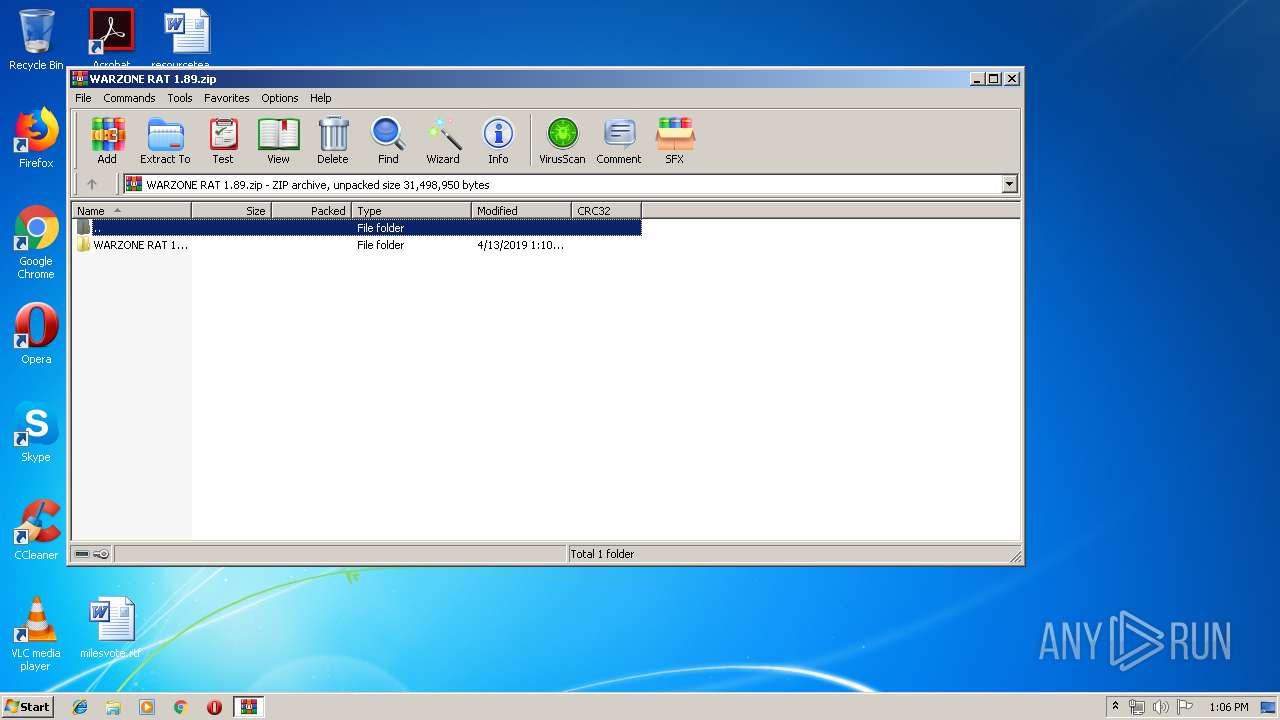
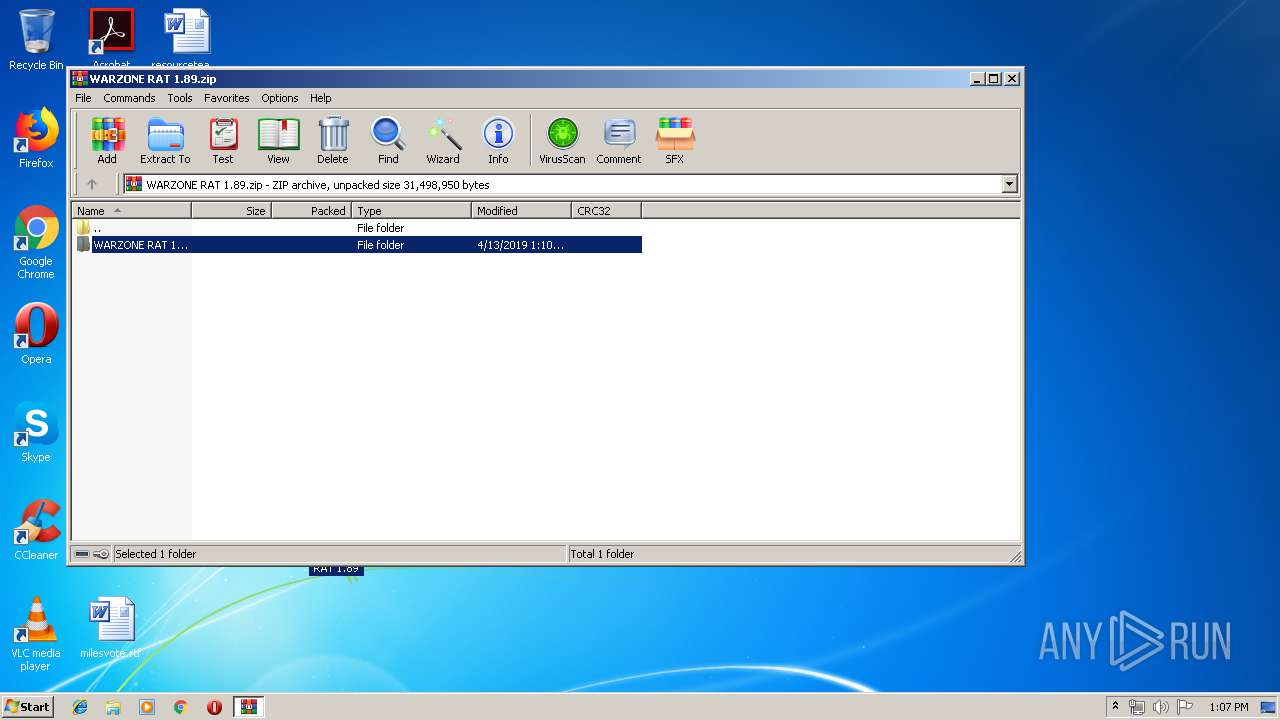
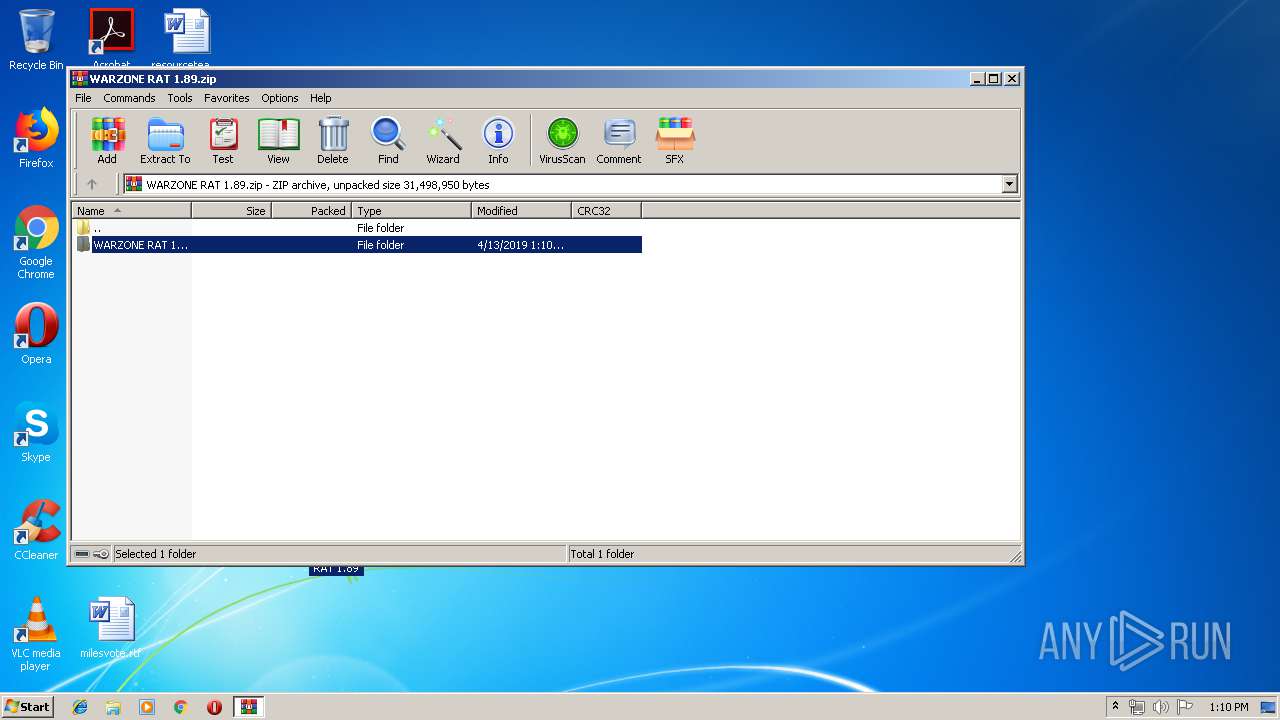
| File name: | WARZONE RAT 1.89.zip |
| Full analysis: | https://app.any.run/tasks/edd8e74b-622e-4a8b-8950-3d457fba5a15 |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 12:06:26 |
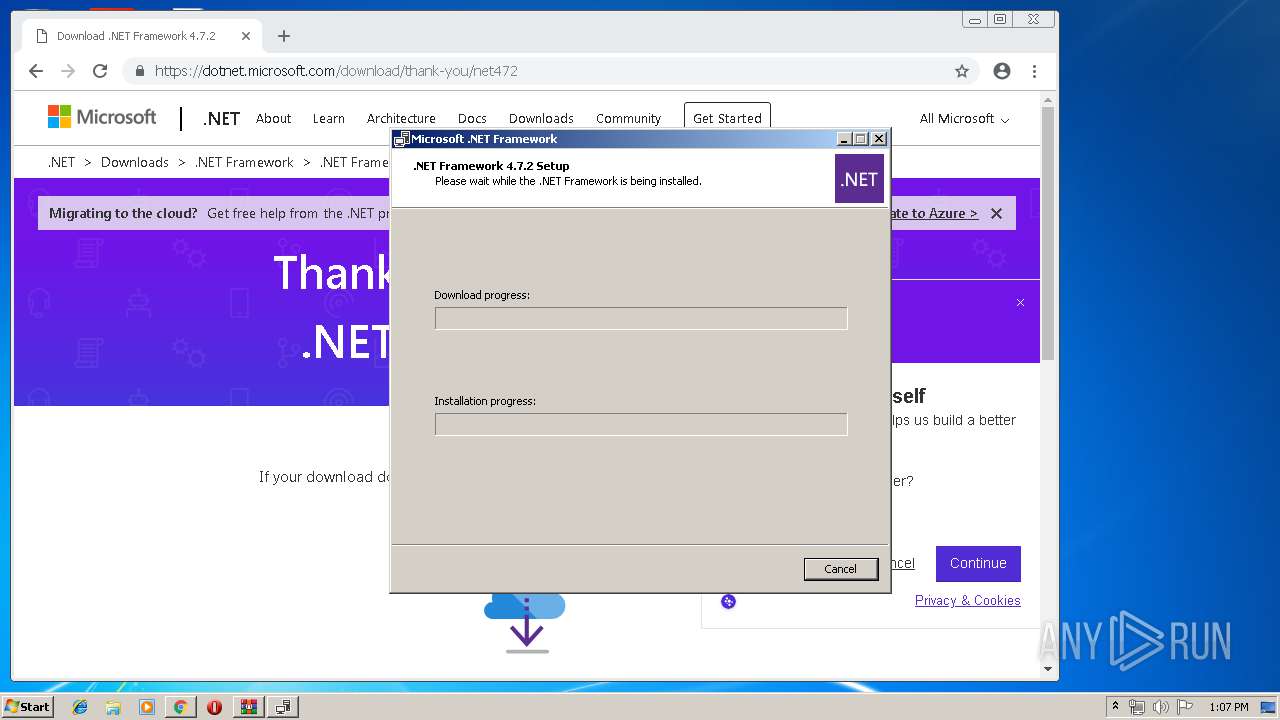
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | DACE5E510A5868CF8A19E53F8AE06C2F |
| SHA1: | D6806589691F51AC14FDE665F9EBBDA56AC6945F |
| SHA256: | 6998346F222A1B82CCB88645F8B8D159B7EB476C076EF7A18C1606F2D2BBCE08 |
| SSDEEP: | 393216:IFKfp6uNojFncU4SlLbO2Ts2VMMcGZVR4Oph8skg0Eejch5P7OK:IGVCjFnccm05VMmZF8szhejy5yK |
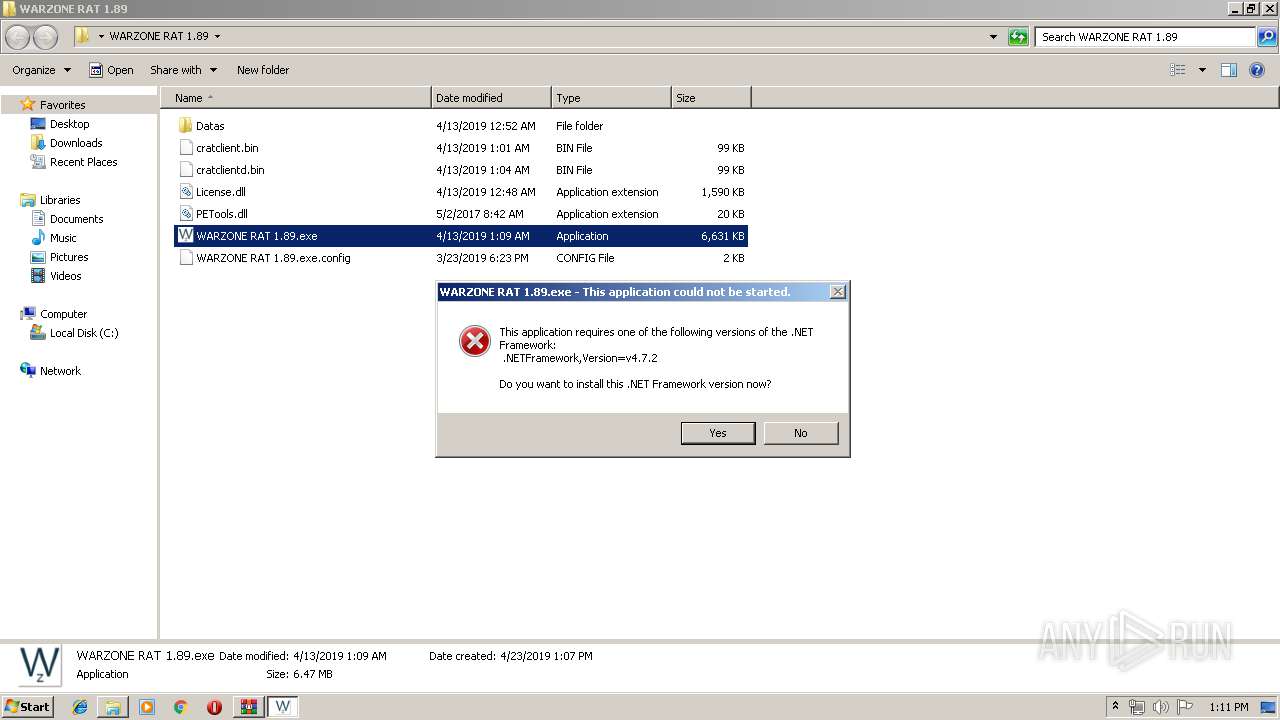
MALICIOUS
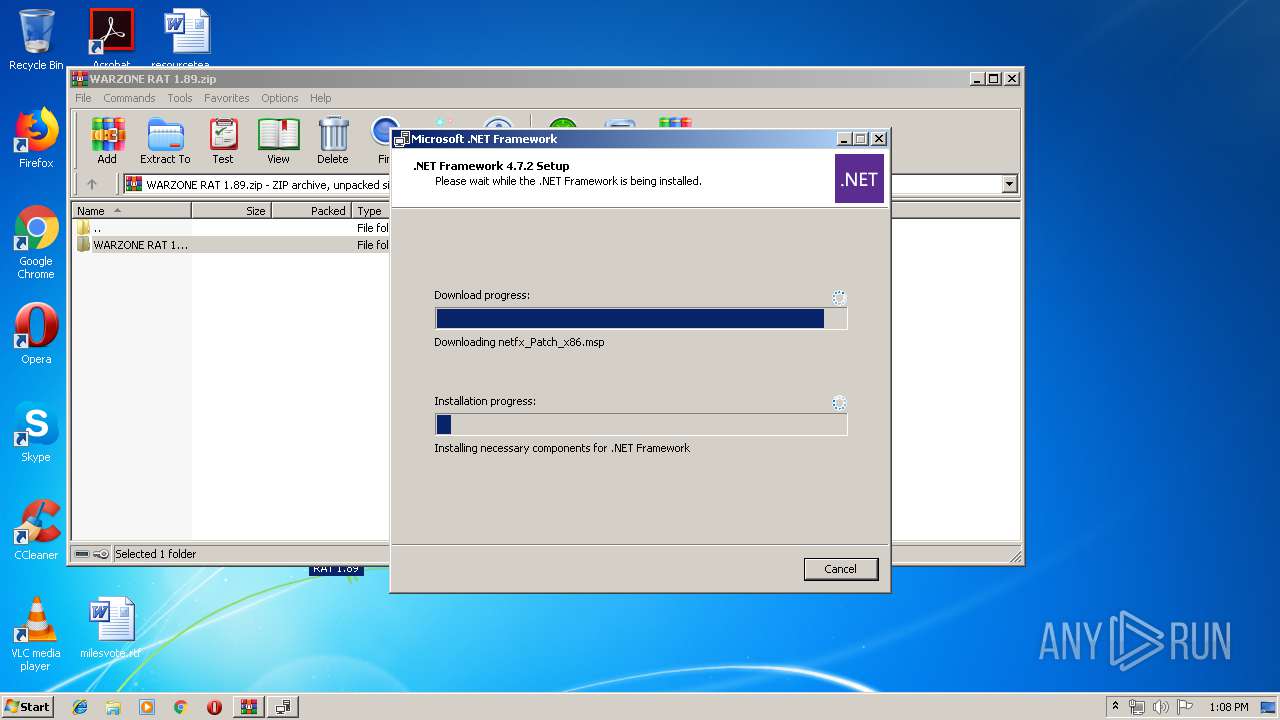
Application was dropped or rewritten from another process
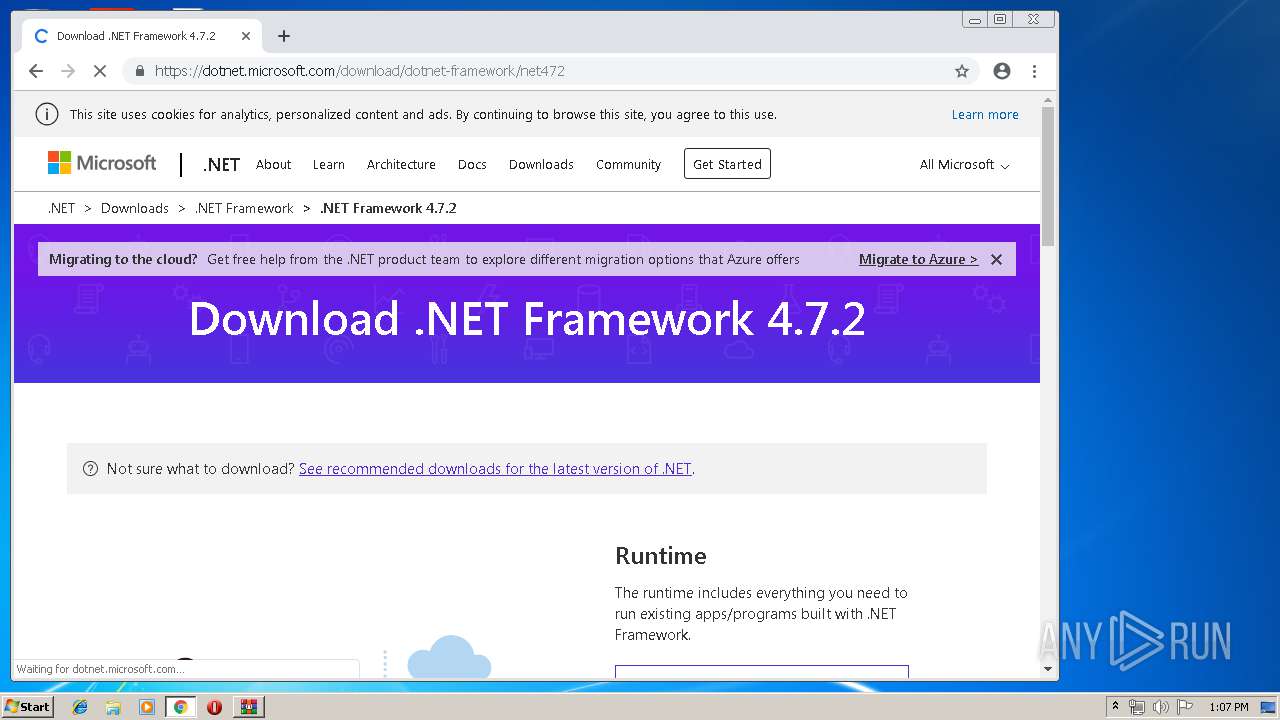
- NDP472-KB4054531-Web.exe (PID: 2952)
- NDP472-KB4054531-Web.exe (PID: 2108)
- Setup.exe (PID: 1520)
- SetupUtility.exe (PID: 2664)
- SetupUtility.exe (PID: 1364)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3180)
- Setup.exe (PID: 1520)
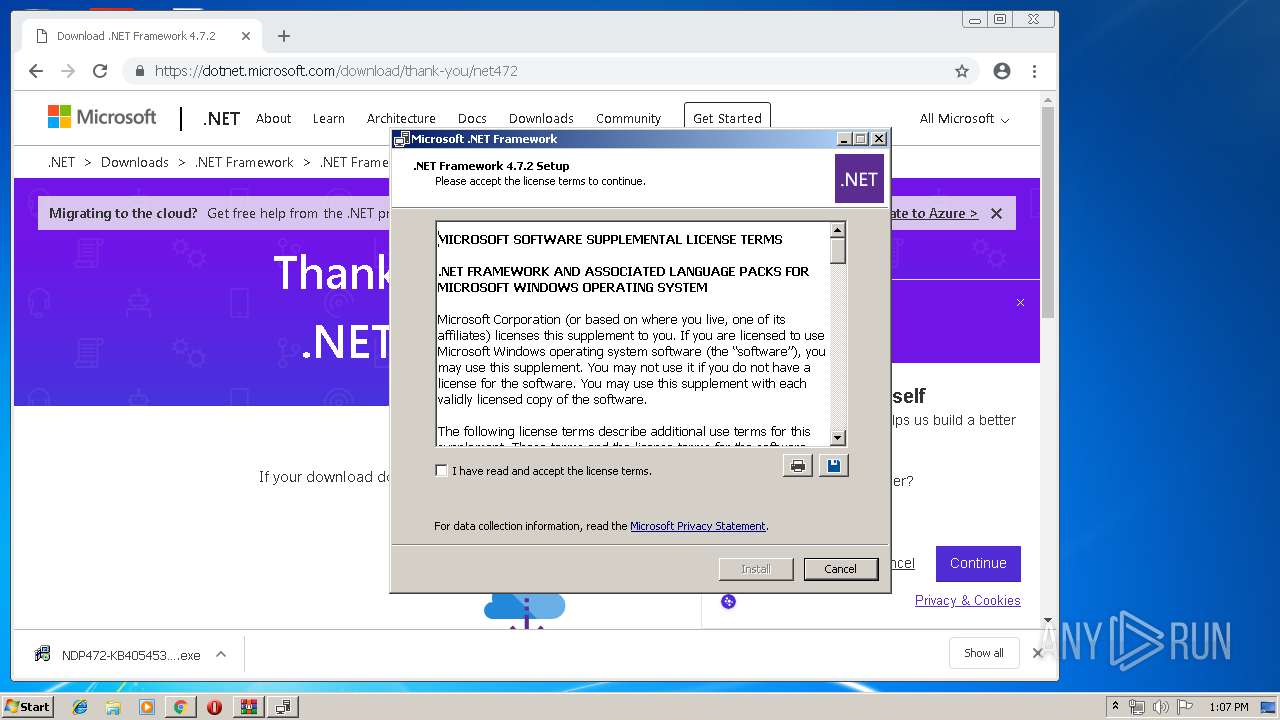
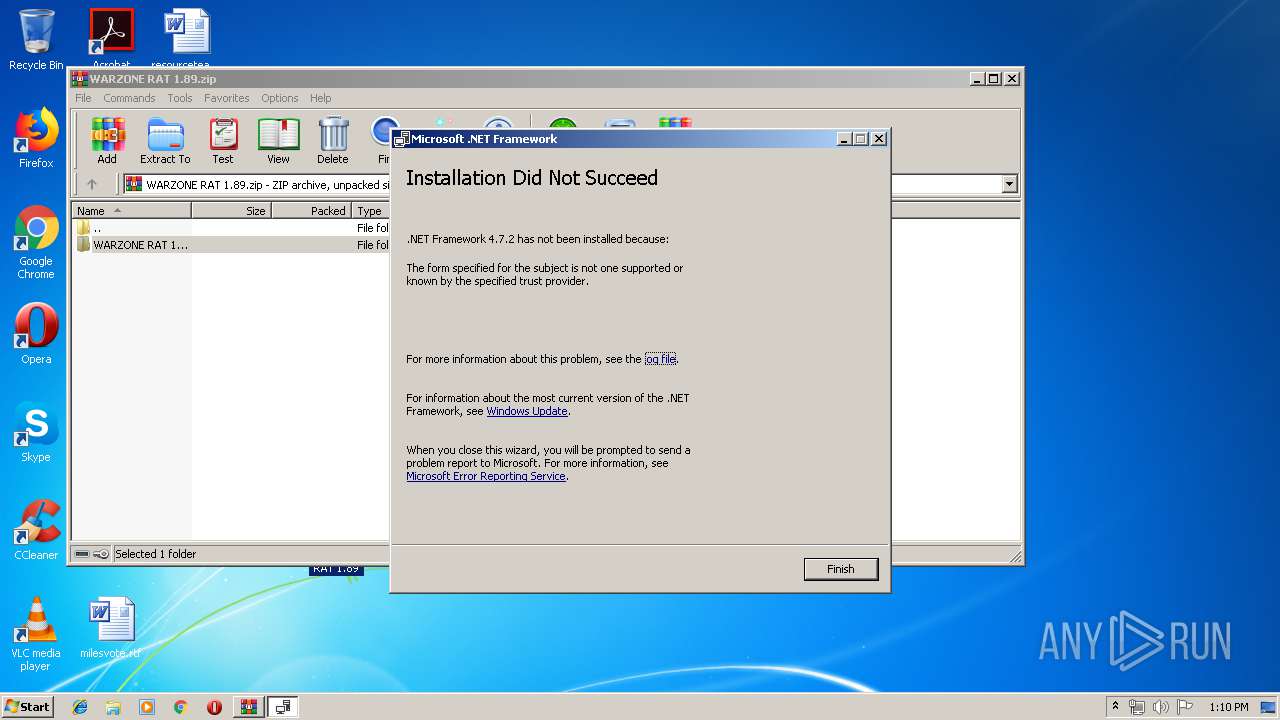
Changes settings of System certificates
- Setup.exe (PID: 1520)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2364)
- chrome.exe (PID: 3412)
- NDP472-KB4054531-Web.exe (PID: 2108)
- TMP64A.tmp.exe (PID: 2104)
- Setup.exe (PID: 1520)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3412)
Adds / modifies Windows certificates
- Setup.exe (PID: 1520)
Creates files in the user directory
- Setup.exe (PID: 1520)
Creates files in the program directory
- Setup.exe (PID: 1520)
INFO
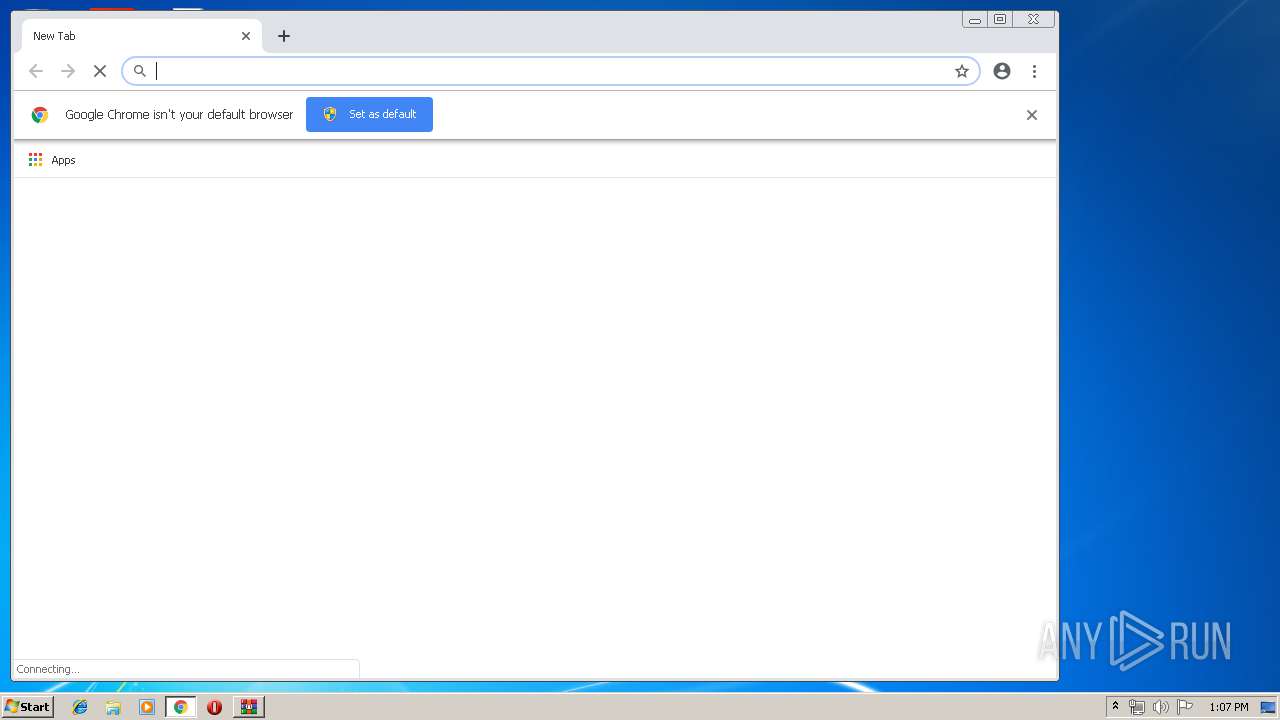
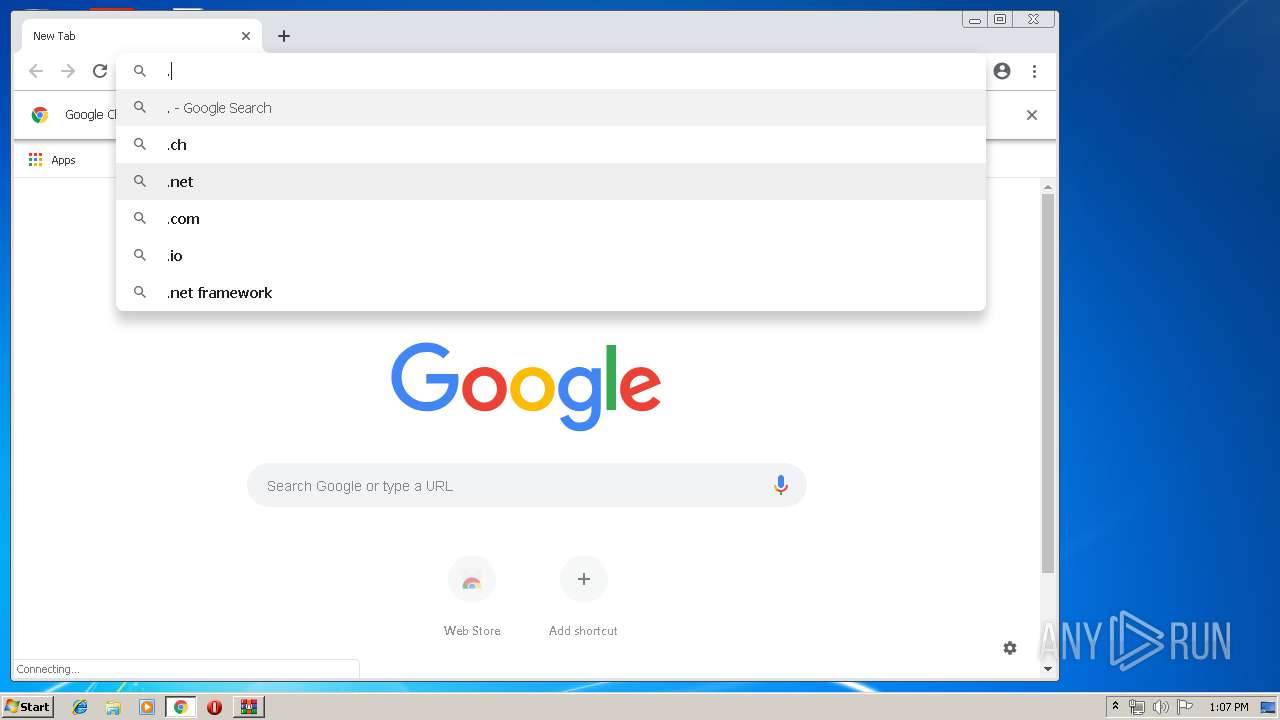
Application launched itself
- chrome.exe (PID: 3412)
Reads settings of System Certificates
- chrome.exe (PID: 3412)
- Setup.exe (PID: 1520)
Dropped object may contain Bitcoin addresses
- Setup.exe (PID: 1520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2019:04:12 17:10:04 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | WARZONE RAT 1.89/ |
Total processes
64
Monitored processes
31
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,2106496114235477589,10289511864880550475,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10586579931966814462 --mojo-platform-channel-handle=4288 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,2106496114235477589,10289511864880550475,131072 --enable-features=PasswordImport --service-pipe-token=3937949531594119849 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3937949531594119849 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1840 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,2106496114235477589,10289511864880550475,131072 --enable-features=PasswordImport --service-pipe-token=12276434331534927883 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12276434331534927883 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1996 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,2106496114235477589,10289511864880550475,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=823552932672923233 --mojo-platform-channel-handle=4752 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6d570f18,0x6d570f28,0x6d570f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,2106496114235477589,10289511864880550475,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=669525766027470659 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=669525766027470659 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1932 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,2106496114235477589,10289511864880550475,131072 --enable-features=PasswordImport --service-pipe-token=17595325443095297589 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17595325443095297589 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1964 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
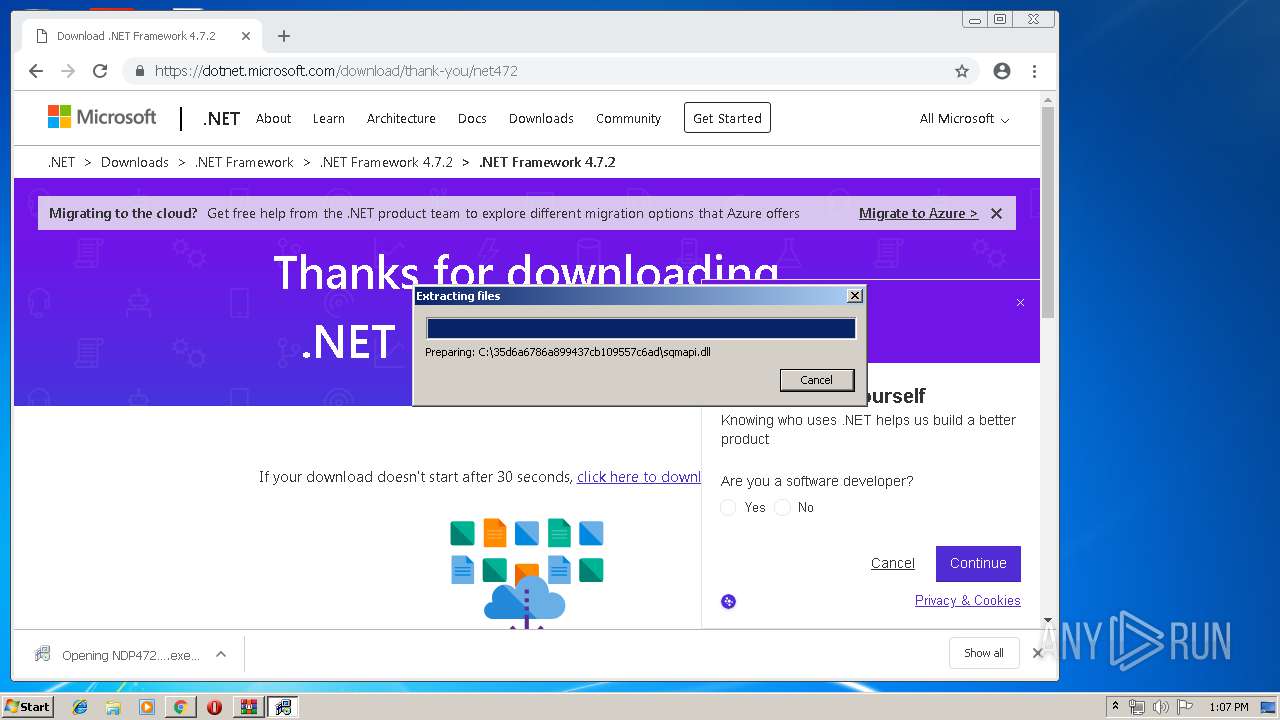
| 1364 | SetupUtility.exe /screboot | C:\35d6a6786a899437cb109557c6ad\SetupUtility.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4.5 Setup Exit code: 0 Version: 14.7.3081.0 built by: NET472REL1 Modules
| |||||||||||||||
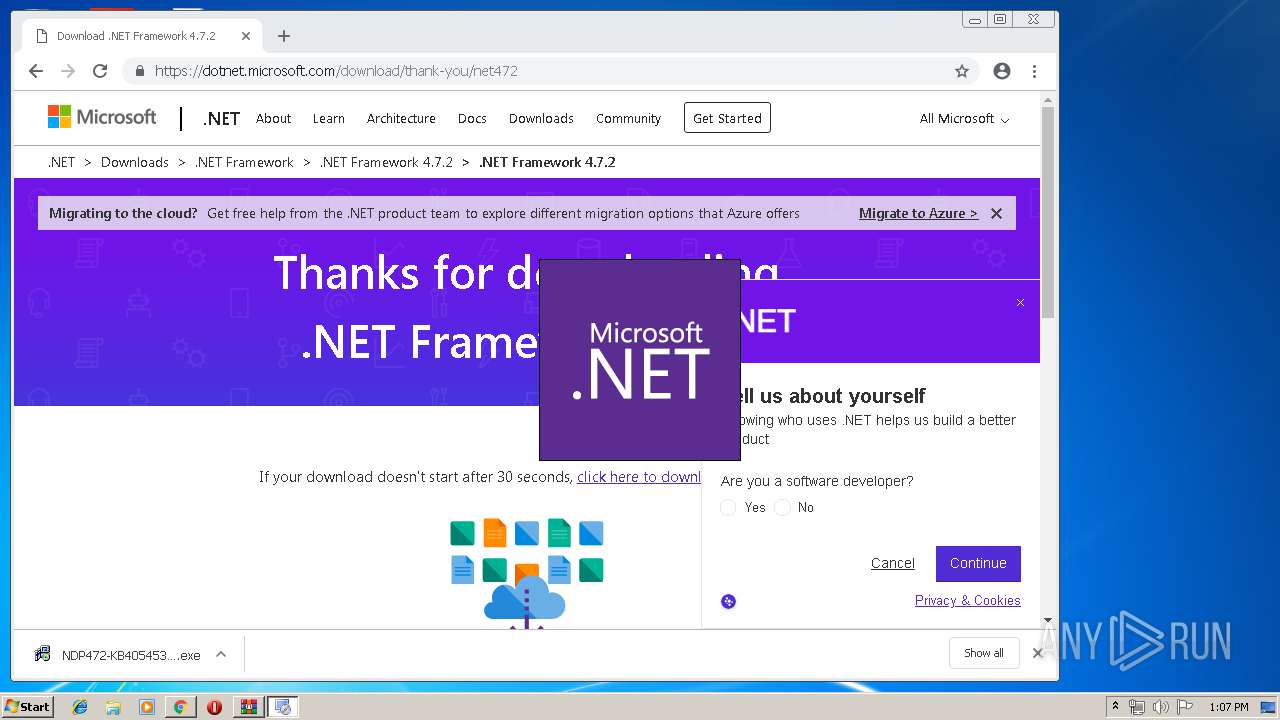
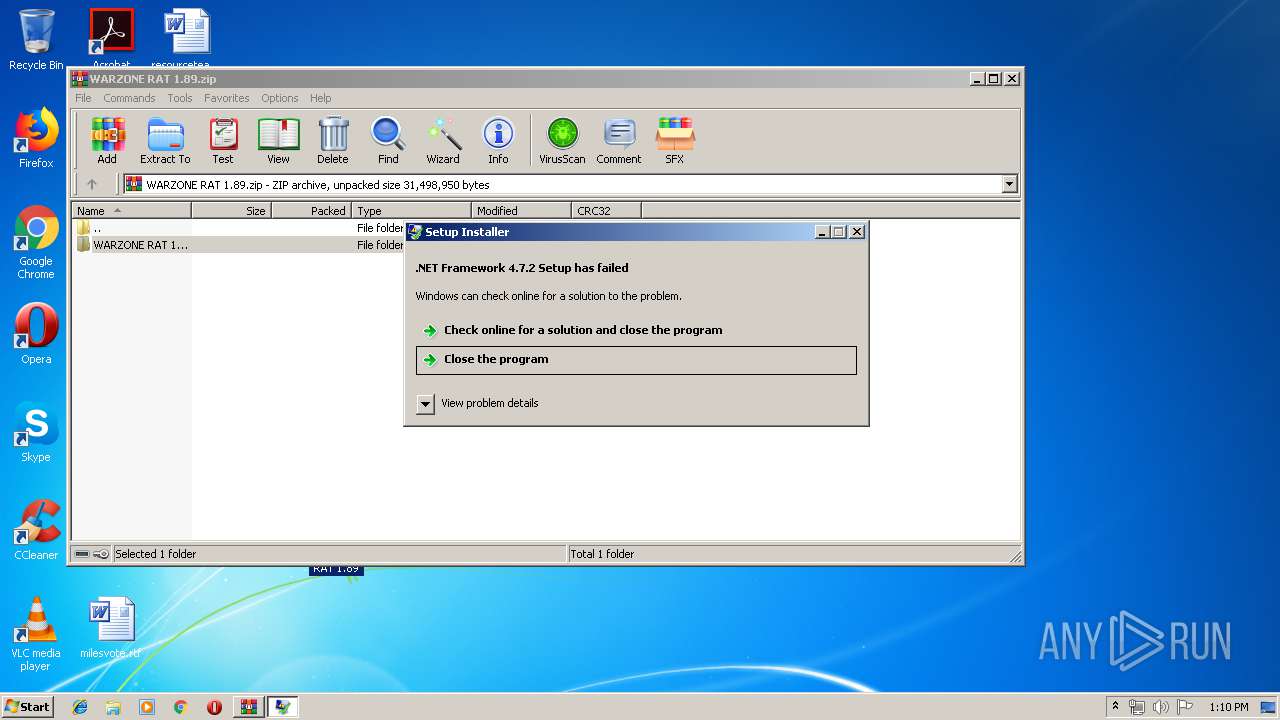
| 1520 | C:\35d6a6786a899437cb109557c6ad\\Setup.exe /x86 /x64 /web | C:\35d6a6786a899437cb109557c6ad\Setup.exe | NDP472-KB4054531-Web.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Setup Installer Exit code: 2148204547 Version: 14.7.3081.0 built by: NET472REL1 Modules
| |||||||||||||||
| 1660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,2106496114235477589,10289511864880550475,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7038659847785579155 --mojo-platform-channel-handle=2732 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
1 942
Read events
1 786
Write events
145
Delete events
11
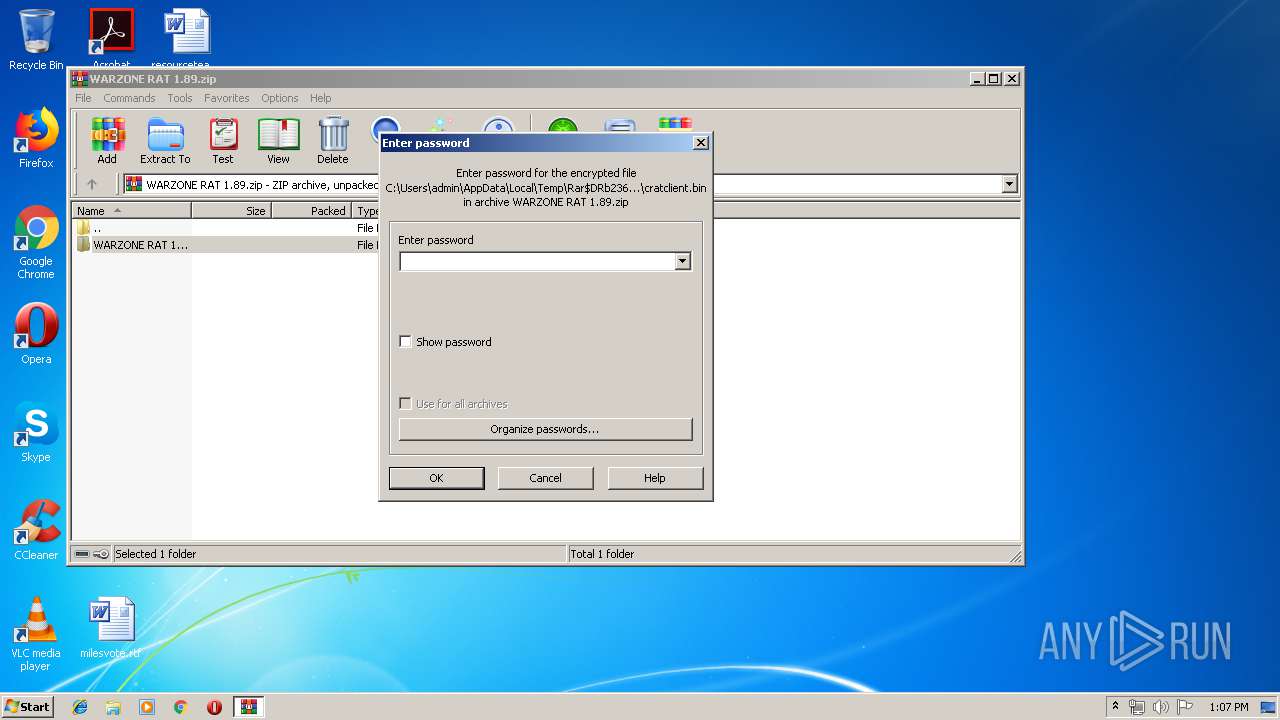
Modification events
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\WARZONE RAT 1.89.zip | |||
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
Executable files
42
Suspicious files
101
Text files
263
Unknown types
17
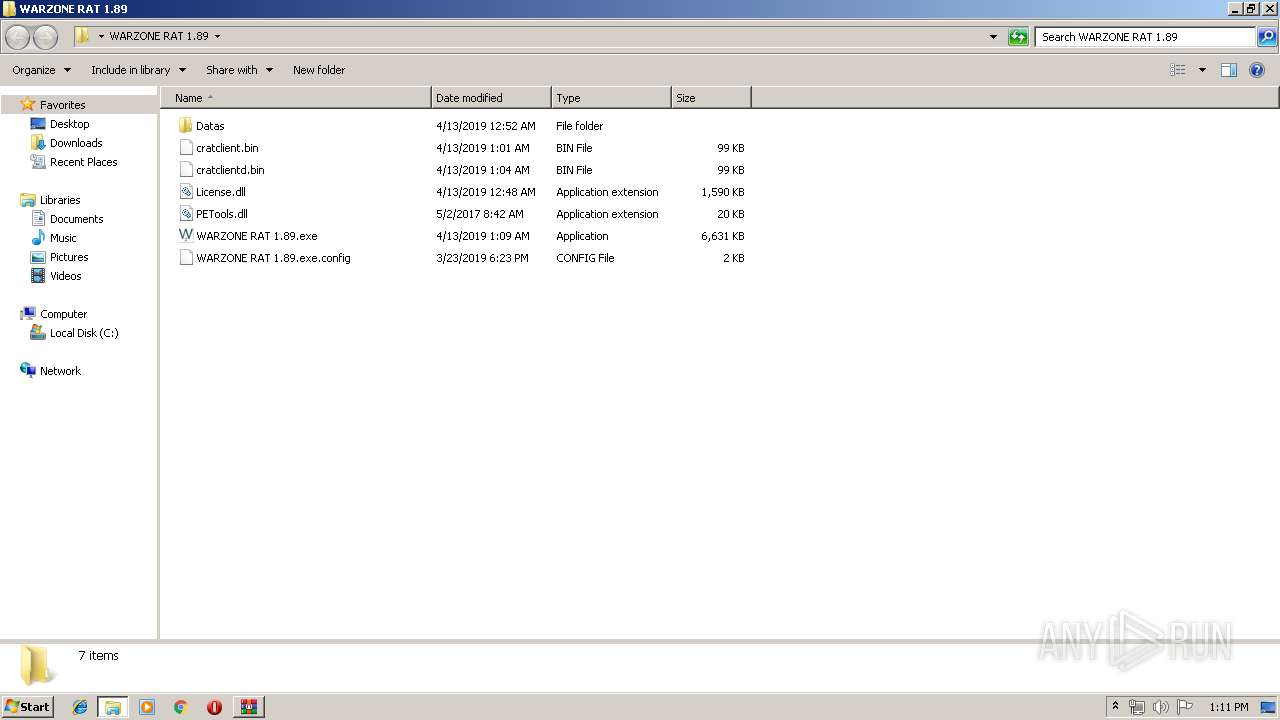
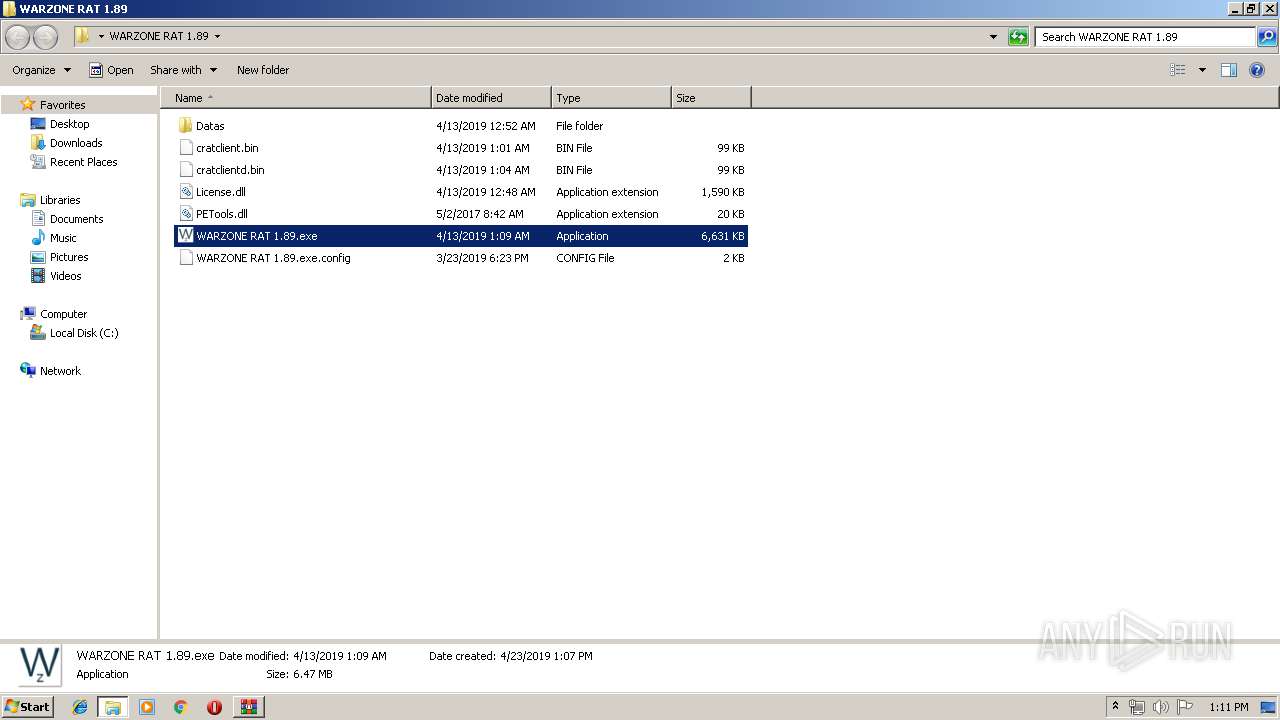
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2364 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2364.22167\WARZONE RAT 1.89\Datas\vncviewer.exe | — | |
MD5:— | SHA256:— | |||
| 2364 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2364.22167\WARZONE RAT 1.89\License.dll | — | |
MD5:— | SHA256:— | |||
| 2364 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2364.22167\WARZONE RAT 1.89\PETools.dll | — | |
MD5:— | SHA256:— | |||
| 2364 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2364.22167\WARZONE RAT 1.89\WARZONE RAT 1.89.exe | — | |
MD5:— | SHA256:— | |||
| 2364 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2364.22167\WARZONE RAT 1.89\WARZONE RAT 1.89.exe.config | — | |
MD5:— | SHA256:— | |||
| 3412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
61
DNS requests
48
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
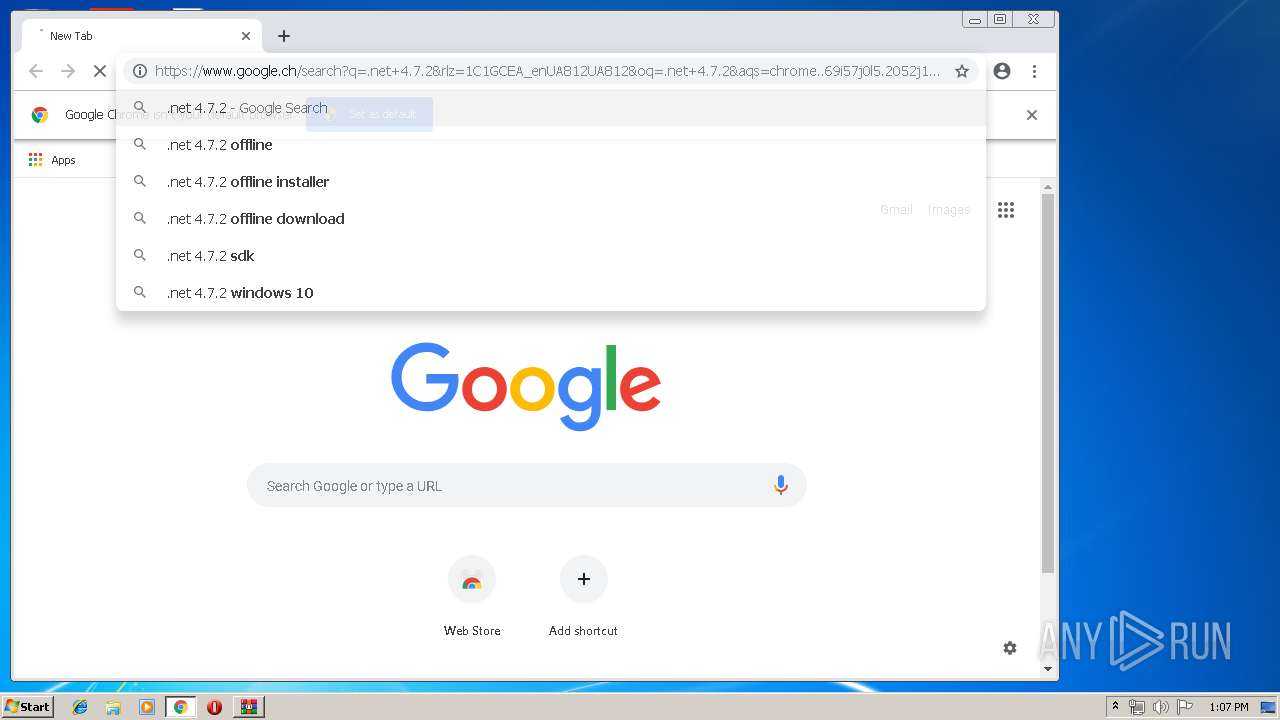
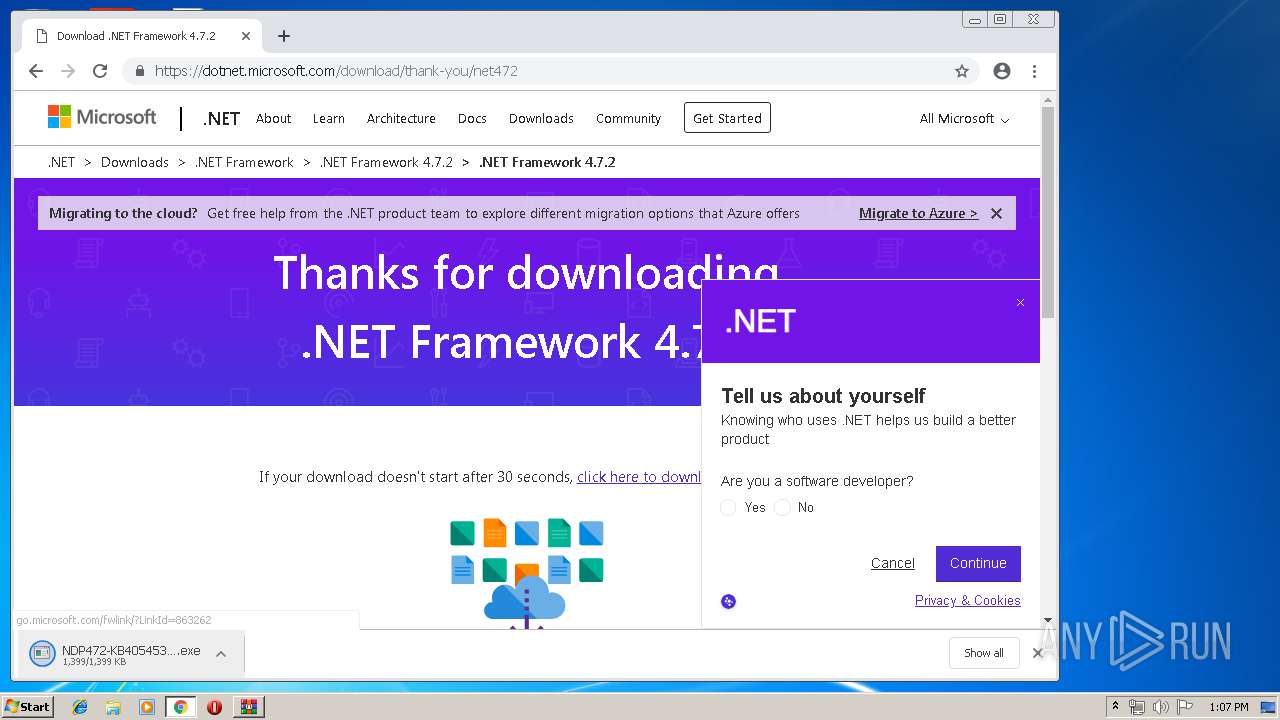
— | — | GET | 302 | 172.227.168.22:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net472Rel1&plcid=0x409&clcid=0x409&ar=03062.00&sar=x86&o1=netfx_Full.mzz | US | — | — | whitelisted |
— | — | GET | 302 | 172.227.168.22:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net472Rel1&plcid=0x409&clcid=0x409&ar=03062.00&sar=amd64&o1=netfx_Full_x86.msi | US | — | — | whitelisted |
— | — | HEAD | 302 | 172.227.168.22:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net472Rel1&plcid=0x409&clcid=0x409&ar=03062.00&sar=x86&o1=netfx_Full.mzz | US | — | — | whitelisted |
— | — | HEAD | 302 | 172.227.168.22:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net472Rel1&plcid=0x409&clcid=0x409&ar=03062.00&sar=amd64&o1=netfx_Full_x86.msi | US | — | — | whitelisted |
— | — | GET | 302 | 172.227.168.22:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net472Rel1&plcid=0x409&clcid=0x409&ar=03081.00&sar=amd64&o1=netfx_Patch_x86.msp | US | — | — | whitelisted |
1520 | Setup.exe | GET | 302 | 104.109.80.115:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net472Rel1&plcid=0x409&clcid=0x409&ar=03081.00&sar=amd64&o1=netfx_Patch_x86.msp | NL | — | — | whitelisted |
— | — | HEAD | 302 | 172.227.168.22:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net472Rel1&plcid=0x409&clcid=0x409&ar=03081.00&sar=amd64&o1=netfx_Patch_x86.msp | US | — | — | whitelisted |
1520 | Setup.exe | GET | 302 | 104.109.80.115:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net472Rel1&plcid=0x409&clcid=0x409&ar=03081.00&sar=amd64&o1=netfx_Patch_x86.msp | NL | — | — | whitelisted |
1520 | Setup.exe | GET | 302 | 104.109.80.115:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net472Rel1&plcid=0x409&clcid=0x409&ar=03081.00&sar=amd64&o1=netfx_Patch_x86.msp | NL | — | — | whitelisted |
— | — | HEAD | 302 | 172.227.168.22:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net472Rel1&plcid=0x409&clcid=0x409&ar=03081.00&sar=amd64&o1=netfx_Patch_x86.msp | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3412 | chrome.exe | 172.217.21.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3412 | chrome.exe | 216.58.210.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
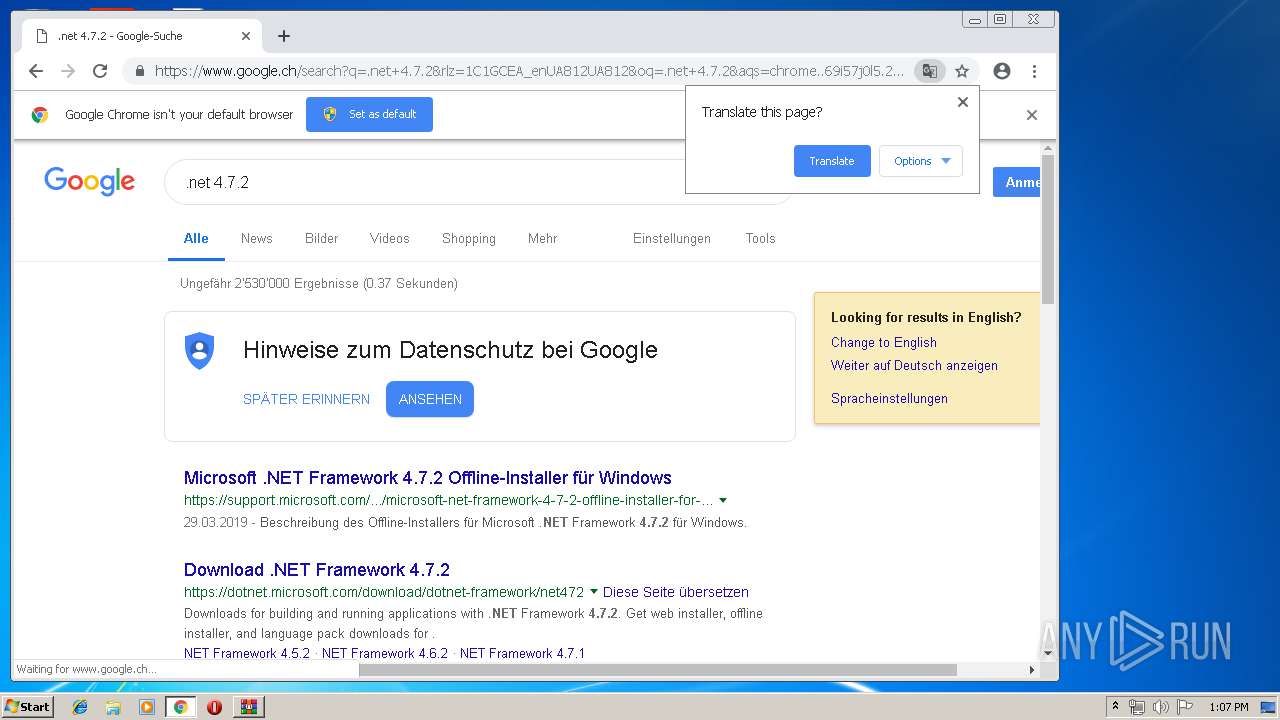
3412 | chrome.exe | 172.217.16.196:443 | www.google.com | Google Inc. | US | whitelisted |
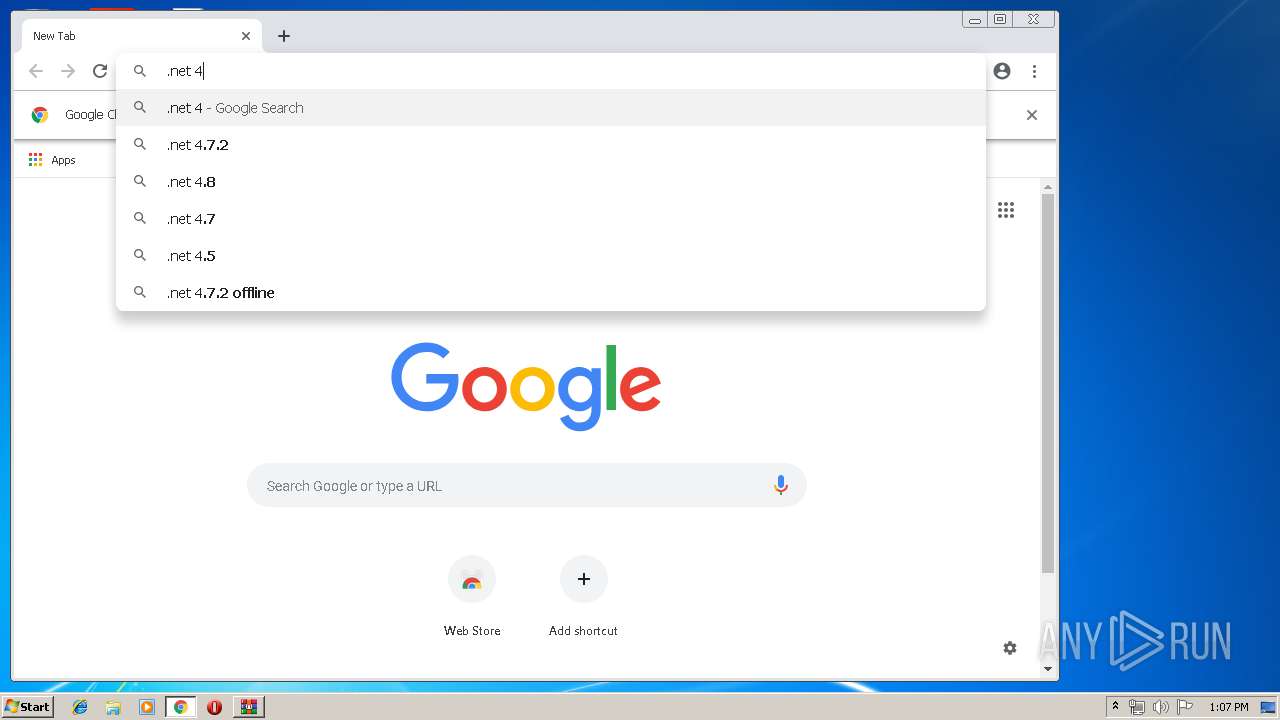
3412 | chrome.exe | 172.217.18.99:443 | www.google.ch | Google Inc. | US | whitelisted |
3412 | chrome.exe | 172.217.21.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3412 | chrome.exe | 172.217.16.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3412 | chrome.exe | 216.58.206.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3412 | chrome.exe | 172.217.22.98:443 | adservice.google.ch | Google Inc. | US | whitelisted |
3412 | chrome.exe | 172.217.22.34:443 | adservice.google.com | Google Inc. | US | whitelisted |
3412 | chrome.exe | 52.160.40.218:443 | dotnet.microsoft.com | Microsoft Corporation | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
www.google.ch |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Setup.exe | The form specified for the subject is not one supported or known by the specified trust provider.
|
Setup.exe | The form specified for the subject is not one supported or known by the specified trust provider.
|