| download: | 1.exe |
| Full analysis: | https://app.any.run/tasks/14d49e1a-75ee-4572-8af2-86cade3947f1 |
| Verdict: | Malicious activity |
| Analysis date: | January 11, 2019, 09:26:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DCB9CB3ABC689F8C0EB39AF6429C1C2F |
| SHA1: | 888488CC2D88BF6221813583195E43D6B240F408 |
| SHA256: | 6966599B3A7786F81A960F012D540866ADA63A1FEF5BE6D775946A47F6983CB7 |
| SSDEEP: | 3072:S5mBBAQLszJ0dYqqnSDCYi/v2rtXxMTAIC91+Z:SIBBgtVSPxGA0Z |
MALICIOUS
Task Manager has been disabled (taskmgr)
- 1.exe (PID: 2332)
SUSPICIOUS
Application launched itself
- 1.exe (PID: 2908)
- powershell.exe (PID: 2436)
Creates files in the user directory
- powershell.exe (PID: 3400)
- powershell.exe (PID: 2892)
- powershell.exe (PID: 2436)
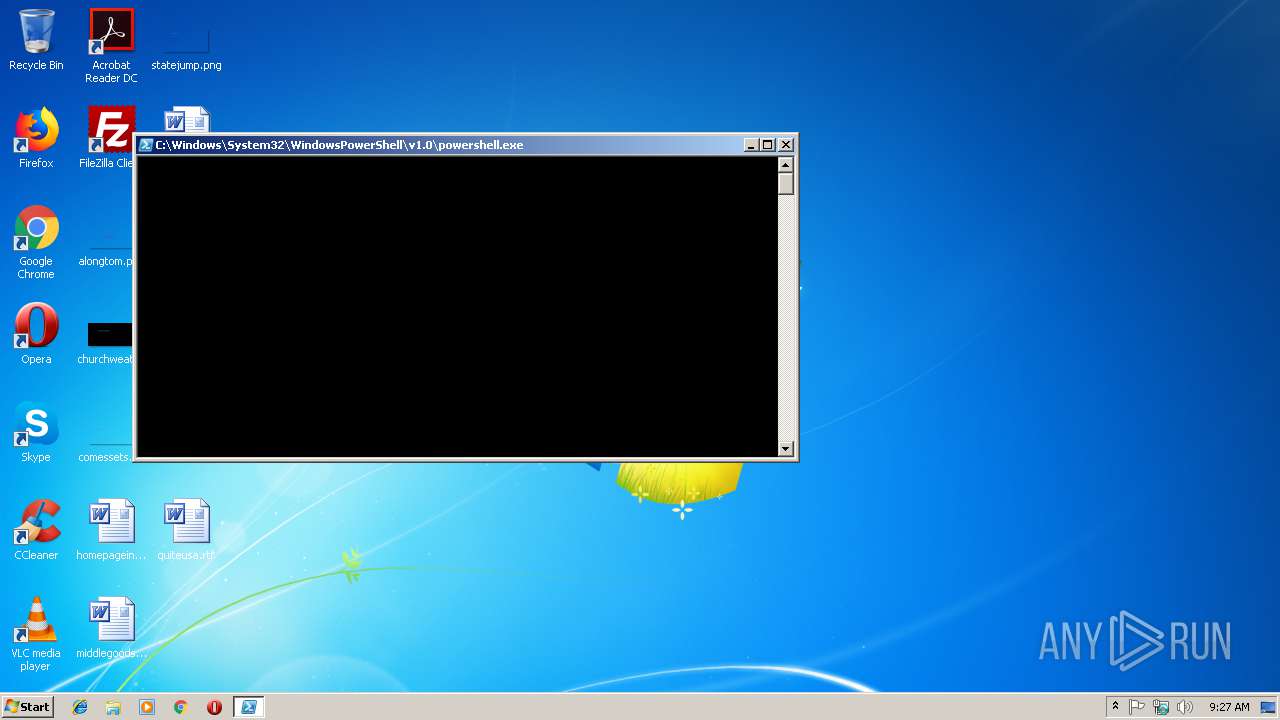
Executes PowerShell scripts
- powershell.exe (PID: 2436)
- 1.exe (PID: 2332)
Starts CMD.EXE for commands execution
- 1.exe (PID: 2332)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:11:06 15:23:02+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.15 |
| CodeSize: | 54272 |
| InitializedDataSize: | 132608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x23f7 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Nov-2018 14:23:02 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 06-Nov-2018 14:23:02 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000D2F5 | 0x0000D400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.61019 |
.rdata | 0x0000F000 | 0x00006B32 | 0x00006C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.78616 |
.data | 0x00016000 | 0x0000155C | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.25531 |
.rsrc | 0x00018000 | 0x000171E8 | 0x00017200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.03296 |
.reloc | 0x00030000 | 0x00001028 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.19725 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.26975 | 3752 | UNKNOWN | Russian - Russia | RT_ICON |
3 | 2.1346 | 2216 | UNKNOWN | Russian - Russia | RT_ICON |
4 | 1.398 | 1384 | UNKNOWN | Russian - Russia | RT_ICON |
5 | 7.34276 | 2315 | UNKNOWN | Russian - Russia | RT_ICON |
6 | 2.68124 | 16936 | UNKNOWN | Russian - Russia | RT_ICON |
7 | 1.81119 | 64 | UNKNOWN | Russian - Russia | RT_STRING |
8 | 2.82161 | 4264 | UNKNOWN | Russian - Russia | RT_ICON |
9 | 2.9458 | 1128 | UNKNOWN | Russian - Russia | RT_ICON |
10 | 6.40514 | 4442 | UNKNOWN | Russian - Russia | RT_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHELL32.dll |
SHLWAPI.dll |
Total processes
44
Monitored processes
7
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2280 | "C:\Program Files\Windows Defender\mpcmdrun.exe" -removedefinitions -all | C:\Program Files\Windows Defender\mpcmdrun.exe | — | 1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Malware Protection Command Line Utility Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2332 | "C:\Users\admin\AppData\Local\Temp\1.exe" --Admin | C:\Users\admin\AppData\Local\Temp\1.exe | 1.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2372 | cmd /c ""C:\Users\admin\AppData\Local\Temp\delself.bat"" | C:\Windows\system32\cmd.exe | — | 1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2436 | powershell -NoProfile -ExecutionPolicy Bypass -Command "& {Start-Process PowerShell -ArgumentList '-NoProfile -ExecutionPolicy Bypass -File ""C:\Users\admin\AppData\Local\script.ps1""' -Verb RunAs}" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | 1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2892 | powershell -Command Set-ExecutionPolicy -Scope CurrentUser RemoteSigned | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | 1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2908 | "C:\Users\admin\AppData\Local\Temp\1.exe" | C:\Users\admin\AppData\Local\Temp\1.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3400 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\script.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 062
Read events
886
Write events
176
Delete events
0
Modification events
| (PID) Process: | (2908) 1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2908) 1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2892) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2892) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\PowerShell\1\ShellIds\Microsoft.PowerShell |
| Operation: | write | Name: | ExecutionPolicy |
Value: RemoteSigned | |||
| (PID) Process: | (2436) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2436) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2436) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2332) 1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (2332) 1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskmgr |
Value: 1 | |||
| (PID) Process: | (3400) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
6
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2892 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\RM2T1FFKNLKD0H2JJ0XX.temp | — | |
MD5:— | SHA256:— | |||
| 2436 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\BF5WW63GMEV0W65SFMTQ.temp | — | |
MD5:— | SHA256:— | |||
| 2332 | 1.exe | C:\Users\admin\AppData\Local\Temp\delself.bat | — | |
MD5:— | SHA256:— | |||
| 3400 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\9RW9QGQMF02Z3SMT6E06.temp | — | |
MD5:— | SHA256:— | |||
| 2280 | mpcmdrun.exe | C:\Users\admin\AppData\Local\Temp\MpCmdRun.log | text | |
MD5:— | SHA256:— | |||
| 3400 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF19a0e9.TMP | binary | |
MD5:— | SHA256:— | |||
| 2436 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2892 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1999b6.TMP | binary | |
MD5:— | SHA256:— | |||
| 2332 | 1.exe | C:\Users\admin\AppData\Local\script.ps1 | text | |
MD5:F972C62F986B5ED49AD7713D93BF6C9F | SHA256:B47F85974A7EC2FD5AA82D52F08EB0F6CEA7E596A98DD29E8B85B5C37BECA0A8 | |||
| 2436 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF199d4f.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report