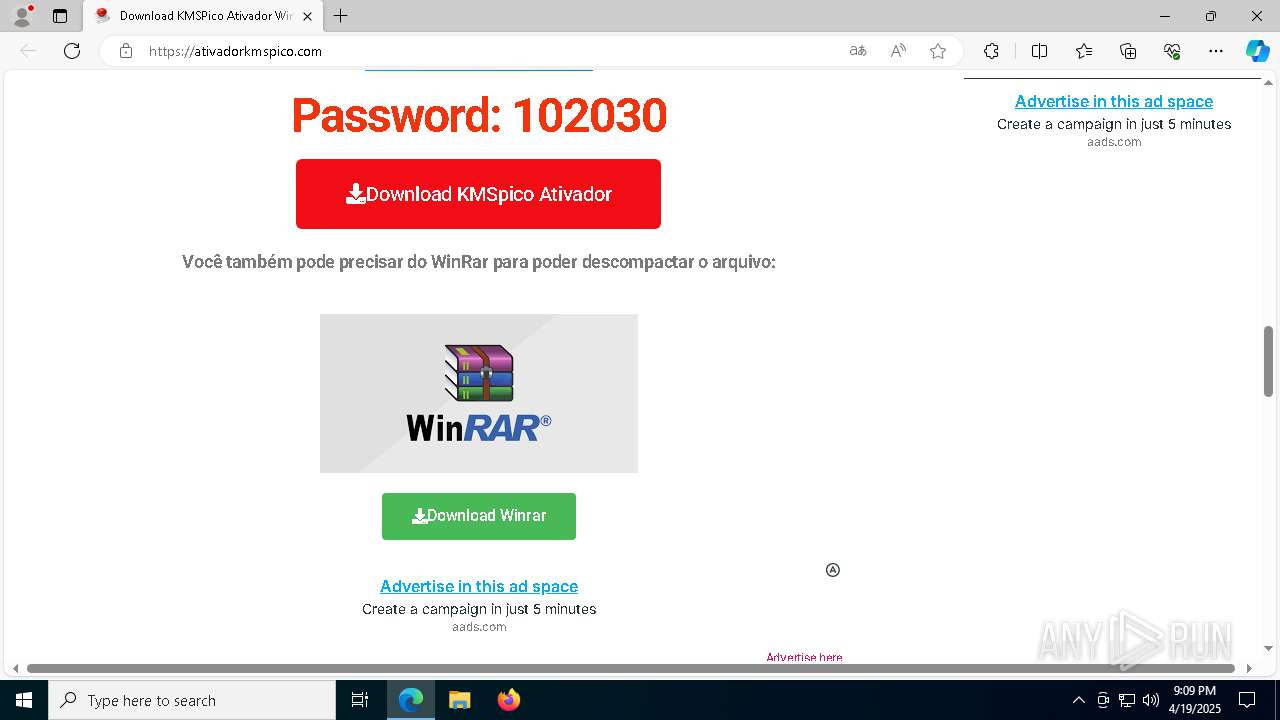
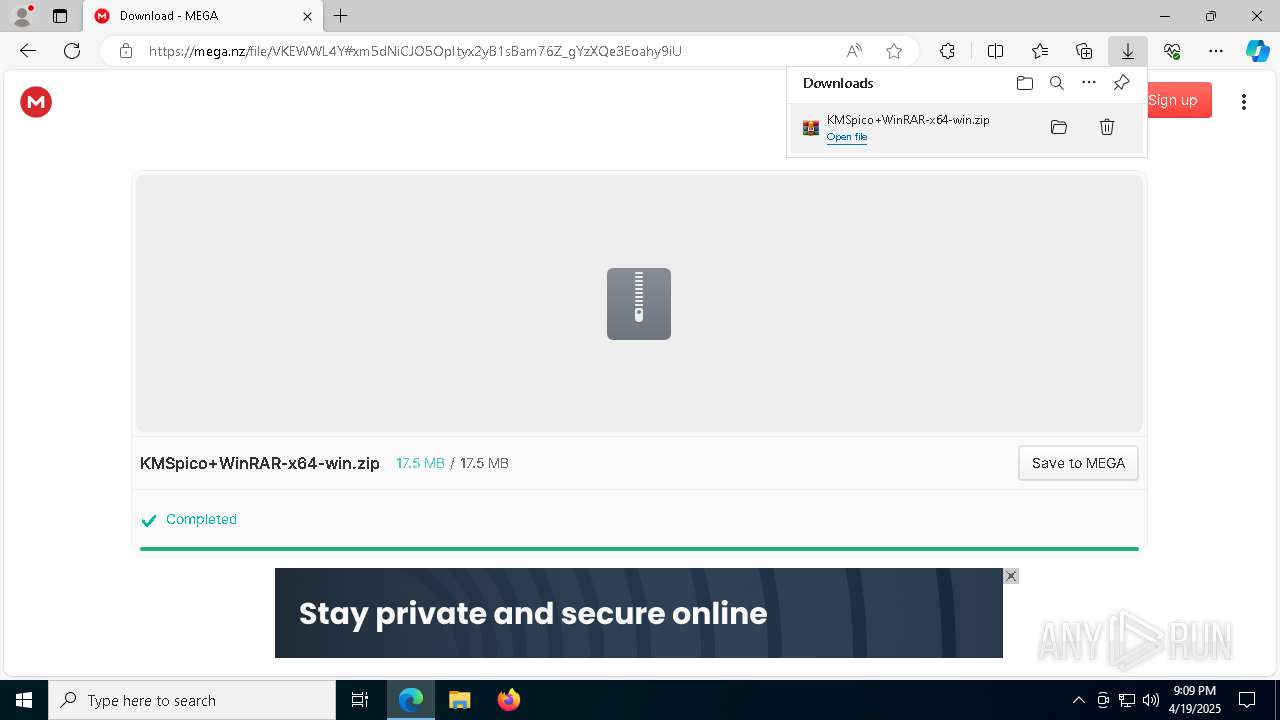
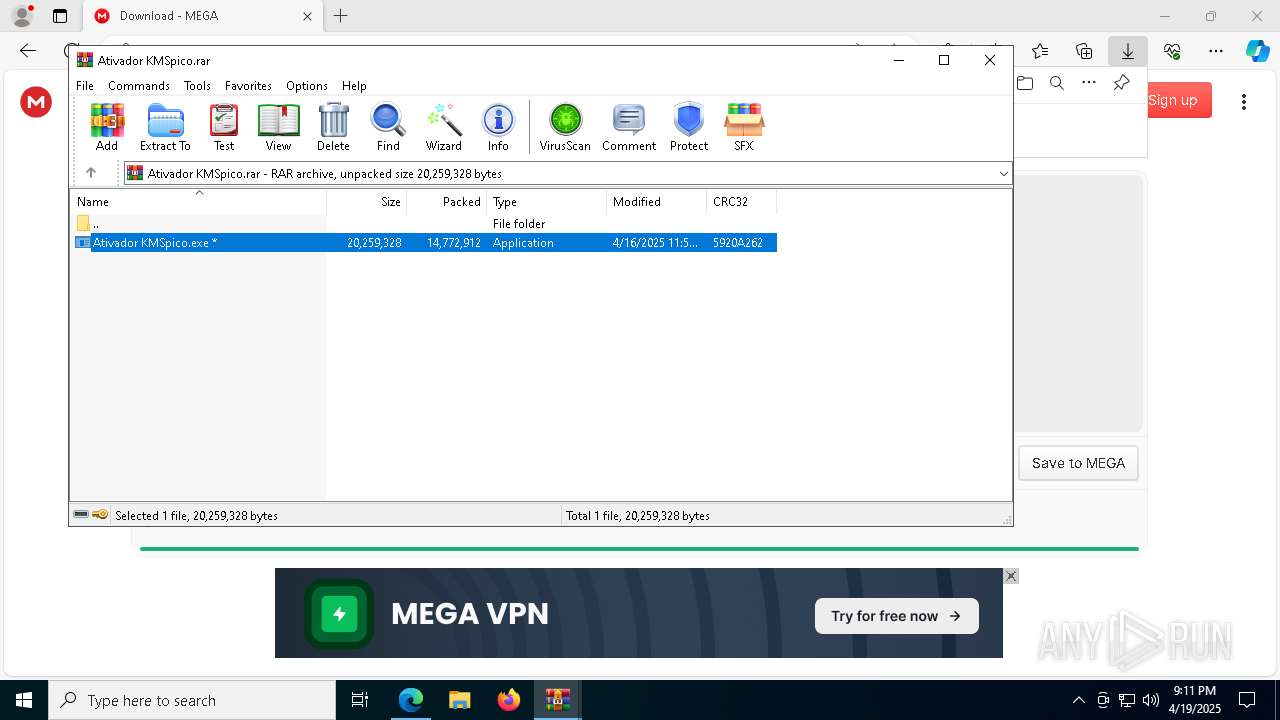
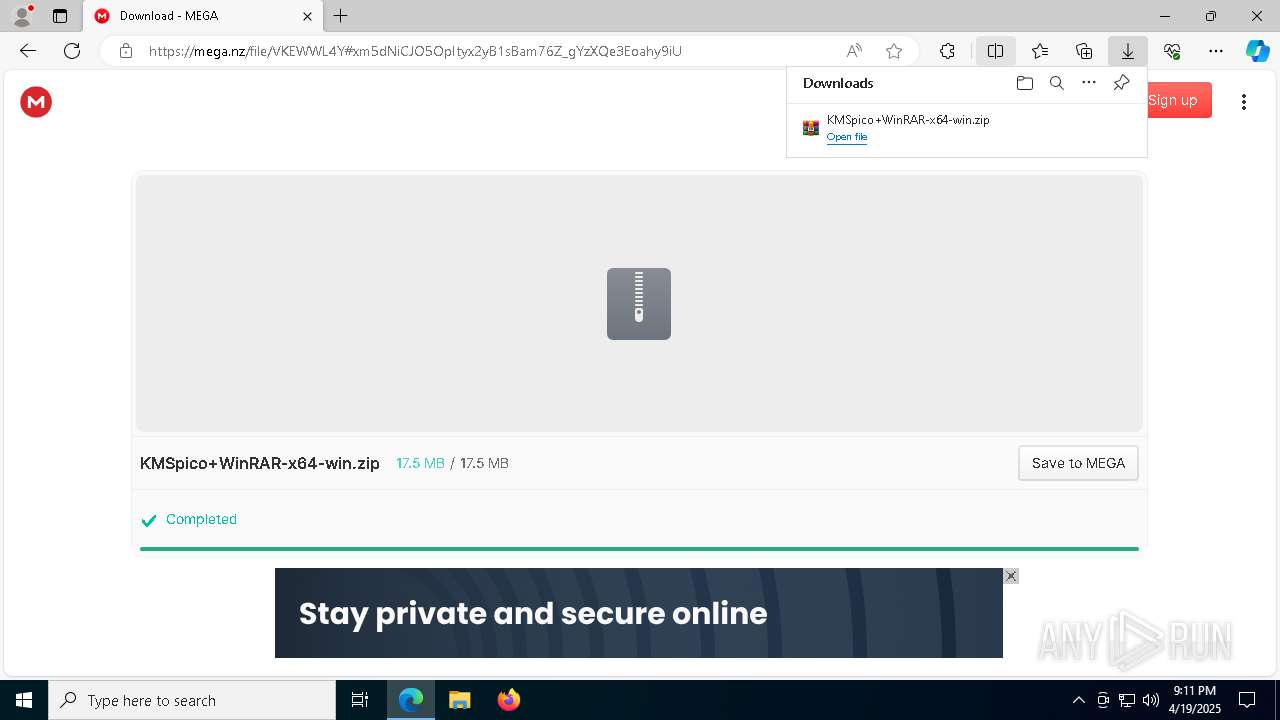
| URL: | https://ativadorkmspico.com/ |
| Full analysis: | https://app.any.run/tasks/5e05334b-28d7-472f-94f2-f57803016a03 |
| Verdict: | Malicious activity |
| Analysis date: | April 19, 2025, 21:08:48 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 579402ABA45FB35B536FBCEF691FBAE5 |
| SHA1: | A31E1826F8C8F05AF01BF4D4D019D7B1BDFBA12B |
| SHA256: | 69479714EBFC7B9822B547A2AF55600AB2702E275C5180E86BEF41D318951A3A |
| SSDEEP: | 3:N83znWV/Kn:2jS/K |
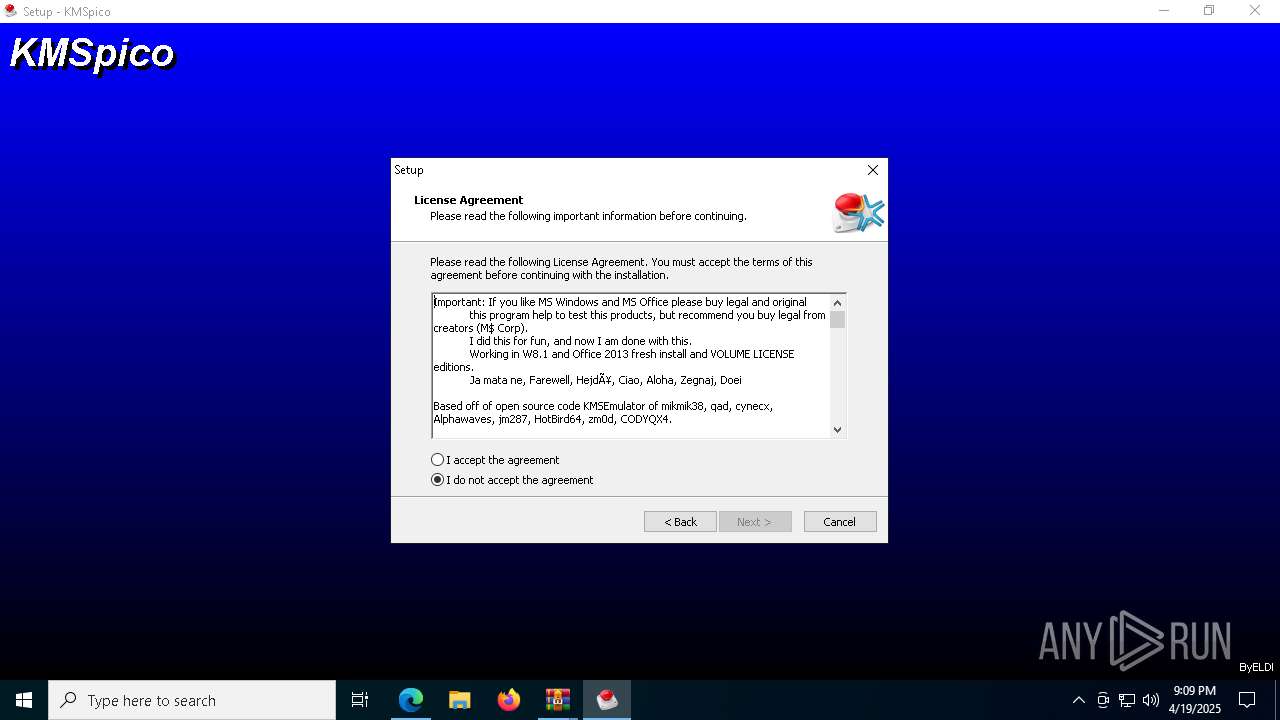
MALICIOUS
Disables Windows Defender
- RegAsm.exe (PID: 7196)
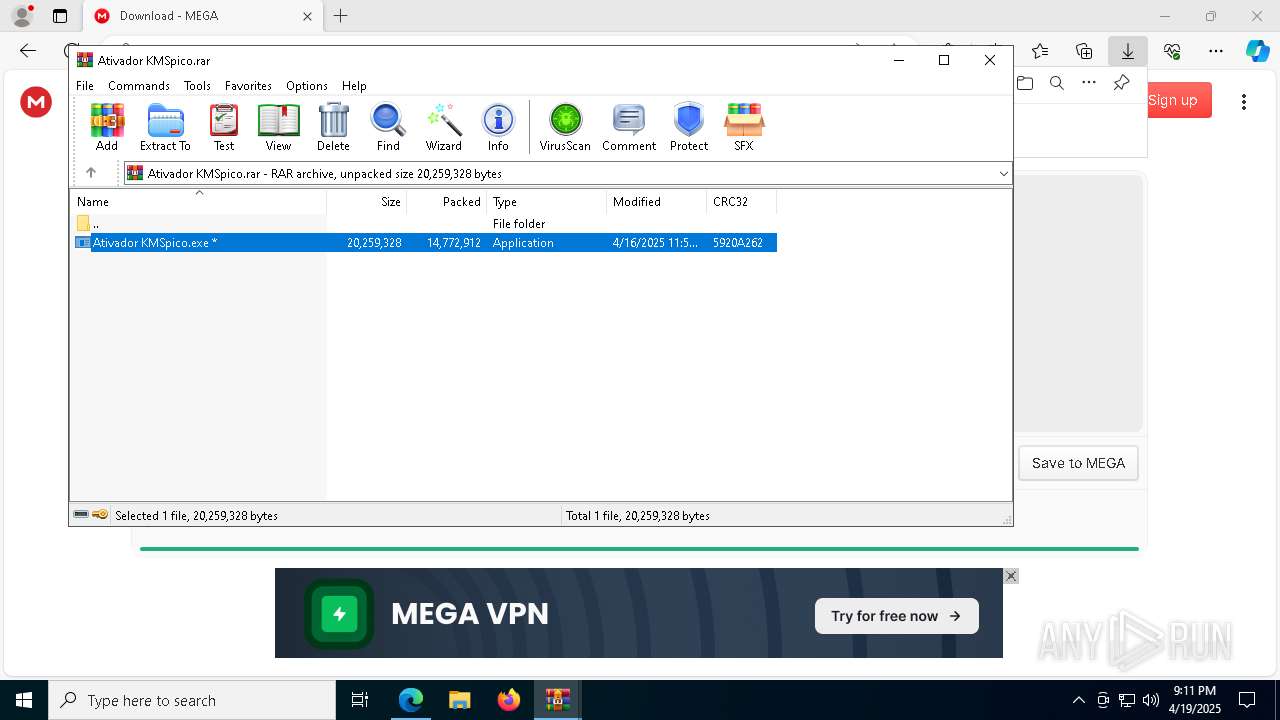
GENERIC has been found (auto)
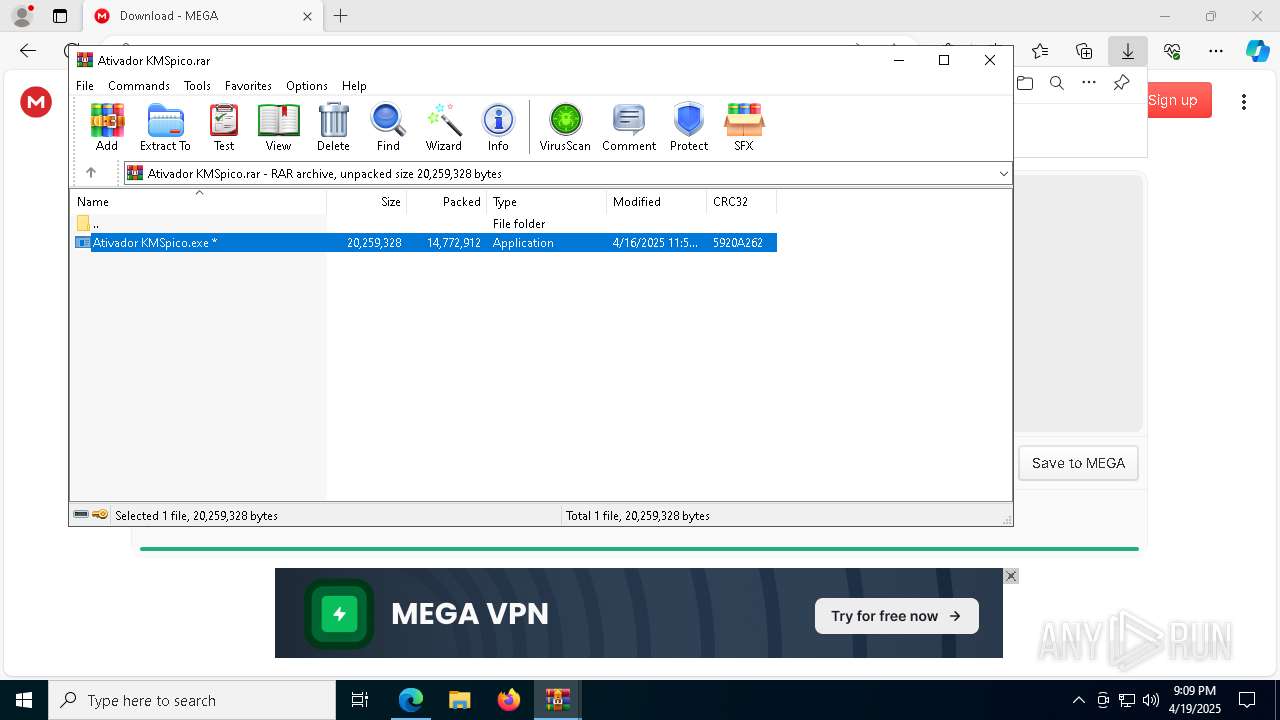
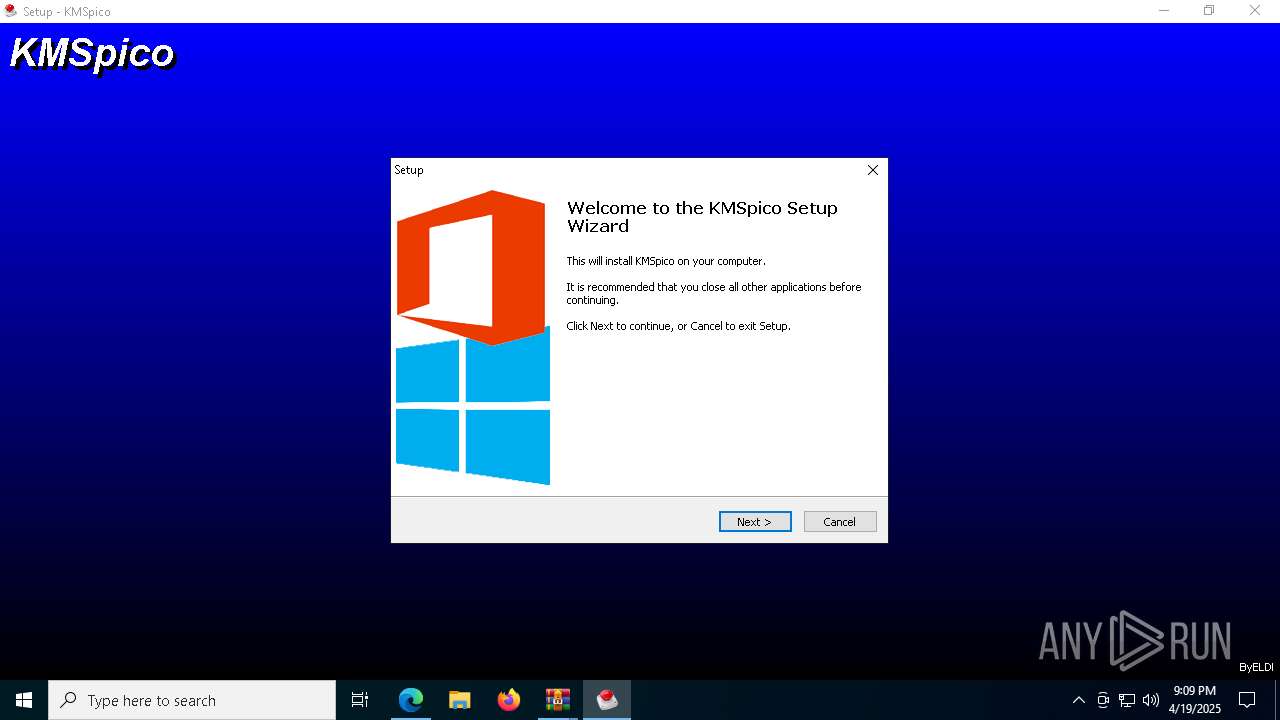
- Ativador KMSpico.exe (PID: 2344)
Executing a file with an untrusted certificate
- 41f0f2e8-9d55-f6d4-4191-0ade0b851e900.exe (PID: 8604)
- KMSELDI.exe (PID: 9532)
- AutoPico.exe (PID: 9408)
Changes Windows Defender settings
- RegAsm.exe (PID: 7196)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 9068)
- powershell.exe (PID: 10160)
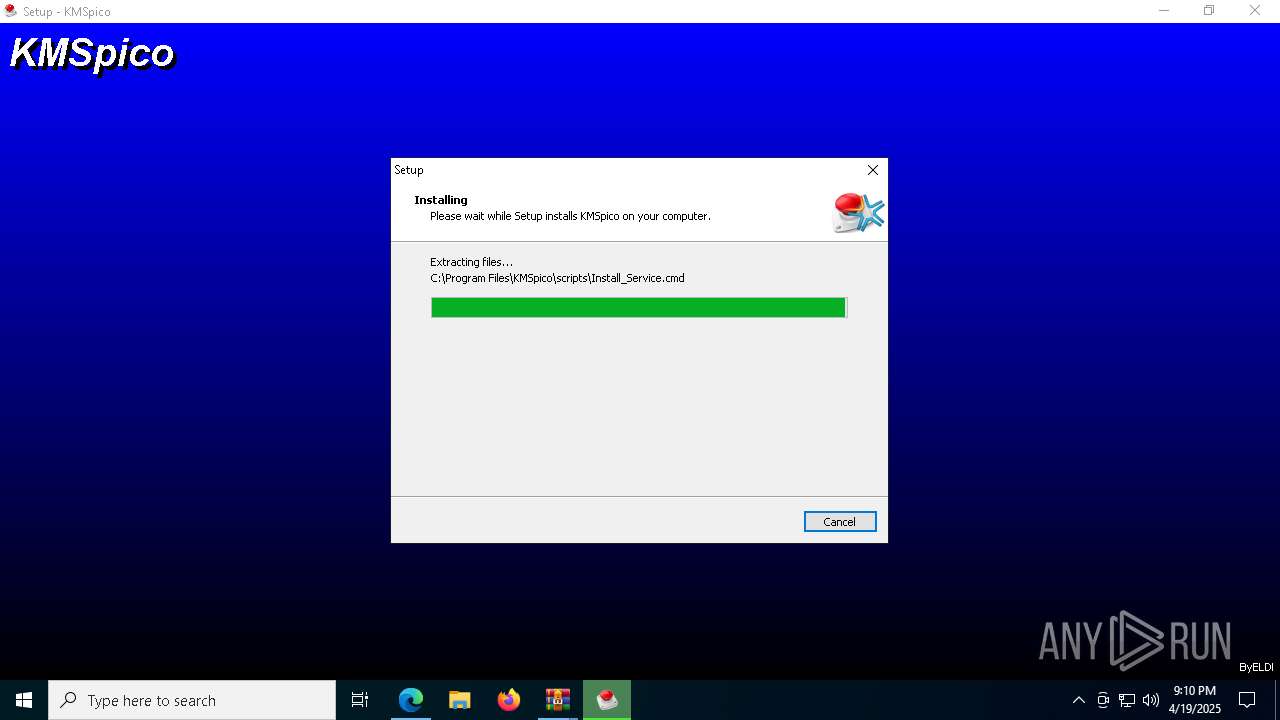
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 8944)
- cmd.exe (PID: 8880)
Starts NET.EXE for service management
- net.exe (PID: 9988)
- powershell.exe (PID: 8132)
- powershell.exe (PID: 6112)
- net.exe (PID: 456)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 2656)
- cmd.exe (PID: 8860)
- cmd.exe (PID: 9092)
- cmd.exe (PID: 10036)
- cmd.exe (PID: 8340)
Changes image file execution options
- KMSELDI.exe (PID: 9532)
- AutoPico.exe (PID: 9408)
Changes the autorun value in the registry
- RegAsm.exe (PID: 5200)
Create files in the Startup directory
- RegAsm.exe (PID: 5200)
SUSPICIOUS
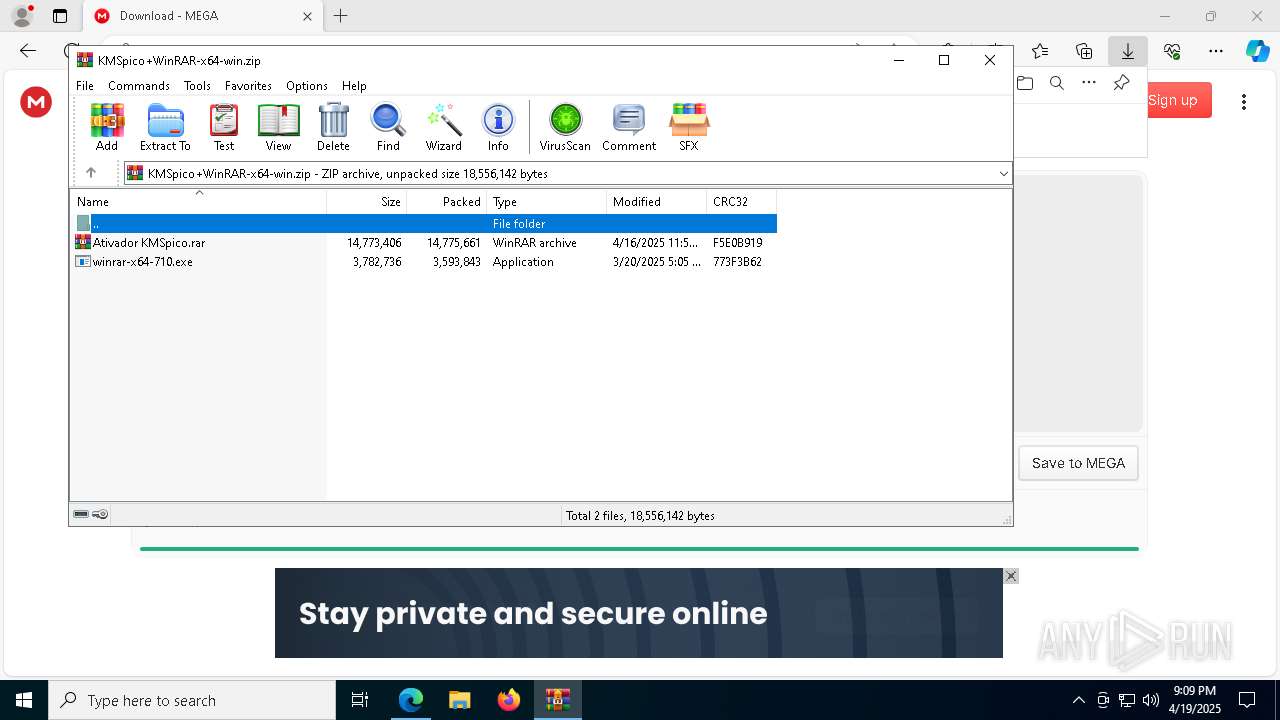
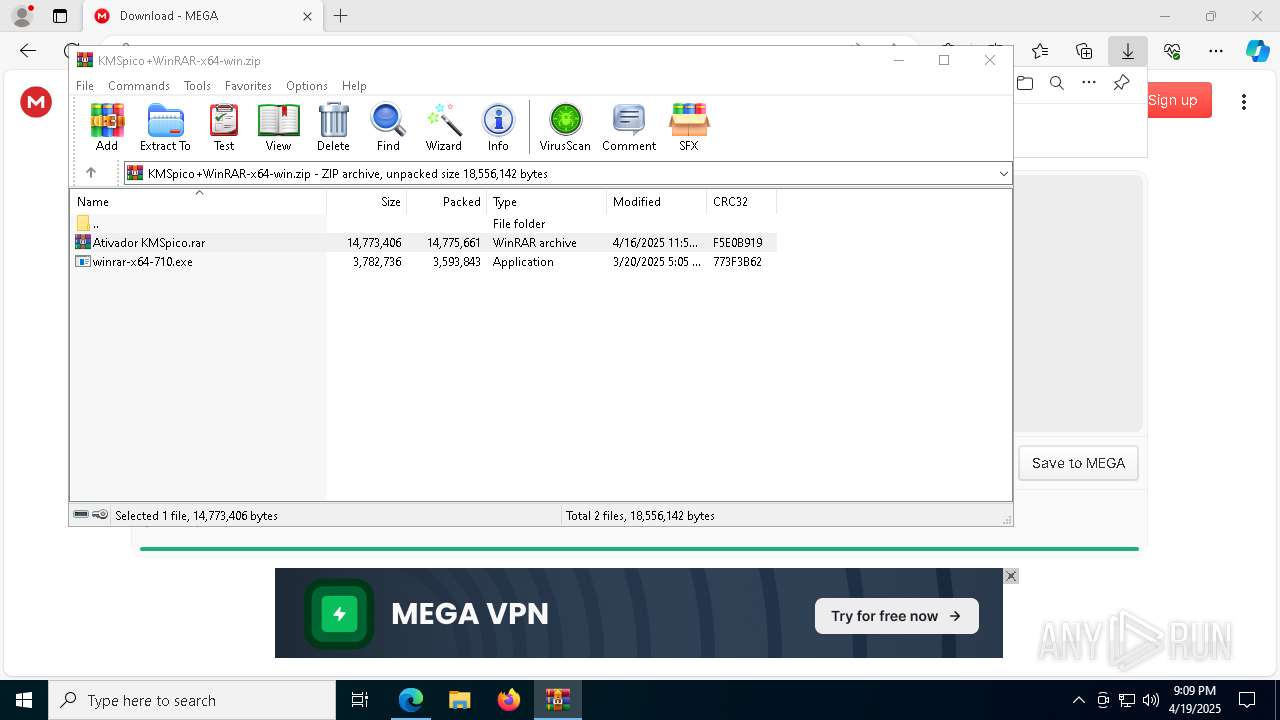
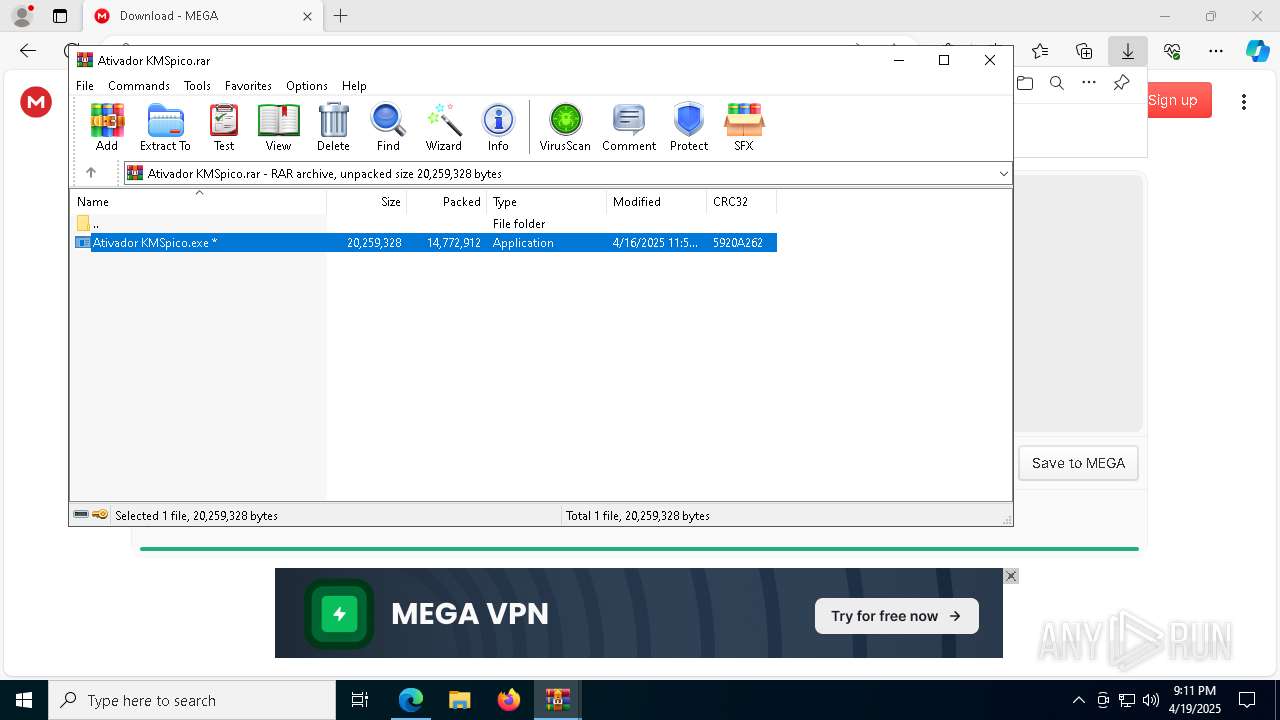
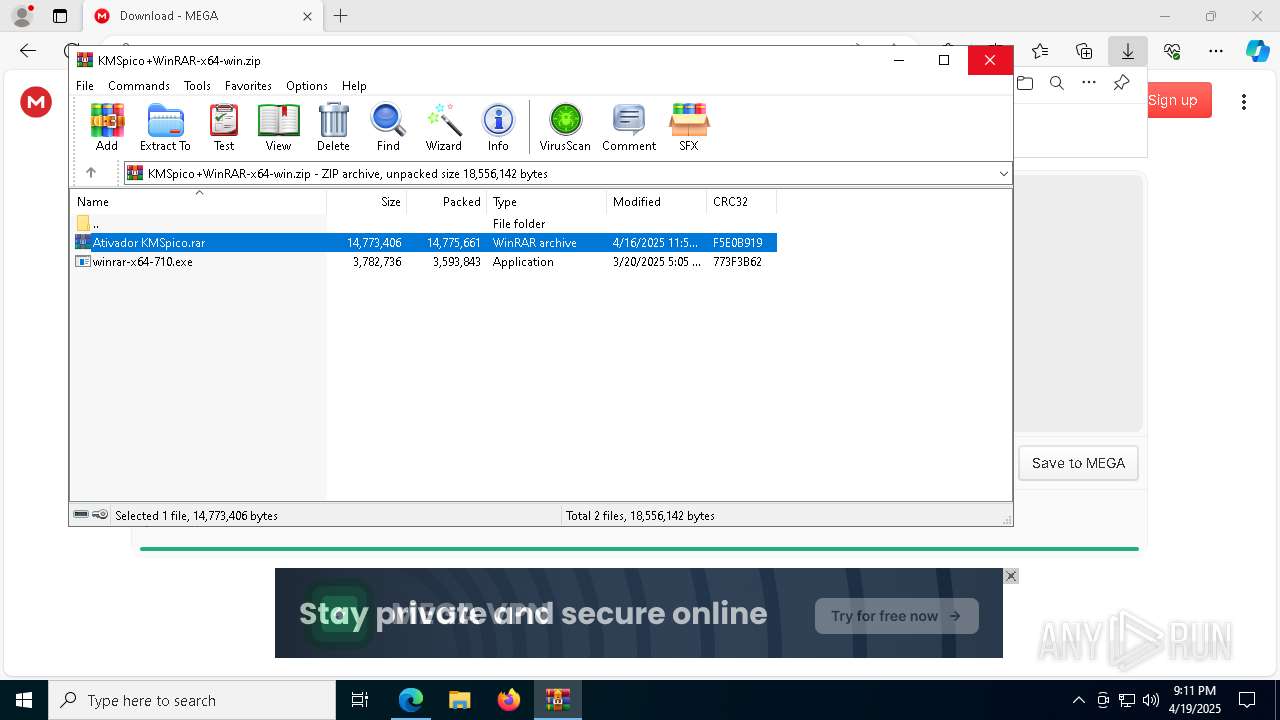
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 644)
- WinRAR.exe (PID: 3300)
- Ativador KMSpico.exe (PID: 2344)
Application launched itself
- WinRAR.exe (PID: 644)
Starts POWERSHELL.EXE for commands execution
- RegAsm.exe (PID: 7196)
- RegAsm.exe (PID: 5200)
Starts CMD.EXE for commands execution
- RegAsm.exe (PID: 7196)
- RegAsm.exe (PID: 5200)
- 41f0f2e8-9d55-f6d4-4191-0ade0b851e900.tmp (PID: 8628)
Modifies existing scheduled task
- schtasks.exe (PID: 8344)
- schtasks.exe (PID: 8352)
- schtasks.exe (PID: 8368)
- schtasks.exe (PID: 8360)
- schtasks.exe (PID: 8392)
- schtasks.exe (PID: 9512)
- schtasks.exe (PID: 9504)
- schtasks.exe (PID: 9476)
- schtasks.exe (PID: 9488)
- schtasks.exe (PID: 9496)
Found strings related to reading or modifying Windows Defender settings
- RegAsm.exe (PID: 7196)
Query Microsoft Defender preferences
- RegAsm.exe (PID: 7196)
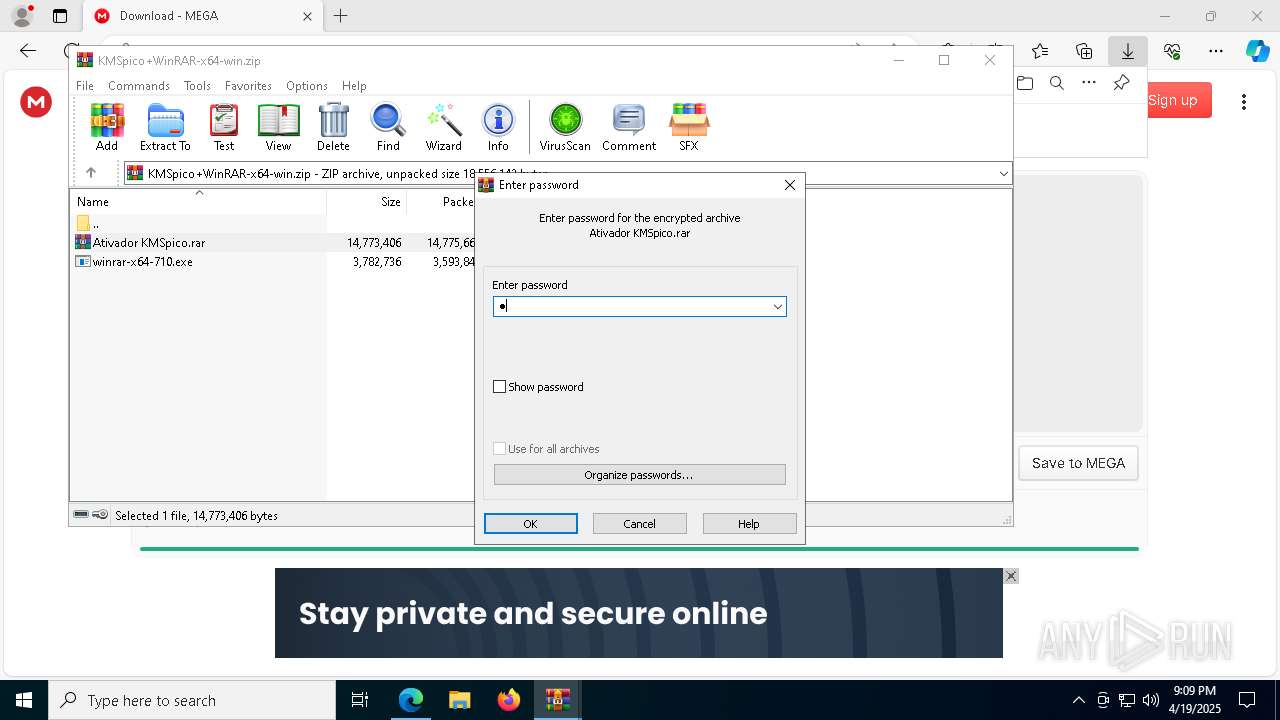
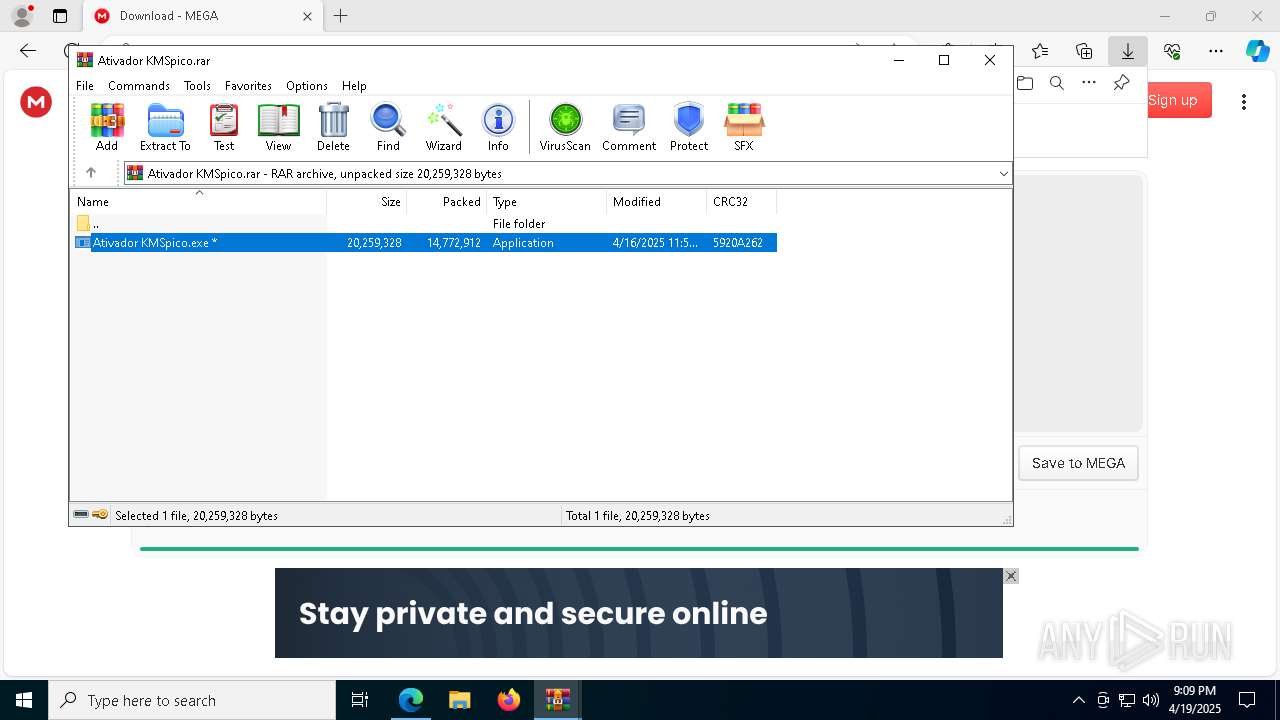
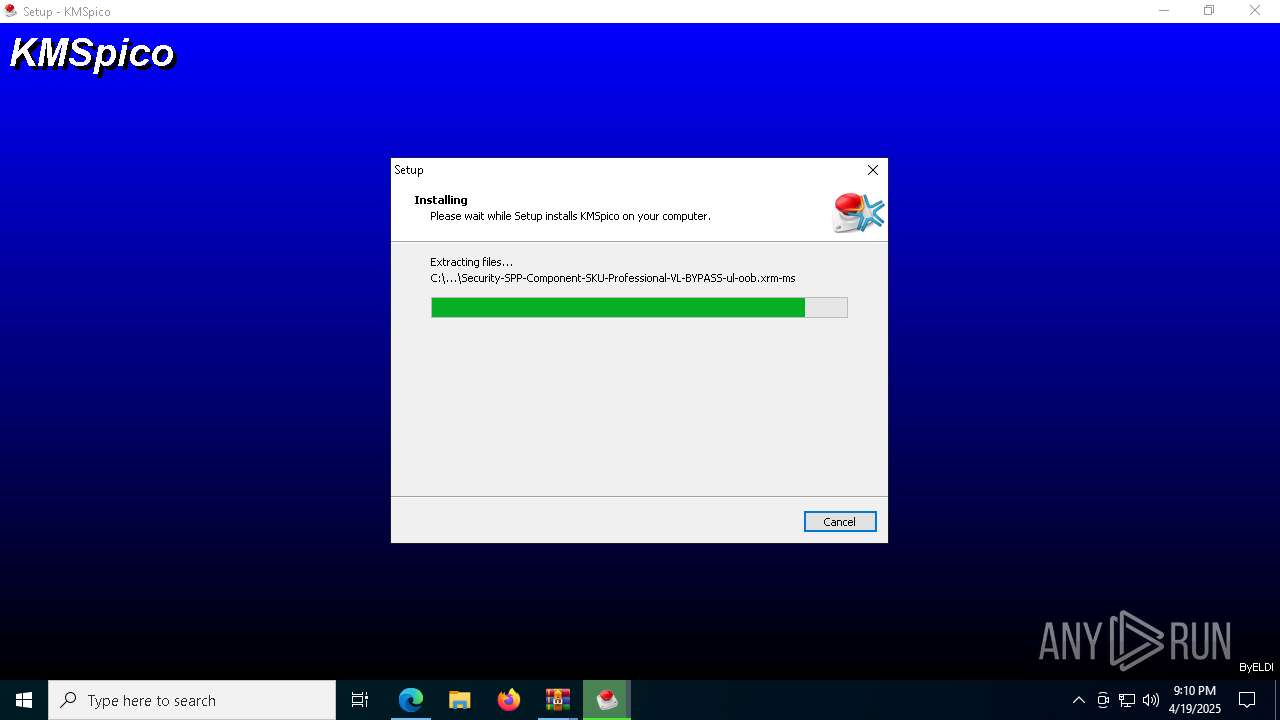
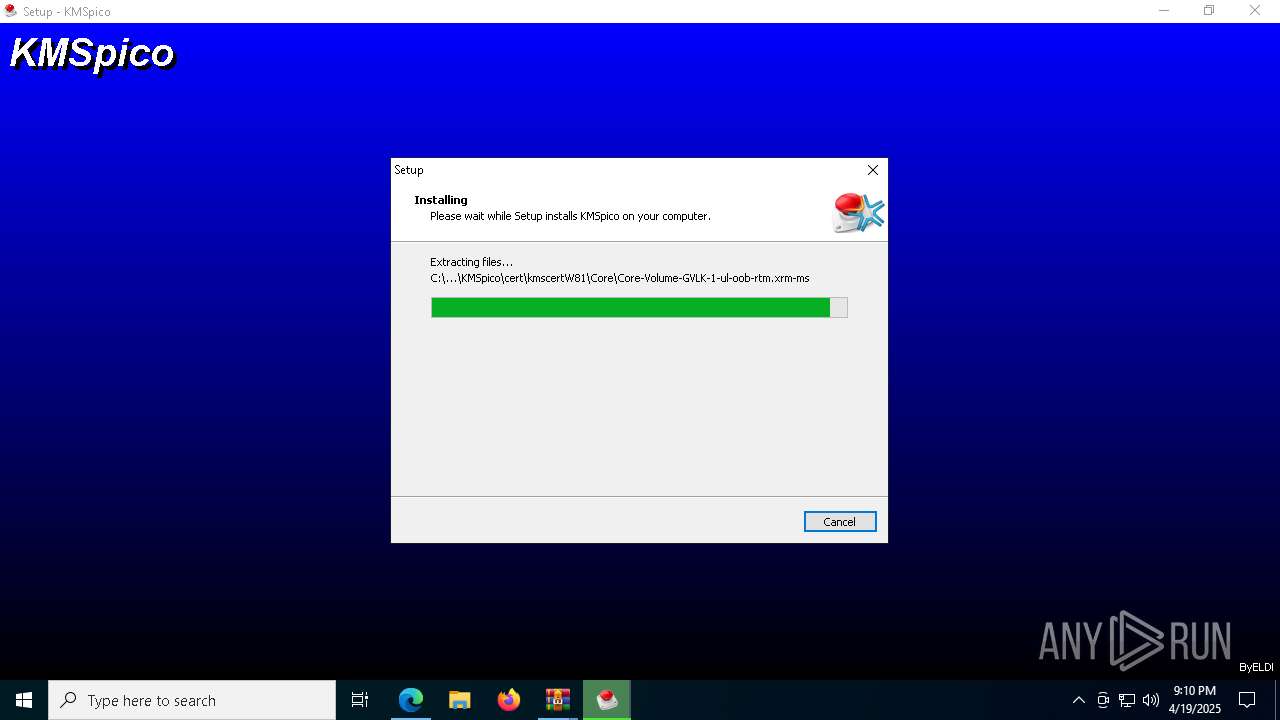
Executable content was dropped or overwritten
- Ativador KMSpico.exe (PID: 2344)
- 41f0f2e8-9d55-f6d4-4191-0ade0b851e900.exe (PID: 8604)
- 41f0f2e8-9d55-f6d4-4191-0ade0b851e900.tmp (PID: 8628)
- KMSELDI.exe (PID: 9532)
- csc.exe (PID: 9564)
Reads the date of Windows installation
- Ativador KMSpico.exe (PID: 2344)
Reads the Windows owner or organization settings
- 41f0f2e8-9d55-f6d4-4191-0ade0b851e900.tmp (PID: 8628)
Process drops legitimate windows executable
- 41f0f2e8-9d55-f6d4-4191-0ade0b851e900.tmp (PID: 8628)
Uses powercfg.exe to modify the power settings
- powershell.exe (PID: 5600)
- powershell.exe (PID: 8972)
- powershell.exe (PID: 8444)
Uses NETSH.EXE to change the status of the firewall
- powershell.exe (PID: 5600)
- powershell.exe (PID: 8972)
- powershell.exe (PID: 8444)
Found regular expressions for crypto-addresses (YARA)
- RegAsm.exe (PID: 5200)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 8924)
- cmd.exe (PID: 8896)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 6248)
- schtasks.exe (PID: 5344)
Modifies the phishing filter of IE
- 41f0f2e8-9d55-f6d4-4191-0ade0b851e900.tmp (PID: 8628)
Starts SC.EXE for service management
- cmd.exe (PID: 7240)
Creates a new Windows service
- sc.exe (PID: 9292)
Executing commands from ".cmd" file
- 41f0f2e8-9d55-f6d4-4191-0ade0b851e900.tmp (PID: 8628)
Connects to unusual port
- KMSELDI.exe (PID: 9532)
INFO
Application launched itself
- msedge.exe (PID: 7312)
- msedge.exe (PID: 8660)
Checks supported languages
- identity_helper.exe (PID: 6048)
- Ativador KMSpico.exe (PID: 2344)
- RegAsm.exe (PID: 5200)
- RegAsm.exe (PID: 7196)
- 41f0f2e8-9d55-f6d4-4191-0ade0b851e900.exe (PID: 8604)
- 41f0f2e8-9d55-f6d4-4191-0ade0b851e900.tmp (PID: 8628)
- csc.exe (PID: 8892)
- csc.exe (PID: 4868)
- KMSELDI.exe (PID: 9532)
- UninsHs.exe (PID: 4488)
- vbc.exe (PID: 9528)
- SECOH-QAD.exe (PID: 8772)
- cvtres.exe (PID: 9324)
- csc.exe (PID: 9564)
- vbc.exe (PID: 7144)
- cvtres.exe (PID: 8740)
- AutoPico.exe (PID: 9408)
- vbc.exe (PID: 9652)
- identity_helper.exe (PID: 8236)
The sample compiled with english language support
- msedge.exe (PID: 7312)
- 41f0f2e8-9d55-f6d4-4191-0ade0b851e900.tmp (PID: 8628)
- msedge.exe (PID: 7956)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3300)
- msedge.exe (PID: 7956)
Reads Environment values
- identity_helper.exe (PID: 6048)
- KMSELDI.exe (PID: 9532)
- AutoPico.exe (PID: 9408)
- identity_helper.exe (PID: 8236)
Reads the machine GUID from the registry
- Ativador KMSpico.exe (PID: 2344)
- RegAsm.exe (PID: 5200)
- csc.exe (PID: 8892)
- csc.exe (PID: 4868)
- KMSELDI.exe (PID: 9532)
- vbc.exe (PID: 9528)
- csc.exe (PID: 9564)
- vbc.exe (PID: 7144)
- AutoPico.exe (PID: 9408)
- vbc.exe (PID: 9652)
Reads the computer name
- RegAsm.exe (PID: 5200)
- Ativador KMSpico.exe (PID: 2344)
- RegAsm.exe (PID: 7196)
- identity_helper.exe (PID: 6048)
- 41f0f2e8-9d55-f6d4-4191-0ade0b851e900.tmp (PID: 8628)
- KMSELDI.exe (PID: 9532)
- AutoPico.exe (PID: 9408)
- identity_helper.exe (PID: 8236)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7312)
- KMSELDI.exe (PID: 9532)
- AutoPico.exe (PID: 9408)
Creates files or folders in the user directory
- Ativador KMSpico.exe (PID: 2344)
- RegAsm.exe (PID: 5200)
- vbc.exe (PID: 9528)
- vbc.exe (PID: 7144)
- vbc.exe (PID: 9652)
Create files in a temporary directory
- 41f0f2e8-9d55-f6d4-4191-0ade0b851e900.exe (PID: 8604)
- 41f0f2e8-9d55-f6d4-4191-0ade0b851e900.tmp (PID: 8628)
- RegAsm.exe (PID: 5200)
- vbc.exe (PID: 9528)
- cvtres.exe (PID: 9324)
- csc.exe (PID: 9564)
- cvtres.exe (PID: 8740)
- vbc.exe (PID: 7144)
- vbc.exe (PID: 9652)
Process checks computer location settings
- Ativador KMSpico.exe (PID: 2344)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 856)
- powershell.exe (PID: 5600)
- powershell.exe (PID: 9044)
- powershell.exe (PID: 9104)
- powershell.exe (PID: 9136)
- powershell.exe (PID: 9052)
- powershell.exe (PID: 9076)
- powershell.exe (PID: 9068)
- powershell.exe (PID: 9116)
- powershell.exe (PID: 7268)
- powershell.exe (PID: 8972)
- powershell.exe (PID: 10196)
- powershell.exe (PID: 10176)
- powershell.exe (PID: 10152)
- powershell.exe (PID: 10160)
- powershell.exe (PID: 10184)
- powershell.exe (PID: 10168)
- powershell.exe (PID: 10204)
- powershell.exe (PID: 10136)
- powershell.exe (PID: 9840)
- powershell.exe (PID: 8444)
- powershell.exe (PID: 8840)
- powershell.exe (PID: 9148)
- powershell.exe (PID: 3784)
- powershell.exe (PID: 9732)
- powershell.exe (PID: 2564)
- powershell.exe (PID: 6572)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 9044)
- powershell.exe (PID: 9136)
- powershell.exe (PID: 9148)
- powershell.exe (PID: 9076)
- powershell.exe (PID: 9116)
- powershell.exe (PID: 9052)
- powershell.exe (PID: 9104)
- powershell.exe (PID: 9068)
- powershell.exe (PID: 10152)
- powershell.exe (PID: 10160)
- powershell.exe (PID: 10196)
- powershell.exe (PID: 10176)
- powershell.exe (PID: 10184)
- powershell.exe (PID: 10168)
- powershell.exe (PID: 10204)
- powershell.exe (PID: 10136)
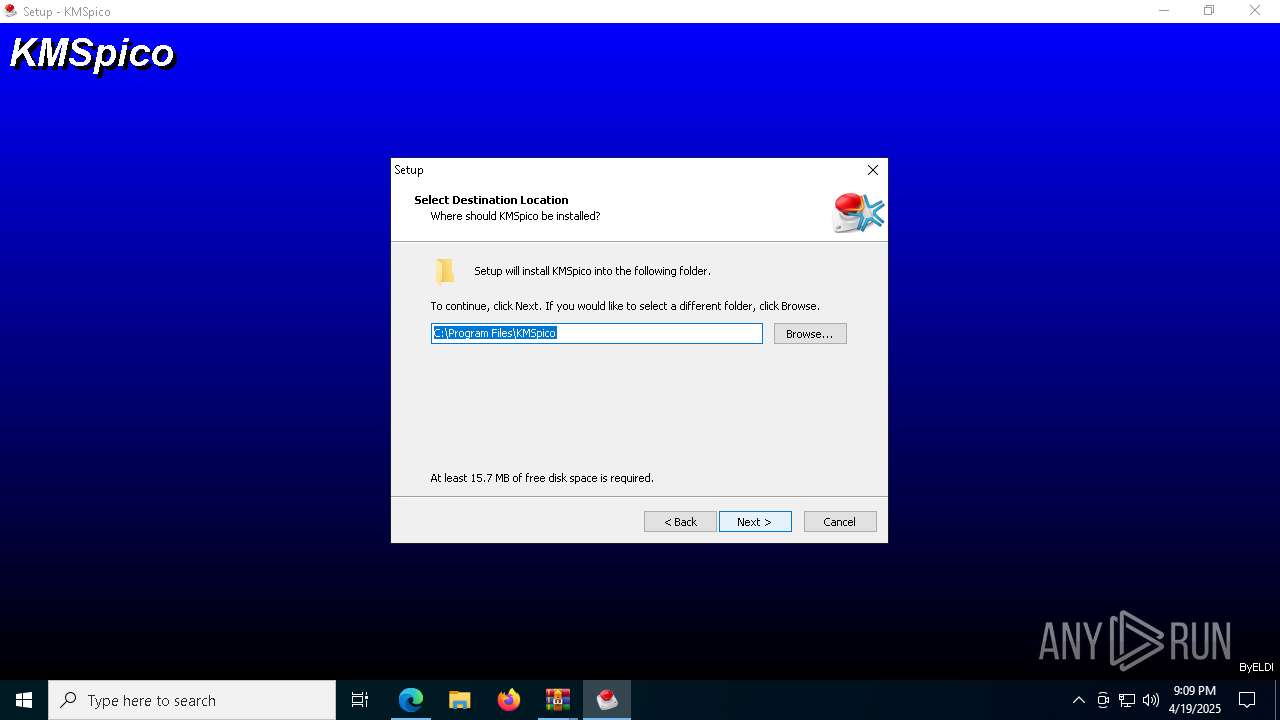
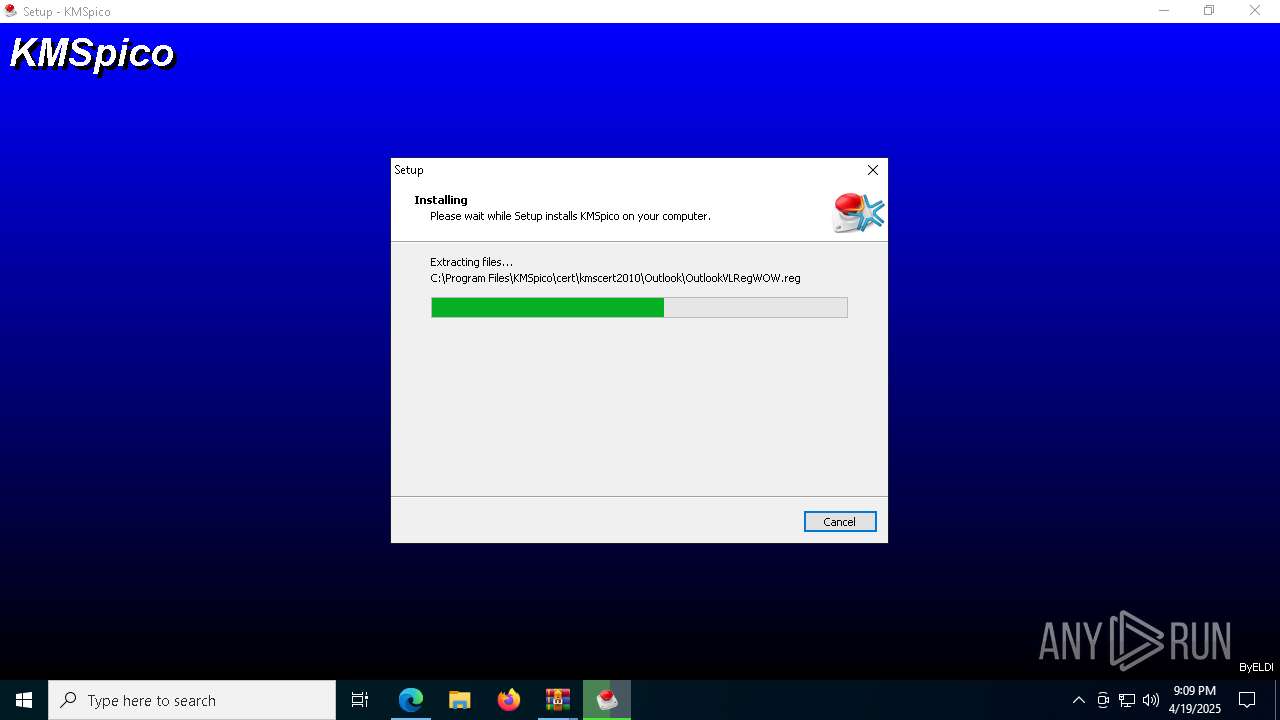
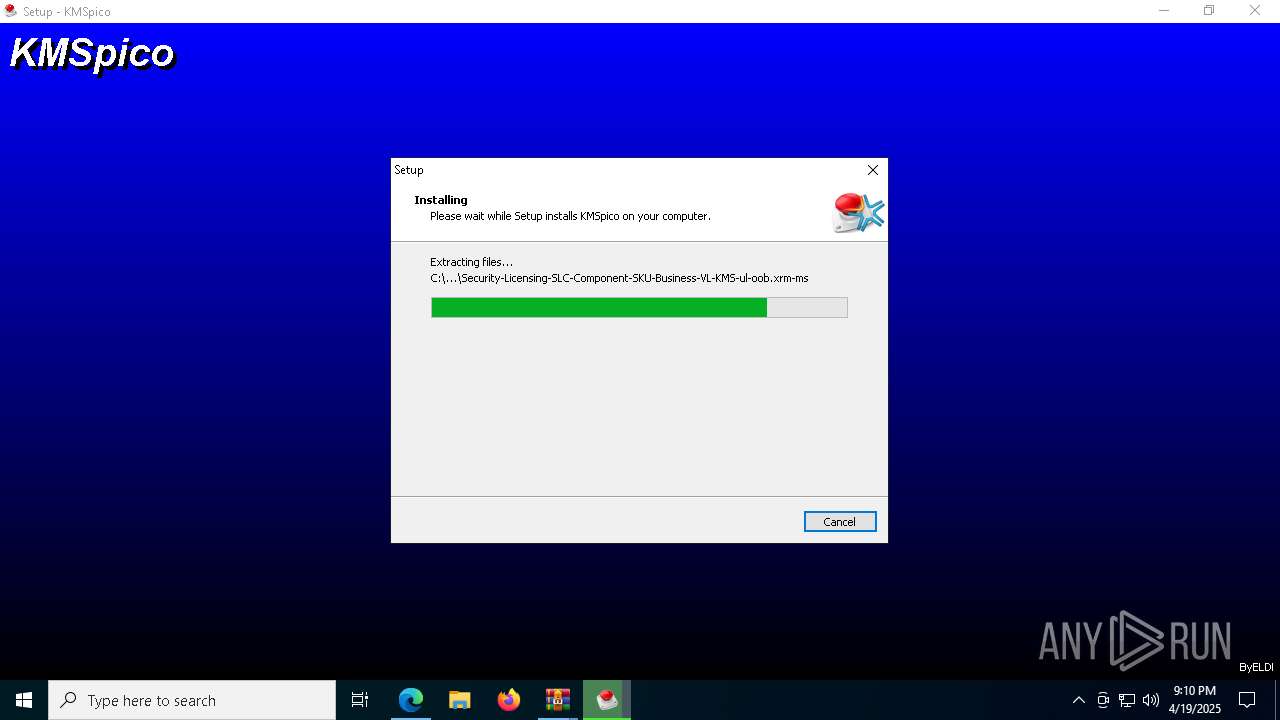
Creates files in the program directory
- 41f0f2e8-9d55-f6d4-4191-0ade0b851e900.tmp (PID: 8628)
- KMSELDI.exe (PID: 9532)
- AutoPico.exe (PID: 9408)
Reads the software policy settings
- slui.exe (PID: 3888)
- slui.exe (PID: 2104)
Detects InnoSetup installer (YARA)
- 41f0f2e8-9d55-f6d4-4191-0ade0b851e900.exe (PID: 8604)
- 41f0f2e8-9d55-f6d4-4191-0ade0b851e900.tmp (PID: 8628)
Compiled with Borland Delphi (YARA)
- 41f0f2e8-9d55-f6d4-4191-0ade0b851e900.tmp (PID: 8628)
Creates a software uninstall entry
- 41f0f2e8-9d55-f6d4-4191-0ade0b851e900.tmp (PID: 8628)
Reads product name
- KMSELDI.exe (PID: 9532)
- AutoPico.exe (PID: 9408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
409
Monitored processes
264
Malicious processes
10
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | "C:\WINDOWS\system32\net.exe" start Schedule | C:\Windows\System32\net.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=31 --mojo-platform-channel-handle=6460 --field-trial-handle=2640,i,2536326973260758160,7671819625416341730,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
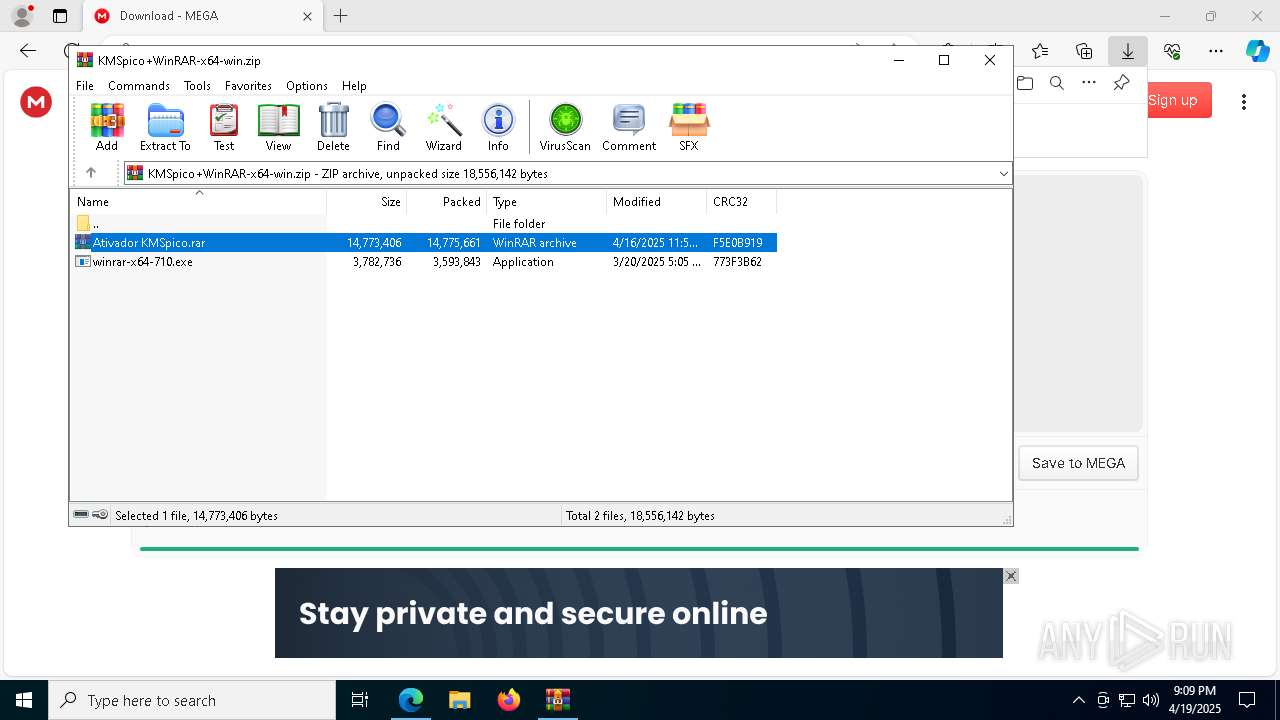
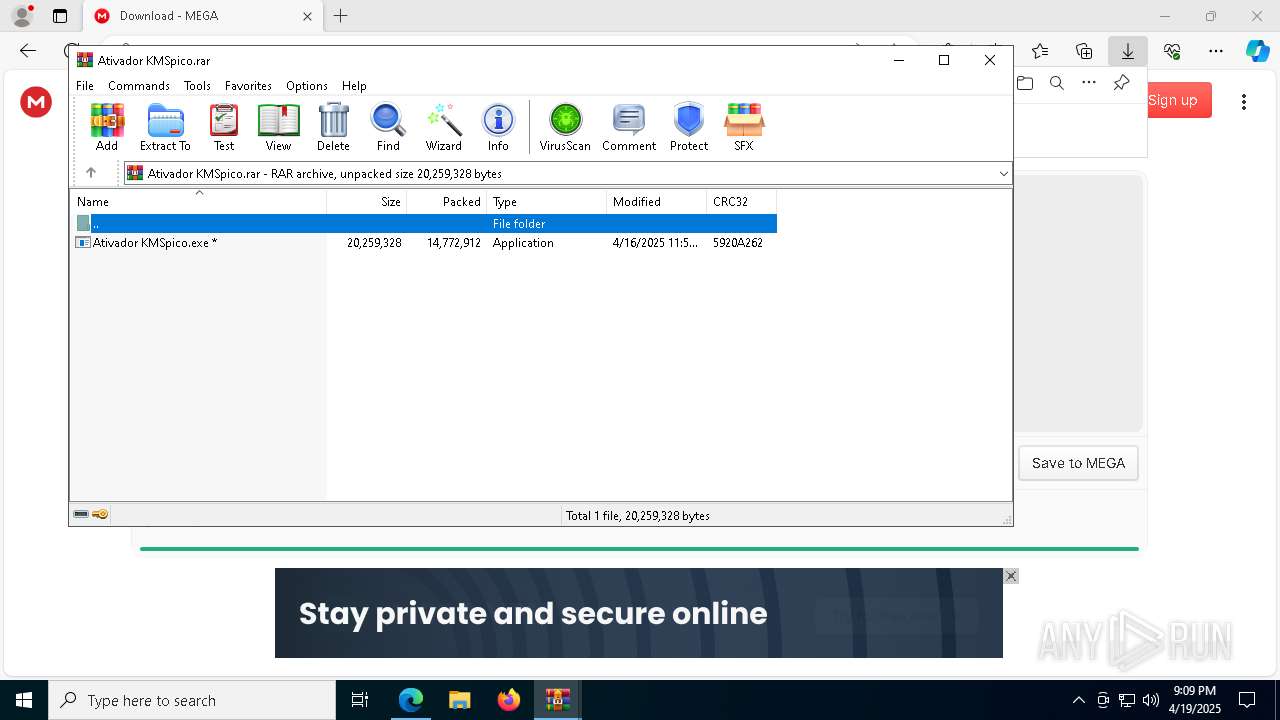
| 644 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\KMSpico+WinRAR-x64-win.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | msedge.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5496 --field-trial-handle=2640,i,2536326973260758160,7671819625416341730,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5484 --field-trial-handle=2180,i,15106981963297451396,17286937079871445047,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 744 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=33 --mojo-platform-channel-handle=7732 --field-trial-handle=2640,i,2536326973260758160,7671819625416341730,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6336 --field-trial-handle=2640,i,2536326973260758160,7671819625416341730,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7748 --field-trial-handle=2640,i,2536326973260758160,7671819625416341730,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
183 718
Read events
183 464
Write events
249
Delete events
5
Modification events
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 4F397653BE912F00 | |||
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: C8C07F53BE912F00 | |||
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197218 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {EC4F9789-07CB-4C5F-9A93-8BFDEF1EB778} | |||
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197218 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2298B6D4-EF03-4D86-BBCE-CFE6D4A7C532} | |||
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197218 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D6A8A5AB-8C48-4096-B0D9-B751E535B772} | |||
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197218 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B4401D69-31D7-4863-9ECE-5545724BCA00} | |||
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
49
Suspicious files
590
Text files
1 346
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bb43.TMP | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bb62.TMP | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bba1.TMP | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bbb1.TMP | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bbc0.TMP | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
58
TCP/UDP connections
121
DNS requests
115
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.13:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4692 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4692 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8588 | svchost.exe | HEAD | 200 | 208.89.74.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5d32607d-eea9-44fc-ac55-77800b9862a5?P1=1745625042&P2=404&P3=2&P4=KEd4mNN6rpTI%2bwjr7ChUj8add%2fcfZdwSAmjhdK4ME1P6LKtgH6uP8BL%2fFWLtbqRtYnfmKGhDVl7ekklejNXvoA%3d%3d | unknown | — | — | whitelisted |
8588 | svchost.exe | GET | 206 | 208.89.74.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5d32607d-eea9-44fc-ac55-77800b9862a5?P1=1745625042&P2=404&P3=2&P4=KEd4mNN6rpTI%2bwjr7ChUj8add%2fcfZdwSAmjhdK4ME1P6LKtgH6uP8BL%2fFWLtbqRtYnfmKGhDVl7ekklejNXvoA%3d%3d | unknown | — | — | whitelisted |
8588 | svchost.exe | GET | 206 | 208.89.74.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5d32607d-eea9-44fc-ac55-77800b9862a5?P1=1745625042&P2=404&P3=2&P4=KEd4mNN6rpTI%2bwjr7ChUj8add%2fcfZdwSAmjhdK4ME1P6LKtgH6uP8BL%2fFWLtbqRtYnfmKGhDVl7ekklejNXvoA%3d%3d | unknown | — | — | whitelisted |
8588 | svchost.exe | GET | 206 | 208.89.74.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5d32607d-eea9-44fc-ac55-77800b9862a5?P1=1745625042&P2=404&P3=2&P4=KEd4mNN6rpTI%2bwjr7ChUj8add%2fcfZdwSAmjhdK4ME1P6LKtgH6uP8BL%2fFWLtbqRtYnfmKGhDVl7ekklejNXvoA%3d%3d | unknown | — | — | whitelisted |
8588 | svchost.exe | GET | 206 | 208.89.74.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5d32607d-eea9-44fc-ac55-77800b9862a5?P1=1745625042&P2=404&P3=2&P4=KEd4mNN6rpTI%2bwjr7ChUj8add%2fcfZdwSAmjhdK4ME1P6LKtgH6uP8BL%2fFWLtbqRtYnfmKGhDVl7ekklejNXvoA%3d%3d | unknown | — | — | whitelisted |
8588 | svchost.exe | GET | 206 | 208.89.74.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5d32607d-eea9-44fc-ac55-77800b9862a5?P1=1745625042&P2=404&P3=2&P4=KEd4mNN6rpTI%2bwjr7ChUj8add%2fcfZdwSAmjhdK4ME1P6LKtgH6uP8BL%2fFWLtbqRtYnfmKGhDVl7ekklejNXvoA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.13:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7704 | msedge.exe | 104.21.96.1:443 | ativadorkmspico.com | — | — | unknown |
7312 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7704 | msedge.exe | 142.250.184.195:443 | fonts.gstatic.com | — | — | whitelisted |
7704 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7704 | msedge.exe | 216.58.206.74:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
ativadorkmspico.com |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7704 | msedge.exe | Misc activity | ET INFO URL Shortener Service Domain in DNS Lookup (rebrand .ly) |
7704 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (rebrand .ly) |
7704 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (rebrand .ly) |
7704 | msedge.exe | Misc activity | ET INFO URL Shortener Service Domain in DNS Lookup (rebrand .ly) |
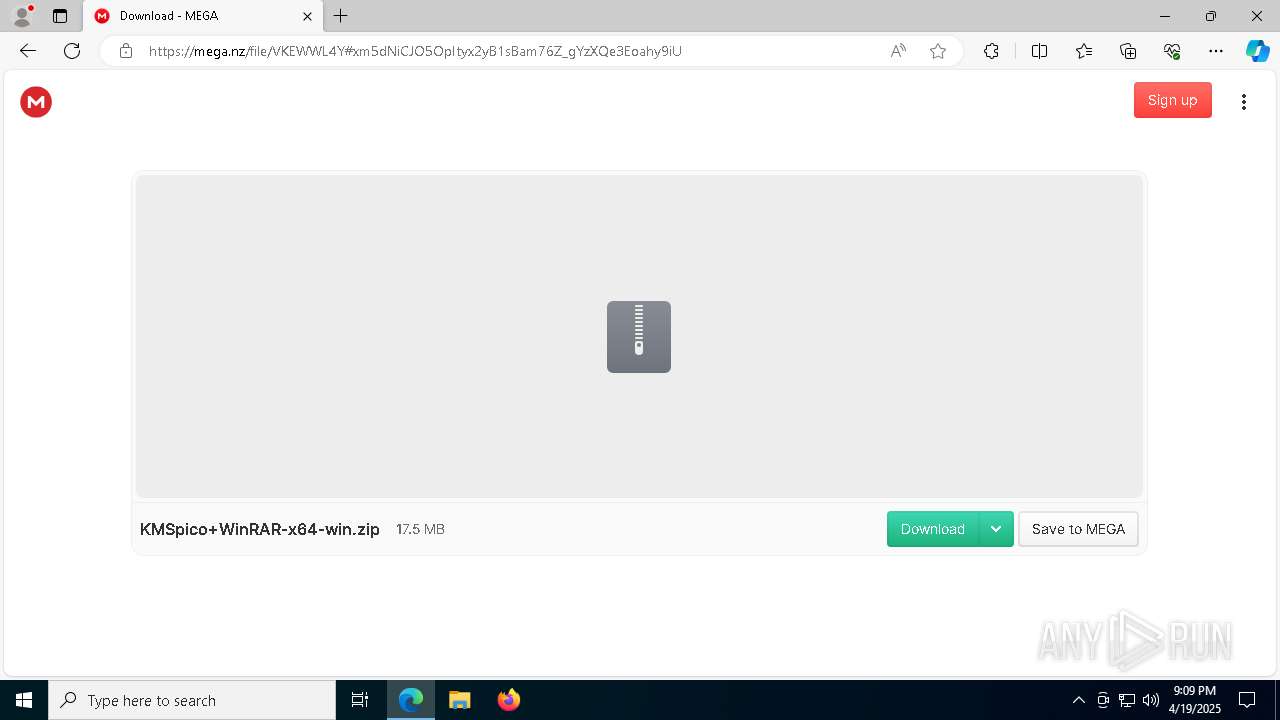
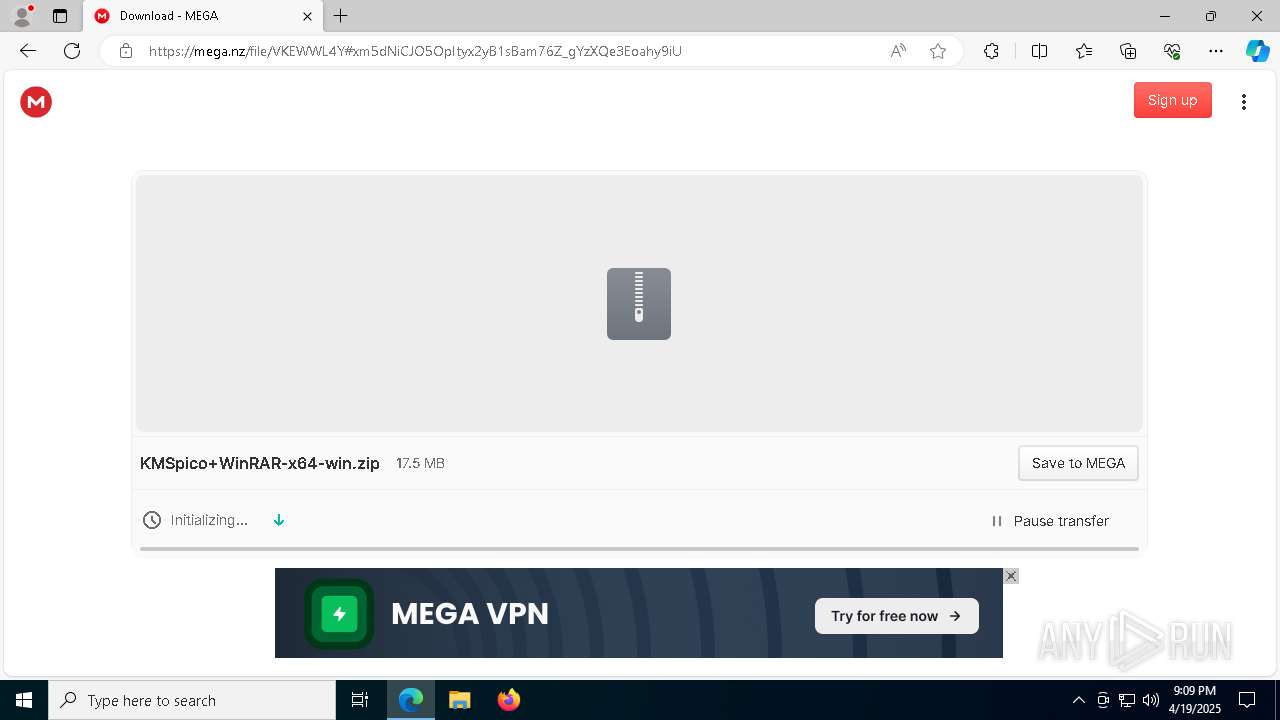
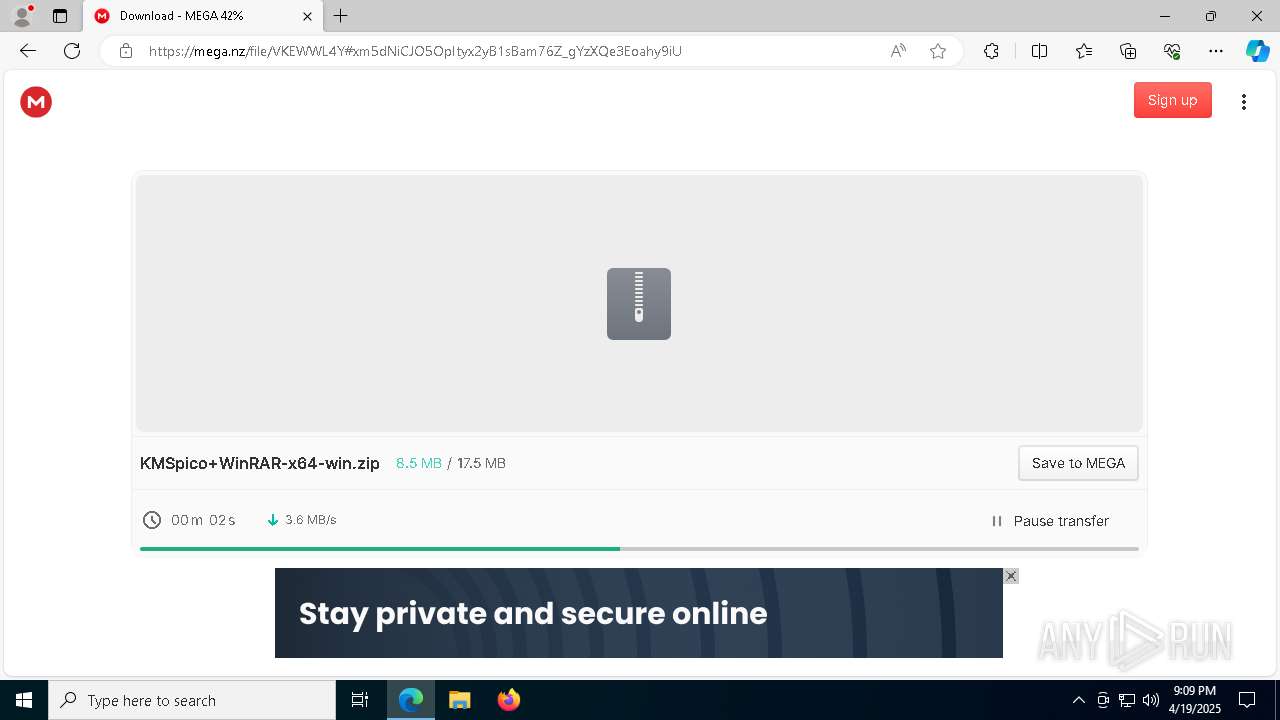
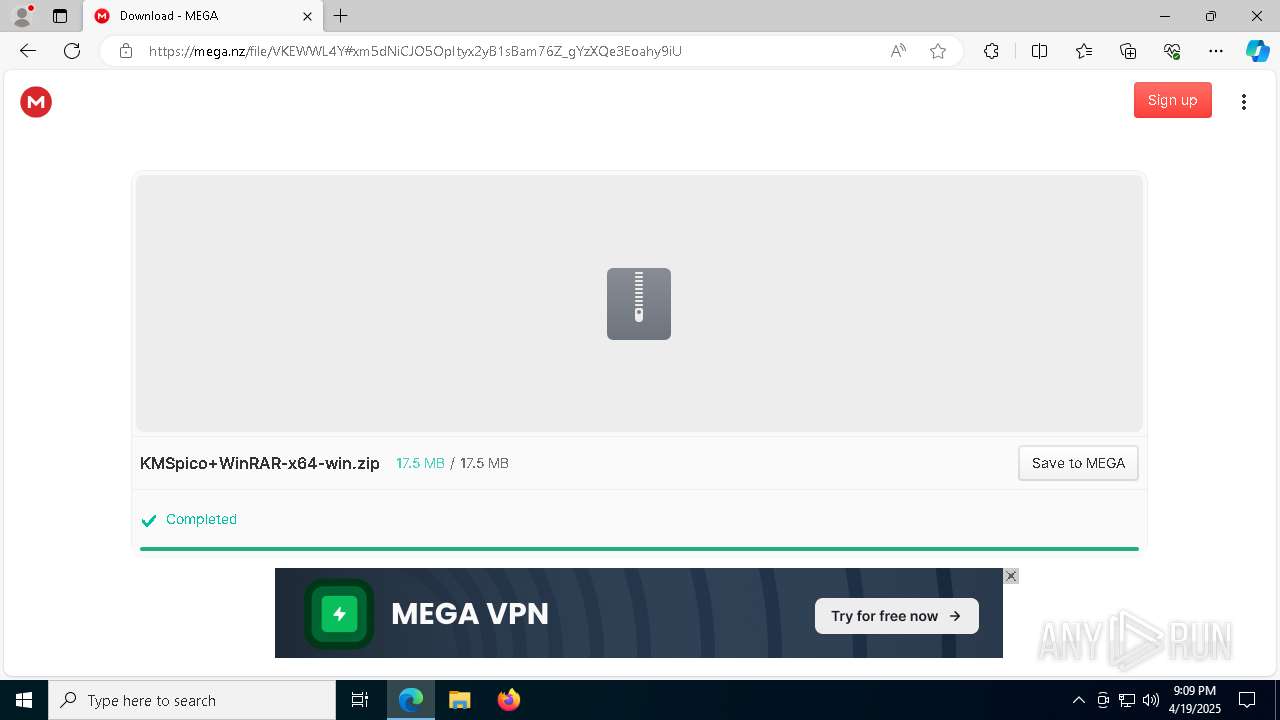
7704 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7704 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7704 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7704 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7704 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
7704 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |