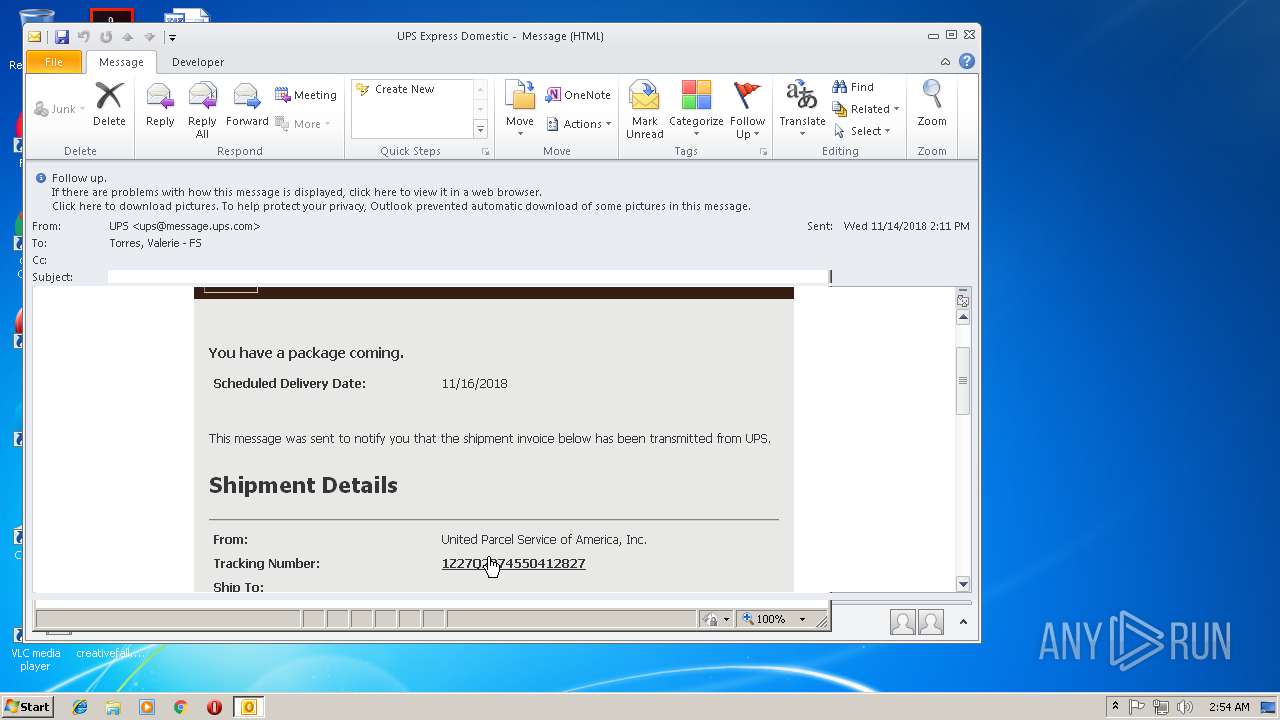
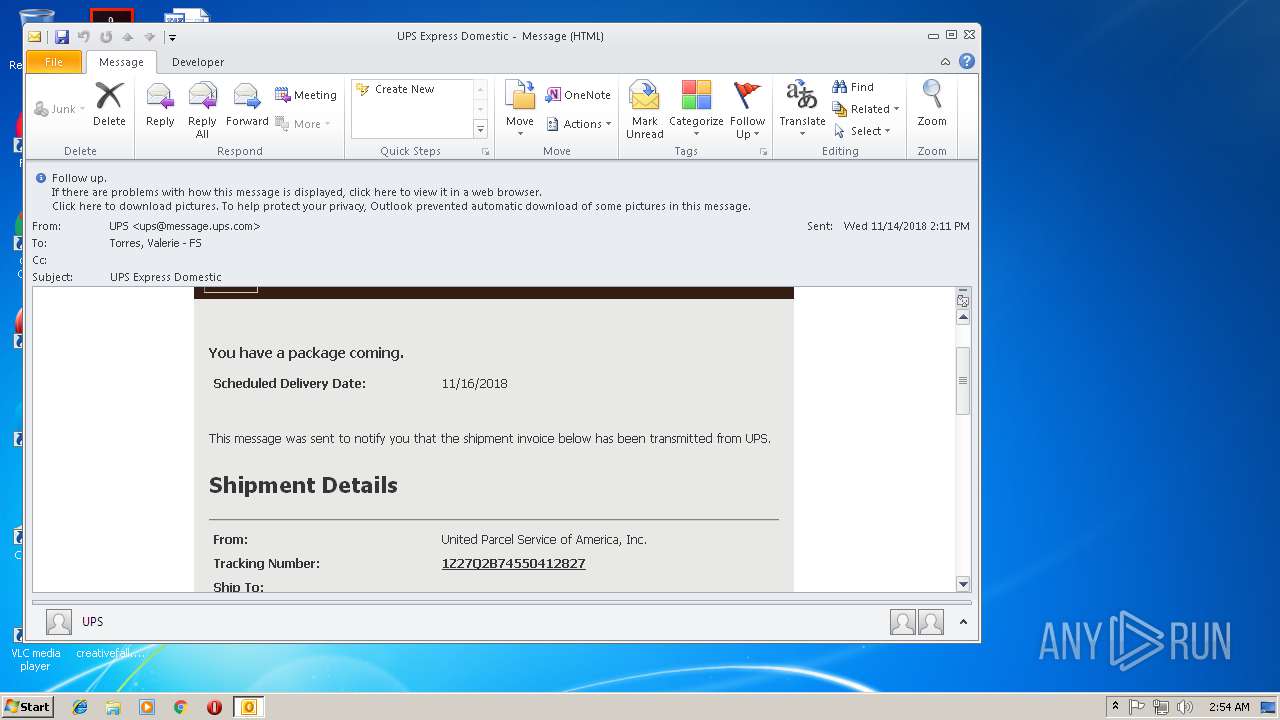
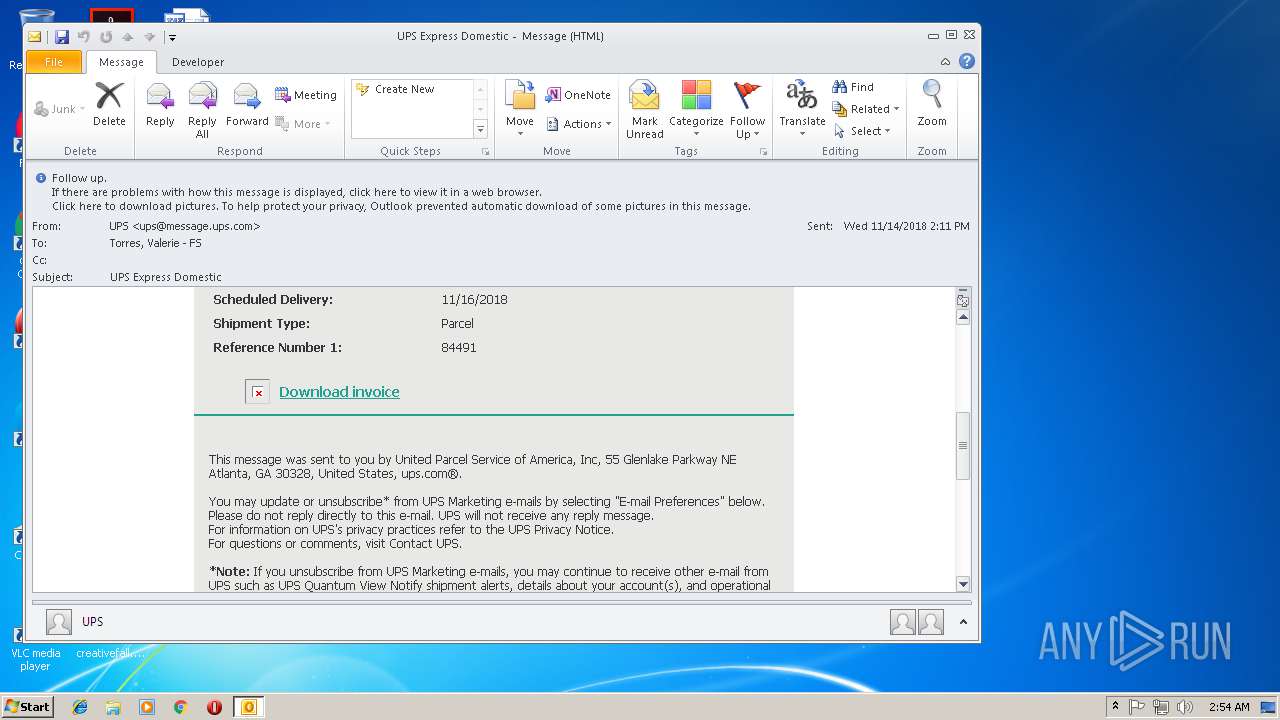
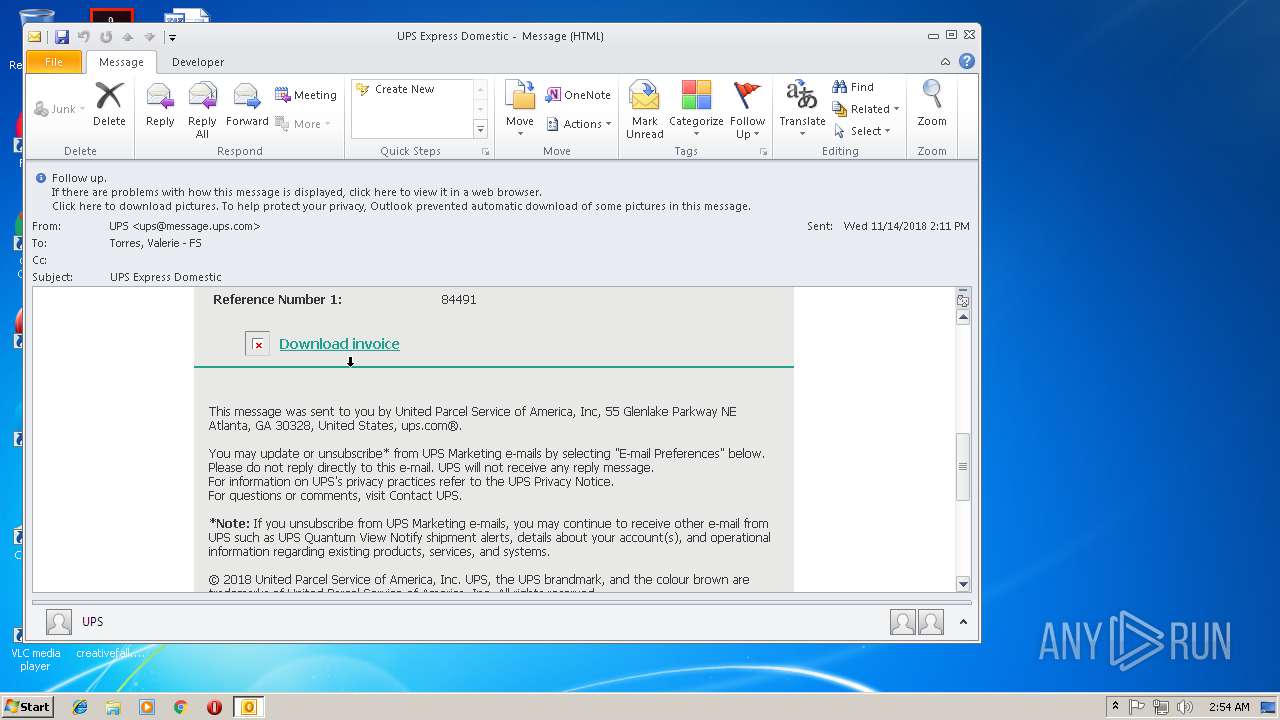
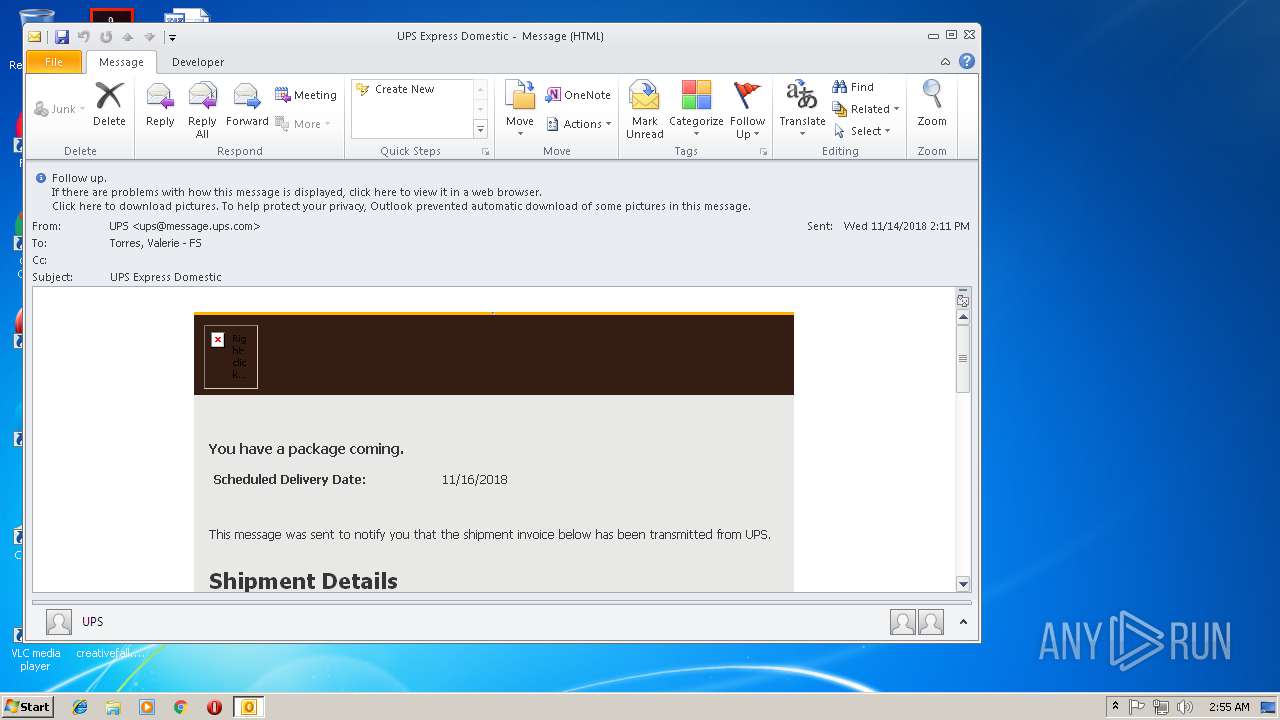
| File name: | UPS Express Domestic.eml |
| Full analysis: | https://app.any.run/tasks/708477e5-32e0-47a9-a21e-b86aecfcc5d2 |
| Verdict: | Malicious activity |
| Analysis date: | November 15, 2018, 02:54:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 351E6299371B0D14F20DA2AE610B083C |
| SHA1: | 42F7158C9CA7949214666F4378CEEE05DCABC3AC |
| SHA256: | 68DB5D2EBCE54B0EBF3F6E96B3BC1150AB368A0F457B4597D2CB7A02F779F5B1 |
| SSDEEP: | 768:l26LuPvfb6ThKwVEUggZCFrBT2V4IAUqpq4W:FuDu4WEUggEFrBT2V4asq4W |
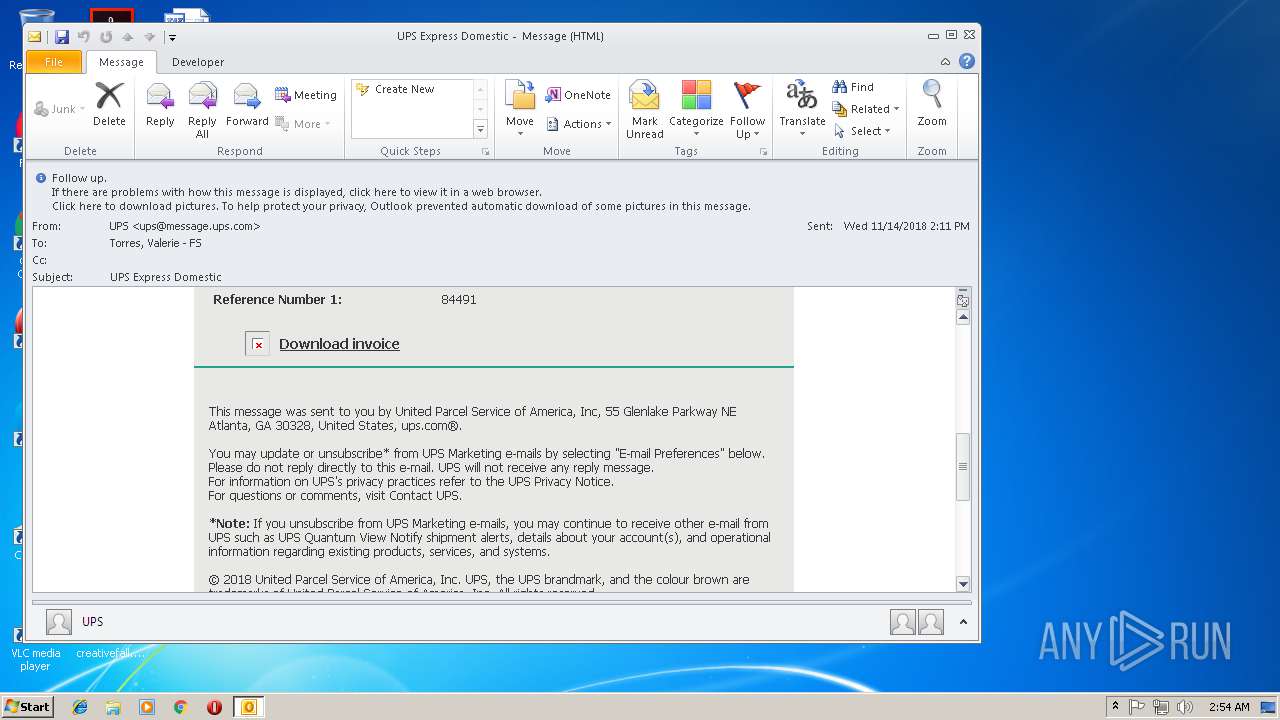
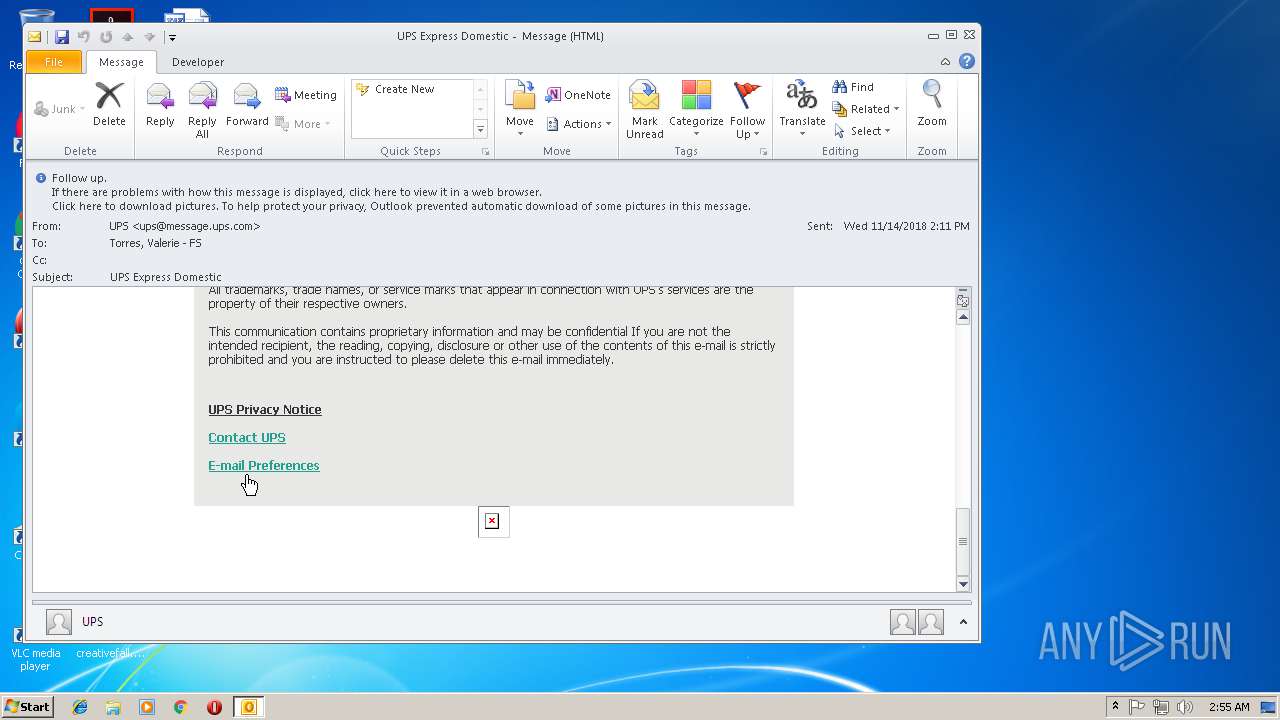
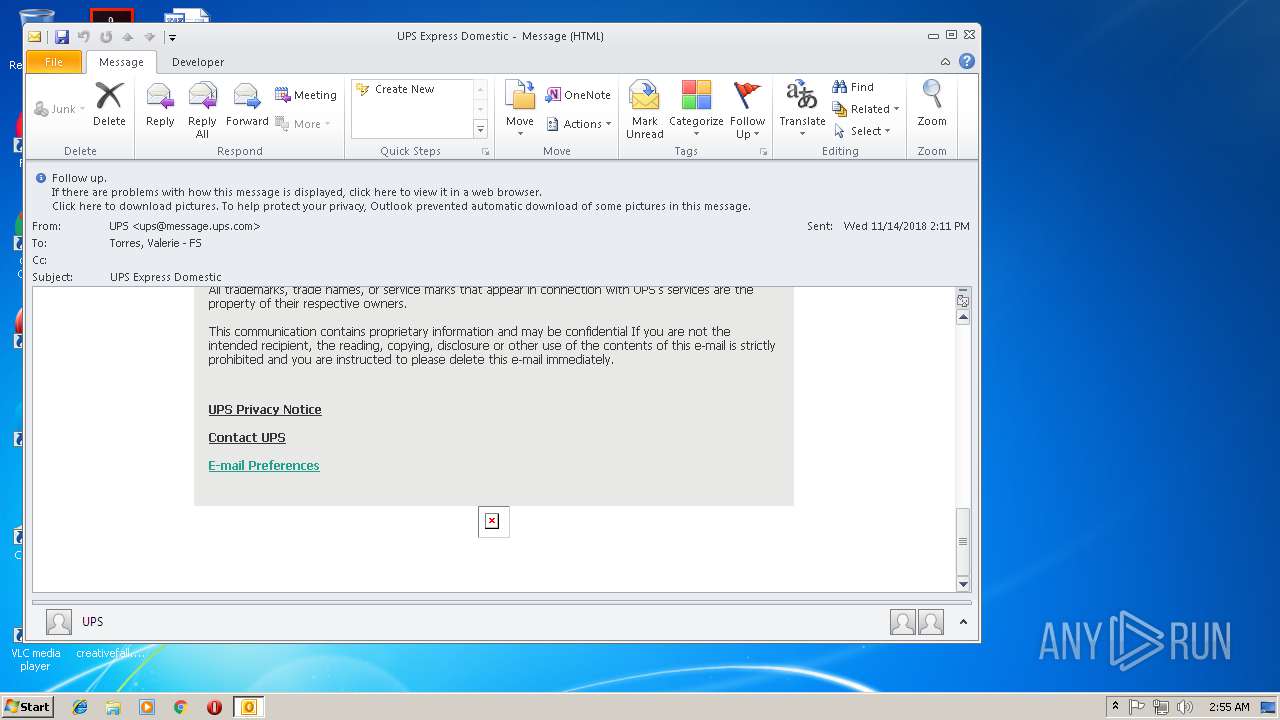
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 3832)
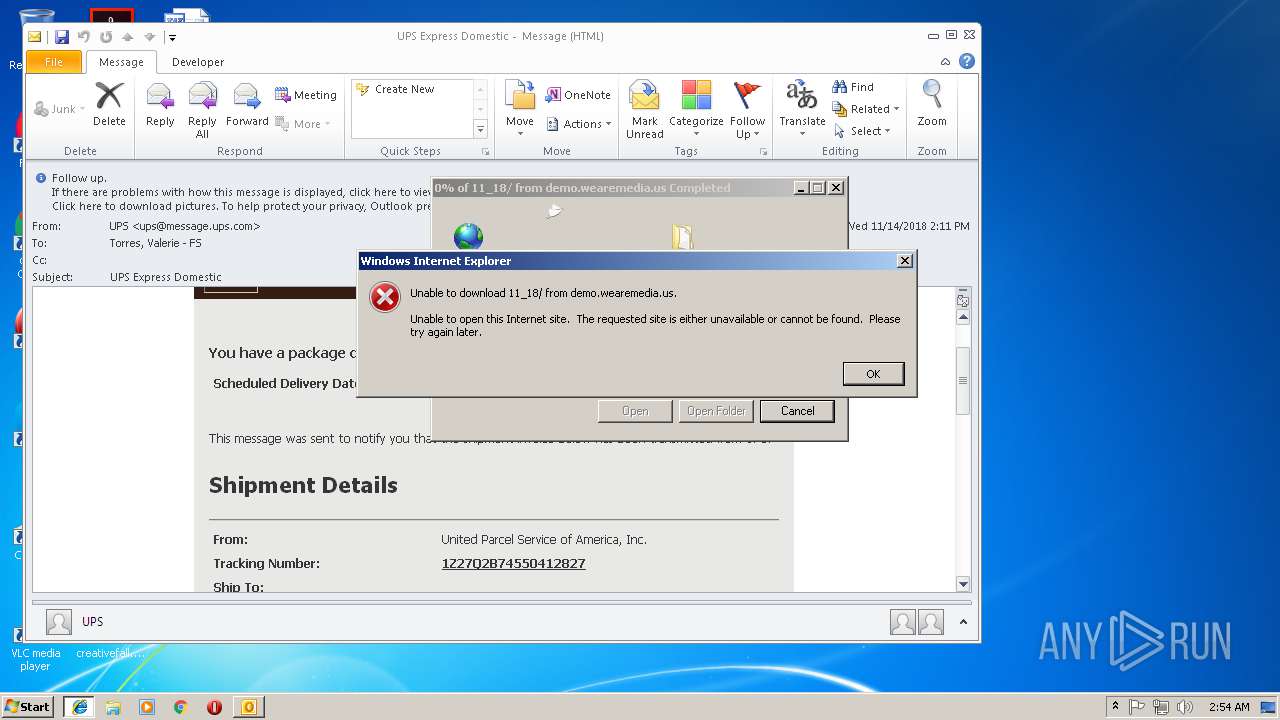
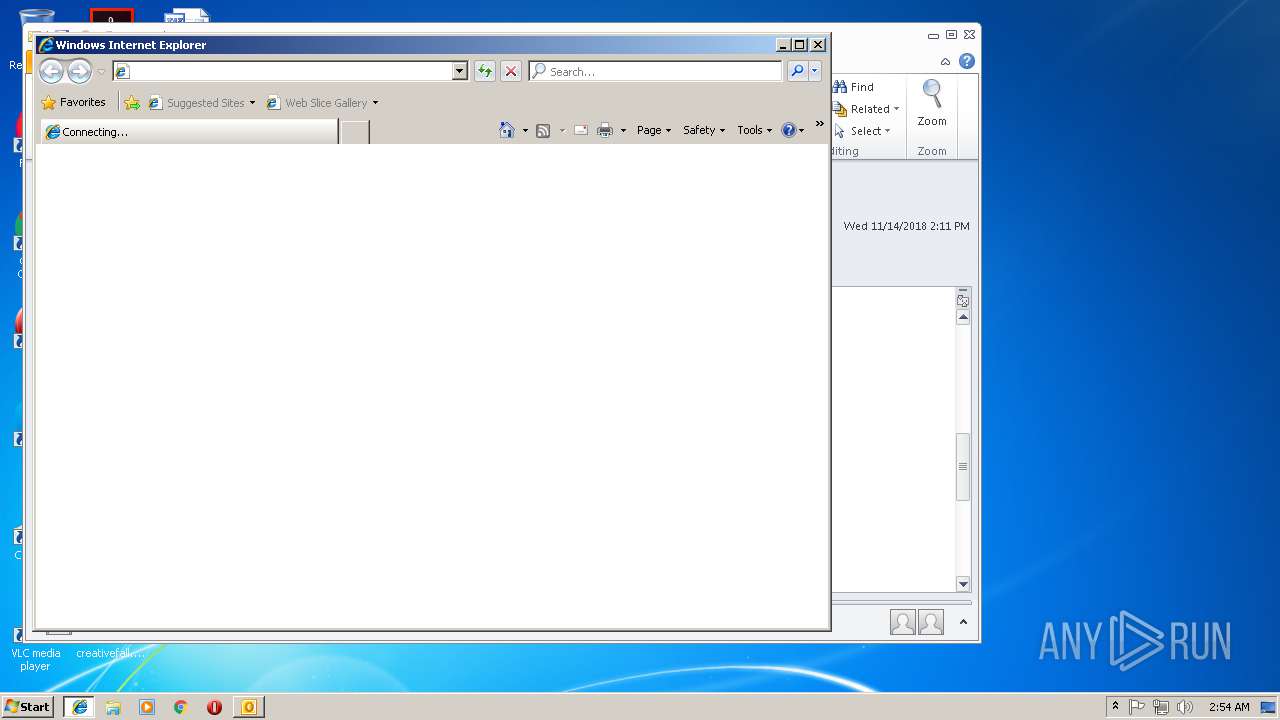
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3832)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3832)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3832)
Changes internet zones settings
- iexplore.exe (PID: 3584)
- iexplore.exe (PID: 2972)
- iexplore.exe (PID: 2896)
- iexplore.exe (PID: 2244)
- iexplore.exe (PID: 968)
Reads internet explorer settings
- iexplore.exe (PID: 2304)
- iexplore.exe (PID: 1672)
- iexplore.exe (PID: 1320)
Application launched itself
- iexplore.exe (PID: 2896)
- iexplore.exe (PID: 968)
- iexplore.exe (PID: 2972)
- iexplore.exe (PID: 3584)
- iexplore.exe (PID: 2244)
Creates files in the user directory
- iexplore.exe (PID: 3704)
Reads Internet Cache Settings
- iexplore.exe (PID: 3704)
- iexplore.exe (PID: 3320)
- iexplore.exe (PID: 2304)
- iexplore.exe (PID: 1672)
- iexplore.exe (PID: 1320)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
43
Monitored processes
11
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
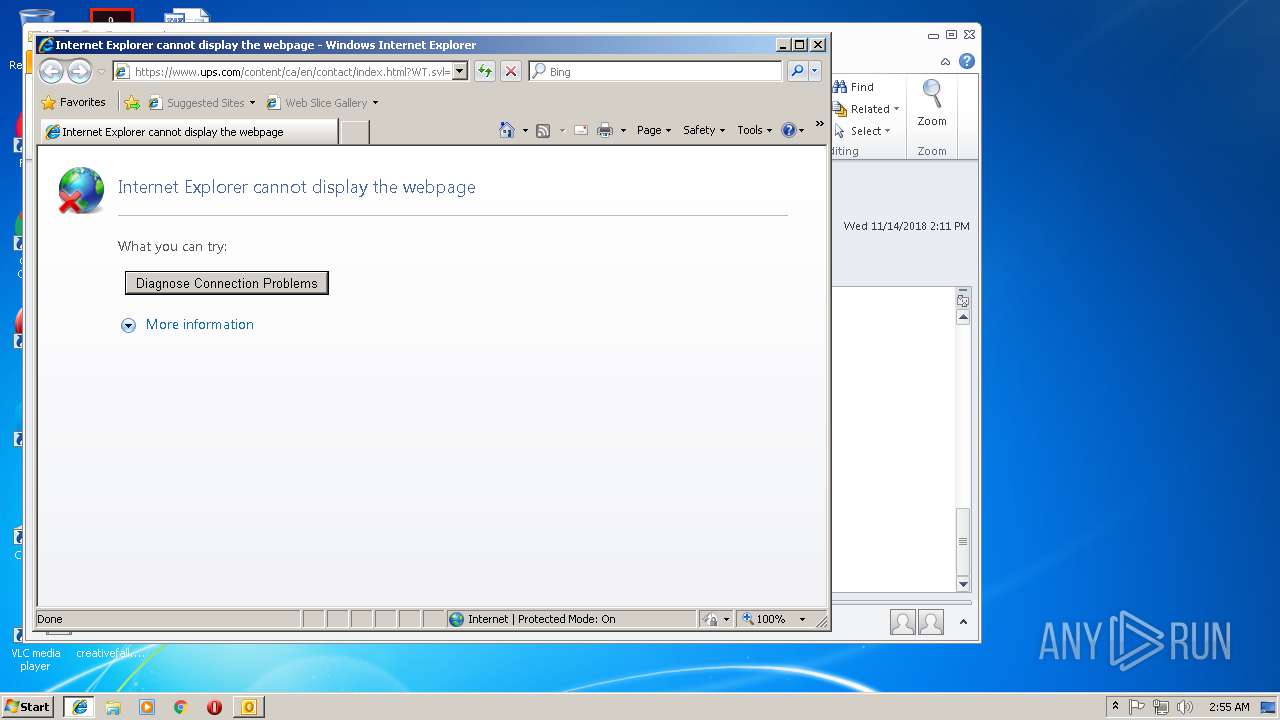
| 968 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.ups.com/content/ca/en/contact/index.html?WT.svl=eFooter | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1320 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2244 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:968 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
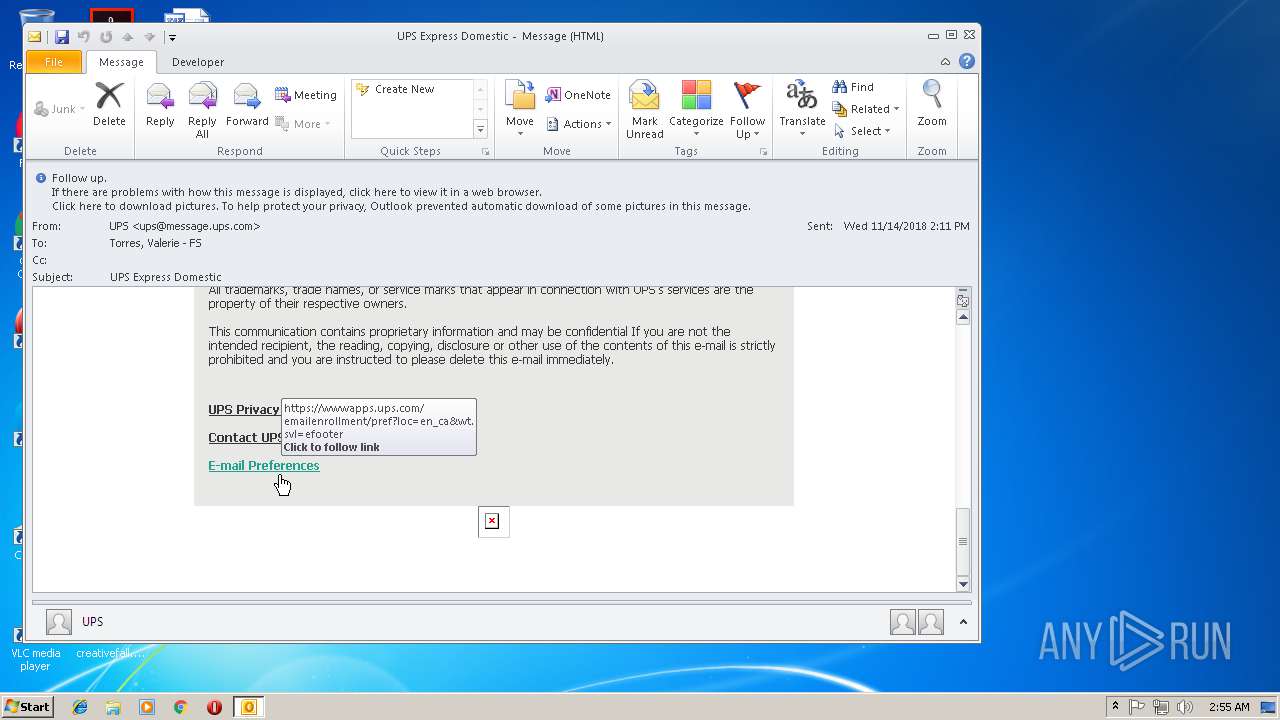
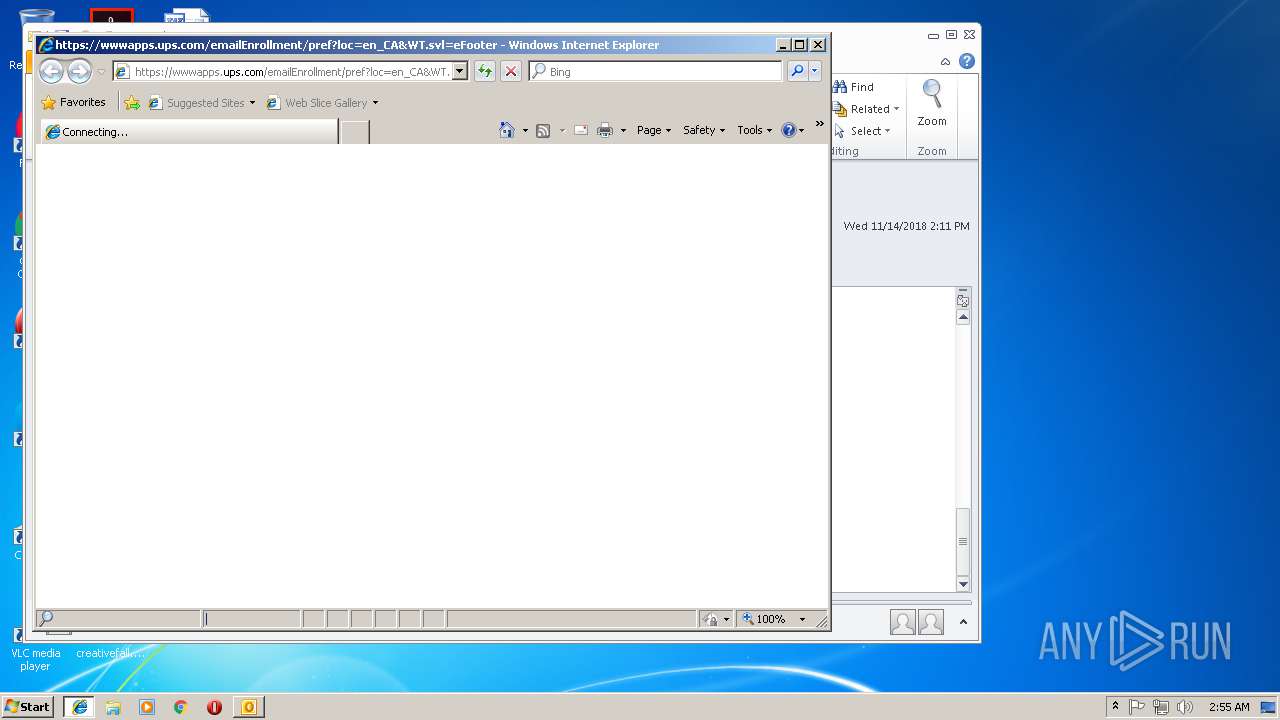
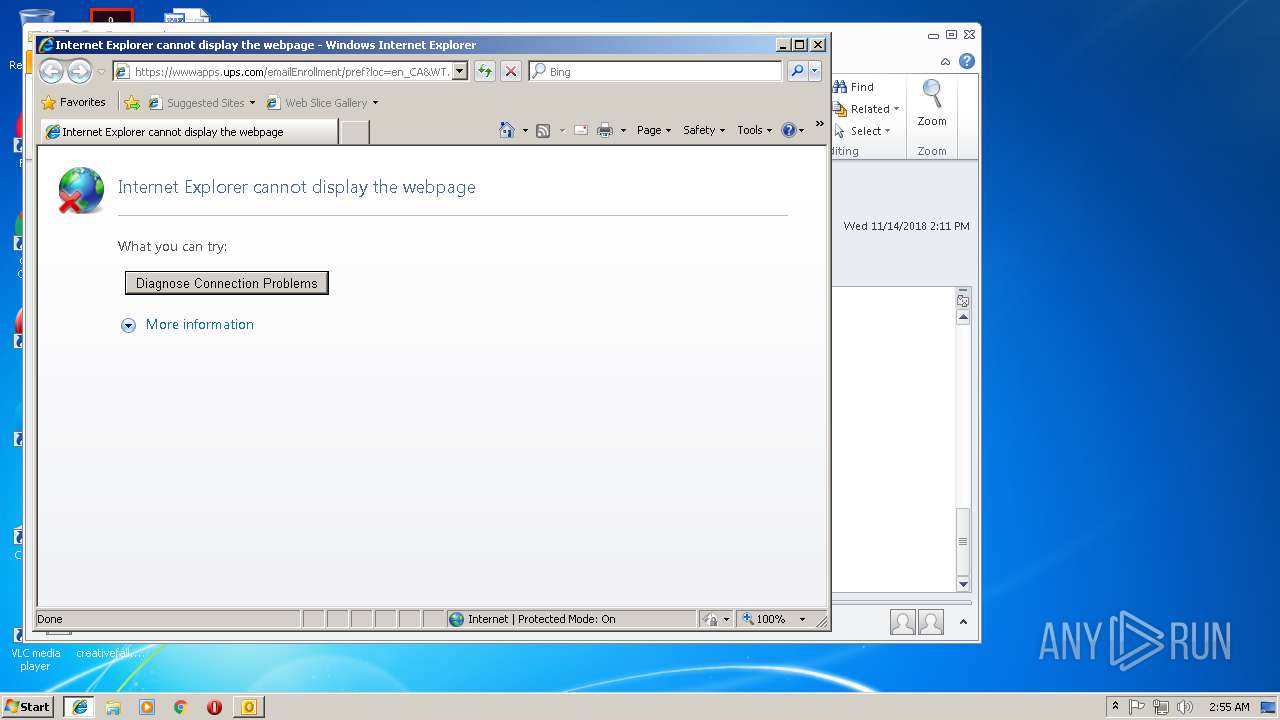
| 2244 | "C:\Program Files\Internet Explorer\iexplore.exe" https://wwwapps.ups.com/emailEnrollment/pref?loc=en_CA&WT.svl=eFooter | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2972 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
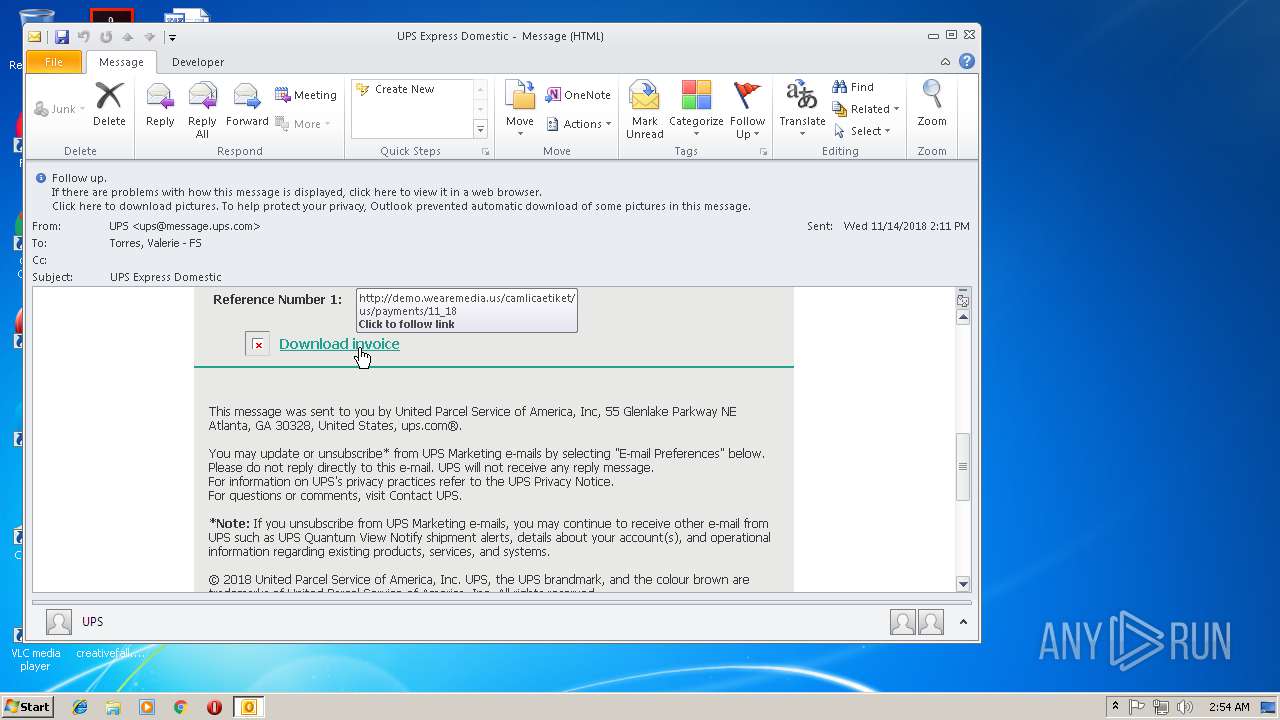
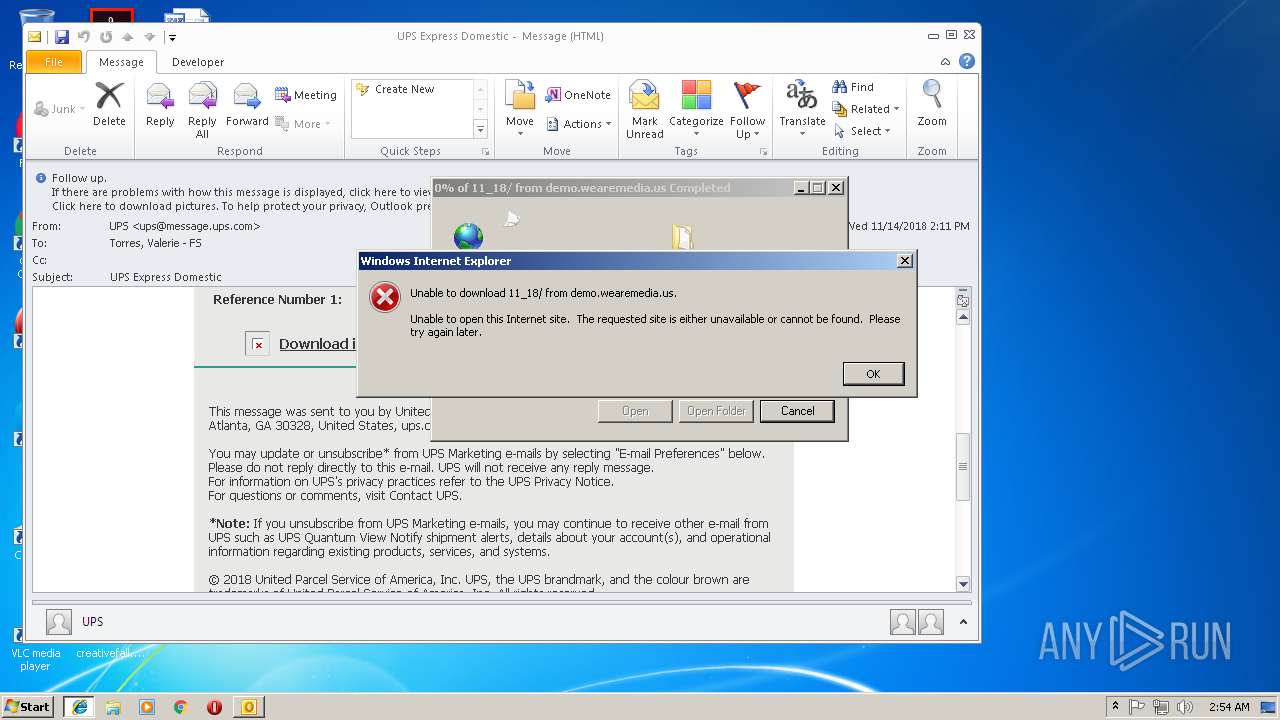
| 2896 | "C:\Program Files\Internet Explorer\iexplore.exe" http://demo.wearemedia.us/camlicaetiket/US/Payments/11_18 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
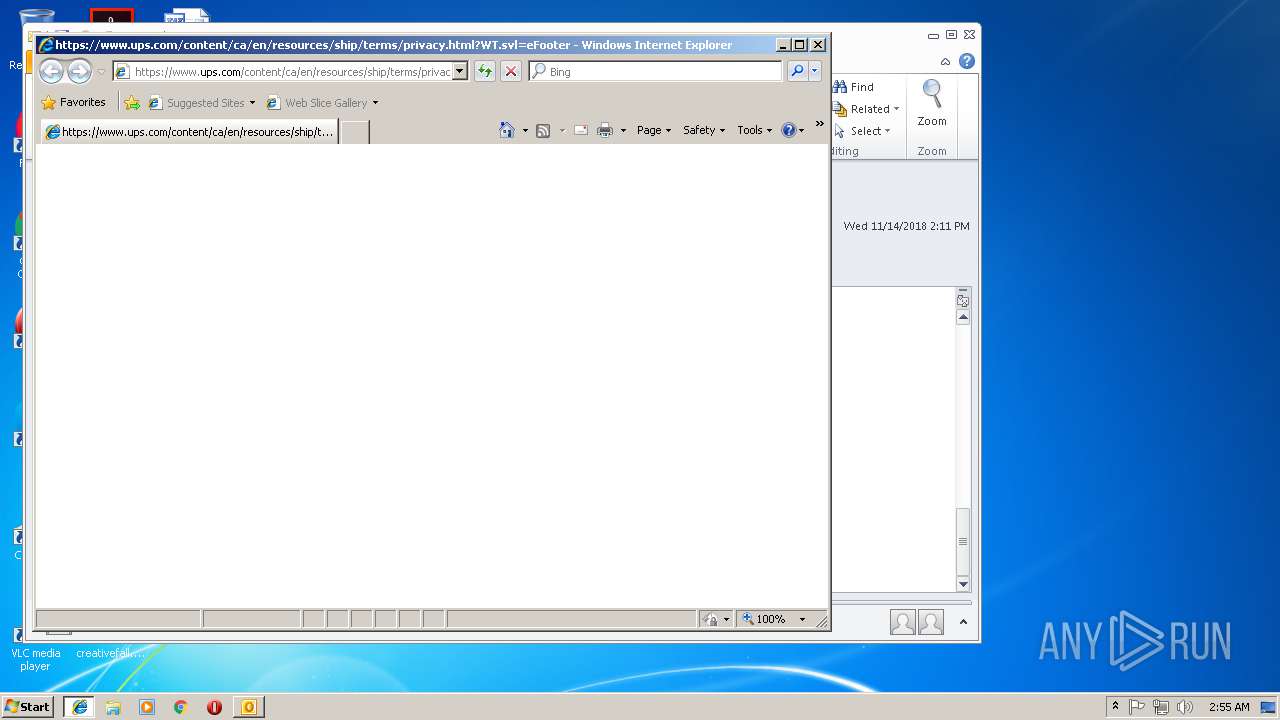
| 2972 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.ups.com/content/ca/en/resources/ship/terms/privacy.html?WT.svl=eFooter | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3320 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3584 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3584 | "C:\Program Files\Internet Explorer\iexplore.exe" http://demo.wearemedia.us/camlicaetiket/US/Payments/11_18 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3704 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2896 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 937
Read events
2 341
Write events
572
Delete events
24
Modification events
| (PID) Process: | (3832) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3832) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3832) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | ~hl |
Value: 7E686C00F80E0000010000000000000000000000 | |||
| (PID) Process: | (3832) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: F80E0000A671AF898E7CD40100000000 | |||
| (PID) Process: | (3832) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3832) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219778560 | |||
| (PID) Process: | (3832) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3832) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3832) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3832) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1299120149 | |||
Executable files
0
Suspicious files
8
Text files
59
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3832 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRA0FE.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2896 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2896 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2896 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFD07BA0E4E53A9441.TMP | — | |
MD5:— | SHA256:— | |||
| 2896 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF36FA43824840276C.TMP | — | |
MD5:— | SHA256:— | |||
| 2896 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{CC20B183-E881-11E8-BFAB-5254004AAD11}.dat | — | |
MD5:— | SHA256:— | |||
| 3584 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3584 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3584 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF30EC7329B8464B22.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
20
DNS requests
7
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3832 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3704 | iexplore.exe | GET | 200 | 94.73.151.74:80 | http://demo.wearemedia.us/camlicaetiket/US/Payments/11_18/ | TR | document | 75.2 Kb | malicious |
3320 | iexplore.exe | GET | 200 | 94.73.151.74:80 | http://demo.wearemedia.us/camlicaetiket/US/Payments/11_18/ | TR | document | 75.2 Kb | malicious |
2972 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3704 | iexplore.exe | GET | 301 | 94.73.151.74:80 | http://demo.wearemedia.us/camlicaetiket/US/Payments/11_18 | TR | html | 1.12 Kb | malicious |
3320 | iexplore.exe | GET | 301 | 94.73.151.74:80 | http://demo.wearemedia.us/camlicaetiket/US/Payments/11_18 | TR | html | 1.12 Kb | malicious |
968 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2244 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2896 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3584 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3832 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3704 | iexplore.exe | 94.73.151.74:80 | demo.wearemedia.us | Cizgi Telekomunikasyon Anonim Sirketi | TR | suspicious |
2896 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3320 | iexplore.exe | 94.73.151.74:80 | demo.wearemedia.us | Cizgi Telekomunikasyon Anonim Sirketi | TR | suspicious |
3584 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2972 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2304 | iexplore.exe | 2.18.232.186:443 | www.ups.com | Akamai International B.V. | — | whitelisted |
1672 | iexplore.exe | 2.18.232.186:443 | www.ups.com | Akamai International B.V. | — | whitelisted |
968 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1320 | iexplore.exe | 2.18.232.186:443 | www.ups.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
demo.wearemedia.us |
| malicious |
www.bing.com |
| whitelisted |
www.ups.com |
| whitelisted |
wwwapps.ups.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
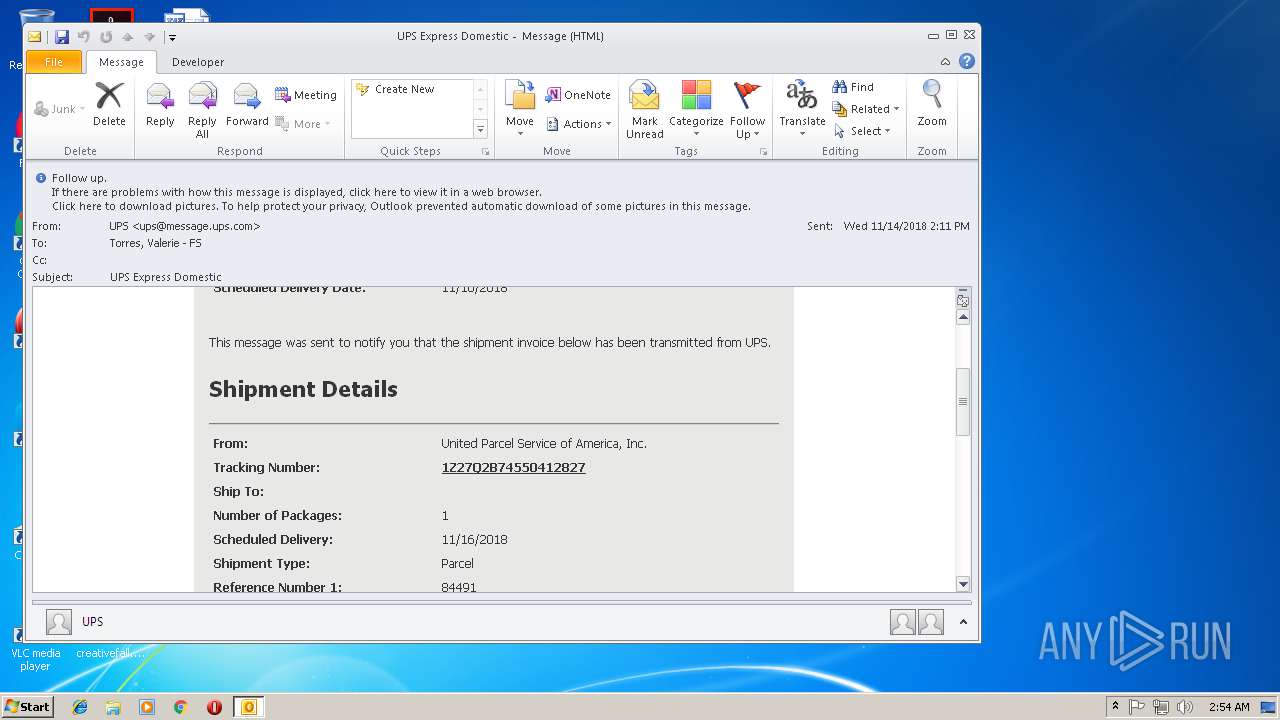
3704 | iexplore.exe | Attempted User Privilege Gain | SC ATTEMPTED_USER Microsoft Word 2016 use after free attempt |
3704 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Office Document Download Containing AutoOpen Macro |
3704 | iexplore.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
3704 | iexplore.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
3320 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Office Document Download Containing AutoOpen Macro |
3320 | iexplore.exe | Attempted User Privilege Gain | SC ATTEMPTED_USER Microsoft Word 2016 use after free attempt |
3320 | iexplore.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
3320 | iexplore.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |