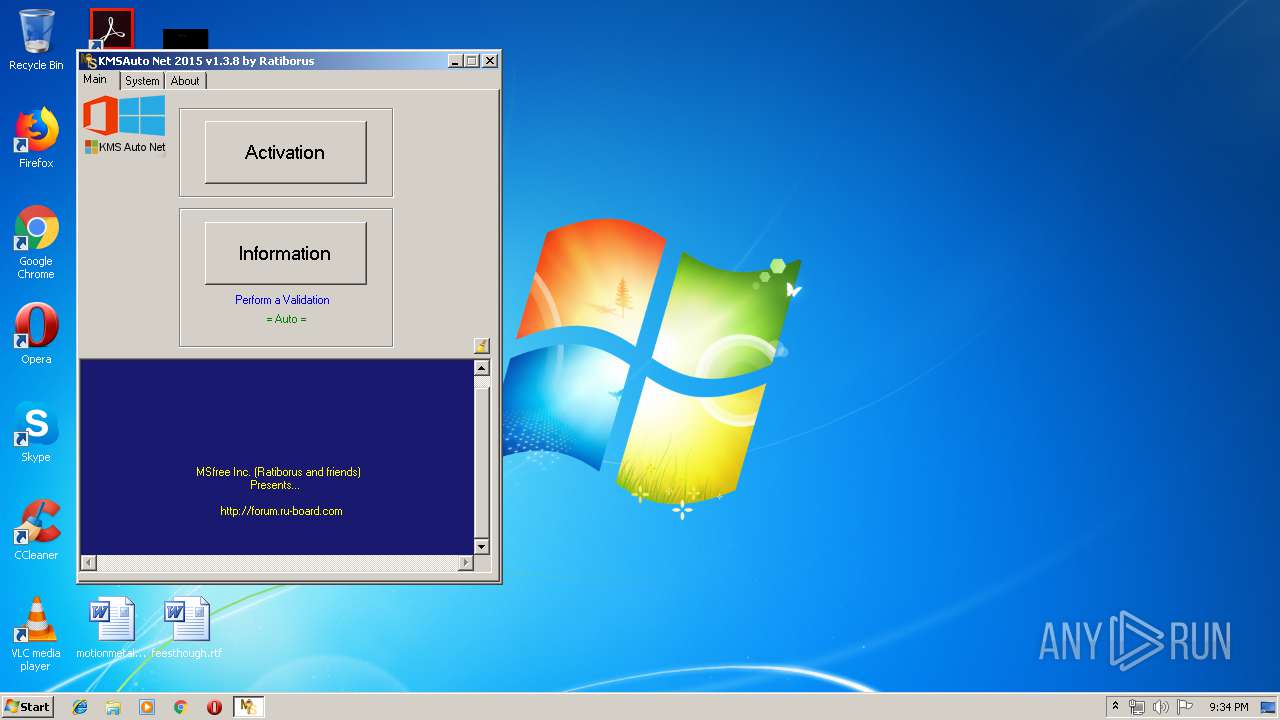
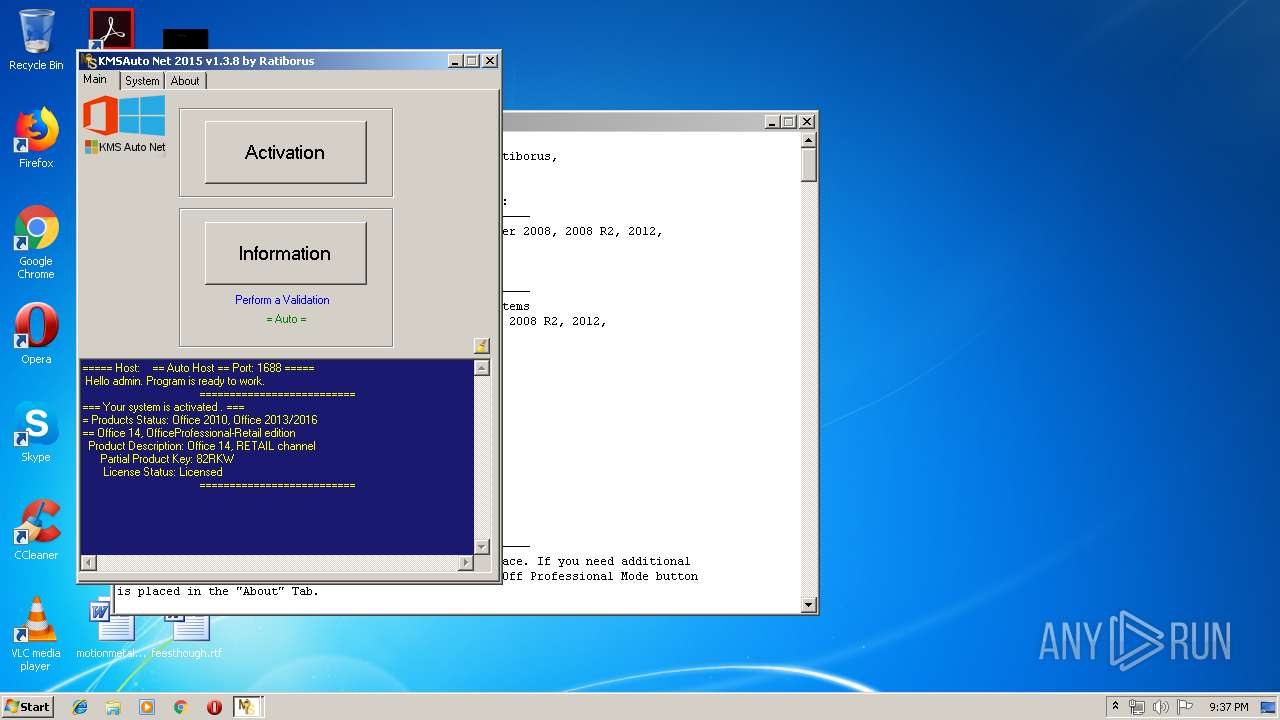
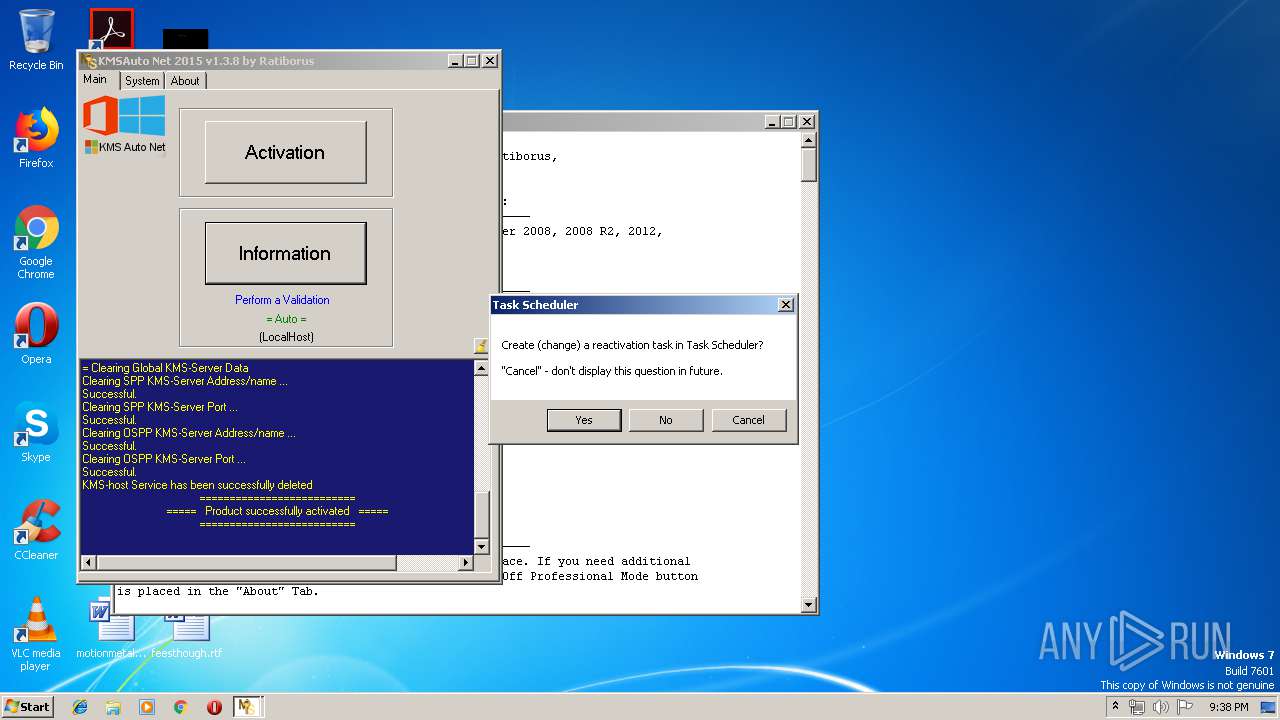
| File name: | KMSAuto Net.exe |
| Full analysis: | https://app.any.run/tasks/3baa4b9c-e2de-4427-9482-8795181e5982 |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2019, 20:33:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 6EE7F3ECD5111CD5306792FD3141515D |
| SHA1: | 45C92D0E691175A39A8C61228F526F80A7CA94FC |
| SHA256: | 69A8AE6352CFFD366409DF8E566E84315B4BFFCF5865A4B8079C446123BA1D26 |
| SSDEEP: | 196608:0eywBGqyw1lT3ywuywQyw1ywlywaywTyw9lywfywEyw1ywHywwywmIBywyywsywv:IwBGnw1l+wjwNw4wIw3w2w9IwqwJw4w4 |
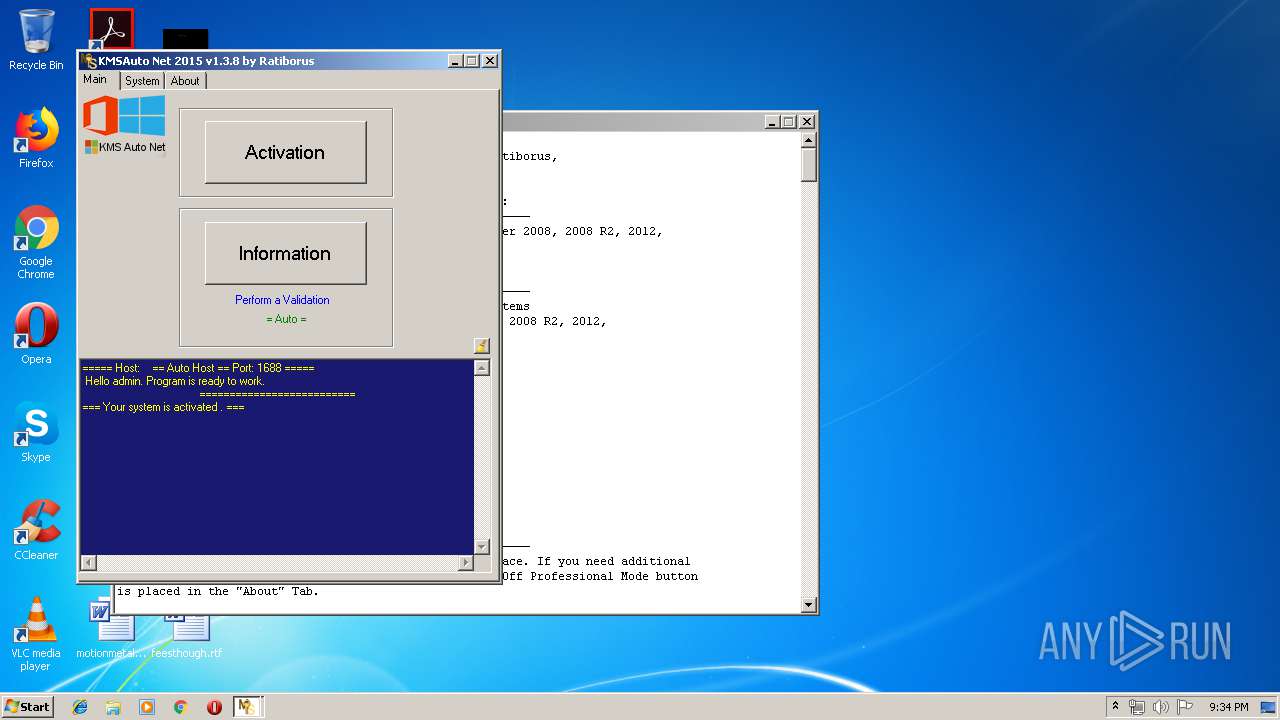
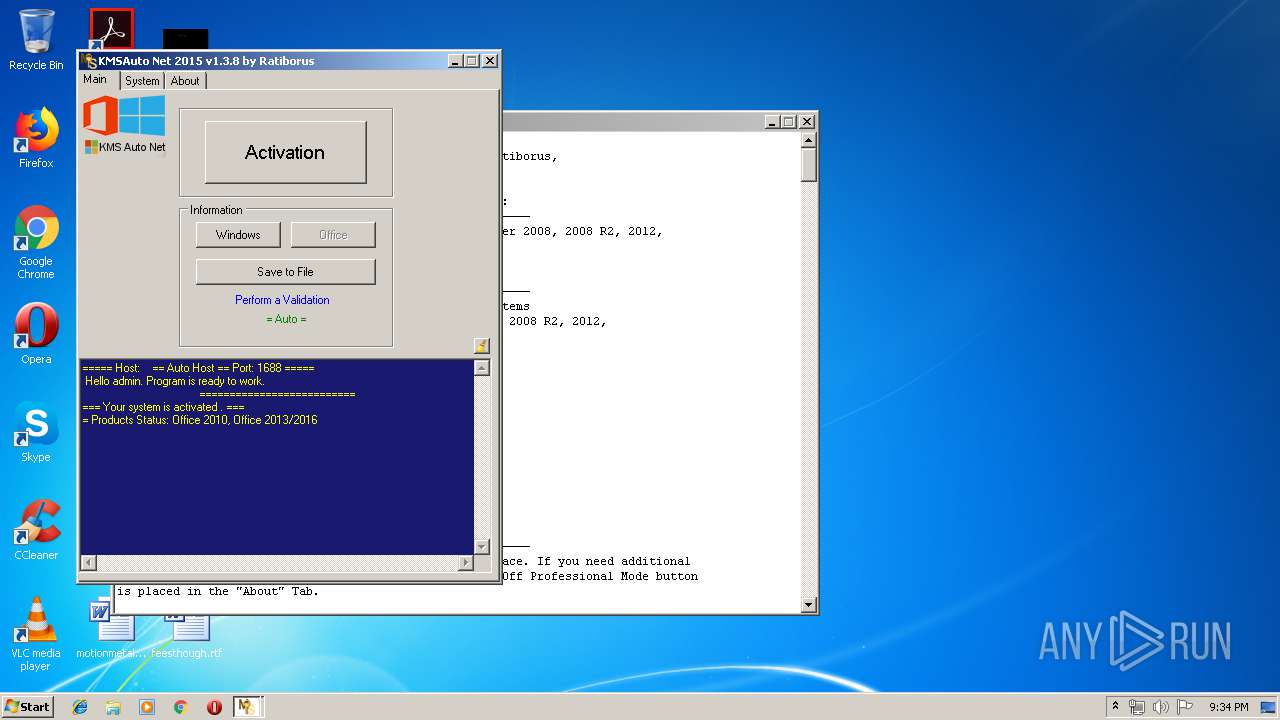
MALICIOUS
Application was dropped or rewritten from another process
- bin.dat (PID: 900)
- bin_x86.dat (PID: 3460)
- KMSSS.exe (PID: 1668)
SUSPICIOUS
Creates files in the program directory
- firefox.exe (PID: 3368)
- KMSAuto Net.exe (PID: 2224)
- bin.dat (PID: 900)
- bin_x86.dat (PID: 3460)
- KMSSS.exe (PID: 1668)
Reads internet explorer settings
- KMSAuto Net.exe (PID: 2224)
Executable content was dropped or overwritten
- KMSAuto Net.exe (PID: 2224)
- bin.dat (PID: 900)
- bin_x86.dat (PID: 3460)
Executes scripts
- KMSAuto Net.exe (PID: 2224)
Starts CMD.EXE for commands execution
- KMSAuto Net.exe (PID: 2224)
- cmd.exe (PID: 3068)
Reads Environment values
- KMSAuto Net.exe (PID: 2224)
Starts application with an unusual extension
- cmd.exe (PID: 1700)
- cmd.exe (PID: 2632)
Uses NETSH.EXE for network configuration
- KMSAuto Net.exe (PID: 2224)
Creates or modifies windows services
- KMSAuto Net.exe (PID: 2224)
Uses NETSTAT.EXE to discover network connections
- cmd.exe (PID: 3608)
Executed as Windows Service
- KMSSS.exe (PID: 1668)
Starts SC.EXE for service management
- KMSAuto Net.exe (PID: 2224)
Uses REG.EXE to modify Windows registry
- KMSAuto Net.exe (PID: 2224)
- cmd.exe (PID: 2400)
INFO
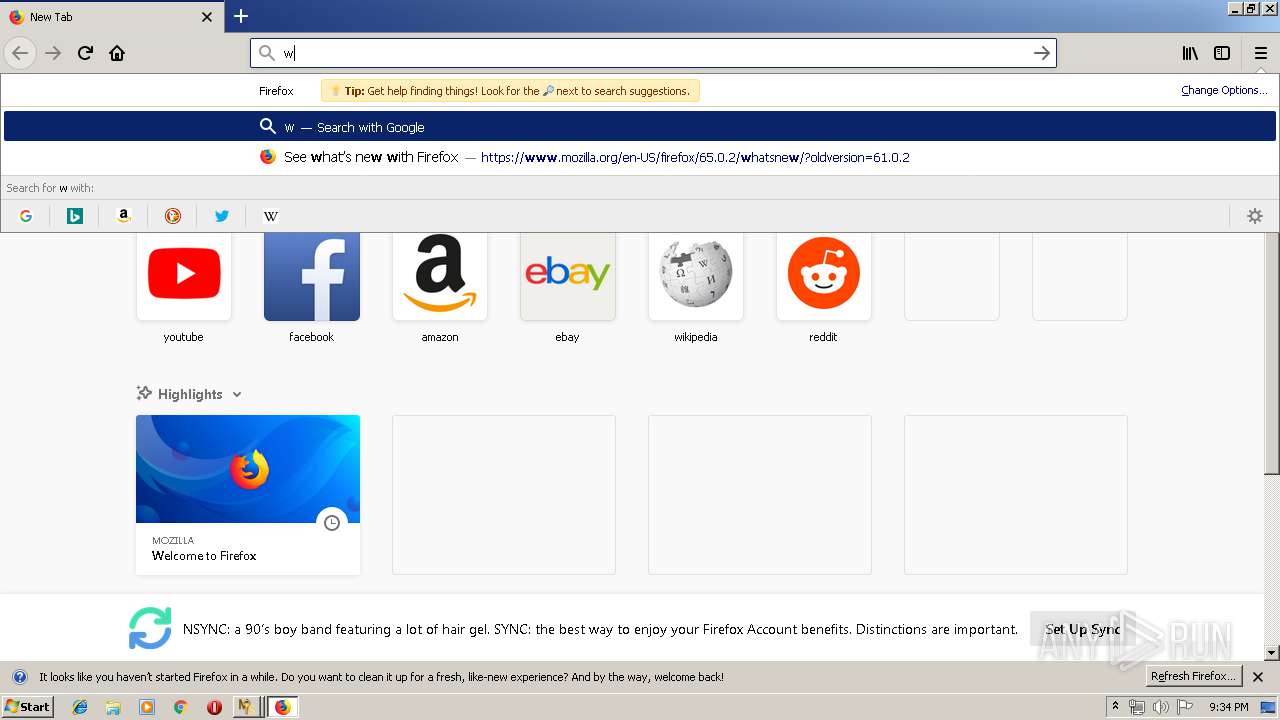
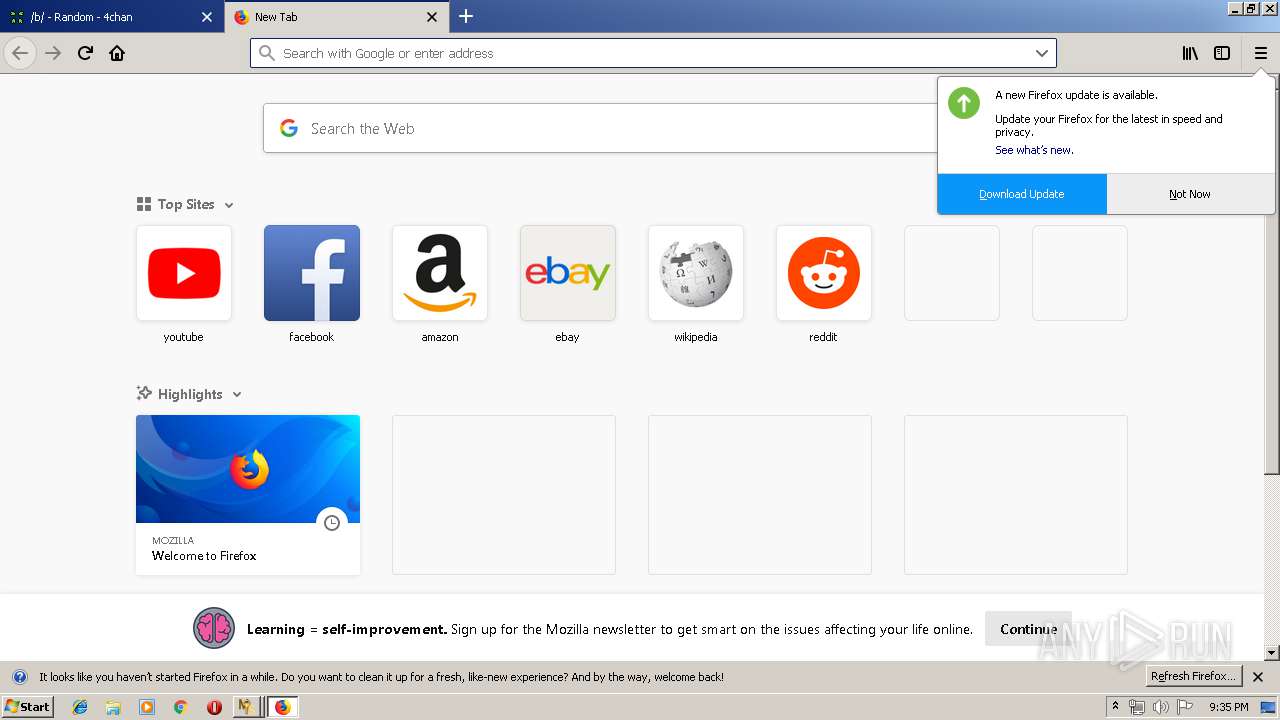
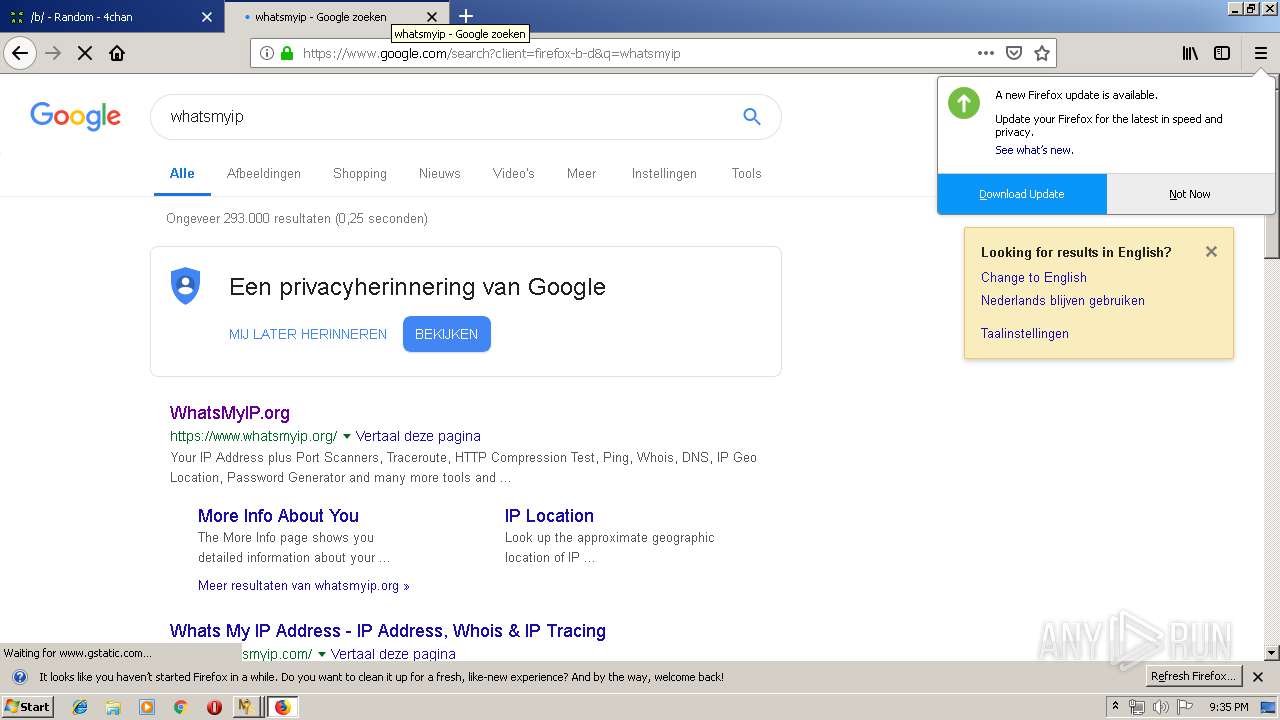
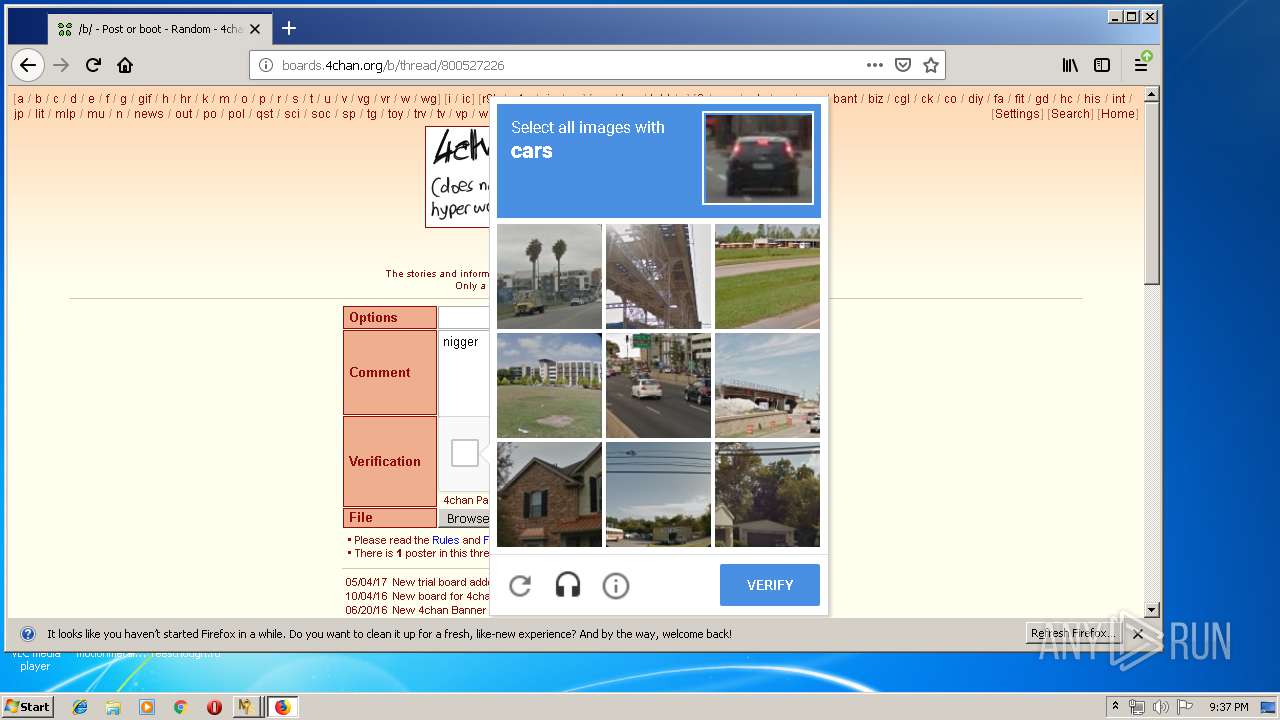
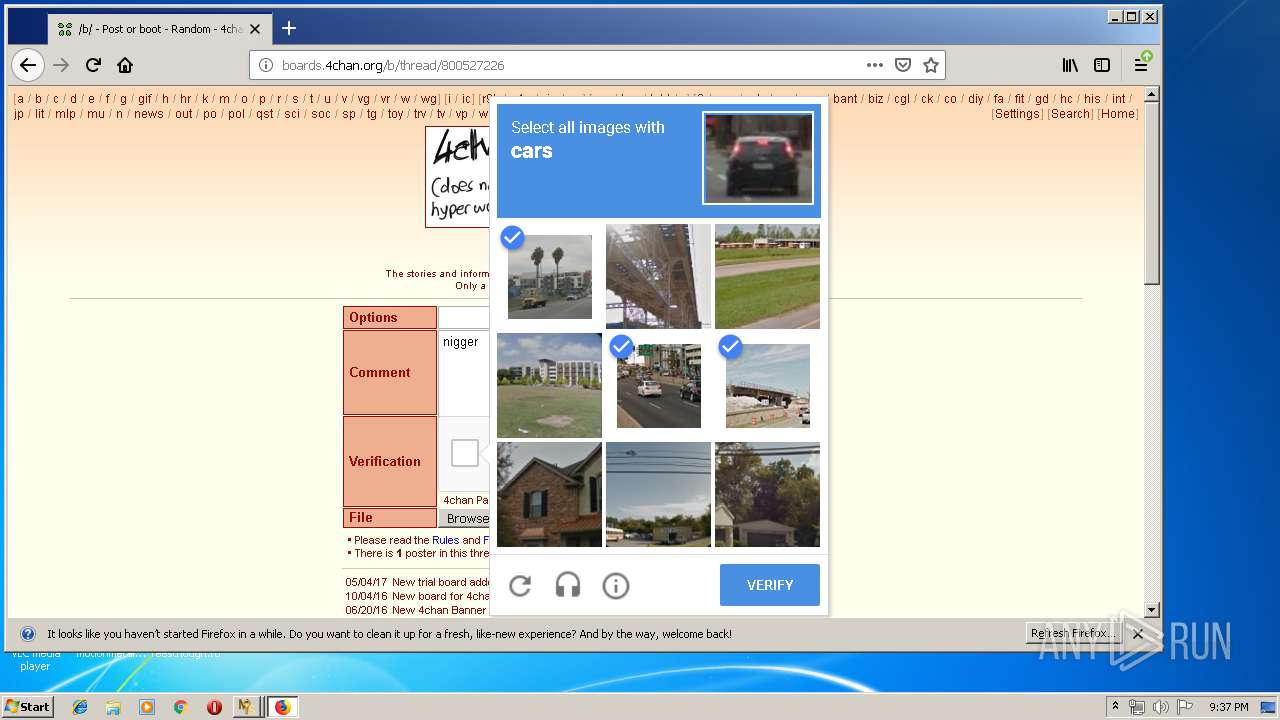
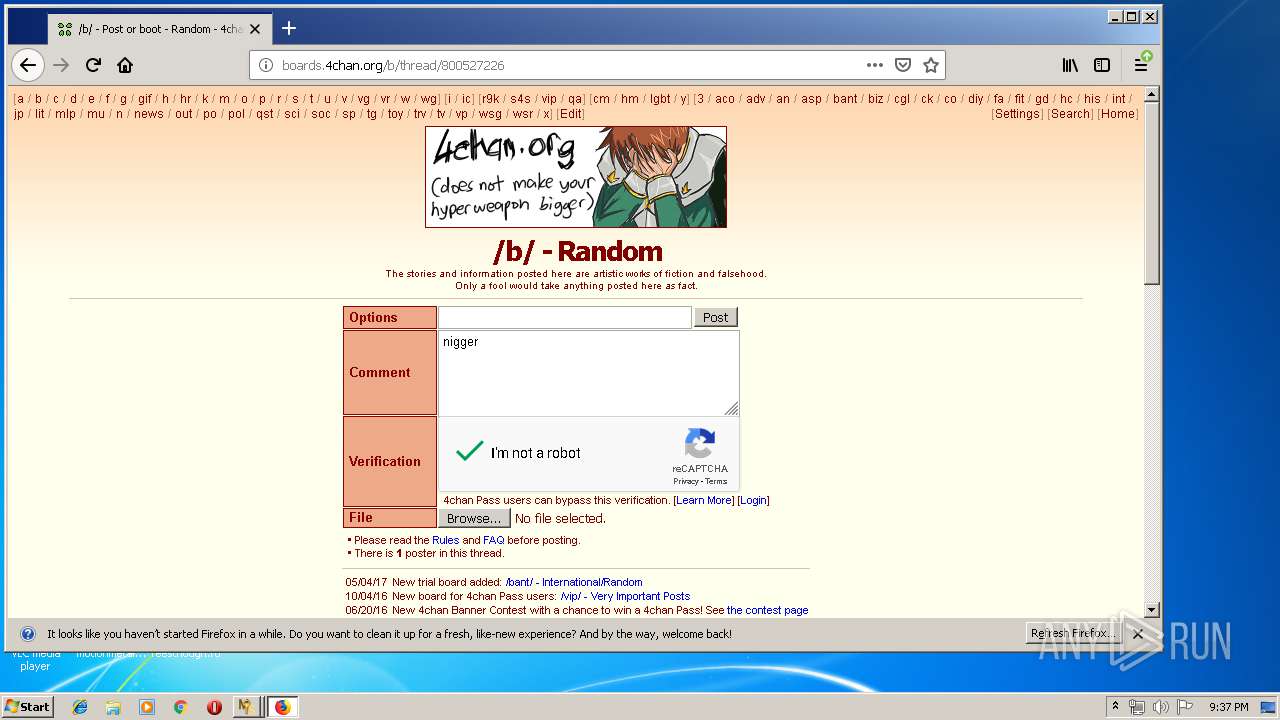
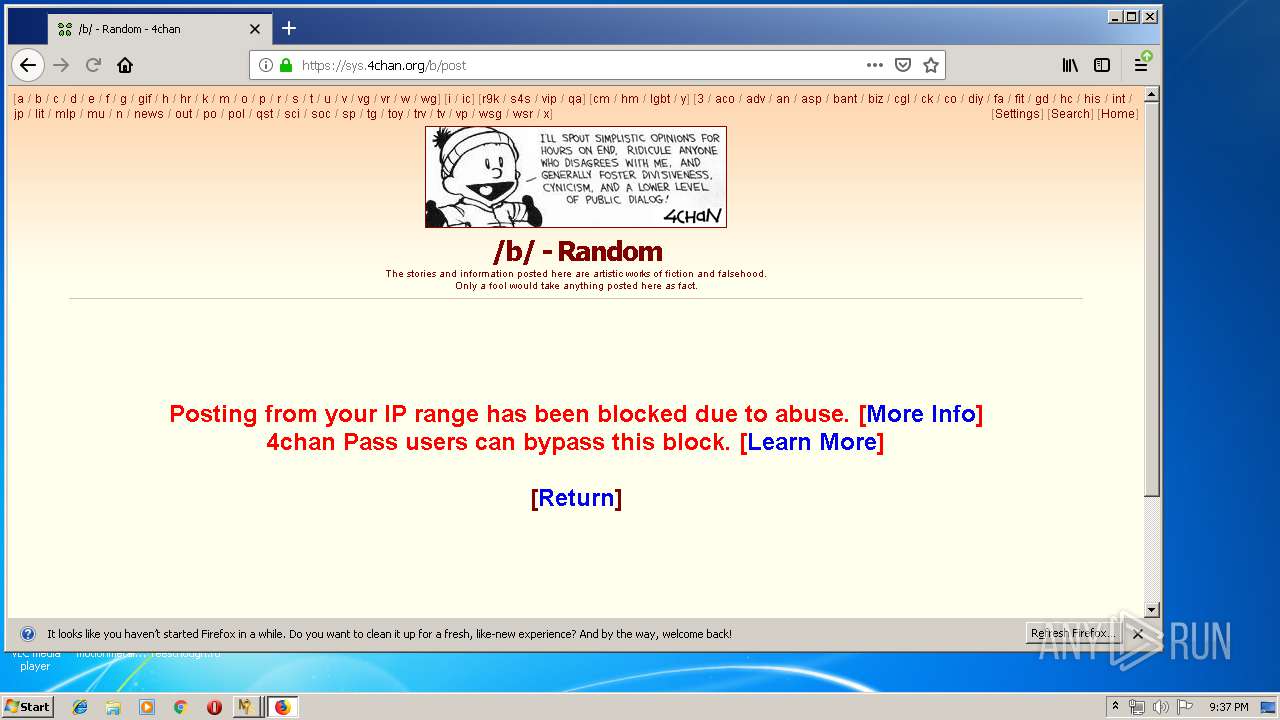
Manual execution by user
- firefox.exe (PID: 3368)
Reads CPU info
- firefox.exe (PID: 3368)
Reads settings of System Certificates
- firefox.exe (PID: 3368)
Application launched itself
- firefox.exe (PID: 3368)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 3368)
Adds / modifies Windows certificates
- pingsender.exe (PID: 3792)
Changes settings of System certificates
- pingsender.exe (PID: 3792)
Creates files in the user directory
- firefox.exe (PID: 3368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (16) |
|---|---|---|
| .scr | | | Windows screen saver (7.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.8) |
| .exe | | | Win32 Executable (generic) (2.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:08:10 09:45:14+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 6923776 |
| InitializedDataSize: | 49152 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x69c4c2 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.3.8.0 |
| ProductVersionNumber: | 1.3.8.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | MSFree Inc. |
| FileDescription: | KMSAuto Net |
| FileVersion: | 1.3.8 |
| InternalName: | KMSAuto Net.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | KMSAuto Net.exe |
| ProductName: | KMSAuto Net |
| ProductVersion: | 1.3.8 |
| AssemblyVersion: | 1.3.8.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Aug-2015 07:45:14 |
| Comments: | - |
| CompanyName: | MSFree Inc. |
| FileDescription: | KMSAuto Net |
| FileVersion: | 1.3.8 |
| InternalName: | KMSAuto Net.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | KMSAuto Net.exe |
| ProductName: | KMSAuto Net |
| ProductVersion: | 1.3.8 |
| Assembly Version: | 1.3.8.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 10-Aug-2015 07:45:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0069A4C8 | 0x0069A600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.09188 |
.rsrc | 0x0069E000 | 0x0000BC3C | 0x0000BE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.62475 |
.reloc | 0x006AA000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.41186 | 3073 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 5.29604 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.35071 | 1736 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.03007 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 3.79019 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 4.1678 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 4.32586 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 4.672 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 5.05539 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.96193 | 132 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
108
Monitored processes
42
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Windows\System32\cmd.exe" /c rd "C:\ProgramData\KMSAuto" /S /Q | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 584 | C:\Windows\System32\reg delete "HKEY_USERS\S-1-5-20\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\0ff1ce15-a989-479d-af46-f275c6370663" /f | C:\Windows\System32\reg.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
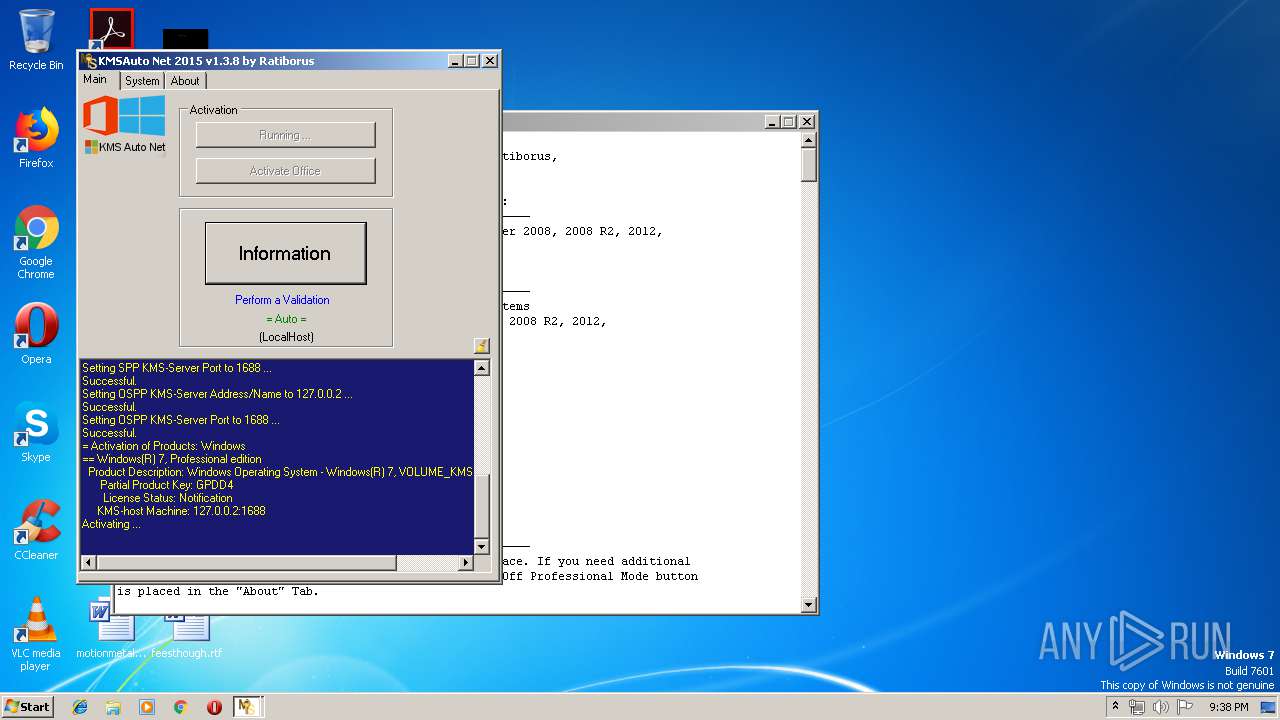
| 752 | "cscript.exe" /nologo C:\Windows\system32\slmgr.vbs /ipk FJ82H-XT6CR-J8D7P-XQJJ2-GPDD4 | C:\Windows\system32\cscript.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 900 | bin.dat -y -pkmsauto | C:\ProgramData\KMSAuto\bin.dat | cmd.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7z Console SFX Exit code: 0 Version: 9.20 Modules
| |||||||||||||||
| 920 | "sc.exe" delete KMSEmulator | C:\Windows\system32\sc.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1352 | C:\Windows\System32\reg delete "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\OfficeSoftwareProtectionPlatform\0FF1CE15-A989-479D-AF46-F275C6370663" /f | C:\Windows\System32\reg.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1356 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3368.20.1298142939\665728700" -childID 3 -isForBrowser -prefsHandle 3396 -prefMapHandle 3408 -prefsLen 5824 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3368 "\\.\pipe\gecko-crash-server-pipe.3368" 3420 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 1524 | cmd /c echo test>>"C:\Users\admin\AppData\Local\Temp\test.test" | C:\Windows\system32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1568 | C:\Windows\System32\Netsh Advfirewall Firewall add rule name="0pen Port KMS" dir=in action=allow protocol=TCP localport=1688 | C:\Windows\System32\Netsh.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
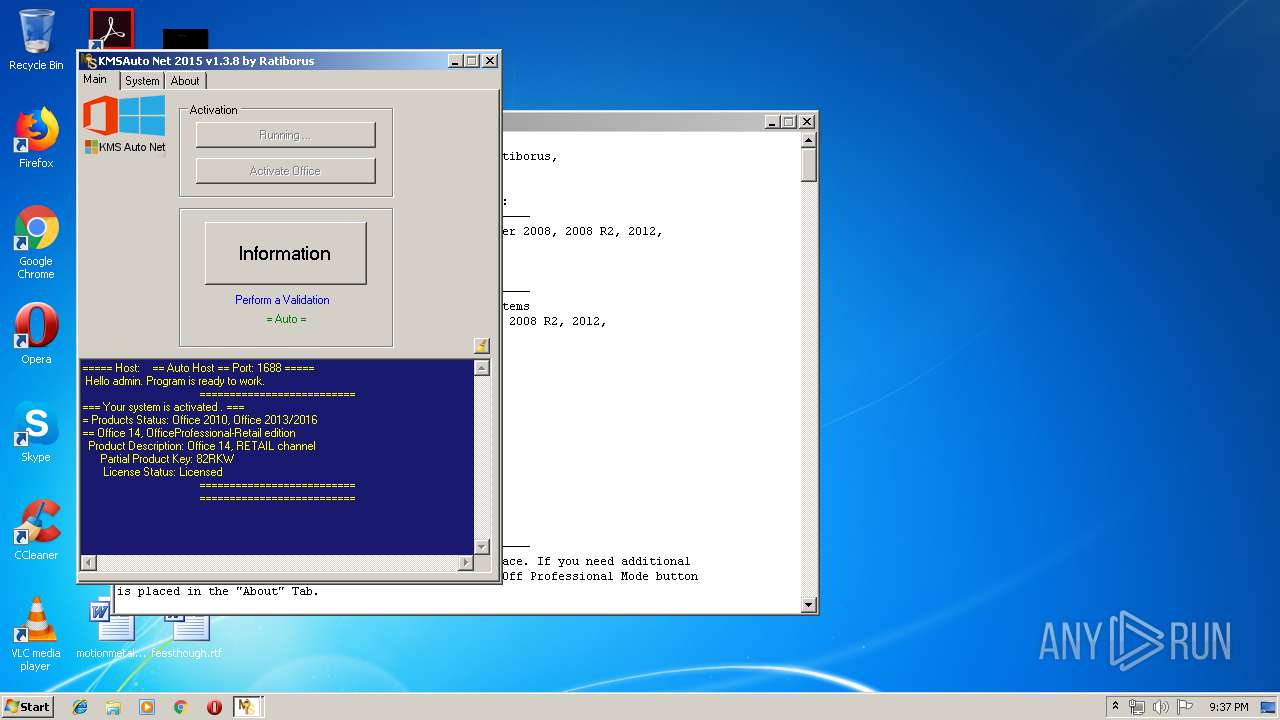
| 1668 | "C:\ProgramData\KMSAuto\bin\KMSSS.exe" -Port 1688 -PWin RandomKMSPID -PO14 RandomKMSPID -PO15 RandomKMSPID -AI 43200 -RI 43200 KillProcessOnPort -Log -IP | C:\ProgramData\KMSAuto\bin\KMSSS.exe | — | services.exe | |||||||||||
User: SYSTEM Company: MDL Forum, mod by Ratiborus Integrity Level: SYSTEM Description: KMS Server Emulator Service (XP) Exit code: 0 Version: 1.2.1.0 Modules
| |||||||||||||||
Total events
1 184
Read events
1 000
Write events
178
Delete events
6
Modification events
| (PID) Process: | (3368) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3368) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3368) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3792) pingsender.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3792) pingsender.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000072000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3792) pingsender.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3792) pingsender.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\91C6D6EE3E8AC86384E548C299295C756C817B81 |
| Operation: | write | Name: | Blob |
Value: 0F000000010000001400000085FEF11B4F47FE3952F98301C9F98976FEFEE0CE09000000010000002A000000302806082B0601050507030106082B0601050507030206082B0601050507030406082B0601050507030353000000010000002500000030233021060B6086480186F8450107300130123010060A2B0601040182373C0101030200C01400000001000000140000007B5B45CFAFCECB7AFD31921A6AB6F346EB5748501D00000001000000100000005B3B67000EEB80022E42605B6B3B72400B000000010000000E000000740068006100770074006500000003000000010000001400000091C6D6EE3E8AC86384E548C299295C756C817B812000000001000000240400003082042030820308A0030201020210344ED55720D5EDEC49F42FCE37DB2B6D300D06092A864886F70D01010505003081A9310B300906035504061302555331153013060355040A130C7468617774652C20496E632E31283026060355040B131F43657274696669636174696F6E205365727669636573204469766973696F6E31383036060355040B132F2863292032303036207468617774652C20496E632E202D20466F7220617574686F72697A656420757365206F6E6C79311F301D06035504031316746861777465205072696D61727920526F6F74204341301E170D3036313131373030303030305A170D3336303731363233353935395A3081A9310B300906035504061302555331153013060355040A130C7468617774652C20496E632E31283026060355040B131F43657274696669636174696F6E205365727669636573204469766973696F6E31383036060355040B132F2863292032303036207468617774652C20496E632E202D20466F7220617574686F72697A656420757365206F6E6C79311F301D06035504031316746861777465205072696D61727920526F6F7420434130820122300D06092A864886F70D01010105000382010F003082010A0282010100ACA0F0FB8059D49CC7A4CF9DA159730910450C0D2C6E68F16C5B4868495937FC0B3319C2777FCC102D95341CE6EB4D09A71CD2B8C9973602B789D4245F06C0CC4494948D02626FEB5ADD118D289A5C8490107A0DBD74662F6A38A0E2D55444EB1D079F07BA6FEEE9FD4E0B29F53E84A001F19CABF81C7E89A4E8A1D871650DA3517BEEBCD222600DB95B9DDFBAFC515B0BAF98B2E92EE904E86287DE2BC8D74EC14C641EDDCF8758BA4A4FCA68071D1C9D4AC6D52F91CC7C71721CC5C067EB32FDC9925C94DA85C09BBF537D2B09F48C9D911F976A52CBDE0936A477D87B875044D53E6E2969FB3949261E09A5807B402DEBE82785C9FE61FD7EE67C971DD59D0203010001A3423040300F0603551D130101FF040530030101FF300E0603551D0F0101FF040403020106301D0603551D0E041604147B5B45CFAFCECB7AFD31921A6AB6F346EB574850300D06092A864886F70D010105050003820101007911C04BB391B6FCF0E967D40D6E45BE55E893D2CE033FEDDA25B01D57CB1E3A76A04CEC5076E864720CA4A9F1B88BD6D68784BB32E54111C077D9B3609DEB1BD5D16E4444A9A601EC55621D77B85C8E48497C9C3B5711ACAD73378E2F785C906847D96060E6FC073D222017C4F716E9C4D872F9C8737CDF162F15A93EFD6A27B6A1EB5ABA981FD5E34D640A9D13C861BAF5391C87BAB8BD7B227FF6FEAC4079E5AC106F3D8F1B79768BC437B3211884E53600EB632099B9E9FE3304BB41C8C102F94463209E81CE42D3D63F2C76D3639C59DD8FA6E10EA02E41F72E9547CFBCFD33F3F60B617E7E912B8147C22730EEA7105D378F5C392BE404F07B8D568C68 | |||
| (PID) Process: | (3792) pingsender.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\91C6D6EE3E8AC86384E548C299295C756C817B81 |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3792) pingsender.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\91C6D6EE3E8AC86384E548C299295C756C817B81 |
| Operation: | write | Name: | Blob |
Value: 190000000100000010000000DC73F9B71E16D51D26527D32B11A6A3D09000000010000002A000000302806082B0601050507030106082B0601050507030206082B0601050507030406082B0601050507030353000000010000002500000030233021060B6086480186F8450107300130123010060A2B0601040182373C0101030200C01400000001000000140000007B5B45CFAFCECB7AFD31921A6AB6F346EB5748501D00000001000000100000005B3B67000EEB80022E42605B6B3B72400B000000010000000E000000740068006100770074006500000003000000010000001400000091C6D6EE3E8AC86384E548C299295C756C817B812000000001000000240400003082042030820308A0030201020210344ED55720D5EDEC49F42FCE37DB2B6D300D06092A864886F70D01010505003081A9310B300906035504061302555331153013060355040A130C7468617774652C20496E632E31283026060355040B131F43657274696669636174696F6E205365727669636573204469766973696F6E31383036060355040B132F2863292032303036207468617774652C20496E632E202D20466F7220617574686F72697A656420757365206F6E6C79311F301D06035504031316746861777465205072696D61727920526F6F74204341301E170D3036313131373030303030305A170D3336303731363233353935395A3081A9310B300906035504061302555331153013060355040A130C7468617774652C20496E632E31283026060355040B131F43657274696669636174696F6E205365727669636573204469766973696F6E31383036060355040B132F2863292032303036207468617774652C20496E632E202D20466F7220617574686F72697A656420757365206F6E6C79311F301D06035504031316746861777465205072696D61727920526F6F7420434130820122300D06092A864886F70D01010105000382010F003082010A0282010100ACA0F0FB8059D49CC7A4CF9DA159730910450C0D2C6E68F16C5B4868495937FC0B3319C2777FCC102D95341CE6EB4D09A71CD2B8C9973602B789D4245F06C0CC4494948D02626FEB5ADD118D289A5C8490107A0DBD74662F6A38A0E2D55444EB1D079F07BA6FEEE9FD4E0B29F53E84A001F19CABF81C7E89A4E8A1D871650DA3517BEEBCD222600DB95B9DDFBAFC515B0BAF98B2E92EE904E86287DE2BC8D74EC14C641EDDCF8758BA4A4FCA68071D1C9D4AC6D52F91CC7C71721CC5C067EB32FDC9925C94DA85C09BBF537D2B09F48C9D911F976A52CBDE0936A477D87B875044D53E6E2969FB3949261E09A5807B402DEBE82785C9FE61FD7EE67C971DD59D0203010001A3423040300F0603551D130101FF040530030101FF300E0603551D0F0101FF040403020106301D0603551D0E041604147B5B45CFAFCECB7AFD31921A6AB6F346EB574850300D06092A864886F70D010105050003820101007911C04BB391B6FCF0E967D40D6E45BE55E893D2CE033FEDDA25B01D57CB1E3A76A04CEC5076E864720CA4A9F1B88BD6D68784BB32E54111C077D9B3609DEB1BD5D16E4444A9A601EC55621D77B85C8E48497C9C3B5711ACAD73378E2F785C906847D96060E6FC073D222017C4F716E9C4D872F9C8737CDF162F15A93EFD6A27B6A1EB5ABA981FD5E34D640A9D13C861BAF5391C87BAB8BD7B227FF6FEAC4079E5AC106F3D8F1B79768BC437B3211884E53600EB632099B9E9FE3304BB41C8C102F94463209E81CE42D3D63F2C76D3639C59DD8FA6E10EA02E41F72E9547CFBCFD33F3F60B617E7E912B8147C22730EEA7105D378F5C392BE404F07B8D568C68 | |||
| (PID) Process: | (2628) NETSTAT.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\RFC1156Agent\CurrentVersion\Parameters |
| Operation: | write | Name: | TrapPollTimeMilliSecs |
Value: 15000 | |||
Executable files
13
Suspicious files
381
Text files
302
Unknown types
140
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1524 | cmd.exe | C:\Users\admin\AppData\Local\Temp\test.test | — | |
MD5:— | SHA256:— | |||
| 3368 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3368 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3368 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 3368 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3368 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\block-flashsubdoc-digest256.pset | — | |
MD5:— | SHA256:— | |||
| 3368 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\block-flashsubdoc-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
| 3368 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\except-flash-digest256.pset | — | |
MD5:— | SHA256:— | |||
| 3368 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\except-flash-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
| 3368 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\except-flashallow-digest256.pset | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
205
TCP/UDP connections
166
DNS requests
295
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3368 | firefox.exe | POST | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3368 | firefox.exe | POST | 200 | 2.20.190.17:80 | http://ocsp.int-x3.letsencrypt.org/ | unknown | der | 527 b | whitelisted |
3368 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3368 | firefox.exe | POST | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
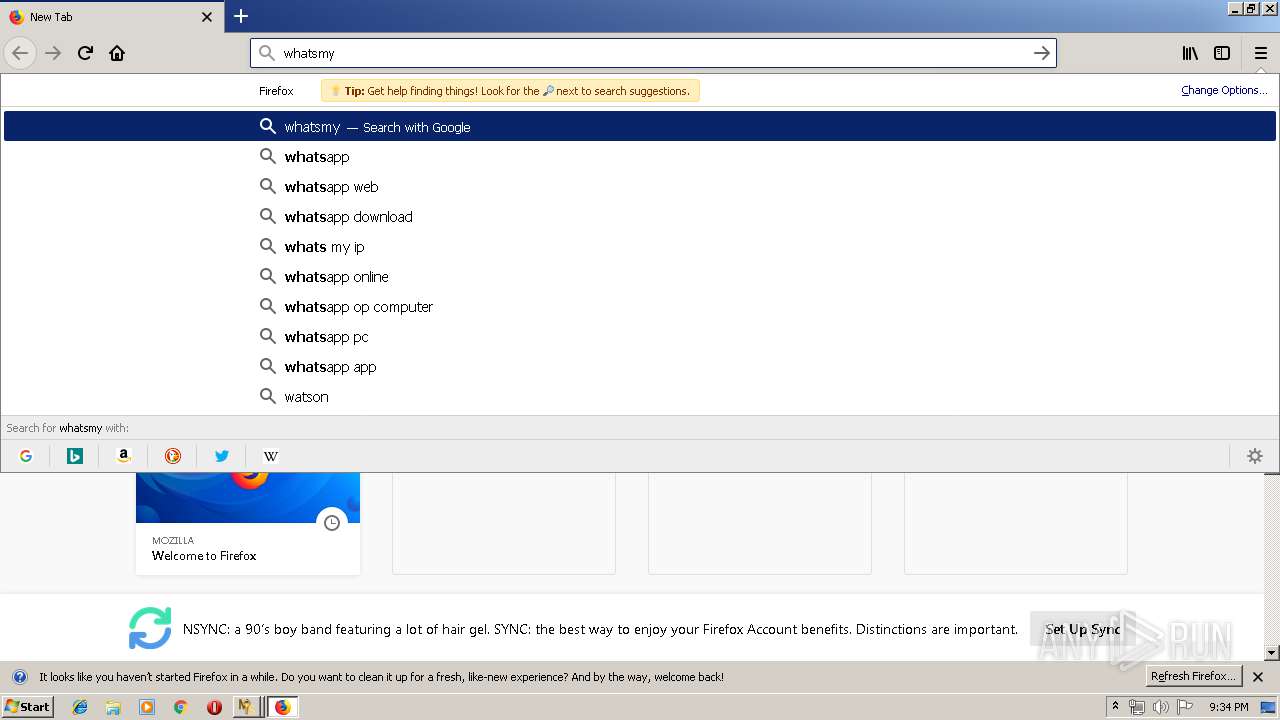
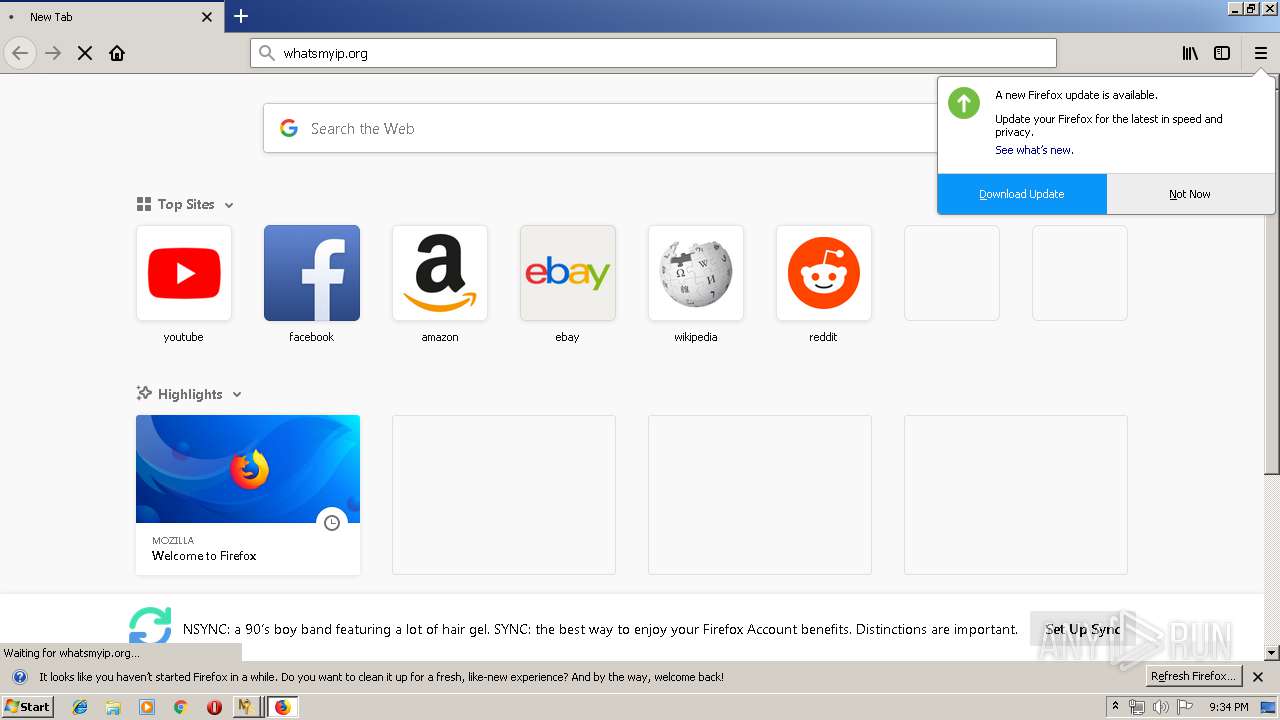
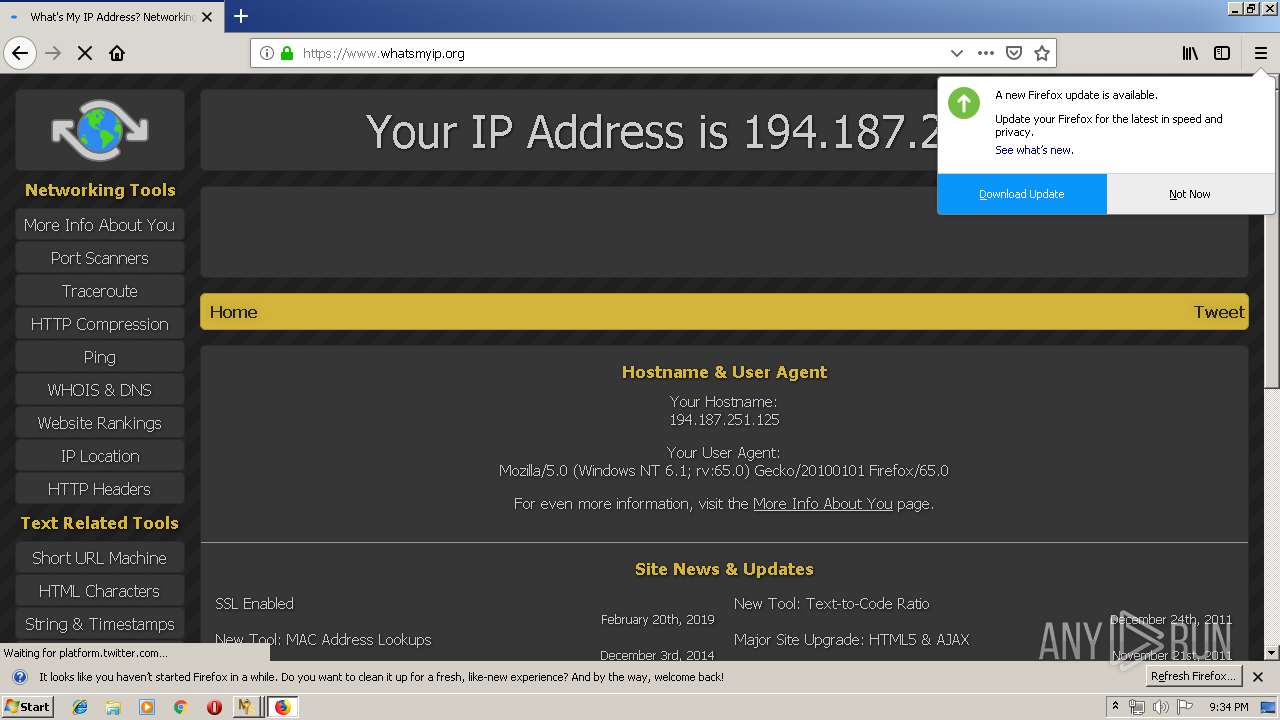
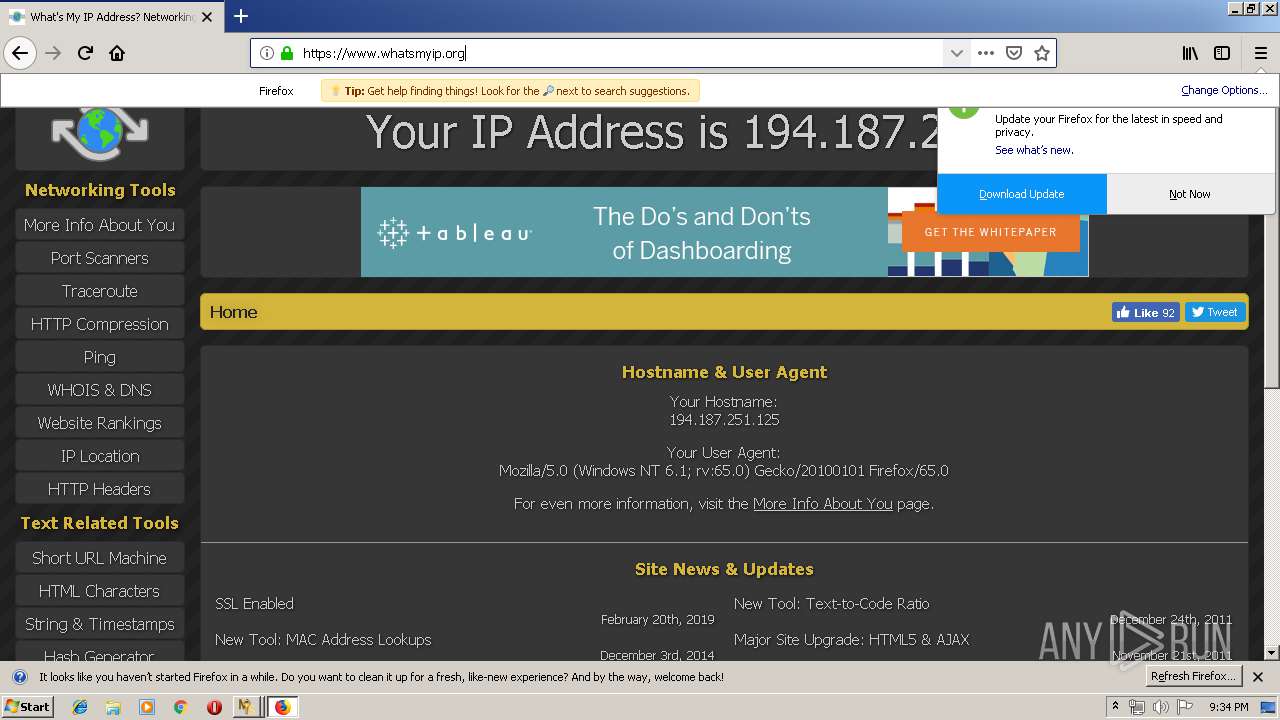
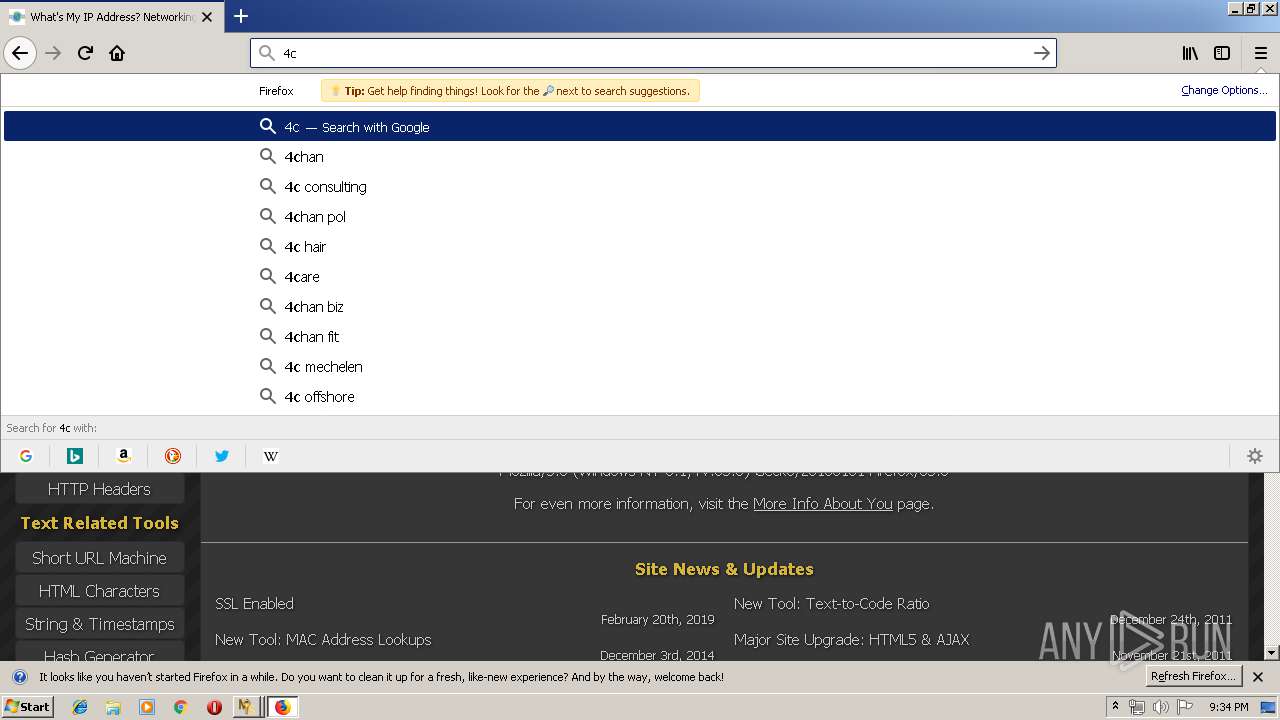
3368 | firefox.exe | GET | 301 | 204.11.35.98:80 | http://whatsmyip.org/ | US | html | 234 b | whitelisted |
3368 | firefox.exe | POST | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3368 | firefox.exe | POST | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3368 | firefox.exe | POST | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3368 | firefox.exe | POST | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3368 | firefox.exe | POST | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3368 | firefox.exe | 204.11.35.98:443 | whatsmyip.org | ManagedWay | US | unknown |
3368 | firefox.exe | 216.58.208.36:443 | www.google.com | Google Inc. | US | whitelisted |
3368 | firefox.exe | 204.11.35.98:80 | whatsmyip.org | ManagedWay | US | unknown |
3368 | firefox.exe | 54.186.120.41:443 | shavar.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3368 | firefox.exe | 2.16.106.209:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
3368 | firefox.exe | 52.88.179.171:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3368 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3368 | firefox.exe | 34.214.241.105:443 | aus5.mozilla.org | Amazon.com, Inc. | US | unknown |
3368 | firefox.exe | 52.222.157.71:443 | tracking-protection.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
3368 | firefox.exe | 31.13.92.14:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
aus5.mozilla.org |
| whitelisted |
balrog-aus5.r53-2.services.mozilla.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
tiles.r53-2.services.mozilla.com |
| whitelisted |