| File name: | Sigmanly_692526eb7b58ff78d370ee6490c58da54cba0cb6582ede927a19f97b77d0171c |
| Full analysis: | https://app.any.run/tasks/4c7381c3-bdce-4963-9164-348f0d9ace62 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 17:18:07 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 094807D91484422204336DB45F336917 |
| SHA1: | 7FBBA68796DB877C4BD26404FAAE8F4810A6425F |
| SHA256: | 692526EB7B58FF78D370EE6490C58DA54CBA0CB6582EDE927A19F97B77D0171C |
| SSDEEP: | 3072:fkLZyldfaw69Rojk1hwfz6vp1BAi9XF6mTZ99999w9IMC9qwGMV24GDI/dK94lZq:PwmFvKOGbMO |
MALICIOUS
Connects to the CnC server
- Sigmanly_692526eb7b58ff78d370ee6490c58da54cba0cb6582ede927a19f97b77d0171c.exe (PID: 1020)
SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- Sigmanly_692526eb7b58ff78d370ee6490c58da54cba0cb6582ede927a19f97b77d0171c.exe (PID: 1020)
Reads the machine GUID from the registry
- Sigmanly_692526eb7b58ff78d370ee6490c58da54cba0cb6582ede927a19f97b77d0171c.exe (PID: 1020)
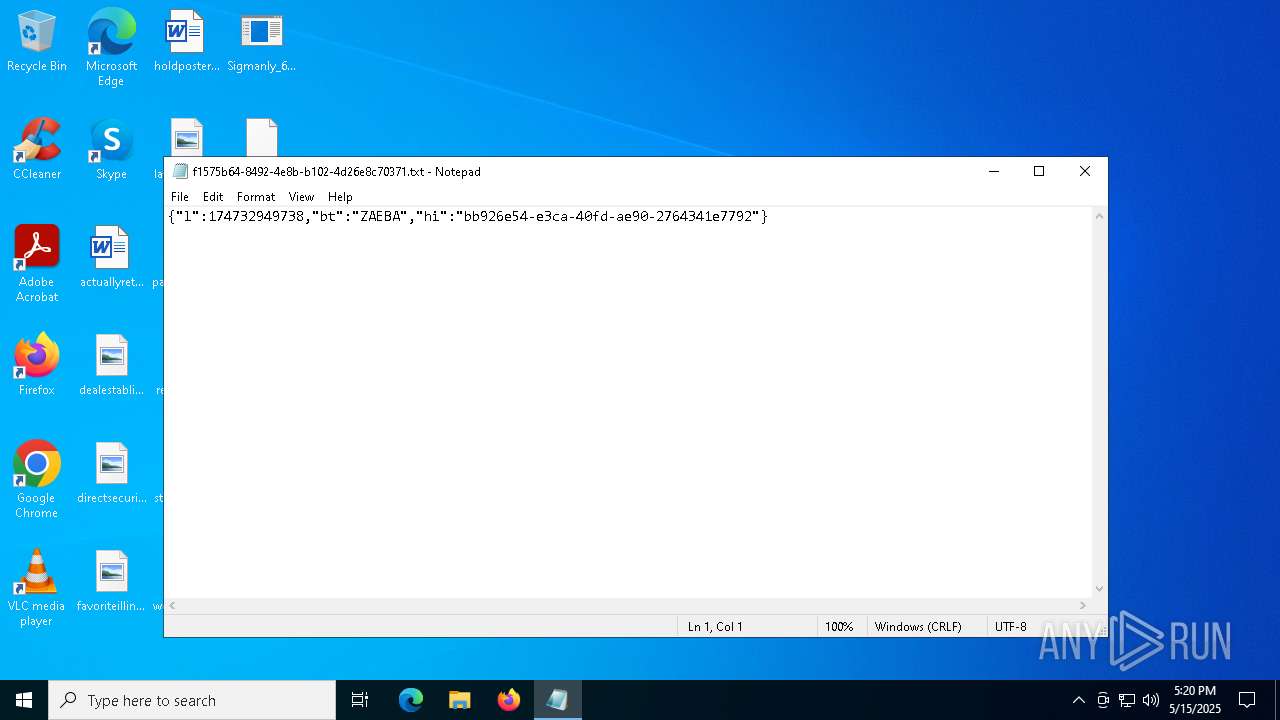
Manual execution by a user
- notepad.exe (PID: 720)
Reads security settings of Internet Explorer
- notepad.exe (PID: 720)
Reads the software policy settings
- slui.exe (PID: 1532)
Checks proxy server information
- slui.exe (PID: 1532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:08:17 08:01:25+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 18.11 |
| CodeSize: | 57344 |
| InitializedDataSize: | 17920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1210 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
123
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 720 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\f1575b64-8492-4e8b-b102-4d26e8c70371.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1020 | "C:\Users\admin\Desktop\Sigmanly_692526eb7b58ff78d370ee6490c58da54cba0cb6582ede927a19f97b77d0171c.exe" | C:\Users\admin\Desktop\Sigmanly_692526eb7b58ff78d370ee6490c58da54cba0cb6582ede927a19f97b77d0171c.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1532 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 517
Read events
3 517
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
41
DNS requests
12
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1020 | Sigmanly_692526eb7b58ff78d370ee6490c58da54cba0cb6582ede927a19f97b77d0171c.exe | GET | 409 | 104.21.80.1:80 | http://overplanteasiest.top/ujs/1ebc820c-f85b-4421-8937-ddd717154b24 | unknown | — | — | malicious |
1020 | Sigmanly_692526eb7b58ff78d370ee6490c58da54cba0cb6582ede927a19f97b77d0171c.exe | POST | 409 | 104.21.80.1:80 | http://overplanteasiest.top/Up | unknown | — | — | unknown |
4688 | SIHClient.exe | GET | 200 | 23.48.23.139:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
4688 | SIHClient.exe | GET | 200 | 23.48.23.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
4688 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4688 | SIHClient.exe | GET | 200 | 23.48.23.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4688 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
4688 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
4688 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
4688 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
1020 | Sigmanly_692526eb7b58ff78d370ee6490c58da54cba0cb6582ede927a19f97b77d0171c.exe | 104.21.80.1:80 | — | CLOUDFLARENET | — | malicious |
4688 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4688 | SIHClient.exe | 23.48.23.139:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4688 | SIHClient.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4688 | SIHClient.exe | 20.3.187.198:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6876 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1020 | Sigmanly_692526eb7b58ff78d370ee6490c58da54cba0cb6582ede927a19f97b77d0171c.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
1020 | Sigmanly_692526eb7b58ff78d370ee6490c58da54cba0cb6582ede927a19f97b77d0171c.exe | A Network Trojan was detected | ET MALWARE ACR Stealer CnC Checkin Attempt |
1020 | Sigmanly_692526eb7b58ff78d370ee6490c58da54cba0cb6582ede927a19f97b77d0171c.exe | Potentially Bad Traffic | ET HUNTING Request to .TOP Domain with Minimal Headers |
1020 | Sigmanly_692526eb7b58ff78d370ee6490c58da54cba0cb6582ede927a19f97b77d0171c.exe | Potentially Bad Traffic | ET HUNTING Request to .TOP Domain with Minimal Headers |