| URL: | https://www.mumuplayer.com/ |
| Full analysis: | https://app.any.run/tasks/237c9b57-8db4-4541-b6e0-5ba4ad142be5 |
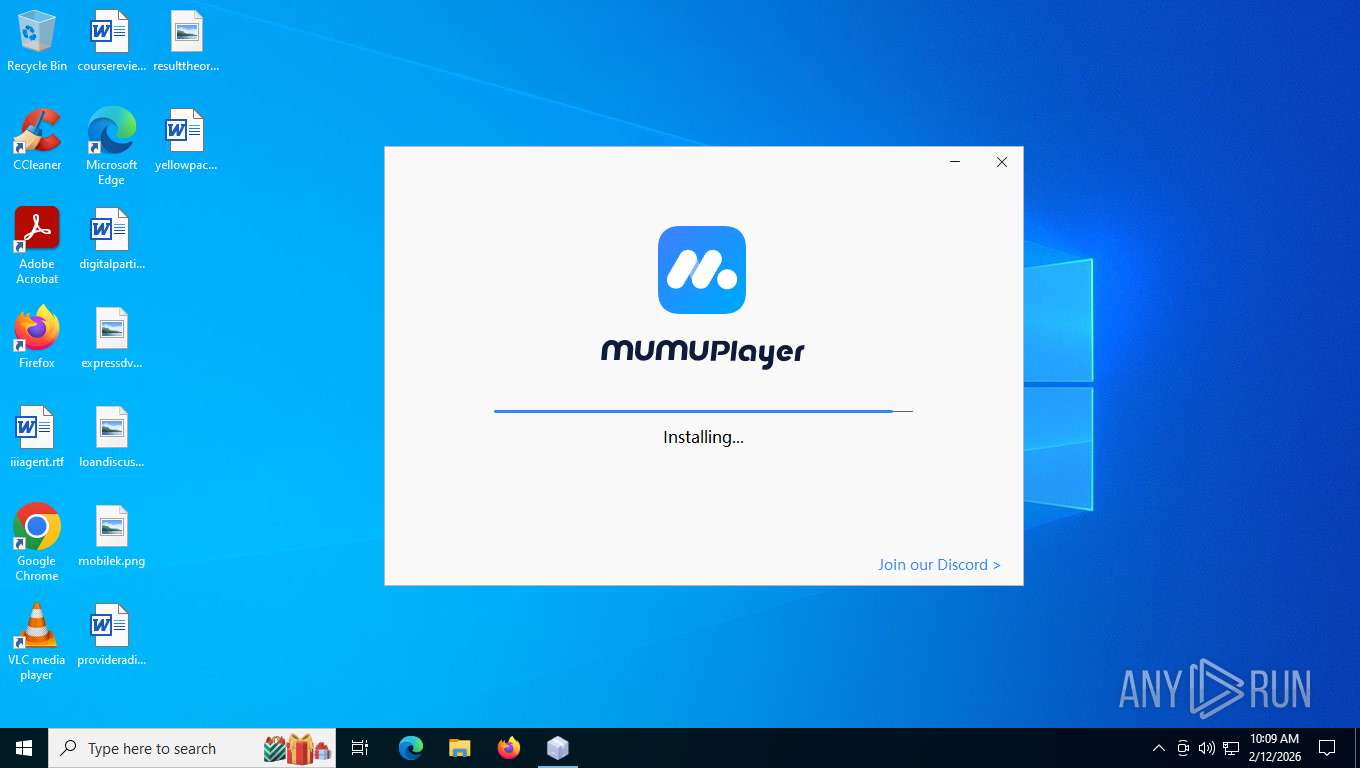
| Verdict: | Malicious activity |
| Analysis date: | February 12, 2026, 15:06:13 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 757B751DD93CF08A1D2D64EC68F85ECA |
| SHA1: | 5BBEAEF09566243215DF1E512D1011047E9FA4E2 |
| SHA256: | 69472ED958C699507A3A5D72CE1C1D57E528AA87D6DD30EB709281DC52995CC8 |
| SSDEEP: | 3:N8DSL7VSLR:2OLiR |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- MuMu-setup-V5.21.3.3067-overseas-0204212000.exe (PID: 1212)
SUSPICIOUS
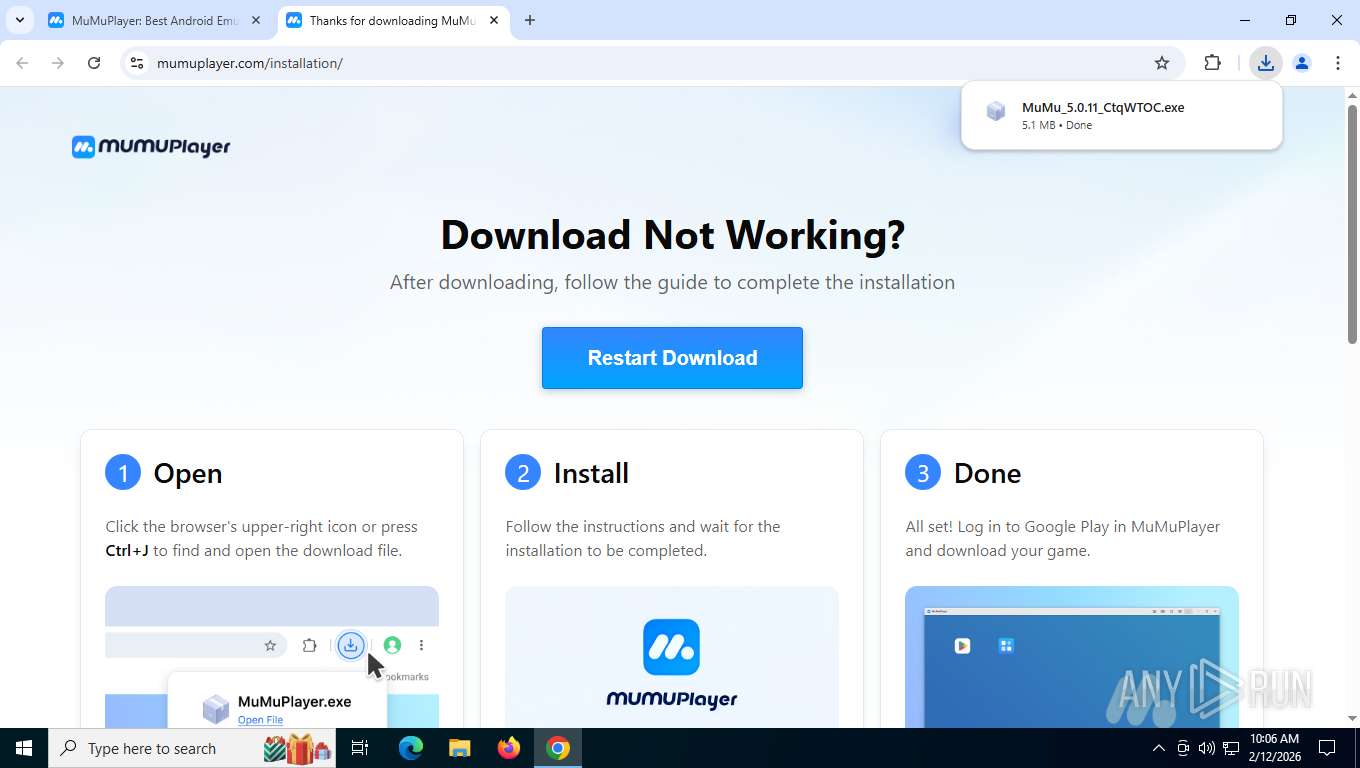
The process drops C-runtime libraries
- MuMu_5.0.11_CtqWTOC.exe (PID: 7780)
- MuMu-setup-V5.21.3.3067-overseas-0204212000.exe (PID: 1212)
Process drops legitimate windows executable
- MuMu_5.0.11_CtqWTOC.exe (PID: 7780)
- MuMu-setup-V5.21.3.3067-overseas-0204212000.exe (PID: 1212)
Drops 7-zip archiver for unpacking
- MuMu_5.0.11_CtqWTOC.exe (PID: 7780)
- MuMu-setup-V5.21.3.3067-overseas-0204212000.exe (PID: 1212)
Executable content was dropped or overwritten
- MuMu_5.0.11_CtqWTOC.exe (PID: 7780)
- MuMu-setup-V5.21.3.3067-overseas-0204212000.exe (PID: 1212)
- ColaBoxChecker.exe (PID: 6908)
Drops a system driver (possible attempt to evade defenses)
- ColaBoxChecker.exe (PID: 6908)
- MuMu-setup-V5.21.3.3067-overseas-0204212000.exe (PID: 1212)
The process creates files with name similar to system file names
- MuMu-setup-V5.21.3.3067-overseas-0204212000.exe (PID: 1212)
Malware-specific behavior (creating "System.dll" in Temp)
- MuMu-setup-V5.21.3.3067-overseas-0204212000.exe (PID: 1212)
Windows service management via SC.EXE
- sc.exe (PID: 3240)
- sc.exe (PID: 8628)
- sc.exe (PID: 7636)
- sc.exe (PID: 8688)
- sc.exe (PID: 7392)
Creates/Modifies COM task schedule object
- MuMu-setup-V5.21.3.3067-overseas-0204212000.exe (PID: 1212)
- regsvr32.exe (PID: 7204)
Uses NETSH.EXE to add a firewall rule or allowed programs
- MuMu-setup-V5.21.3.3067-overseas-0204212000.exe (PID: 1212)
INFO
Drops script file
- chrome.exe (PID: 1884)
- MuMu-setup-V5.21.3.3067-overseas-0204212000.exe (PID: 1212)
Application launched itself
- chrome.exe (PID: 1884)
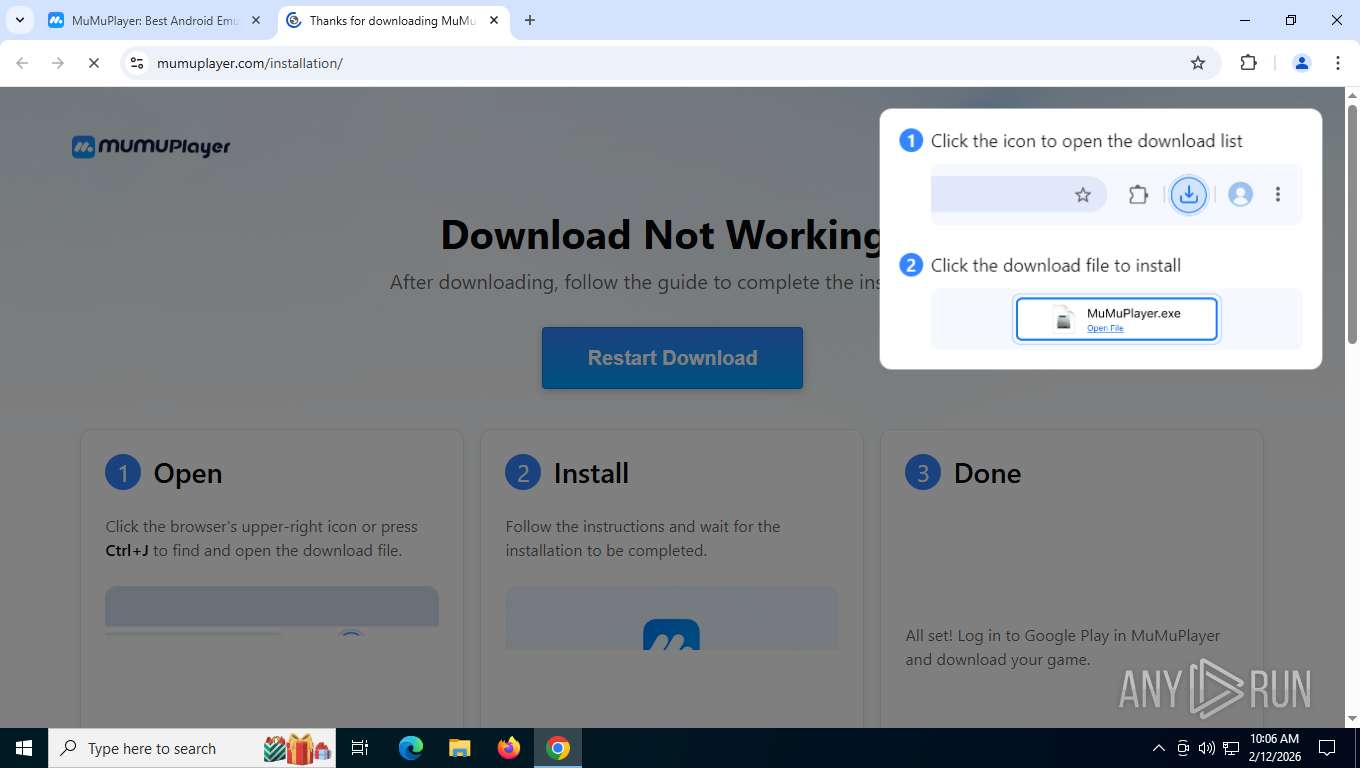
Launching a file from the Downloads directory
- chrome.exe (PID: 1884)
The sample compiled with english language support
- chrome.exe (PID: 1884)
- chrome.exe (PID: 9092)
- MuMu_5.0.11_CtqWTOC.exe (PID: 7780)
- MuMu-setup-V5.21.3.3067-overseas-0204212000.exe (PID: 1212)
Executable content was dropped or overwritten
- chrome.exe (PID: 9092)
- chrome.exe (PID: 1884)
Checks supported languages
- MuMu_5.0.11_CtqWTOC.exe (PID: 7780)
- HyperVChecker.exe (PID: 848)
- HyperVChecker.exe (PID: 5516)
- HyperVChecker.exe (PID: 7548)
- MuMuDownloader.exe (PID: 6172)
- MuMu-setup-V5.21.3.3067-overseas-0204212000.exe (PID: 1212)
- ColaBoxChecker.exe (PID: 6908)
- MuMuVMMSVC.exe (PID: 1932)
- MuMuVMMSVC.exe (PID: 6664)
- NetLwfUninstall.exe (PID: 8380)
- SUPUninstall.exe (PID: 8360)
- SUPUninstall.exe (PID: 9044)
- SUPInstall.exe (PID: 8976)
- nemu-downloader.exe (PID: 5216)
The sample compiled with chinese language support
- MuMu_5.0.11_CtqWTOC.exe (PID: 7780)
- MuMu-setup-V5.21.3.3067-overseas-0204212000.exe (PID: 1212)
Create files in a temporary directory
- MuMu_5.0.11_CtqWTOC.exe (PID: 7780)
- nemu-downloader.exe (PID: 5216)
- ColaBoxChecker.exe (PID: 6908)
- MuMuDownloader.exe (PID: 6172)
- MuMu-setup-V5.21.3.3067-overseas-0204212000.exe (PID: 1212)
Reads the computer name
- nemu-downloader.exe (PID: 5216)
- ColaBoxChecker.exe (PID: 6908)
- MuMuDownloader.exe (PID: 6172)
- MuMu-setup-V5.21.3.3067-overseas-0204212000.exe (PID: 1212)
- MuMuVMMSVC.exe (PID: 1932)
- MuMuVMMSVC.exe (PID: 6664)
- NetLwfUninstall.exe (PID: 8380)
- SUPUninstall.exe (PID: 9044)
- SUPUninstall.exe (PID: 8360)
- SUPInstall.exe (PID: 8976)
Creates files in the program directory
- nemu-downloader.exe (PID: 5216)
- MuMu-setup-V5.21.3.3067-overseas-0204212000.exe (PID: 1212)
Reads the machine GUID from the registry
- MuMuDownloader.exe (PID: 6172)
There is functionality for taking screenshot (YARA)
- nemu-downloader.exe (PID: 5216)
- MuMu-setup-V5.21.3.3067-overseas-0204212000.exe (PID: 1212)
Checks proxy server information
- slui.exe (PID: 2600)
Reads security settings of Internet Explorer
- MuMu-setup-V5.21.3.3067-overseas-0204212000.exe (PID: 1212)
- nemu-downloader.exe (PID: 5216)
Process checks computer location settings
- nemu-downloader.exe (PID: 5216)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
233
Monitored processes
78
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 848 | "C:\Users\admin\AppData\Local\Temp\7zE020BE64\HyperVChecker.exe" | C:\Users\admin\AppData\Local\Temp\7zE020BE64\HyperVChecker.exe | — | nemu-downloader.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5724,i,9969894442809732518,13815591124023418089,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5856 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
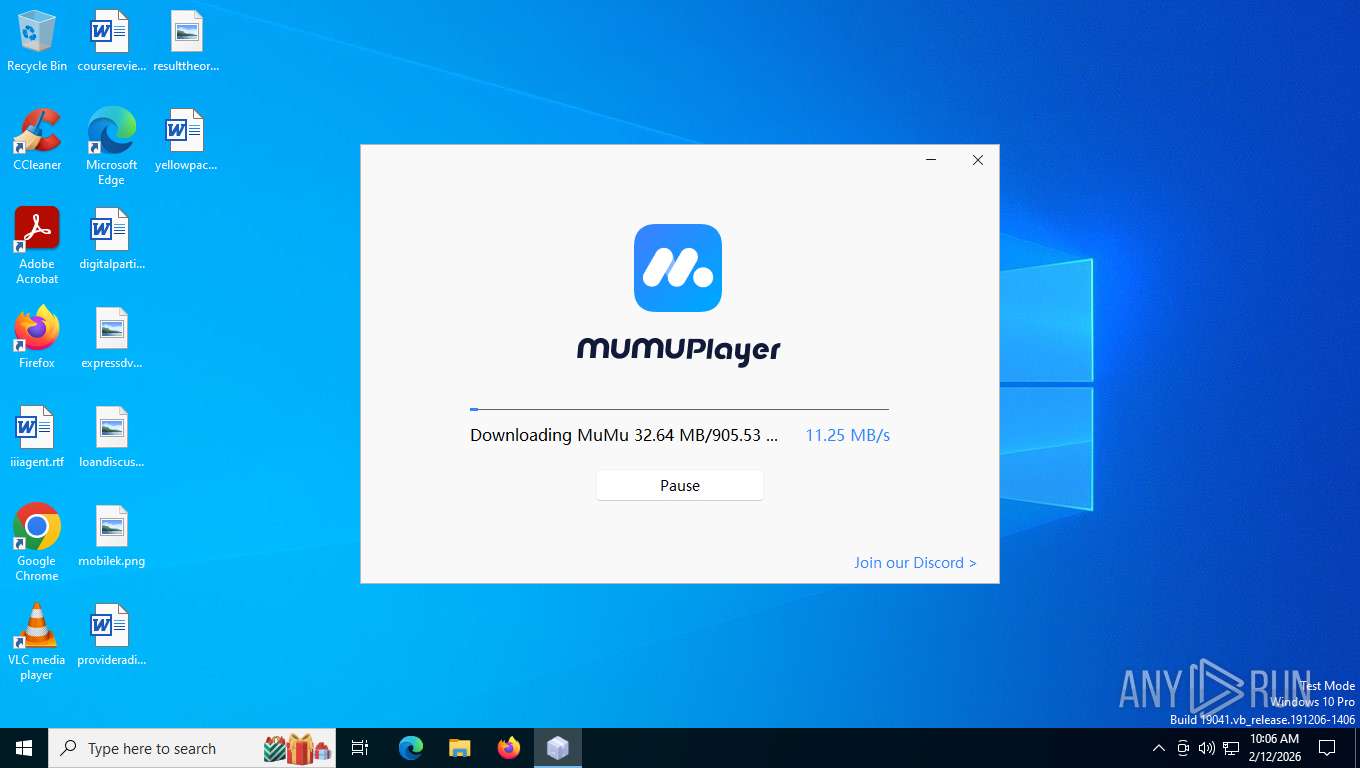
| 1212 | "C:\Users\admin\AppData\Local\Temp\MuMu-setup-V5.21.3.3067-overseas-0204212000.exe" /gv=2 /S /auto_start=false /fchannel=gw-overseas12 /D=C:\Program Files\Netease\MuMuPlayer | C:\Users\admin\AppData\Local\Temp\MuMu-setup-V5.21.3.3067-overseas-0204212000.exe | nemu-downloader.exe | ||||||||||||
User: admin Company: NetEase Games Integrity Level: HIGH Description: MuMuPlayer Version: 5.21.3.3067 Modules
| |||||||||||||||
| 1388 | /u /s "C:\Program Files\MuMuVMMVbox\Hypervisor\MuMuVMMProxyStub.dll" | C:\Windows\System32\regsvr32.exe | — | regsvr32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1428 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | HyperVChecker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=6224,i,9969894442809732518,13815591124023418089,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=6840 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disable-features=HttpsUpgrades,HttpsFirstModeV2,HttpsOnlyMode,HttpsFirstBalancedMode --no-first-run --no-default-browser-check https://www.mumuplayer.com/ | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1932 | "C:\Program Files\MuMuVMMVbox\Hypervisor\MuMuVMMSVC.exe" /UnregServer | C:\Program Files\MuMuVMMVbox\Hypervisor\MuMuVMMSVC.exe | — | MuMu-setup-V5.21.3.3067-overseas-0204212000.exe | |||||||||||
User: admin Company: NetEase Corporation Integrity Level: HIGH Description: MuMuVMM Interface Exit code: 0 Version: 6.1.36.152435 Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --string-annotations --field-trial-handle=6244,i,9969894442809732518,13815591124023418089,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=6268 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2284 | /u /s "C:\Program Files\MuMuVMMVbox\Hypervisor\MuMuVMMC.dll" | C:\Windows\System32\regsvr32.exe | — | regsvr32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 380
Read events
9 362
Write events
18
Delete events
0
Modification events
| (PID) Process: | (5216) nemu-downloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\NemuServer |
| Operation: | write | Name: | uuid |
Value: a2cea944-9ba7-4181-8e12-c36b7eaab2c5 | |||
| (PID) Process: | (5216) nemu-downloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\NemuServer |
| Operation: | write | Name: | channel |
Value: gw-overseas12 | |||
| (PID) Process: | (5216) nemu-downloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\NemuServer |
| Operation: | write | Name: | package |
Value: mumu | |||
| (PID) Process: | (1212) MuMu-setup-V5.21.3.3067-overseas-0204212000.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{00020424-0000-0000-C000-000000000046}\InprocServer32 |
| Operation: | write | Name: | InprocServer32 |
Value: C:\WINDOWS\system32\oleaut32.dll | |||
| (PID) Process: | (1212) MuMu-setup-V5.21.3.3067-overseas-0204212000.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{00020420-0000-0000-C000-000000000046}\InprocServer32 |
| Operation: | write | Name: | InprocServer32 |
Value: C:\WINDOWS\system32\oleaut32.dll | |||
| (PID) Process: | (1212) MuMu-setup-V5.21.3.3067-overseas-0204212000.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\SOFTWARE\Classes\CLSID\{00020420-0000-0000-C000-000000000046}\InprocServer32 |
| Operation: | write | Name: | InprocServer32 |
Value: C:\WINDOWS\system32\oleaut32.dll | |||
| (PID) Process: | (1212) MuMu-setup-V5.21.3.3067-overseas-0204212000.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\SOFTWARE\Classes\CLSID\{00020420-0000-0000-C000-000000000046}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (1212) MuMu-setup-V5.21.3.3067-overseas-0204212000.exe | Key: | HKEY_CLASSES_ROOT\CLSID\{00020424-0000-0000-C000-000000000046}\InprocServer32 |
| Operation: | write | Name: | InprocServer32 |
Value: C:\WINDOWS\system32\oleaut32.dll | |||
| (PID) Process: | (1212) MuMu-setup-V5.21.3.3067-overseas-0204212000.exe | Key: | HKEY_CLASSES_ROOT\CLSID\{00020424-0000-0000-C000-000000000046}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (1212) MuMu-setup-V5.21.3.3067-overseas-0204212000.exe | Key: | HKEY_CLASSES_ROOT\CLSID\{00020420-0000-0000-C000-000000000046}\InprocServer32 |
| Operation: | write | Name: | InprocServer32 |
Value: C:\WINDOWS\system32\oleaut32.dll | |||
Executable files
764
Suspicious files
219
Text files
2 378
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF1e4f08.TMP | — | |
MD5:— | SHA256:— | |||
| 1884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF1e4f18.TMP | — | |
MD5:— | SHA256:— | |||
| 1884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF1e4f18.TMP | — | |
MD5:— | SHA256:— | |||
| 1884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF1e4f27.TMP | — | |
MD5:— | SHA256:— | |||
| 1884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF1e4f27.TMP | — | |
MD5:— | SHA256:— | |||
| 1884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1e4f18.TMP | — | |
MD5:— | SHA256:— | |||
| 1884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF1e4f27.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
286
TCP/UDP connections
125
DNS requests
99
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
9092 | chrome.exe | GET | 200 | 142.251.208.14:80 | http://clients2.google.com/time/1/current?cup2key=8:fQoZxg1bPbWLsbMS5iT3IcZvJMUx_hOe0tCoVvyF91E&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 101 b | whitelisted |
9092 | chrome.exe | GET | 200 | 172.217.16.170:443 | https://safebrowsingohttpgateway.googleapis.com/v1/ohttp/hpkekeyconfig?key=AIzaSyA2KlwBX3mkFo30om9LUFYQhpqLoa_BNhE | US | binary | 41 b | whitelisted |
9092 | chrome.exe | GET | 200 | 2.16.10.173:443 | https://www.mumuplayer.com/ | NL | html | 94.3 Kb | unknown |
9092 | chrome.exe | GET | 200 | 2.16.10.173:443 | https://www.mumuplayer.com/pc/gw/20250122155220/img/kv_bg_fca44add.jpg | NL | image | 36.6 Kb | unknown |
9092 | chrome.exe | POST | 200 | 142.251.127.84:443 | https://accounts.google.com/ListAccounts?gpsia=1&source=ChromiumBrowser&json=standard | US | text | 17 b | whitelisted |
9092 | chrome.exe | GET | 200 | 2.16.10.173:443 | https://www.mumuplayer.com/pc/gw/20250122155220/data/kv_dark.webp | NL | image | 130 Kb | unknown |
9092 | chrome.exe | GET | 200 | 2.16.10.173:443 | https://www.mumuplayer.com/pc/gw/20250122155220/js/cms/index_home_1df196a2.js | NL | text | 33.2 Kb | unknown |
9092 | chrome.exe | GET | 200 | 2.16.10.173:443 | https://www.mumuplayer.com/pc/gw/20250122155220/img/search_btn_ef976b39.png | NL | image | 1.25 Kb | unknown |
9092 | chrome.exe | GET | 200 | 2.16.10.173:443 | https://www.mumuplayer.com/pc/gw/20250122155220/img/kv_bg_98bec904.jpg | NL | image | 20.3 Kb | unknown |
9092 | chrome.exe | GET | 200 | 2.16.10.173:443 | https://www.mumuplayer.com/pc/gw/20250122155220/data/md6.jpg | NL | image | 173 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
9088 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4948 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
9092 | chrome.exe | 142.251.208.14:80 | clients2.google.com | GOOGLE | US | whitelisted |
9092 | chrome.exe | 172.217.16.170:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
9092 | chrome.exe | 142.251.37.3:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
9092 | chrome.exe | 142.251.127.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
9092 | chrome.exe | 2.16.10.173:443 | www.mumuplayer.com | AKAMAI-ASN1 | NL | whitelisted |
9092 | chrome.exe | 2.19.126.210:443 | comm.res.easebar.com | AKAMAI-ASN1 | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.mumuplayer.com |
| whitelisted |
accounts.google.com |
| whitelisted |
comm.res.easebar.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
9092 | chrome.exe | Potentially Bad Traffic | ET INFO PE EXE or DLL Windows file download HTTP |
9092 | chrome.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
6172 | MuMuDownloader.exe | A Network Trojan was detected | ET USER_AGENTS Aria2 User-Agent |
6172 | MuMuDownloader.exe | Potentially Bad Traffic | ET INFO PE EXE or DLL Windows file download HTTP |
6172 | MuMuDownloader.exe | A Network Trojan was detected | ET USER_AGENTS Aria2 User-Agent |
6172 | MuMuDownloader.exe | A Network Trojan was detected | ET USER_AGENTS Aria2 User-Agent |
6172 | MuMuDownloader.exe | A Network Trojan was detected | ET USER_AGENTS Aria2 User-Agent |
6172 | MuMuDownloader.exe | A Network Trojan was detected | ET USER_AGENTS Aria2 User-Agent |
9088 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
6172 | MuMuDownloader.exe | A Network Trojan was detected | ET USER_AGENTS Aria2 User-Agent |