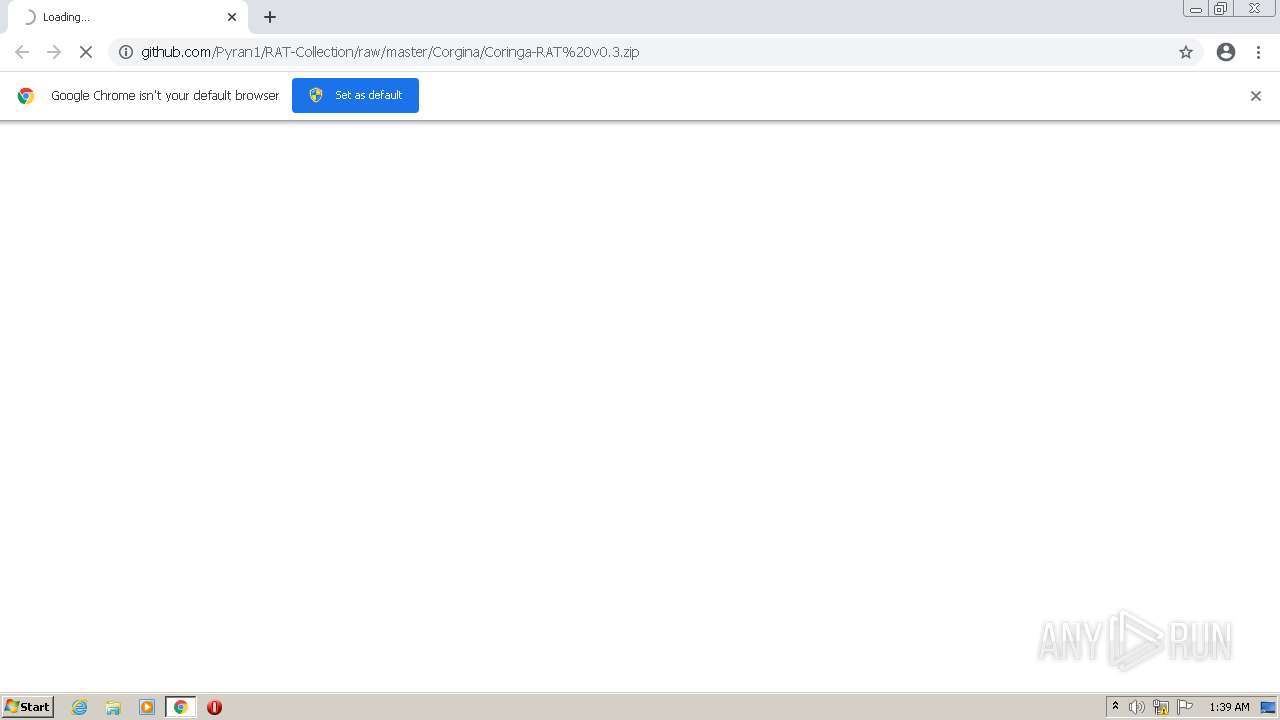
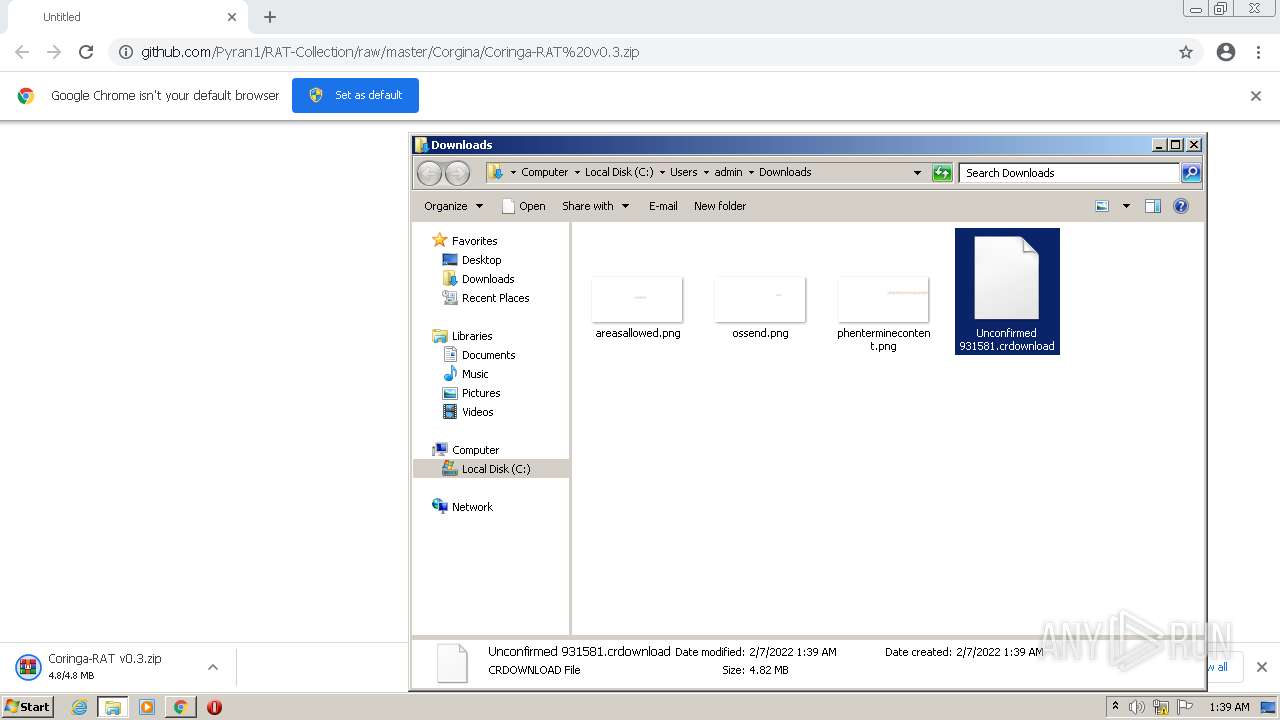
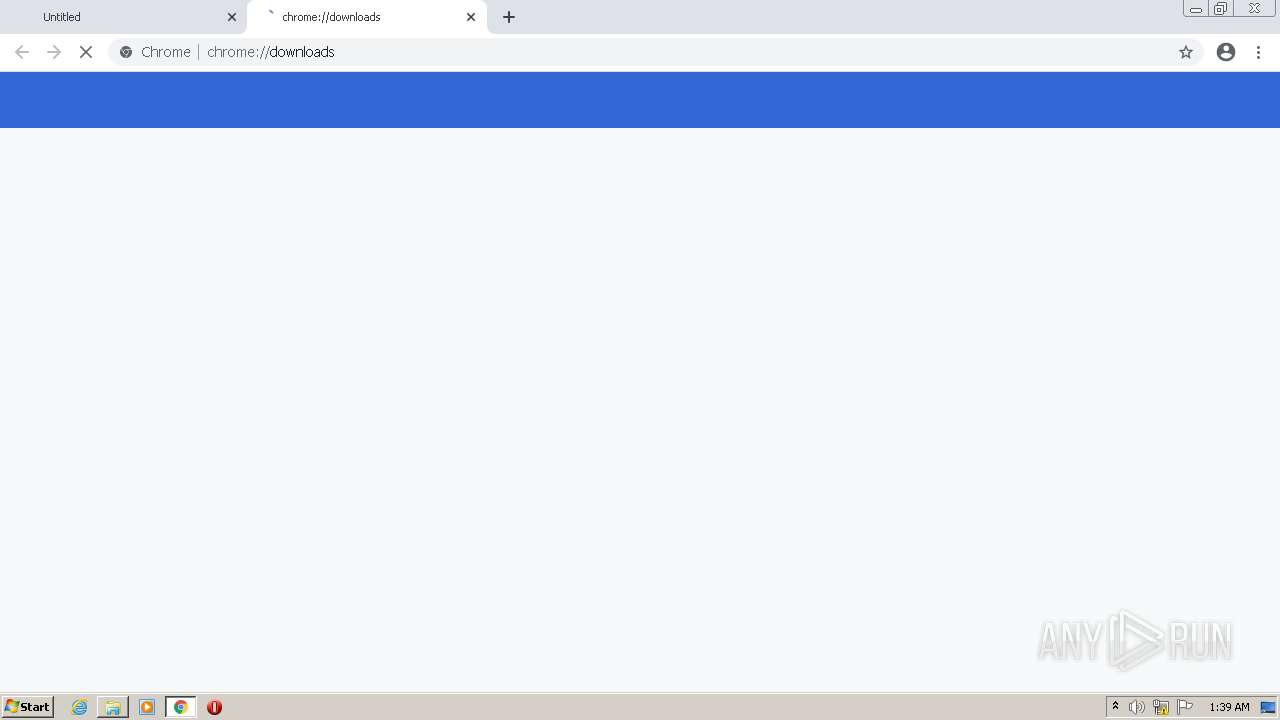
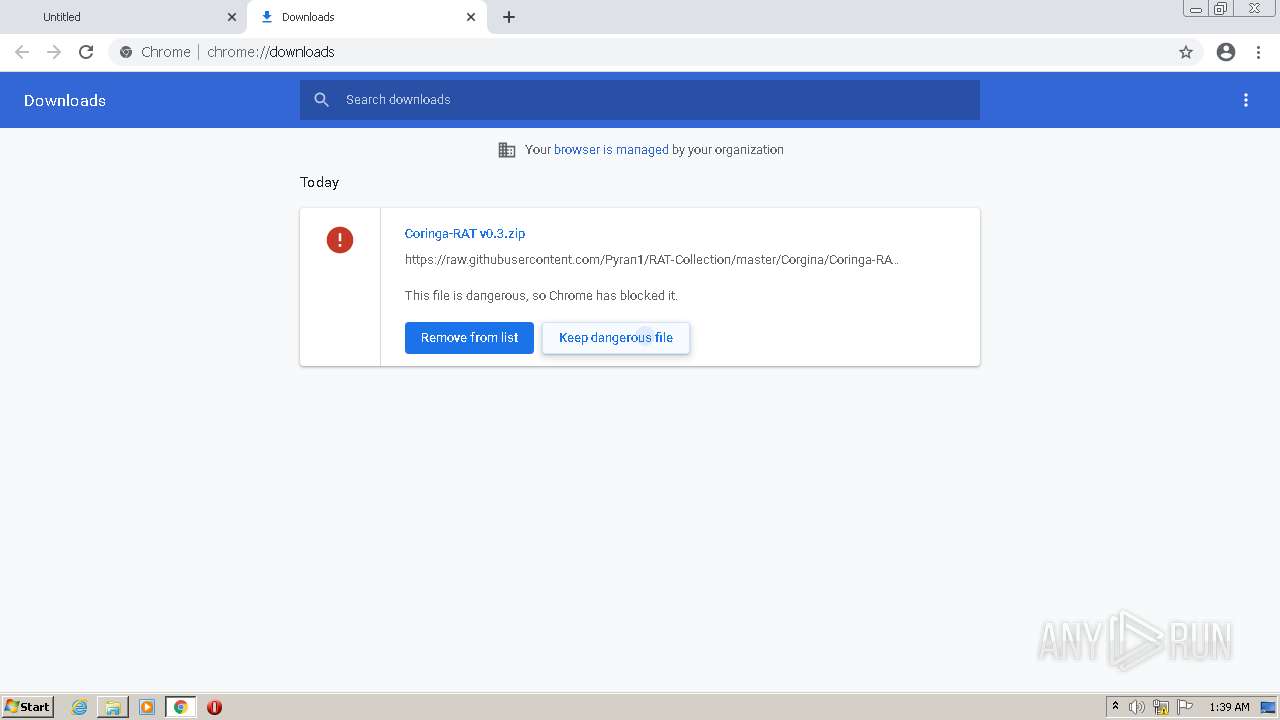
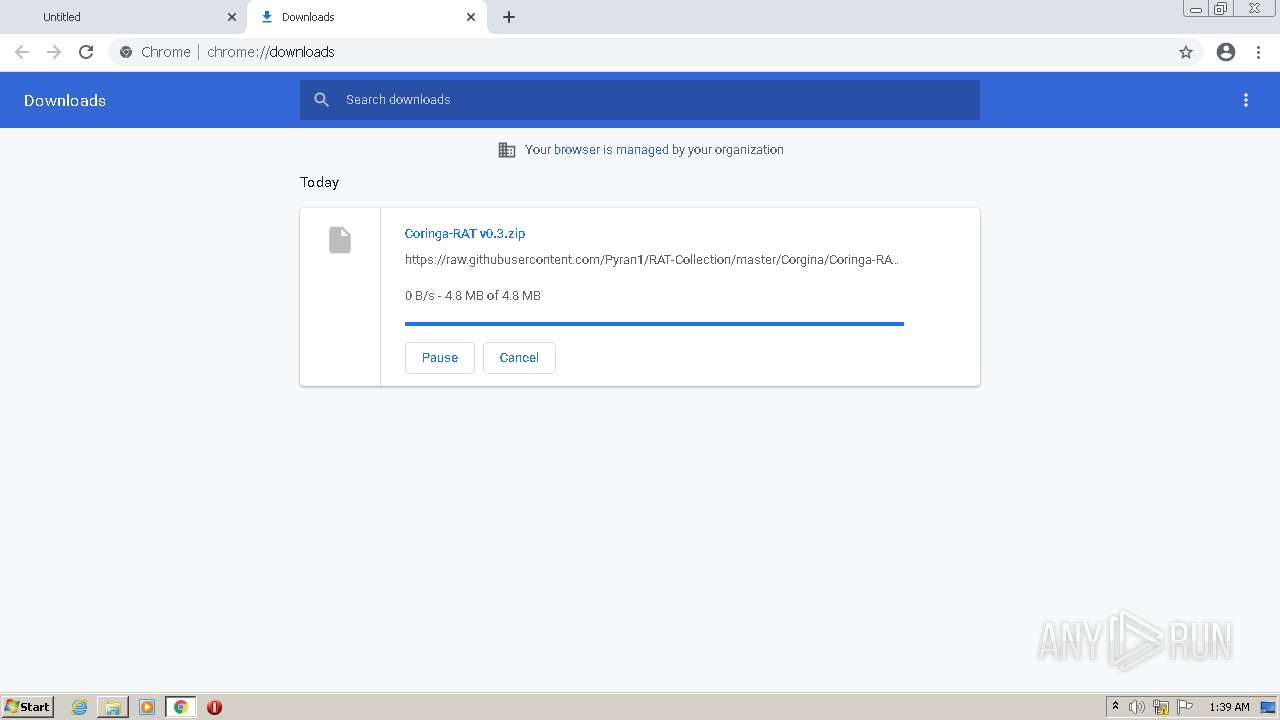
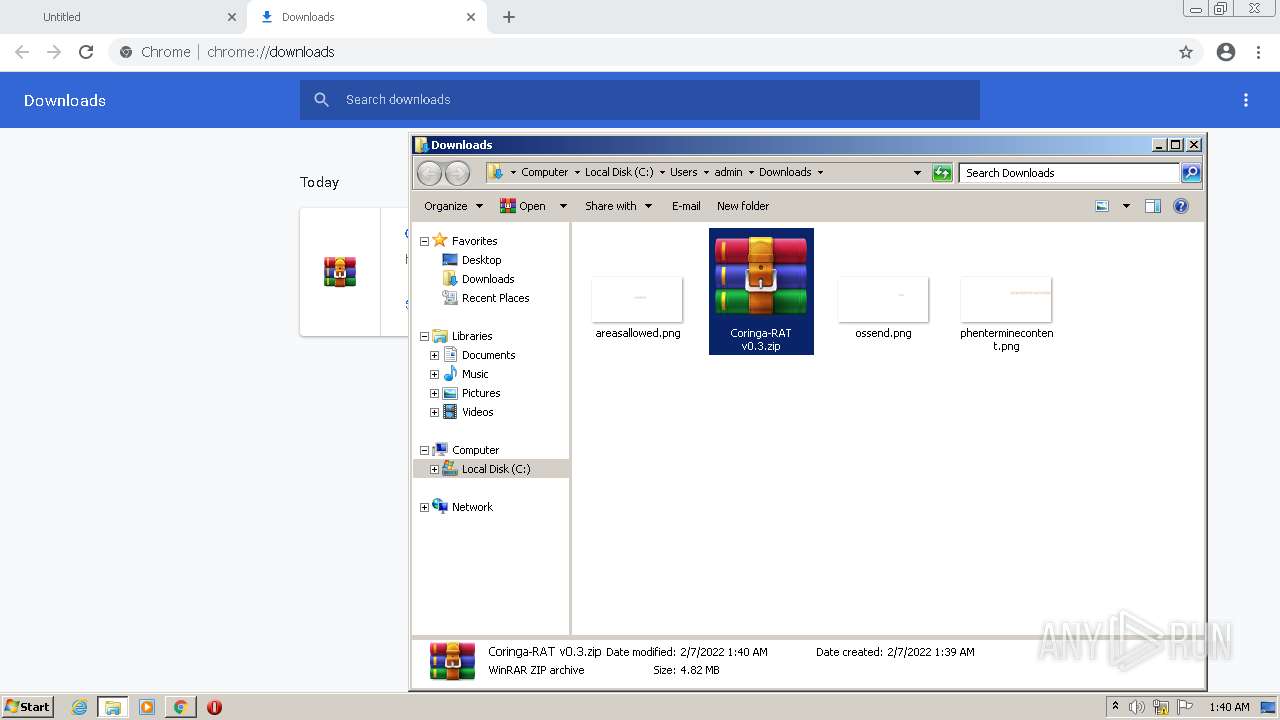
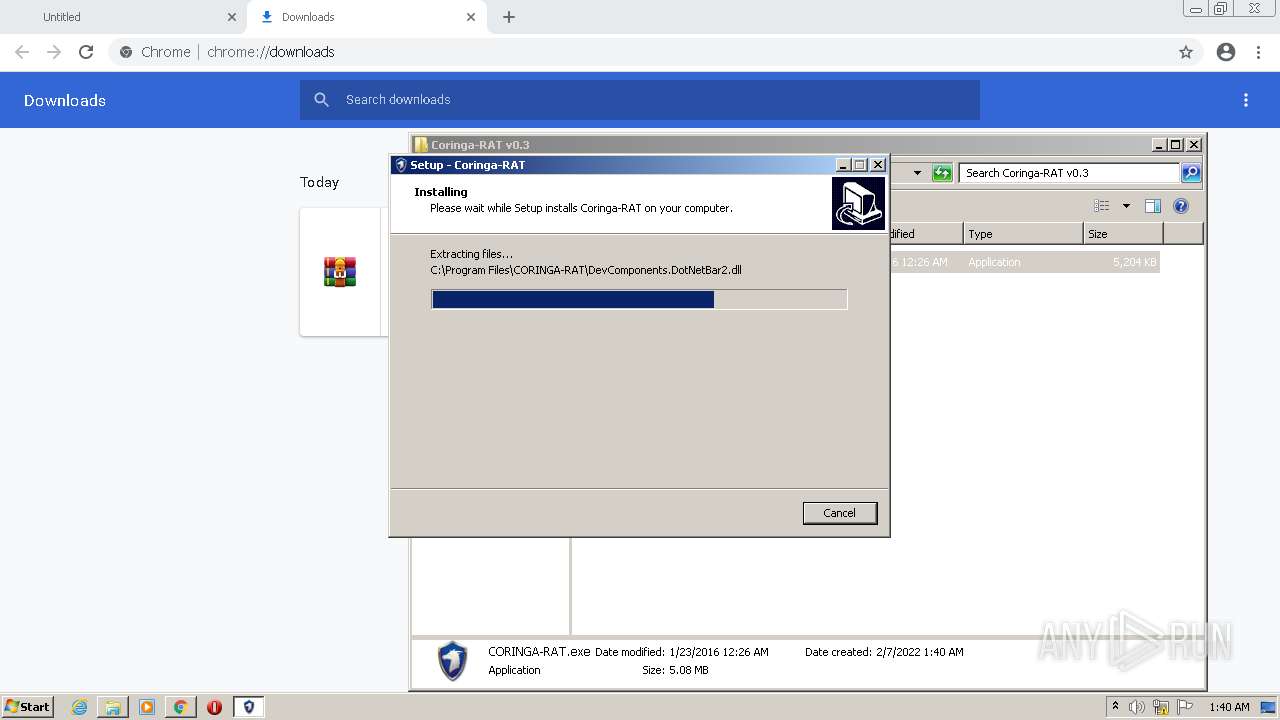
| URL: | https://github.com/Pyran1/RAT-Collection/raw/master/Corgina/Coringa-RAT%20v0.3.zip |
| Full analysis: | https://app.any.run/tasks/711d9ff4-4172-4034-b4c5-901eb637593d |
| Verdict: | Malicious activity |
| Analysis date: | February 07, 2022, 01:39:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7A6673A37886061A169F1B2630580EBA |
| SHA1: | F1E3FFE59B80C4C88FCCD575C61470BDF930EBD9 |
| SHA256: | 6981240538BB9F19DE7E024403EB35E0358A27AD5A1C27E198406E9974B3B09D |
| SSDEEP: | 3:N8tEd9TUxIrOGRd2CM/9XM2hifUn:2urggOGeXGTcn |
MALICIOUS
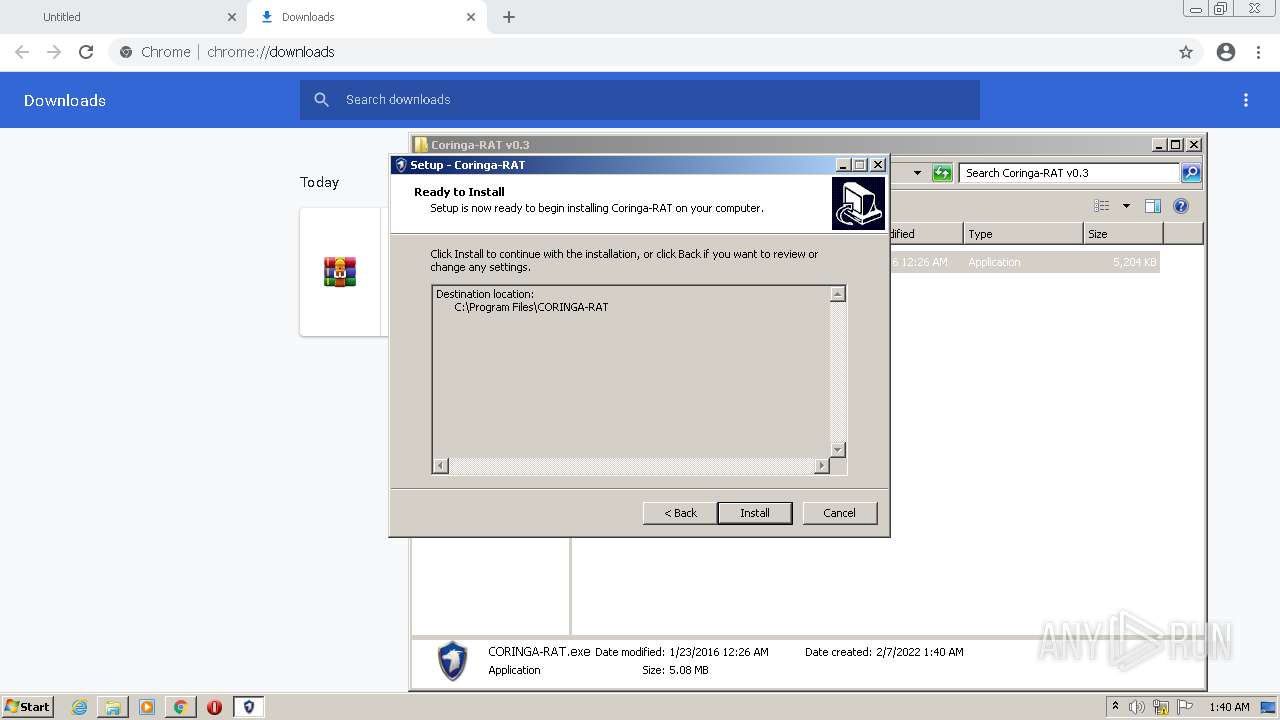
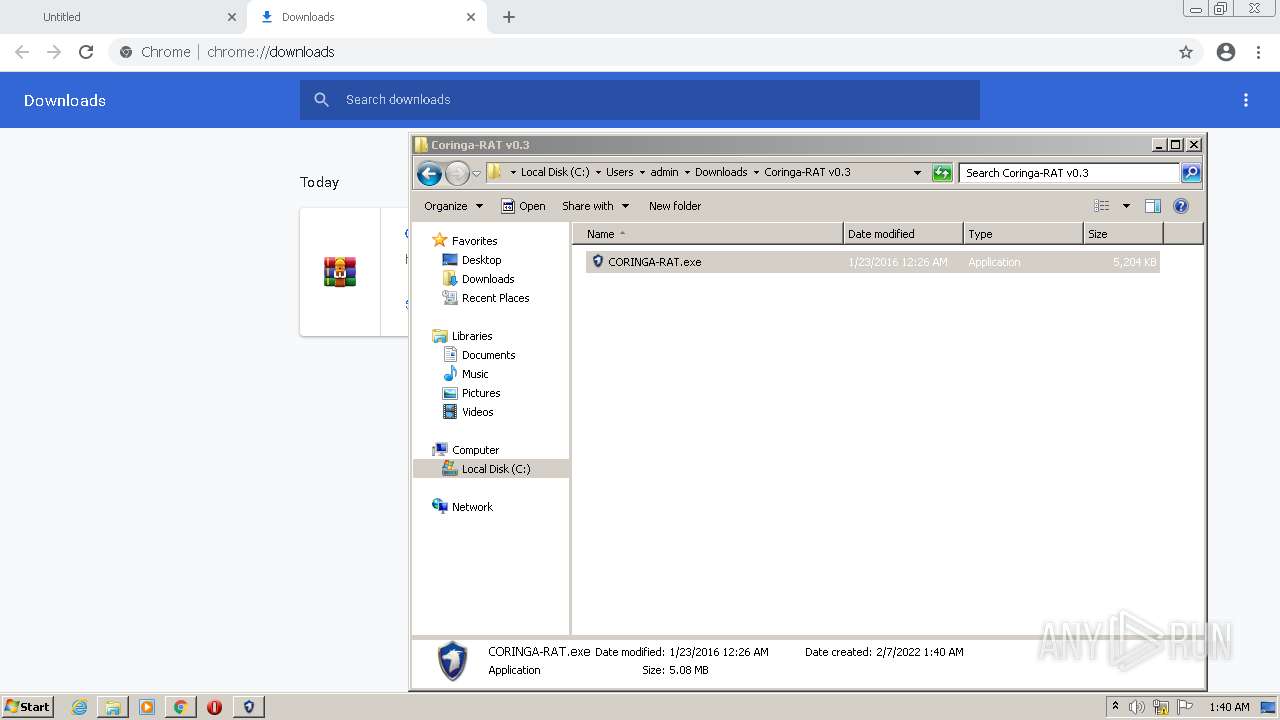
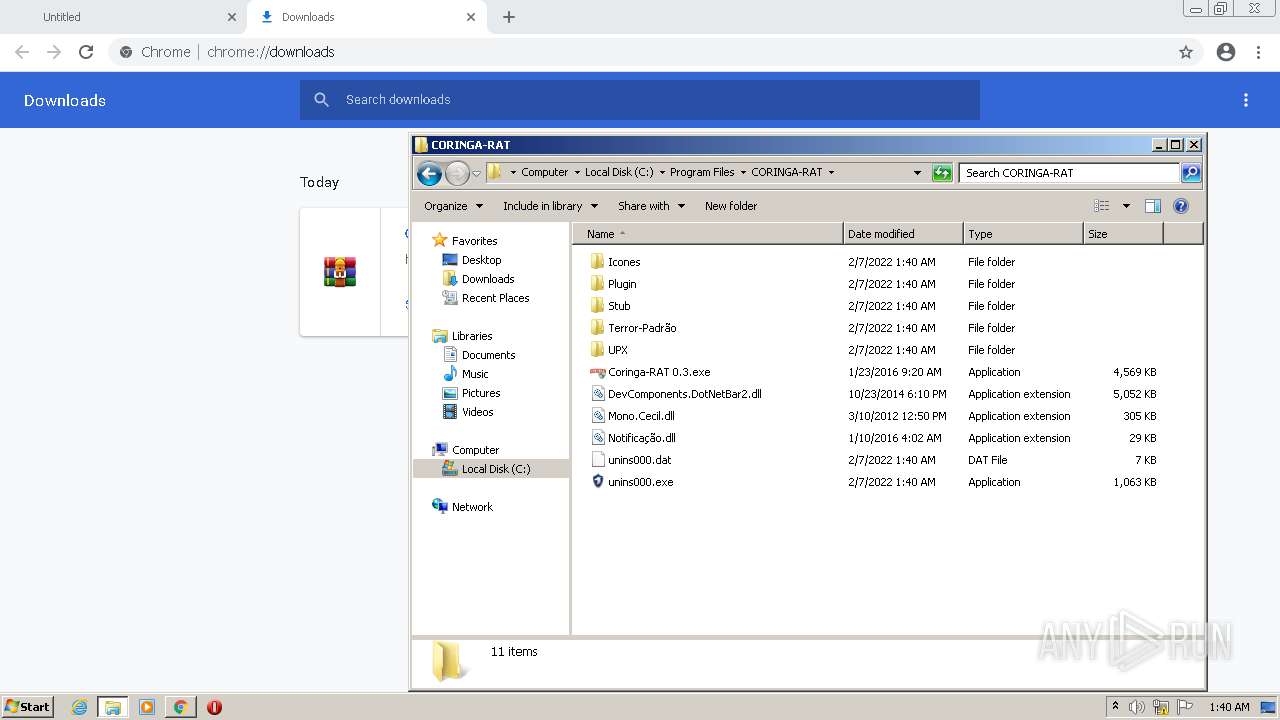
Application was dropped or rewritten from another process
- CORINGA-RAT.exe (PID: 3980)
- CORINGA-RAT.exe (PID: 1008)
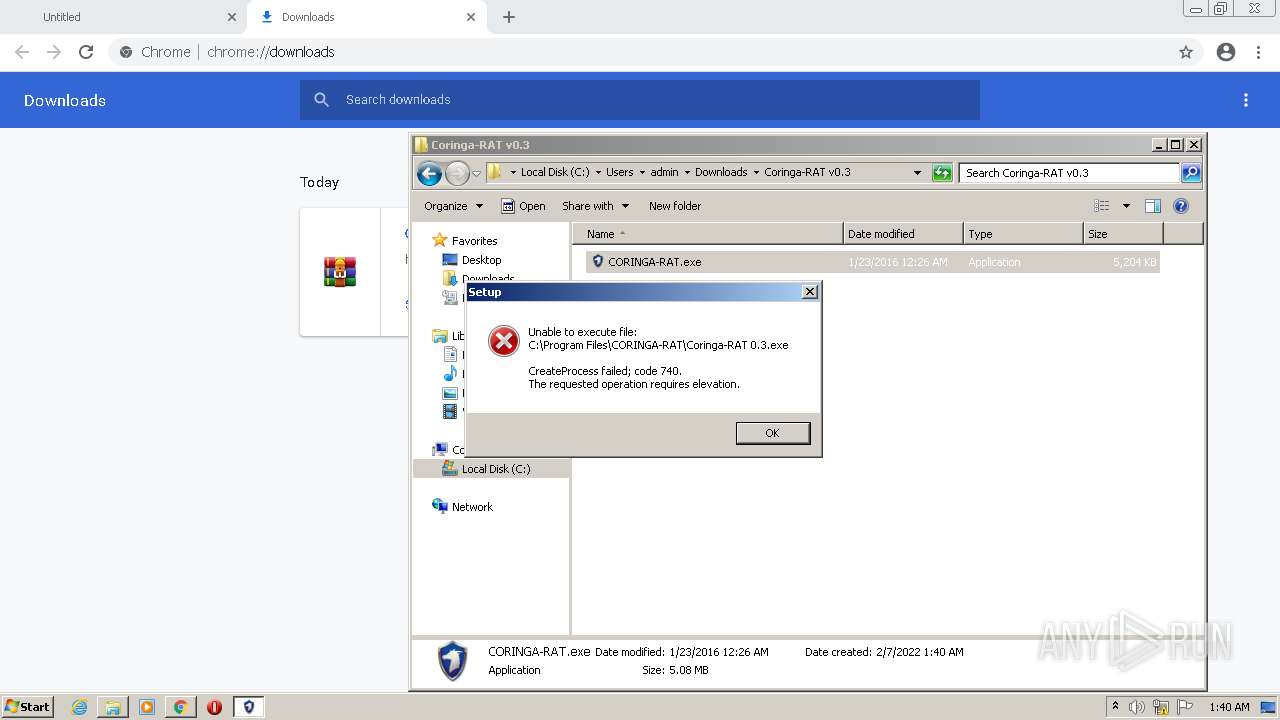
- Coringa-RAT 0.3.exe (PID: 3116)
- Coringa-RAT 0.3.exe (PID: 1044)
Drops executable file immediately after starts
- CORINGA-RAT.exe (PID: 1008)
- CORINGA-RAT.exe (PID: 3980)
Loads dropped or rewritten executable
- Coringa-RAT 0.3.exe (PID: 1044)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2476)
- CORINGA-RAT.exe (PID: 3980)
- WinRAR.exe (PID: 1120)
- CORINGA-RAT.exe (PID: 1008)
- CORINGA-RAT.tmp (PID: 2076)
Reads the computer name
- WinRAR.exe (PID: 1120)
- CORINGA-RAT.tmp (PID: 1268)
- CORINGA-RAT.tmp (PID: 2076)
- Coringa-RAT 0.3.exe (PID: 1044)
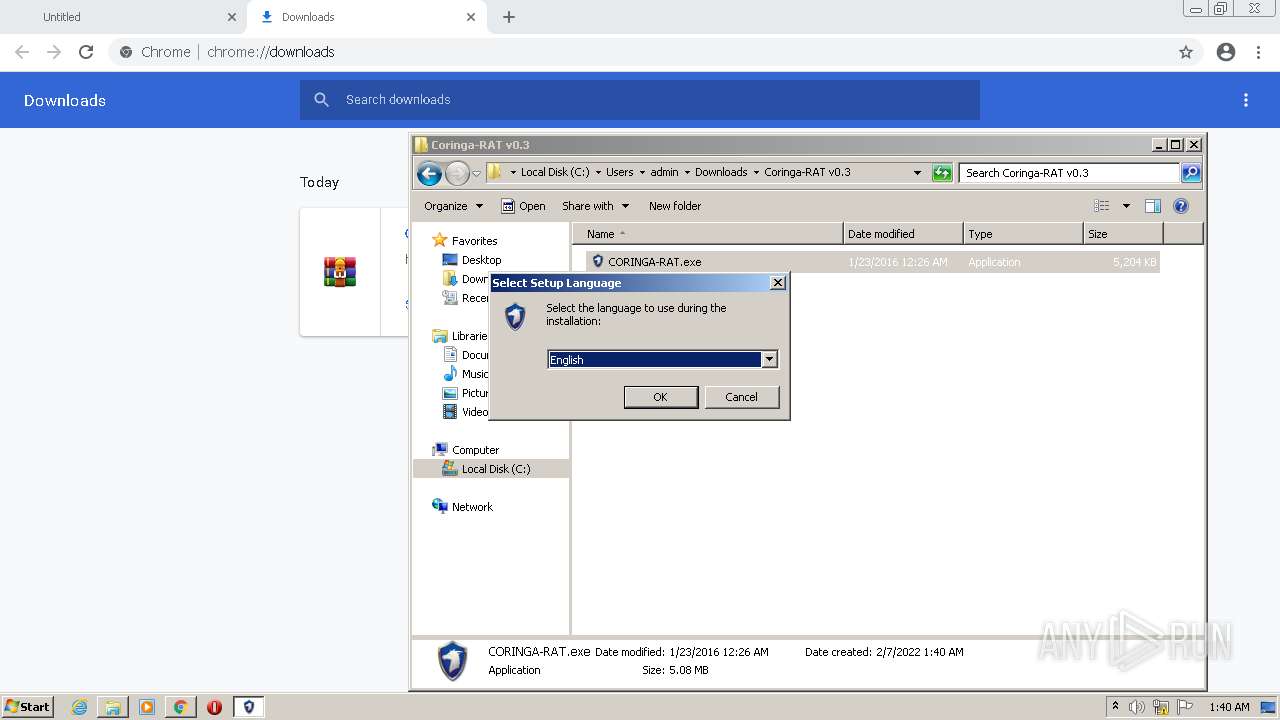
Checks supported languages
- WinRAR.exe (PID: 1120)
- CORINGA-RAT.exe (PID: 3980)
- CORINGA-RAT.exe (PID: 1008)
- CORINGA-RAT.tmp (PID: 2076)
- Coringa-RAT 0.3.exe (PID: 1044)
- CORINGA-RAT.tmp (PID: 1268)
Drops a file with too old compile date
- WinRAR.exe (PID: 1120)
- CORINGA-RAT.exe (PID: 3980)
- CORINGA-RAT.exe (PID: 1008)
- CORINGA-RAT.tmp (PID: 2076)
- chrome.exe (PID: 2476)
Reads Windows owner or organization settings
- CORINGA-RAT.tmp (PID: 2076)
Reads the Windows organization settings
- CORINGA-RAT.tmp (PID: 2076)
Drops a file that was compiled in debug mode
- CORINGA-RAT.tmp (PID: 2076)
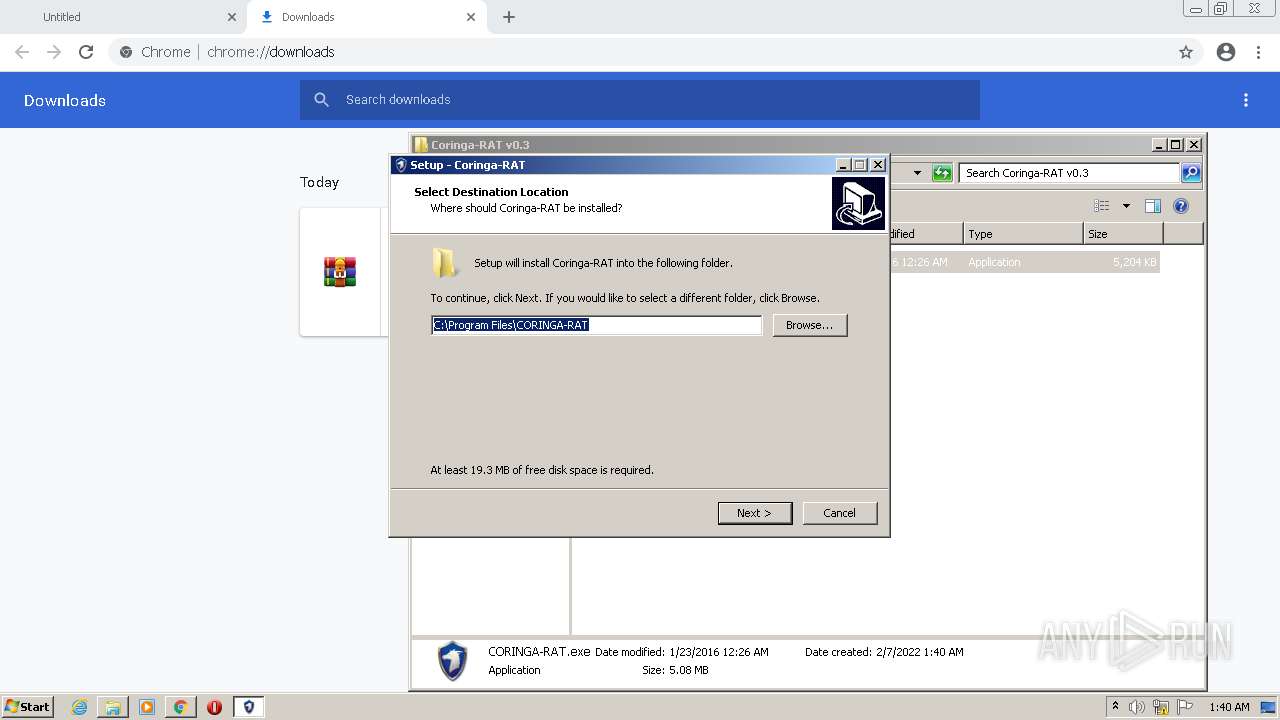
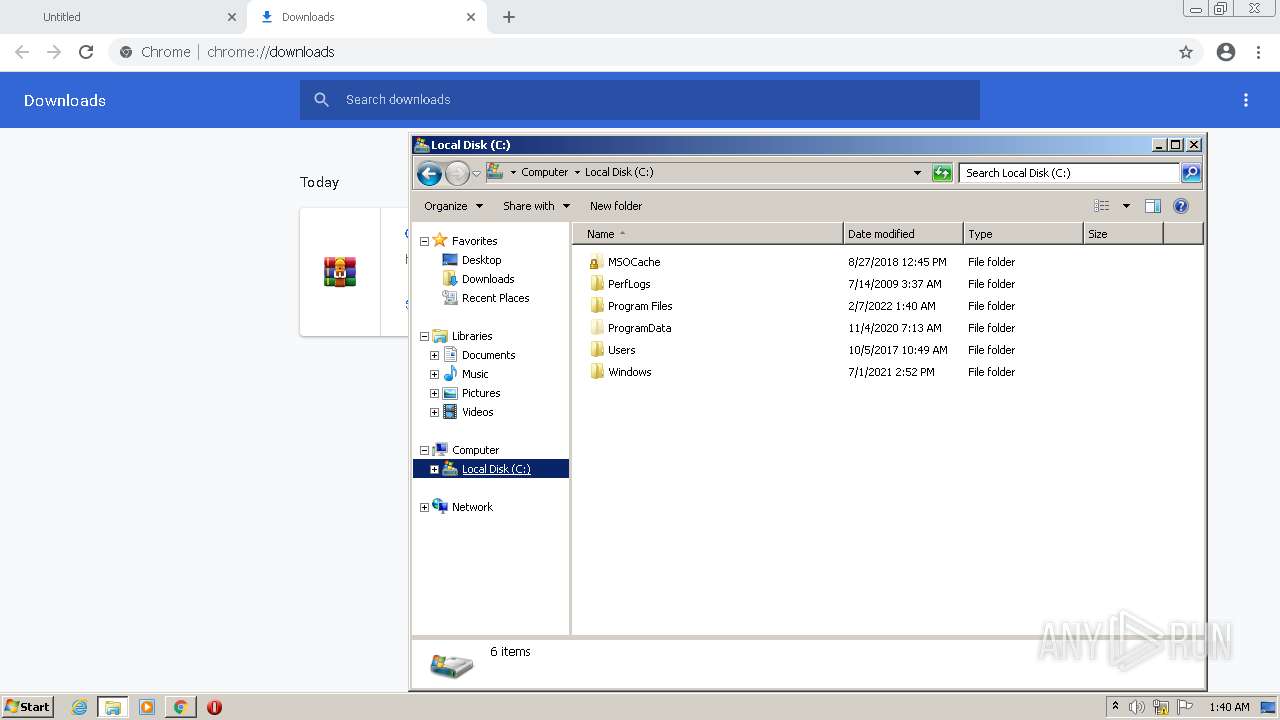
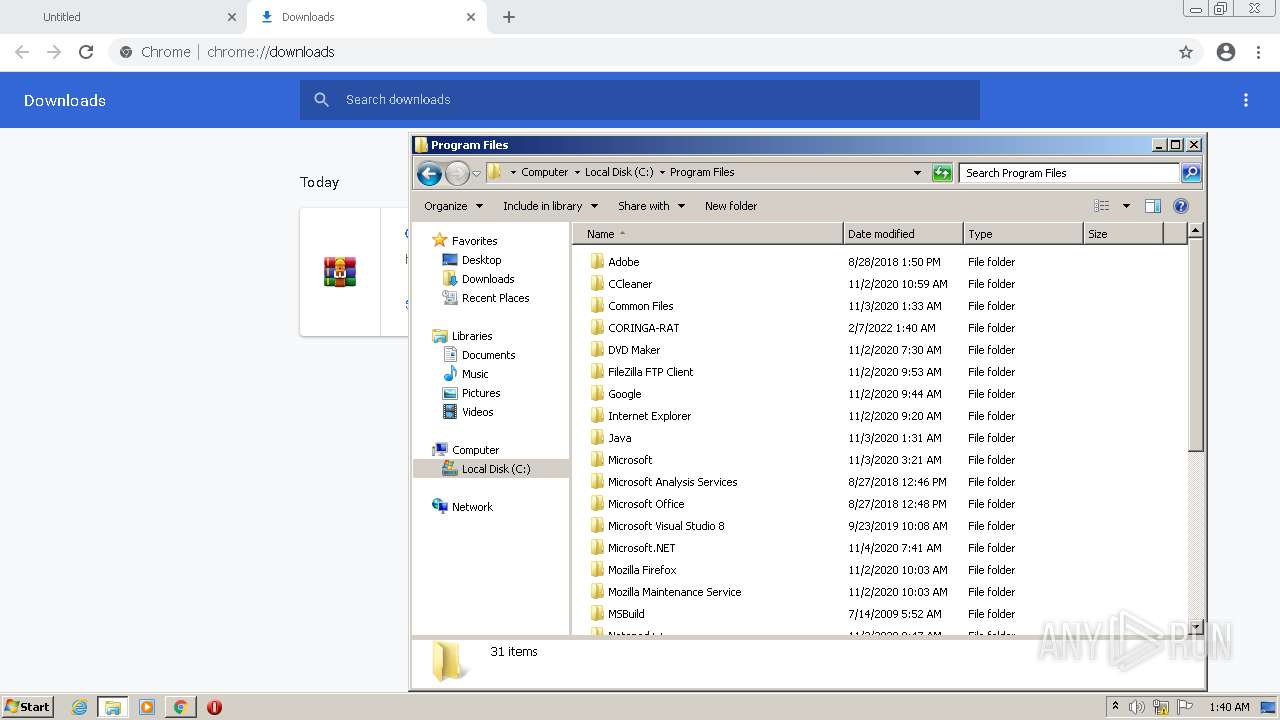
Creates a directory in Program Files
- CORINGA-RAT.tmp (PID: 2076)
INFO
Application launched itself
- chrome.exe (PID: 2856)
Checks supported languages
- chrome.exe (PID: 2012)
- chrome.exe (PID: 360)
- chrome.exe (PID: 1492)
- chrome.exe (PID: 444)
- chrome.exe (PID: 2476)
- chrome.exe (PID: 2172)
- chrome.exe (PID: 2380)
- chrome.exe (PID: 2180)
- chrome.exe (PID: 4000)
- chrome.exe (PID: 3028)
- chrome.exe (PID: 1704)
- chrome.exe (PID: 2856)
- chrome.exe (PID: 456)
- chrome.exe (PID: 1136)
- chrome.exe (PID: 2916)
Reads the computer name
- chrome.exe (PID: 2012)
- chrome.exe (PID: 1492)
- chrome.exe (PID: 360)
- chrome.exe (PID: 2172)
- chrome.exe (PID: 2856)
- chrome.exe (PID: 2380)
- chrome.exe (PID: 456)
- chrome.exe (PID: 1136)
- chrome.exe (PID: 2916)
Reads the hosts file
- chrome.exe (PID: 2856)
- chrome.exe (PID: 1492)
Reads settings of System Certificates
- chrome.exe (PID: 1492)
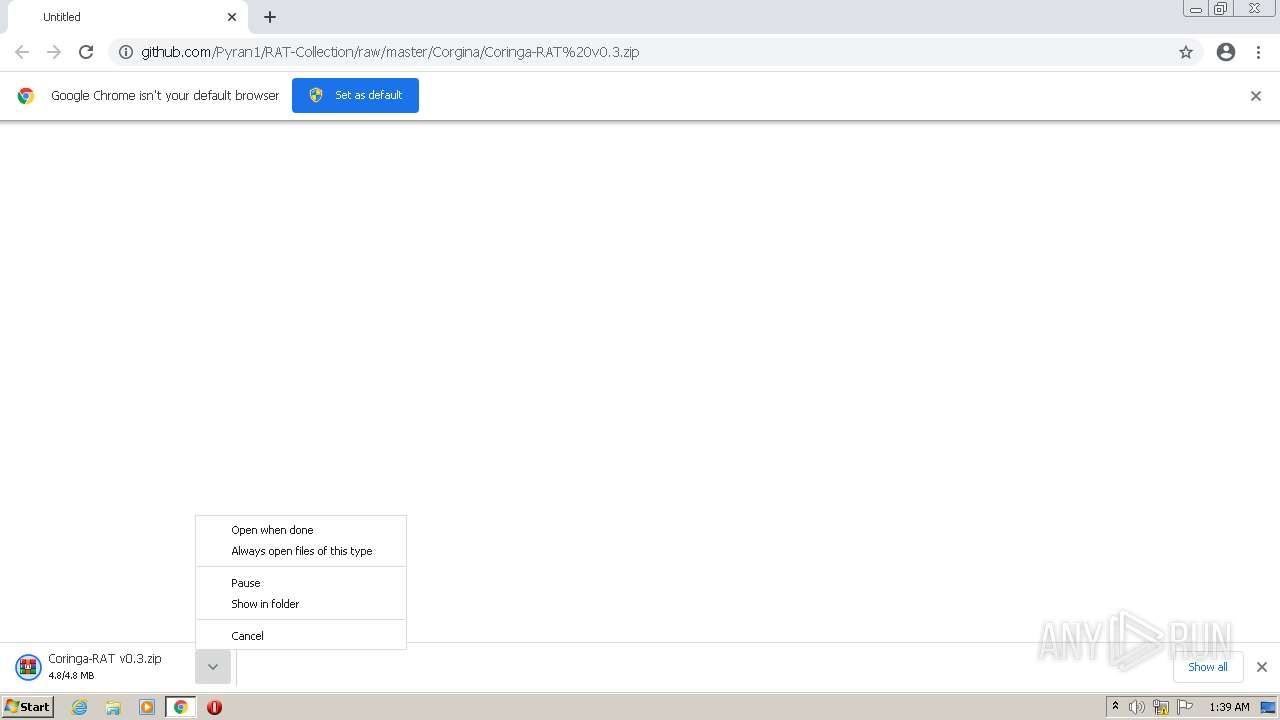
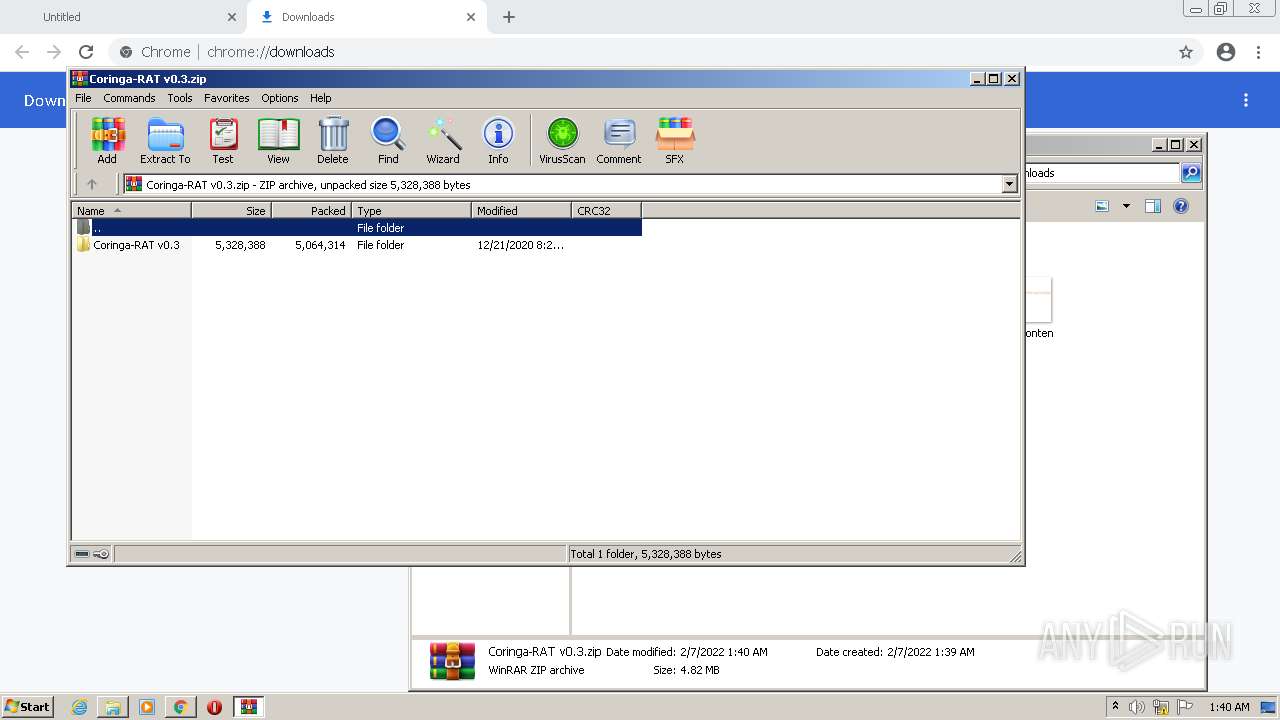
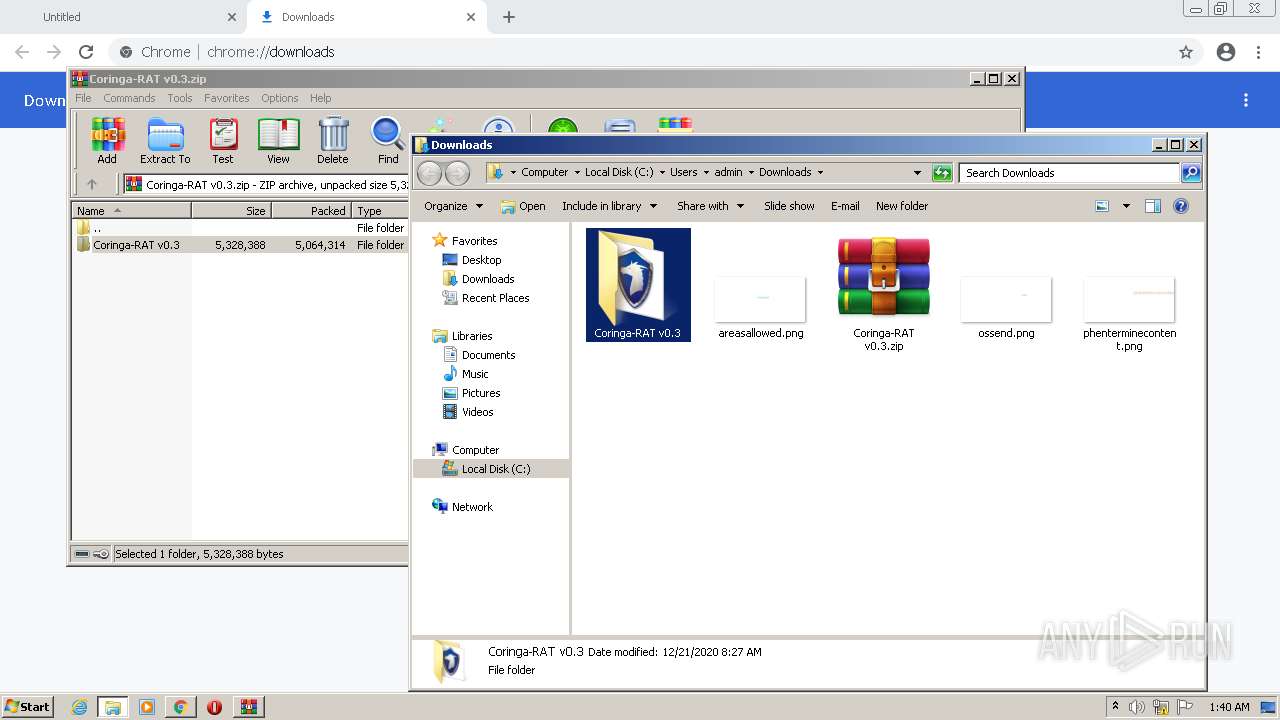
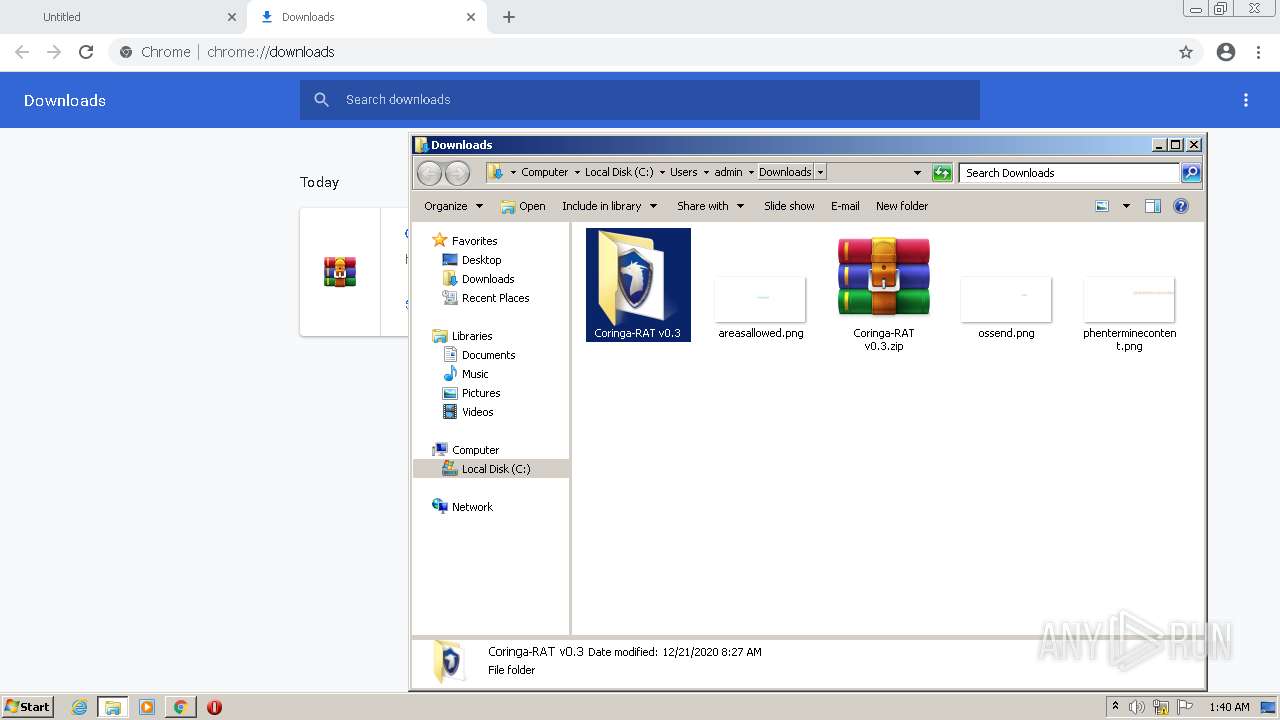
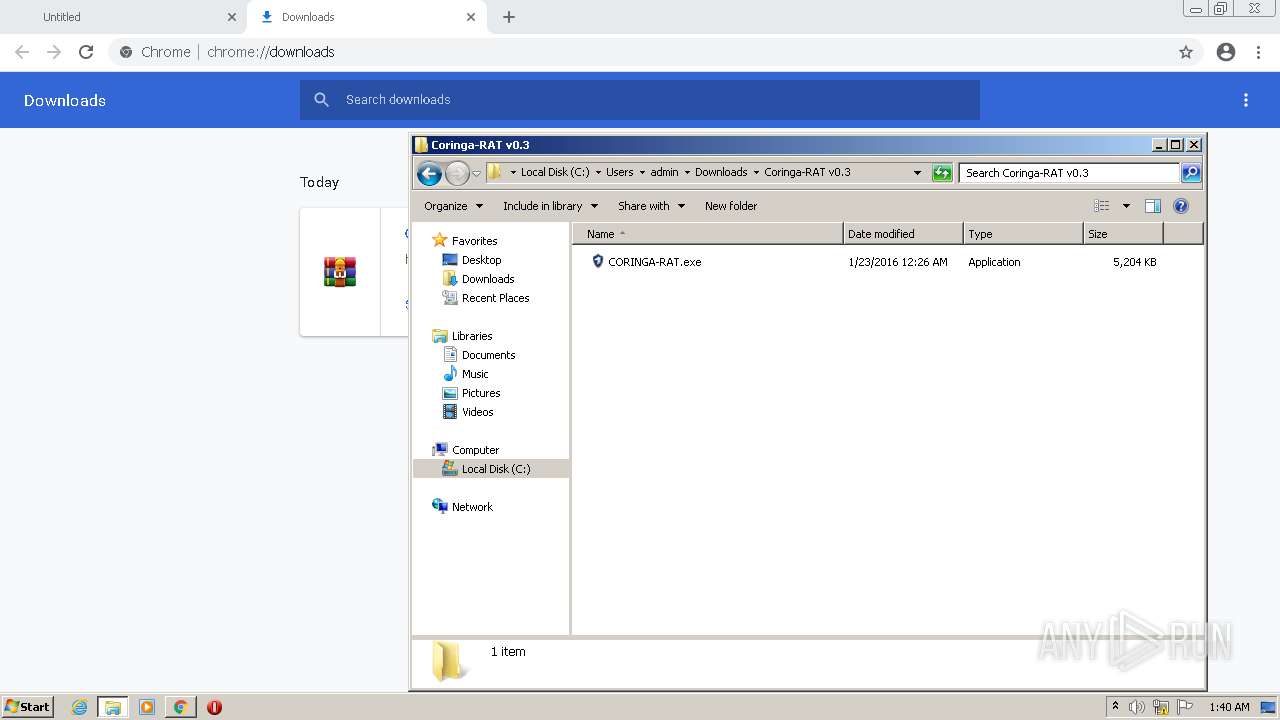
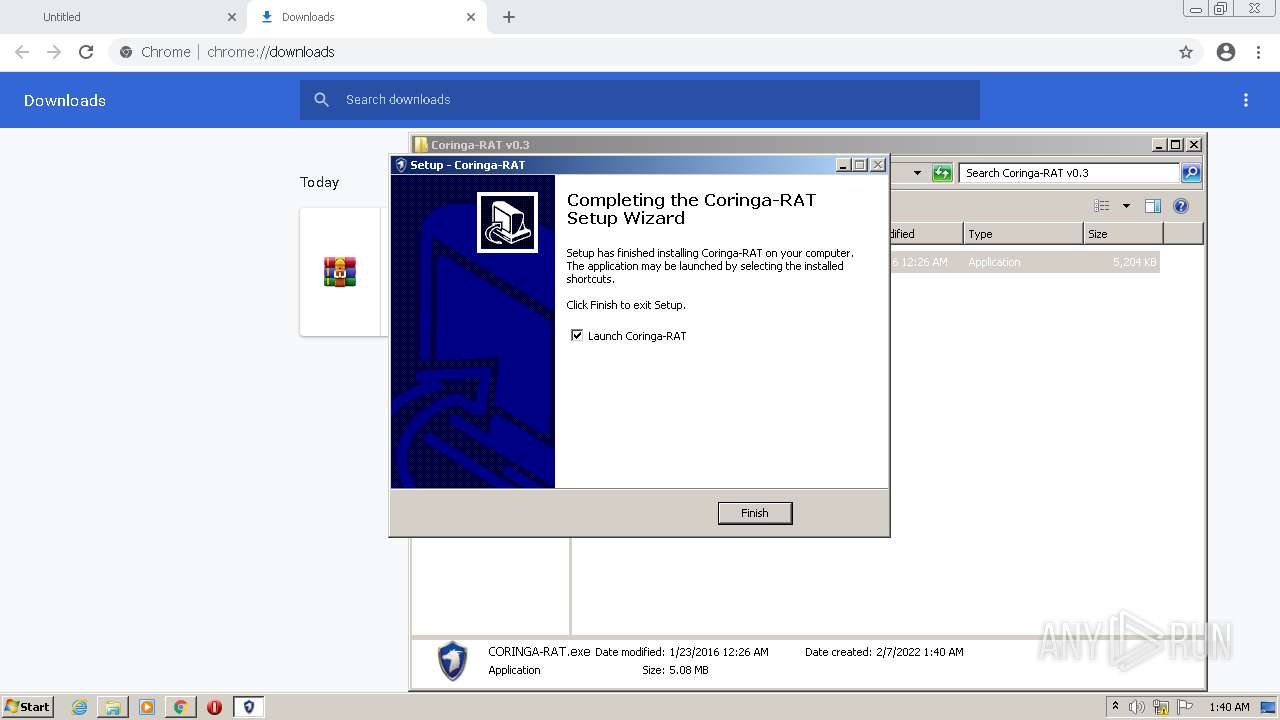
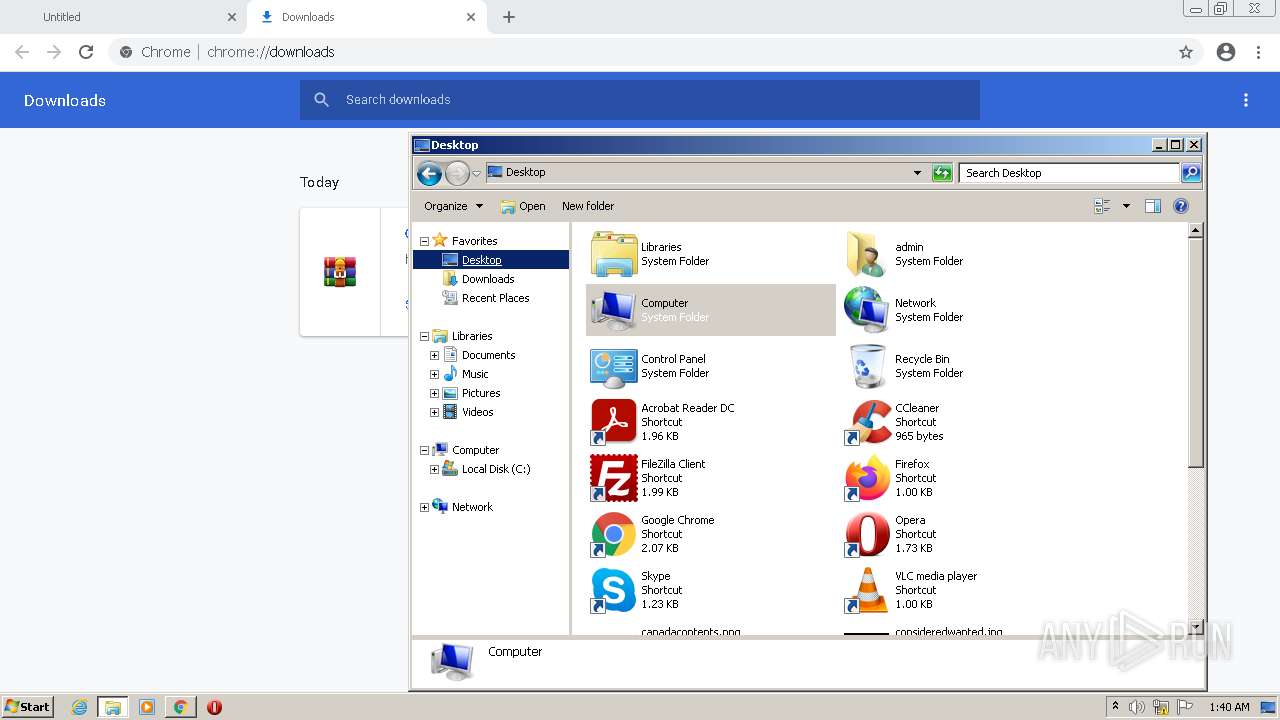
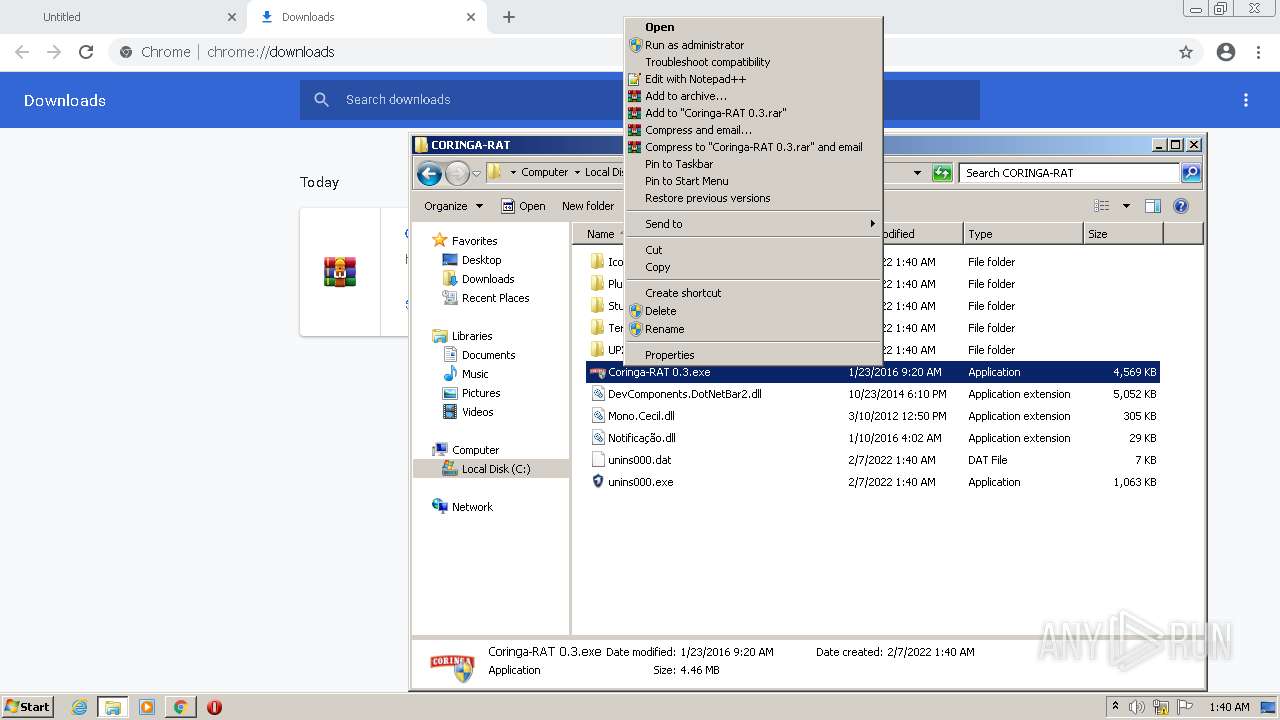
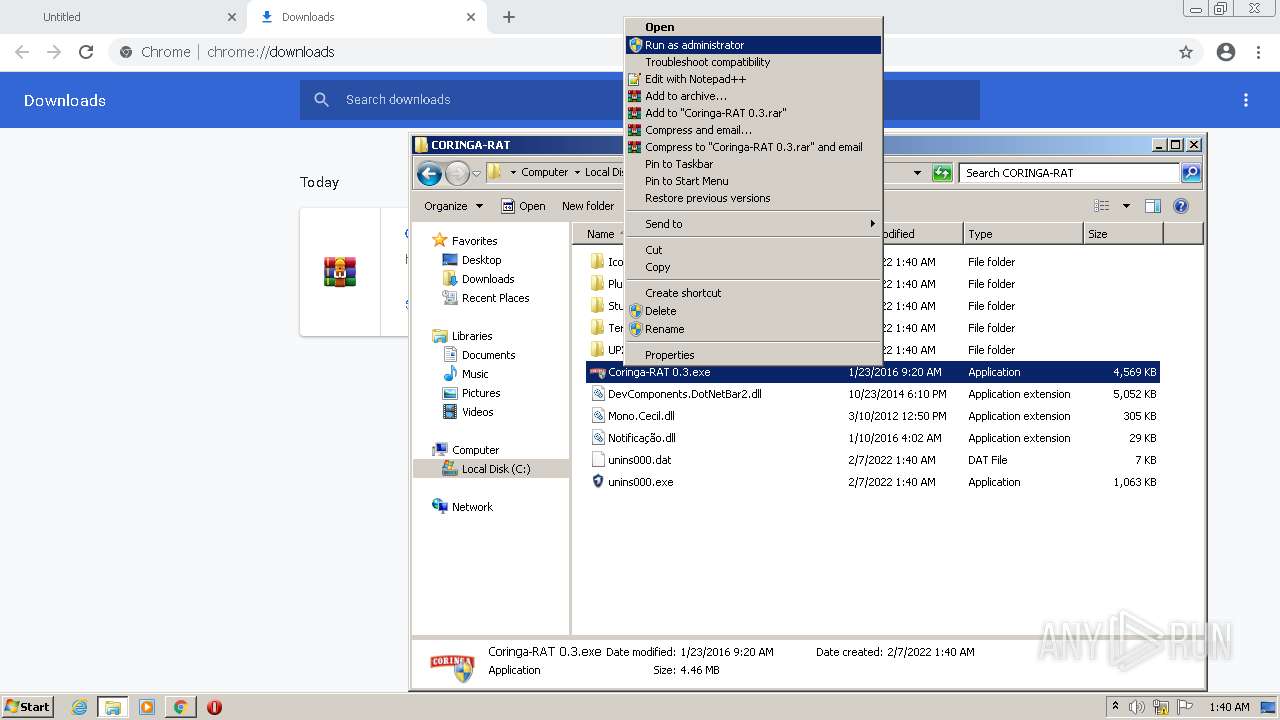
Manual execution by user
- WinRAR.exe (PID: 1120)
- CORINGA-RAT.exe (PID: 3980)
- Coringa-RAT 0.3.exe (PID: 1044)
Application was dropped or rewritten from another process
- CORINGA-RAT.tmp (PID: 1268)
- CORINGA-RAT.tmp (PID: 2076)
Loads dropped or rewritten executable
- CORINGA-RAT.tmp (PID: 2076)
Creates a software uninstall entry
- CORINGA-RAT.tmp (PID: 2076)
Reads the date of Windows installation
- chrome.exe (PID: 1136)
Creates files in the program directory
- CORINGA-RAT.tmp (PID: 2076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
67
Monitored processes
22
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,8420905723023492817,1863921715114014642,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1132 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,8420905723023492817,1863921715114014642,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1840 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,8420905723023492817,1863921715114014642,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1400 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1008 | "C:\Users\admin\Downloads\Coringa-RAT v0.3\CORINGA-RAT.exe" /SPAWNWND=$201E4 /NOTIFYWND=$201D8 | C:\Users\admin\Downloads\Coringa-RAT v0.3\CORINGA-RAT.exe | CORINGA-RAT.tmp | ||||||||||||
User: admin Company: Hacking.SooftT, Inc. Integrity Level: HIGH Description: Coringa-RAT Setup Exit code: 0 Version: Modules
| |||||||||||||||
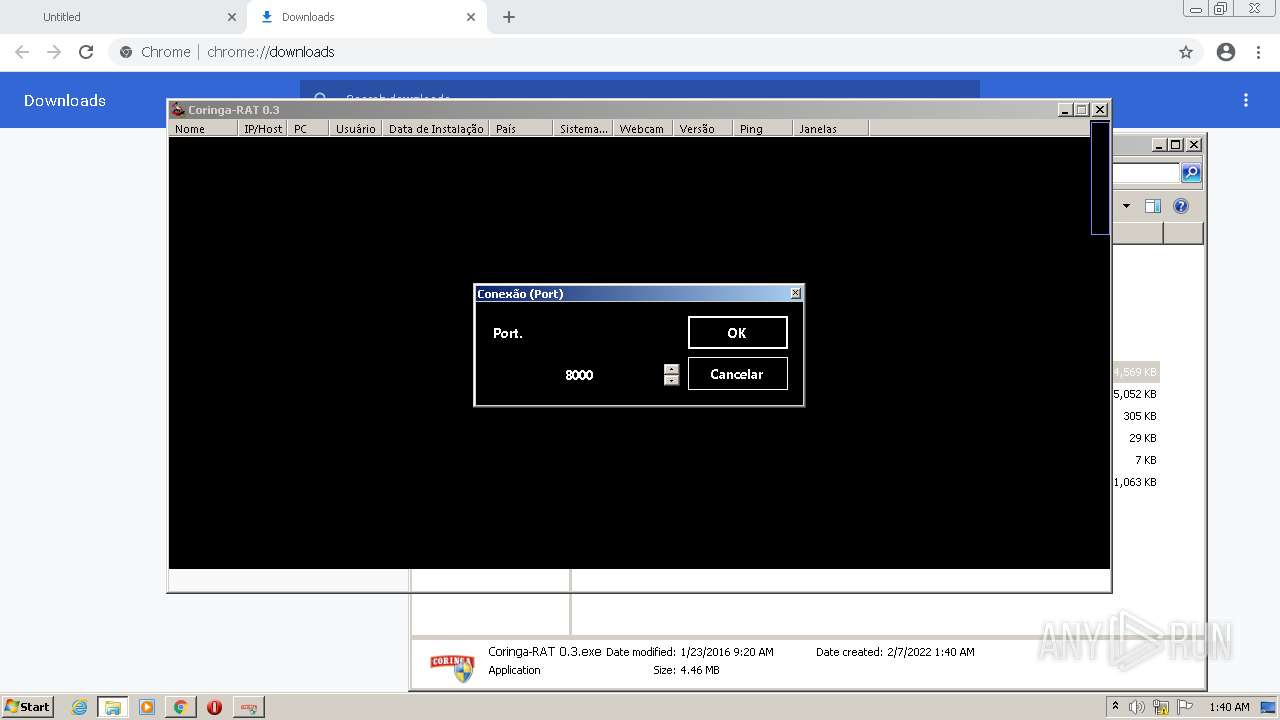
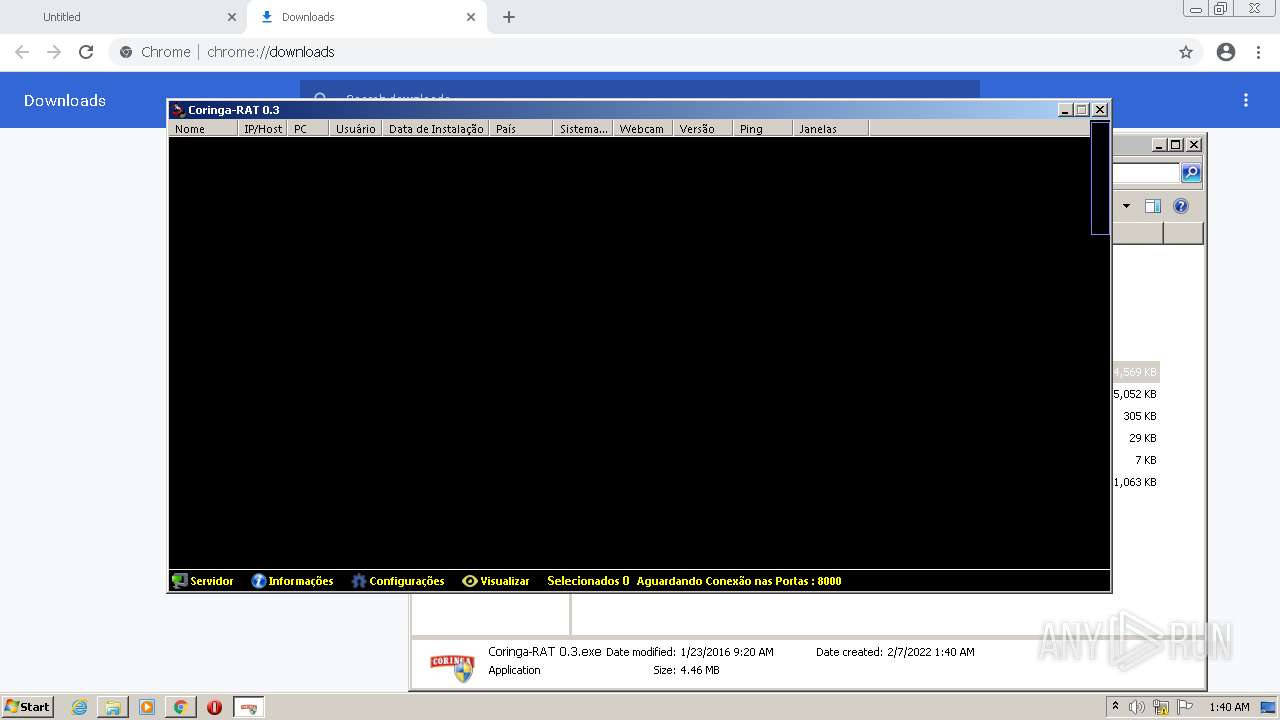
| 1044 | "C:\Program Files\CORINGA-RAT\Coringa-RAT 0.3.exe" | C:\Program Files\CORINGA-RAT\Coringa-RAT 0.3.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 0.0.0.3 Modules
| |||||||||||||||
| 1120 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Coringa-RAT v0.3.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,8420905723023492817,1863921715114014642,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1632 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1268 | "C:\Users\admin\AppData\Local\Temp\is-HUG5C.tmp\CORINGA-RAT.tmp" /SL5="$201D8,4893996,422400,C:\Users\admin\Downloads\Coringa-RAT v0.3\CORINGA-RAT.exe" | C:\Users\admin\AppData\Local\Temp\is-HUG5C.tmp\CORINGA-RAT.tmp | — | CORINGA-RAT.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1044,8420905723023492817,1863921715114014642,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1304 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,8420905723023492817,1863921715114014642,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2120 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
11 974
Read events
11 811
Write events
157
Delete events
6
Modification events
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
32
Suspicious files
24
Text files
188
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62007859-B28.pma | — | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFeda1f.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFeda10.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RFeda1f.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d277bcf2-3247-4e18-a955-353ab5bb91ef.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RFedb58.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RFedb48.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
12
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1492 | chrome.exe | 142.250.186.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
1492 | chrome.exe | 142.250.185.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
1492 | chrome.exe | 185.199.111.133:443 | raw.githubusercontent.com | GitHub, Inc. | NL | suspicious |
1492 | chrome.exe | 142.250.185.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1492 | chrome.exe | 142.250.186.110:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
1492 | chrome.exe | 216.58.212.163:443 | update.googleapis.com | Google Inc. | US | whitelisted |
884 | svchost.exe | 34.104.35.123:80 | edgedl.me.gvt1.com | — | US | whitelisted |
1492 | chrome.exe | 140.82.121.4:443 | github.com | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
github.com |
| malicious |
raw.githubusercontent.com |
| shared |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
safebrowsing.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |