| File name: | 69053e4a5fb9b5634c326a4f5c72770b157907e98e26d59ae1e8554f3df38483.doc |
| Full analysis: | https://app.any.run/tasks/2ee8ccf2-bf2a-452f-802f-9188f8b044c0 |
| Verdict: | Malicious activity |
| Analysis date: | March 12, 2024, 20:29:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
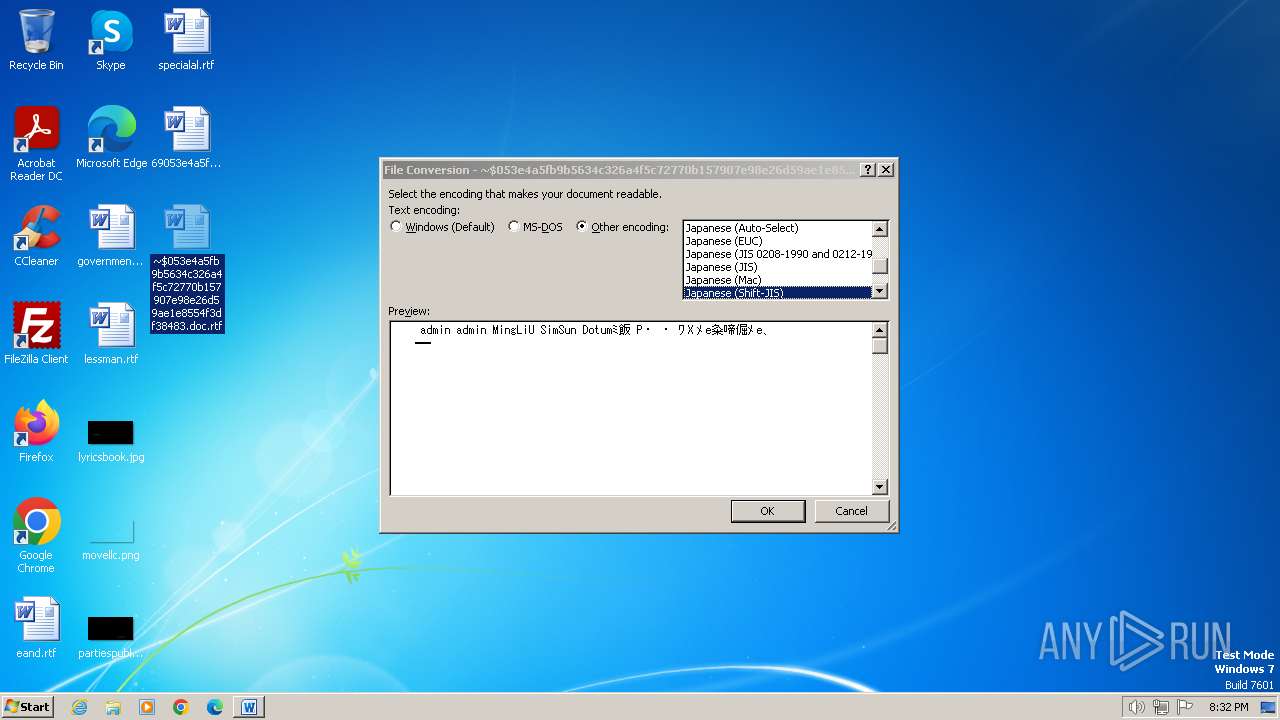
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1 |
| MD5: | 65014753390EA021BC4BE75D38840F5D |
| SHA1: | D78EB7A0A1BF2F810024B7A3AF85DAB6526825C1 |
| SHA256: | 69053E4A5FB9B5634C326A4F5C72770B157907E98E26D59AE1E8554F3DF38483 |
| SSDEEP: | 768:XwARU+obMX9gRWjTwARU+obMX9gRWjTwARU+obMX9gRWjbssDUZiFFt1KHFB70n+:XwAK3ewAK3ewAK3OksFtUHfwgy4r |
MALICIOUS
Equation Editor starts application (likely CVE-2017-11882)
- EQNEDT32.EXE (PID: 3732)
Suspicious connection from the Equation Editor
- EQNEDT32.EXE (PID: 3732)
SUSPICIOUS
Reads settings of System Certificates
- EQNEDT32.EXE (PID: 3732)
Reads security settings of Internet Explorer
- EQNEDT32.EXE (PID: 3732)
Reads the Internet Settings
- EQNEDT32.EXE (PID: 3732)
Checks Windows Trust Settings
- EQNEDT32.EXE (PID: 3732)
Non-standard symbols in registry
- WINWORD.EXE (PID: 3672)
- WINWORD.EXE (PID: 1928)
INFO
Checks supported languages
- EQNEDT32.EXE (PID: 3732)
Checks proxy server information
- EQNEDT32.EXE (PID: 3732)
Reads the computer name
- EQNEDT32.EXE (PID: 3732)
Reads the software policy settings
- EQNEDT32.EXE (PID: 3732)
Reads the machine GUID from the registry
- EQNEDT32.EXE (PID: 3732)
Creates files or folders in the user directory
- EQNEDT32.EXE (PID: 3732)
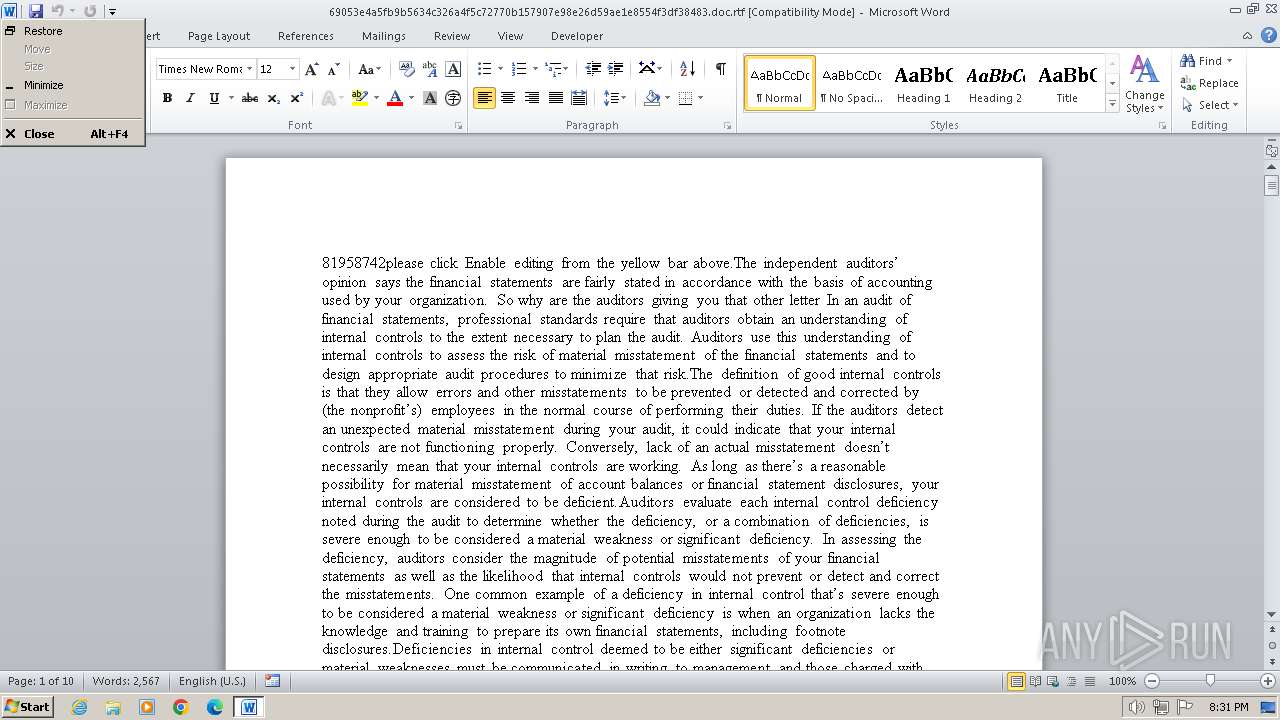
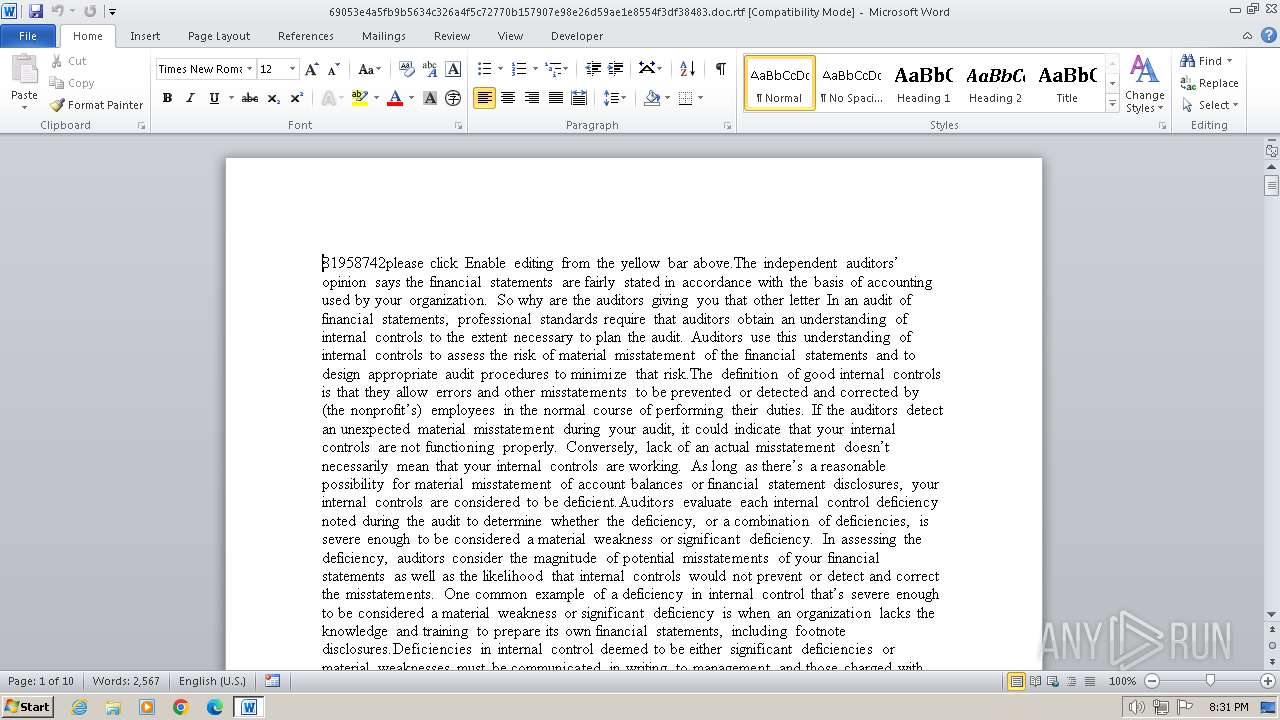
Manual execution by a user
- WINWORD.EXE (PID: 1928)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
Total processes
43
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1928 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\~$053e4a5fb9b5634c326a4f5c72770b157907e98e26d59ae1e8554f3df38483.doc.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3672 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\69053e4a5fb9b5634c326a4f5c72770b157907e98e26d59ae1e8554f3df38483.doc.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3732 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
Total events
12 946
Read events
11 611
Write events
725
Delete events
610
Modification events
| (PID) Process: | (3672) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | e+' |
Value: 652B2700580E0000010000000000000000000000 | |||
| (PID) Process: | (3672) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3672) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3672) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3672) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3672) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3672) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3672) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3672) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3672) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
1
Suspicious files
8
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3672 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRF3E5.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1928 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR437.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3732 | EQNEDT32.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:AB5299EAFDB3B1491E769FC515A905BB | SHA256:2FF22DEF16933F2D4CB6A76F4E8370DD1673A7EA1B29E4C9CF86CC040E16C5FB | |||
| 3672 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:9174E00390946045D9394834ABCADFD9 | SHA256:4CD51D1FC5FDA7835FFBA71A536E22B20476151260FB5DD71D1DF0CD06B557F8 | |||
| 3672 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:280D2B65A6285DCE35099F1721B7999D | SHA256:9C481BFD497634B56792F1F82F7323677D76F0ECD94EC28D527714D4DEF38B52 | |||
| 3732 | EQNEDT32.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:EE28D00FD970B53524B7292D28151AD1 | SHA256:98F0E6239914F7C7612DB770FB7F5233BD7CB3DD72B674569351BB945179267B | |||
| 3672 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\69053e4a5fb9b5634c326a4f5c72770b157907e98e26d59ae1e8554f3df38483.doc.rtf.LNK | binary | |
MD5:89BA7DF5F5295E8ADE1BB6D65C38462F | SHA256:6021D3B5955E684B13EB97428AC40E1B629154F4B04648437DB3043D751C7716 | |||
| 3732 | EQNEDT32.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | der | |
MD5:8202A1CD02E7D69597995CABBE881A12 | SHA256:58F381C3A0A0ACE6321DA22E40BD44A597BD98B9C9390AB9258426B5CF75A7A5 | |||
| 3672 | WINWORD.EXE | C:\Users\admin\Desktop\~$053e4a5fb9b5634c326a4f5c72770b157907e98e26d59ae1e8554f3df38483.doc.rtf | pgc | |
MD5:5FC3AADDC84FEC74EDDFE4F31824DFD5 | SHA256:6F5C16B306BA4CE29F3C93A17B545324900C246D07FAD23E3328C9B95FD47CA5 | |||
| 3672 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\~$053e4a5fb9b5634c326a4f5c72770b157907e98e26d59ae1e8554f3df38483.doc.rtf.LNK | binary | |
MD5:06CB60898C5F5FED6C1CF1EC862E63F2 | SHA256:7620BFCD046EC636C7C23C4B3B709B1978E90D81D7A3E565748EAF990A43B908 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
10
DNS requests
5
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3732 | EQNEDT32.EXE | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | binary | 1.41 Kb | unknown |
3732 | EQNEDT32.EXE | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | US | binary | 724 b | unknown |
1080 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?89bca2e7018c82c0 | DE | compressed | 67.5 Kb | unknown |
1080 | svchost.exe | GET | 304 | 23.48.23.143:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?3e412f7b4eff0943 | DE | compressed | 67.5 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3732 | EQNEDT32.EXE | 104.21.68.43:443 | amassmodel.top | CLOUDFLARENET | — | unknown |
3732 | EQNEDT32.EXE | 23.48.23.34:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3732 | EQNEDT32.EXE | 142.250.186.67:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
1080 | svchost.exe | 23.48.23.169:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1080 | svchost.exe | 23.48.23.143:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
amassmodel.top |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |