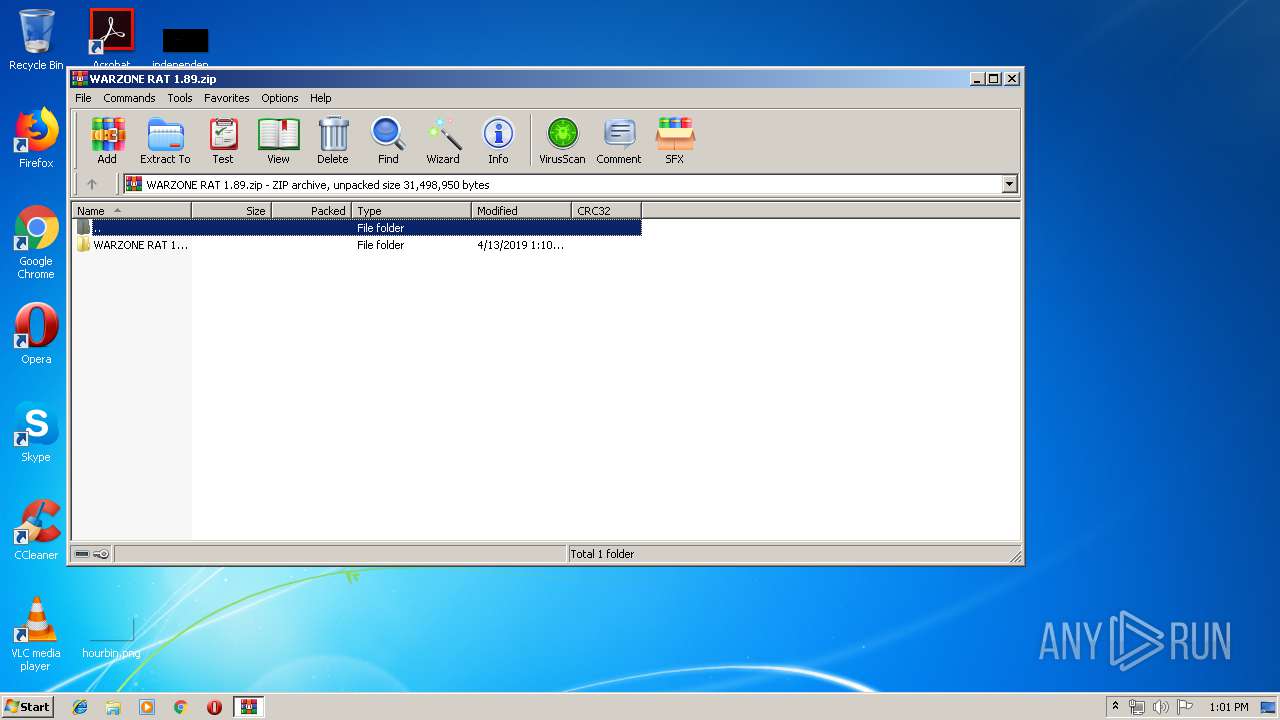
| File name: | WARZONE RAT 1.89.zip |
| Full analysis: | https://app.any.run/tasks/dba2b730-2658-4382-8a50-6e11ea9a8945 |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 12:01:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | DACE5E510A5868CF8A19E53F8AE06C2F |
| SHA1: | D6806589691F51AC14FDE665F9EBBDA56AC6945F |
| SHA256: | 6998346F222A1B82CCB88645F8B8D159B7EB476C076EF7A18C1606F2D2BBCE08 |
| SSDEEP: | 393216:IFKfp6uNojFncU4SlLbO2Ts2VMMcGZVR4Oph8skg0Eejch5P7OK:IGVCjFnccm05VMmZF8szhejy5yK |
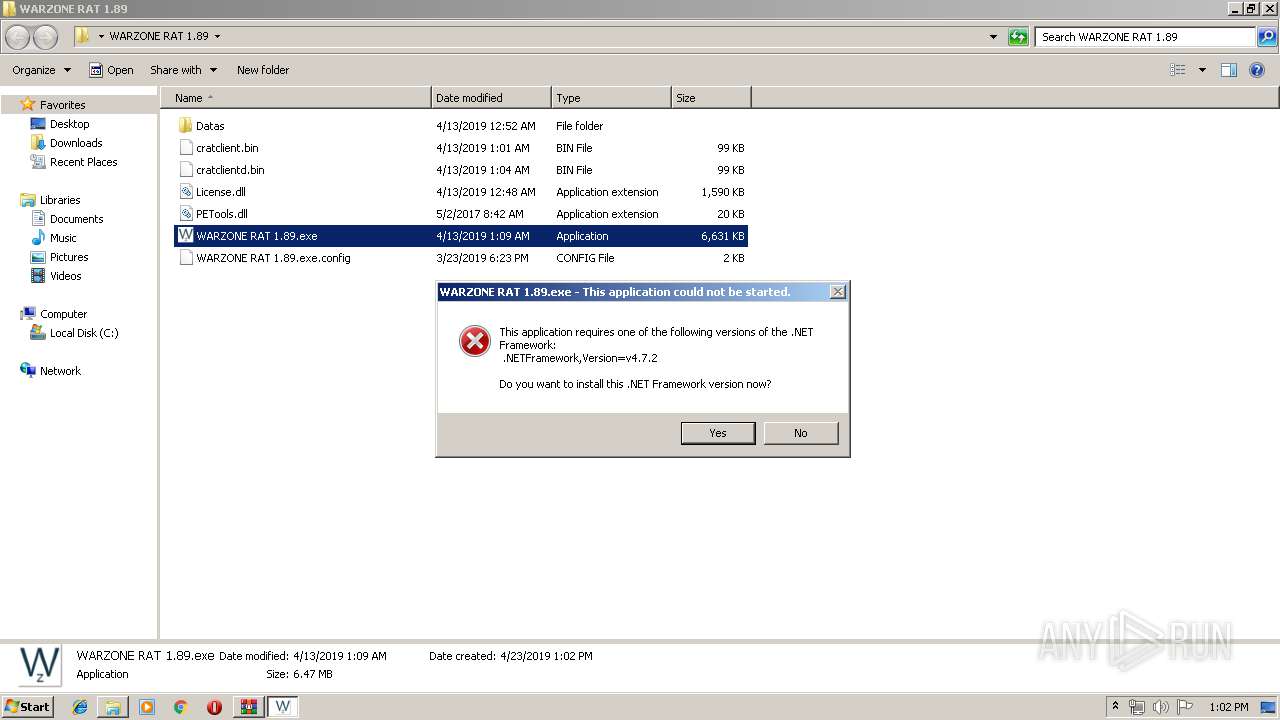
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3896)
SUSPICIOUS
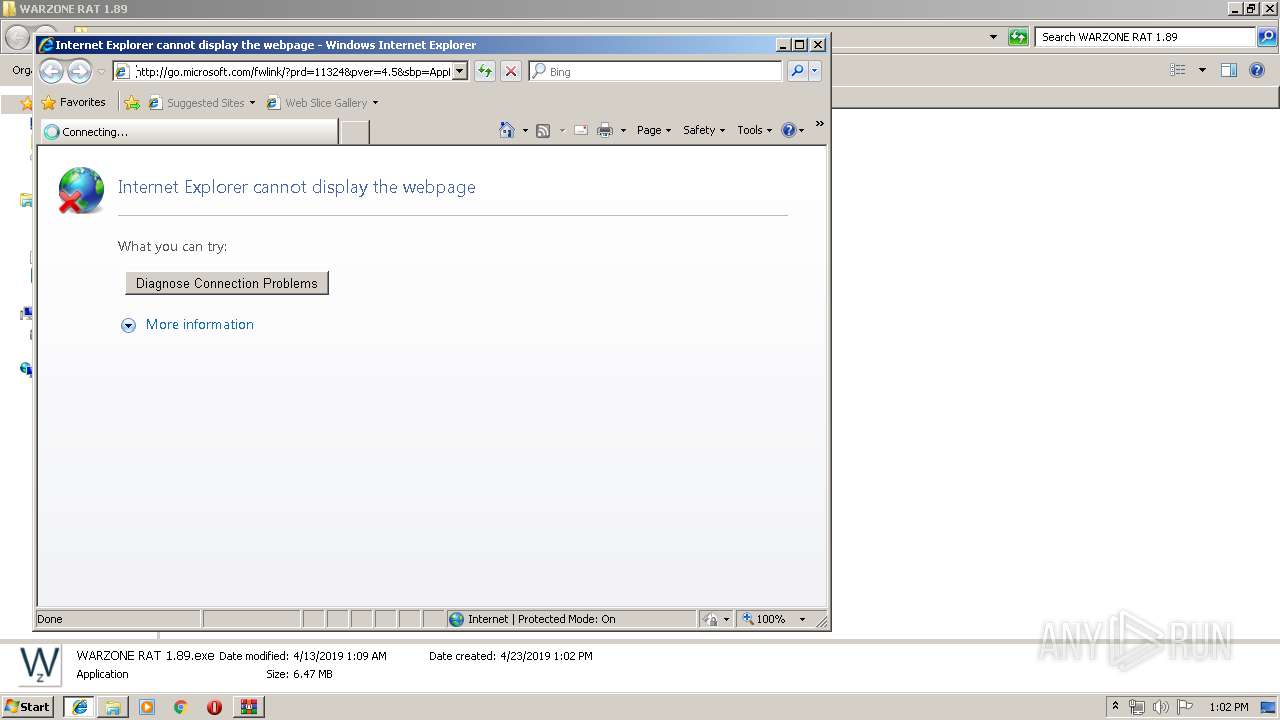
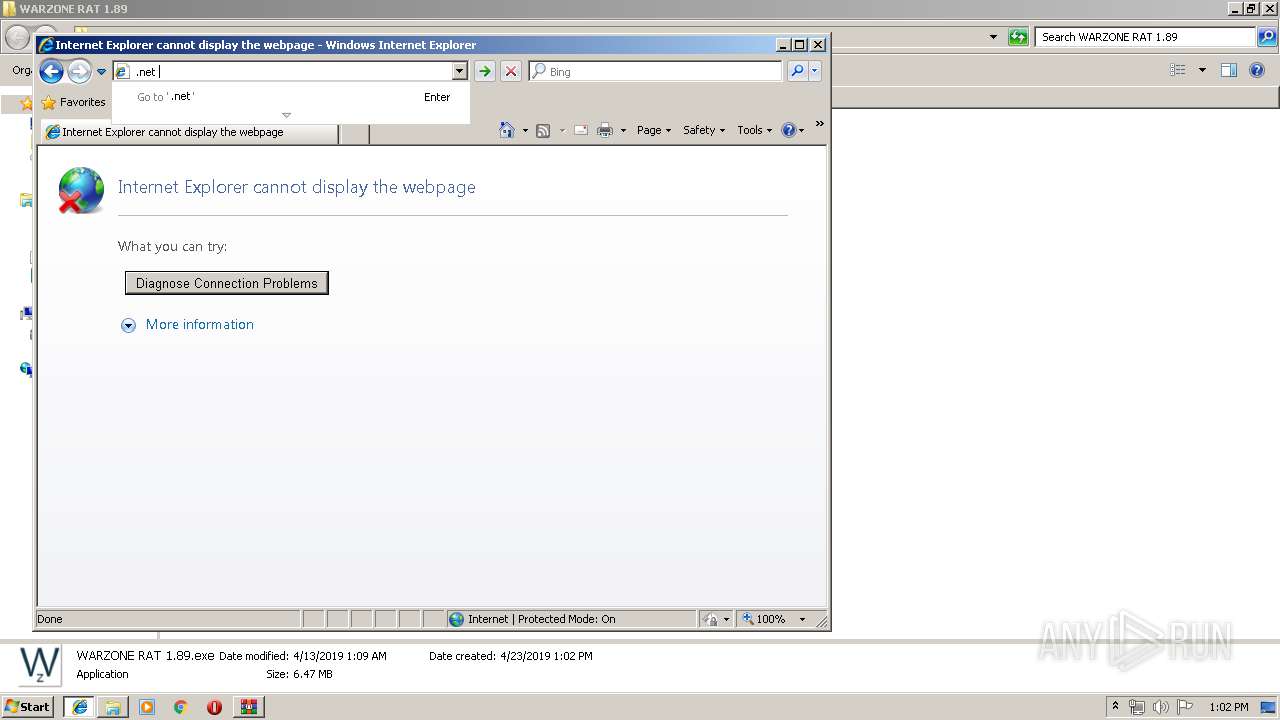
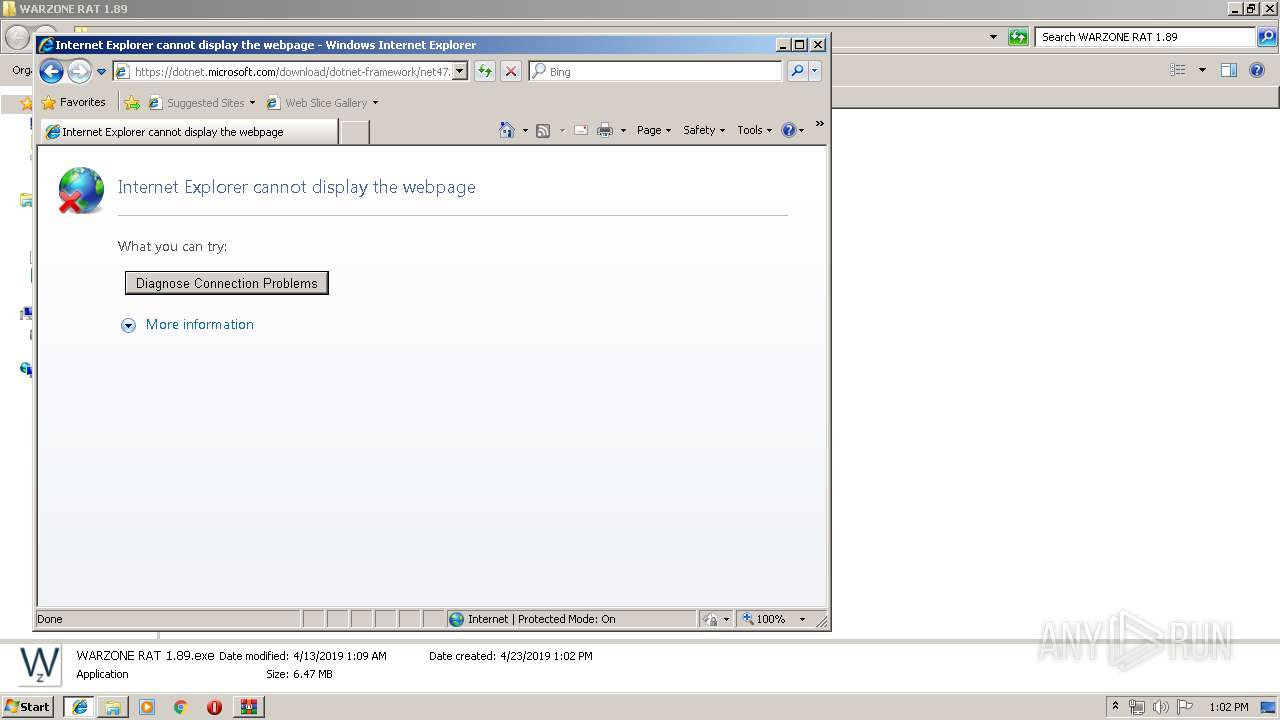
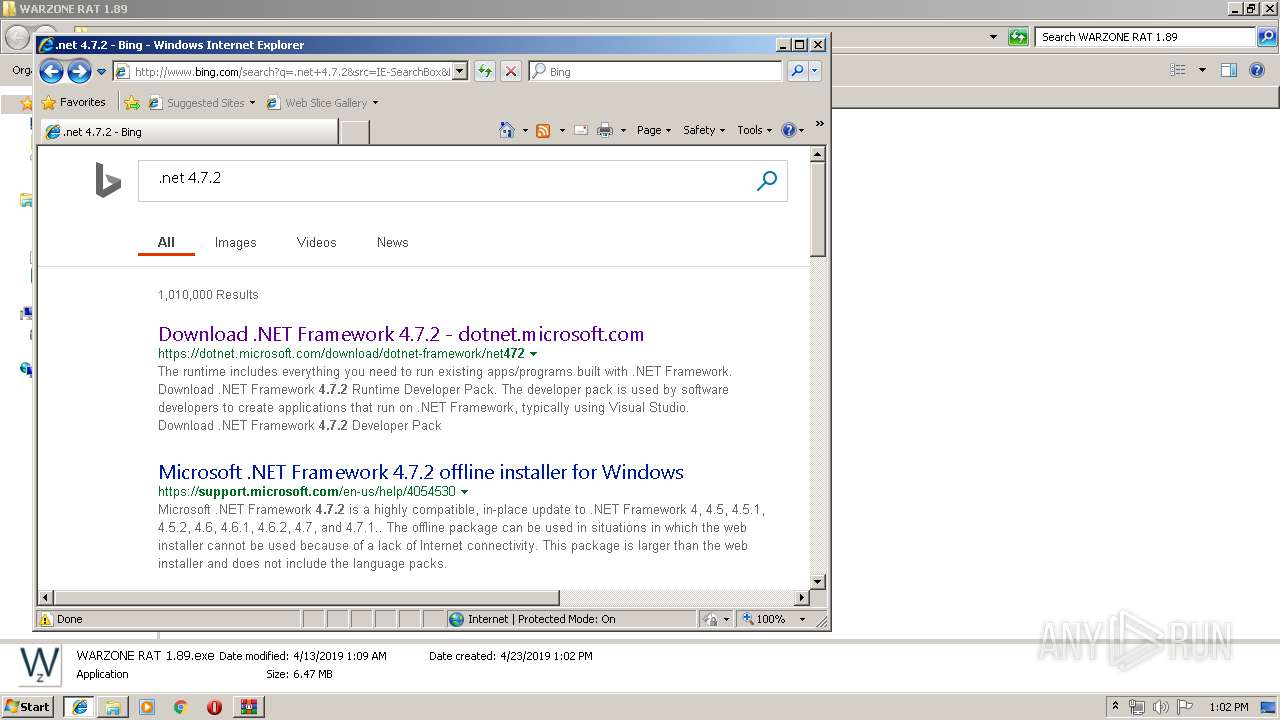
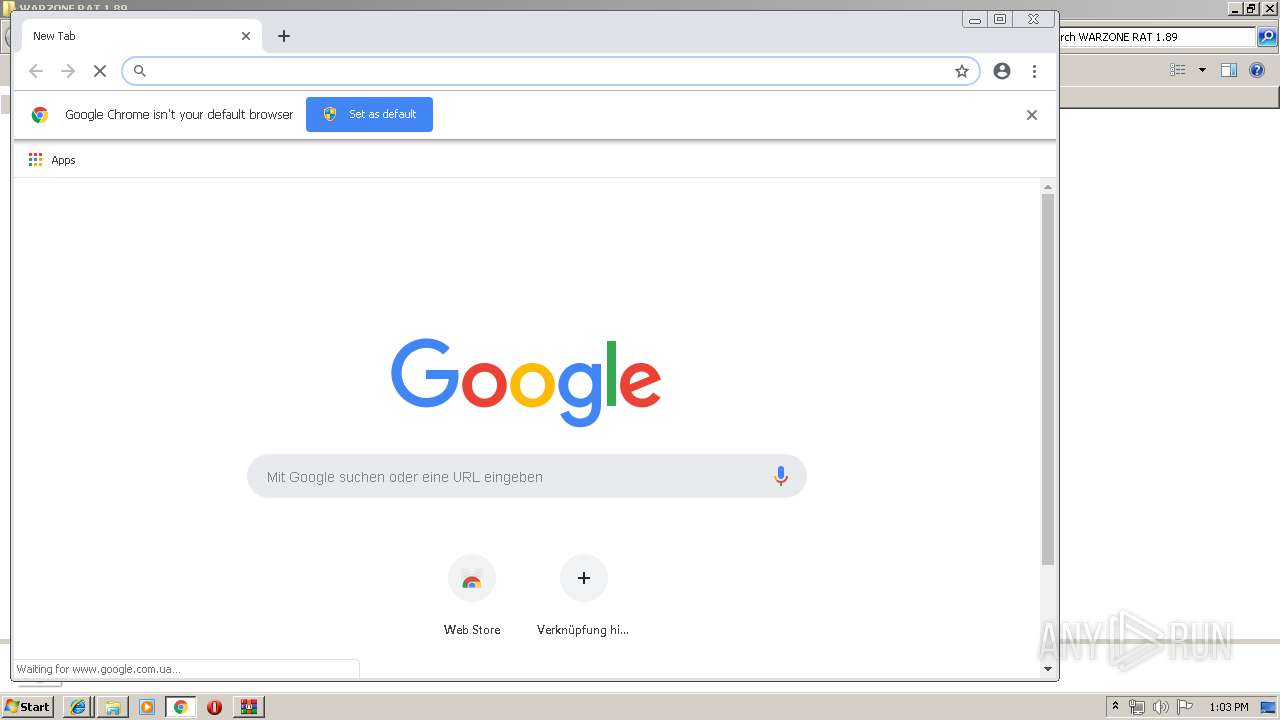
Starts Internet Explorer
- WARZONE RAT 1.89.exe (PID: 3232)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2960)
- chrome.exe (PID: 2168)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2168)
INFO
Application launched itself
- iexplore.exe (PID: 2716)
- chrome.exe (PID: 2168)
Creates files in the user directory
- iexplore.exe (PID: 3012)
- iexplore.exe (PID: 3604)
Changes internet zones settings
- iexplore.exe (PID: 2716)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3012)
Reads Internet Cache Settings
- iexplore.exe (PID: 3604)
- iexplore.exe (PID: 3012)
Reads internet explorer settings
- iexplore.exe (PID: 3012)
- iexplore.exe (PID: 3604)
Reads settings of System Certificates
- iexplore.exe (PID: 3012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2019:04:12 17:10:04 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | WARZONE RAT 1.89/ |
Total processes
64
Monitored processes
30
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,14914790123563892350,985098277853863837,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=18026591470527047617 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18026591470527047617 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4404 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,14914790123563892350,985098277853863837,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=11729406300526817830 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11729406300526817830 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3568 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,14914790123563892350,985098277853863837,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3862398527622339954 --mojo-platform-channel-handle=2248 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,14914790123563892350,985098277853863837,131072 --enable-features=PasswordImport --service-pipe-token=8989796831859897944 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8989796831859897944 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2124 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=960,14914790123563892350,985098277853863837,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7381565966435063550 --mojo-platform-channel-handle=4308 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,14914790123563892350,985098277853863837,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13582389893665295784 --mojo-platform-channel-handle=464 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,14914790123563892350,985098277853863837,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14374441074752798840 --mojo-platform-channel-handle=4712 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=960,14914790123563892350,985098277853863837,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4868864138435964157 --mojo-platform-channel-handle=980 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,14914790123563892350,985098277853863837,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=2407489424792303619 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2407489424792303619 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2624 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
1 985
Read events
1 783
Write events
196
Delete events
6
Modification events
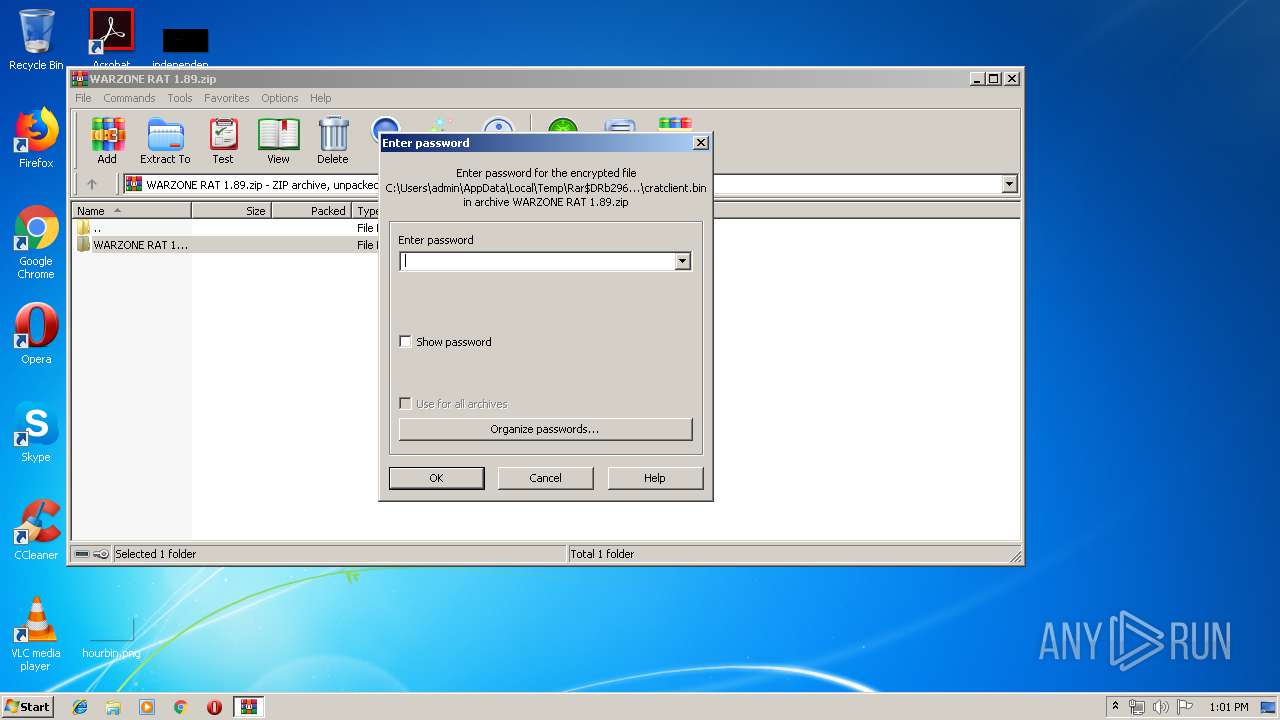
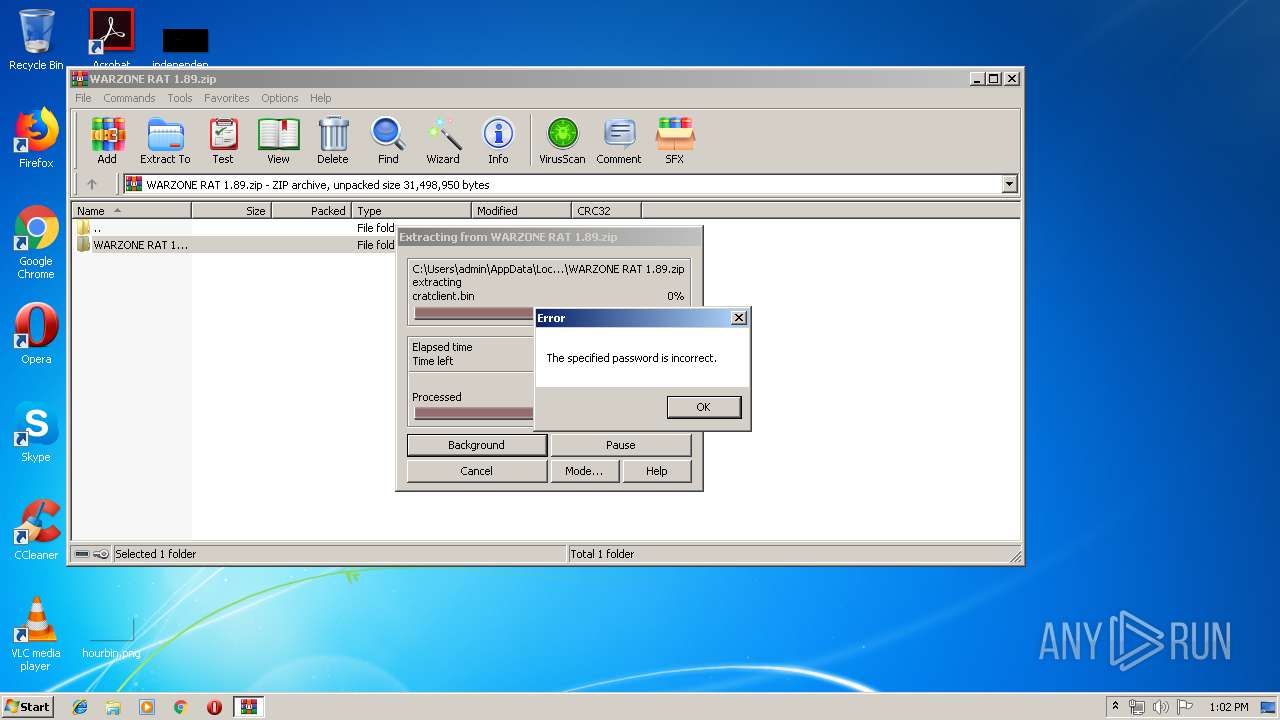
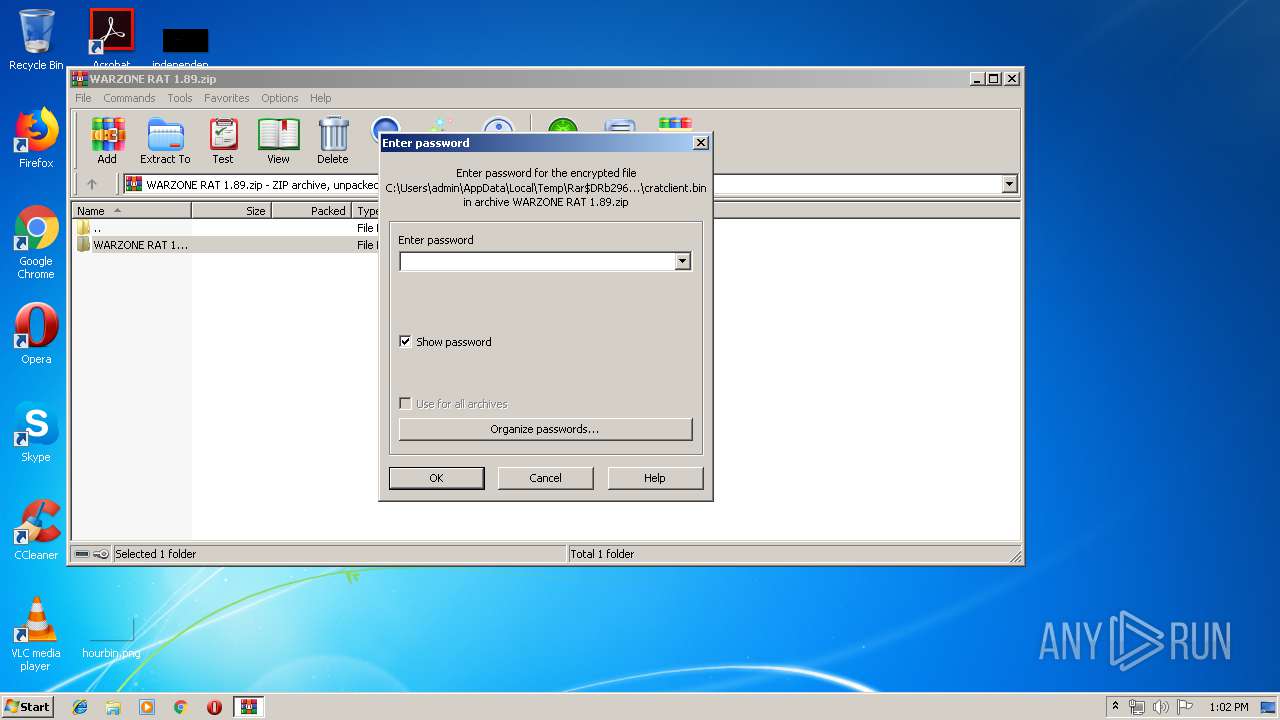
| (PID) Process: | (2960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2960) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\WARZONE RAT 1.89.zip | |||
| (PID) Process: | (2960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
| (PID) Process: | (2716) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
Executable files
5
Suspicious files
100
Text files
231
Unknown types
13
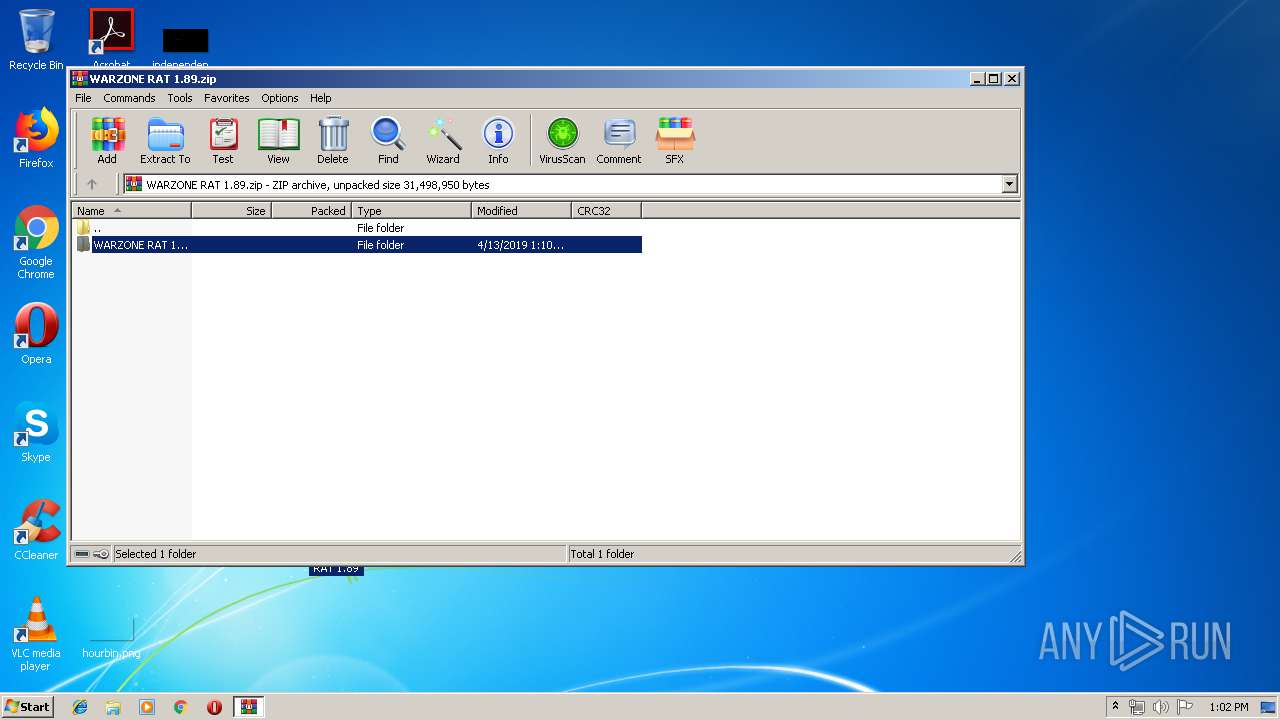
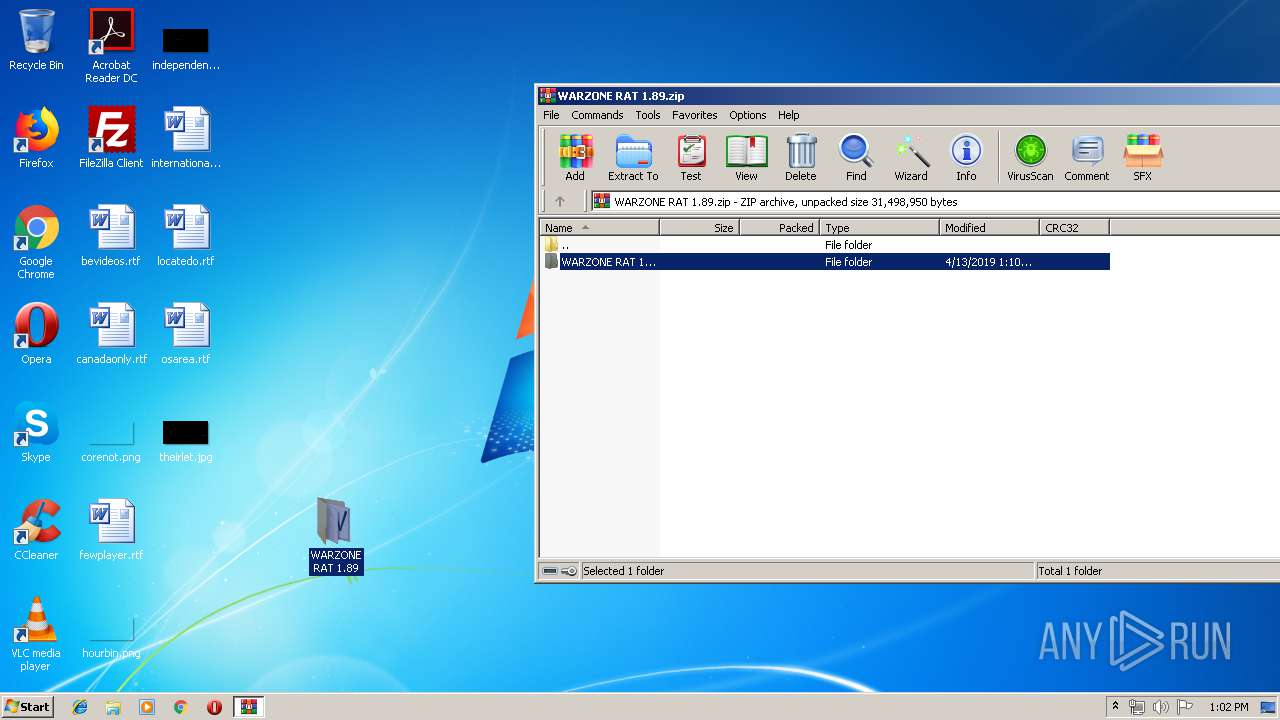
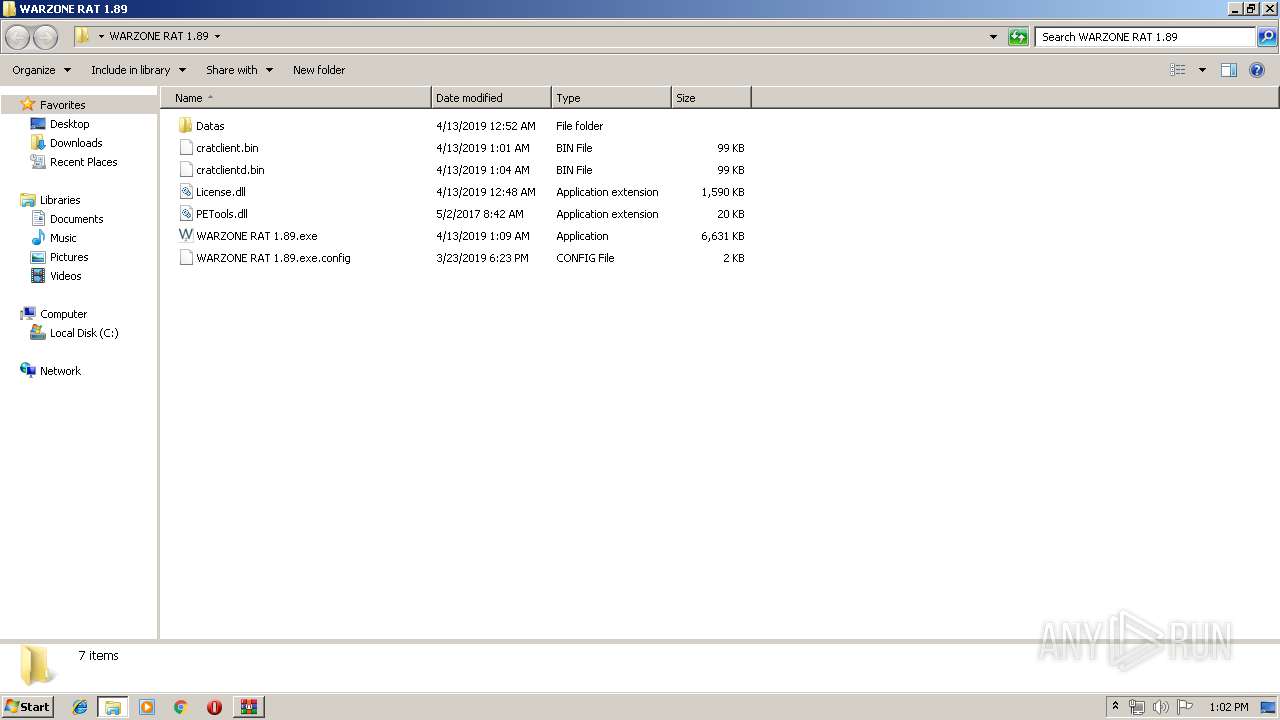
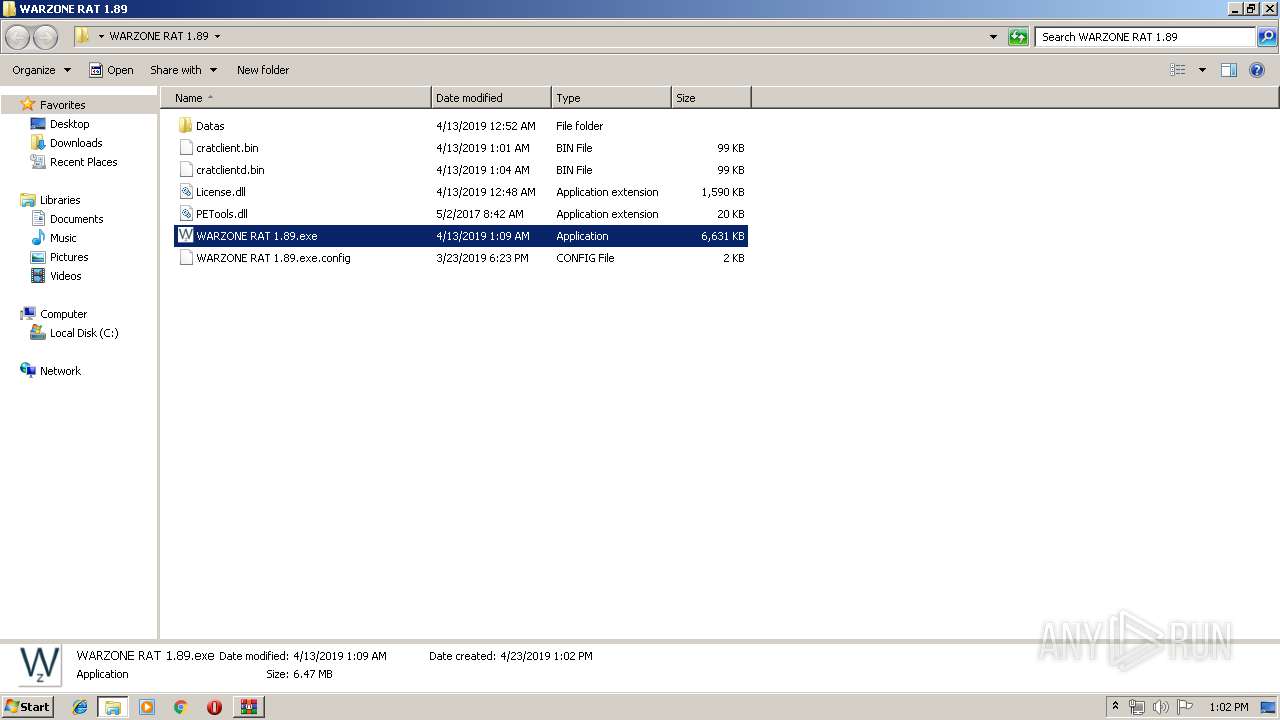
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2960 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2960.41475\WARZONE RAT 1.89\Datas\rV.bsp1 | — | |
MD5:— | SHA256:— | |||
| 2960 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2960.41475\WARZONE RAT 1.89\Datas\rvncviewer.exe | — | |
MD5:— | SHA256:— | |||
| 2960 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2960.41475\WARZONE RAT 1.89\Datas\ServerManager.dll | — | |
MD5:— | SHA256:— | |||
| 2960 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2960.41475\WARZONE RAT 1.89\Datas\SocksManager.exe | — | |
MD5:— | SHA256:— | |||
| 2960 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2960.41475\WARZONE RAT 1.89\Datas\sqlite3.dll | — | |
MD5:— | SHA256:— | |||
| 2960 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2960.41475\WARZONE RAT 1.89\Datas\tvnviewer.exe | — | |
MD5:— | SHA256:— | |||
| 2960 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2960.41475\WARZONE RAT 1.89\Datas\vncviewer.exe | — | |
MD5:— | SHA256:— | |||
| 2960 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2960.41475\WARZONE RAT 1.89\License.dll | — | |
MD5:— | SHA256:— | |||
| 2960 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2960.41475\WARZONE RAT 1.89\PETools.dll | — | |
MD5:— | SHA256:— | |||
| 2960 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2960.41475\WARZONE RAT 1.89\WARZONE RAT 1.89.exe | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
95
DNS requests
51
Threats
1
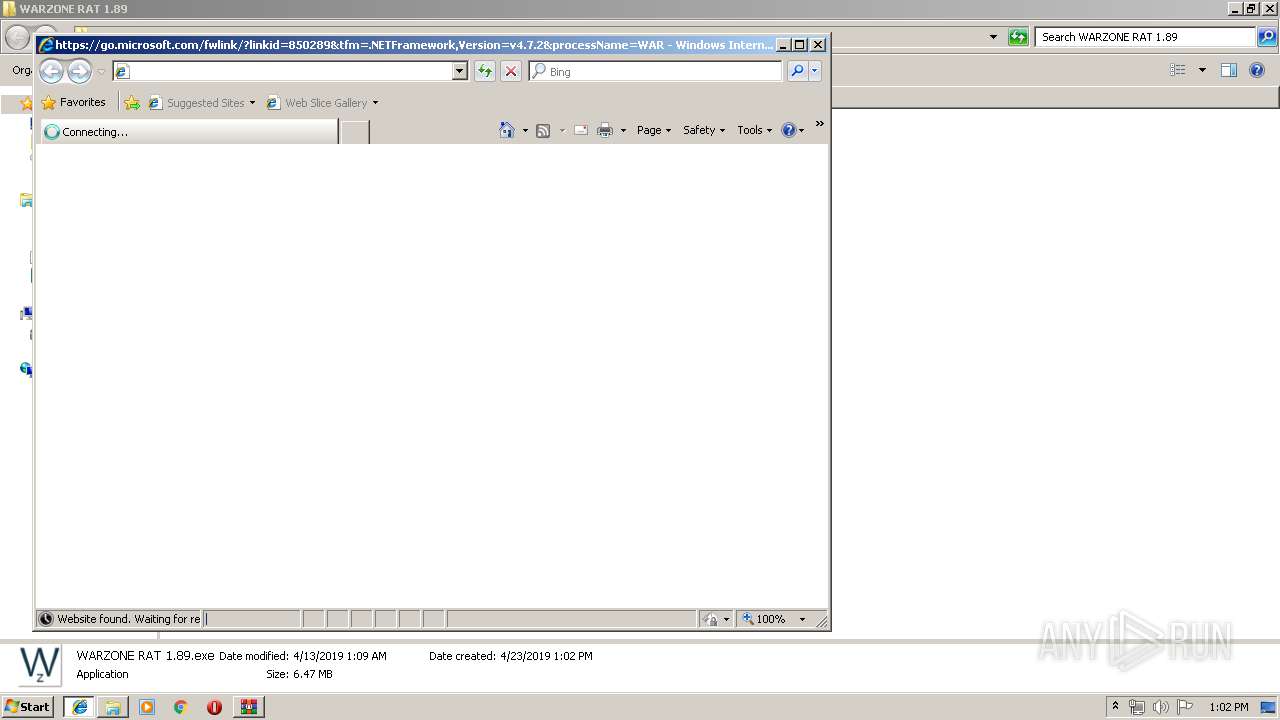
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
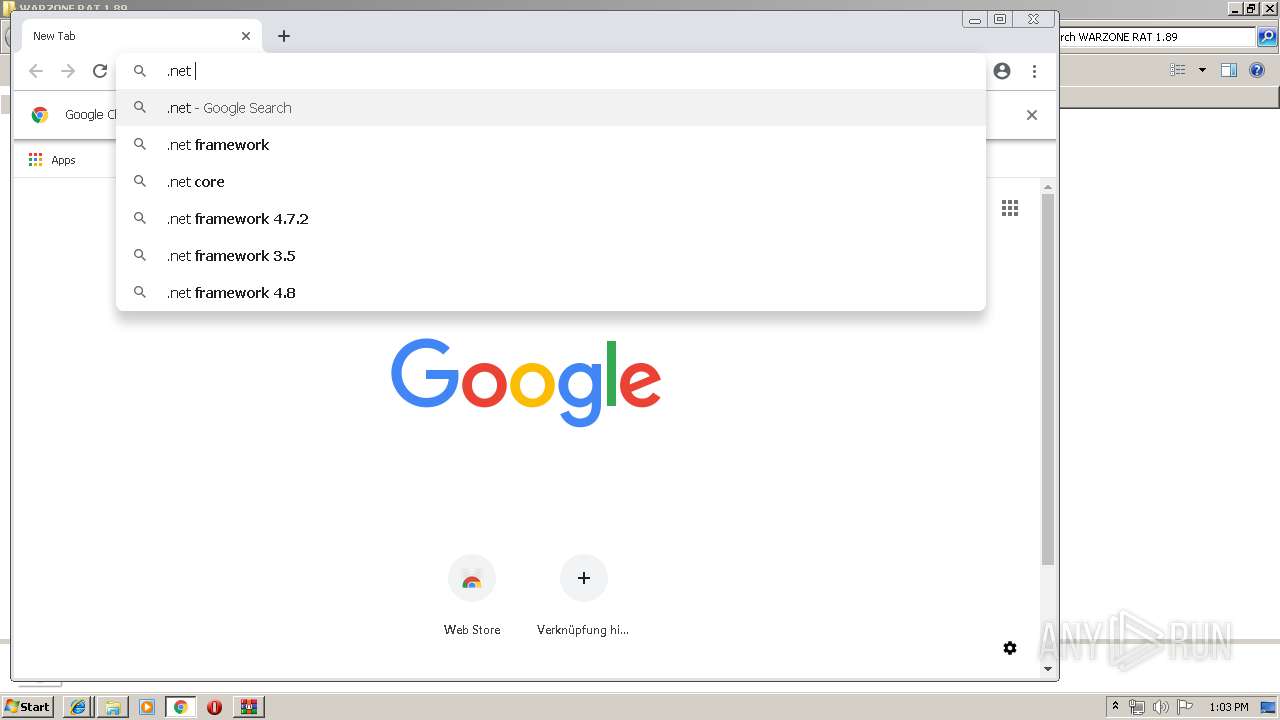
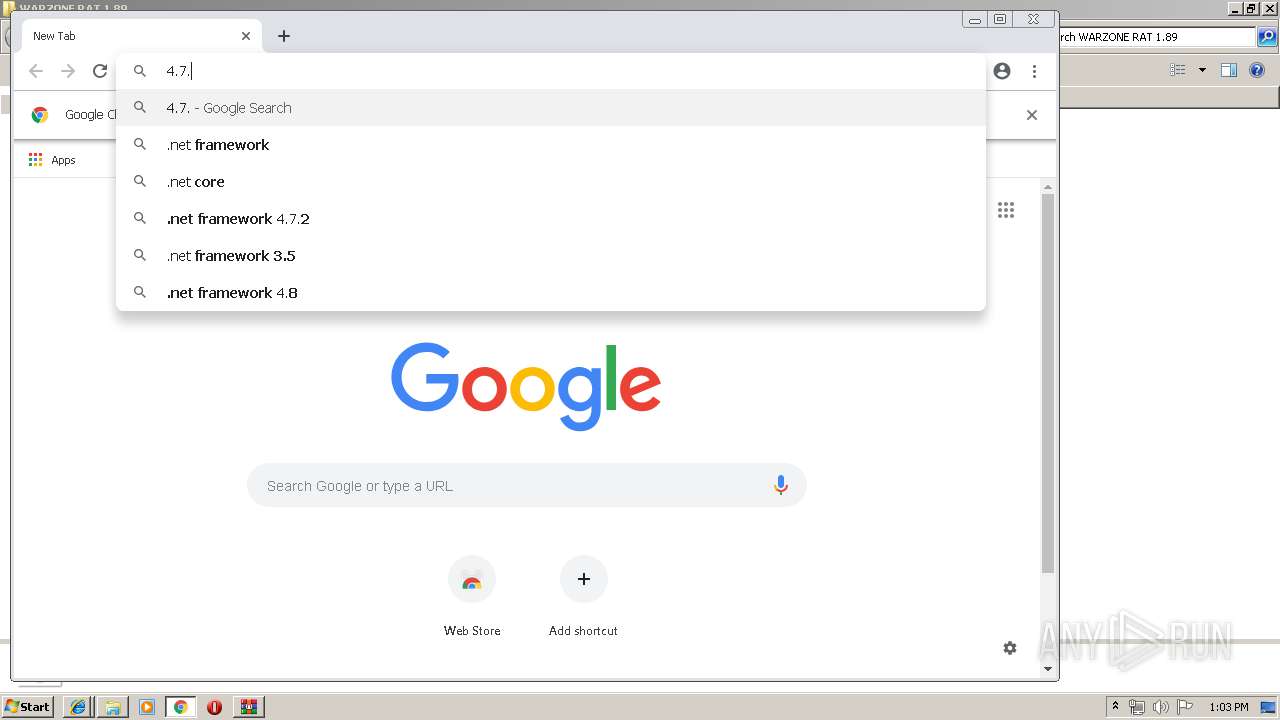
3012 | iexplore.exe | GET | 302 | 172.227.168.22:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=4.5&sbp=AppLaunch&plcid=0x409&o1=.NETFramework,Version=v4.7.2&processName=WARZONE%20RAT%201.89.exe&platform=0000&osver=5&isServer=0&shimver=4.0.30319.0 | US | — | — | whitelisted |
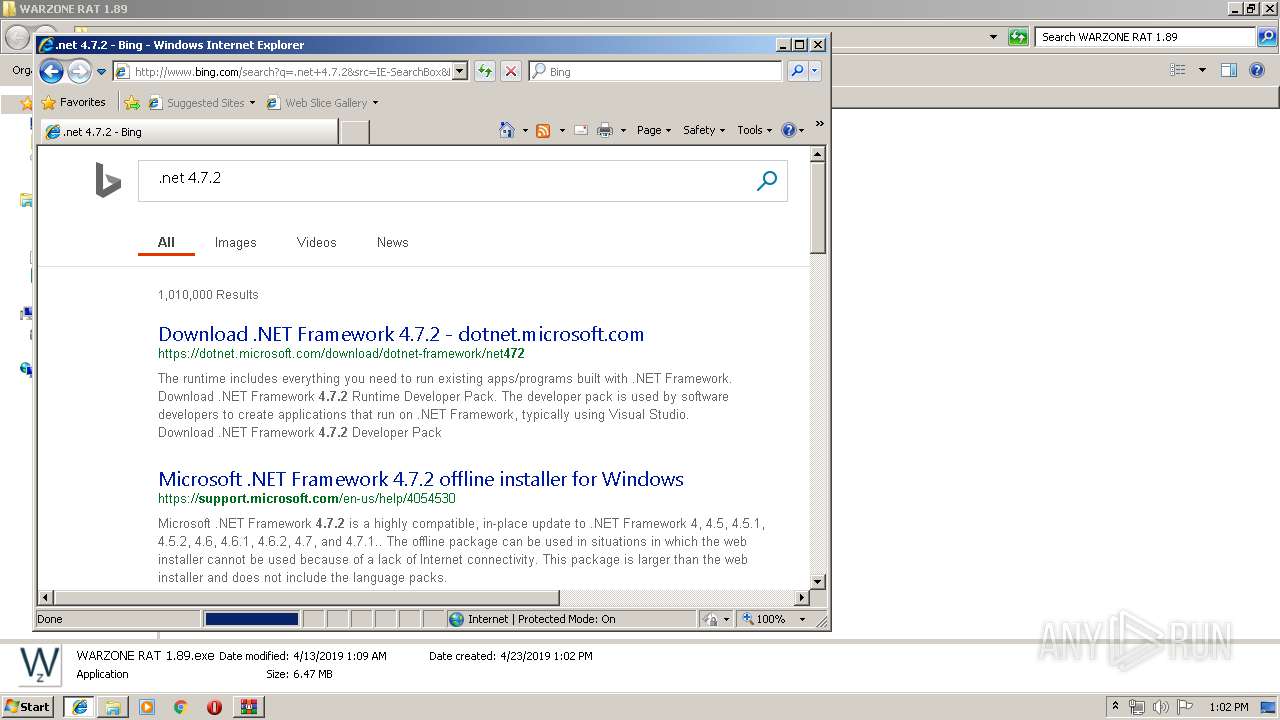
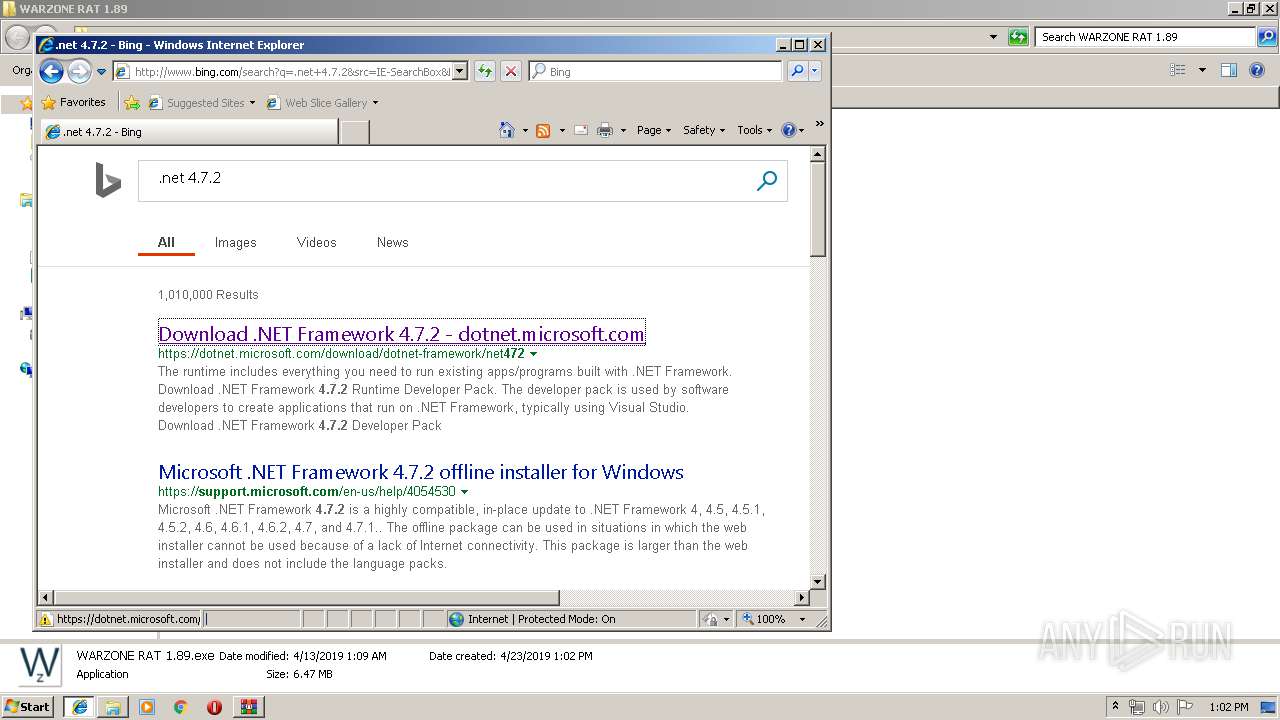
3012 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rb/5q/cj,nj/c44ec255/9a358300.js?bu=Eo0frB_THtge6QTmHugeuB_qHvEe-R6kH6Iflh-HHpEdlB2KHg | US | text | 4.95 Kb | whitelisted |
3012 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/fd/ls/l?IG=9DA537F983A945D69096CB0ED996A82B&CID=257B9FAFE4CF6A96041992E8E5E76B34&Type=Event.ClientInst&DATA=[{"T":"CI.GetError","FID":"CI","Name":"JSGetError","Text":"%27SVGElement%27%20is%20undefined","Meta":"http%3A//www.bing.com/search%3Fq%3D.net+4.7.2%26src%3DIE-SearchBox%26FORM%3DIE8SRC","Line":9264735,"Char":%20undefined}] | US | compressed | 773 b | whitelisted |
3012 | iexplore.exe | GET | 302 | 172.227.168.22:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=4.5&sbp=AppLaunch&plcid=0x409&o1=.NETFramework,Version=v4.7.2&processName=WARZONE%20RAT%201.89.exe&platform=0000&osver=5&isServer.net%204.7.2shimver=4.0.30319.0 | US | — | — | whitelisted |
3012 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/31/1Y/cj,nj/4c7364c5/40e1b425.js | US | text | 816 b | whitelisted |
3012 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/31/1I/cj,nj/3f1e2270/f8c6dd44.js | US | text | 773 b | whitelisted |
3012 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/fd/ls/GLinkPing.aspx?IG=9DA537F983A945D69096CB0ED996A82B&CID=257B9FAFE4CF6A96041992E8E5E76B34&&ID=SERP,5096.1&url=https%3A%2F%2Fdotnet.microsoft.com%2Fdownload%2Fdotnet-framework%2Fnet472 | US | compressed | 816 b | whitelisted |
3012 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/6t/4N/cj,nj/347afee2/33036ea1.js | US | text | 1.77 Kb | whitelisted |
3012 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/sa/simg/SharedSpriteDesktopRewards_022118.png | US | image | 5.73 Kb | whitelisted |
3012 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rb/16/cj,nj/1b7dfb88/cc8437ad.js?bu=DikuXGxwdGhgZKwBsAEuoAEu | US | text | 7.54 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
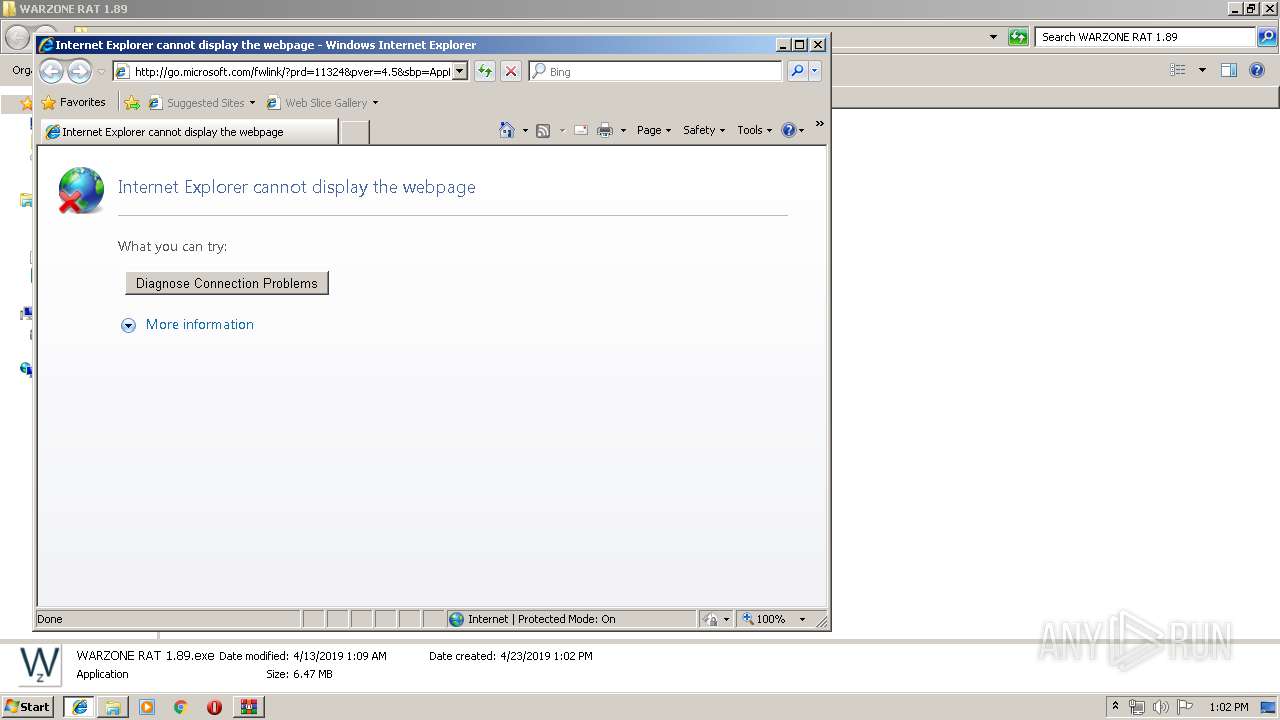
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2716 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3012 | iexplore.exe | 172.227.168.22:80 | go.microsoft.com | Akamai International B.V. | US | whitelisted |
3012 | iexplore.exe | 23.96.207.177:443 | dotnetdownloadservice.azurewebsites.net | Microsoft Corporation | US | whitelisted |
3012 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3012 | iexplore.exe | 65.55.163.78:443 | login.live.com | Microsoft Corporation | US | whitelisted |
3012 | iexplore.exe | 52.160.40.218:443 | dotnet.microsoft.com | Microsoft Corporation | US | unknown |
3012 | iexplore.exe | 52.231.32.10:80 | 8d0456cd7957950f53f0d788bb372d80.clo.footprintdns.com | Microsoft Corporation | KR | whitelisted |
3012 | iexplore.exe | 13.107.18.254:80 | cf466516677836e7252b42ecb9e07da2.clo.footprintdns.com | Microsoft Corporation | US | whitelisted |
3012 | iexplore.exe | 40.86.215.224:80 | 90cb006e71b54590ff836db4163c4bd6.clo.footprintdns.com | Microsoft Corporation | CA | whitelisted |
3012 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
dotnetdownloadservice.azurewebsites.net |
| unknown |
login.live.com |
| whitelisted |
dotnet.microsoft.com |
| whitelisted |
8d0456cd7957950f53f0d788bb372d80.clo.footprintdns.com |
| unknown |
cf466516677836e7252b42ecb9e07da2.clo.footprintdns.com |
| suspicious |
e7c69a62579c0b9d10dea8bf60aecd31.clo.footprintdns.com |
| unknown |
90cb006e71b54590ff836db4163c4bd6.clo.footprintdns.com |
| unknown |
92b640edc8a340e6b53fd85771018e10.clo.footprintdns.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2168 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |