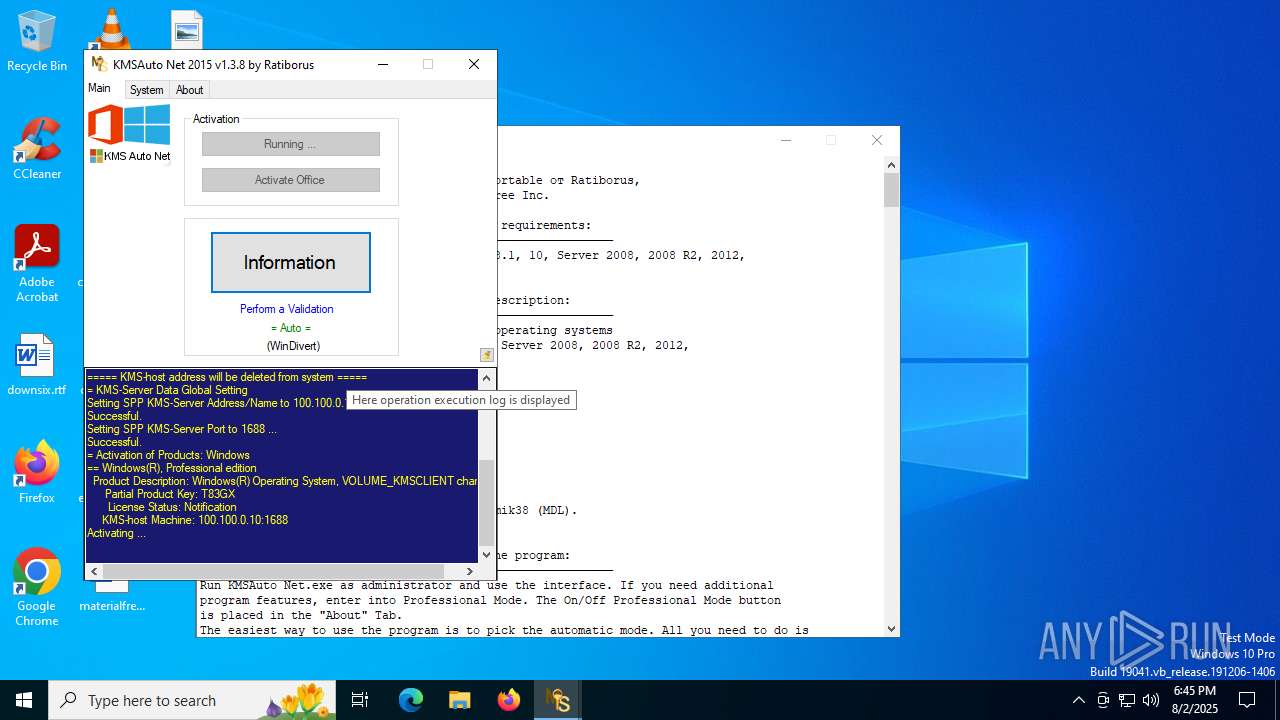
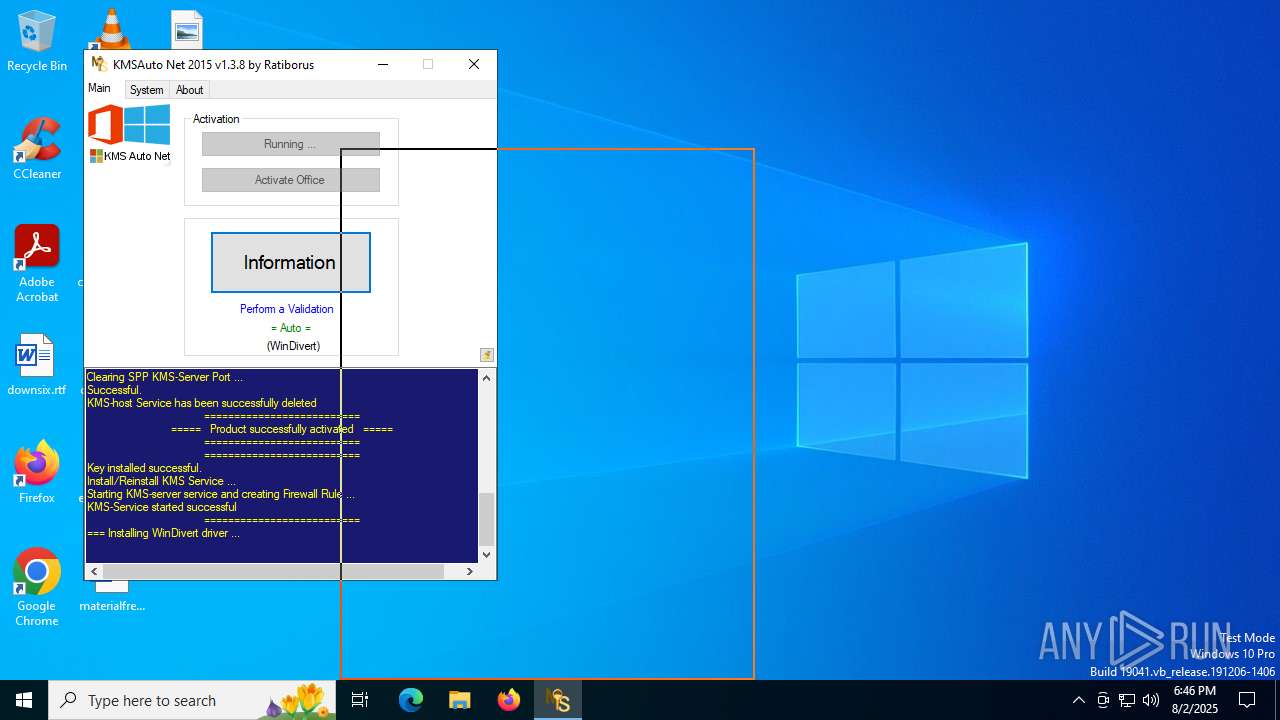
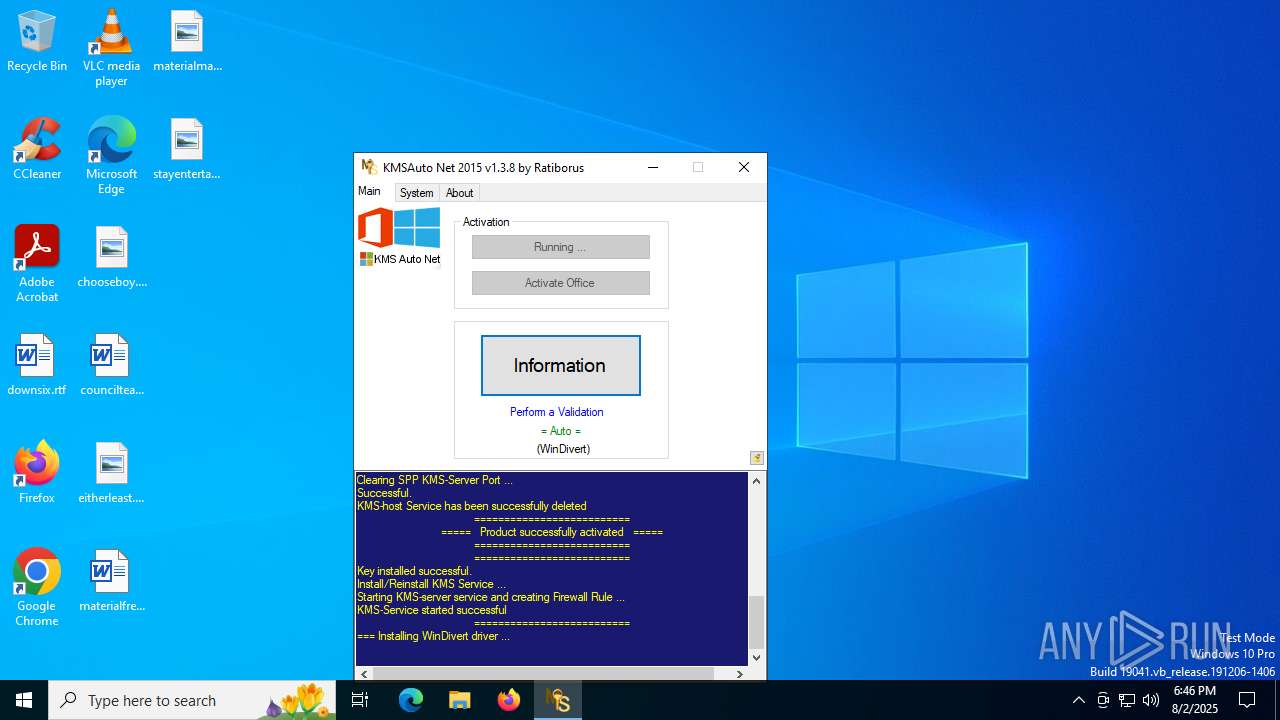
Drops a system driver (possible attempt to evade defenses)
- bin_x64.dat (PID: 440)
- bin_x64.dat (PID: 4032)
Executable content was dropped or overwritten
- KMSAuto Net.exe (PID: 1948)
- bin.dat (PID: 6768)
- bin_x64.dat (PID: 440)
- bin.dat (PID: 6720)
- bin_x64.dat (PID: 4032)
Drops 7-zip archiver for unpacking
- KMSAuto Net.exe (PID: 1948)
Starts application with an unusual extension
- cmd.exe (PID: 4044)
- cmd.exe (PID: 6900)
- cmd.exe (PID: 1380)
- cmd.exe (PID: 7076)
Process drops legitimate windows executable
- bin_x64.dat (PID: 440)
- bin_x64.dat (PID: 4032)
Application launched itself
- cmd.exe (PID: 5780)
- cmd.exe (PID: 304)
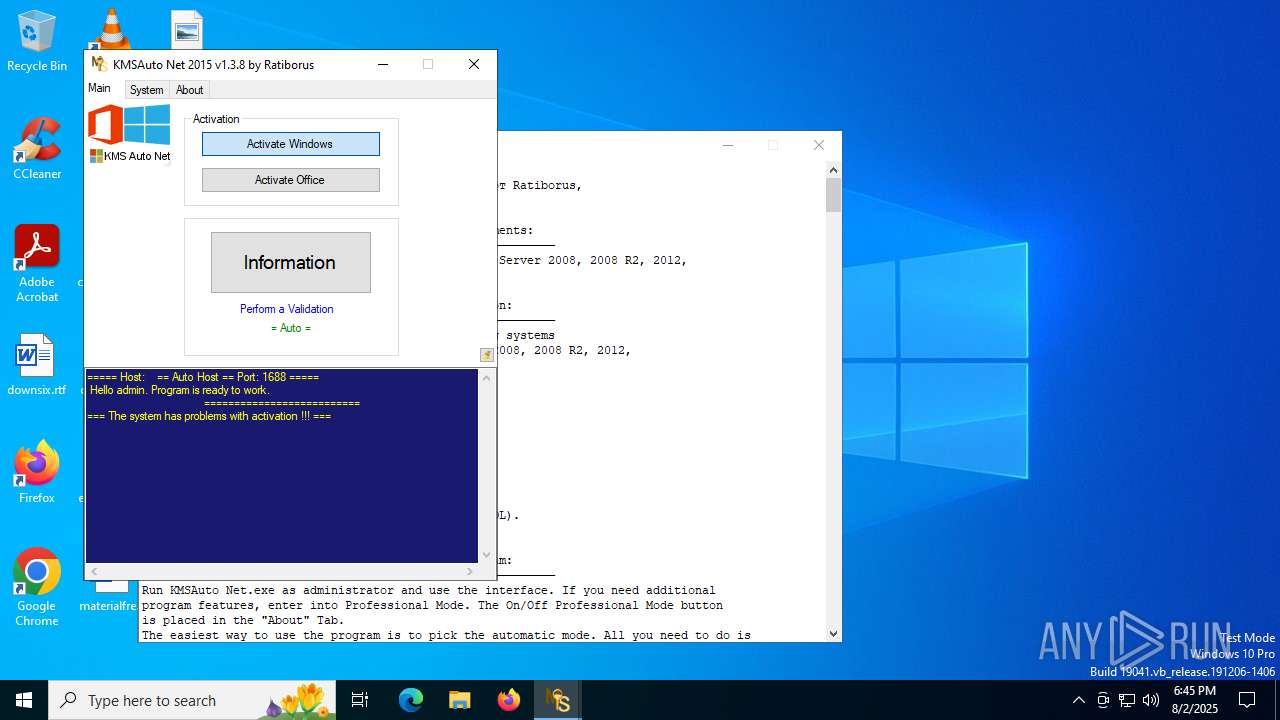
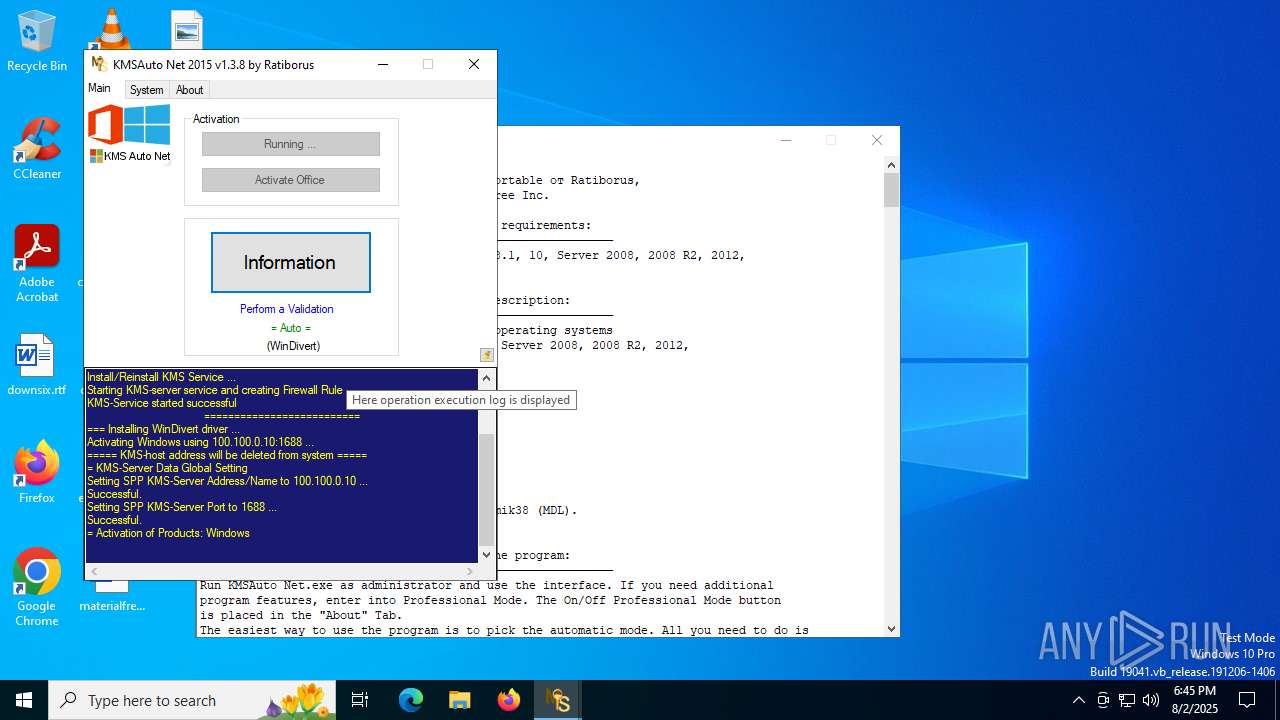
Uses NETSH.EXE to delete a firewall rule or allowed programs
- KMSAuto Net.exe (PID: 1948)
Uses NETSH.EXE to add a firewall rule or allowed programs
- KMSAuto Net.exe (PID: 1948)
Windows service management via SC.EXE
- sc.exe (PID: 6572)
- sc.exe (PID: 6636)
- sc.exe (PID: 4112)
- sc.exe (PID: 5724)
- sc.exe (PID: 592)
- sc.exe (PID: 6364)
Executes as Windows Service
- KMSSS.exe (PID: 3876)
- KMSSS.exe (PID: 4020)
Uses ROUTE.EXE to modify routing table
- cmd.exe (PID: 2632)
- cmd.exe (PID: 1148)
Uses REG/REGEDIT.EXE to modify registry
- KMSAuto Net.exe (PID: 1948)
- cmd.exe (PID: 2388)
- cmd.exe (PID: 2120)
Uses ROUTE.EXE to obtain the routing table information
- cmd.exe (PID: 4168)
- cmd.exe (PID: 828)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 1288)
- cmd.exe (PID: 304)
- cmd.exe (PID: 1508)
Creates a new Windows service
- sc.exe (PID: 6836)
- sc.exe (PID: 4892)
Creates or modifies Windows services
- KMSAuto Net.exe (PID: 1948)
Stops a currently running service
- sc.exe (PID: 2628)
- sc.exe (PID: 2528)
- sc.exe (PID: 6096)
- sc.exe (PID: 6544)
INFO
Reads the computer name
- KMSAuto Net.exe (PID: 1948)
- FakeClient.exe (PID: 3860)
- KMSSS.exe (PID: 3876)
- KMSSS.exe (PID: 4020)
- FakeClient.exe (PID: 3876)
Checks supported languages
- KMSAuto Net.exe (PID: 1948)
- bin.dat (PID: 6768)
- bin_x64.dat (PID: 440)
- FakeClient.exe (PID: 3860)
- KMSSS.exe (PID: 3876)
- bin.dat (PID: 6720)
- bin_x64.dat (PID: 4032)
- KMSSS.exe (PID: 4020)
- FakeClient.exe (PID: 3876)
Creates a new folder
- cmd.exe (PID: 5772)
- cmd.exe (PID: 5772)
- cmd.exe (PID: 768)
Reads the machine GUID from the registry
- KMSAuto Net.exe (PID: 1948)
- KMSSS.exe (PID: 3876)
- KMSSS.exe (PID: 4020)
Creates files or folders in the user directory
- KMSAuto Net.exe (PID: 1948)
Reads Environment values
- KMSAuto Net.exe (PID: 1948)
Reads product name
- KMSAuto Net.exe (PID: 1948)
Reads security settings of Internet Explorer
- cscript.exe (PID: 3148)
- cscript.exe (PID: 1216)
Creates files in the program directory
- cmd.exe (PID: 5772)
- KMSAuto Net.exe (PID: 1948)
- bin.dat (PID: 6768)
- bin_x64.dat (PID: 440)
- KMSSS.exe (PID: 3876)
- cmd.exe (PID: 768)
- bin.dat (PID: 6720)
- bin_x64.dat (PID: 4032)
- KMSSS.exe (PID: 4020)
The sample compiled with english language support
- KMSAuto Net.exe (PID: 1948)
- bin.dat (PID: 6768)
- bin_x64.dat (PID: 440)
- bin.dat (PID: 6720)
- bin_x64.dat (PID: 4032)
Adds a route via ROUTE.EXE
- ROUTE.EXE (PID: 1976)
- ROUTE.EXE (PID: 2140)
Deletes a route via ROUTE.EXE
- ROUTE.EXE (PID: 4024)
- ROUTE.EXE (PID: 5988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (16) |
|---|---|---|
| .scr | | | Windows screen saver (7.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.8) |
| .exe | | | Win32 Executable (generic) (2.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:08:10 07:45:14+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 6923776 |
| InitializedDataSize: | 49152 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x69c4c2 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.3.8.0 |
| ProductVersionNumber: | 1.3.8.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
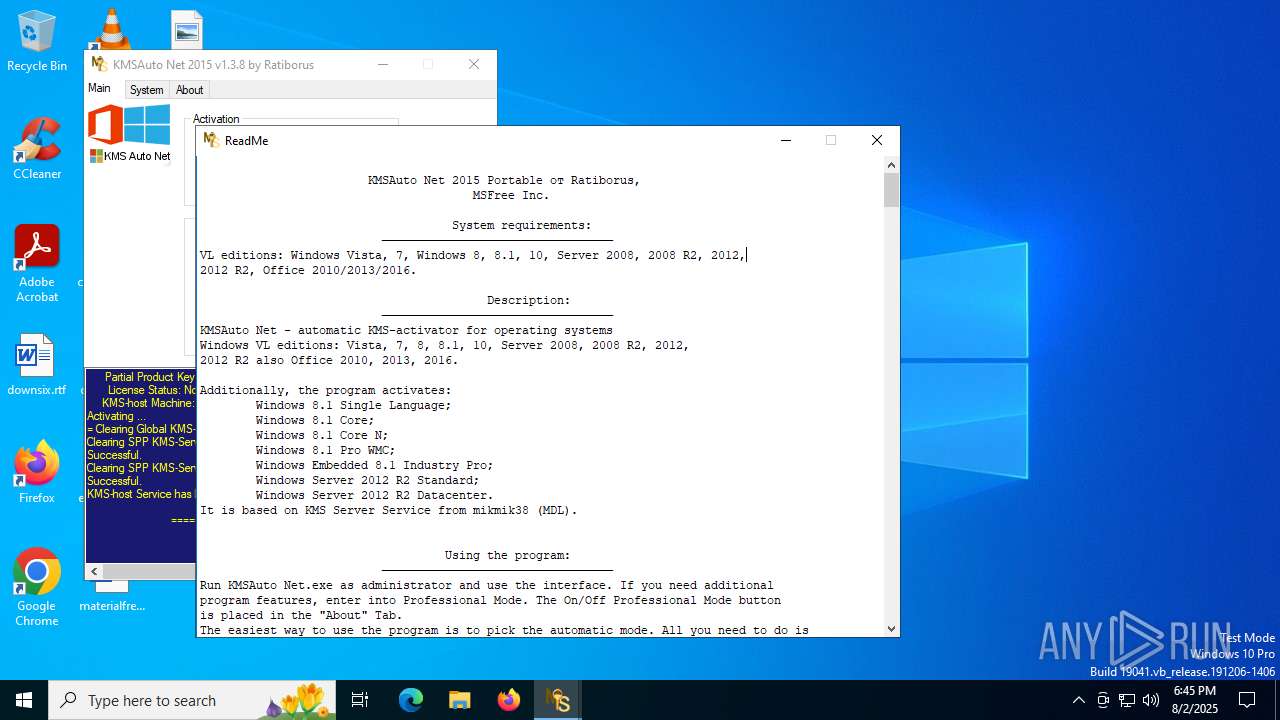
| CompanyName: | MSFree Inc. |
| FileDescription: | KMSAuto Net |
| FileVersion: | 1.3.8 |
| InternalName: | KMSAuto Net.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | KMSAuto Net.exe |
| ProductName: | KMSAuto Net |
| ProductVersion: | 1.3.8 |
| AssemblyVersion: | 1.3.8.0 |
Total processes
288
Monitored processes
146
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 304 | C:\WINDOWS\Sysnative\cmd.exe /c for /f "tokens=5 delims=, " %i in ('netstat -ano ^| find ":1688 "') do taskkill /pid %i /f | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 320 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 440 | bin_x64.dat -y -pkmsauto | C:\ProgramData\KMSAuto\bin_x64.dat | cmd.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7z Console SFX Exit code: 0 Version: 9.20 Modules
| |||||||||||||||
| 592 | "sc.exe" delete WinDivert1.1 | C:\Windows\SysWOW64\sc.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 640 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | svchost.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | C:\WINDOWS\Sysnative\Netsh Advfirewall Firewall delete rule name="0pen Port KMS" protocol=TCP | C:\Windows\System32\netsh.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | C:\WINDOWS\Sysnative\reg delete "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\OfficeSoftwareProtectionPlatform\59A52881-A989-479D-AF46-F275C6370663" /f | C:\Windows\System32\reg.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 768 | C:\WINDOWS\Sysnative\cmd.exe /c md "C:\ProgramData\KMSAuto" | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 790
Read events
6 777
Write events
9
Delete events
4
Modification events
| (PID) Process: | (1948) KMSAuto Net.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\KMSEmulator |
| Operation: | write | Name: | ImagePath |
Value: "C:\ProgramData\KMSAuto\bin\KMSSS.exe" -Port 1688 -PWin RandomKMSPID -PO14 RandomKMSPID -PO15 RandomKMSPID -AI 43200 -RI 43200 KillProcessOnPort -Log -IP | |||
| (PID) Process: | (1948) KMSAuto Net.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\KMSEmulator |
| Operation: | write | Name: | Description |
Value: KMS-host for all Microsoft VL Products | |||
| (PID) Process: | (1948) KMSAuto Net.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\KMSEmulator |
| Operation: | write | Name: | DisplayName |
Value: KMS-host Service | |||
| (PID) Process: | (1712) NETSTAT.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\RFC1156Agent\CurrentVersion\Parameters |
| Operation: | write | Name: | TrapPollTimeMilliSecs |
Value: 15000 | |||
| (PID) Process: | (5532) reg.exe | Key: | HKEY_USERS\S-1-5-20\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\55c92734-d682-4d71-983e-d6ec3f16059f\2de67392-b7a7-462a-b1ca-108dd189f588 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5532) reg.exe | Key: | HKEY_USERS\S-1-5-20\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\55c92734-d682-4d71-983e-d6ec3f16059f |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6620) NETSTAT.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\RFC1156Agent\CurrentVersion\Parameters |
| Operation: | write | Name: | TrapPollTimeMilliSecs |
Value: 15000 | |||
| (PID) Process: | (640) SppExtComObj.Exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\55c92734-d682-4d71-983e-d6ec3f16059f\2de67392-b7a7-462a-b1ca-108dd189f588 |
| Operation: | write | Name: | DiscoveredKeyManagementServiceIpAddress |
Value: 100.100.0.10 | |||
| (PID) Process: | (5884) reg.exe | Key: | HKEY_USERS\S-1-5-20\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\55c92734-d682-4d71-983e-d6ec3f16059f\2de67392-b7a7-462a-b1ca-108dd189f588 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5884) reg.exe | Key: | HKEY_USERS\S-1-5-20\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\55c92734-d682-4d71-983e-d6ec3f16059f |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
27
Suspicious files
12
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1948 | KMSAuto Net.exe | C:\Users\admin\AppData\Local\MSfree Inc\kmsauto.ini | text | |
MD5:B22721ECC7249380EF3032685ED19A5A | SHA256:2AC517A3388939951E5BC81489A251193C4BCB4620A9968BA0EC8F34594952D8 | |||
| 2964 | cmd.exe | C:\Users\admin\AppData\Local\Temp\test.test | text | |
MD5:9F06243ABCB89C70E0C331C61D871FA7 | SHA256:837CCB607E312B170FAC7383D7CCFD61FA5072793F19A25E75FBACB56539B86B | |||
| 6768 | bin.dat | C:\ProgramData\KMSAuto\bin\KMSSS.exe | executable | |
MD5:0F03F72A92AEF6D63EB74E73F8AC201D | SHA256:ACD55C44B8B0D66D66DEFED85CA18082C092F048D3621DA827FCE593305C11FD | |||
| 6768 | bin.dat | C:\ProgramData\KMSAuto\bin\TunMirror2.exe | executable | |
MD5:4AA2E87FBA32884CC6FF97B1798E69EB | SHA256:8D6432321E0C5BC3C9ABEFB6B0C102F30E910B0691D90194DD0115A4F4DC4D9C | |||
| 1948 | KMSAuto Net.exe | C:\ProgramData\KMSAuto\bin_x64.dat | executable | |
MD5:0D42791E1447DDAB3D145E4A9354ACC3 | SHA256:A374C877CFAD58399CC7100DA71D11FC81119E6940F62D0C98A4FF4034D8A653 | |||
| 6768 | bin.dat | C:\ProgramData\KMSAuto\bin\TunMirror.exe | executable | |
MD5:362498C3E71EEAA066A67E4A3F981D1C | SHA256:D87E8D9D43758CE67A8052CB2334B99CC24F9B0437EE44815F360BE0B22D835A | |||
| 440 | bin_x64.dat | C:\ProgramData\KMSAuto\bin\driver\x64TAP1\OemVista.inf | binary | |
MD5:864625122184689B4854483B51BD4C09 | SHA256:4A4CC81DD6655906E817EBAEDE1692871A79B7000A5F9188B30082C06C71894B | |||
| 440 | bin_x64.dat | C:\ProgramData\KMSAuto\bin\driver\x64WDV\WinDivert.inf | text | |
MD5:A94D989905A248AFCA52BC3CBFCB248B | SHA256:6C9F7DEA4F9A47788D5D2BA110B08457FD00DBABE4812EBCA6F022300843A75D | |||
| 440 | bin_x64.dat | C:\ProgramData\KMSAuto\bin\driver\oas_sert.cer | binary | |
MD5:0041584E5F66762B1FA9BE8910D0B92B | SHA256:BB27684B569CBB72DEC63EA6FDEF8E5F410CDAEB73717EEE1B36478DBCFF94CC | |||
| 440 | bin_x64.dat | C:\ProgramData\KMSAuto\bin\driver\x64TAP2\tapoas.inf | binary | |
MD5:61243CB103543EE3163BF16DF69BCB54 | SHA256:1652B1DE2F15EEACBD06E0AB14ADA5A466316FFD3AB88D4A2A46CFCBD25FDFA1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
23
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.14:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
3644 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
4512 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 420 b | whitelisted |
4512 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
1268 | svchost.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
2940 | svchost.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | DE | binary | 734 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3480 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3644 | svchost.exe | 20.190.159.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3644 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.216.77.14:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
validation-v2.sls.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
FakeClient.exe | WdfCoInstaller: [08/02/2025 18:45.14.395] ReadComponents: WdfSection for Driver Service windivert using KMDF lib version Major 0x1, minor 0x9
|
FakeClient.exe | WdfCoInstaller: [08/02/2025 18:45.14.411] BootApplication: could not open service windivert, error error(1060) The specified service does not exist as an installed service.
|
FakeClient.exe | WdfCoInstaller: [08/02/2025 18:45.14.411] BootApplication: GetStartType error error(87) The parameter is incorrect.
Driver Service name windivert
|
FakeClient.exe | WdfCoInstaller: [08/02/2025 18:46.07.898] ReadComponents: WdfSection for Driver Service windivert using KMDF lib version Major 0x1, minor 0x9
|
FakeClient.exe | WdfCoInstaller: [08/02/2025 18:46.07.898] BootApplication: could not open service windivert, error error(1060) The specified service does not exist as an installed service.
|
FakeClient.exe | WdfCoInstaller: [08/02/2025 18:46.07.898] BootApplication: GetStartType error error(87) The parameter is incorrect.
Driver Service name windivert
|