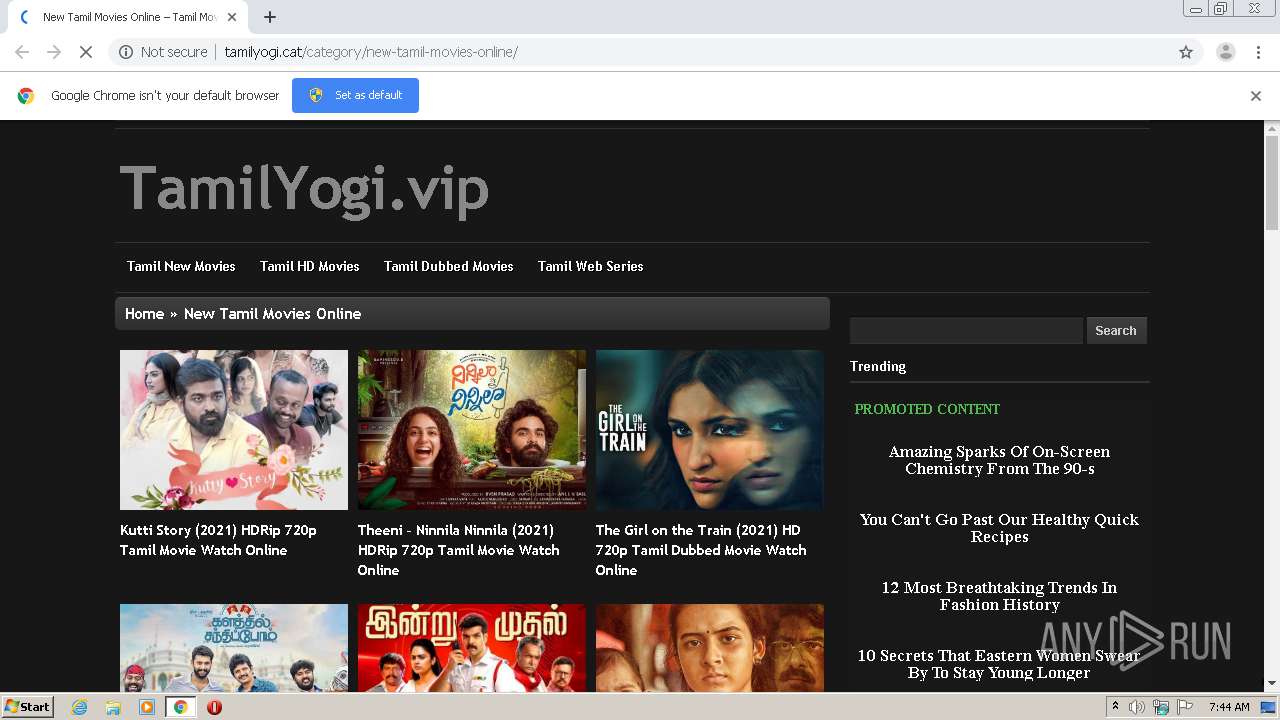
| URL: | http://tamilyogi.cat/category/new-tamil-movies-online/ |
| Full analysis: | https://app.any.run/tasks/1c49e17e-dd4f-4857-800c-480fbe1a82e5 |
| Verdict: | Malicious activity |
| Analysis date: | February 27, 2021, 07:44:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C1BDF715BF50BDE6AC953E20366E69D9 |
| SHA1: | CE280637D2E8BCBD6F1934A1FFB214444523D1C9 |
| SHA256: | 695AF8A8B7BB5E161CC899E4BF32A48983157FC314DFE69435E2546CED8223C5 |
| SSDEEP: | 3:N1KKExJGKTNl4Rw7Ju:CKaJG3Rw7o |
MALICIOUS
No malicious indicators.SUSPICIOUS
Drops a file with a compile date too recent
- chrome.exe (PID: 3316)
INFO
Application launched itself
- chrome.exe (PID: 3316)
Reads the hosts file
- chrome.exe (PID: 3316)
- chrome.exe (PID: 2796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
50
Monitored processes
11
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,16582659858037492649,8800130144963901532,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4216538034523322740 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,16582659858037492649,8800130144963901532,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11267232980719961501 --mojo-platform-channel-handle=3712 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6c23a9d0,0x6c23a9e0,0x6c23a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,16582659858037492649,8800130144963901532,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2275792615647284848 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2180 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,16582659858037492649,8800130144963901532,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11179415110345135957 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2176 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,16582659858037492649,8800130144963901532,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17262884310139369629 --mojo-platform-channel-handle=1024 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,16582659858037492649,8800130144963901532,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=4718676687215809693 --mojo-platform-channel-handle=1268 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,16582659858037492649,8800130144963901532,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=13047361098448565361 --mojo-platform-channel-handle=1560 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3200 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://tamilyogi.cat/category/new-tamil-movies-online/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
597
Read events
534
Write events
60
Delete events
3
Modification events
| (PID) Process: | (3316) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3316) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3316) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3316) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3052) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3316-13258885495530250 |
Value: 259 | |||
| (PID) Process: | (3316) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3316) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3316) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3316) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (3316) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
41
Text files
68
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6039F878-CF4.pma | — | |
MD5:— | SHA256:— | |||
| 3316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c7a66ab4-f8d3-4c82-9df8-3ad6668c8d4a.tmp | — | |
MD5:— | SHA256:— | |||
| 3316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:D4322EEBAC92D1B8F7A6F5E39F6264B7 | SHA256:A3EEDF21B850DCC7CE5AE04395ECDD2D29DA4EA549C8A185DD9E8B552A87B8C2 | |||
| 3316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:C2DDBA63E4A2BD2E39A8B6C2C6384AAE | SHA256:6D5C1C78341C6F84911055D970ADDB0EC3499F8BF7FADE062122A22209CE67D9 | |||
| 3316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFd8e56.TMP | text | |
MD5:D4322EEBAC92D1B8F7A6F5E39F6264B7 | SHA256:A3EEDF21B850DCC7CE5AE04395ECDD2D29DA4EA549C8A185DD9E8B552A87B8C2 | |||
| 3316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:1C97B70A4BAD7C026F79467C7D496AFA | SHA256:C5A02E4984DE3F30DADFC0A89A93F45418C06653C3962EAA94C93909E51D272D | |||
| 3316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFd9069.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
88
TCP/UDP connections
71
DNS requests
44
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2796 | chrome.exe | GET | 200 | 45.178.7.246:80 | http://tamilyogi.cat/wp-content/themes/tamilyogi/styles/dark.css?ver=5.6.2 | unknown | — | — | whitelisted |
2796 | chrome.exe | GET | 200 | 45.178.7.246:80 | http://tamilyogi.cat/wp-includes/js/jquery/jquery-migrate.min.js?ver=3.3.2 | unknown | text | 4.08 Kb | whitelisted |
2796 | chrome.exe | GET | 200 | 45.178.7.246:80 | http://tamilyogi.cat/wp-content/themes/tamilyogi/style.css | unknown | text | 8.77 Kb | whitelisted |
2796 | chrome.exe | GET | 200 | 45.178.7.246:80 | http://tamilyogi.cat/category/new-tamil-movies-online/ | unknown | html | 13.3 Kb | whitelisted |
2796 | chrome.exe | GET | 200 | 45.178.7.246:80 | http://tamilyogi.cat/wp-content/themes/tamilyogi/custom.css?ver=5.6.2 | unknown | text | 240 b | whitelisted |
2796 | chrome.exe | GET | 200 | 45.178.7.246:80 | http://tamilyogi.cat/wp-content/themes/tamilyogi/js/init.js?ver=5.6.2 | unknown | text | 1.57 Kb | whitelisted |
2796 | chrome.exe | GET | 200 | 45.178.7.246:80 | http://tamilyogi.cat/wp-content/uploads/2021/02/Kutti-Story-2021-HQ-DVDScr-Tamil-Full-Movie-Watch-Online.jpg | unknown | image | 36.3 Kb | whitelisted |
2796 | chrome.exe | GET | 200 | 45.178.7.246:80 | http://tamilyogi.cat/wp-content/themes/tamilyogi/js/script.js?ver=5.6.2 | unknown | text | 2.26 Kb | whitelisted |
2796 | chrome.exe | GET | 200 | 142.91.9.135:80 | http://video.your-notice.com/html_102017.js | NL | html | 1.85 Kb | whitelisted |
2796 | chrome.exe | GET | 200 | 45.178.7.246:80 | http://tamilyogi.cat/wp-content/plugins/wordpress-23-related-posts-plugin/static/themes/vertical-m.css?version=3.6.4 | unknown | text | 593 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2796 | chrome.exe | 139.45.197.15:80 | inpagepush.com | — | US | unknown |
2796 | chrome.exe | 45.178.7.246:80 | tamilyogi.cat | — | — | unknown |
2796 | chrome.exe | 142.250.185.205:443 | accounts.google.com | Google Inc. | US | suspicious |
2796 | chrome.exe | 142.250.186.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2796 | chrome.exe | 139.45.197.241:80 | cdn.itphanpytor.club | — | US | suspicious |
2796 | chrome.exe | 142.250.185.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
2796 | chrome.exe | 139.45.195.8:80 | cdn.betgorebysson.club | — | US | suspicious |
2796 | chrome.exe | 185.156.202.211:443 | m.mstorer.net | Amberway Development LTD | BZ | suspicious |
2796 | chrome.exe | 216.59.56.9:443 | displayvertising.com | Total Uptime Technologies, LLC | US | unknown |
2796 | chrome.exe | 104.17.167.186:443 | c.adsco.re | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tamilyogi.cat |
| unknown |
accounts.google.com |
| shared |
inpagepush.com |
| whitelisted |
s.w.org |
| whitelisted |
jsc.adskeeper.com |
| suspicious |
video.your-notice.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
www.displayvertising.com |
| suspicious |
cdn.itphanpytor.club |
| whitelisted |
cdn.betgorebysson.club |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2796 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
2796 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |