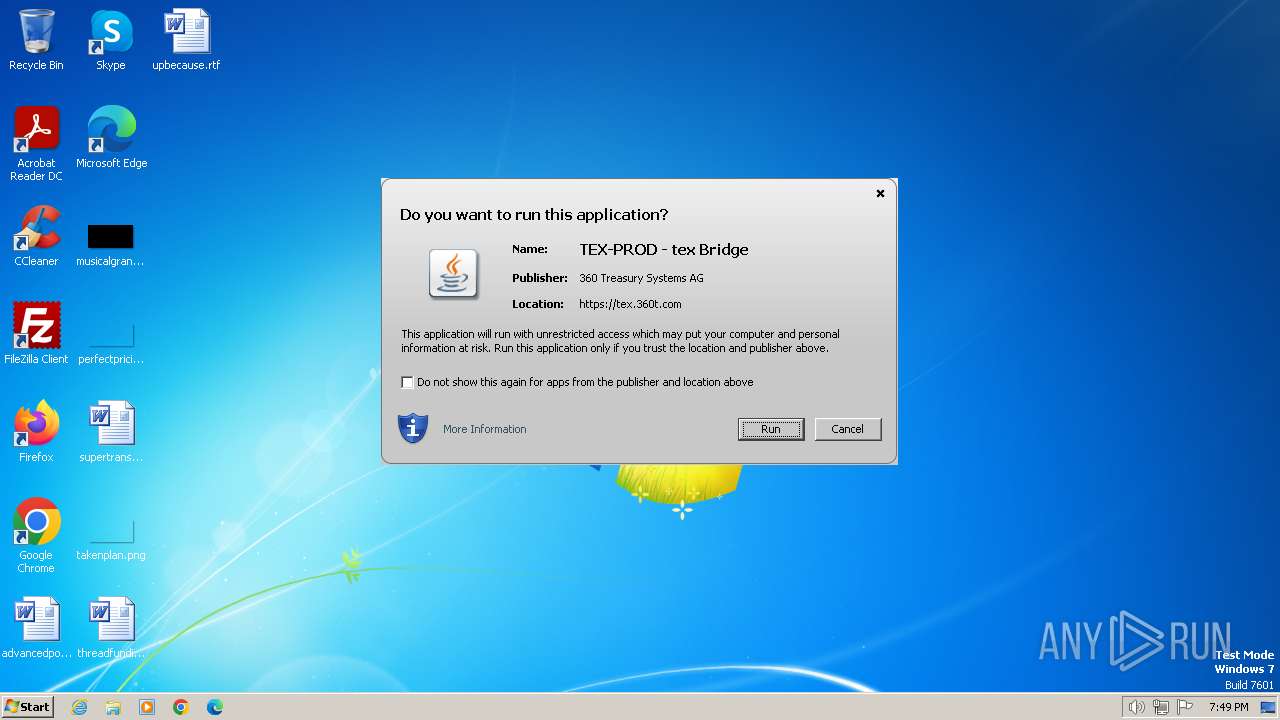
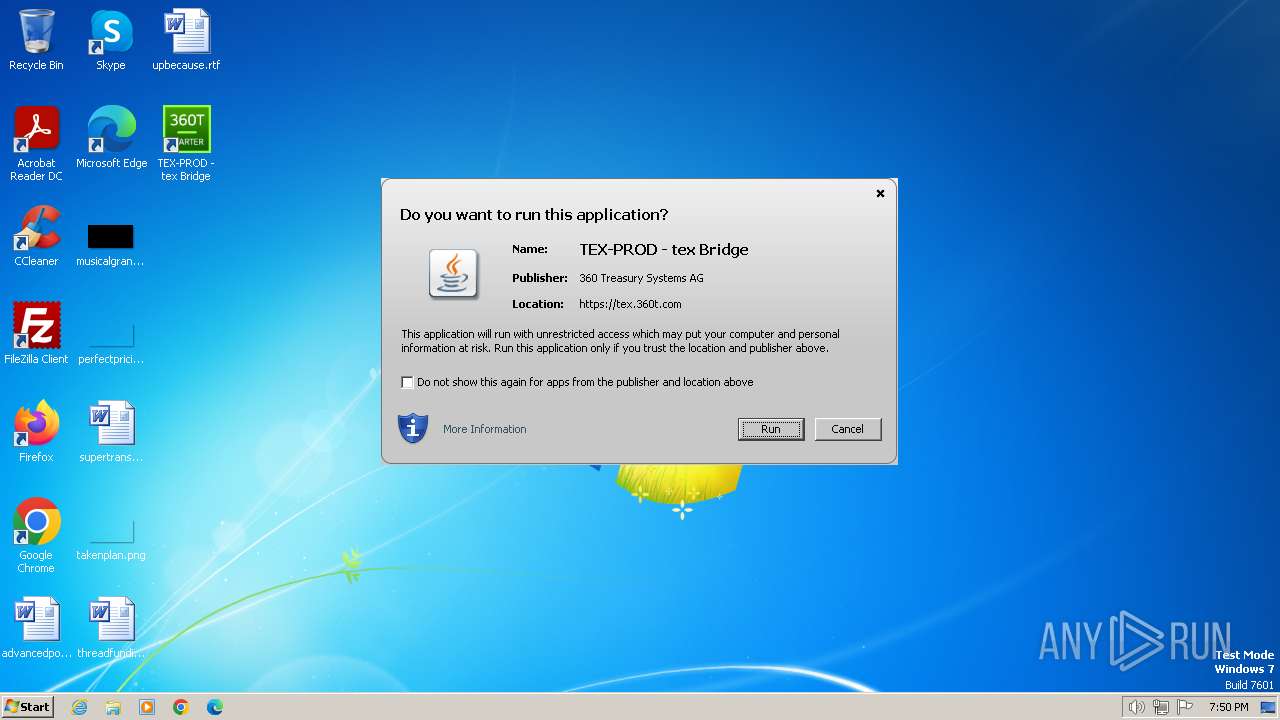
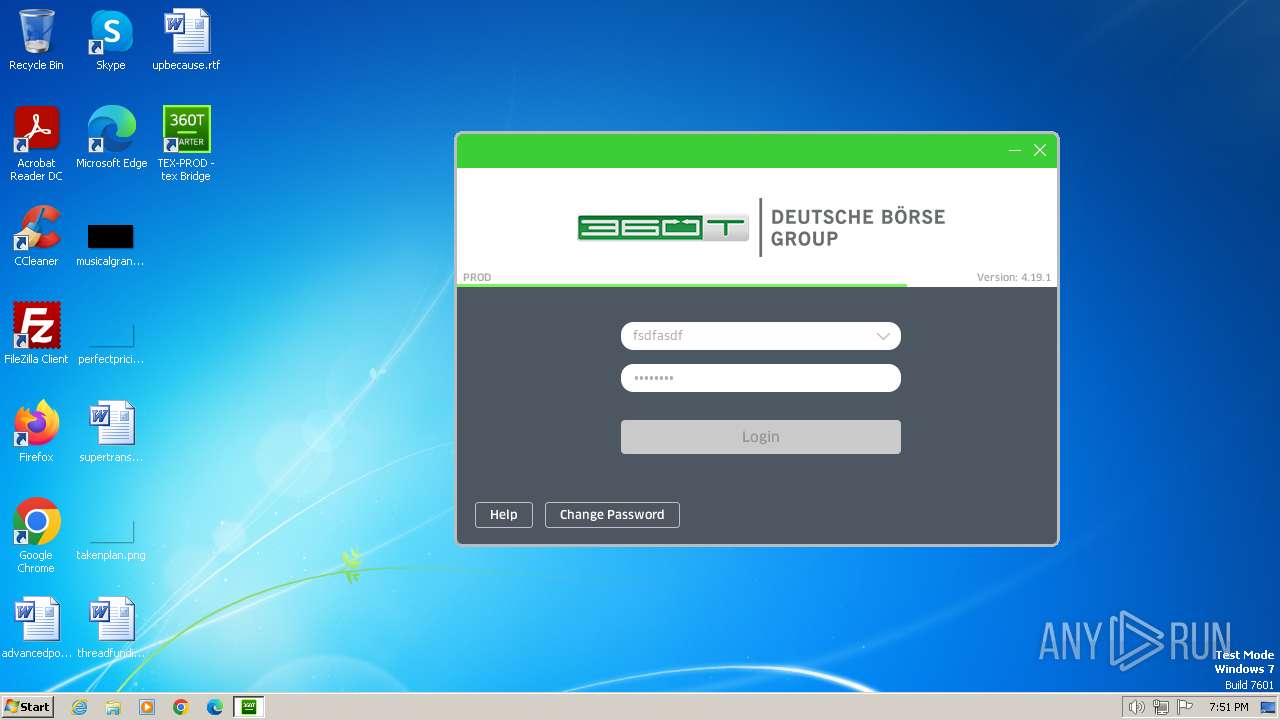
| URL: | https://tex.360t.com/bridge-tex.jnlp |
| Full analysis: | https://app.any.run/tasks/11cf537f-72b2-4429-acc4-89452f9f4f52 |
| Verdict: | Malicious activity |
| Analysis date: | February 14, 2024, 19:49:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6E6086BB6FD23BCBD3994A420EF984DF |
| SHA1: | 86D5193DC7DFAA361363CADDB7E198874F50A05D |
| SHA256: | 6934062F6601C012558BBCDB5526B2BB2BB4FB6E225573C482585E4EC535F9C1 |
| SSDEEP: | 3:N8IYuNIRAJP3:2IY6sGP |
MALICIOUS
No malicious indicators.SUSPICIOUS
Application launched itself
- javaws.exe (PID: 3956)
- jp2launcher.exe (PID: 1992)
- javaws.exe (PID: 1628)
- javaws.exe (PID: 3472)
- jp2launcher.exe (PID: 1124)
- jp2launcher.exe (PID: 3016)
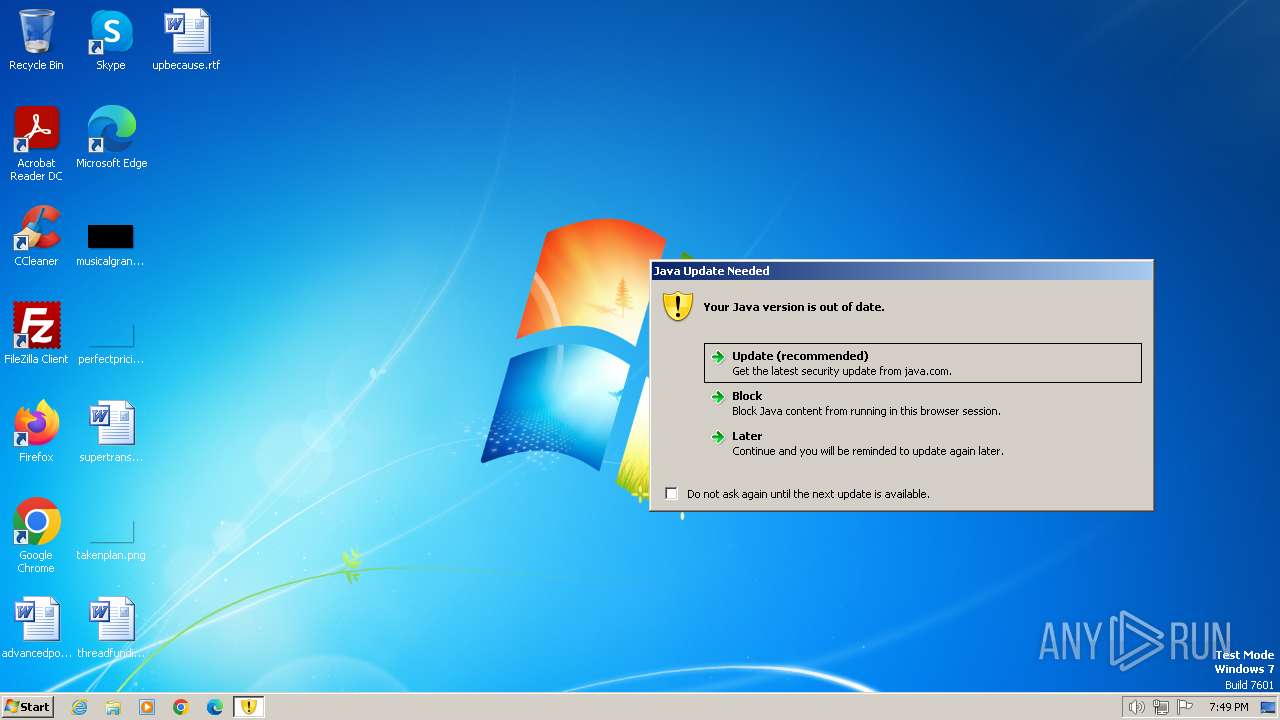
Checks for Java to be installed
- javaw.exe (PID: 2168)
- javaw.exe (PID: 1824)
- javaws.exe (PID: 3956)
- jp2launcher.exe (PID: 1992)
- jp2launcher.exe (PID: 3980)
- javaws.exe (PID: 1628)
- jp2launcher.exe (PID: 1124)
- javaws.exe (PID: 3472)
- jp2launcher.exe (PID: 3016)
- jp2launcher.exe (PID: 3920)
- jp2launcher.exe (PID: 2856)
- javaw.exe (PID: 2692)
Reads the Internet Settings
- jp2launcher.exe (PID: 1992)
- jp2launcher.exe (PID: 3980)
- jp2launcher.exe (PID: 1124)
- jp2launcher.exe (PID: 3016)
- jp2launcher.exe (PID: 3920)
- jp2launcher.exe (PID: 2856)
Reads security settings of Internet Explorer
- jp2launcher.exe (PID: 1992)
- jp2launcher.exe (PID: 3980)
- jp2launcher.exe (PID: 1124)
- jp2launcher.exe (PID: 3016)
- jp2launcher.exe (PID: 2856)
- jp2launcher.exe (PID: 3920)
Reads settings of System Certificates
- jp2launcher.exe (PID: 1992)
- jp2launcher.exe (PID: 3980)
- jp2launcher.exe (PID: 1124)
- jp2launcher.exe (PID: 3016)
- jp2launcher.exe (PID: 3920)
- jp2launcher.exe (PID: 2856)
INFO
Checks supported languages
- javaws.exe (PID: 3956)
- javaws.exe (PID: 3776)
- javaw.exe (PID: 2168)
- javaw.exe (PID: 2692)
- jp2launcher.exe (PID: 1992)
- jp2launcher.exe (PID: 3980)
- javaws.exe (PID: 1628)
- javaws.exe (PID: 3232)
- jp2launcher.exe (PID: 1124)
- javaws.exe (PID: 3472)
- javaws.exe (PID: 3248)
- jp2launcher.exe (PID: 3016)
- jp2launcher.exe (PID: 3920)
- jp2launcher.exe (PID: 2856)
- javaw.exe (PID: 1824)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2472)
Reads the computer name
- javaw.exe (PID: 1824)
- javaw.exe (PID: 2168)
- jp2launcher.exe (PID: 1992)
- jp2launcher.exe (PID: 3980)
- jp2launcher.exe (PID: 1124)
- jp2launcher.exe (PID: 3016)
- jp2launcher.exe (PID: 3920)
- jp2launcher.exe (PID: 2856)
- javaw.exe (PID: 2692)
Create files in a temporary directory
- javaw.exe (PID: 2168)
- javaw.exe (PID: 2692)
- jp2launcher.exe (PID: 1992)
- jp2launcher.exe (PID: 3980)
- jp2launcher.exe (PID: 1124)
- jp2launcher.exe (PID: 3920)
- jp2launcher.exe (PID: 3016)
- jp2launcher.exe (PID: 2856)
- javaw.exe (PID: 1824)
Application launched itself
- iexplore.exe (PID: 2472)
The process uses the downloaded file
- iexplore.exe (PID: 2472)
Creates files or folders in the user directory
- jp2launcher.exe (PID: 1992)
- jp2launcher.exe (PID: 3980)
- jp2launcher.exe (PID: 3016)
- jp2launcher.exe (PID: 2856)
Reads the machine GUID from the registry
- jp2launcher.exe (PID: 1992)
- jp2launcher.exe (PID: 3980)
- jp2launcher.exe (PID: 1124)
- jp2launcher.exe (PID: 3016)
- jp2launcher.exe (PID: 3920)
- jp2launcher.exe (PID: 2856)
Checks proxy server information
- jp2launcher.exe (PID: 1992)
- jp2launcher.exe (PID: 3980)
- jp2launcher.exe (PID: 1124)
- jp2launcher.exe (PID: 3920)
- jp2launcher.exe (PID: 3016)
- jp2launcher.exe (PID: 2856)
Manual execution by a user
- javaws.exe (PID: 1628)
- javaws.exe (PID: 3472)
Creates files in the program directory
- javaw.exe (PID: 2692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
63
Monitored processes
18
Malicious processes
10
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1124 | "C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe" -secure -javaws -jre "C:\Program Files\Java\jre1.8.0_271" -vma LWNsYXNzcGF0aABDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMjcxXGxpYlxkZXBsb3kuamFyAC1EamF2YS5zZWN1cml0eS5wb2xpY3k9ZmlsZTpDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMjcxXGxpYlxzZWN1cml0eVxqYXZhd3MucG9saWN5AC1EdHJ1c3RQcm94eT10cnVlAC1YdmVyaWZ5OnJlbW90ZQAtRGpubHB4LmhvbWU9QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzI3MVxiaW4ALURqYXZhLnNlY3VyaXR5Lm1hbmFnZXIALURqbmxweC5vcmlnRmlsZW5hbWVBcmc9QzpcVXNlcnNcYWRtaW5cQXBwRGF0YVxMb2NhbExvd1xTdW5cSmF2YVxEZXBsb3ltZW50XGNhY2hlXDYuMFwzNlw0ZDAyNDU2NC0zYjVjMjJiYwAtRGpubHB4LnJlbW92ZT1mYWxzZQAtRHN1bi5hd3Qud2FybXVwPXRydWUALVhib290Y2xhc3NwYXRoL2E6QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzI3MVxsaWJcamF2YXdzLmphcjtDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMjcxXGxpYlxkZXBsb3kuamFyO0M6XFByb2dyYW0gRmlsZXNcSmF2YVxqcmUxLjguMF8yNzFcbGliXHBsdWdpbi5qYXIALVhYOk1heFBlcm1TaXplPTUwbQAtRGF3dC51c2VTeXN0ZW1BQUZvbnRTZXR0aW5ncz1nYXNwAC12ZXJib3NlOmdjAC1YWDorUHJpbnRHQ0RldGFpbHMALVhYOitQcmludEdDVGltZVN0YW1wcwAtWFg6K1ByaW50VGVudXJpbmdEaXN0cmlidXRpb24ALVhYOitIZWFwRHVtcE9uT3V0T2ZNZW1vcnlFcnJvcgAtWG1zMzJtAC1YbXgyNTZtAC1Eam5scHguaGVhcHNpemU9MzJtLDI1Nm0ALURqbmxweC5zcGxhc2hwb3J0PTQ5MjMwAC1Eam5scC5hcHBsaWNhdGlvbi5ocmVmPWh0dHBzOi8vdGV4LjM2MHQuY29tL2dldGRvd24vam5scC90ZXgvYnJpZGdlLWxvZ2luLmpubHAALURqbmxweC5qdm09QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzI3MVxiaW5camF2YXcuZXhlAC1Eam5scHgudm1hcmdzPUxWaFlPazFoZUZCbGNtMVRhWHBsUFRVd2JRQXRSR0YzZEM1MWMyVlRlWE4wWlcxQlFVWnZiblJUWlhSMGFXNW5jejFuWVhOd0FDMTJaWEppYjNObE9tZGpBQzFZV0RvclVISnBiblJIUTBSbGRHRnBiSE1BTFZoWU9pdFFjbWx1ZEVkRFZHbHRaVk4wWVcxd2N3QXRXRmc2SzFCeWFXNTBWR1Z1ZFhKcGJtZEVhWE4wY21saWRYUnBiMjRBTFZoWU9pdElaV0Z3UkhWdGNFOXVUM1YwVDJaTlpXMXZjbmxGY25KdmNnQXRSR3B1YkhBdVlYQndiR2xqWVhScGIyNHVhSEpsWmoxb2RIUndjem92TDNSbGVDNHpOakIwTG1OdmJTOW5aWFJrYjNkdUwycHViSEF2ZEdWNEwySnlhV1JuWlMxc2IyZHBiaTVxYm14d0FBPT0= -ma LW5vdFdlYkphdmEAQzpcVXNlcnNcYWRtaW5cQXBwRGF0YVxMb2NhbExvd1xTdW5cSmF2YVxEZXBsb3ltZW50XGNhY2hlXDYuMFwzNlw0ZDAyNDU2NC0zYjVjMjJiYw== | C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe | javaws.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Web Launcher Exit code: 0 Version: 11.271.2.09 Modules
| |||||||||||||||
| 1628 | "C:\Program Files\Java\jre1.8.0_271\bin\javaws.exe" -localfile -J-Djnlp.application.href=https://tex.360t.com/getdown/jnlp/tex/bridge-login.jnlp "C:\Users\admin\AppData\LocalLow\Sun\Java\Deployment\cache\6.0\36\4d024564-3b5c22bc" | C:\Program Files\Java\jre1.8.0_271\bin\javaws.exe | — | explorer.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Web Start Launcher Exit code: 0 Version: 11.271.2.09 Modules
| |||||||||||||||
| 1824 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_2\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.timestamp.11.271.2" "1707940183" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | javaws.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 1992 | "C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe" -secure -javaws -jre "C:\Program Files\Java\jre1.8.0_271" -vma LWNsYXNzcGF0aABDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMjcxXGxpYlxkZXBsb3kuamFyAC1EamF2YS5zZWN1cml0eS5wb2xpY3k9ZmlsZTpDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMjcxXGxpYlxzZWN1cml0eVxqYXZhd3MucG9saWN5AC1EdHJ1c3RQcm94eT10cnVlAC1YdmVyaWZ5OnJlbW90ZQAtRGpubHB4LmhvbWU9QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzI3MVxiaW4ALURqYXZhLnNlY3VyaXR5Lm1hbmFnZXIALURqbmxweC5vcmlnRmlsZW5hbWVBcmc9QzpcVXNlcnNcYWRtaW5cQXBwRGF0YVxMb2NhbFxNaWNyb3NvZnRcV2luZG93c1xUZW1wb3JhcnkgSW50ZXJuZXQgRmlsZXNcQ29udGVudC5JRTVcQjZRR1g3TFBcYnJpZGdlLXRleC5qbmxwAC1Eam5scHgucmVtb3ZlPXRydWUALURzdW4uYXd0Lndhcm11cD10cnVlAC1YYm9vdGNsYXNzcGF0aC9hOkM6XFByb2dyYW0gRmlsZXNcSmF2YVxqcmUxLjguMF8yNzFcbGliXGphdmF3cy5qYXI7QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzI3MVxsaWJcZGVwbG95LmphcjtDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMjcxXGxpYlxwbHVnaW4uamFyAC1YWDpNYXhQZXJtU2l6ZT01MG0ALURhd3QudXNlU3lzdGVtQUFGb250U2V0dGluZ3M9Z2FzcAAtdmVyYm9zZTpnYwAtWFg6K1ByaW50R0NEZXRhaWxzAC1YWDorUHJpbnRHQ1RpbWVTdGFtcHMALVhYOitQcmludFRlbnVyaW5nRGlzdHJpYnV0aW9uAC1YWDorSGVhcER1bXBPbk91dE9mTWVtb3J5RXJyb3IALVhtczMybQAtWG14MjU2bQAtRGpubHB4LmhlYXBzaXplPTMybSwyNTZtAC1Eam5scHguc3BsYXNocG9ydD00OTIxNQAtRGpubHB4Lmp2bT1DOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMjcxXGJpblxqYXZhdy5leGUALURqbmxweC52bWFyZ3M9TFZoWU9rMWhlRkJsY20xVGFYcGxQVFV3YlFBdFJHRjNkQzUxYzJWVGVYTjBaVzFCUVVadmJuUlRaWFIwYVc1bmN6MW5ZWE53QUMxMlpYSmliM05sT21kakFDMVlXRG9yVUhKcGJuUkhRMFJsZEdGcGJITUFMVmhZT2l0UWNtbHVkRWREVkdsdFpWTjBZVzF3Y3dBdFdGZzZLMUJ5YVc1MFZHVnVkWEpwYm1kRWFYTjBjbWxpZFhScGIyNEFMVmhZT2l0SVpXRndSSFZ0Y0U5dVQzVjBUMlpOWlcxdmNubEZjbkp2Y2dBPQ== -ma QzpcVXNlcnNcYWRtaW5cQXBwRGF0YVxMb2NhbFxNaWNyb3NvZnRcV2luZG93c1xUZW1wb3JhcnkgSW50ZXJuZXQgRmlsZXNcQ29udGVudC5JRTVcQjZRR1g3TFBcYnJpZGdlLXRleC5qbmxw | C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe | javaws.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Web Launcher Exit code: 0 Version: 11.271.2.09 Modules
| |||||||||||||||
| 2168 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_2\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.suppression.11.271.2" "false" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | javaws.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 2408 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\System32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2472 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://tex.360t.com/bridge-tex.jnlp" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2692 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_2\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.11.271.2" "later" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | javaws.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 2856 | "C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe" -secure -javaws -jre "C:\Program Files\Java\jre1.8.0_271" -vma LVhYOk1heFBlcm1TaXplPTUwbQAtWFg6K1ByaW50R0NEZXRhaWxzAC1YWDorUHJpbnRHQ1RpbWVTdGFtcHMALVhYOitQcmludFRlbnVyaW5nRGlzdHJpYnV0aW9uAC1YWDorSGVhcER1bXBPbk91dE9mTWVtb3J5RXJyb3IALURhd3QudXNlU3lzdGVtQUFGb250U2V0dGluZ3M9Z2FzcAAtRGpubHAuYXBwbGljYXRpb24uaHJlZj1odHRwczovL3RleC4zNjB0LmNvbS9nZXRkb3duL2pubHAvdGV4L2JyaWRnZS1sb2dpbi5qbmxwAC12ZXJib3NlOmdjAC1YbXgyNTZtAC1YbXMzMm0ALURqYXZheC5uZXQuZGVidWc9YWxsAC1YYm9vdGNsYXNzcGF0aC9hOkM6XFByb2dyYW0gRmlsZXNcSmF2YVxqcmUxLjguMF8yNzFcbGliXGphdmF3cy5qYXI7QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzI3MVxsaWJcZGVwbG95LmphcjtDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMjcxXGxpYlxwbHVnaW4uamFyAC1Eam5scC50az1hd3QALWNsYXNzcGF0aABDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMjcxXGxpYlxkZXBsb3kuamFyAC1Eam5scHgudm1hcmdzPUxWaFlPazFoZUZCbGNtMVRhWHBsUFRVd2JRQXRXRmc2SzFCeWFXNTBSME5FWlhSaGFXeHpBQzFZV0RvclVISnBiblJIUTFScGJXVlRkR0Z0Y0hNQUxWaFlPaXRRY21sdWRGUmxiblZ5YVc1blJHbHpkSEpwWW5WMGFXOXVBQzFZV0RvclNHVmhjRVIxYlhCUGJrOTFkRTltVFdWdGIzSjVSWEp5YjNJQUxVUmhkM1F1ZFhObFUzbHpkR1Z0UVVGR2IyNTBVMlYwZEdsdVozTTlaMkZ6Y0FBdFJHcHViSEF1WVhCd2JHbGpZWFJwYjI0dWFISmxaajFvZEhSd2N6b3ZMM1JsZUM0ek5qQjBMbU52YlM5blpYUmtiM2R1TDJwdWJIQXZkR1Y0TDJKeWFXUm5aUzFzYjJkcGJpNXFibXh3QUMxMlpYSmliM05sT21kakFDMVliWGd5TlRadEFDMVliWE16TW0wQUxVUnFZWFpoZUM1dVpYUXVaR1ZpZFdjOVlXeHNBQT09AC1Eam5scHguanZtPUM6XFByb2dyYW0gRmlsZXNcSmF2YVxqcmUxLjguMF8yNzFcYmluXGphdmF3LmV4ZQAtRGpubHB4LnNwbGFzaHBvcnQ9NDkyMzgALURqbmxweC5ob21lPUM6XFByb2dyYW0gRmlsZXNcSmF2YVxqcmUxLjguMF8yNzFcYmluAC1Eam5scHgucmVtb3ZlPWZhbHNlAC1Eam5scHgub2ZmbGluZT1mYWxzZQAtRGpubHB4LnJlbGF1bmNoPXRydWUALURqbmxweC5zZXNzaW9uLmRhdGE9QzpcVXNlcnNcYWRtaW5cQXBwRGF0YVxMb2NhbFxUZW1wXHNlc3Npb240MzkxMjY0Njg4Mzg2NjUxMjcwAC1Eam5scHguaGVhcHNpemU9MzM1NTQ0MzIsMjY4NDM1NDU2AC1EamF2YS5zZWN1cml0eS5wb2xpY3k9ZmlsZTpDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMjcxXGxpYlxzZWN1cml0eVxqYXZhd3MucG9saWN5AC1EdHJ1c3RQcm94eT10cnVlAC1YdmVyaWZ5OnJlbW90ZQAtRGpubHB4Lm9yaWdGaWxlbmFtZUFyZz1DOlxVc2Vyc1xhZG1pblxBcHBEYXRhXExvY2FsTG93XFN1blxKYXZhXERlcGxveW1lbnRcY2FjaGVcNi4wXDM2XDRkMDI0NTY0LTNiNWMyMmJjAC1Ec3VuLmF3dC53YXJtdXA9dHJ1ZQAtRGphdmEuc2VjdXJpdHkubWFuYWdlcgA= -ma LXNlY3VyZQAtbm90V2ViSmF2YQBDOlxVc2Vyc1xhZG1pblxBcHBEYXRhXExvY2FsTG93XFN1blxKYXZhXERlcGxveW1lbnRcY2FjaGVcNi4wXDM2XDRkMDI0NTY0LTNiNWMyMmJjAA== -ta LURqYXZheC5uZXQuZGVidWc9YWxsAA== -checkParent | C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe | jp2launcher.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Web Launcher Exit code: 0 Version: 11.271.2.09 Modules
| |||||||||||||||
| 3016 | "C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe" -secure -javaws -jre "C:\Program Files\Java\jre1.8.0_271" -vma LWNsYXNzcGF0aABDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMjcxXGxpYlxkZXBsb3kuamFyAC1EamF2YS5zZWN1cml0eS5wb2xpY3k9ZmlsZTpDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMjcxXGxpYlxzZWN1cml0eVxqYXZhd3MucG9saWN5AC1EdHJ1c3RQcm94eT10cnVlAC1YdmVyaWZ5OnJlbW90ZQAtRGpubHB4LmhvbWU9QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzI3MVxiaW4ALURqYXZhLnNlY3VyaXR5Lm1hbmFnZXIALURqbmxweC5vcmlnRmlsZW5hbWVBcmc9QzpcVXNlcnNcYWRtaW5cQXBwRGF0YVxMb2NhbExvd1xTdW5cSmF2YVxEZXBsb3ltZW50XGNhY2hlXDYuMFwzNlw0ZDAyNDU2NC0zYjVjMjJiYwAtRGpubHB4LnJlbW92ZT1mYWxzZQAtRHN1bi5hd3Qud2FybXVwPXRydWUALVhib290Y2xhc3NwYXRoL2E6QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzI3MVxsaWJcamF2YXdzLmphcjtDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMjcxXGxpYlxkZXBsb3kuamFyO0M6XFByb2dyYW0gRmlsZXNcSmF2YVxqcmUxLjguMF8yNzFcbGliXHBsdWdpbi5qYXIALVhYOk1heFBlcm1TaXplPTUwbQAtRGF3dC51c2VTeXN0ZW1BQUZvbnRTZXR0aW5ncz1nYXNwAC12ZXJib3NlOmdjAC1YWDorUHJpbnRHQ0RldGFpbHMALVhYOitQcmludEdDVGltZVN0YW1wcwAtWFg6K1ByaW50VGVudXJpbmdEaXN0cmlidXRpb24ALVhYOitIZWFwRHVtcE9uT3V0T2ZNZW1vcnlFcnJvcgAtWG1zMzJtAC1YbXgyNTZtAC1Eam5scHguaGVhcHNpemU9MzJtLDI1Nm0ALURqbmxweC5zcGxhc2hwb3J0PTQ5MjM4AC1Eam5scC5hcHBsaWNhdGlvbi5ocmVmPWh0dHBzOi8vdGV4LjM2MHQuY29tL2dldGRvd24vam5scC90ZXgvYnJpZGdlLWxvZ2luLmpubHAALURqbmxweC5qdm09QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzI3MVxiaW5camF2YXcuZXhlAC1Eam5scHgudm1hcmdzPUxWaFlPazFoZUZCbGNtMVRhWHBsUFRVd2JRQXRSR0YzZEM1MWMyVlRlWE4wWlcxQlFVWnZiblJUWlhSMGFXNW5jejFuWVhOd0FDMTJaWEppYjNObE9tZGpBQzFZV0RvclVISnBiblJIUTBSbGRHRnBiSE1BTFZoWU9pdFFjbWx1ZEVkRFZHbHRaVk4wWVcxd2N3QXRXRmc2SzFCeWFXNTBWR1Z1ZFhKcGJtZEVhWE4wY21saWRYUnBiMjRBTFZoWU9pdElaV0Z3UkhWdGNFOXVUM1YwVDJaTlpXMXZjbmxGY25KdmNnQXRSR3B1YkhBdVlYQndiR2xqWVhScGIyNHVhSEpsWmoxb2RIUndjem92TDNSbGVDNHpOakIwTG1OdmJTOW5aWFJrYjNkdUwycHViSEF2ZEdWNEwySnlhV1JuWlMxc2IyZHBiaTVxYm14d0FBPT0= -ma LW5vdFdlYkphdmEAQzpcVXNlcnNcYWRtaW5cQXBwRGF0YVxMb2NhbExvd1xTdW5cSmF2YVxEZXBsb3ltZW50XGNhY2hlXDYuMFwzNlw0ZDAyNDU2NC0zYjVjMjJiYw== | C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe | javaws.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Web Launcher Exit code: 0 Version: 11.271.2.09 Modules
| |||||||||||||||
Total events
44 128
Read events
43 650
Write events
401
Delete events
77
Modification events
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31088510 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31088510 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
10
Suspicious files
60
Text files
85
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_BACC6CD2B29F18349081C9FD2343833B | der | |
MD5:BD36DC5D5E18B9D3678632AF95B04DA3 | SHA256:75913D8ED495A6B1CA581FCA196D33C944C02F29524F9E165DC1706F591CD0B1 | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:0412B31E1BF613BC1CD862FBC8A80EE6 | SHA256:F5C23E602447D92258AEB105FD7376E1AA199AEE951C807D4CB6D345477AFB21 | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\72BA427A91F50409B9EAC87F2B59B951_0CB3F1BA2BBFB73B354A8A65136DC06F | der | |
MD5:A12331C631CE4AD783EB195DABAC3C56 | SHA256:484B93BF565EF8E50E81115EC4EC8352CD75FB594C6F78C9CB762F0283970D13 | |||
| 2472 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB5E3C78AC6A30FAE.TMP | gmc | |
MD5:7AC6EFA096AC2E32F81136497B27100A | SHA256:E748AE5080FC52BA2424D2712FA1555E66EB94485D7D7B5FD9AB32BAD0DC5089 | |||
| 2692 | javaw.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:66C507E4C2DFF2EAF52F3706939F6B03 | SHA256:1984530501018F7332918ACF5C0DE66628AE7CEED70B92D25ECABB64901E29D0 | |||
| 2472 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\bridge-tex.jnlp.wyk8fgq.partial:Zone.Identifier | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
| 2472 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\bridge-tex.jnlp | xml | |
MD5:7478D6387423DE595E660843D025553A | SHA256:41FDD03BA595977BC88561D0E39B5C7B8A1A110E1275AF2C076AA6C6C2A8437F | |||
| 2692 | javaw.exe | C:\Users\admin\AppData\Local\Temp\JavaDeployReg.log | text | |
MD5:B25C4AD905561851B9C98D3882B1A74F | SHA256:71EA7DEB24A0561B21916B664A714DA481EF452E1FFA0250DF5FEB2CF84F6584 | |||
| 2692 | javaw.exe | C:\Users\admin\AppData\LocalLow\Sun\Java\Deployment\deployment.properties | text | |
MD5:CF3A93B9F260D6D14FC0BC03C6735E56 | SHA256:6AC5FDF5AA902F1F7933CBA0766EA76F4DD3DE593DCE2A4CC6C4B011183D2AD6 | |||
| 2472 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFCB1D4DC2DBD99E49.TMP | binary | |
MD5:878399A27A00739CB2FA69BC8DEBB08E | SHA256:AC1F5CEAE3A1F6C02DD6C56A78B601DC91A0D4CFA08A529B330BFDE5B30EDC63 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
44
DNS requests
8
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3348 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f78d505714a595e3 | unknown | — | — | unknown |
3348 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?545e1839169dd0e6 | unknown | — | — | unknown |
3348 | iexplore.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | unknown | binary | 1.42 Kb | unknown |
3348 | iexplore.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEBN9U5yqfDGppDNwGWiEeo0%3D | unknown | binary | 2.18 Kb | unknown |
3348 | iexplore.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQh80WaEMqmyEvaHjlisSfVM4p8SAQUF9nWJSdn%2BTHCSUPZMDZEjGypT%2BsCEGxyZNQ6vknxz3AU08zGNVI%3D | unknown | binary | 471 b | unknown |
1992 | jp2launcher.exe | POST | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/ | unknown | binary | 471 b | unknown |
1992 | jp2launcher.exe | POST | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/ | unknown | binary | 1.42 Kb | unknown |
1992 | jp2launcher.exe | POST | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/ | unknown | binary | 765 b | unknown |
1992 | jp2launcher.exe | POST | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/ | unknown | binary | 638 b | unknown |
1080 | svchost.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?1b8fee253118cbef | unknown | compressed | 65.2 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
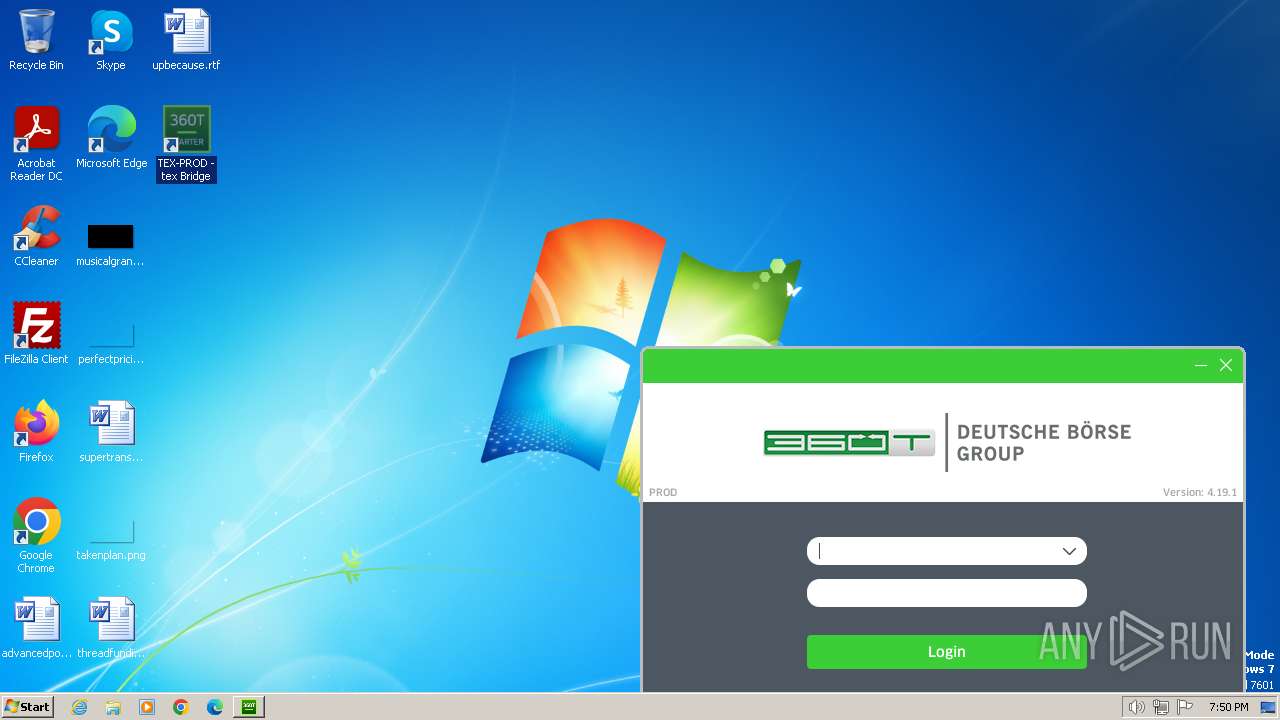
3348 | iexplore.exe | 193.29.38.131:443 | tex.360t.com | 360 Treasury Systems AG | DE | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3348 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3348 | iexplore.exe | 172.64.149.23:80 | ocsp.comodoca.com | CLOUDFLARENET | US | unknown |
3348 | iexplore.exe | 104.18.38.233:80 | ocsp.comodoca.com | CLOUDFLARENET | — | shared |
1992 | jp2launcher.exe | 193.29.38.131:443 | tex.360t.com | 360 Treasury Systems AG | DE | unknown |
1992 | jp2launcher.exe | 172.64.149.23:80 | ocsp.comodoca.com | CLOUDFLARENET | US | unknown |
3980 | jp2launcher.exe | 193.29.38.131:443 | tex.360t.com | 360 Treasury Systems AG | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tex.360t.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
javadl-esd-secure.oracle.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1992 | jp2launcher.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |
1992 | jp2launcher.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |