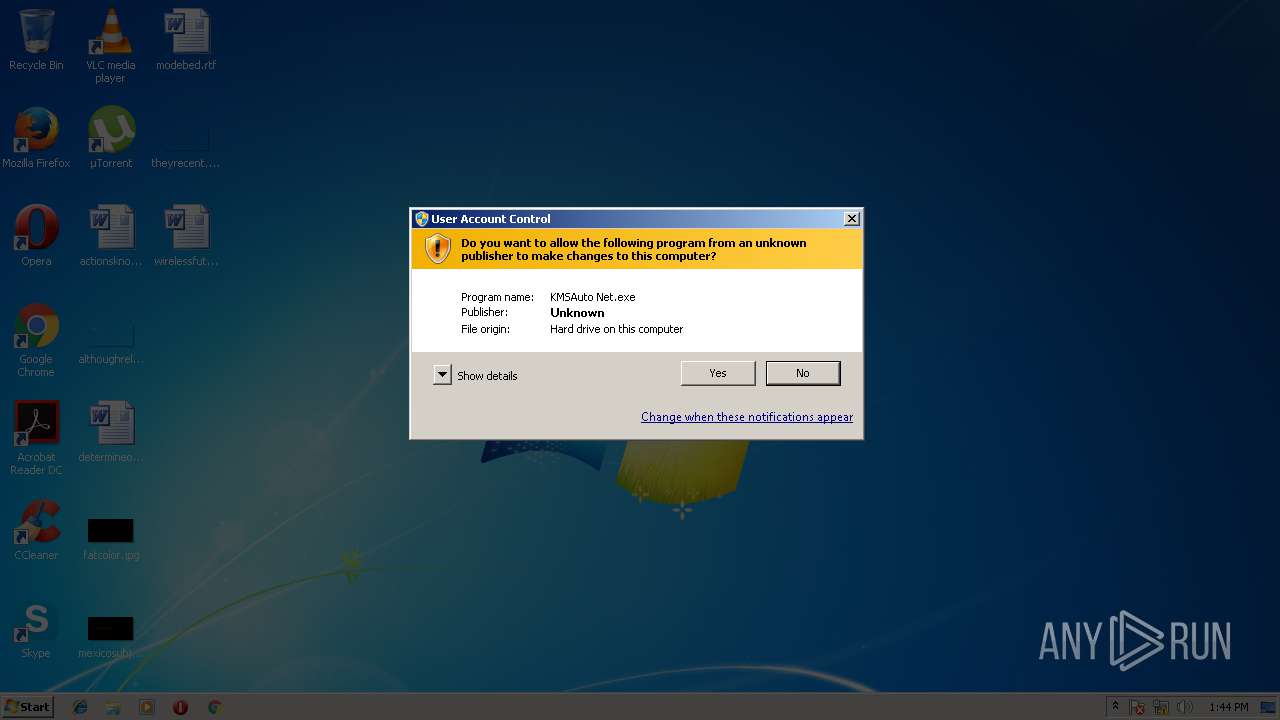
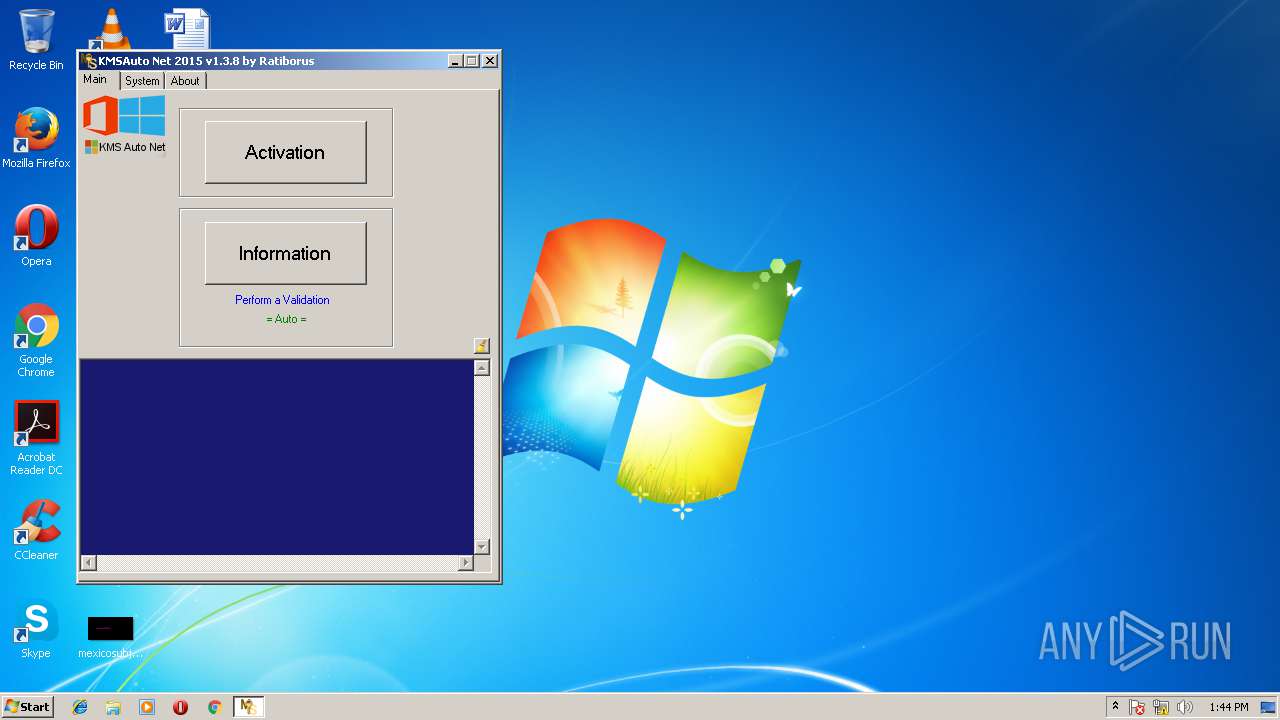
| File name: | KMSAuto Net.exe |
| Full analysis: | https://app.any.run/tasks/91afc0f3-63f8-459f-8a49-971c44a46093 |
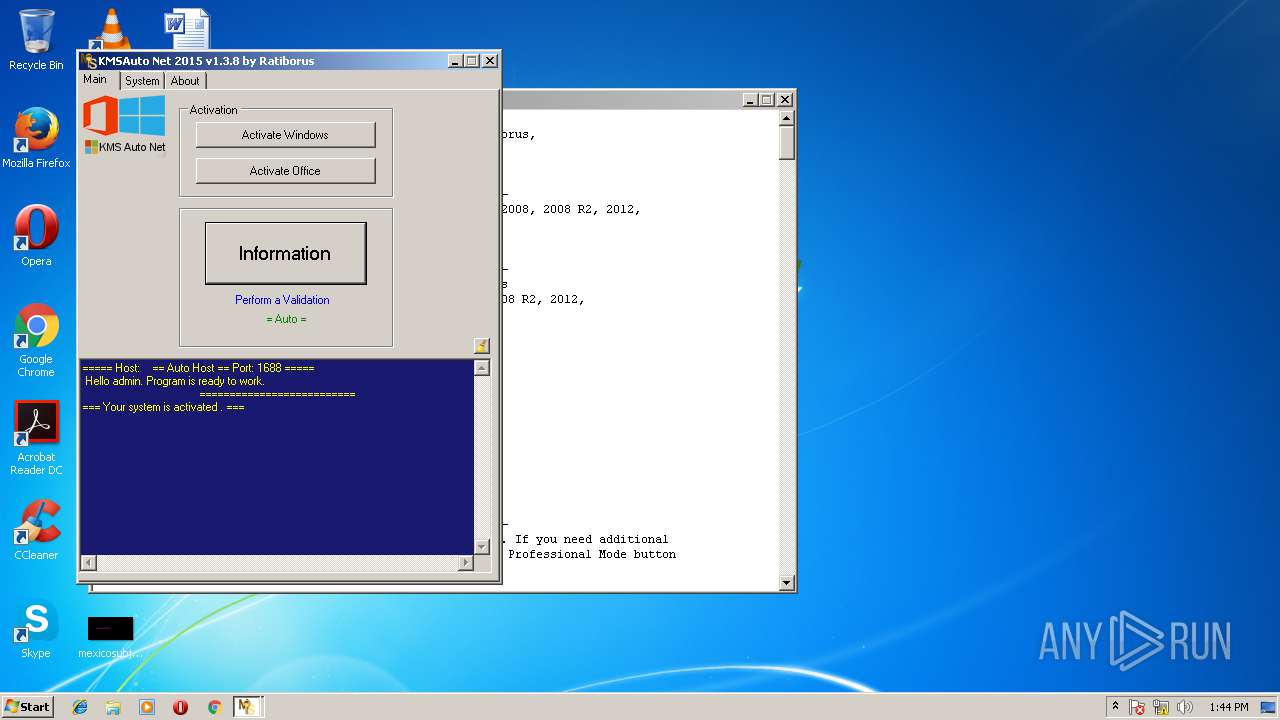
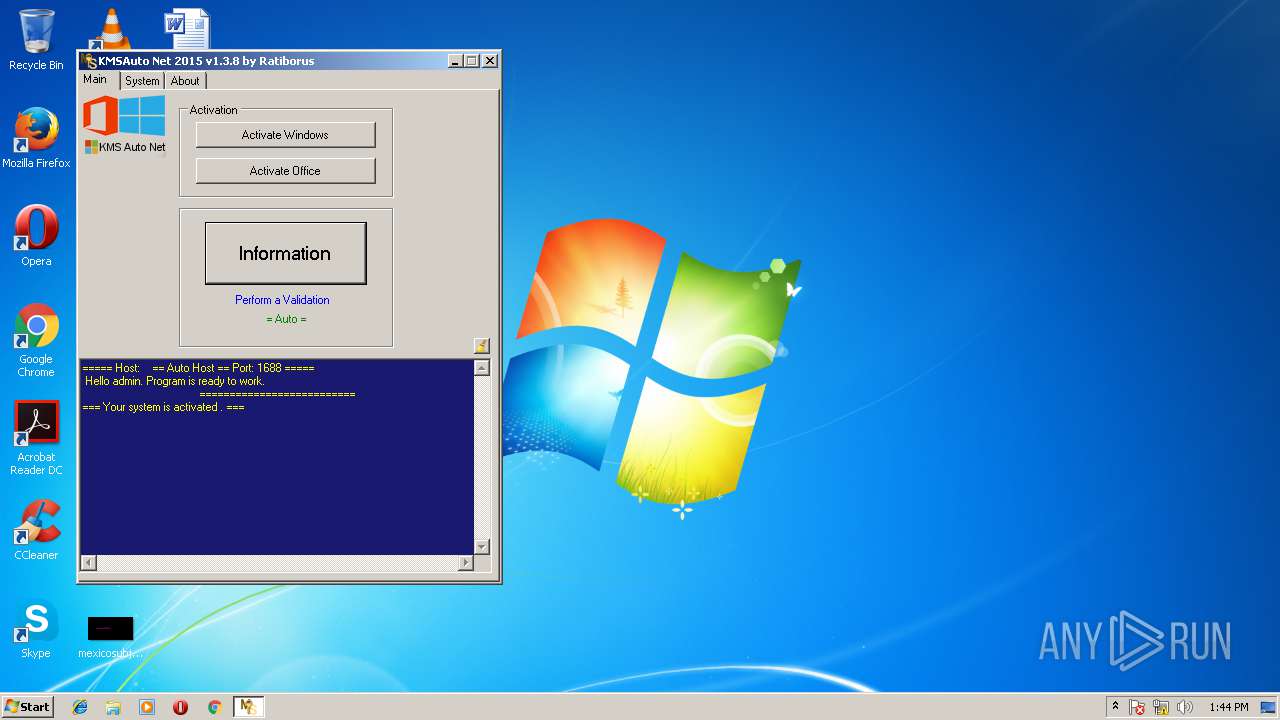
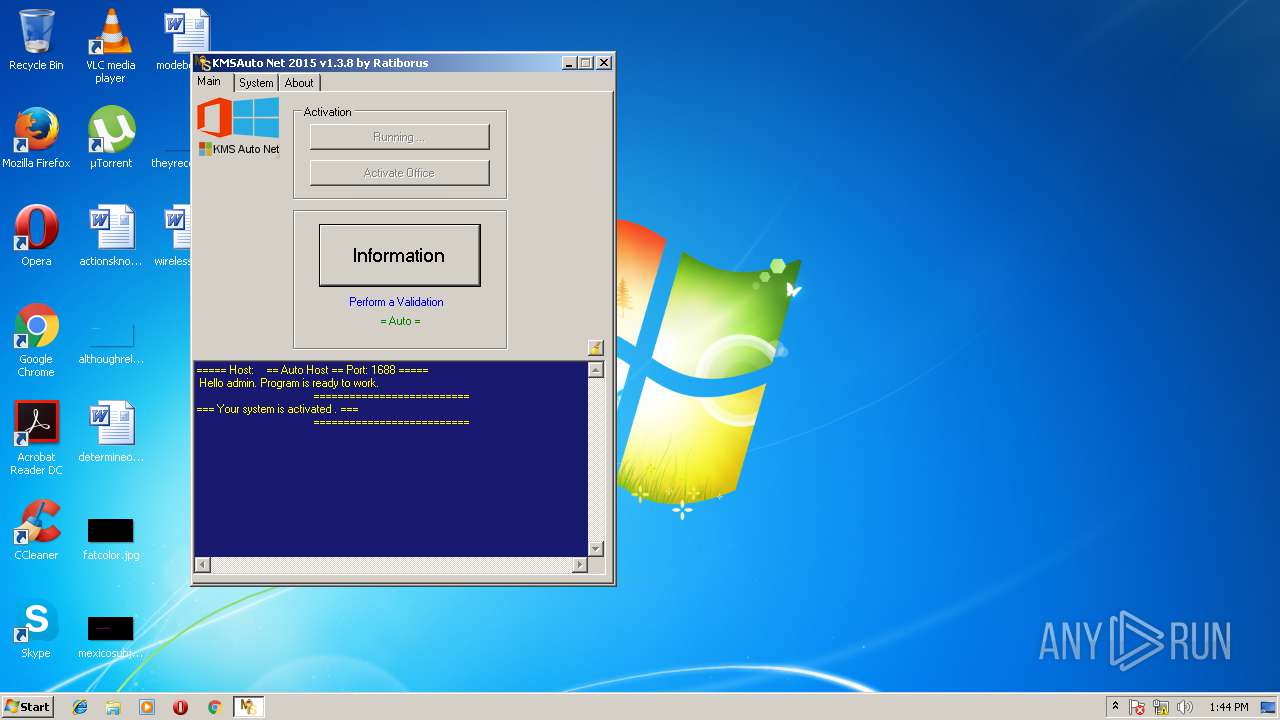
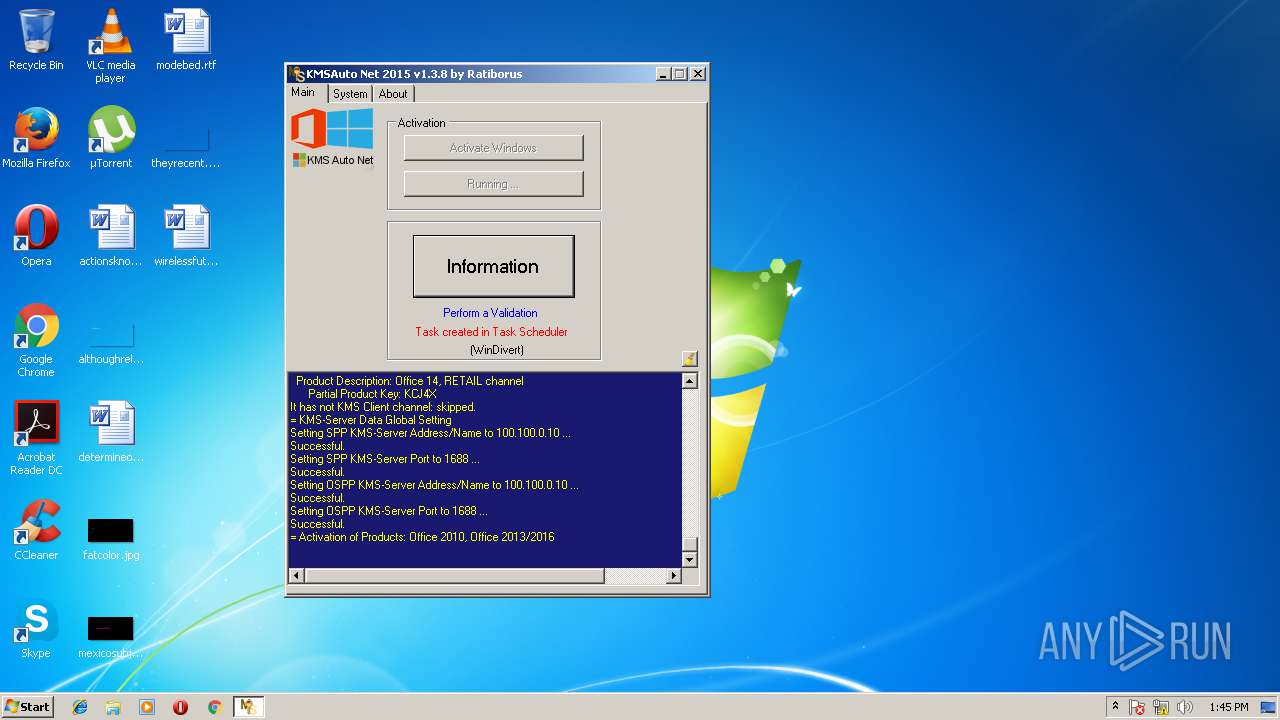
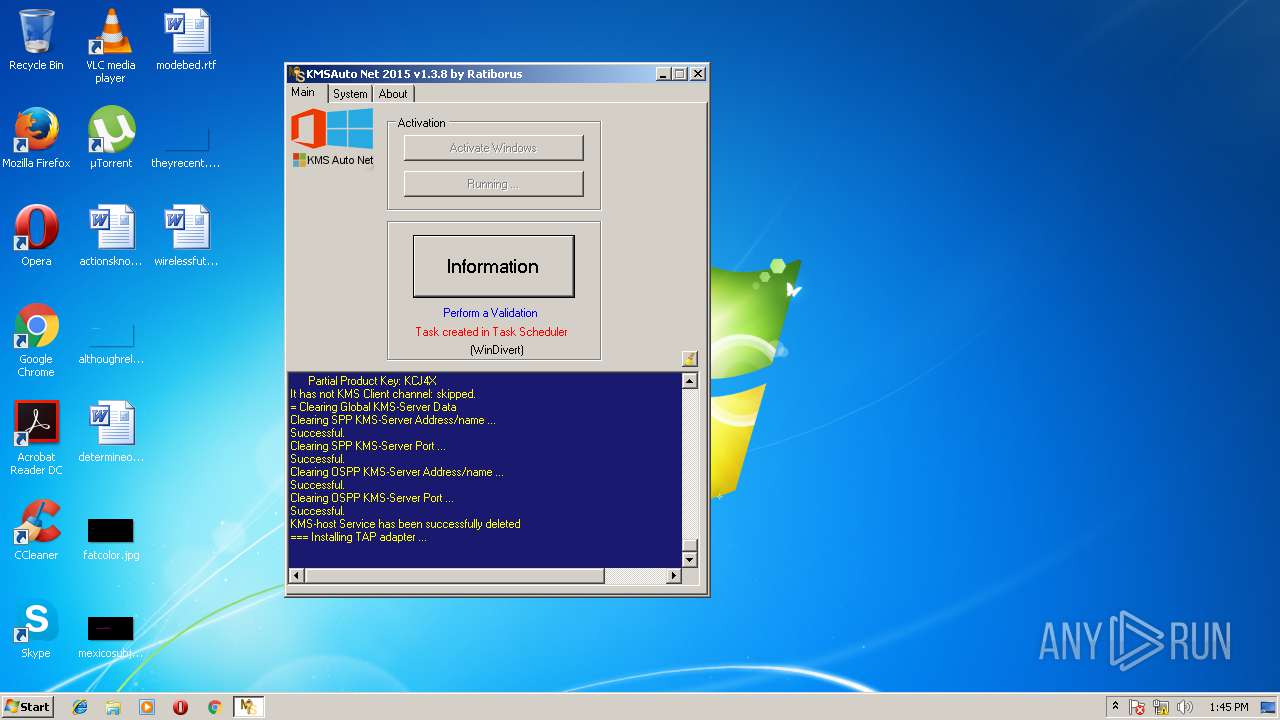
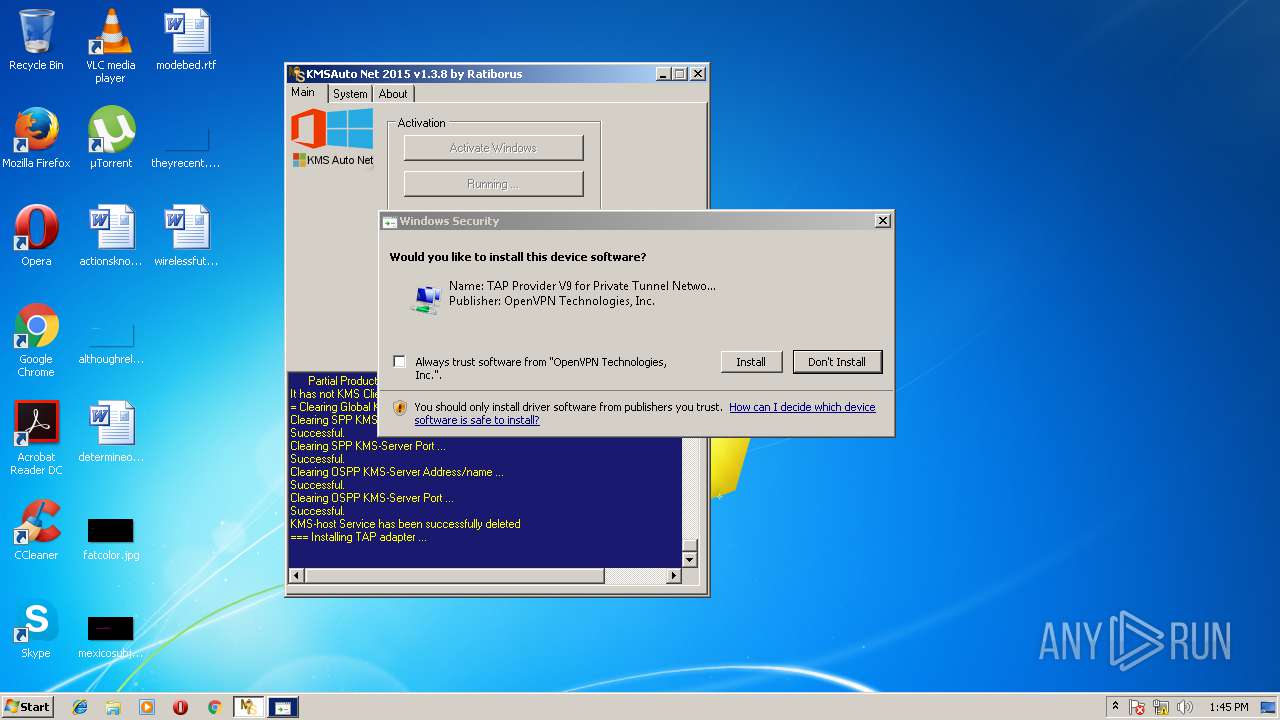
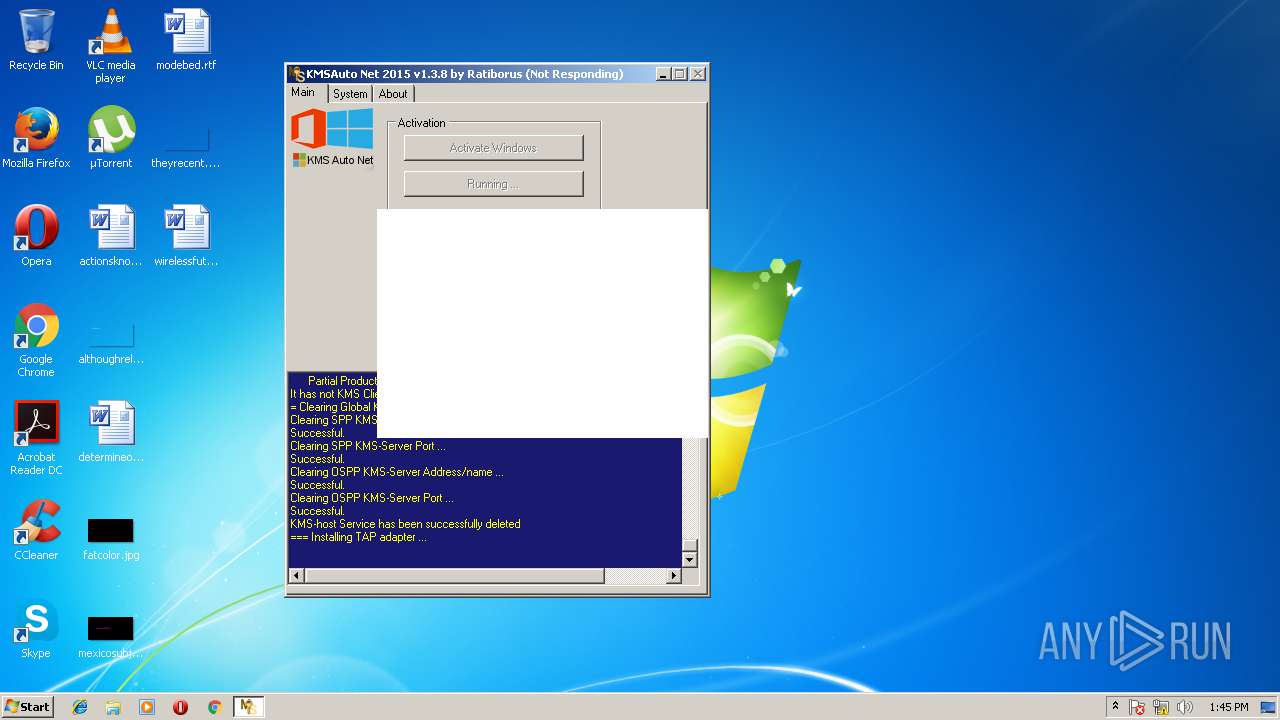
| Verdict: | Malicious activity |
| Analysis date: | March 17, 2018, 13:43:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 6EE7F3ECD5111CD5306792FD3141515D |
| SHA1: | 45C92D0E691175A39A8C61228F526F80A7CA94FC |
| SHA256: | 69A8AE6352CFFD366409DF8E566E84315B4BFFCF5865A4B8079C446123BA1D26 |
| SSDEEP: | 196608:0eywBGqyw1lT3ywuywQyw1ywlywaywTyw9lywfywEyw1ywHywwywmIBywyywsywv:IwBGnw1l+wjwNw4wIw3w2w9IwqwJw4w4 |
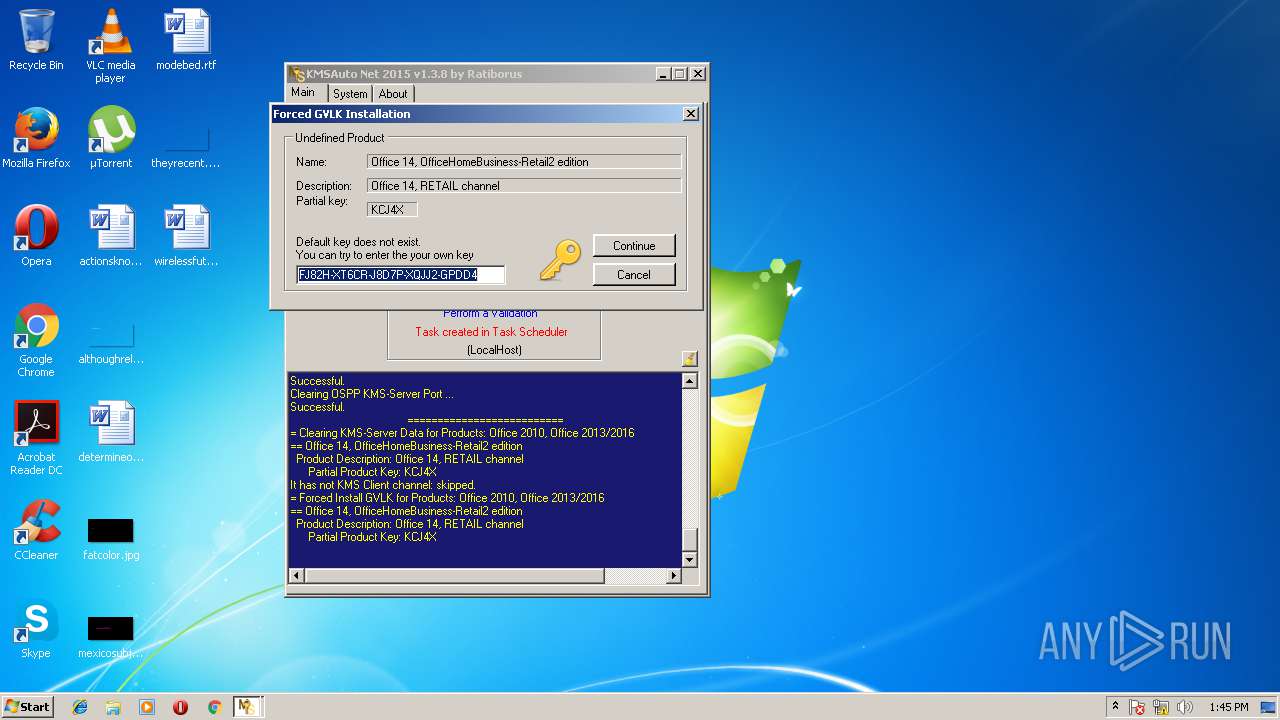
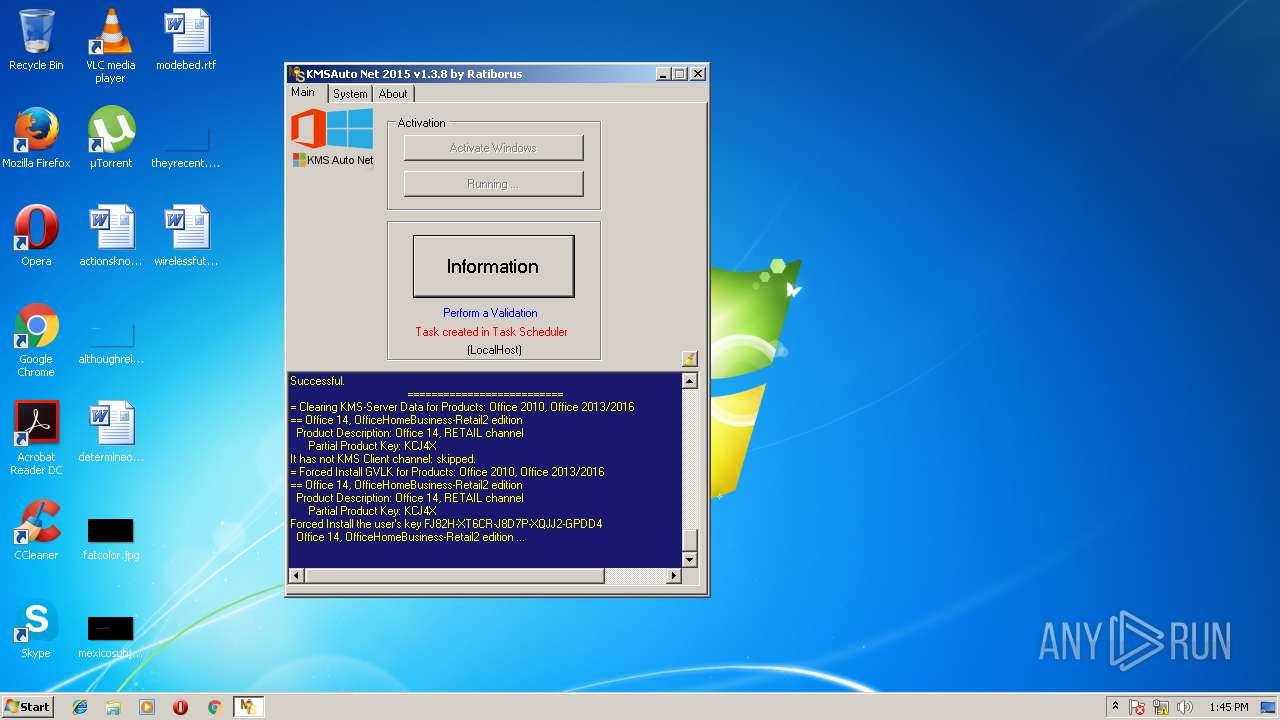
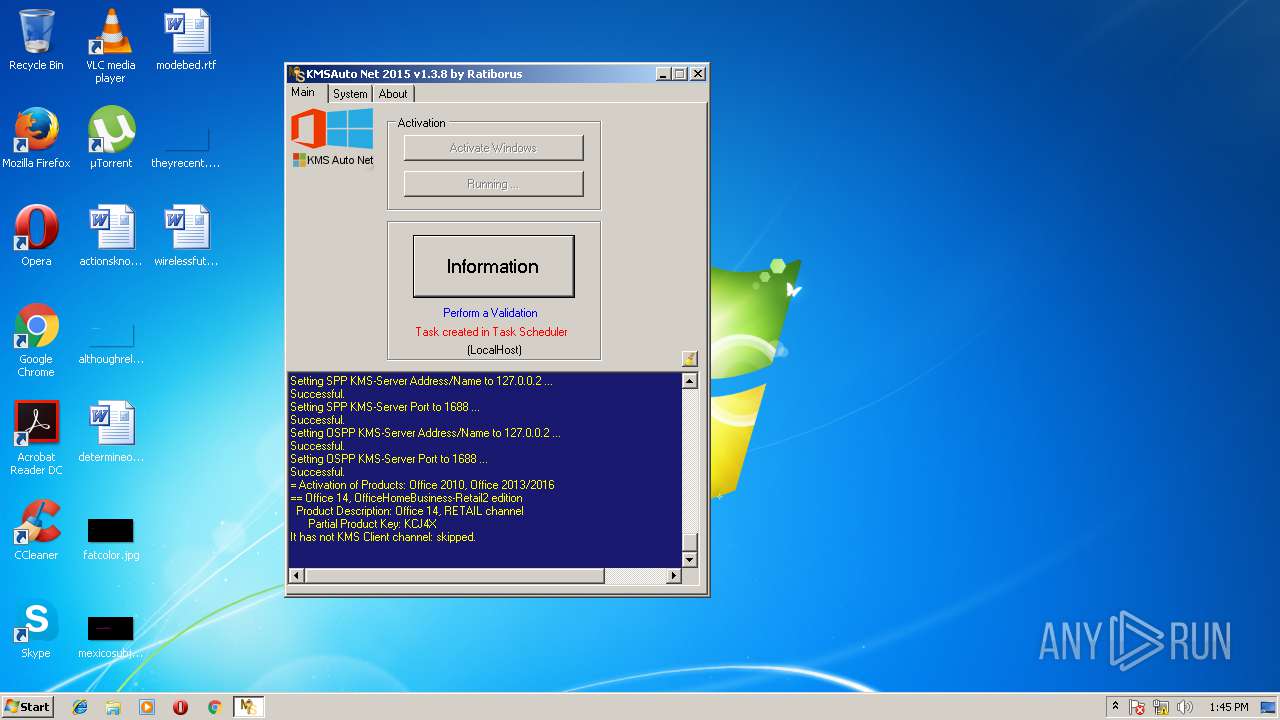
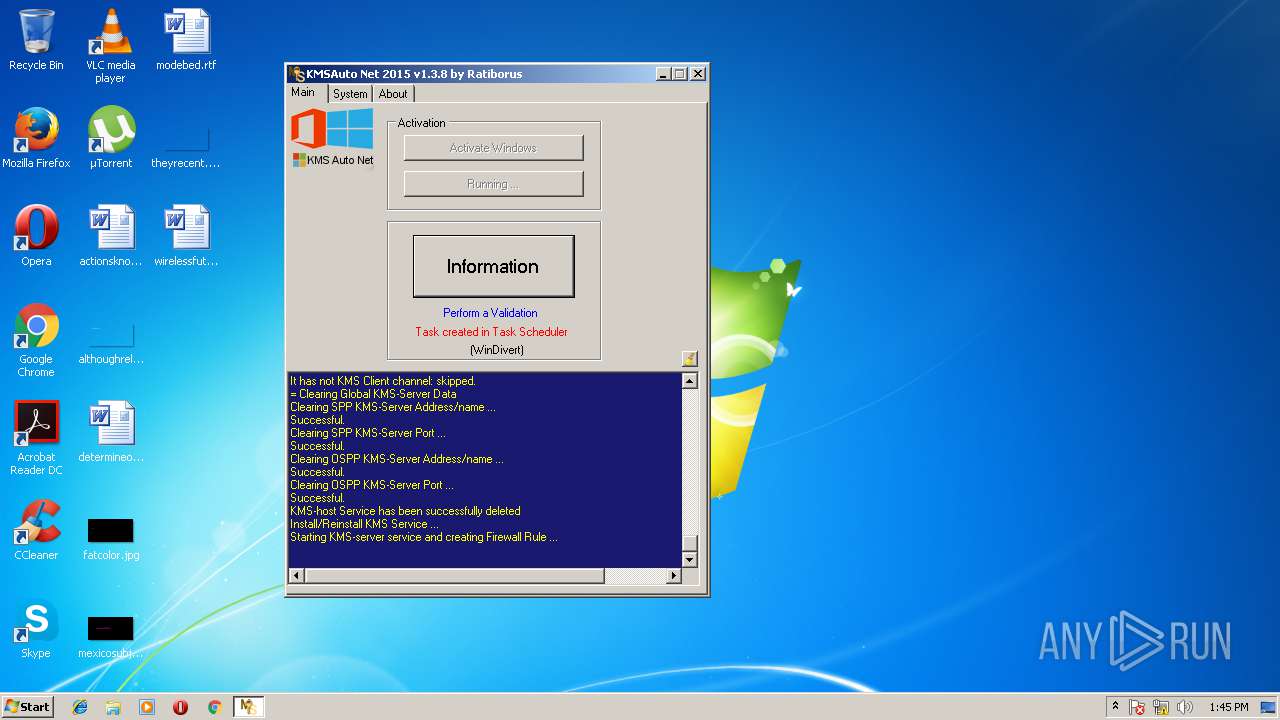
MALICIOUS
Application was dropped or rewritten from another process
- bin.dat (PID: 2244)
- bin_x86.dat (PID: 1008)
- KMSSS.exe (PID: 2816)
- bin.dat (PID: 3872)
- bin_x86.dat (PID: 2180)
- bin.dat (PID: 2944)
- bin_x86.dat (PID: 3160)
- KMSSS.exe (PID: 3872)
- bin.dat (PID: 2976)
- bin_x86.dat (PID: 3544)
- KMSSS.exe (PID: 2248)
- FakeClient.exe (PID: 3760)
- bin.dat (PID: 2184)
- bin_x86.dat (PID: 3668)
- devcon.exe (PID: 4068)
- TunMirror.exe (PID: 3792)
- TunMirror.exe (PID: 2184)
- KMSSS.exe (PID: 1388)
- TunMirror.exe (PID: 1772)
- devcon.exe (PID: 2740)
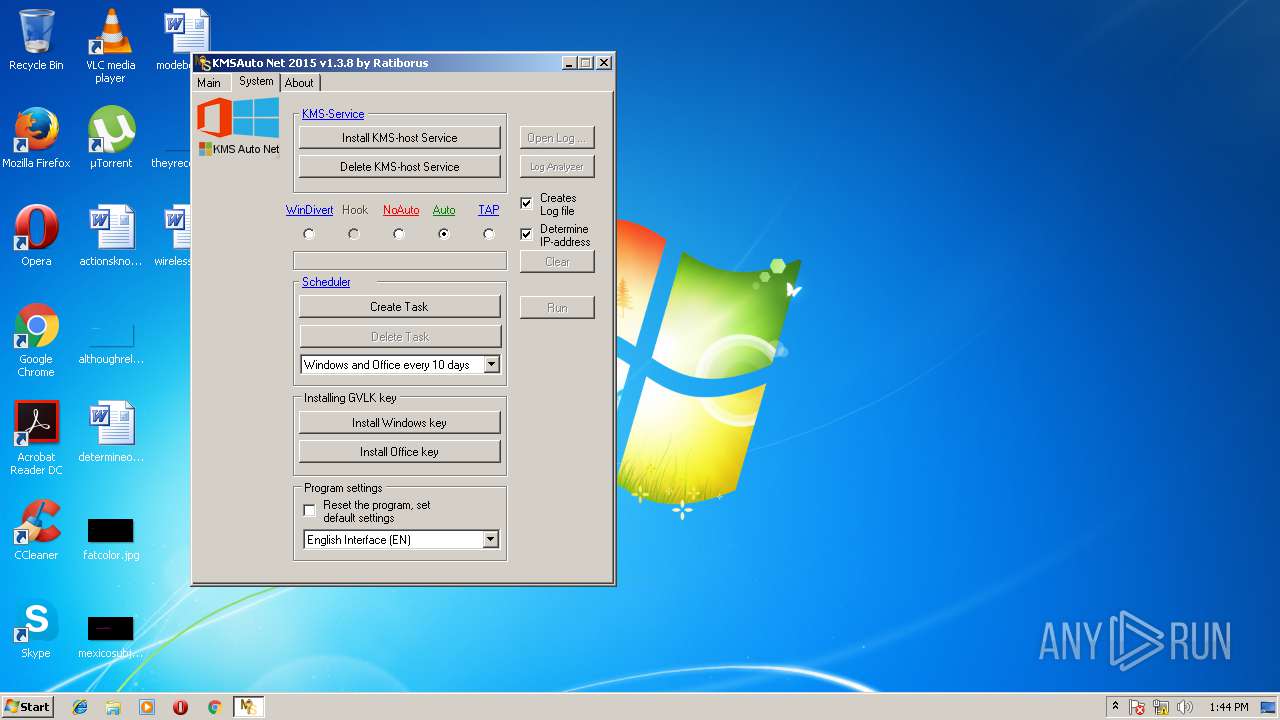
Uses NETSH.EXE for network configuration
- KMSAuto Net.exe (PID: 2784)
- cmd.exe (PID: 3788)
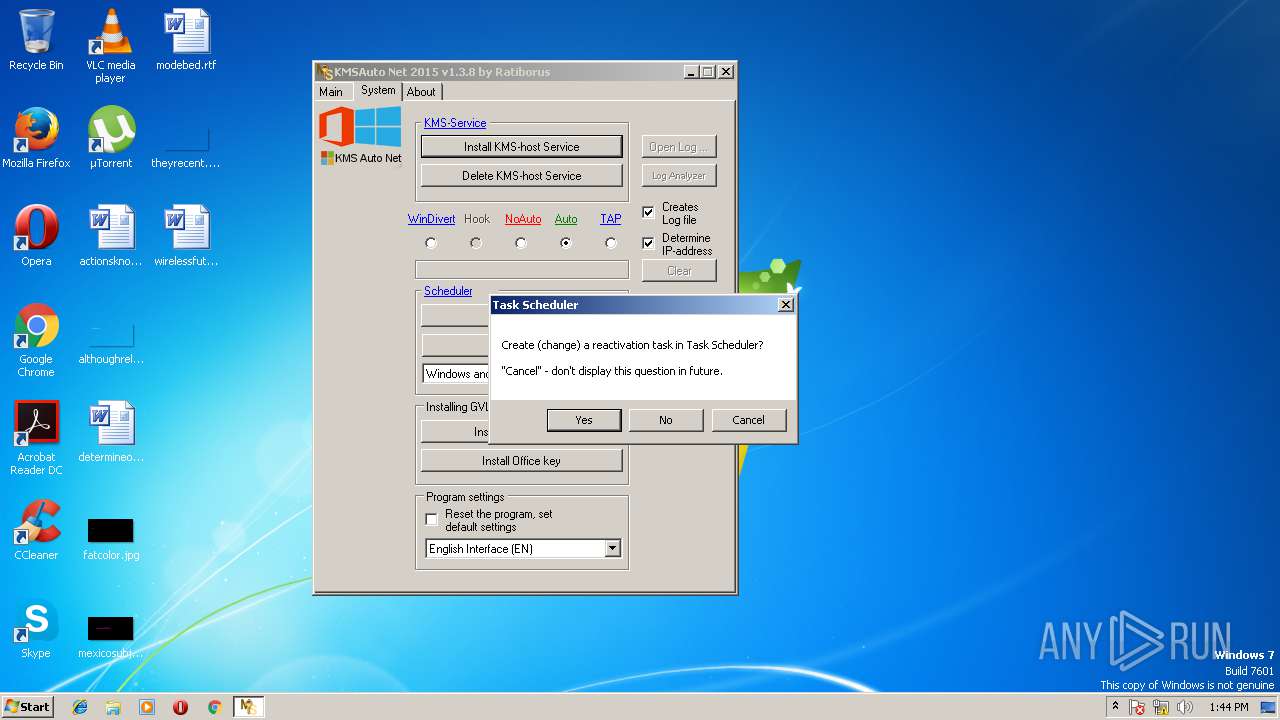
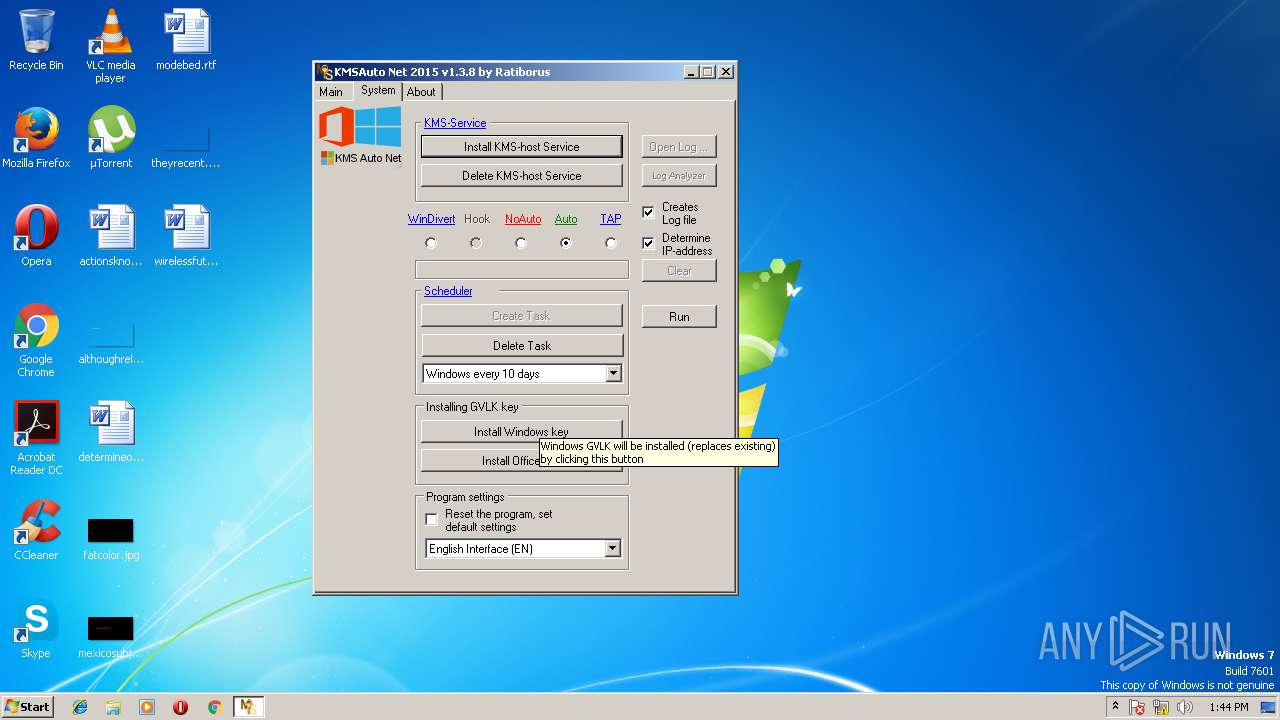
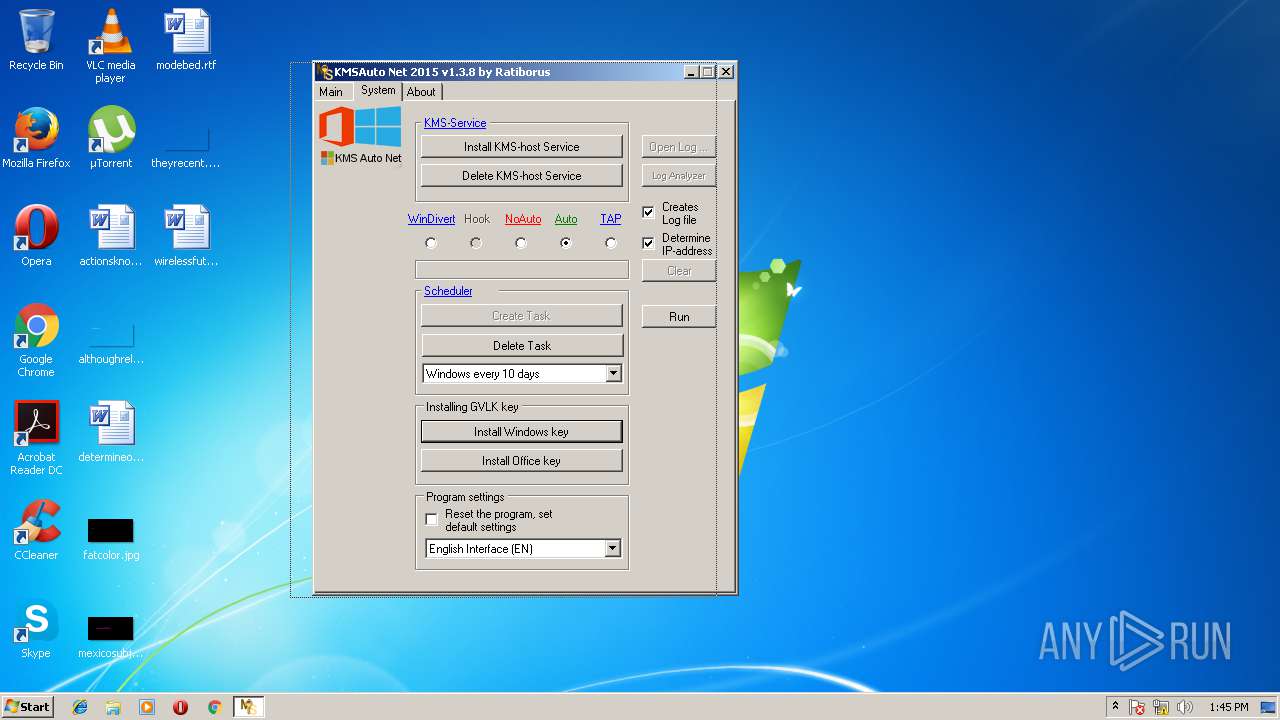
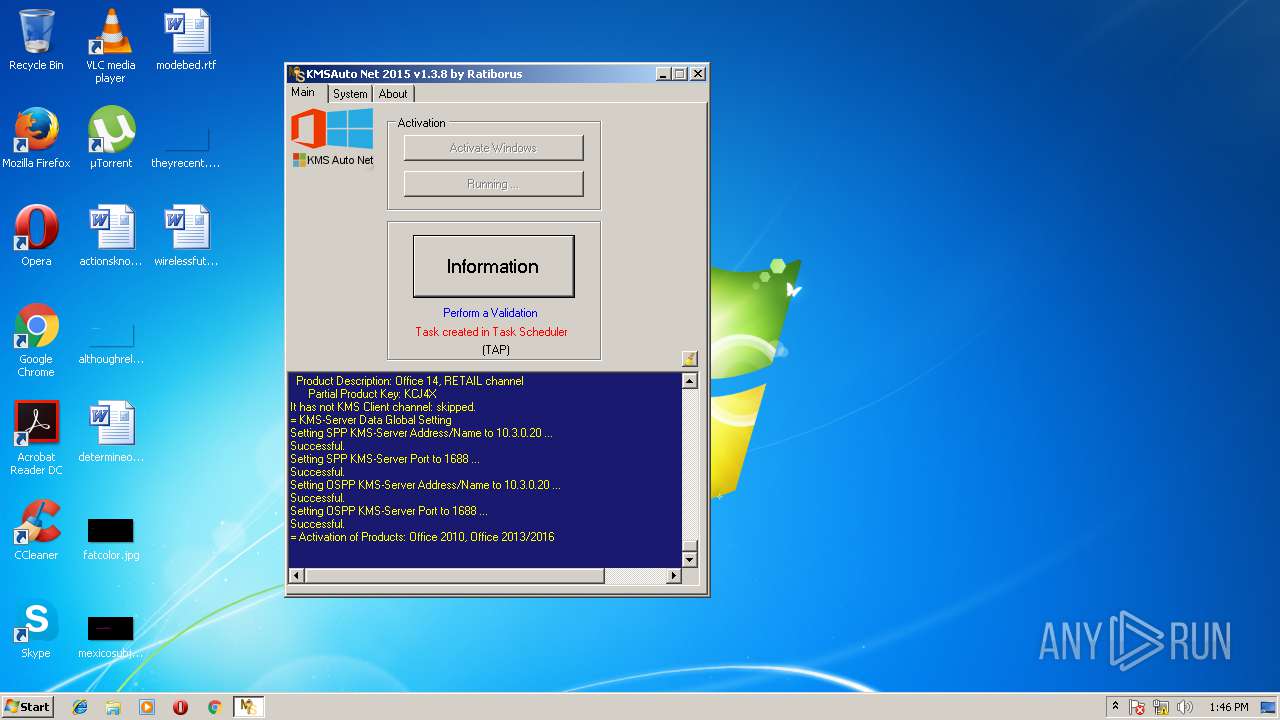
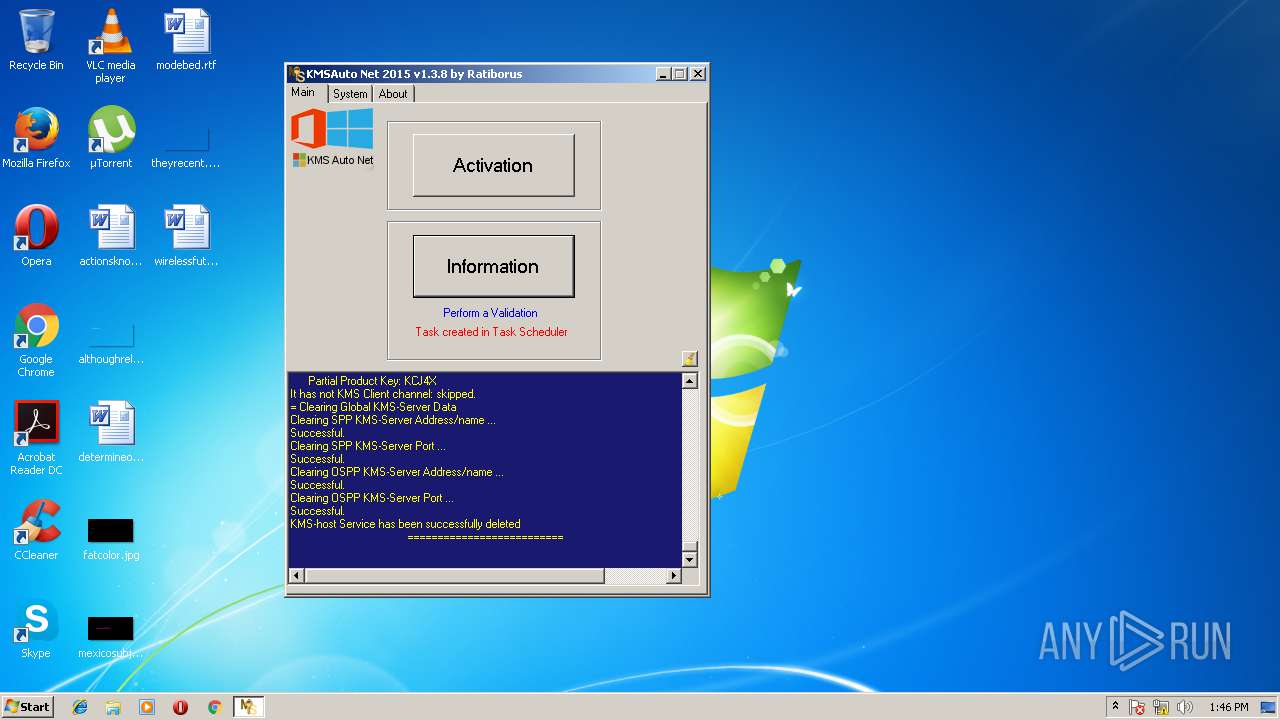
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3292)
- cmd.exe (PID: 2708)
- cmd.exe (PID: 2276)
- cmd.exe (PID: 2212)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2312)
- schtasks.exe (PID: 2136)
- schtasks.exe (PID: 3648)
- schtasks.exe (PID: 3284)
Application loaded dropped or rewritten executable
- FakeClient.exe (PID: 3760)
Changes settings of System certificates
- certutil.exe (PID: 3592)
- devcon.exe (PID: 4068)
SUSPICIOUS
Reads internet explorer settings
- KMSAuto Net.exe (PID: 2784)
Starts CMD.EXE for commands execution
- KMSAuto Net.exe (PID: 2784)
- cmd.exe (PID: 3564)
- cmd.exe (PID: 2860)
- cmd.exe (PID: 3628)
- cmd.exe (PID: 3000)
- cmd.exe (PID: 2516)
Starts application with an unusual extension
- cmd.exe (PID: 3736)
- cmd.exe (PID: 3604)
- cmd.exe (PID: 2100)
- cmd.exe (PID: 3528)
- cmd.exe (PID: 3528)
- cmd.exe (PID: 2772)
- cmd.exe (PID: 2844)
- cmd.exe (PID: 3992)
- cmd.exe (PID: 2916)
- cmd.exe (PID: 2820)
Creates files in the program directory
- bin.dat (PID: 2244)
- KMSAuto Net.exe (PID: 2784)
- bin_x86.dat (PID: 1008)
- KMSSS.exe (PID: 2816)
- bin.dat (PID: 3872)
- bin_x86.dat (PID: 2180)
- KMSSS.exe (PID: 3872)
- bin_x86.dat (PID: 3160)
- bin_x86.dat (PID: 3544)
- bin.dat (PID: 2976)
- KMSSS.exe (PID: 2248)
- bin.dat (PID: 2944)
- bin.dat (PID: 2184)
- bin_x86.dat (PID: 3668)
- TunMirror.exe (PID: 3792)
- KMSSS.exe (PID: 1388)
- TunMirror.exe (PID: 1772)
Executes Visual Basic scripts
- KMSAuto Net.exe (PID: 2784)
Starts SC.EXE for service management
- KMSAuto Net.exe (PID: 2784)
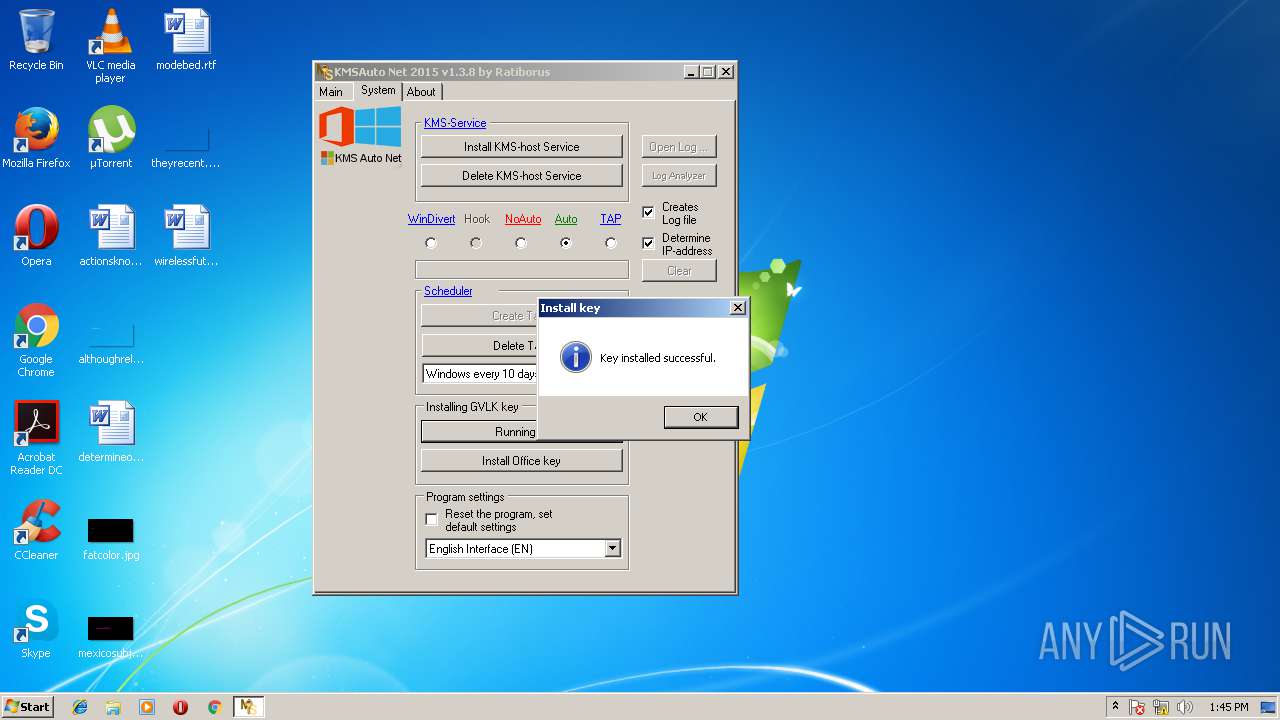
Creates or modifies windows services
- KMSAuto Net.exe (PID: 2784)
- DrvInst.exe (PID: 2344)
- TunMirror.exe (PID: 3792)
- DrvInst.exe (PID: 3724)
- TunMirror.exe (PID: 2184)
- vssvc.exe (PID: 3188)
- devcon.exe (PID: 2740)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3968)
- KMSAuto Net.exe (PID: 2784)
- cmd.exe (PID: 3836)
- cmd.exe (PID: 560)
- cmd.exe (PID: 3668)
Modifies files in the system directory
- FakeClient.exe (PID: 3760)
- devcon.exe (PID: 4068)
- DrvInst.exe (PID: 2344)
- vssvc.exe (PID: 3188)
- DrvInst.exe (PID: 3724)
- TunMirror.exe (PID: 3792)
- TunMirror.exe (PID: 2184)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2768)
Creates files in the Windows directory
- devcon.exe (PID: 4068)
- certutil.exe (PID: 3592)
- DrvInst.exe (PID: 2344)
- DrvInst.exe (PID: 3724)
Removes files from Windows directory
- certutil.exe (PID: 3592)
- DrvInst.exe (PID: 2344)
- DrvInst.exe (PID: 3724)
Adds / modifies Windows certificates
- devcon.exe (PID: 4068)
Creates files in the driver directory
- DrvInst.exe (PID: 2344)
- DrvInst.exe (PID: 3724)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3188)
INFO
Loads the .NET runtime environment
- KMSAuto Net.exe (PID: 2784)
- TunMirror.exe (PID: 3792)
- TunMirror.exe (PID: 2184)
- TunMirror.exe (PID: 1772)
Dropped object may contain URL's
- bin_x86.dat (PID: 1008)
- bin_x86.dat (PID: 2180)
- KMSAuto Net.exe (PID: 2784)
- bin_x86.dat (PID: 3160)
- bin_x86.dat (PID: 3544)
- bin_x86.dat (PID: 3668)
- DrvInst.exe (PID: 2344)
- devcon.exe (PID: 4068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .ocx | | | Windows ActiveX control (67.6) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (16) |
| .scr | | | Windows screen saver (7.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.8) |
| .exe | | | Win32 Executable (generic) (2.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:08:10 09:45:14+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 6923776 |
| InitializedDataSize: | 49152 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x69c4c2 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.3.8.0 |
| ProductVersionNumber: | 1.3.8.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | MSFree Inc. |
| FileDescription: | KMSAuto Net |
| FileVersion: | 1.3.8 |
| InternalName: | KMSAuto Net.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | KMSAuto Net.exe |
| ProductName: | KMSAuto Net |
| ProductVersion: | 1.3.8 |
| AssemblyVersion: | 1.3.8.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Aug-2015 07:45:14 |
| Comments: | - |
| CompanyName: | MSFree Inc. |
| FileDescription: | KMSAuto Net |
| FileVersion: | 1.3.8 |
| InternalName: | KMSAuto Net.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | KMSAuto Net.exe |
| ProductName: | KMSAuto Net |
| ProductVersion: | 1.3.8 |
| Assembly Version: | 1.3.8.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 10-Aug-2015 07:45:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0069A4C8 | 0x0069A600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.09188 |
.rsrc | 0x0069E000 | 0x0000BC3C | 0x0000BE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.62475 |
.reloc | 0x006AA000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.41186 | 3073 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 5.29604 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.35071 | 1736 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.03007 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 3.79019 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 4.1678 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 4.32586 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 4.672 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 5.05539 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.96193 | 132 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
402
Monitored processes
211
Malicious processes
13
Suspicious processes
14
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 560 | WMIC Path Win32_NetworkAdapter WHERE ServiceName="ptun0901" get InterfaceIndex | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 560 | C:\Windows\System32\cmd.exe /c reg.exe DELETE HKLM\SYSTEM\CurrentControlSet\Services\KMSEmulator /f | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 864 | C:\Windows\system32\cmd.exe /c netstat -ano | find ":1688 " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 864 | C:\Windows\System32\reg delete "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\55C92734-D682-4D71-983E-D6EC3F16059F" /f | C:\Windows\System32\reg.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 868 | net start TunMirror | C:\Windows\system32\net.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 940 | "sc.exe" stop KMSEmulator | C:\Windows\system32\sc.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 988 | reg.exe DELETE HKLM\SYSTEM\CurrentControlSet\Services\KMSEmulator /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 996 | WMIC Path Win32_NetworkAdapter WHERE ServiceName="tapoas" get Manufacturer | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1008 | bin_x86.dat -y -pkmsauto | C:\ProgramData\KMSAuto\bin_x86.dat | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1008 | net start dot3svc | C:\Windows\system32\net.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 704
Read events
1 147
Write events
1 438
Delete events
119
Modification events
| (PID) Process: | (2372) NETSTAT.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\RFC1156Agent\CurrentVersion\Parameters |
| Operation: | write | Name: | TrapPollTimeMilliSecs |
Value: 15000 | |||
| (PID) Process: | (2620) Netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2620) Netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (2620) Netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (2620) Netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (2620) Netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
| (PID) Process: | (2620) Netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-1 |
Value: IPsec Relying Party | |||
| (PID) Process: | (2620) Netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-2 |
Value: Provides IPsec based enforcement for Network Access Protection | |||
| (PID) Process: | (2620) Netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-4 |
Value: 1.0 | |||
| (PID) Process: | (2620) Netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-3 |
Value: Microsoft Corporation | |||
Executable files
65
Suspicious files
27
Text files
243
Unknown types
34
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3168 | cmd.exe | C:\Users\admin\AppData\Local\Temp\test.test | — | |
MD5:— | SHA256:— | |||
| 2784 | KMSAuto Net.exe | C:\ProgramData\KMSAuto\bin.dat | — | |
MD5:— | SHA256:— | |||
| 2244 | bin.dat | C:\ProgramData\KMSAuto\bin\TunMirror.exe | executable | |
MD5:362498C3E71EEAA066A67E4A3F981D1C | SHA256:D87E8D9D43758CE67A8052CB2334B99CC24F9B0437EE44815F360BE0B22D835A | |||
| 2244 | bin.dat | C:\ProgramData\KMSAuto\bin\KMSSS.exe | executable | |
MD5:0F03F72A92AEF6D63EB74E73F8AC201D | SHA256:ACD55C44B8B0D66D66DEFED85CA18082C092F048D3621DA827FCE593305C11FD | |||
| 2784 | KMSAuto Net.exe | C:\ProgramData\KMSAuto\bin_x86.dat | executable | |
MD5:EE610244248F502AA9755A7EA85C341C | SHA256:205987B7CCC639AE1F7185C6F4326FE926FF74272915B2FDA7CE8D43A4E2A803 | |||
| 1008 | bin_x86.dat | C:\ProgramData\KMSAuto\bin\driver\x86TAP2\tapoas.cat | cat | |
MD5:F06DEB48D9149B3227C09FE4B9C3615E | SHA256:EC8A15EBD17E56F60851C557119E81A7F6EAAAB871ABFE9685926DF0C7AA6D4E | |||
| 2784 | KMSAuto Net.exe | C:\ProgramData\KMSAutoS\bin.dat | — | |
MD5:— | SHA256:— | |||
| 1008 | bin_x86.dat | C:\ProgramData\KMSAuto\bin\driver\x86TAP1\OemVista.inf | binary | |
MD5:8578CF3536DF7D6A2ED44C989A51C5DB | SHA256:DC5AE432C7C6586D29AE522DCA9BB91AC692EBD25A9B0E5C7728887AB2B2A668 | |||
| 1008 | bin_x86.dat | C:\ProgramData\KMSAuto\bin\driver\x86TAP2\tapoas.inf | binary | |
MD5:474A35760A3B1971CBFC1118D5B425F8 | SHA256:05F57863E4B1543EA251016104AEA4C8B06A2B1AB5E09AC623B36F85E82E4D5F | |||
| 1008 | bin_x86.dat | C:\ProgramData\KMSAuto\bin\driver\x86WDV\WinDivert.inf | ini | |
MD5:A94D989905A248AFCA52BC3CBFCB248B | SHA256:6C9F7DEA4F9A47788D5D2BA110B08457FD00DBABE4812EBCA6F022300843A75D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
teredo.ipv6.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
FakeClient.exe | WdfCoInstaller: [03/17/2018 13:45.38.625] ReadComponents: WdfSection for Driver Service windivert using KMDF lib version Major 0x1, minor 0x9
|
FakeClient.exe | WdfCoInstaller: [03/17/2018 13:45.38.625] BootApplication: could not open service windivert, error error(1060) The specified service does not exist as an installed service.
|
FakeClient.exe | WdfCoInstaller: [03/17/2018 13:45.38.625] BootApplication: GetStartType error error(87) The parameter is incorrect.
Driver Service name windivert
|