| File name: | CCSetup.exe |
| Full analysis: | https://app.any.run/tasks/0c6a5c2a-695f-4bd2-a762-d29350f87c63 |
| Verdict: | Malicious activity |
| Analysis date: | October 16, 2021, 13:37:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DA8725FFE858355E550D11D65B0623F4 |
| SHA1: | EDA96106E9F0316D464854535DCEAC9BF9A35B50 |
| SHA256: | 6955798C828DE55B53B8991DA5DDE634A24BC711D258602B72F259707E629D5B |
| SSDEEP: | 98304:ZwXioIPCfxoMEJnGU2qqqpn/ZPuV426nU:YiJP2RaRPur6U |
MALICIOUS
Changes the autorun value in the registry
- CCSetup.exe (PID: 776)
Drops executable file immediately after starts
- CCSetup.exe (PID: 3872)
SUSPICIOUS
Checks supported languages
- CCSetup.exe (PID: 3872)
- CCSetup.exe (PID: 776)
Reads the computer name
- CCSetup.exe (PID: 776)
- CCSetup.exe (PID: 3872)
Drops a file that was compiled in debug mode
- CCSetup.exe (PID: 3872)
Executable content was dropped or overwritten
- CCSetup.exe (PID: 3872)
Starts itself from another location
- CCSetup.exe (PID: 3872)
INFO
Reads settings of System Certificates
- CCSetup.exe (PID: 776)
Checks Windows Trust Settings
- CCSetup.exe (PID: 776)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:11:23 01:55:36+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 614400 |
| InitializedDataSize: | 776704 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5851a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.54.0 |
| ProductVersionNumber: | 1.0.54.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | RCS LT |
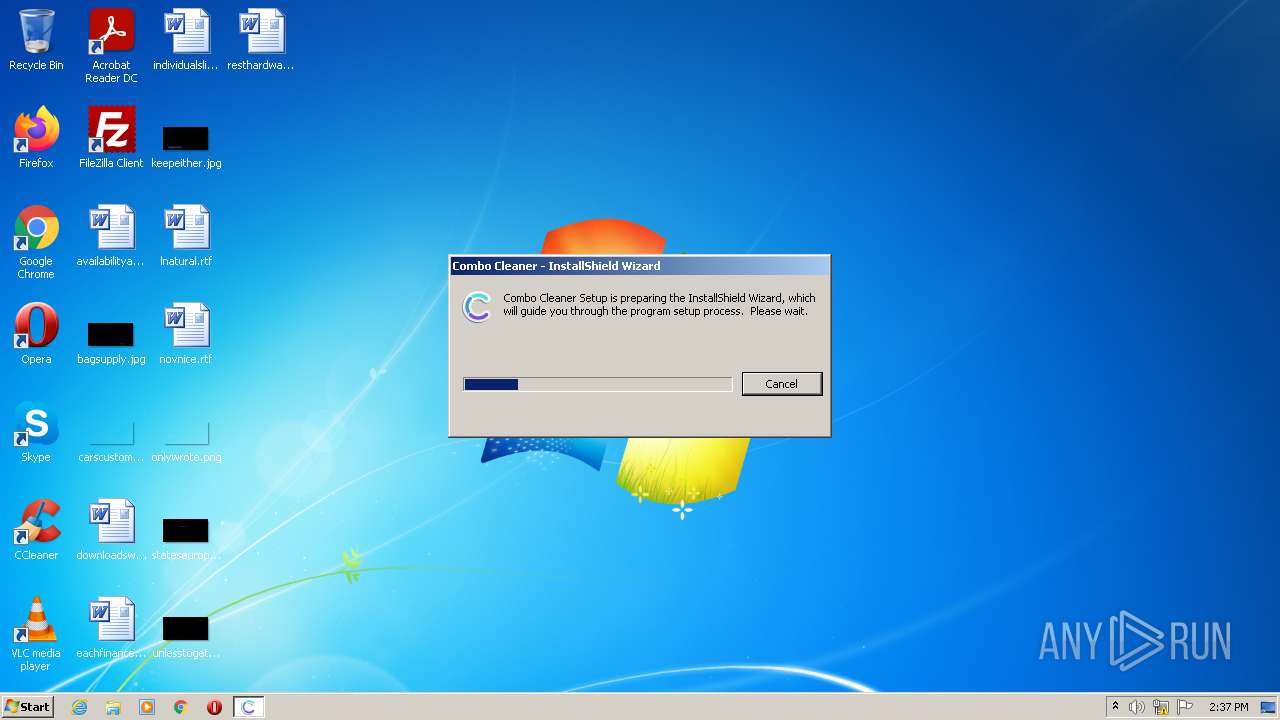
| FileDescription: | Combo Cleaner |
| FileVersion: | 1.0.54.0 |
| InternalName: | Setup |
| LegalCopyright: | Copyright (c) 2021 RCS LT, UAB. All Rights Reserved. |
| OriginalFileName: | CCSetup.exe |
| ProductName: | Combo Cleaner |
| ProductVersion: | 1.0.54.0 |
| InternalBuildNumber: | 200860 |
| ISInternalVersion: | 26.0.717 |
| ISInternalDescription: | Setup Launcher Unicode |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Nov-2020 00:55:36 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | RCS LT |
| FileDescription: | Combo Cleaner |
| FileVersion: | 1.0.54.0 |
| InternalName: | Setup |
| LegalCopyright: | Copyright (c) 2021 RCS LT, UAB. All Rights Reserved. |
| OriginalFilename: | CCSetup.exe |
| ProductName: | Combo Cleaner |
| ProductVersion: | 1.0.54.0 |
| Internal Build Number: | 200860 |
| ISInternalVersion: | 26.0.717 |
| ISInternalDescription: | Setup Launcher Unicode |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 23-Nov-2020 00:55:36 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00095F97 | 0x00096000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.53511 |
.rdata | 0x00097000 | 0x0002EB0E | 0x0002EC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.58108 |
.data | 0x000C6000 | 0x0000AF50 | 0x00002800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.3773 |
.rsrc | 0x000D1000 | 0x00064354 | 0x00064400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.35604 |
.reloc | 0x00136000 | 0x00028126 | 0x00028200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 2.482 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07176 | 640 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.89113 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 4.17876 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 4.39118 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 4.66602 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 5.26754 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
69 | 3.10251 | 352 | Latin 1 / Western European | English - United States | RT_STRING |
70 | 3.14661 | 574 | Latin 1 / Western European | English - United States | RT_STRING |
71 | 3.25053 | 888 | Latin 1 / Western European | English - United States | RT_STRING |
72 | 3.13124 | 594 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
VERSION.dll (delay-loaded) |
Total processes
39
Monitored processes
3
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 776 | C:\Users\admin\AppData\Local\Temp\{85680B07-A4A4-4F28-9C8F-37298B63748B}\CCSetup.exe /q"C:\Users\admin\AppData\Local\Temp\CCSetup.exe" /tempdisk1folder"C:\Users\admin\AppData\Local\Temp\{85680B07-A4A4-4F28-9C8F-37298B63748B}" /IS_temp | C:\Users\admin\AppData\Local\Temp\{85680B07-A4A4-4F28-9C8F-37298B63748B}\CCSetup.exe | CCSetup.exe | ||||||||||||
User: admin Company: RCS LT Integrity Level: HIGH Description: Combo Cleaner Exit code: 0 Version: 1.0.54.0 Modules
| |||||||||||||||
| 3872 | "C:\Users\admin\AppData\Local\Temp\CCSetup.exe" | C:\Users\admin\AppData\Local\Temp\CCSetup.exe | Explorer.EXE | ||||||||||||
User: admin Company: RCS LT Integrity Level: HIGH Description: Combo Cleaner Exit code: 0 Version: 1.0.54.0 Modules
| |||||||||||||||
| 4084 | "C:\Users\admin\AppData\Local\Temp\CCSetup.exe" | C:\Users\admin\AppData\Local\Temp\CCSetup.exe | — | Explorer.EXE | |||||||||||
User: admin Company: RCS LT Integrity Level: MEDIUM Description: Combo Cleaner Exit code: 3221226540 Version: 1.0.54.0 Modules
| |||||||||||||||
Total events
4 516
Read events
4 480
Write events
34
Delete events
2
Modification events
| (PID) Process: | (776) CCSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion |
| Operation: | write | Name: | %IS_PREREQ%-Combo Cleaner |
Value: 0 | |||
| (PID) Process: | (776) CCSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | ISSetupPrerequisistes |
Value: "C:\Users\admin\AppData\Local\Temp\CCSetup.exe" | |||
| (PID) Process: | (776) CCSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (776) CCSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000043010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (776) CCSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (776) CCSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (776) CCSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (776) CCSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (776) CCSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (776) CCSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
1
Suspicious files
4
Text files
13
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3872 | CCSetup.exe | C:\Users\admin\AppData\Local\Temp\{85680B07-A4A4-4F28-9C8F-37298B63748B}\CCSetup.exe | executable | |
MD5:— | SHA256:— | |||
| 3872 | CCSetup.exe | C:\Users\admin\AppData\Local\Temp\~B37B.tmp | text | |
MD5:— | SHA256:— | |||
| 3872 | CCSetup.exe | C:\Users\admin\AppData\Local\Temp\{85680B07-A4A4-4F28-9C8F-37298B63748B}\_ISMSIDEL.INI | text | |
MD5:— | SHA256:— | |||
| 3872 | CCSetup.exe | C:\Users\admin\AppData\Local\Temp\~B379.tmp | text | |
MD5:— | SHA256:— | |||
| 3872 | CCSetup.exe | C:\Users\admin\AppData\Local\Temp\~B38C.tmp | text | |
MD5:— | SHA256:— | |||
| 3872 | CCSetup.exe | C:\Users\admin\AppData\Local\Temp\~B37A.tmp | text | |
MD5:— | SHA256:— | |||
| 776 | CCSetup.exe | C:\Users\admin\AppData\Local\Temp\{85680B07-A4A4-4F28-9C8F-37298B63748B}\Setup.INI | text | |
MD5:— | SHA256:— | |||
| 776 | CCSetup.exe | C:\Users\admin\AppData\Local\Temp\~B3D8.tmp | text | |
MD5:— | SHA256:— | |||
| 776 | CCSetup.exe | C:\Users\admin\AppData\Local\Temp\~B3D7.tmp | text | |
MD5:— | SHA256:— | |||
| 776 | CCSetup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
12
DNS requests
4
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
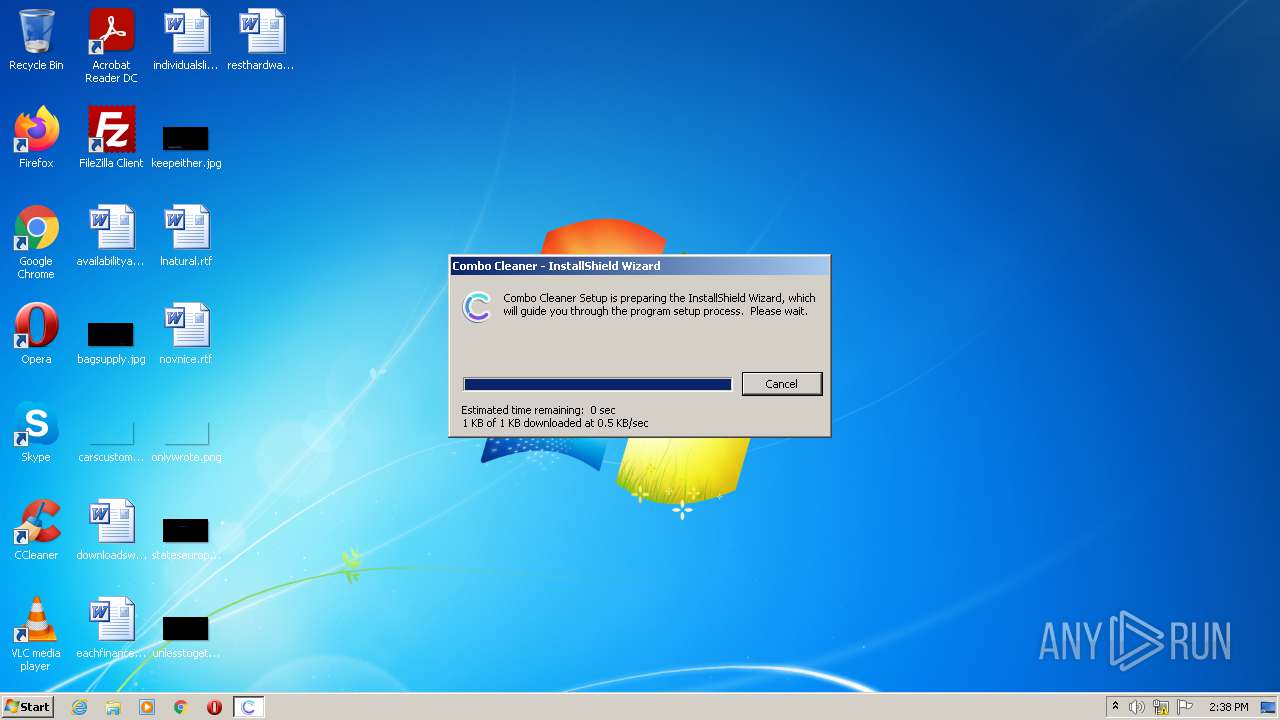
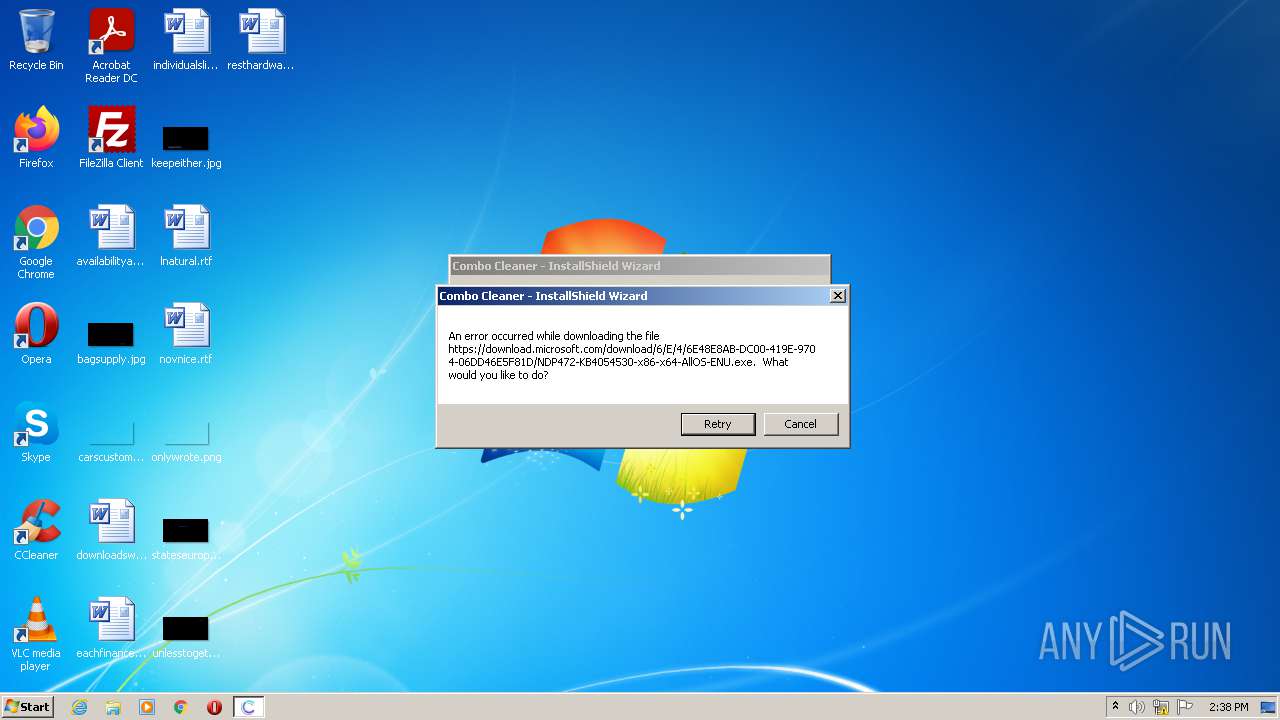
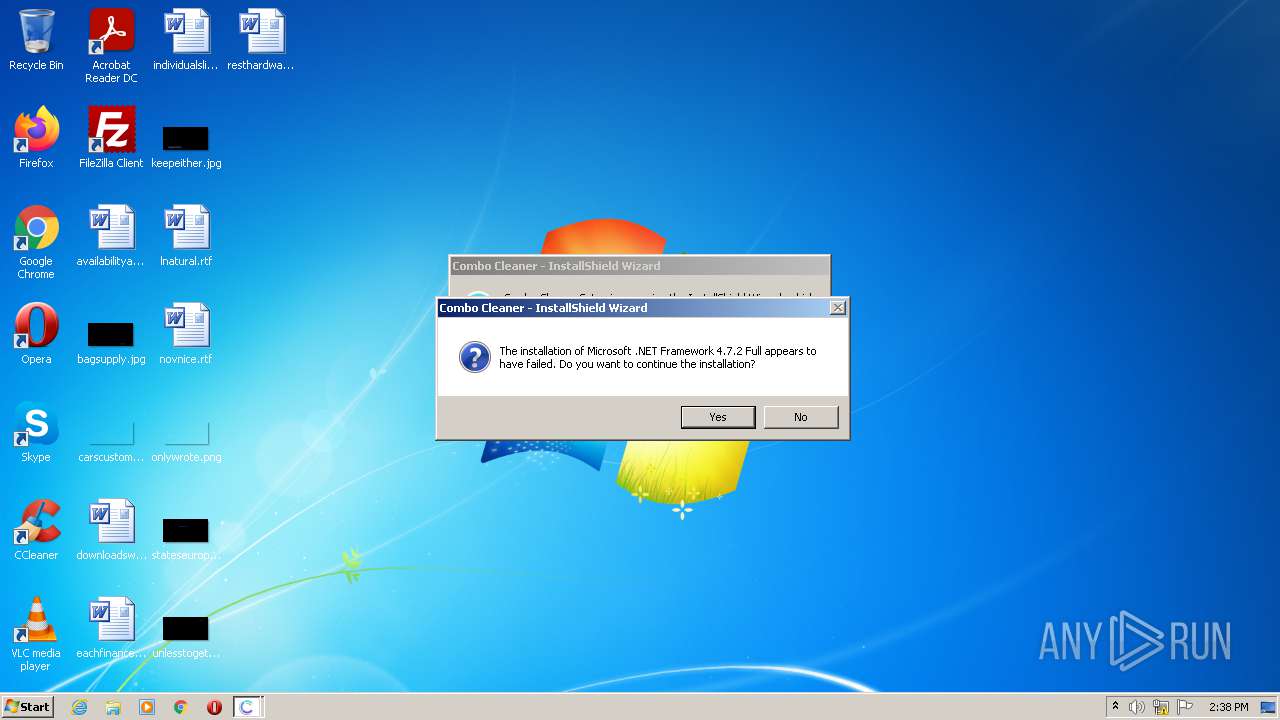
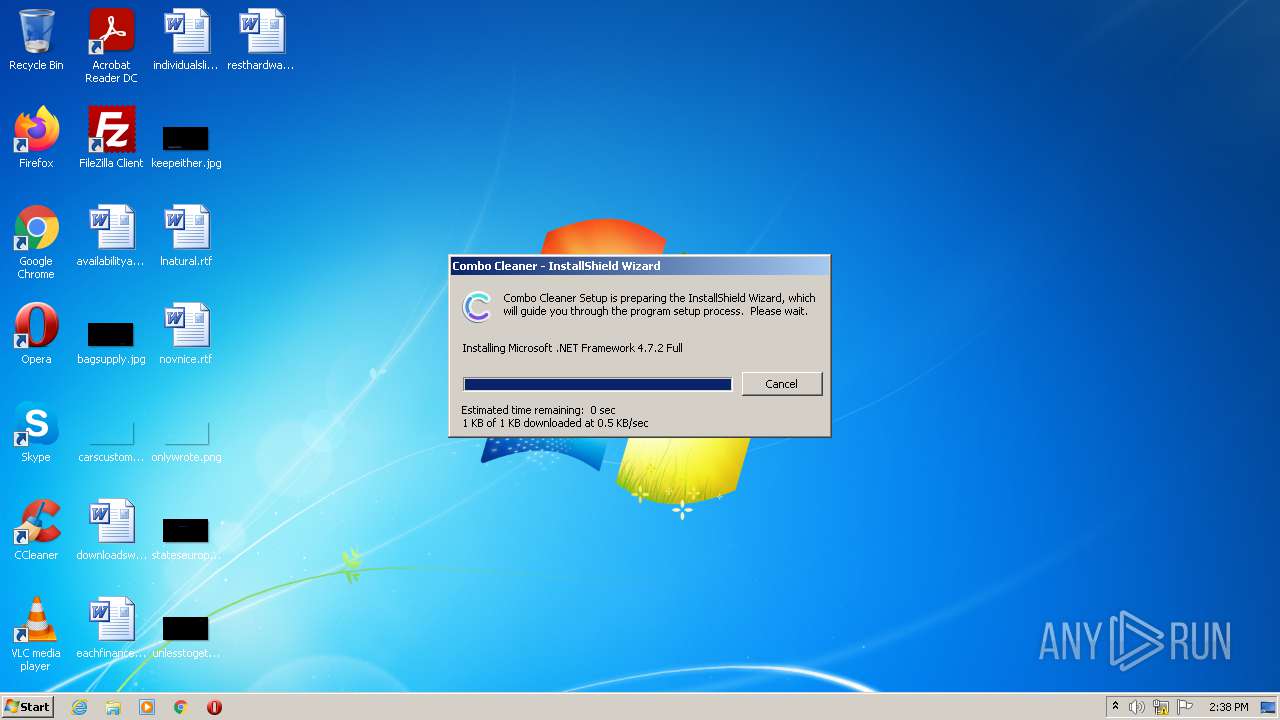
776 | CCSetup.exe | GET | 200 | 64.14.29.56:80 | http://saturn.installshield.com/is/prerequisites/Microsoft%20.NET%20Framework%204.7.2%20Full.prq | US | xml | 1.55 Kb | suspicious |
776 | CCSetup.exe | GET | 200 | 64.14.29.56:80 | http://saturn.installshield.com/is/prerequisites/Microsoft%20.NET%20Framework%204.7.2%20Full.prq | US | xml | 1.55 Kb | suspicious |
776 | CCSetup.exe | GET | 200 | 2.16.186.81:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?ec842625eacb8d15 | unknown | compressed | 4.70 Kb | whitelisted |
776 | CCSetup.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
776 | CCSetup.exe | 64.14.29.56:80 | saturn.installshield.com | Flexera Software Limited | US | suspicious |
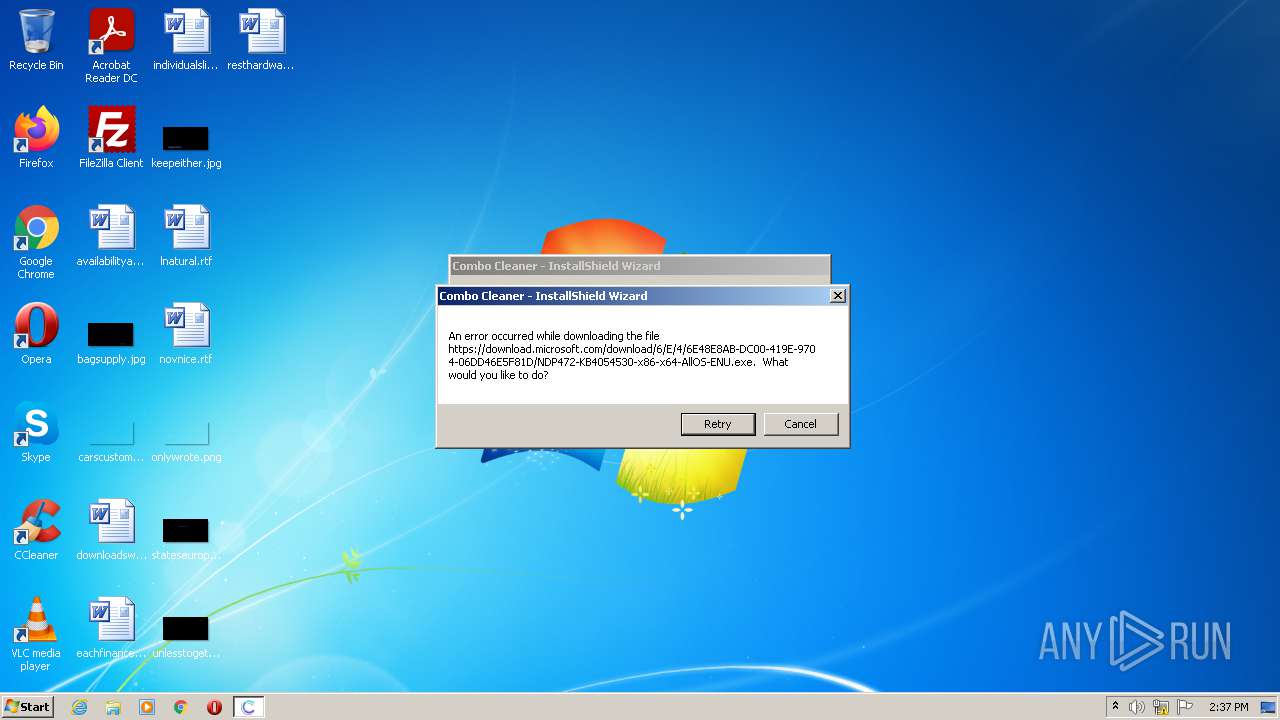
776 | CCSetup.exe | 104.90.185.48:443 | download.microsoft.com | Akamai Technologies, Inc. | NL | unknown |
776 | CCSetup.exe | 2.16.186.81:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
776 | CCSetup.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
saturn.installshield.com |
| suspicious |
download.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
776 | CCSetup.exe | A Network Trojan was detected | ET POLICY Installshield One Click Install User-Agent Toys File |
776 | CCSetup.exe | A Network Trojan was detected | ET POLICY Installshield One Click Install User-Agent Toys File |