| File name: | KMSAuto Net.exe |
| Full analysis: | https://app.any.run/tasks/1148bd47-0a00-4435-be2e-d8503212ea11 |
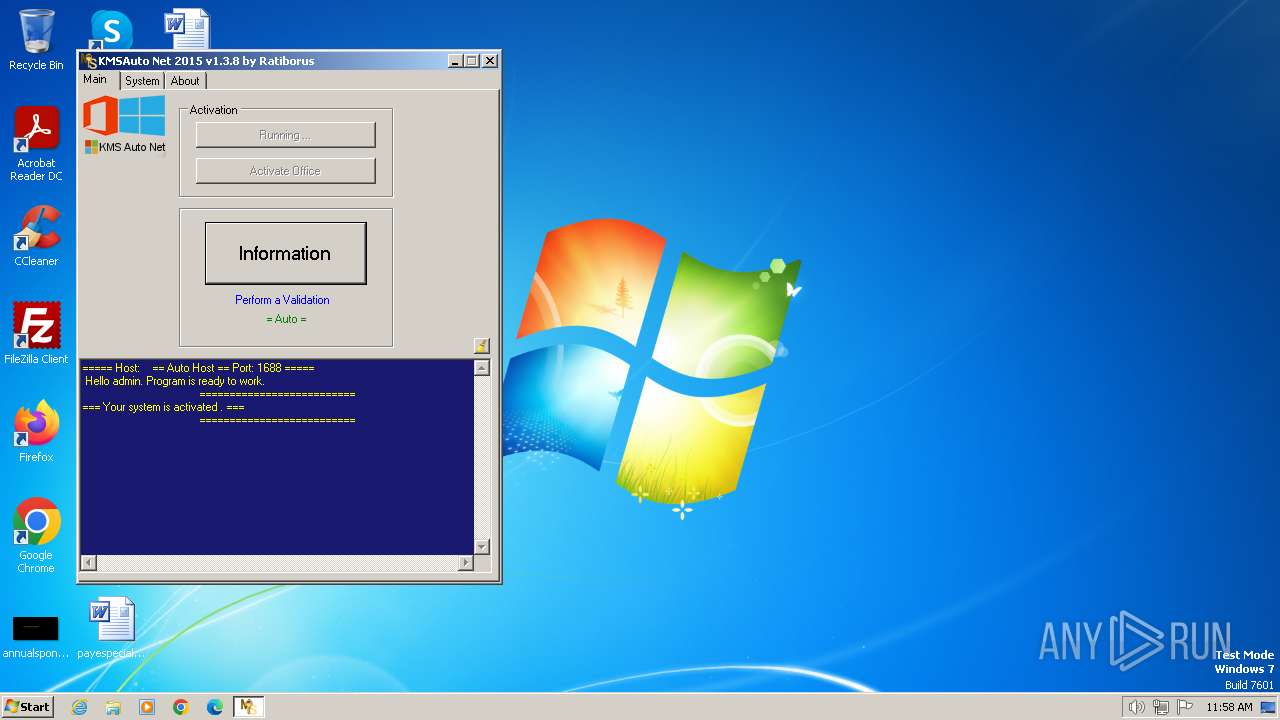
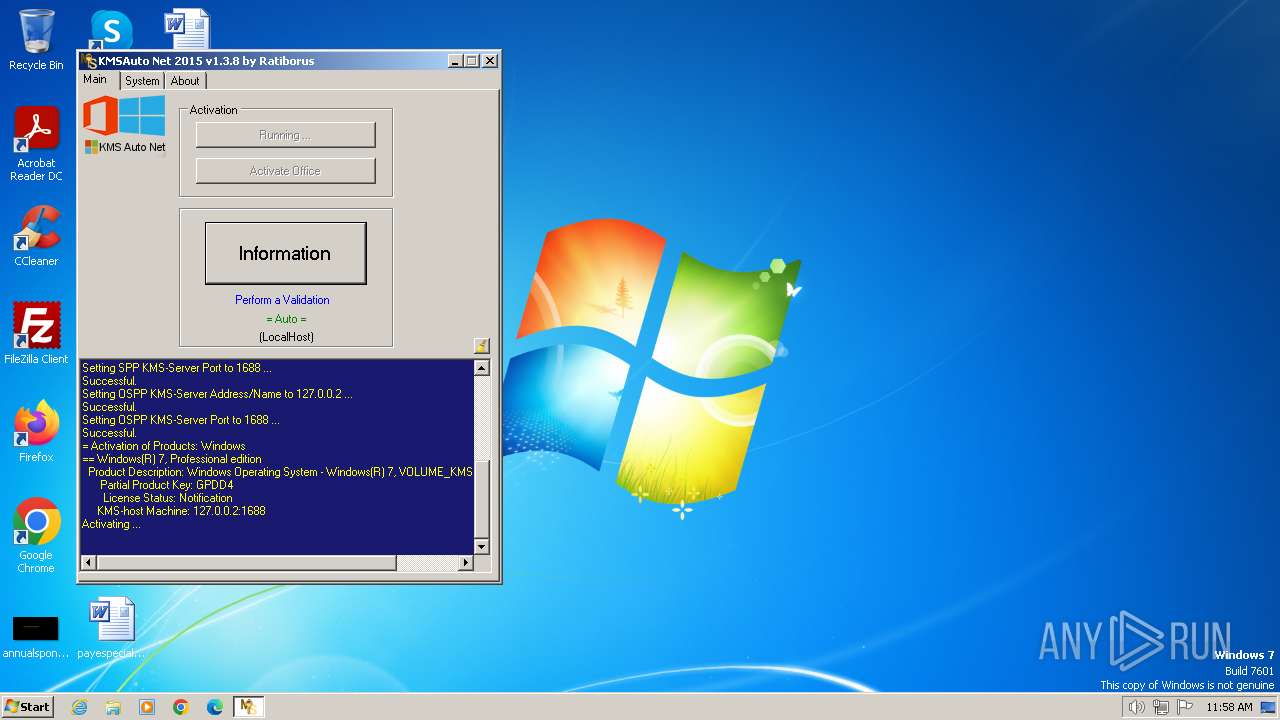
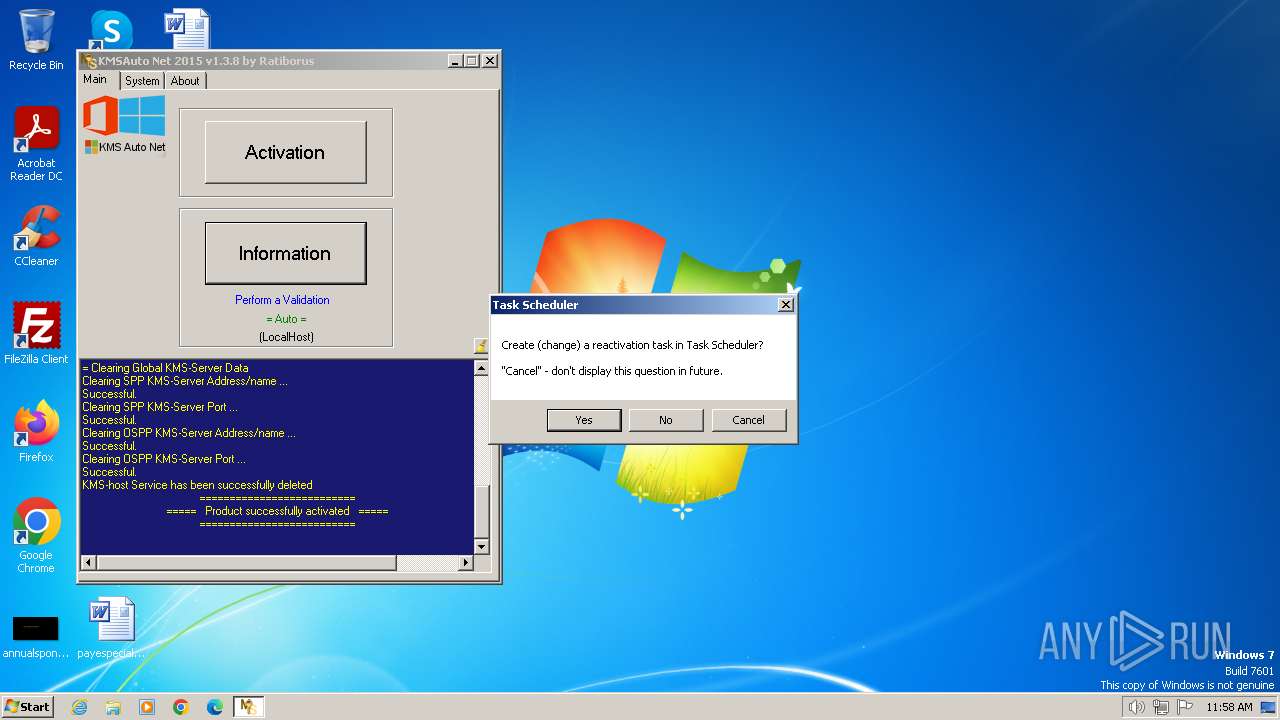
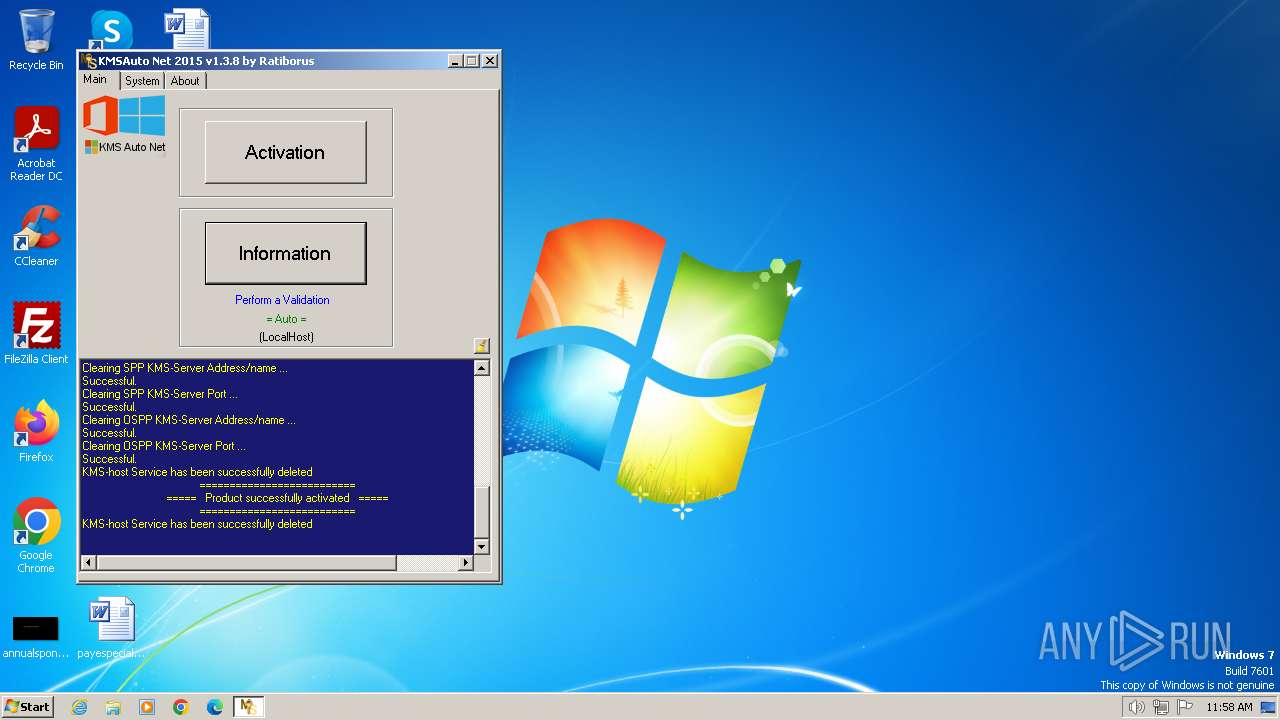
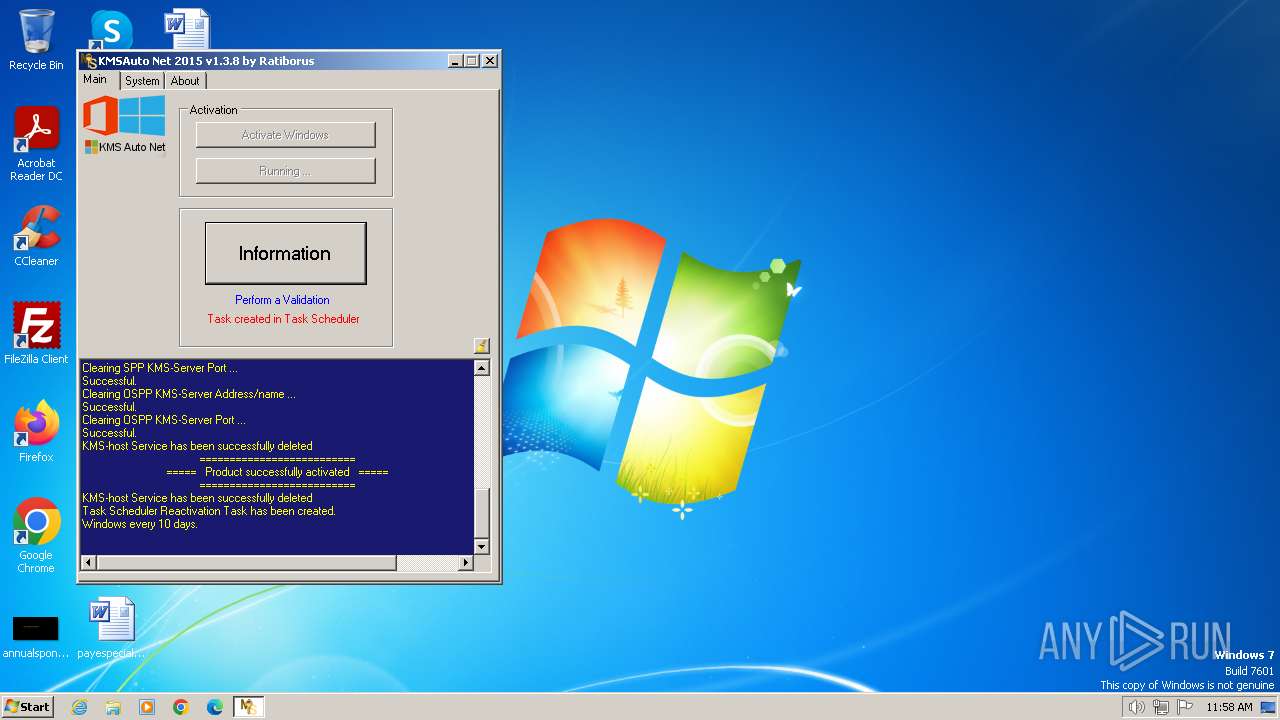
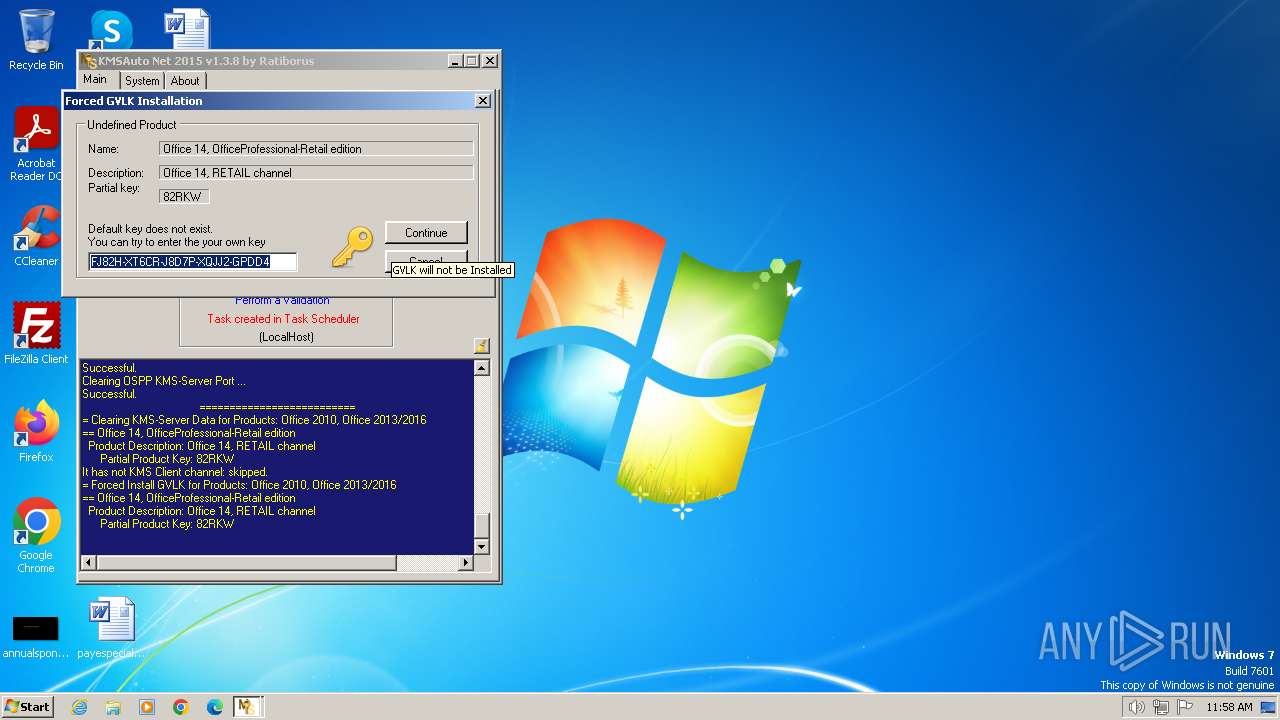
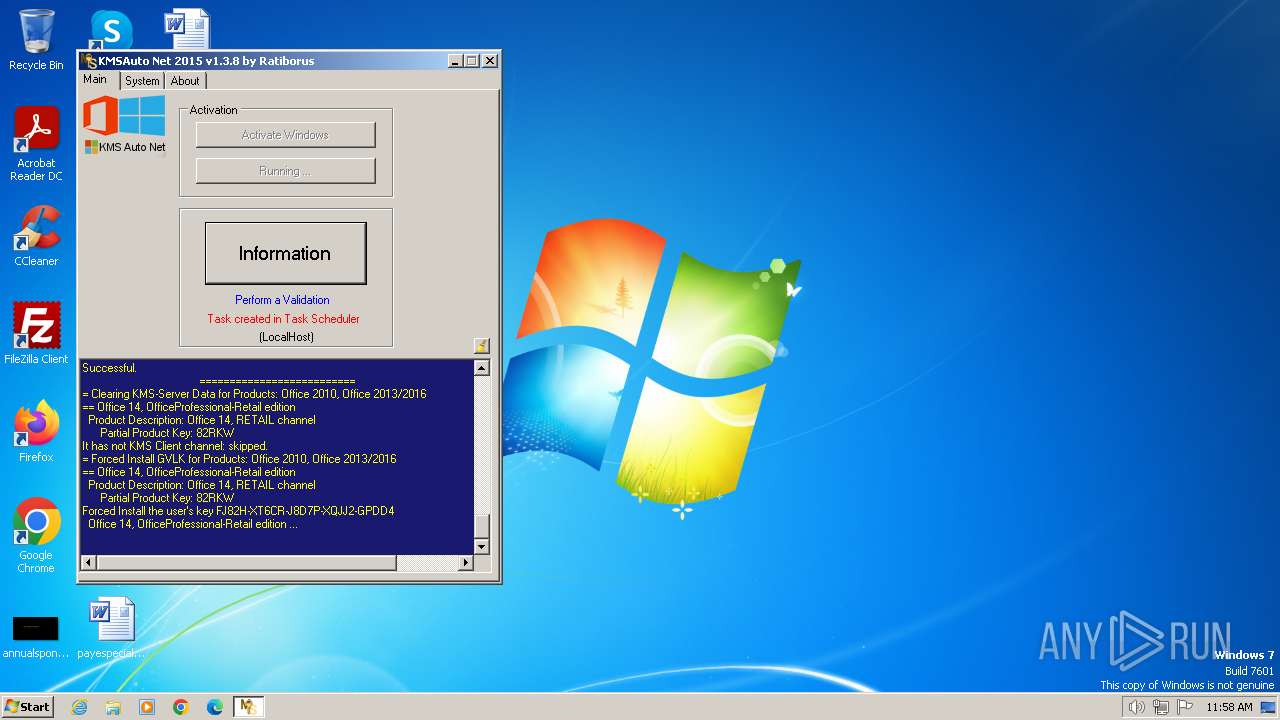
| Verdict: | Malicious activity |
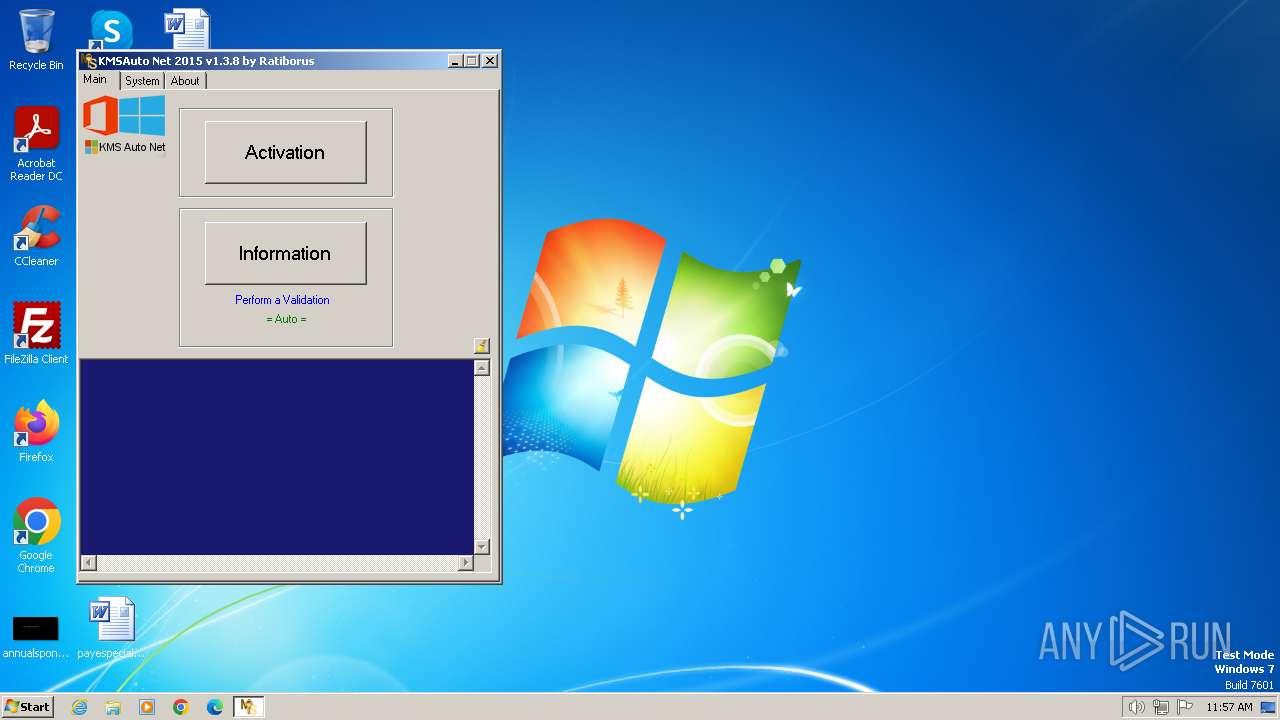
| Analysis date: | January 28, 2024, 11:57:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 6EE7F3ECD5111CD5306792FD3141515D |
| SHA1: | 45C92D0E691175A39A8C61228F526F80A7CA94FC |
| SHA256: | 69A8AE6352CFFD366409DF8E566E84315B4BFFCF5865A4B8079C446123BA1D26 |
| SSDEEP: | 196608:0eywBGqyw1lT3ywuywQyw1ywlywaywTyw9lywfywEyw1ywHywwywmIBywyywsywv:IwBGnw1l+wjwNw4wIw3w2w9IwqwJw4w4 |
MALICIOUS
Drops the executable file immediately after the start
- KMSAuto Net.exe (PID: 2592)
- bin.dat (PID: 3600)
- bin_x86.dat (PID: 3796)
- bin.dat (PID: 2372)
- bin_x86.dat (PID: 3056)
- bin.dat (PID: 1432)
- bin_x86.dat (PID: 604)
Opens a text file (SCRIPT)
- cscript.exe (PID: 2820)
SUSPICIOUS
Executes WMI query (SCRIPT)
- cscript.exe (PID: 2820)
Reads Internet Explorer settings
- KMSAuto Net.exe (PID: 2592)
The process executes VB scripts
- KMSAuto Net.exe (PID: 2592)
Starts CMD.EXE for commands execution
- KMSAuto Net.exe (PID: 2592)
- cmd.exe (PID: 3860)
- cmd.exe (PID: 1056)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 2820)
Drops 7-zip archiver for unpacking
- KMSAuto Net.exe (PID: 2592)
Executable content was dropped or overwritten
- KMSAuto Net.exe (PID: 2592)
- bin.dat (PID: 3600)
- bin_x86.dat (PID: 3796)
- bin.dat (PID: 2372)
- bin_x86.dat (PID: 3056)
- bin_x86.dat (PID: 604)
- bin.dat (PID: 1432)
Starts application with an unusual extension
- cmd.exe (PID: 3580)
- cmd.exe (PID: 3784)
- cmd.exe (PID: 3072)
- cmd.exe (PID: 2880)
- cmd.exe (PID: 3916)
- cmd.exe (PID: 3284)
Drops a system driver (possible attempt to evade defenses)
- bin_x86.dat (PID: 3796)
- bin_x86.dat (PID: 3056)
- bin_x86.dat (PID: 604)
Process drops legitimate windows executable
- bin_x86.dat (PID: 3796)
- bin_x86.dat (PID: 3056)
- bin_x86.dat (PID: 604)
Application launched itself
- cmd.exe (PID: 3860)
- cmd.exe (PID: 1056)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- KMSAuto Net.exe (PID: 2592)
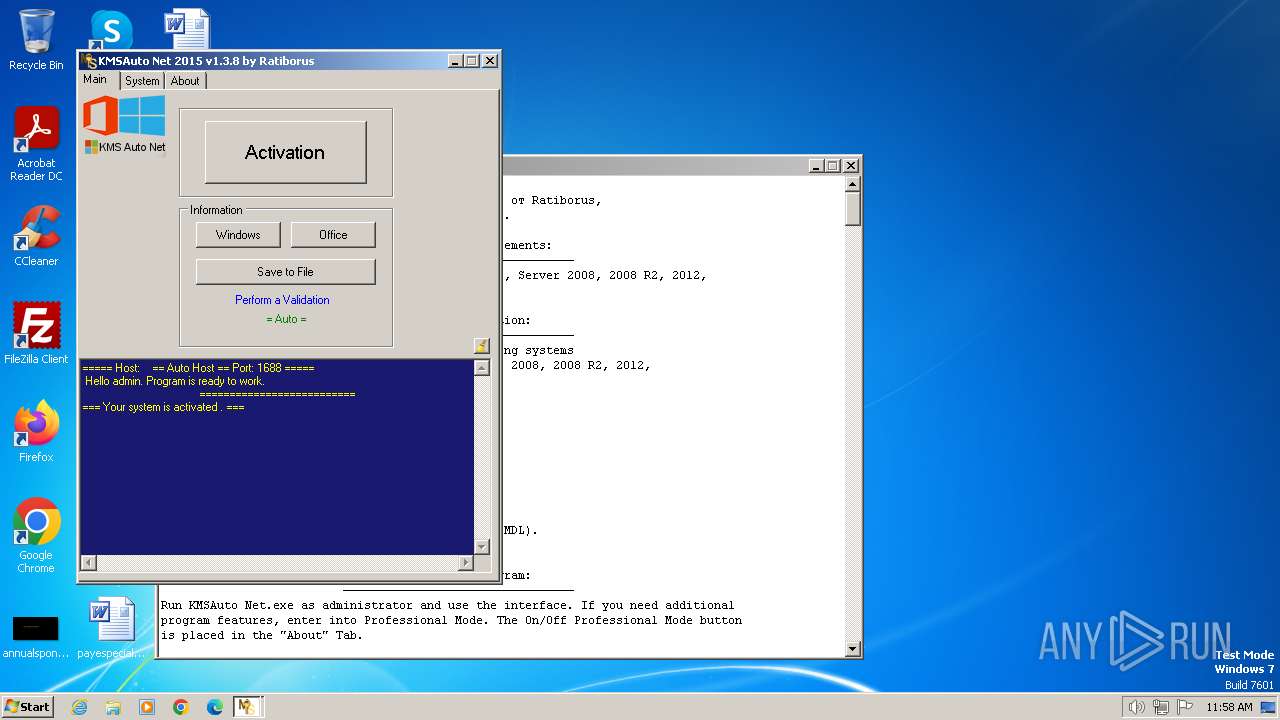
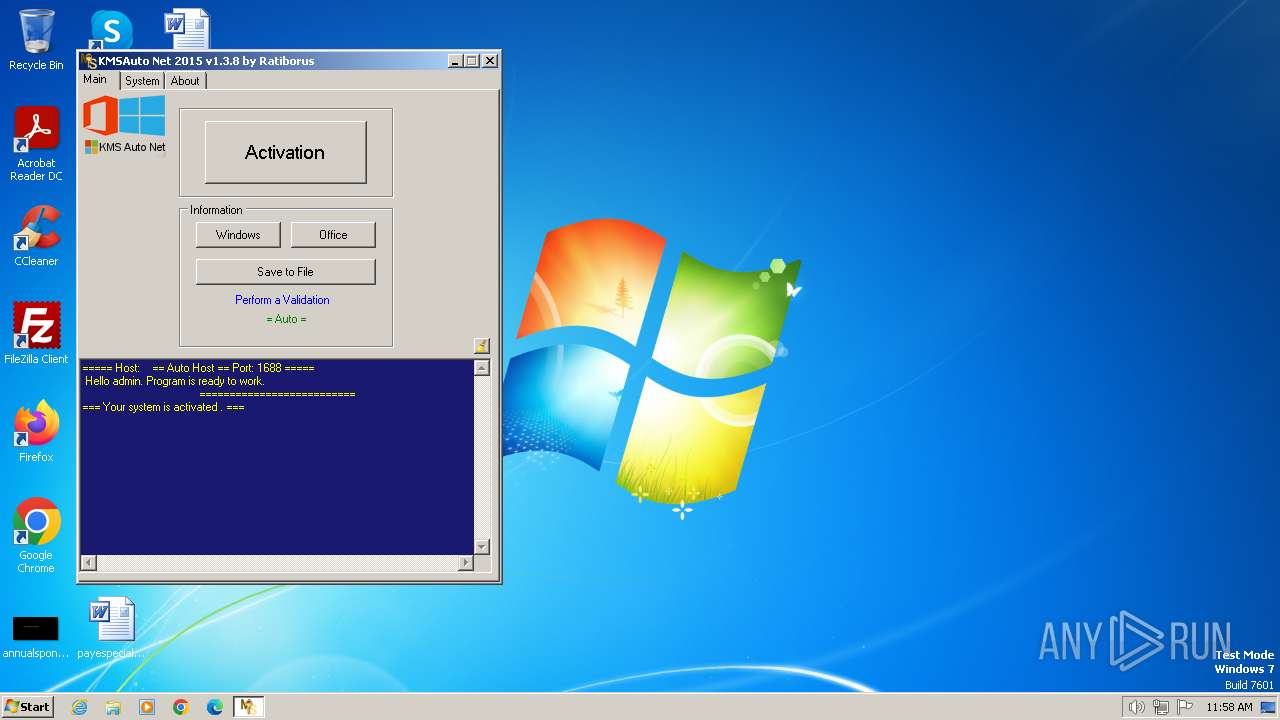
Executes as Windows Service
- KMSSS.exe (PID: 3964)
- KMSSS.exe (PID: 668)
Uses NETSH.EXE to add a firewall rule or allowed programs
- KMSAuto Net.exe (PID: 2592)
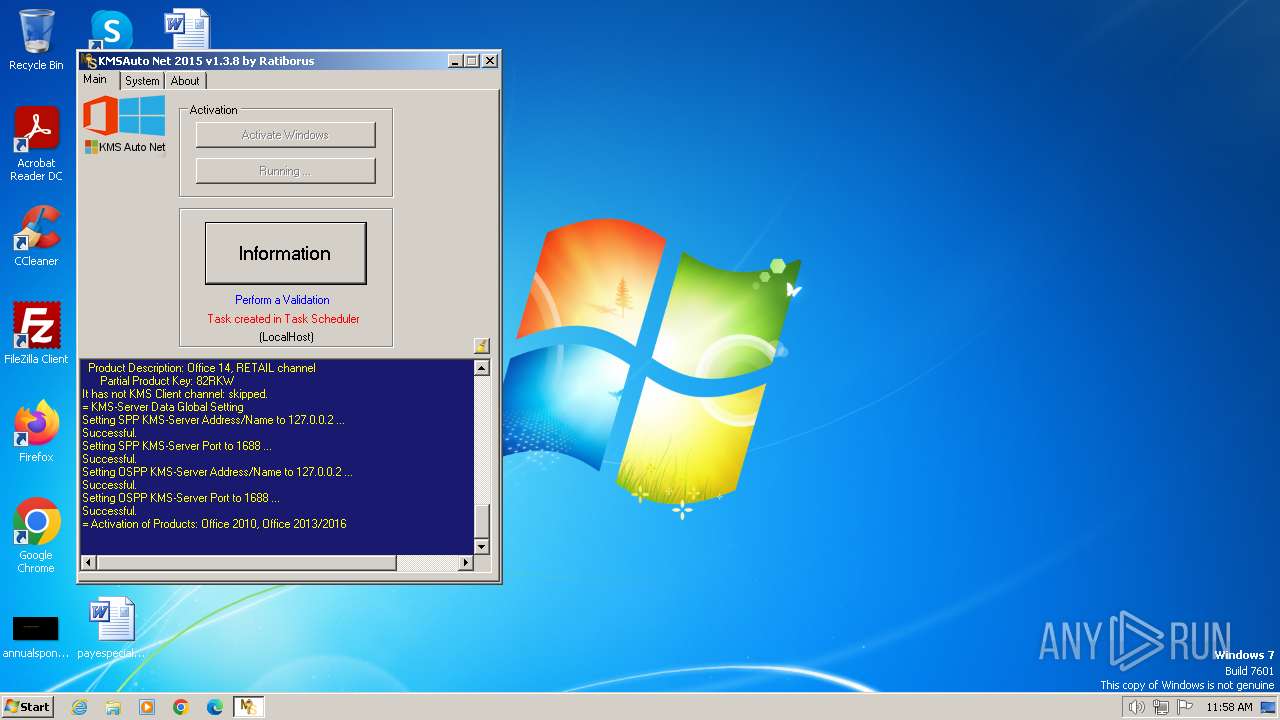
Creates or modifies Windows services
- KMSAuto Net.exe (PID: 2592)
Uses REG/REGEDIT.EXE to modify registry
- KMSAuto Net.exe (PID: 2592)
- cmd.exe (PID: 3528)
Starts SC.EXE for service management
- KMSAuto Net.exe (PID: 2592)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 2820)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- cscript.exe (PID: 2820)
Checks whether a specific file exists (SCRIPT)
- cscript.exe (PID: 2820)
Reads data from a binary Stream object (SCRIPT)
- cscript.exe (PID: 2820)
INFO
Checks supported languages
- KMSAuto Net.exe (PID: 2592)
- bin.dat (PID: 3600)
- bin_x86.dat (PID: 3796)
- KMSSS.exe (PID: 3964)
- bin.dat (PID: 2372)
- bin.dat (PID: 1432)
- bin_x86.dat (PID: 3056)
- bin_x86.dat (PID: 604)
- KMSSS.exe (PID: 668)
Reads the computer name
- KMSAuto Net.exe (PID: 2592)
- KMSSS.exe (PID: 3964)
- KMSSS.exe (PID: 668)
Reads the machine GUID from the registry
- KMSAuto Net.exe (PID: 2592)
- KMSSS.exe (PID: 3964)
Creates files or folders in the user directory
- KMSAuto Net.exe (PID: 2592)
Reads Environment values
- KMSAuto Net.exe (PID: 2592)
Reads product name
- KMSAuto Net.exe (PID: 2592)
Creates files in the program directory
- KMSAuto Net.exe (PID: 2592)
- bin.dat (PID: 3600)
- bin_x86.dat (PID: 3796)
- KMSSS.exe (PID: 3964)
- cmd.exe (PID: 3324)
- bin_x86.dat (PID: 3056)
- bin.dat (PID: 2372)
- cmd.exe (PID: 3740)
- bin.dat (PID: 1432)
- bin_x86.dat (PID: 604)
- KMSSS.exe (PID: 668)
- cmd.exe (PID: 3524)
Create files in a temporary directory
- KMSAuto Net.exe (PID: 2592)
Reads security settings of Internet Explorer
- cscript.exe (PID: 2820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (16) |
|---|---|---|
| .scr | | | Windows screen saver (7.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.8) |
| .exe | | | Win32 Executable (generic) (2.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:08:10 09:45:14+02:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 6923776 |
| InitializedDataSize: | 49152 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x69c4c2 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.3.8.0 |
| ProductVersionNumber: | 1.3.8.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
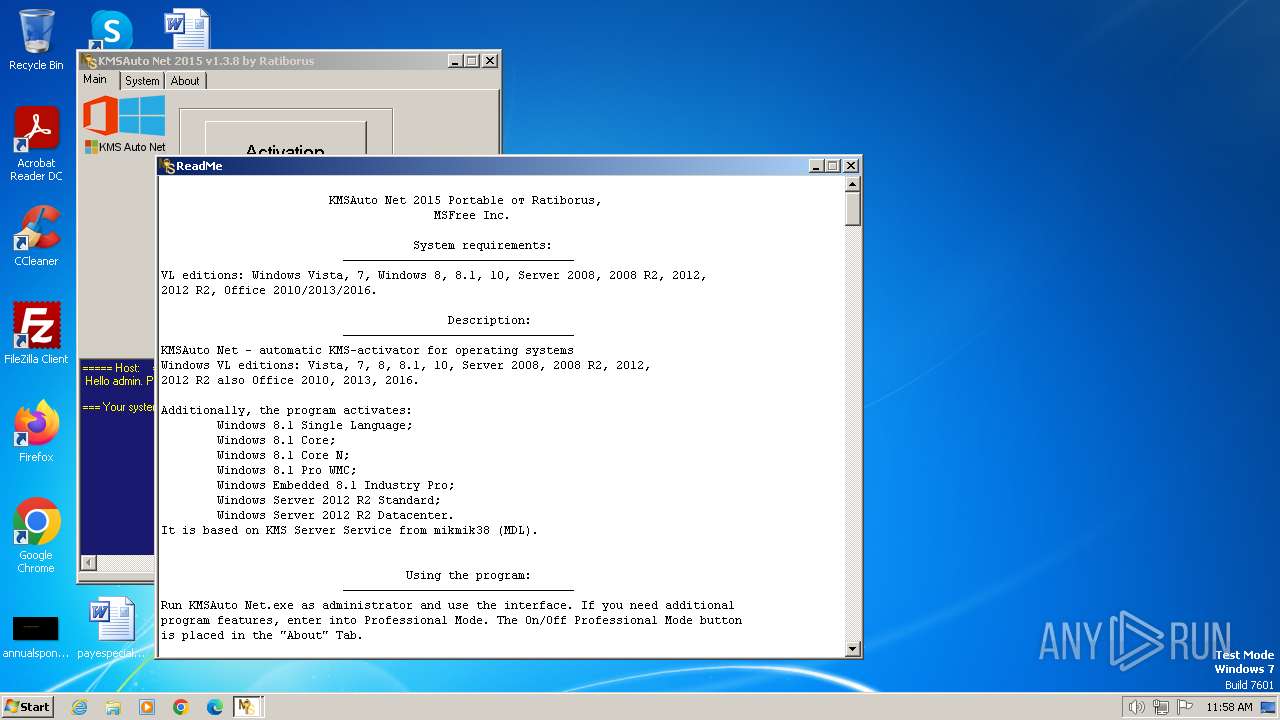
| CompanyName: | MSFree Inc. |
| FileDescription: | KMSAuto Net |
| FileVersion: | 1.3.8 |
| InternalName: | KMSAuto Net.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | KMSAuto Net.exe |
| ProductName: | KMSAuto Net |
| ProductVersion: | 1.3.8 |
| AssemblyVersion: | 1.3.8.0 |
Total processes
174
Monitored processes
76
Malicious processes
11
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 376 | C:\Windows\System32\reg delete "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\OfficeSoftwareProtectionPlatform\59A52881-A989-479D-AF46-F275C6370663" /f | C:\Windows\System32\reg.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 448 | schtasks.exe /delete /TN KMSAutoNet /F | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 480 | "sc.exe" start KMSEmulator | C:\Windows\System32\sc.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 532 | find ":1688 " | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 604 | bin_x86.dat -y -pkmsauto | C:\ProgramData\KMSAuto\bin_x86.dat | cmd.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7z Console SFX Exit code: 0 Version: 9.20 Modules
| |||||||||||||||
| 664 | schtasks.exe /end /TN KMSAutoNet | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 668 | "C:\ProgramData\KMSAuto\bin\KMSSS.exe" -Port 1688 -PWin RandomKMSPID -PO14 RandomKMSPID -PO15 RandomKMSPID -AI 43200 -RI 43200 KillProcessOnPort -Log -IP | C:\ProgramData\KMSAuto\bin\KMSSS.exe | — | services.exe | |||||||||||
User: SYSTEM Company: MDL Forum, mod by Ratiborus Integrity Level: SYSTEM Description: KMS Server Emulator Service (XP) Exit code: 0 Version: 1.2.1.0 Modules
| |||||||||||||||
| 752 | "sc.exe" stop KMSEmulator | C:\Windows\System32\sc.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1056 | C:\Windows\System32\reg delete "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\55C92734-D682-4D71-983E-D6EC3F16059F" /f | C:\Windows\System32\reg.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1056 | C:\Windows\System32\cmd.exe /c for /f "tokens=5 delims=, " %i in ('netstat -ano ^| find ":1688 "') do taskkill /pid %i /f | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
4 622
Read events
4 335
Write events
279
Delete events
8
Modification events
| (PID) Process: | (3448) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3668) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2592) KMSAuto Net.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\KMSEmulator |
| Operation: | write | Name: | ImagePath |
Value: temp.exe | |||
| (PID) Process: | (2592) KMSAuto Net.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform |
| Operation: | delete value | Name: | KeyManagementServiceName |
Value: 127.0.0.2 | |||
| (PID) Process: | (2592) KMSAuto Net.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform |
| Operation: | delete value | Name: | KeyManagementServicePort |
Value: 1688 | |||
| (PID) Process: | (2592) KMSAuto Net.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\OfficeSoftwareProtectionPlatform |
| Operation: | delete value | Name: | KeyManagementServiceName |
Value: 127.0.0.2 | |||
| (PID) Process: | (2592) KMSAuto Net.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\OfficeSoftwareProtectionPlatform |
| Operation: | delete value | Name: | KeyManagementServicePort |
Value: 1688 | |||
| (PID) Process: | (2580) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2896) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4080) NETSTAT.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\RFC1156Agent\CurrentVersion\Parameters |
| Operation: | write | Name: | TrapPollTimeMilliSecs |
Value: 15000 | |||
Executable files
40
Suspicious files
20
Text files
10
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2592 | KMSAuto Net.exe | C:\Users\admin\AppData\Local\MSfree Inc\kmsauto.ini | text | |
MD5:B22721ECC7249380EF3032685ED19A5A | SHA256:2AC517A3388939951E5BC81489A251193C4BCB4620A9968BA0EC8F34594952D8 | |||
| 3600 | bin.dat | C:\ProgramData\KMSAuto\bin\TunMirror2.exe | executable | |
MD5:4AA2E87FBA32884CC6FF97B1798E69EB | SHA256:8D6432321E0C5BC3C9ABEFB6B0C102F30E910B0691D90194DD0115A4F4DC4D9C | |||
| 3796 | bin_x86.dat | C:\ProgramData\KMSAuto\bin\driver\oas_sert.cer | binary | |
MD5:0041584E5F66762B1FA9BE8910D0B92B | SHA256:BB27684B569CBB72DEC63EA6FDEF8E5F410CDAEB73717EEE1B36478DBCFF94CC | |||
| 3796 | bin_x86.dat | C:\ProgramData\KMSAuto\bin\driver\tap0901.cer | binary | |
MD5:3D5FFD53BE77C32CBB147F32423C0A86 | SHA256:669C56DB590C0308EA25C4508375BB88611B06B1AE689A895DC6B19F4DF5619C | |||
| 2592 | KMSAuto Net.exe | C:\ProgramData\KMSAuto\bin_x86.dat | executable | |
MD5:EE610244248F502AA9755A7EA85C341C | SHA256:205987B7CCC639AE1F7185C6F4326FE926FF74272915B2FDA7CE8D43A4E2A803 | |||
| 2804 | cmd.exe | C:\Users\admin\AppData\Local\Temp\test.test | text | |
MD5:9F06243ABCB89C70E0C331C61D871FA7 | SHA256:837CCB607E312B170FAC7383D7CCFD61FA5072793F19A25E75FBACB56539B86B | |||
| 3796 | bin_x86.dat | C:\ProgramData\KMSAuto\bin\driver\x86TAP2\oas_sert.cer | binary | |
MD5:0041584E5F66762B1FA9BE8910D0B92B | SHA256:BB27684B569CBB72DEC63EA6FDEF8E5F410CDAEB73717EEE1B36478DBCFF94CC | |||
| 2592 | KMSAuto Net.exe | C:\ProgramData\KMSAuto\bin.dat | executable | |
MD5:25F096B533E87AFBA34432F577E45013 | SHA256:0B4AF6D407E5ADB4975CCB3D3B1A504F211DFC9E3307A36E8D40D8029A7D11FA | |||
| 3600 | bin.dat | C:\ProgramData\KMSAuto\bin\TunMirror.exe | executable | |
MD5:362498C3E71EEAA066A67E4A3F981D1C | SHA256:D87E8D9D43758CE67A8052CB2334B99CC24F9B0437EE44815F360BE0B22D835A | |||
| 3600 | bin.dat | C:\ProgramData\KMSAuto\bin\KMSSS.exe | executable | |
MD5:0F03F72A92AEF6D63EB74E73F8AC201D | SHA256:ACD55C44B8B0D66D66DEFED85CA18082C092F048D3621DA827FCE593305C11FD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |