| URL: | https://pixel.mathtag.com/click/img?exch_aid=3a0f6f902bf3729c512c6a81a7d49a1c565d5764&mt_aid=7399895530664286874&mt_id=9717175&mt_adid=250114&mt_sid=10015533&mt_exid=9&mt_inapp=0&mt_os=Windows&mt_uuid=269f60a5-f723-4900-903f-7c61217cd76a&mt_cid=269f60a5-f723-4900-903f-7c61217cd76a&mt_3pck=https%3A//beacon-nf.rubiconproject.com/beacon/v2/t/0/8723d7b6-4139-461e-a6d4-94062042f284/&mt_lp=https%3A//www.bybit.com/en-us/promo/global/bybitlevelup%3Fmedium%3Dpaid_banner%26source%3Dmediamath%26channel%3Dpaid_%26campaign%3Dimc_q122_tr_en%26stage%3Dcurious_pros%26term%3Dbanner_728x90%26content%3Dproduct_usp_v1%26dtpid%3D1640174340449&redirect=https%3A%2F%2Fd.adx.io%2Fdclicks%3Fxb%3D35CJa4376%26xd%3D28%26xnw%3Dxad%26xtm_content%3D15647871060.698.4279.103210962%26xauto_diux%3Ddxid%26xu%3Dhttps%3A%2F%2Fwww.bybit.com%2Fen-us%2Fpromo%2Fglobal%2Fbybitlevelup%3Fmedium%3Dpaid_banner%26source%3Dmediamath%26channel%3Dpaid_%26campaign%3Dimc_q122_tr_en%26stage%3Dcurious_pros%26term%3Dbanner_728x90%26content%3Dproduct_usp_v1%26dtpid%3D1640174340449 |
| Full analysis: | https://app.any.run/tasks/372ff6ea-c66d-49c8-9665-7d541f69b38e |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 18:37:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DFD848B6309C736258B886151A1A8DD9 |
| SHA1: | F8BEE04F8C4992CE4F37DB36038E3A0C2D632C9B |
| SHA256: | 69947E19FF49697D1DFCAD3B5036D05E1FDE6DCBDF1E8E16B3E7560BA5DF29B9 |
| SSDEEP: | 24:2Ia2EhGc3832FsdmjZIyB9GlR88rumqgf+i4YoyB9GlR88rumqgG:e2/QwjqIyuRfr/Fx4LyuRfr/k |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3564)
- iexplore.exe (PID: 2076)
INFO
Reads the computer name
- iexplore.exe (PID: 1828)
- iexplore.exe (PID: 3564)
- iexplore.exe (PID: 3864)
- iexplore.exe (PID: 2076)
Checks supported languages
- iexplore.exe (PID: 1828)
- iexplore.exe (PID: 3564)
- iexplore.exe (PID: 3864)
- iexplore.exe (PID: 2076)
Application launched itself
- iexplore.exe (PID: 1828)
- iexplore.exe (PID: 3864)
Reads settings of System Certificates
- iexplore.exe (PID: 3564)
- iexplore.exe (PID: 1828)
- iexplore.exe (PID: 3864)
- iexplore.exe (PID: 2076)
Reads internet explorer settings
- iexplore.exe (PID: 3564)
- iexplore.exe (PID: 2076)
Manual execution by user
- iexplore.exe (PID: 3864)
Changes internet zones settings
- iexplore.exe (PID: 1828)
- iexplore.exe (PID: 3864)
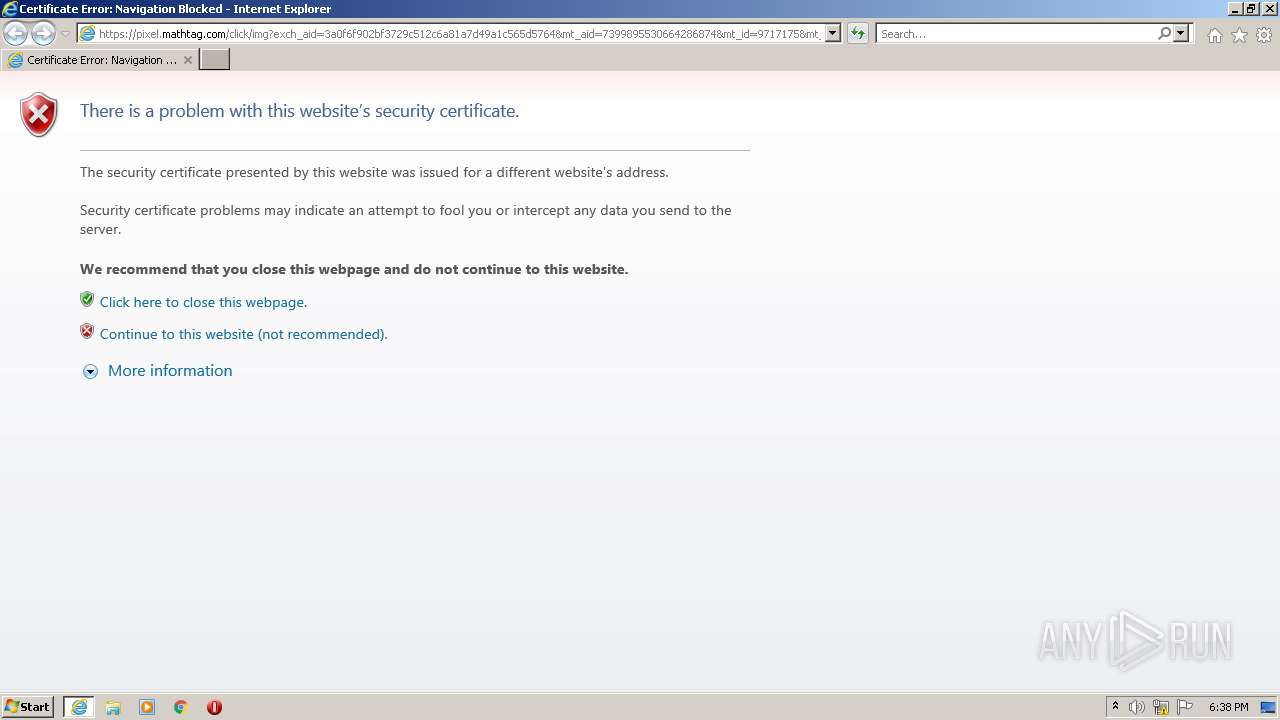
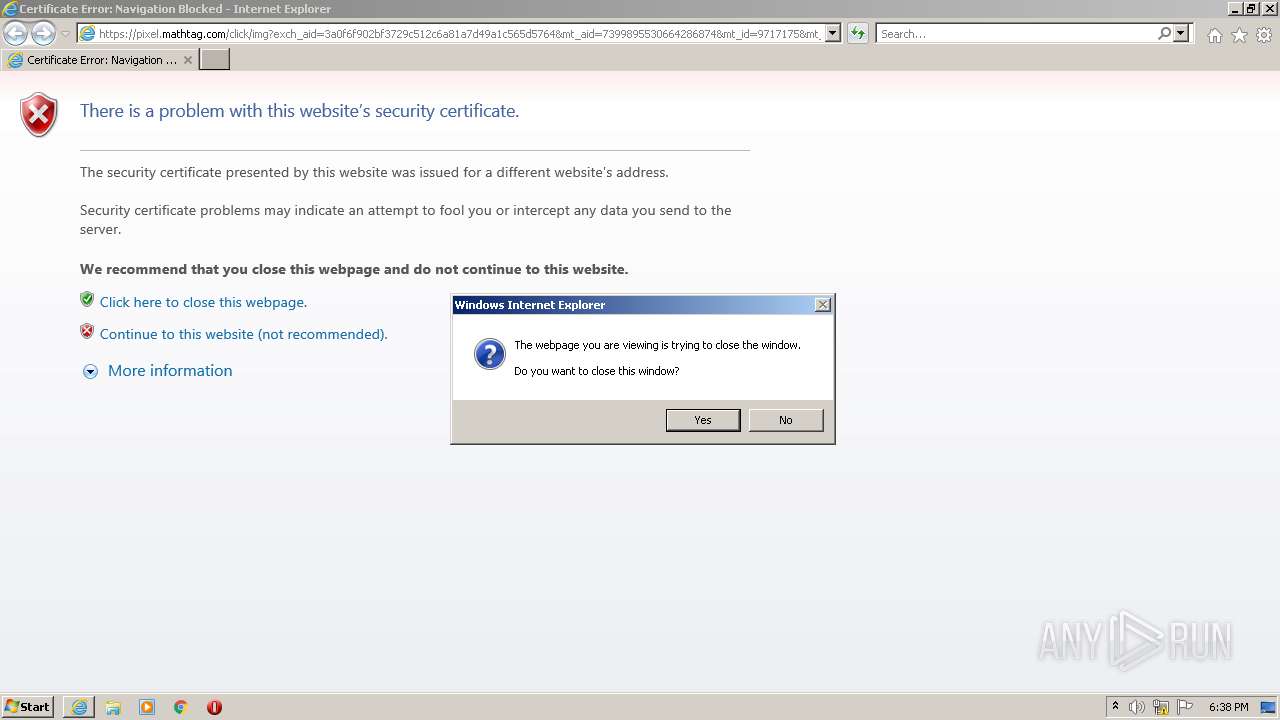
Checks Windows Trust Settings
- iexplore.exe (PID: 3564)
- iexplore.exe (PID: 1828)
- iexplore.exe (PID: 3864)
- iexplore.exe (PID: 2076)
Reads the date of Windows installation
- iexplore.exe (PID: 1828)
- iexplore.exe (PID: 3864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1828 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://pixel.mathtag.com/click/img?exch_aid=3a0f6f902bf3729c512c6a81a7d49a1c565d5764&mt_aid=7399895530664286874&mt_id=9717175&mt_adid=250114&mt_sid=10015533&mt_exid=9&mt_inapp=0&mt_os=Windows&mt_uuid=269f60a5-f723-4900-903f-7c61217cd76a&mt_cid=269f60a5-f723-4900-903f-7c61217cd76a&mt_3pck=https%3A//beacon-nf.rubiconproject.com/beacon/v2/t/0/8723d7b6-4139-461e-a6d4-94062042f284/&mt_lp=https%3A//www.bybit.com/en-us/promo/global/bybitlevelup%3Fmedium%3Dpaid_banner%26source%3Dmediamath%26channel%3Dpaid_%26campaign%3Dimc_q122_tr_en%26stage%3Dcurious_pros%26term%3Dbanner_728x90%26content%3Dproduct_usp_v1%26dtpid%3D1640174340449&redirect=https%3A%2F%2Fd.adx.io%2Fdclicks%3Fxb%3D35CJa4376%26xd%3D28%26xnw%3Dxad%26xtm_content%3D15647871060.698.4279.103210962%26xauto_diux%3Ddxid%26xu%3Dhttps%3A%2F%2Fwww.bybit.com%2Fen-us%2Fpromo%2Fglobal%2Fbybitlevelup%3Fmedium%3Dpaid_banner%26source%3Dmediamath%26channel%3Dpaid_%26campaign%3Dimc_q122_tr_en%26stage%3Dcurious_pros%26term%3Dbanner_728x90%26content%3Dproduct_usp_v1%26dtpid%3D1640174340449" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2076 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3864 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3564 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1828 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3864 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
24 431
Read events
24 244
Write events
184
Delete events
3
Modification events
| (PID) Process: | (1828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30937425 | |||
| (PID) Process: | (1828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30937425 | |||
| (PID) Process: | (1828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
7
Text files
0
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3564 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 1828 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{BEC4C55D-7D44-11EC-A20C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{CBD82AF5-7D44-11EC-A20C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 1828 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF134253C4E3B939C3.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{CBD82AF7-7D44-11EC-A20C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 1828 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{BEC4C55F-7D44-11EC-A20C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFD0225F373CFE3DDC.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFCDD5BC161CDF4F36.TMP | gmc | |
MD5:— | SHA256:— | |||
| 1828 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFF909FCCC137CE11A.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{D2880360-7D44-11EC-A20C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
18
DNS requests
18
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
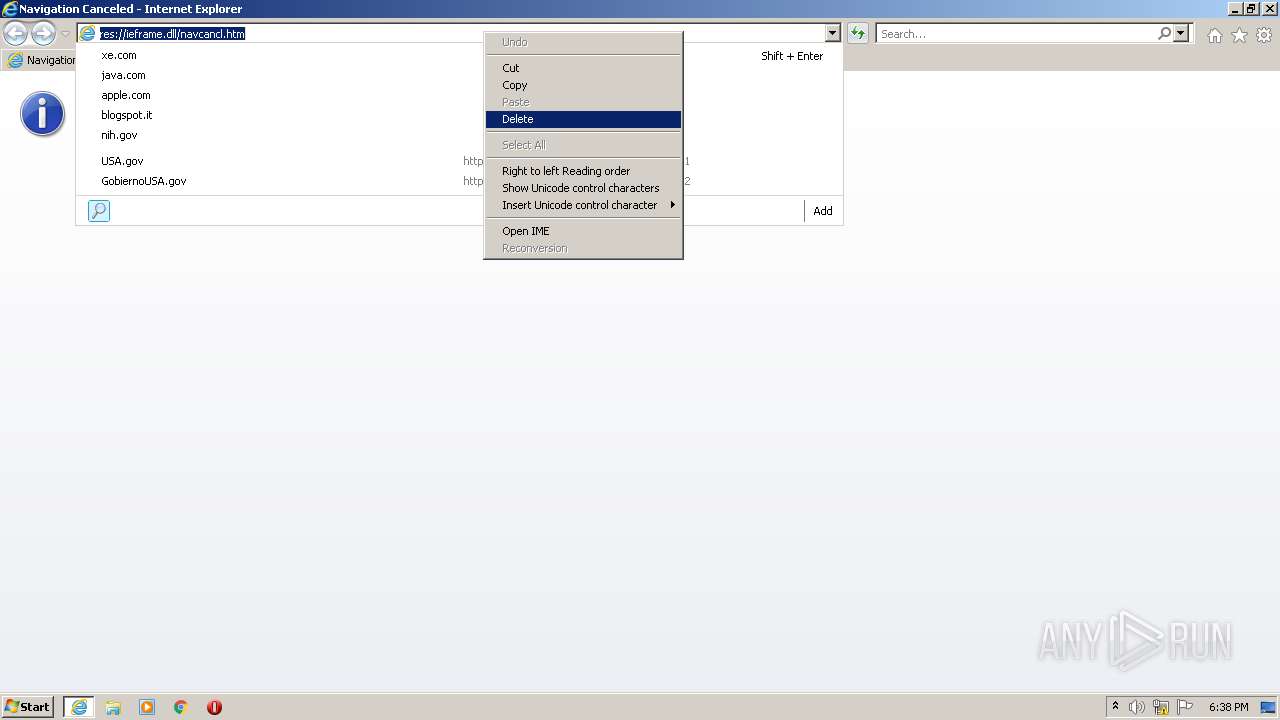
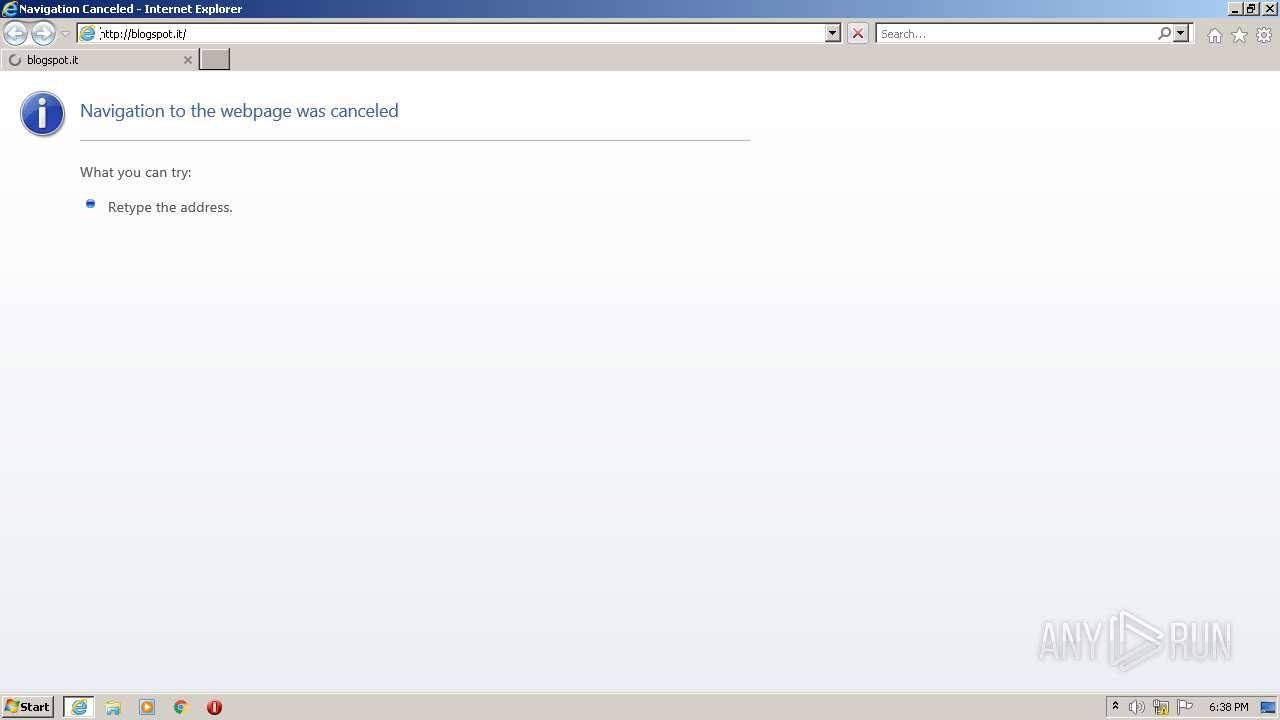
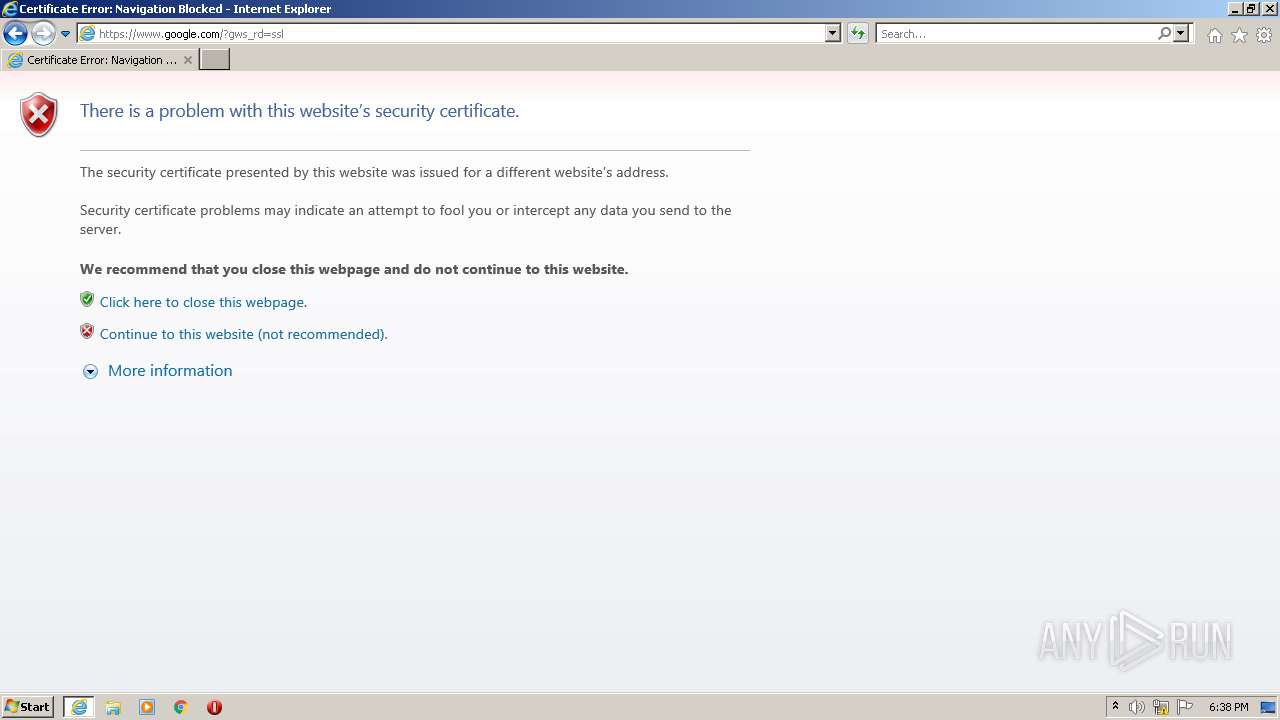
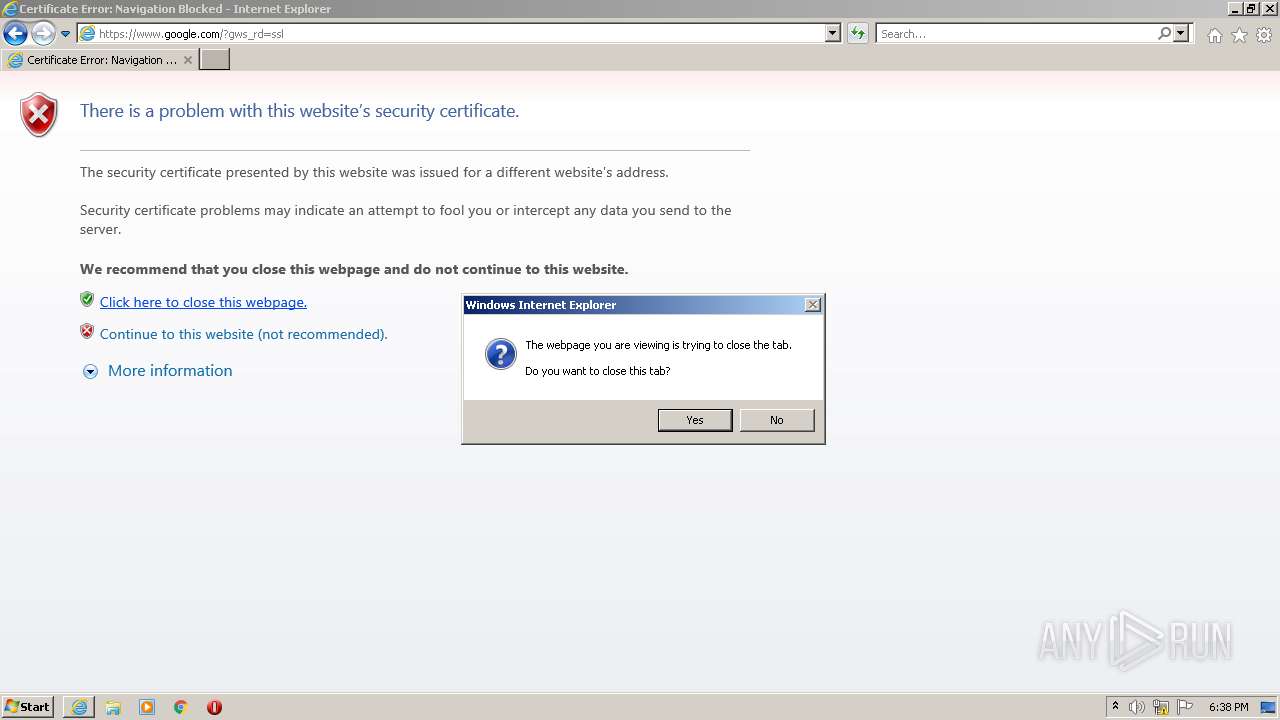
2076 | iexplore.exe | GET | 302 | 142.250.186.100:80 | http://www.google.com/ | US | html | 231 b | malicious |
2076 | iexplore.exe | GET | 302 | 142.250.184.201:80 | http://blogspot.it/ | US | html | 219 b | suspicious |
3564 | iexplore.exe | GET | 200 | 67.27.158.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c11a9e5204e805b1 | US | compressed | 4.70 Kb | whitelisted |
3564 | iexplore.exe | GET | 200 | 67.27.158.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b2261f61964f64d3 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3564 | iexplore.exe | 67.27.158.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | malicious |
3564 | iexplore.exe | 184.30.20.207:443 | pixel.mathtag.com | GTT Communications Inc. | US | suspicious |
1828 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3864 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1828 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2076 | iexplore.exe | 142.250.184.201:80 | blogspot.it | Google Inc. | US | unknown |
2076 | iexplore.exe | 142.250.186.100:443 | www.google.com | Google Inc. | US | whitelisted |
2076 | iexplore.exe | 142.250.186.100:80 | www.google.com | Google Inc. | US | whitelisted |
3864 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pixel.mathtag.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
blogspot.it |
| unknown |
www.google.com |
| malicious |
Threats
10 ETPRO signatures available at the full report