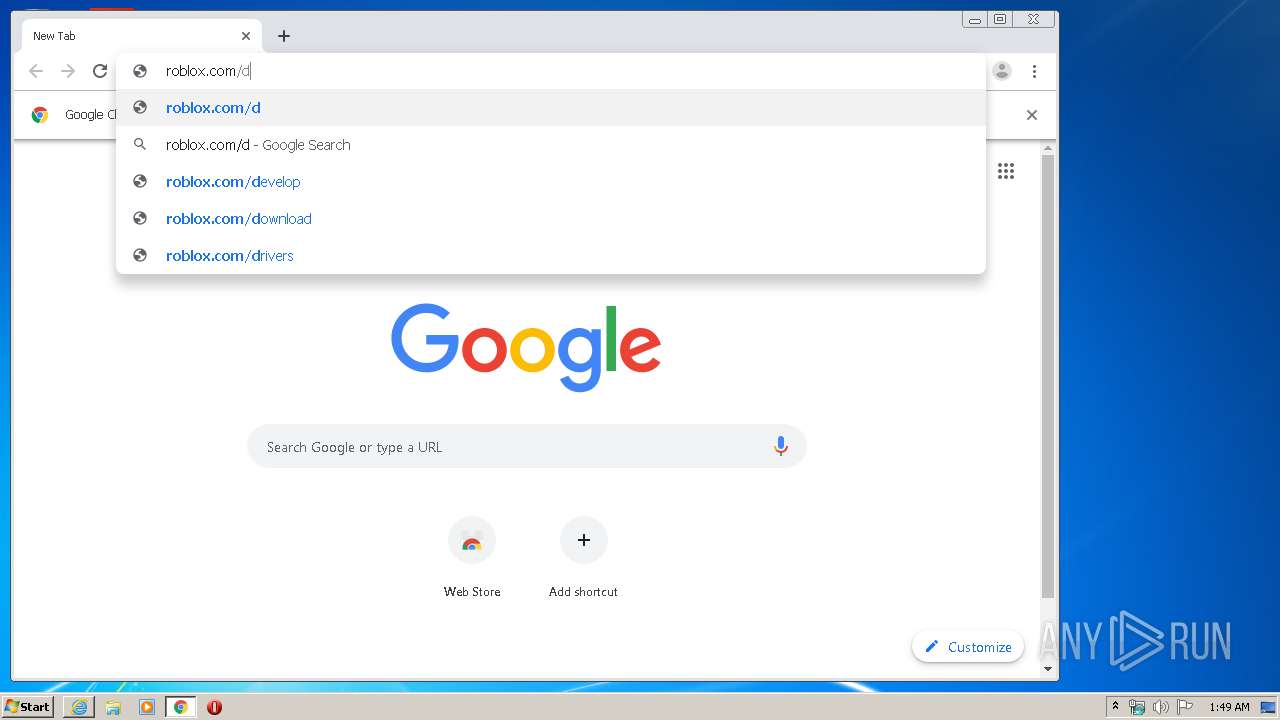
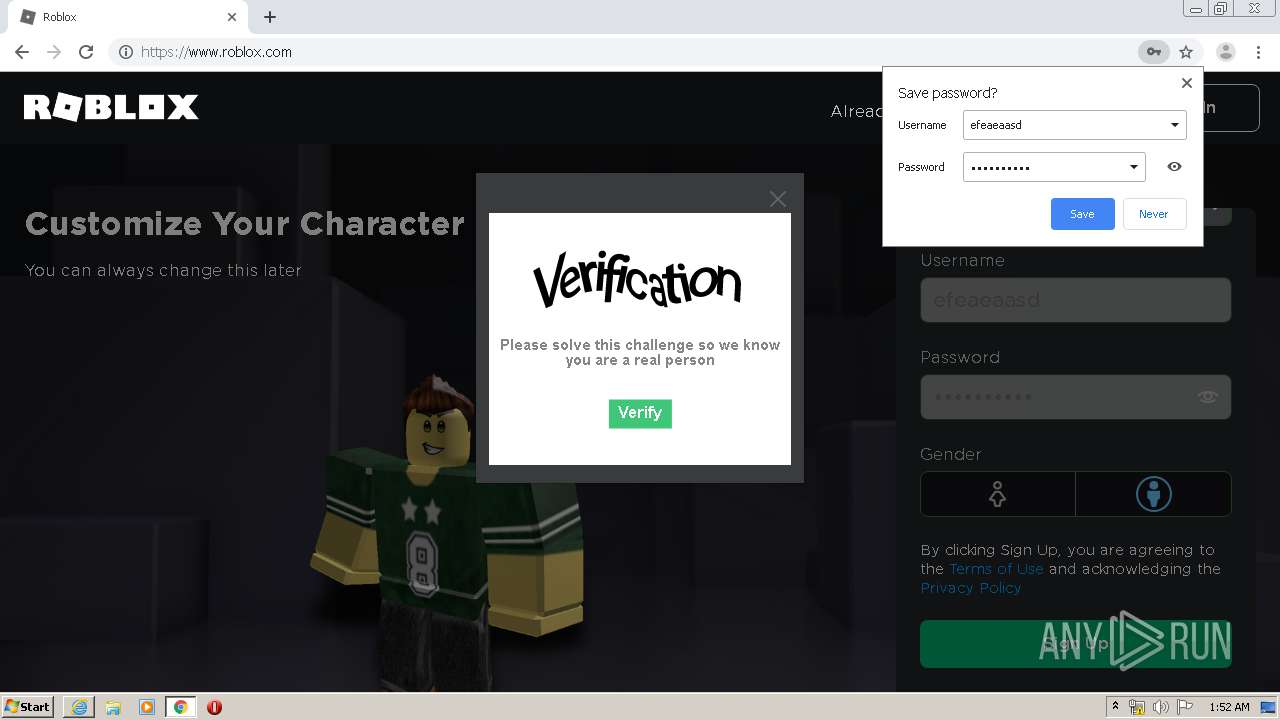
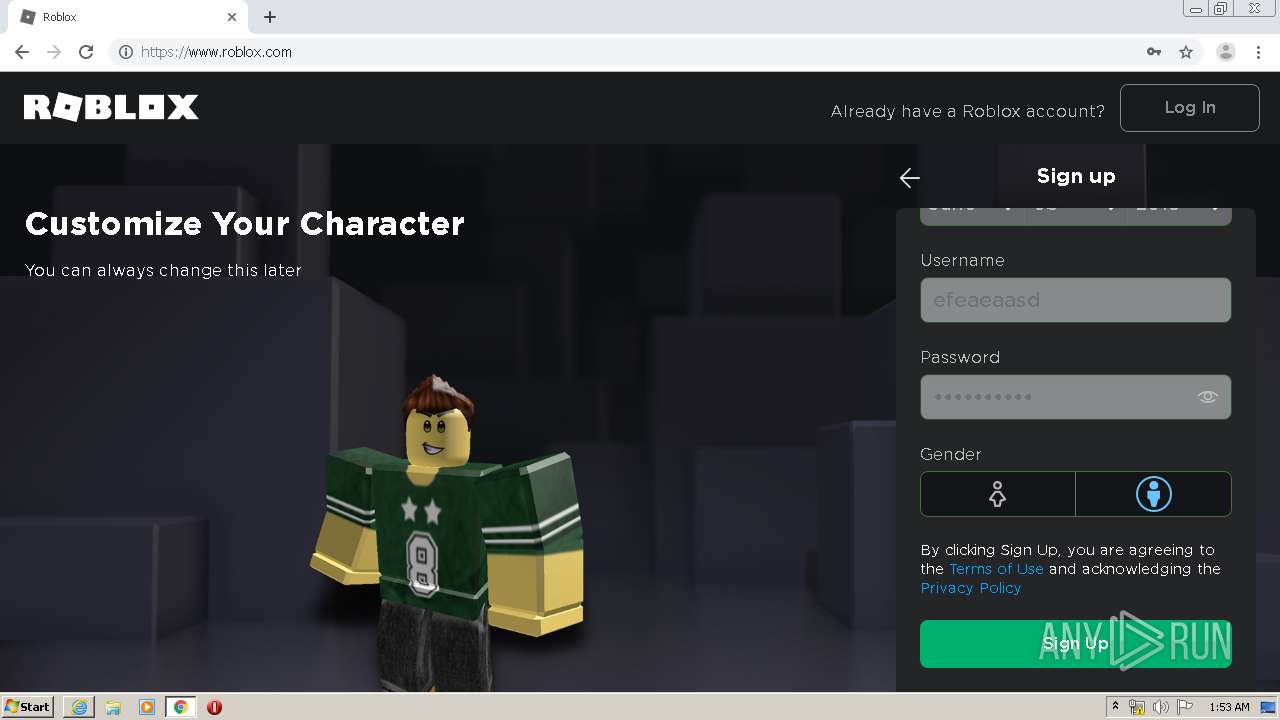
| URL: | https://www.roblox.com/install/setup.ashx |
| Full analysis: | https://app.any.run/tasks/8ecafe5e-e6df-4b02-a72b-eabf0b368c3b |
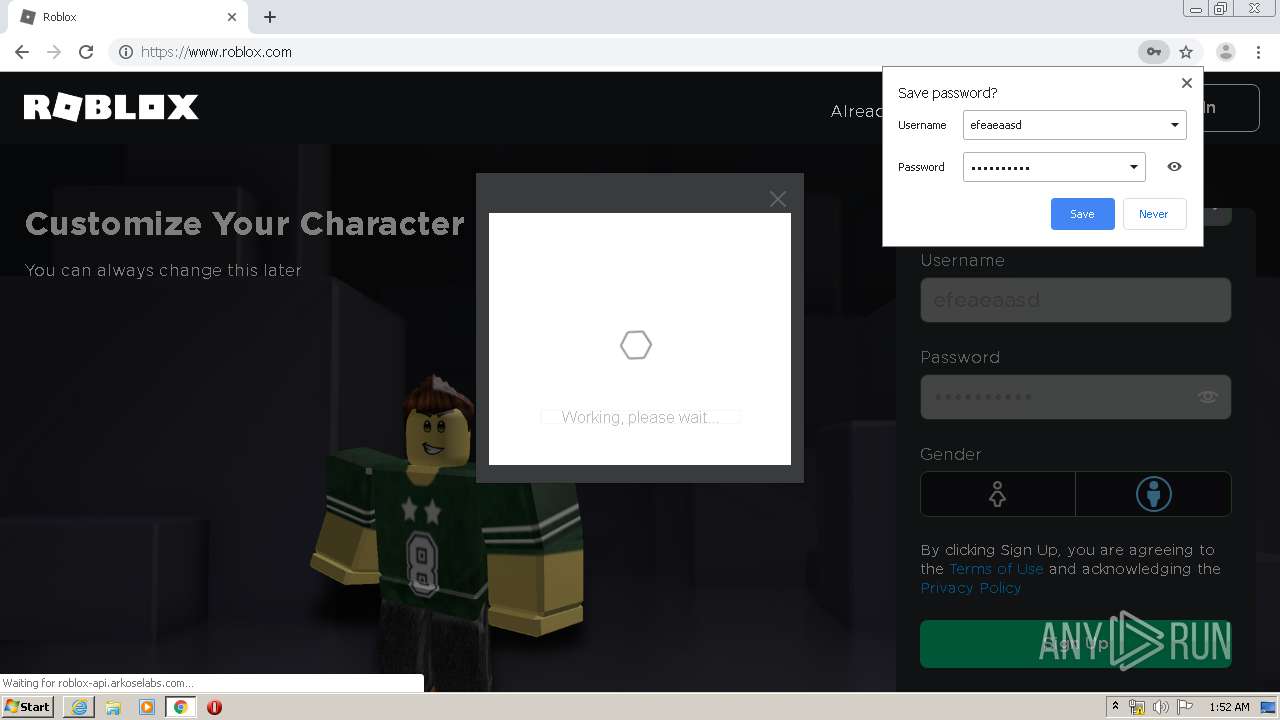
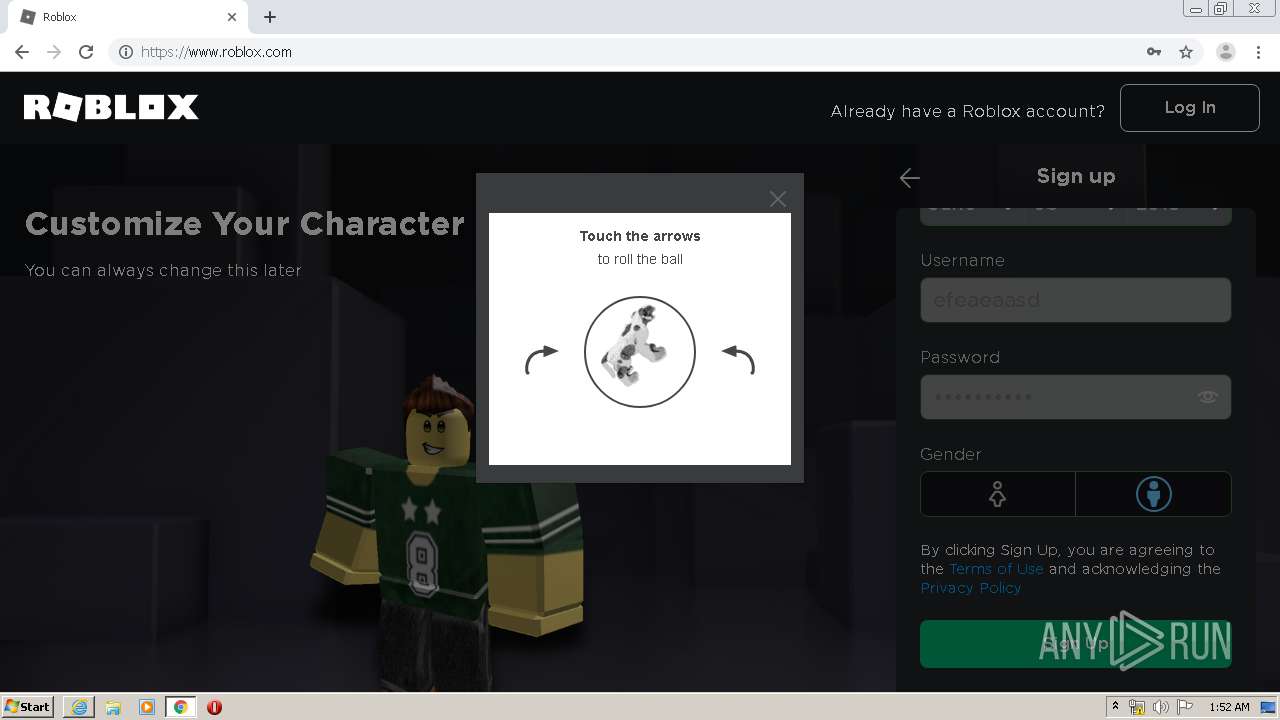
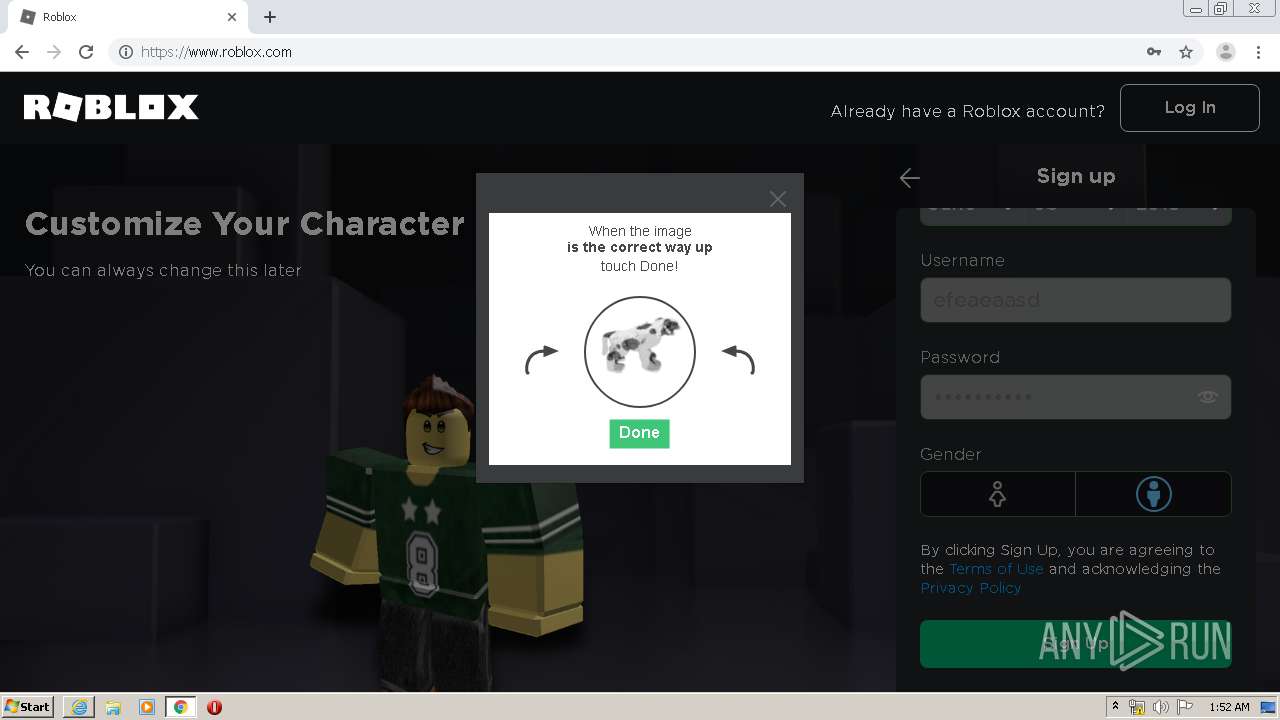
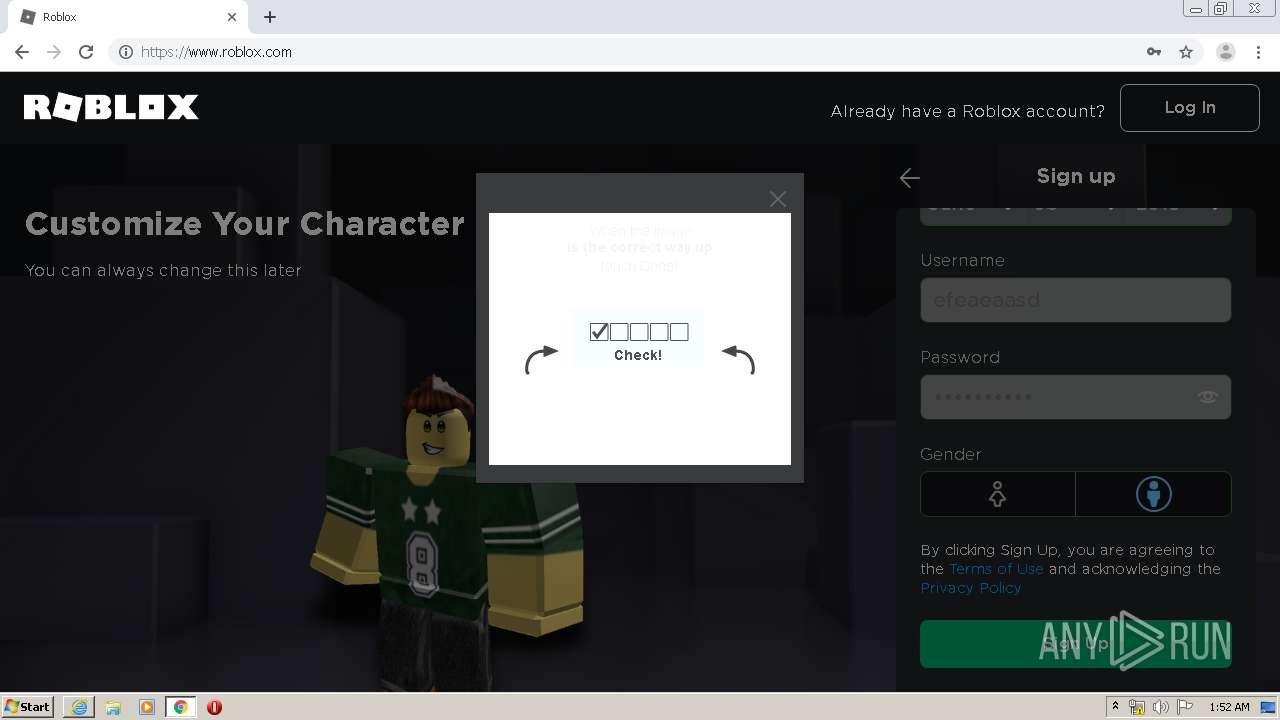
| Verdict: | Malicious activity |
| Analysis date: | April 10, 2020, 00:49:04 |
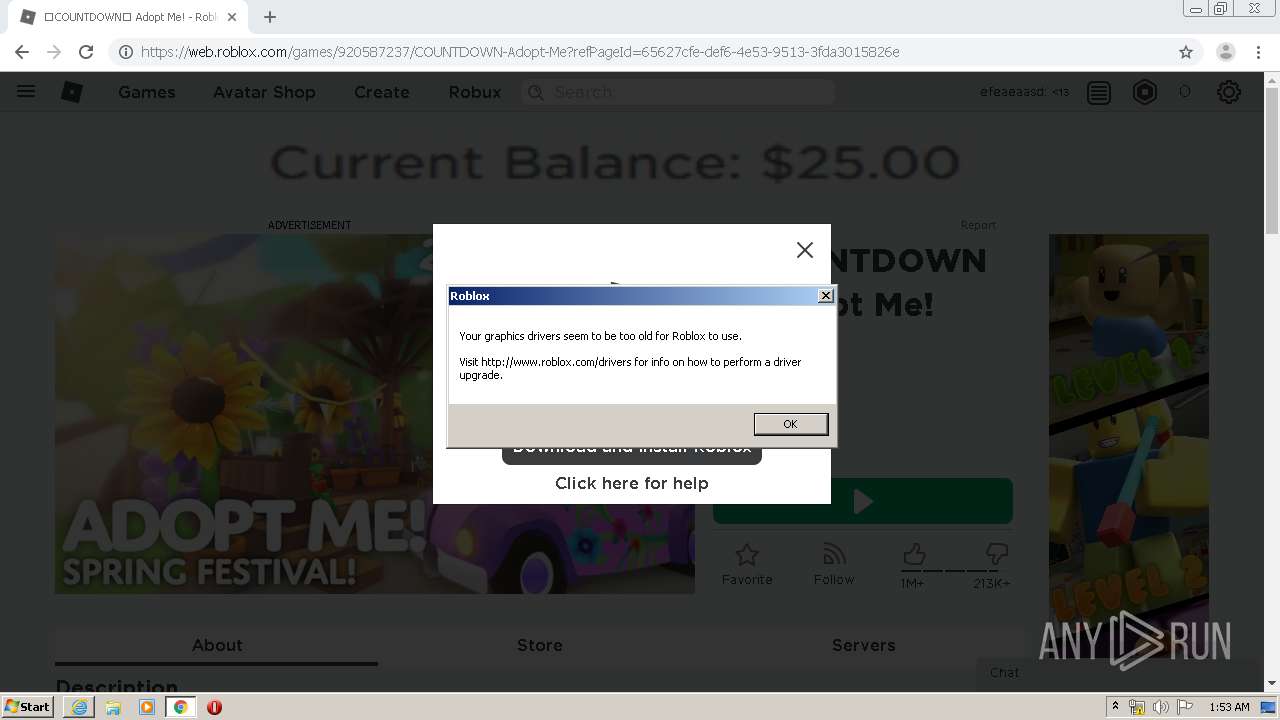
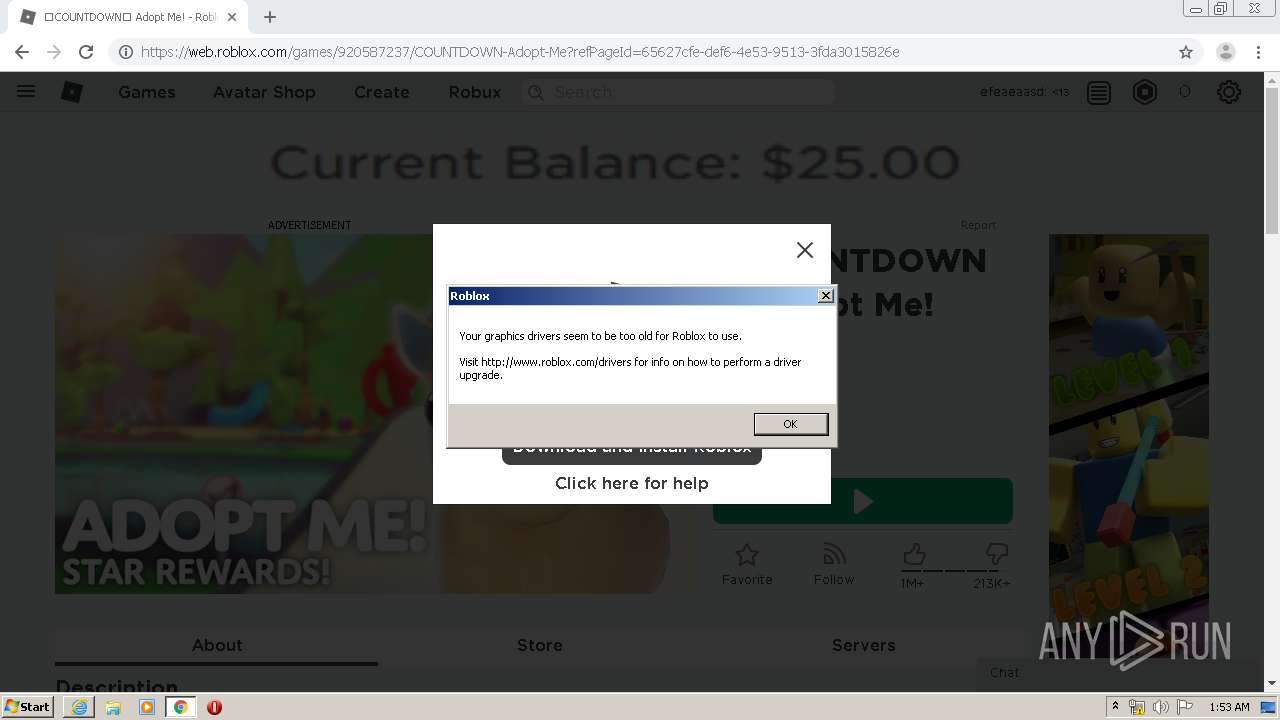
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1FC53B16B32F10FC7BDFC0F91ECF9D74 |
| SHA1: | 1F295BE61D2371443E1ED93F0C1EC462B15FF575 |
| SHA256: | 68DBFE29AF0927F13737B0681C608FDD7779DAD4FF0546EFE331C58D9AAB3D29 |
| SSDEEP: | 3:N8DSLaHE3IXygEWVL/P:2OLatXygESLn |
MALICIOUS
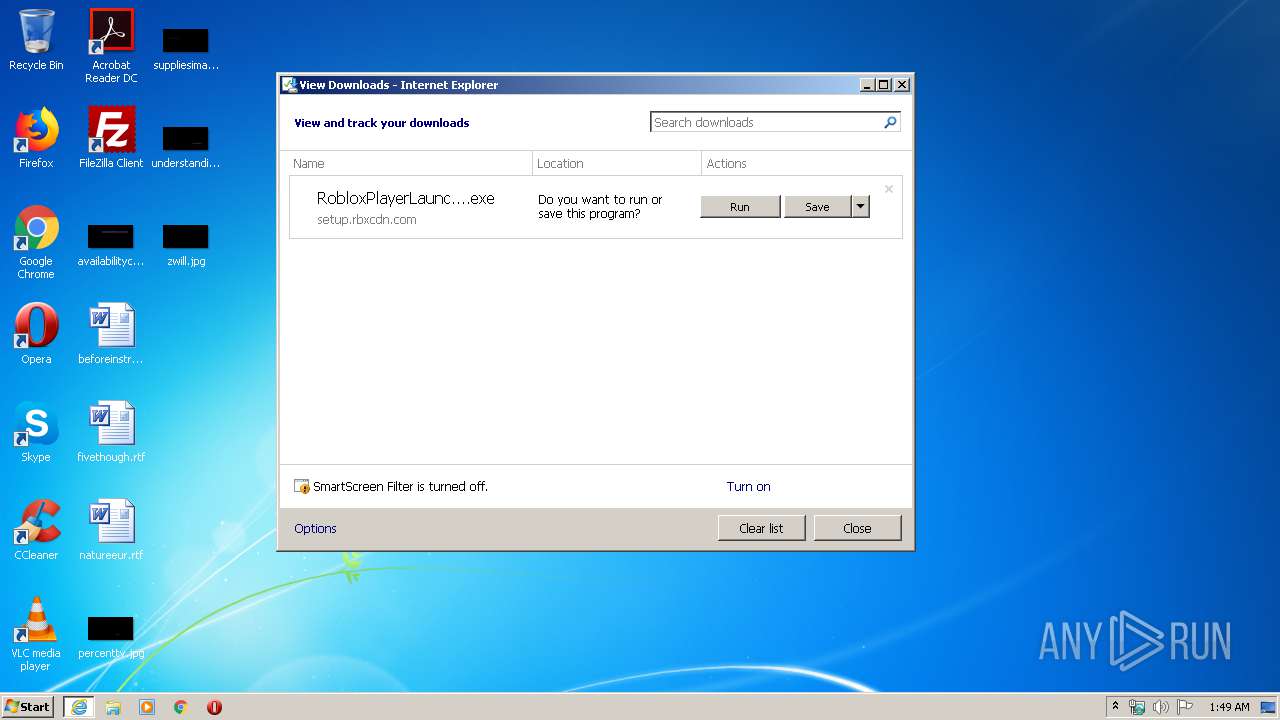
Application was dropped or rewritten from another process
- RobloxPlayerLauncher.exe (PID: 3352)
- RobloxPlayerLauncher.exe (PID: 2540)
- RobloxPlayerLauncher.exe (PID: 3100)
- RobloxPlayerLauncher.exe (PID: 256)
SUSPICIOUS
Executable content was dropped or overwritten
- iexplore.exe (PID: 3252)
- iexplore.exe (PID: 304)
- RobloxPlayerLauncher.exe (PID: 3352)
Reads Internet Cache Settings
- RobloxPlayerLauncher.exe (PID: 3352)
- RobloxPlayerLauncher.exe (PID: 3100)
- RobloxPlayerLauncher.exe (PID: 2540)
- RobloxPlayerLauncher.exe (PID: 256)
Application launched itself
- RobloxPlayerLauncher.exe (PID: 3352)
- RobloxPlayerLauncher.exe (PID: 3100)
Creates files in the user directory
- RobloxPlayerLauncher.exe (PID: 3352)
Modifies the open verb of a shell class
- RobloxPlayerLauncher.exe (PID: 3352)
Creates a software uninstall entry
- RobloxPlayerLauncher.exe (PID: 3352)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3212)
Changes IE settings (feature browser emulation)
- RobloxPlayerBeta.exe (PID: 944)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 304)
- iexplore.exe (PID: 3252)
Changes internet zones settings
- iexplore.exe (PID: 304)
Creates files in the user directory
- iexplore.exe (PID: 3252)
- iexplore.exe (PID: 304)
Modifies the phishing filter of IE
- iexplore.exe (PID: 304)
Application launched itself
- iexplore.exe (PID: 304)
- chrome.exe (PID: 3212)
Manual execution by user
- chrome.exe (PID: 3212)
Reads settings of System Certificates
- iexplore.exe (PID: 304)
- chrome.exe (PID: 3008)
- RobloxPlayerBeta.exe (PID: 944)
- iexplore.exe (PID: 3252)
Reads the hosts file
- chrome.exe (PID: 3008)
- chrome.exe (PID: 3212)
Dropped object may contain Bitcoin addresses
- RobloxPlayerLauncher.exe (PID: 3352)
Changes settings of System certificates
- iexplore.exe (PID: 304)
Adds / modifies Windows certificates
- iexplore.exe (PID: 304)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
80
Monitored processes
40
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | C:\Users\admin\AppData\Local\Roblox\Versions\version-76da16af95e2466c\RobloxPlayerLauncher.exe --crashpad --no-rate-limit --database=C:\Users\admin\AppData\Local\Temp\crashpad_roblox --metrics-dir=C:\Users\admin\AppData\Local\Temp\crashpad_roblox --url=https://upload.crashes.rbxinfra.com/post --annotation=UploadAttachmentKiloByteLimit=100 --annotation=UploadPercentage=100 --annotation=format=minidump --annotation=token=a2440b0bfdada85f34d79b43839f2b49ea6bba474bd7d126e844bc119271a1c3 --initial-client-data=0x4d8,0x4dc,0x4e0,0x4d4,0x4e8,0x3723a4,0x3723b4,0x3723c4 | C:\Users\admin\AppData\Local\Roblox\Versions\version-76da16af95e2466c\RobloxPlayerLauncher.exe | RobloxPlayerLauncher.exe | ||||||||||||
User: admin Company: Roblox Corporation Integrity Level: MEDIUM Description: Roblox Exit code: 0 Version: 1, 6, 0, 399257 Modules
| |||||||||||||||
| 280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,7461129839537033880,9597405677200184502,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11832806762184829688 --mojo-platform-channel-handle=3900 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 304 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.roblox.com/install/setup.ashx | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 944 | "C:\Users\admin\AppData\Local\Roblox\Versions\version-76da16af95e2466c\RobloxPlayerBeta.exe" --play -a https://www.roblox.com/Login/Negotiate.ashx -t C37CB3FFC2FCBE0B4B398AC008F9E06C10EA5C5208CD5E1FE687B84C48A2440DD4013D5CB03D9289A89911330FDF7ED8CAE7D6D21C37CE897DE04A0A4EDA50B6B9BB5E16A7DEF191889DAB5DC97A3B36397E934B9E40CDE4FBD4BB4D925FC563E81B55C729E2B83C7186499FBC41D7894BE142FA44AC3149693615C42D261C0F912ADDF92DD085A54AE043322518D09AE97B8F6740B1C299DF29F0613150EE904D9BF03D -j https://assetgame.roblox.com/game/PlaceLauncher.ashx?request=RequestGame&browserTrackerId=49987460144&placeId=920587237&isPlayTogetherGame=false -b 49987460144 --launchtime=1586480012894 --rloc en_us --gloc en_us | C:\Users\admin\AppData\Local\Roblox\Versions\version-76da16af95e2466c\RobloxPlayerBeta.exe | RobloxPlayerLauncher.exe | ||||||||||||
User: admin Company: Roblox Corporation Integrity Level: MEDIUM Description: Roblox Game Client Exit code: 0 Version: 0, 427, 0, 399257 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,7461129839537033880,9597405677200184502,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=512067108872718400 --mojo-platform-channel-handle=4332 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,7461129839537033880,9597405677200184502,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18301938060047015869 --mojo-platform-channel-handle=4040 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,7461129839537033880,9597405677200184502,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16461870283012520330 --mojo-platform-channel-handle=4380 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=996,7461129839537033880,9597405677200184502,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4089382367890222177 --mojo-platform-channel-handle=3828 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,7461129839537033880,9597405677200184502,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15866688574666980249 --mojo-platform-channel-handle=3964 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,7461129839537033880,9597405677200184502,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1549664707407047093 --mojo-platform-channel-handle=4016 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
6 040
Read events
2 215
Write events
2 631
Delete events
1 194
Modification events
| (PID) Process: | (304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 4041866702 | |||
| (PID) Process: | (304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30805713 | |||
| (PID) Process: | (304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
7
Suspicious files
222
Text files
382
Unknown types
29
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3252 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabF2C5.tmp | — | |
MD5:— | SHA256:— | |||
| 3252 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarF2C6.tmp | — | |
MD5:— | SHA256:— | |||
| 3252 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\Q3QPTE7A.txt | — | |
MD5:— | SHA256:— | |||
| 304 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 304 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF3CC89F6D6E781AC8.TMP | — | |
MD5:— | SHA256:— | |||
| 304 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\RobloxPlayerLauncher.exe.gb9ay00.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 3212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E8FC2A3-C8C.pma | — | |
MD5:— | SHA256:— | |||
| 3252 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | der | |
MD5:— | SHA256:— | |||
| 3212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3252 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
186
DNS requests
120
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3008 | chrome.exe | GET | 308 | 128.116.123.3:80 | http://roblox.com/drivers | US | — | — | whitelisted |
3252 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr5/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQiD0S5cIHyfrLTJ1fvAkJWflH%2B2QQUPeYpSJvqB8ohREom3m7e0oPQn1kCDQHuXyKVQkkF%2BQGRqNw%3D | US | der | 1.34 Kb | whitelisted |
3252 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/gseccovsslca2018/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBSTMjK03nNiYoQYvu4Izyfn9OJNdAQUWHuOdSr%2BYYCqkEABrtboB0ZuP0gCDGbM6PQ9Yanr1EKr1g%3D%3D | US | der | 1.01 Kb | whitelisted |
3352 | RobloxPlayerLauncher.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3008 | chrome.exe | GET | 200 | 205.234.175.102:80 | http://images.rbxcdn.com/c_cf_dj_ng_clothing_v1.png | US | image | 26.7 Kb | whitelisted |
3008 | chrome.exe | GET | 200 | 205.234.175.102:80 | http://images.rbxcdn.com/c_cf_gj_ng_clothing_v1.png | US | image | 24.6 Kb | whitelisted |
3252 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gseccovsslca2018/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBSTMjK03nNiYoQYvu4Izyfn9OJNdAQUWHuOdSr%2BYYCqkEABrtboB0ZuP0gCDGbM6PQ9Yanr1EKr1g%3D%3D | US | der | 1.01 Kb | whitelisted |
304 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3252 | iexplore.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
304 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3252 | iexplore.exe | 128.116.123.3:443 | www.roblox.com | University Corporation for Atmospheric Research | US | suspicious |
3252 | iexplore.exe | 192.124.249.41:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
3252 | iexplore.exe | 192.124.249.24:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
3252 | iexplore.exe | 205.234.175.102:443 | setup.rbxcdn.com | CacheNetworks, Inc. | US | suspicious |
3252 | iexplore.exe | 104.18.21.226:80 | ocsp2.globalsign.com | Cloudflare Inc | US | shared |
304 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3252 | iexplore.exe | 104.18.20.226:80 | ocsp2.globalsign.com | Cloudflare Inc | US | shared |
3008 | chrome.exe | 172.217.23.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3252 | iexplore.exe | 192.124.249.31:80 | crl.godaddy.com | Sucuri | US | unknown |
3008 | chrome.exe | 216.58.207.35:443 | www.google.com.ua | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.roblox.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
setup.rbxcdn.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
crl.godaddy.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
Threats
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
RobloxPlayerBeta.exe | |
RobloxPlayerBeta.exe | 1586480019.33312,06dc,6 LoadClientSettingsFromLocal group: "ClientAppSettings" |
RobloxPlayerBeta.exe | 1586480019.33808,06dc,6 Loading AppSettings.xml from C:\Users\admin\AppData\Local\Roblox\Versions\version-76da16af95e2466c\AppSettings.xml |
RobloxPlayerBeta.exe | |
RobloxPlayerBeta.exe | 1586480019.34304,06dc,6 setAssetFolder content |
RobloxPlayerBeta.exe | |
RobloxPlayerBeta.exe | |
RobloxPlayerBeta.exe | 1586480019.35991,06dc,6 setExtraAssetFolder C:/Users\admin\AppData\Local\Roblox\Versions\version-76da16af95e2466c\ExtraContent |
RobloxPlayerBeta.exe | |
RobloxPlayerBeta.exe | |