| File name: | python-3.13.3-amd64.exe |
| Full analysis: | https://app.any.run/tasks/3a23624c-1dd7-47b2-9148-75f070d9f54f |
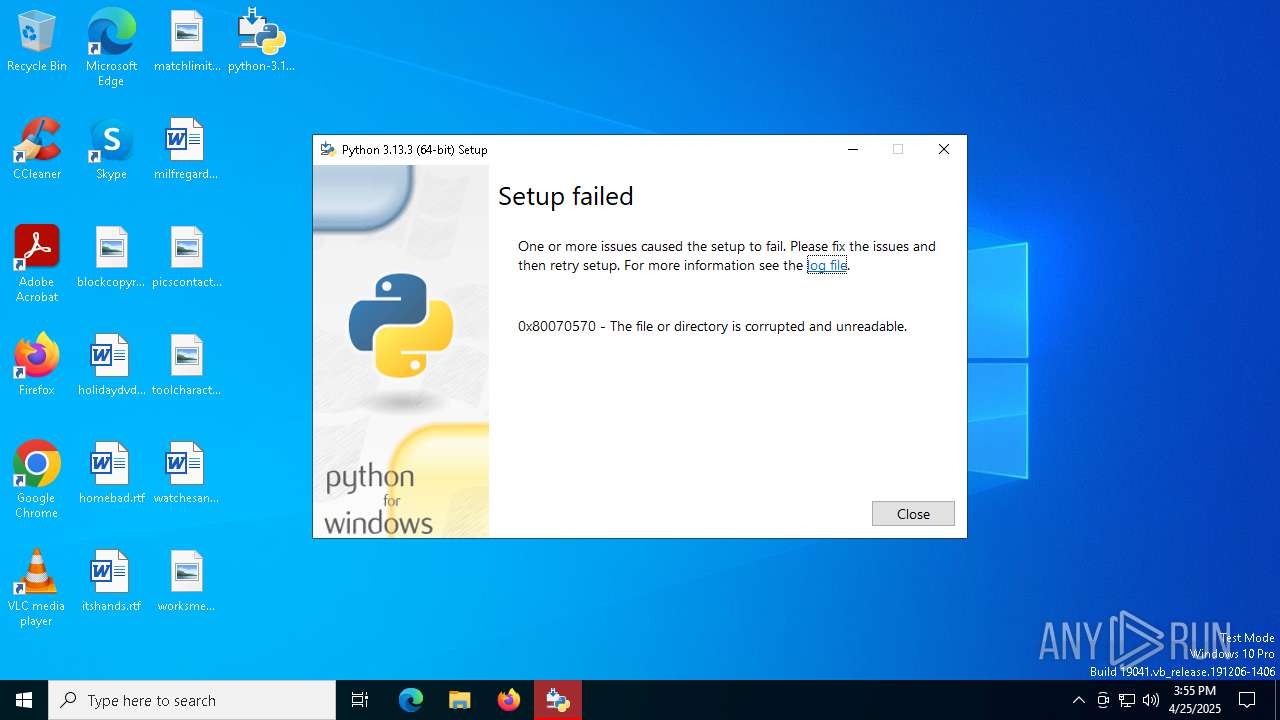
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2025, 15:54:46 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | BE3264DAEB8C5E08365492DD02908CFA |
| SHA1: | 5B03805FAC97F041616A427A811C325C513E0586 |
| SHA256: | 698F2DF46E1A3DD92F393458EEA77BD94EF5FF21F0D5BF5CF676F3D28A9B4B6C |
| SSDEEP: | 393216:EXE+SC/jWsdMWf+hSsXpqxn858p6gELsNZewog:4jSCLWsdMWXMQ8580hsNZewog |
MALICIOUS
Changes the autorun value in the registry
- python-3.13.3-amd64.exe (PID: 1812)
SUSPICIOUS
Executable content was dropped or overwritten
- python-3.13.3-amd64.exe (PID: 2392)
- python-3.13.3-amd64.exe (PID: 1812)
The process drops C-runtime libraries
- python-3.13.3-amd64.exe (PID: 1812)
Process drops legitimate windows executable
- python-3.13.3-amd64.exe (PID: 1812)
Searches for installed software
- python-3.13.3-amd64.exe (PID: 1812)
Creates a software uninstall entry
- python-3.13.3-amd64.exe (PID: 1812)
INFO
The sample compiled with english language support
- python-3.13.3-amd64.exe (PID: 1812)
- python-3.13.3-amd64.exe (PID: 2392)
Reads the software policy settings
- slui.exe (PID: 3896)
Checks proxy server information
- slui.exe (PID: 3896)
Create files in a temporary directory
- python-3.13.3-amd64.exe (PID: 2392)
- python-3.13.3-amd64.exe (PID: 1812)
Checks supported languages
- python-3.13.3-amd64.exe (PID: 2392)
- python-3.13.3-amd64.exe (PID: 1812)
Creates files or folders in the user directory
- python-3.13.3-amd64.exe (PID: 1812)
Auto-launch of the file from Registry key
- python-3.13.3-amd64.exe (PID: 1812)
Reads the computer name
- python-3.13.3-amd64.exe (PID: 1812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:03:22 22:14:43+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit, Removable run from swap, Net run from swap |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 314368 |
| InitializedDataSize: | 240640 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x302e5 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.13.3150.0 |
| ProductVersionNumber: | 3.13.3150.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Python Software Foundation |
| FileDescription: | Python 3.13.3 (64-bit) |
| FileVersion: | 3.13.3150.0 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Python Software Foundation. All rights reserved. |
| OriginalFileName: | python-3.13.3-amd64.exe |
| ProductName: | Python 3.13.3 (64-bit) |
| ProductVersion: | 3.13.3150.0 |
Total processes
124
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1812 | "C:\Users\admin\AppData\Local\Temp\{57428941-2A03-4CFD-899F-4D76E2716B51}\.cr\python-3.13.3-amd64.exe" -burn.clean.room="C:\Users\admin\Desktop\python-3.13.3-amd64.exe" -burn.filehandle.attached=752 -burn.filehandle.self=708 | C:\Users\admin\AppData\Local\Temp\{57428941-2A03-4CFD-899F-4D76E2716B51}\.cr\python-3.13.3-amd64.exe | python-3.13.3-amd64.exe | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python 3.13.3 (64-bit) Exit code: 1392 Version: 3.13.3150.0 Modules
| |||||||||||||||
| 2392 | "C:\Users\admin\Desktop\python-3.13.3-amd64.exe" | C:\Users\admin\Desktop\python-3.13.3-amd64.exe | explorer.exe | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python 3.13.3 (64-bit) Exit code: 1392 Version: 3.13.3150.0 Modules
| |||||||||||||||
| 3896 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 492
Read events
3 459
Write events
26
Delete events
7
Modification events
| (PID) Process: | (1812) python-3.13.3-amd64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{08e71e50-ef1b-4db1-82a2-622d72b5fee9} |
| Operation: | write | Name: | BundleCachePath |
Value: C:\Users\admin\AppData\Local\Package Cache\{08e71e50-ef1b-4db1-82a2-622d72b5fee9}\python-3.13.3-amd64.exe | |||
| (PID) Process: | (1812) python-3.13.3-amd64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{08e71e50-ef1b-4db1-82a2-622d72b5fee9} |
| Operation: | write | Name: | BundleUpgradeCode |
Value: {F96F59BD-3E48-5E4E-B1A4-6CAFADEFEAE8} | |||
| (PID) Process: | (1812) python-3.13.3-amd64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{08e71e50-ef1b-4db1-82a2-622d72b5fee9} |
| Operation: | write | Name: | BundleAddonCode |
Value: | |||
| (PID) Process: | (1812) python-3.13.3-amd64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{08e71e50-ef1b-4db1-82a2-622d72b5fee9} |
| Operation: | write | Name: | BundleDetectCode |
Value: | |||
| (PID) Process: | (1812) python-3.13.3-amd64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{08e71e50-ef1b-4db1-82a2-622d72b5fee9} |
| Operation: | write | Name: | BundlePatchCode |
Value: | |||
| (PID) Process: | (1812) python-3.13.3-amd64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{08e71e50-ef1b-4db1-82a2-622d72b5fee9} |
| Operation: | write | Name: | BundleVersion |
Value: 3.13.3150.0 | |||
| (PID) Process: | (1812) python-3.13.3-amd64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{08e71e50-ef1b-4db1-82a2-622d72b5fee9} |
| Operation: | write | Name: | VersionMajor |
Value: 3 | |||
| (PID) Process: | (1812) python-3.13.3-amd64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{08e71e50-ef1b-4db1-82a2-622d72b5fee9} |
| Operation: | write | Name: | VersionMinor |
Value: 13 | |||
| (PID) Process: | (1812) python-3.13.3-amd64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{08e71e50-ef1b-4db1-82a2-622d72b5fee9} |
| Operation: | write | Name: | BundleProviderKey |
Value: CPython-3.13 | |||
| (PID) Process: | (1812) python-3.13.3-amd64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{08e71e50-ef1b-4db1-82a2-622d72b5fee9} |
| Operation: | write | Name: | BundleTag |
Value: | |||
Executable files
8
Suspicious files
2
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1812 | python-3.13.3-amd64.exe | C:\Users\admin\AppData\Local\Temp\{CAA33963-FB72-4E1D-AD6D-D3C40B16E8AC}\lib_JustForMe | — | |
MD5:— | SHA256:— | |||
| 1812 | python-3.13.3-amd64.exe | C:\Users\admin\AppData\Local\Temp\{CAA33963-FB72-4E1D-AD6D-D3C40B16E8AC}\test_JustForMe | — | |
MD5:— | SHA256:— | |||
| 1812 | python-3.13.3-amd64.exe | C:\Users\admin\AppData\Local\Temp\{CAA33963-FB72-4E1D-AD6D-D3C40B16E8AC}\doc_JustForMe | — | |
MD5:— | SHA256:— | |||
| 1812 | python-3.13.3-amd64.exe | C:\Users\admin\AppData\Local\Temp\{CAA33963-FB72-4E1D-AD6D-D3C40B16E8AC}\.ba\Default.thm | xml | |
MD5:1D2CBC76A6A70F60729EE66D6876BB66 | SHA256:D0D3351D4CDE77EB245B026D677E4AE5177A50EE0B9A43DB23349F1AB5DEEDC9 | |||
| 2392 | python-3.13.3-amd64.exe | C:\Users\admin\AppData\Local\Temp\{57428941-2A03-4CFD-899F-4D76E2716B51}\.cr\python-3.13.3-amd64.exe | executable | |
MD5:15797B42F45C5C86D0A0ACC802D91BFE | SHA256:1C54A6C111355FAE2E89FF65211C0DC753C94553883005DB3DE2C75F055C76A2 | |||
| 1812 | python-3.13.3-amd64.exe | C:\Users\admin\AppData\Local\Temp\{CAA33963-FB72-4E1D-AD6D-D3C40B16E8AC}\.ba\Default.wxl | xml | |
MD5:E1A9ABB2936BC6E980C9BACEBE71C5A9 | SHA256:7F30044D0B14262F8BACD2891A810B127550CA56FC4D0E1D619AE489AAF6EC18 | |||
| 1812 | python-3.13.3-amd64.exe | C:\Users\admin\AppData\Local\Package Cache\{08e71e50-ef1b-4db1-82a2-622d72b5fee9}\python-3.13.3-amd64.exe | executable | |
MD5:15797B42F45C5C86D0A0ACC802D91BFE | SHA256:1C54A6C111355FAE2E89FF65211C0DC753C94553883005DB3DE2C75F055C76A2 | |||
| 1812 | python-3.13.3-amd64.exe | C:\Users\admin\AppData\Local\Temp\{CAA33963-FB72-4E1D-AD6D-D3C40B16E8AC}\2466F1A4951CE9B58776858C613A3960980F58CC | executable | |
MD5:67D7D208114081E0E239CC1509E8FFDB | SHA256:A59BDC5024990B4DD788C086B76267F3F8BD8FF76846E3602C23E24E1145F04F | |||
| 1812 | python-3.13.3-amd64.exe | C:\Users\admin\AppData\Local\Package Cache\{08e71e50-ef1b-4db1-82a2-622d72b5fee9}\state.rsm | binary | |
MD5:ADFD6039C81C6D14ACB8A3C0BBF69752 | SHA256:4439BF8E8B92AD9ACC9AC992870C84ADFD9BF20B8461C251D129FE2E01866BE1 | |||
| 1812 | python-3.13.3-amd64.exe | C:\Users\admin\AppData\Local\Temp\{CAA33963-FB72-4E1D-AD6D-D3C40B16E8AC}\.ba\PythonBA.dll | executable | |
MD5:4A8C11BBA51B46F0B53A1D774FBDB83E | SHA256:90A4F1BEEDF0A345D3E261E49B13D72A30E8B6BBAD3CA1532EA84B6E9588B59B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
23
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 23.48.23.183:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 72.246.169.155:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 23.48.23.183:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 72.246.169.155:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6488 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3896 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |