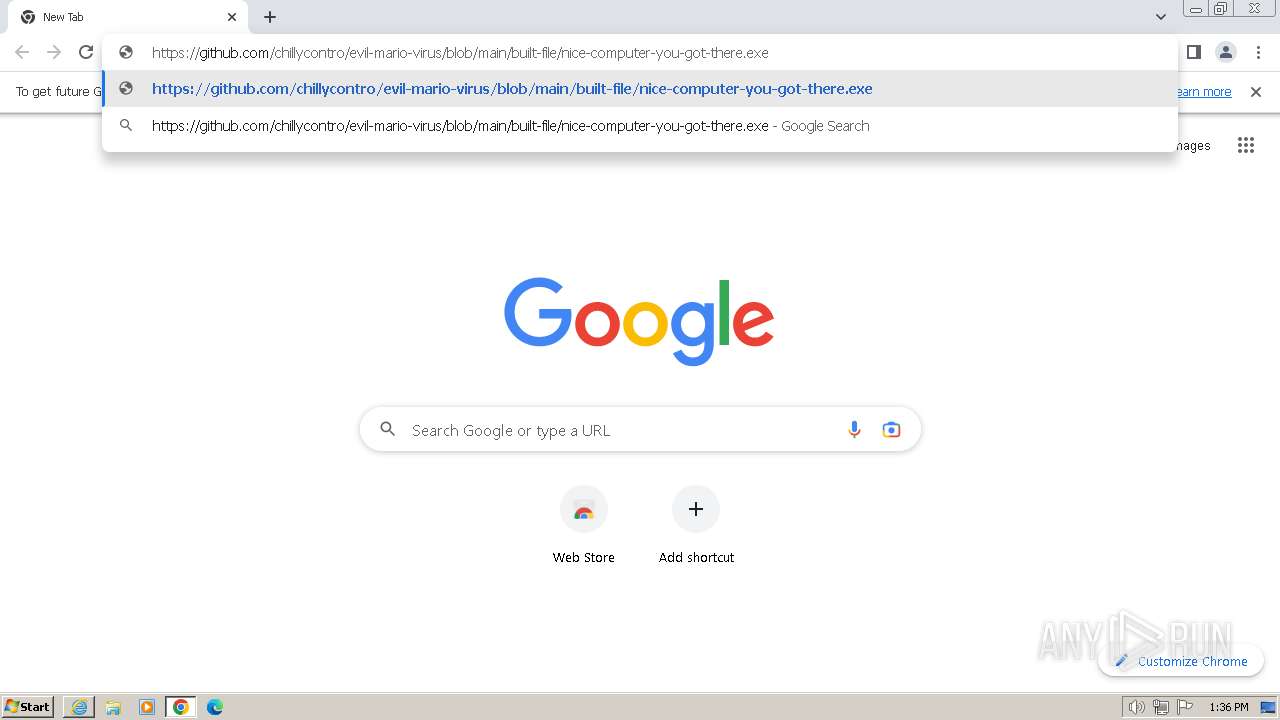
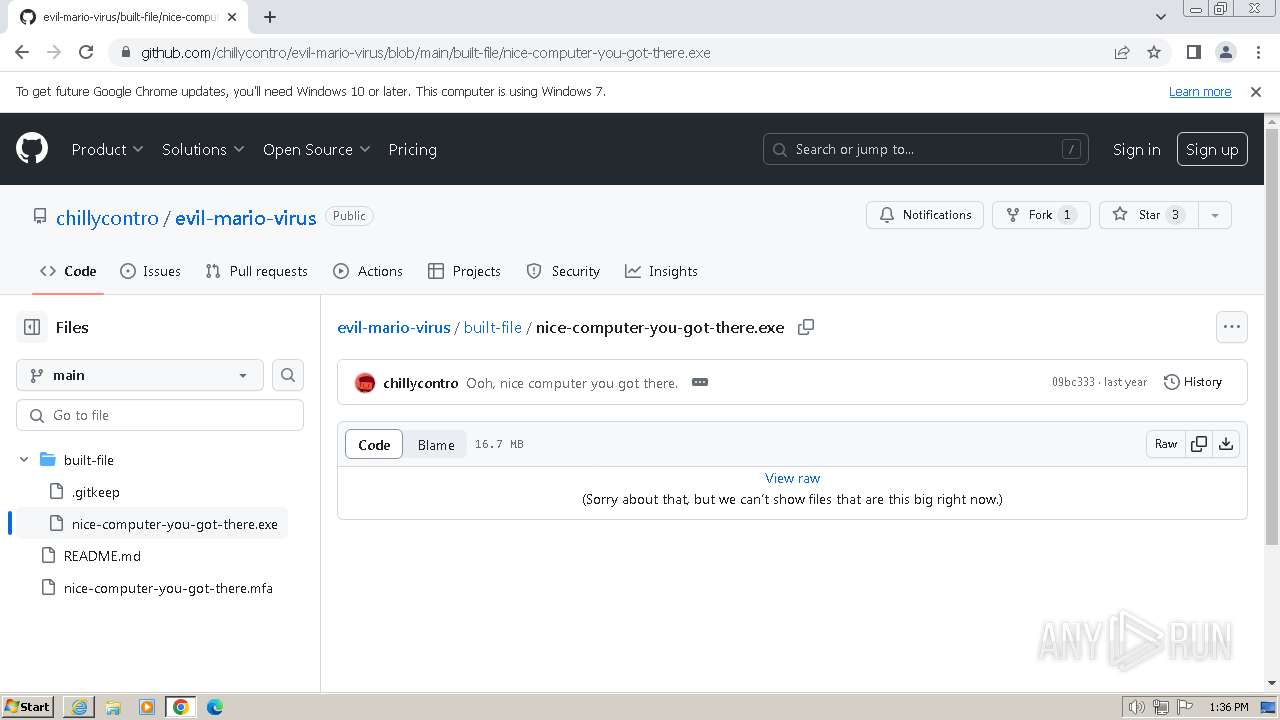
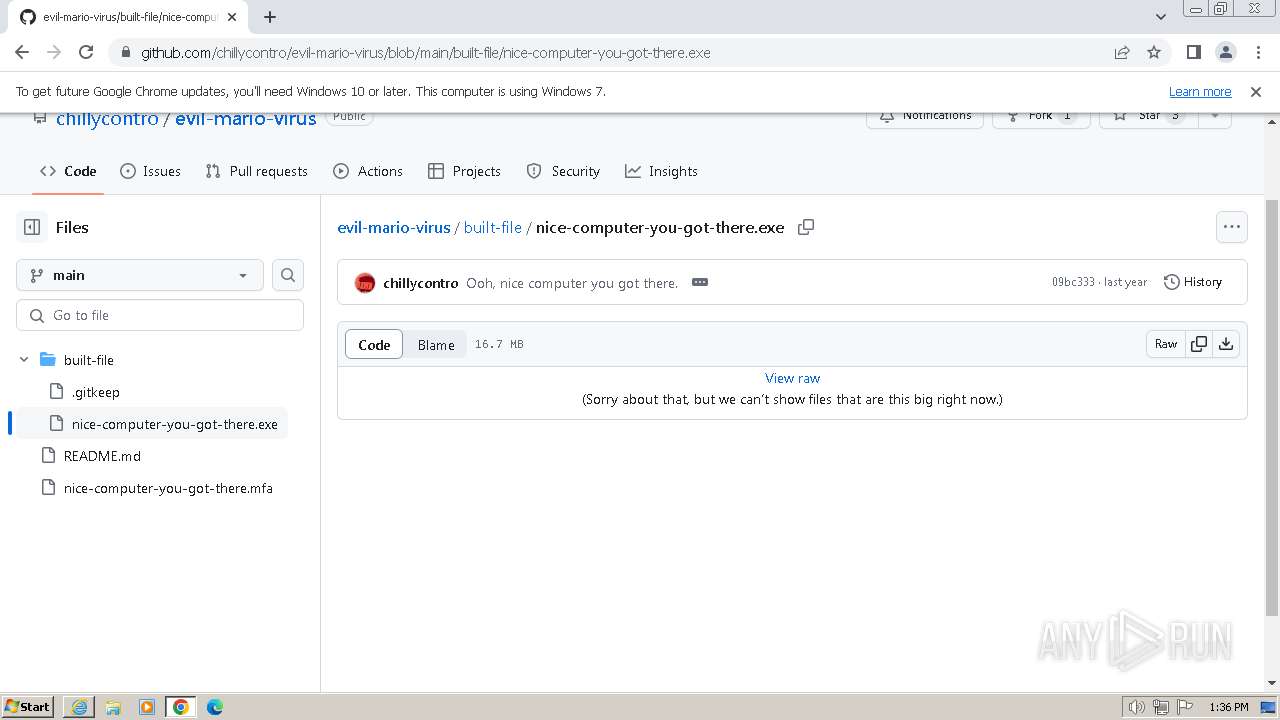
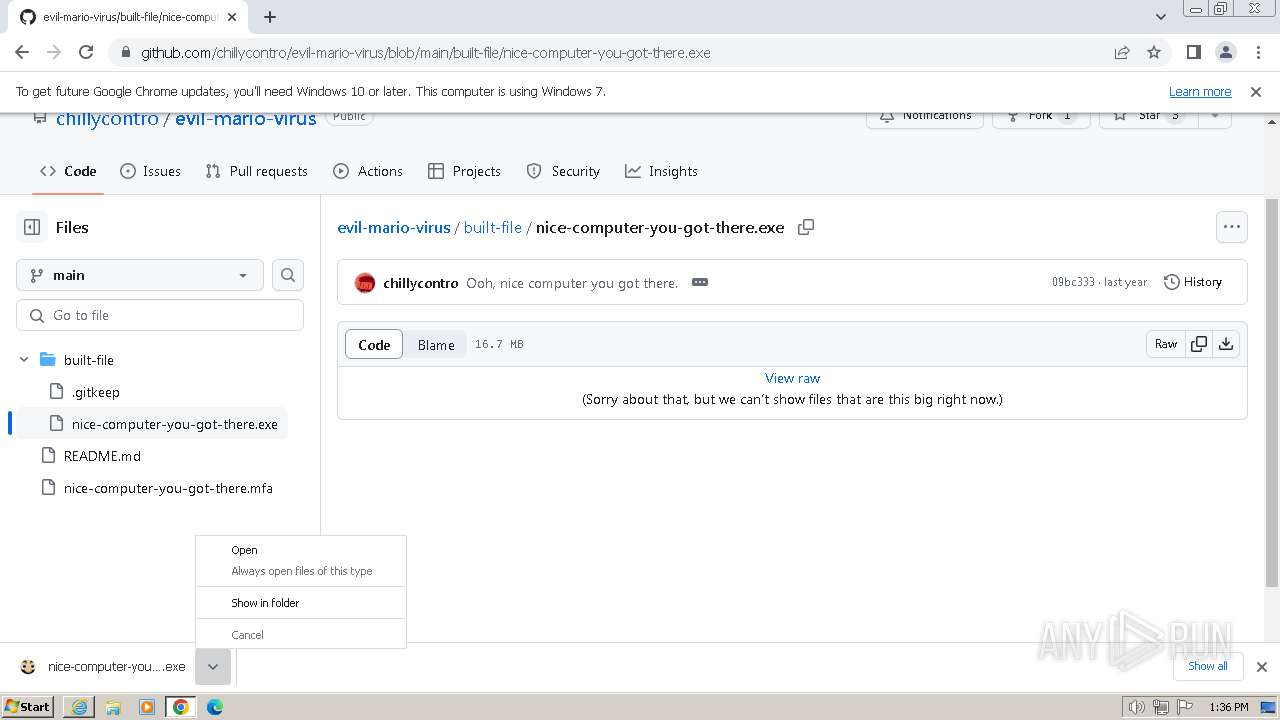
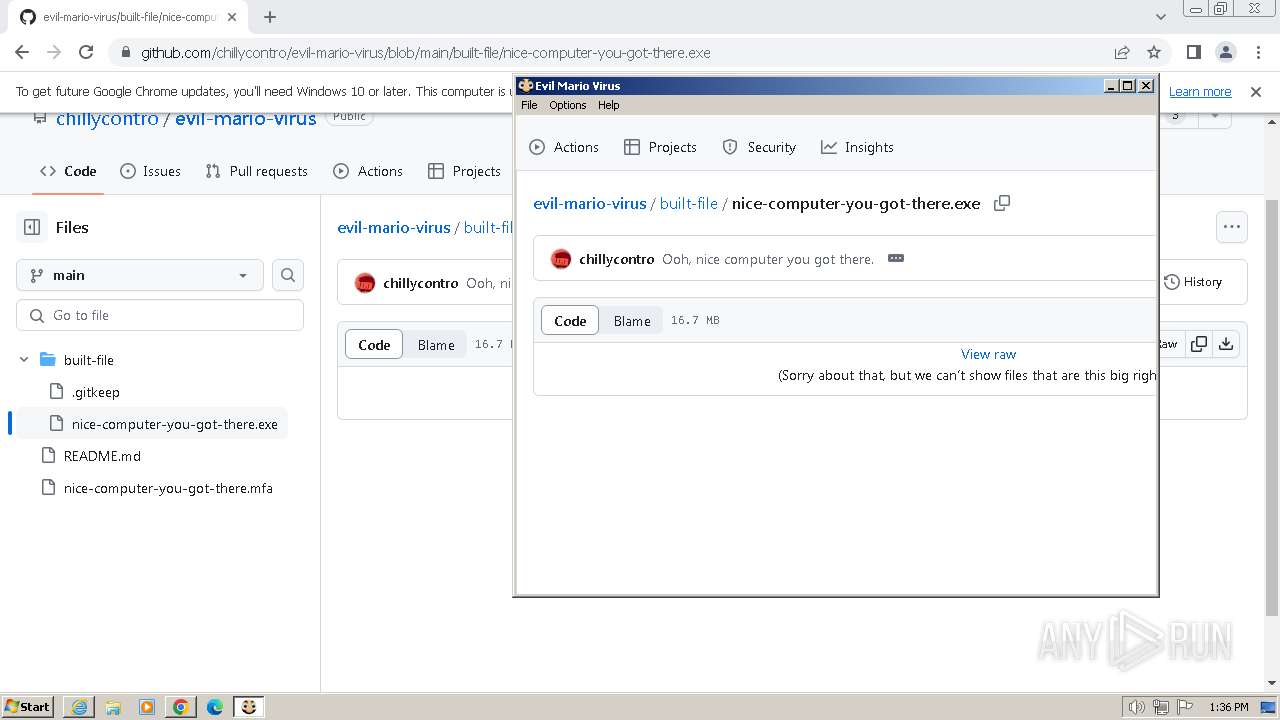
| URL: | https://github.com/chillycontro/evil-mario-virus/blob/main/built-file/nice-computer-you-got-there.exe |
| Full analysis: | https://app.any.run/tasks/e4b882f7-7978-4a3a-8a61-c28e1f2937ed |
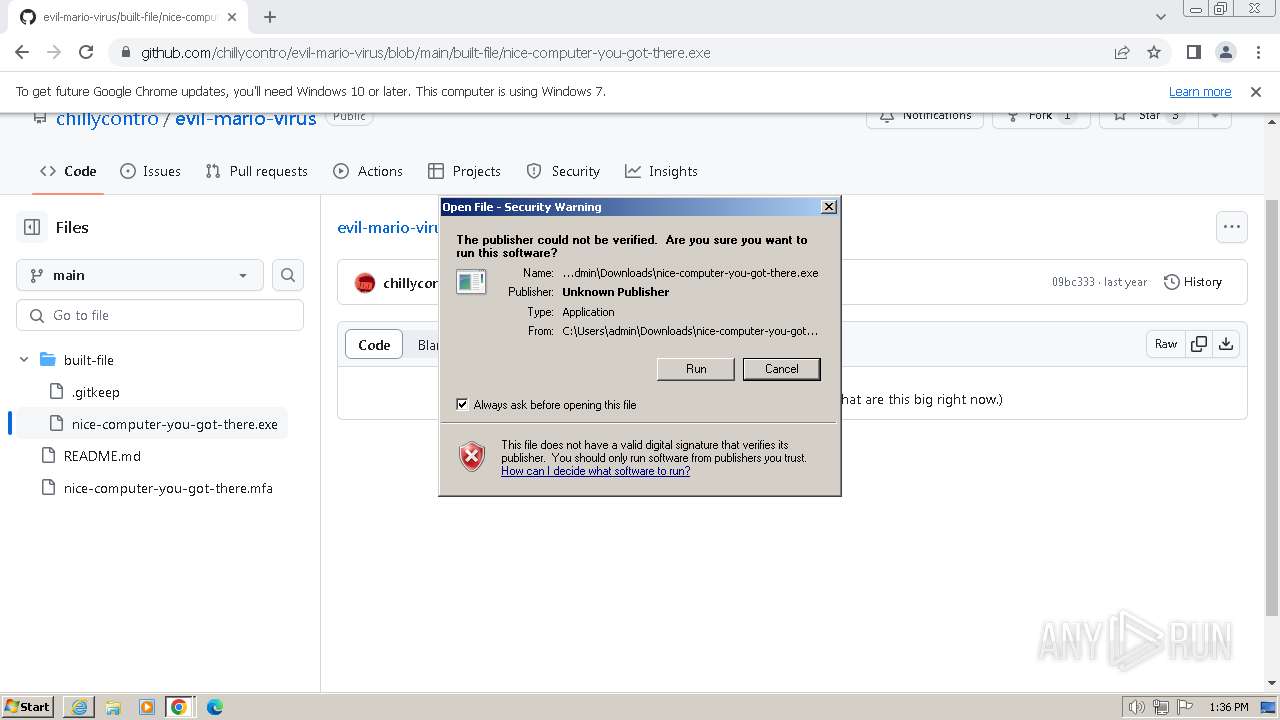
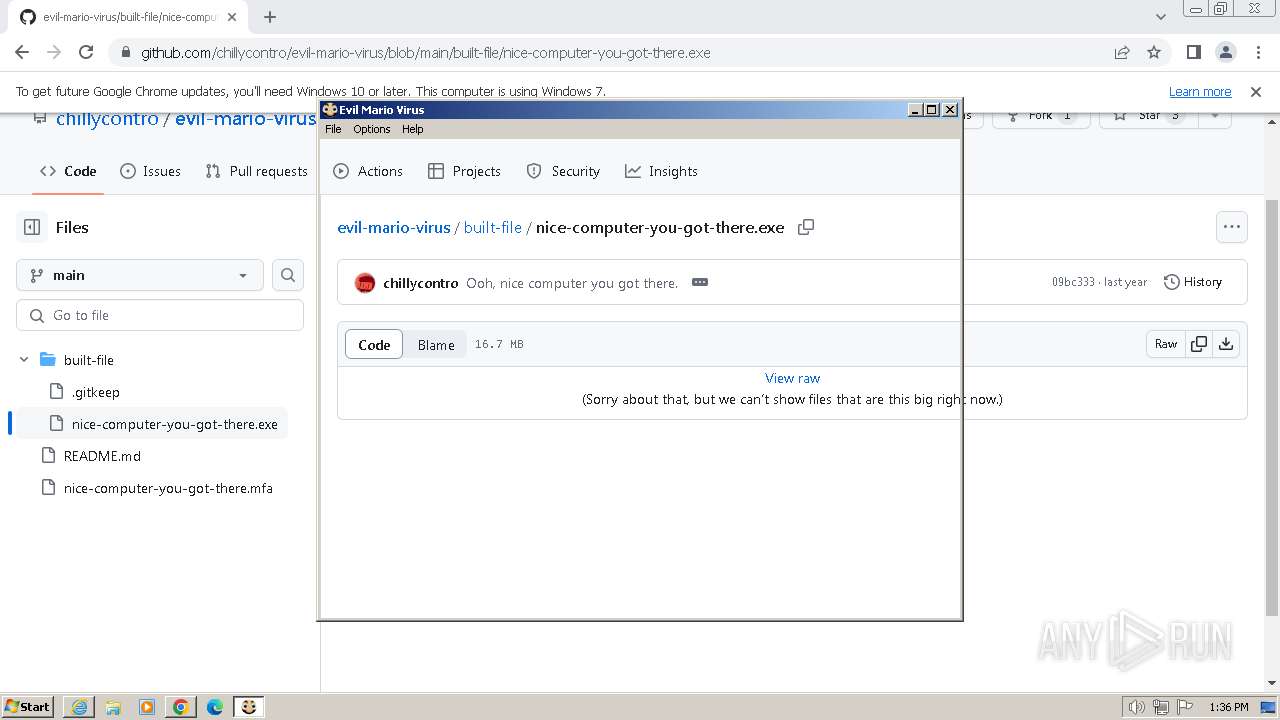
| Verdict: | Malicious activity |
| Analysis date: | December 27, 2023, 13:35:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | EDB2FFFB1A2042B333CE0BBB61742BD2 |
| SHA1: | A57D667BE6CE52DB015FBBF34458D194599B2B8C |
| SHA256: | 69730D89BB5F2A9C59253B1D7FD4B008E7541487295F9FF61CE1D64513B45B5B |
| SSDEEP: | 3:N8tEd2NMH6LxmT3vAyERw+iIZAxKQSBan:2ugNMH6qvAysg6pBan |
MALICIOUS
Steals credentials from Web Browsers
- taskhost.exe (PID: 3100)
- setup.exe (PID: 3976)
Changes the autorun value in the registry
- unregmp2.exe (PID: 3452)
- regsvr32.exe (PID: 3600)
Create files in the Startup directory
- regsvr32.exe (PID: 3600)
SUSPICIOUS
Reads Internet Explorer settings
- ie4uinit.exe (PID: 1124)
Reads the Internet Settings
- ie4uinit.exe (PID: 1124)
- rundll32.exe (PID: 3136)
- taskhost.exe (PID: 3100)
- rundll32.exe (PID: 3372)
- ie4uinit.exe (PID: 3676)
- ie4uinit.exe (PID: 3732)
Changes internet zones settings
- ie4uinit.exe (PID: 1124)
Uses RUNDLL32.EXE to load library
- ie4uinit.exe (PID: 1124)
- rundll32.exe (PID: 3136)
Reads Microsoft Outlook installation path
- ie4uinit.exe (PID: 1124)
Changes default file association
- unregmp2.exe (PID: 3452)
Write to the desktop.ini file (may be used to cloak folders)
- ie4uinit.exe (PID: 1124)
- unregmp2.exe (PID: 3452)
- regsvr32.exe (PID: 3600)
Reads settings of System Certificates
- sipnotify.exe (PID: 2496)
INFO
Application launched itself
- iexplore.exe (PID: 124)
- chrome.exe (PID: 2620)
- ie4uinit.exe (PID: 1124)
- rundll32.exe (PID: 3136)
- chrmstp.exe (PID: 3876)
- chrmstp.exe (PID: 1168)
- setup.exe (PID: 3976)
- msedge.exe (PID: 4076)
Drops the executable file immediately after the start
- chrome.exe (PID: 2404)
- nice-computer-you-got-there.exe (PID: 3900)
- chrome.exe (PID: 2620)
The process uses the downloaded file
- chrome.exe (PID: 2620)
- chrome.exe (PID: 2768)
Reads the computer name
- nice-computer-you-got-there.exe (PID: 3900)
- setup.exe (PID: 3348)
- setup.exe (PID: 924)
- IMEKLMG.EXE (PID: 3068)
- IMEKLMG.EXE (PID: 3544)
- wmpnscfg.exe (PID: 1776)
- wmpnscfg.exe (PID: 2256)
Manual execution by a user
- chrome.exe (PID: 2620)
- ie4uinit.exe (PID: 1124)
- ie4uinit.exe (PID: 3676)
- unregmp2.exe (PID: 3452)
- ie4uinit.exe (PID: 3732)
- chrmstp.exe (PID: 1168)
- setup.exe (PID: 3976)
- regsvr32.exe (PID: 3600)
- IMEKLMG.EXE (PID: 3544)
- wmpnscfg.exe (PID: 2256)
- wmpnscfg.exe (PID: 1776)
- IMEKLMG.EXE (PID: 3068)
Executes as Windows Service
- taskhost.exe (PID: 3100)
- EOSNotify.exe (PID: 2088)
Checks supported languages
- nice-computer-you-got-there.exe (PID: 3900)
- setup.exe (PID: 3348)
- setup.exe (PID: 924)
- setup.exe (PID: 3976)
- IMEKLMG.EXE (PID: 3544)
- IMEKLMG.EXE (PID: 3068)
- IMKRMIG.EXE (PID: 3456)
- wmpnscfg.exe (PID: 1776)
- wmpnscfg.exe (PID: 2256)
The process executes via Task Scheduler
- sipnotify.exe (PID: 2496)
Create files in a temporary directory
- nice-computer-you-got-there.exe (PID: 3900)
Reads security settings of Internet Explorer
- ie4uinit.exe (PID: 1124)
- sipnotify.exe (PID: 2496)
Creates files in the program directory
- ie4uinit.exe (PID: 1124)
- setup.exe (PID: 3348)
- chrmstp.exe (PID: 1168)
- setup.exe (PID: 3976)
- setup.exe (PID: 924)
- chrmstp.exe (PID: 3876)
Process checks are UAC notifies on
- IMEKLMG.EXE (PID: 3544)
- IMEKLMG.EXE (PID: 3068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
102
Monitored processes
56
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://github.com/chillycontro/evil-mario-virus/blob/main/built-file/nice-computer-you-got-there.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1073807364 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3612 --field-trial-handle=1200,i,10001080234903040669,10074260923991646665,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 548 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1260 --field-trial-handle=1300,i,1316802875711040264,2922886012659368562,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Microsoft\Edge\Application\109.0.1518.115\Installer\setup.exe" --msedge --channel=stable --launch-msedge-after-unlock --verbose-logging --system-level | C:\Program Files\Microsoft\Edge\Application\109.0.1518.115\Installer\setup.exe | — | setup.exe | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Installer Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=2324 --field-trial-handle=1200,i,10001080234903040669,10074260923991646665,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1124 | "C:\Windows\System32\ie4uinit.exe" -UserConfig | C:\Windows\System32\ie4uinit.exe | — | explorer.exe | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: IE Per-User Initialization Utility Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Google\Chrome\Application\109.0.5414.120\Installer\chrmstp.exe" --configure-user-settings --verbose-logging --system-level | C:\Program Files\Google\Chrome\Application\109.0.5414.120\Installer\chrmstp.exe | — | explorer.exe | |||||||||||
User: Administrator Company: Google LLC Integrity Level: HIGH Description: Google Chrome Installer Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1612 --field-trial-handle=1200,i,10001080234903040669,10074260923991646665,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1776 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6a4d8b38,0x6a4d8b48,0x6a4d8b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 1073807364 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
29 236
Read events
28 263
Write events
964
Delete events
9
Modification events
| (PID) Process: | (124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
19
Suspicious files
261
Text files
245
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2204 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\repository-2e5f0ce2e282[1].css | text | |
MD5:BC97299DCBF4929F31487D9558C23CD7 | SHA256:5827C8559316C0479EADD631DFDD27DA20B69370329802A91FEC2BD92EF2EDDA | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\dark-56010aa53a8f[1].css | text | |
MD5:7110FBC4050DE42CAE72D8A68F513BE9 | SHA256:75564BC9CEA3F9A261DA3423633C1E235CFF36AD4656C0053136567FC512716C | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\wp-runtime-baca81ae4722[1].js | text | |
MD5:2F863BA21920FCAAB2B8BFA6C341EE87 | SHA256:192E5909155985A8F41F62509FFA8FC0038C3B97202EDADE48F7A110467616A2 | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\vendors-node_modules_stacktrace-parser_dist_stack-trace-parser_esm_js-node_modules_github_bro-a4c183-79f9611c275b[1].js | text | |
MD5:0EBF88B18838CA3926ECE77027C1A096 | SHA256:452A443EFADF60DA1B19B9BF50D6CBBB25AB9441A3E9FE73B678D9CD486D80B6 | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\github-9ed33716809f[1].css | text | |
MD5:A73A04919D3934755B5E41F0C2417616 | SHA256:2FC6FE36E52251D5184230BAFA10A9E6EC14A971A5FE64F0EFE52ED2C3A73ED9 | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\code-8f92bf8847ed[1].css | text | |
MD5:D2578BEC62BB230BCF9292EA55B46000 | SHA256:1D989270098F39457DE7B9494B625E97A0F38051A42A56909C5DA22C899847D1 | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_ADE4E4D3A3BCBCA5C39C54D362D88565 | binary | |
MD5:AEBB224F06DB9B6B3BDA15249DF5D8F6 | SHA256:4AB4D56A8D44700F5932505EF58B46BC5CB7422EB6F4B1973CB1E972C0298506 | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\50CD3D75D026C82E2E718570BD6F44D0_D222662A57BAA60D2F5EA0D2CC7B2F1C | binary | |
MD5:B6E6E393477622D72E918C63ED09BCE3 | SHA256:FB8173332D4252181882BF43B09AA120D81A5FCF0EE6F3E2FB9C500A2FC85F3C | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\QQDHICYI.txt | text | |
MD5:F2D27CC785BB8FD02E9DB99C3A13F00C | SHA256:3E053045F3E58F884037BFB14AAF12366D546DAC13F4248160378C646BADDDEF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
64
DNS requests
64
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2204 | iexplore.exe | GET | 200 | 178.79.208.1:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?53bfb7cf8a6cf97e | unknown | compressed | 4.66 Kb | unknown |
2204 | iexplore.exe | GET | 200 | 178.79.208.1:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6b21170b0e7a1648 | unknown | compressed | 4.66 Kb | unknown |
2204 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAfy81yHqHeveu%2FpR5k1Jb0%3D | unknown | binary | 471 b | unknown |
2204 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrHR6YzPN2BNbByL0VoiTIBBMAOAQUCrwIKReMpTlteg7OM8cus%2B37w3oCEAzQqL7GMs%2FmReygqbCE%2Bxw%3D | unknown | binary | 312 b | unknown |
2204 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | binary | 471 b | unknown |
124 | iexplore.exe | GET | 304 | 178.79.208.1:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?1a6e676fbb64f2cc | unknown | — | — | unknown |
124 | iexplore.exe | GET | 304 | 178.79.208.1:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a85e8d0c2f0a71a5 | unknown | — | — | unknown |
124 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 314 b | unknown |
124 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
124 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2204 | iexplore.exe | 140.82.121.4:443 | github.com | GITHUB | US | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2204 | iexplore.exe | 178.79.208.1:80 | ctldl.windowsupdate.com | LLNW | NL | unknown |
2204 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2204 | iexplore.exe | 185.199.109.154:443 | github.githubassets.com | FASTLY | US | unknown |
124 | iexplore.exe | 185.199.109.154:443 | github.githubassets.com | FASTLY | US | unknown |
124 | iexplore.exe | 178.79.208.1:80 | ctldl.windowsupdate.com | LLNW | NL | unknown |
124 | iexplore.exe | 23.37.226.90:443 | www.bing.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |
user-images.githubusercontent.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |