| File name: | SetupYabe_v1.3.2.exe |
| Full analysis: | https://app.any.run/tasks/0ef2e6db-fa7f-4d11-9865-1f58852d5678 |
| Verdict: | Malicious activity |
| Analysis date: | February 13, 2024, 17:17:30 |
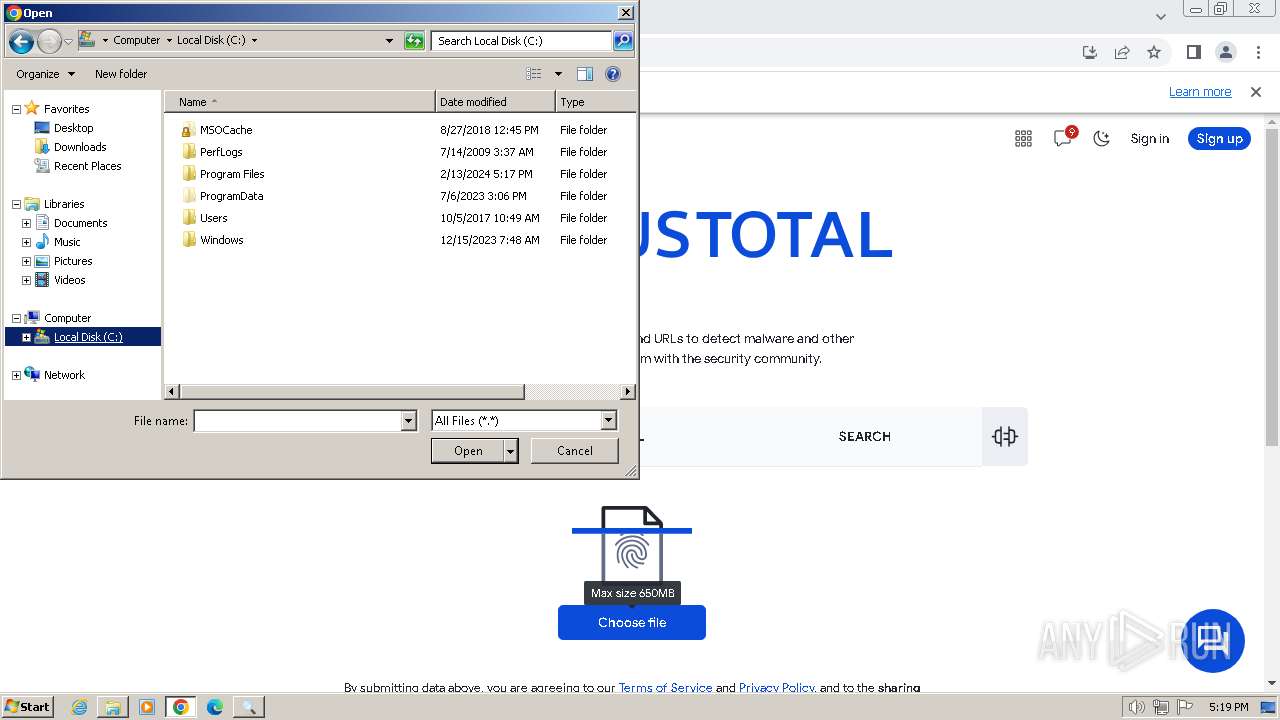
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 5D40F1CF3C1CC7DFFD721F0AEB1D7629 |
| SHA1: | 045FD62948AF0CA9BE1FE94AD01716FF8C494032 |
| SHA256: | 68D730B093258D1BC102361E8F3A714B07676FF42349F563E27EB939D7EA0773 |
| SSDEEP: | 98304:FbUoO+RQ4OSiJiY636OUtpySSW+mSY1e7a0bEhHuYMkkff0ZLqXjOA7ftjop0+5x:1mN |
MALICIOUS
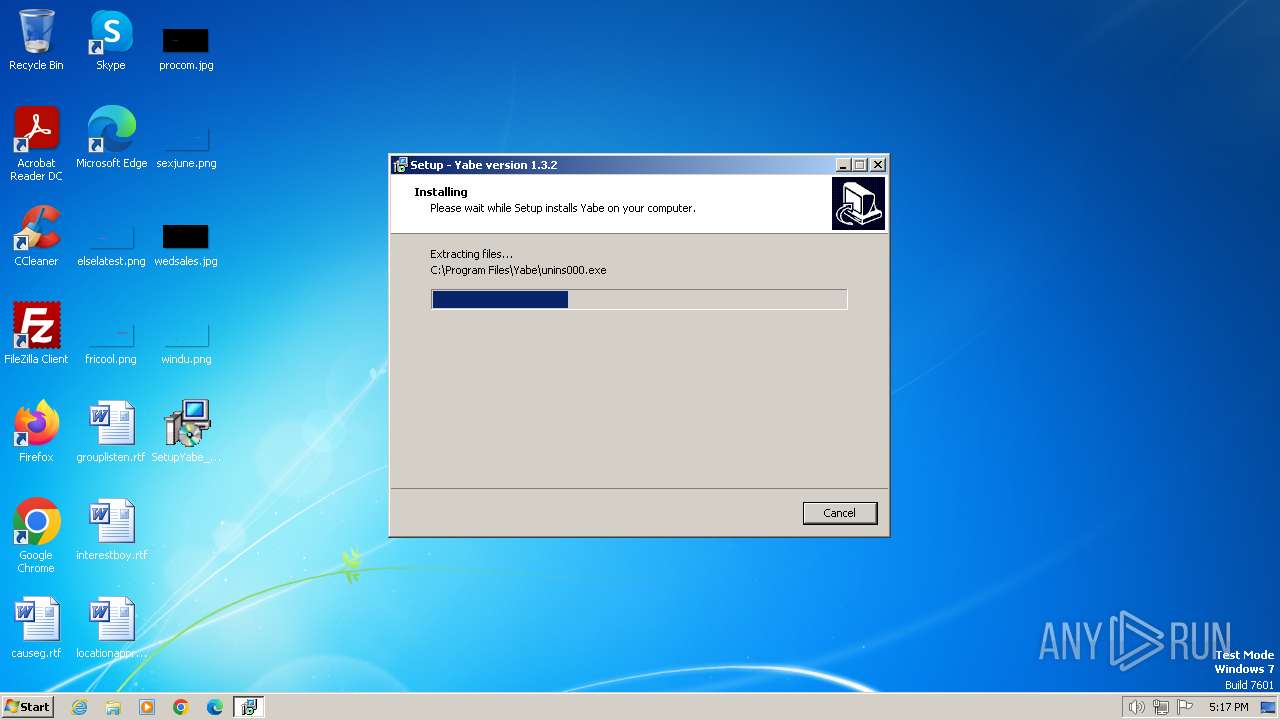
Drops the executable file immediately after the start
- SetupYabe_v1.3.2.exe (PID: 3240)
- SetupYabe_v1.3.2.exe (PID: 1776)
- SetupYabe_v1.3.2.tmp (PID: 2840)
SUSPICIOUS
Executable content was dropped or overwritten
- SetupYabe_v1.3.2.exe (PID: 3240)
- SetupYabe_v1.3.2.exe (PID: 1776)
- SetupYabe_v1.3.2.tmp (PID: 2840)
Reads the Windows owner or organization settings
- SetupYabe_v1.3.2.tmp (PID: 2840)
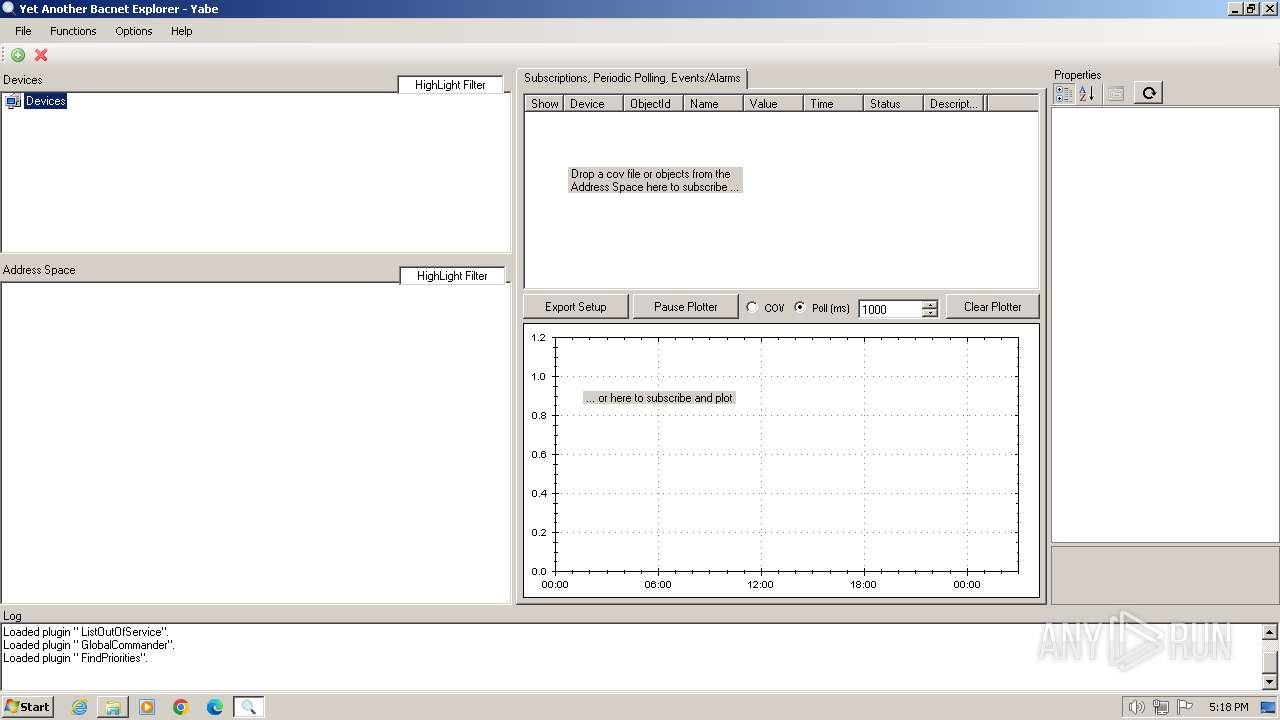
Reads security settings of Internet Explorer
- Yabe.exe (PID: 2232)
Reads the Internet Settings
- Yabe.exe (PID: 2232)
INFO
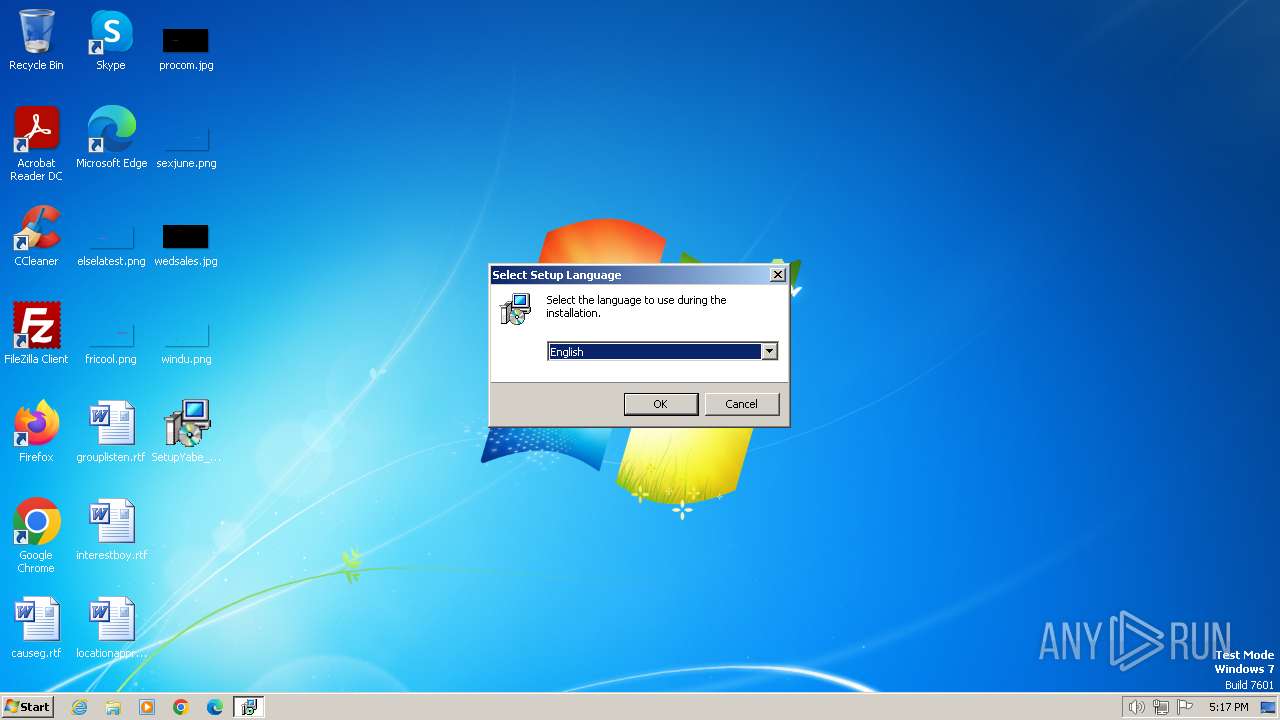
Checks supported languages
- SetupYabe_v1.3.2.exe (PID: 3240)
- SetupYabe_v1.3.2.exe (PID: 1776)
- SetupYabe_v1.3.2.tmp (PID: 3864)
- SetupYabe_v1.3.2.tmp (PID: 2840)
- Yabe.exe (PID: 2232)
Create files in a temporary directory
- SetupYabe_v1.3.2.exe (PID: 3240)
- SetupYabe_v1.3.2.exe (PID: 1776)
Reads the computer name
- SetupYabe_v1.3.2.tmp (PID: 3864)
- SetupYabe_v1.3.2.tmp (PID: 2840)
- Yabe.exe (PID: 2232)
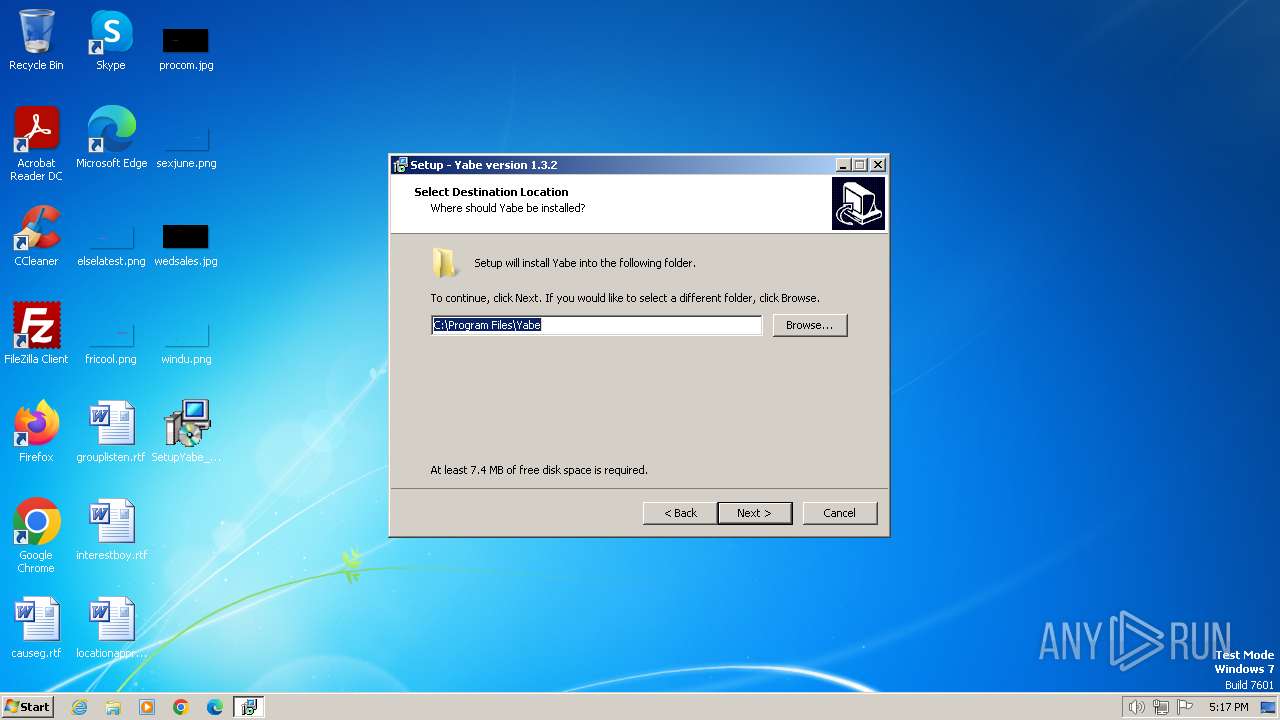
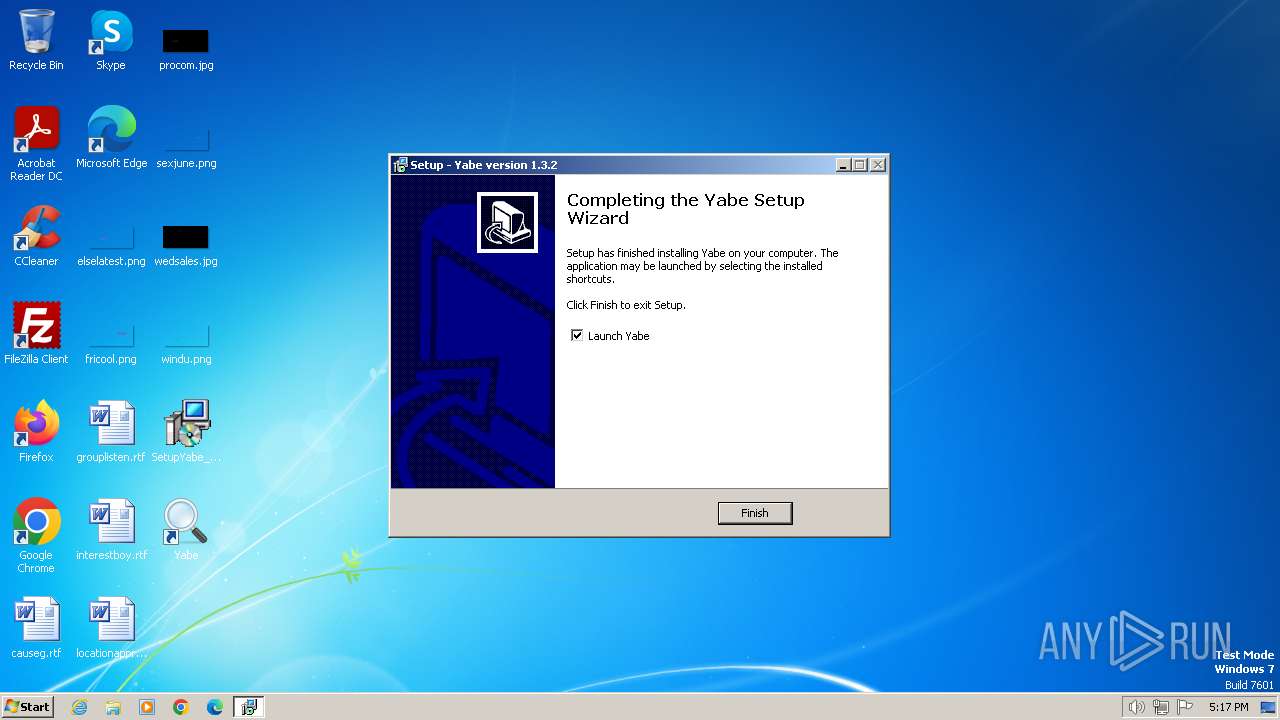
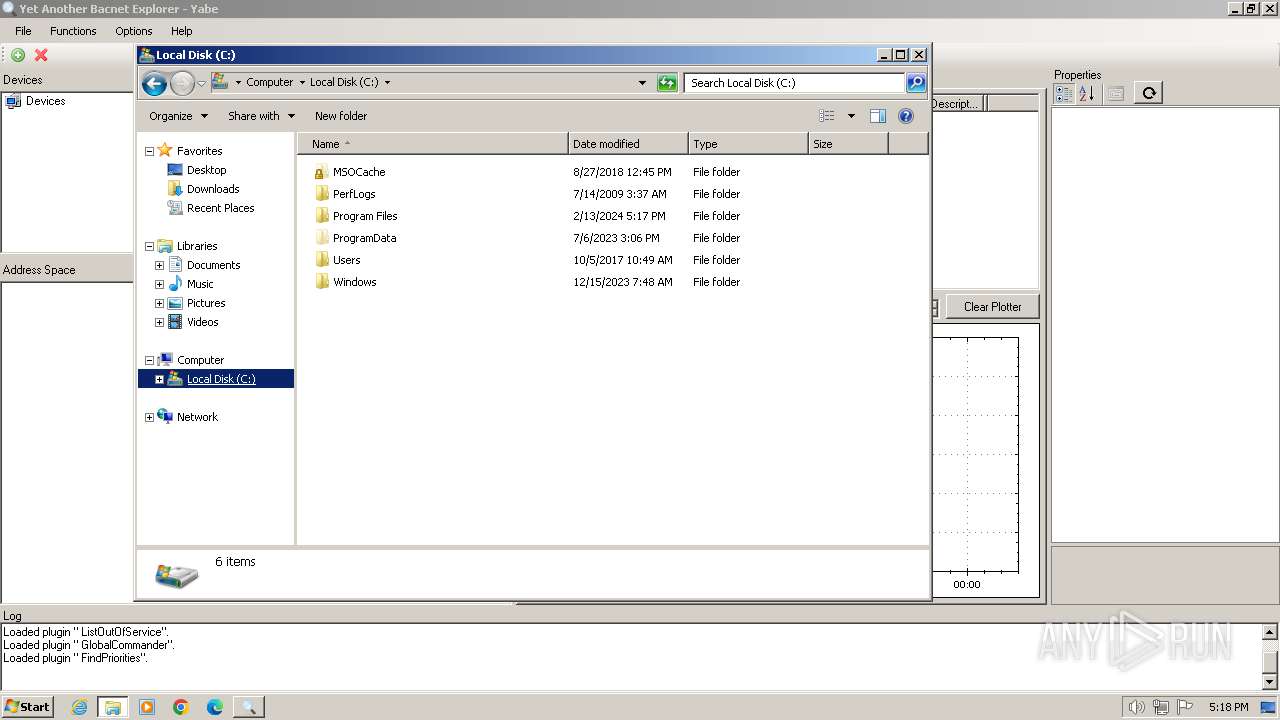
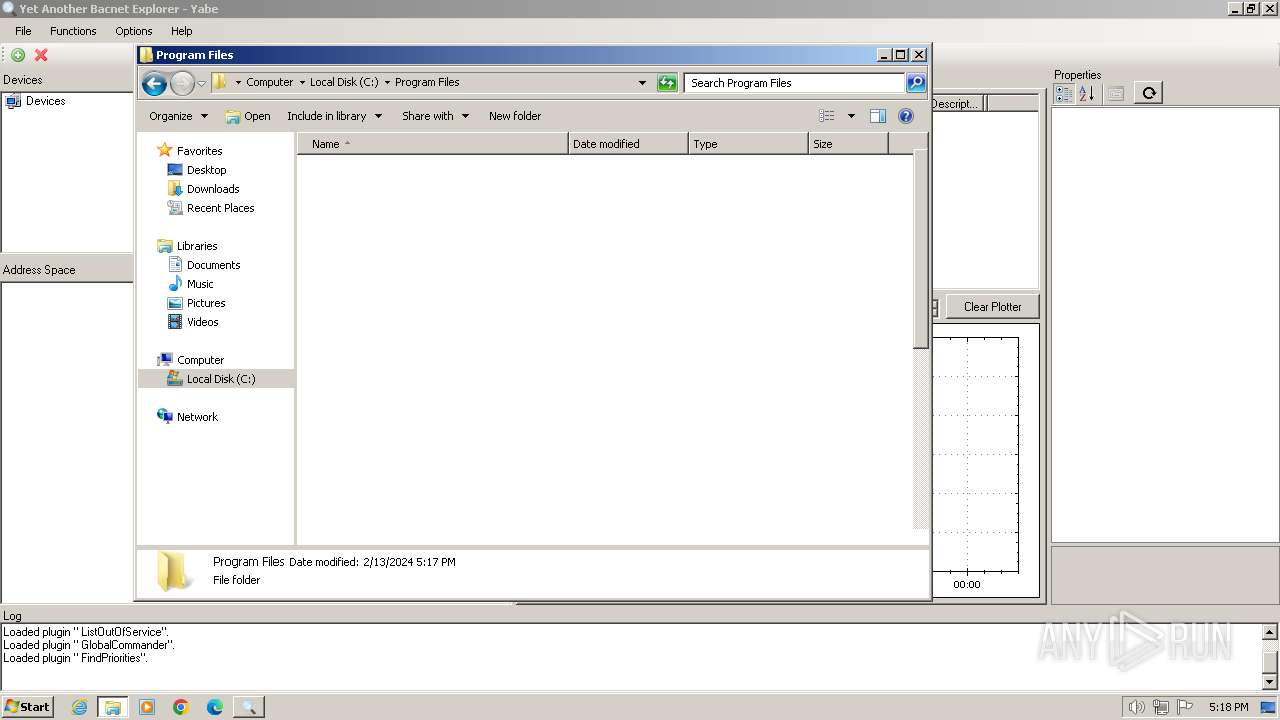
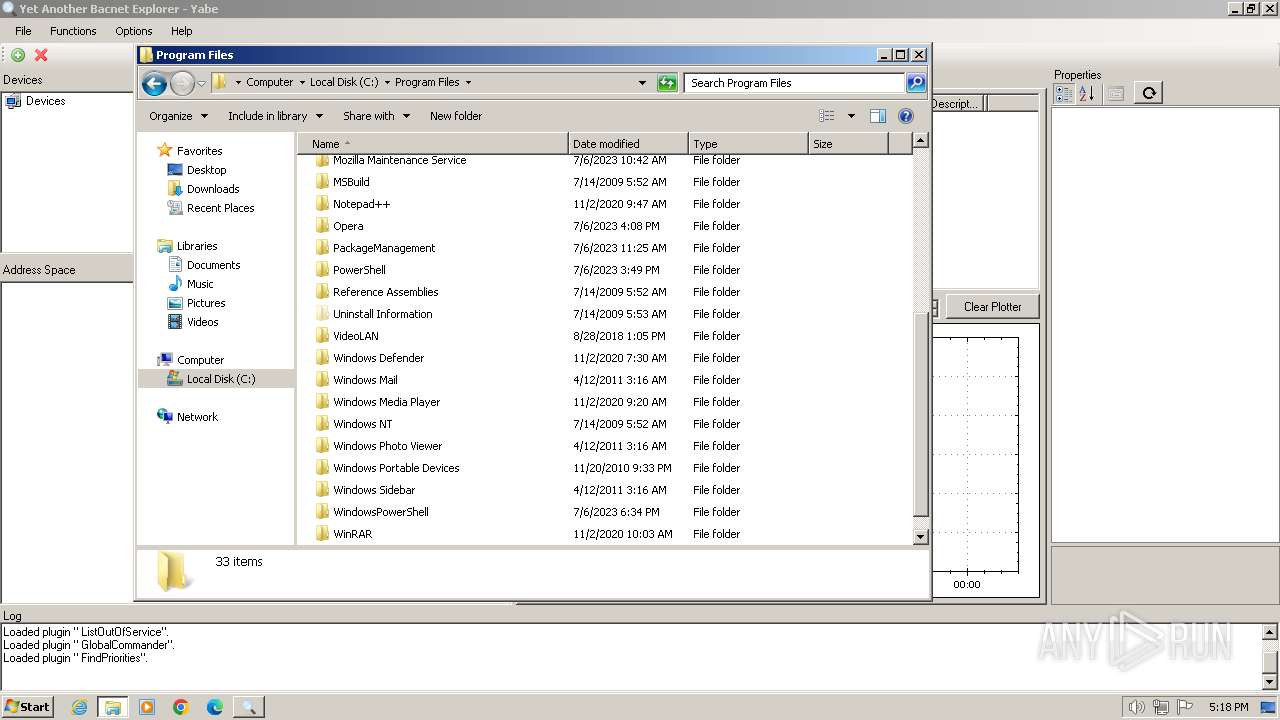
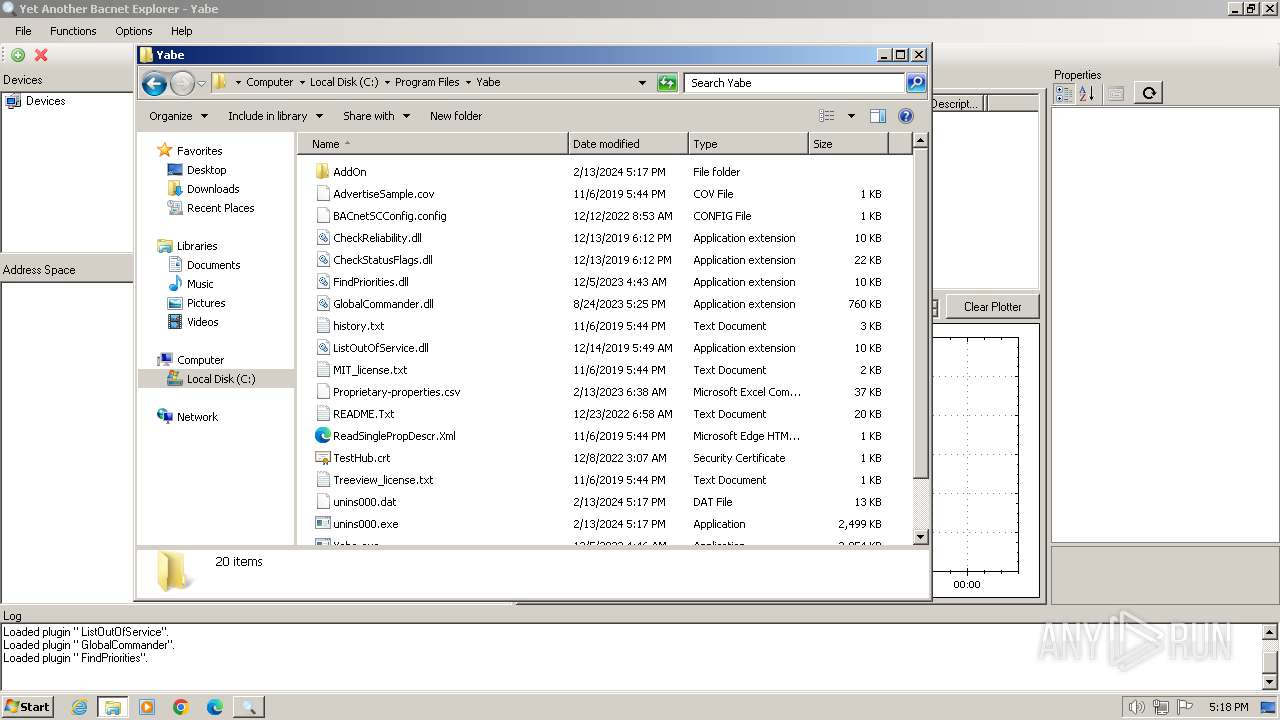
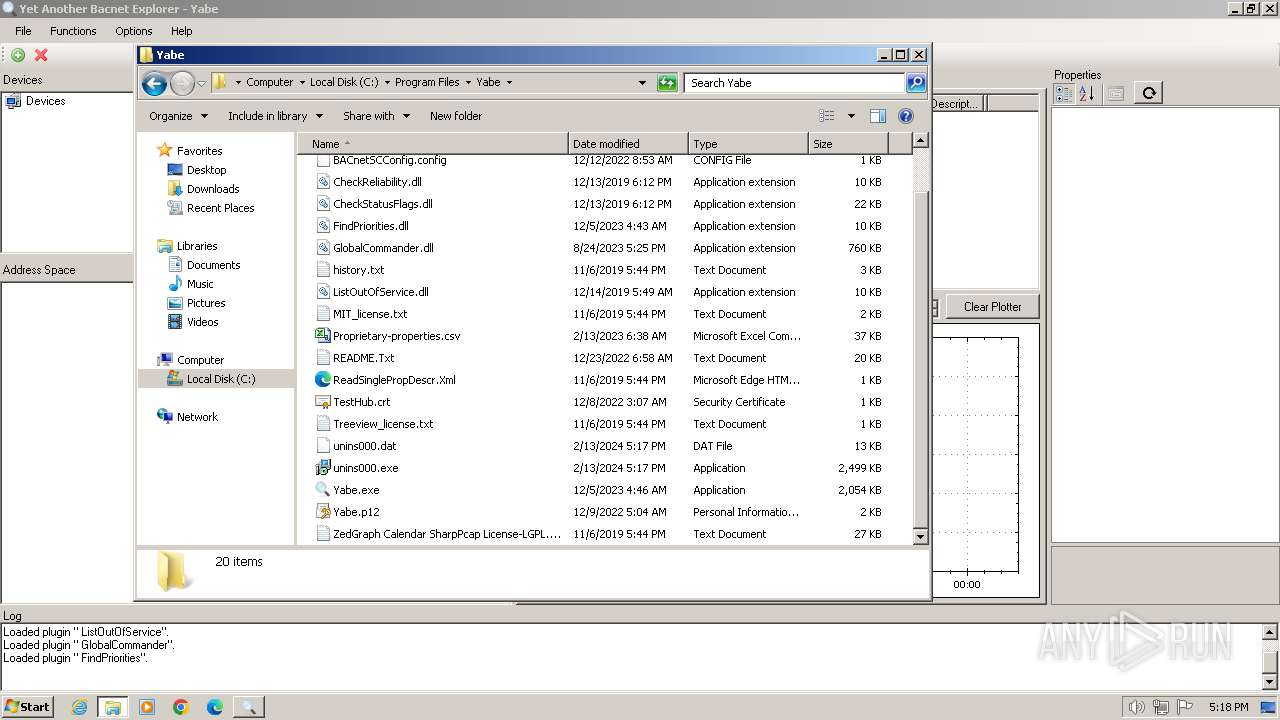
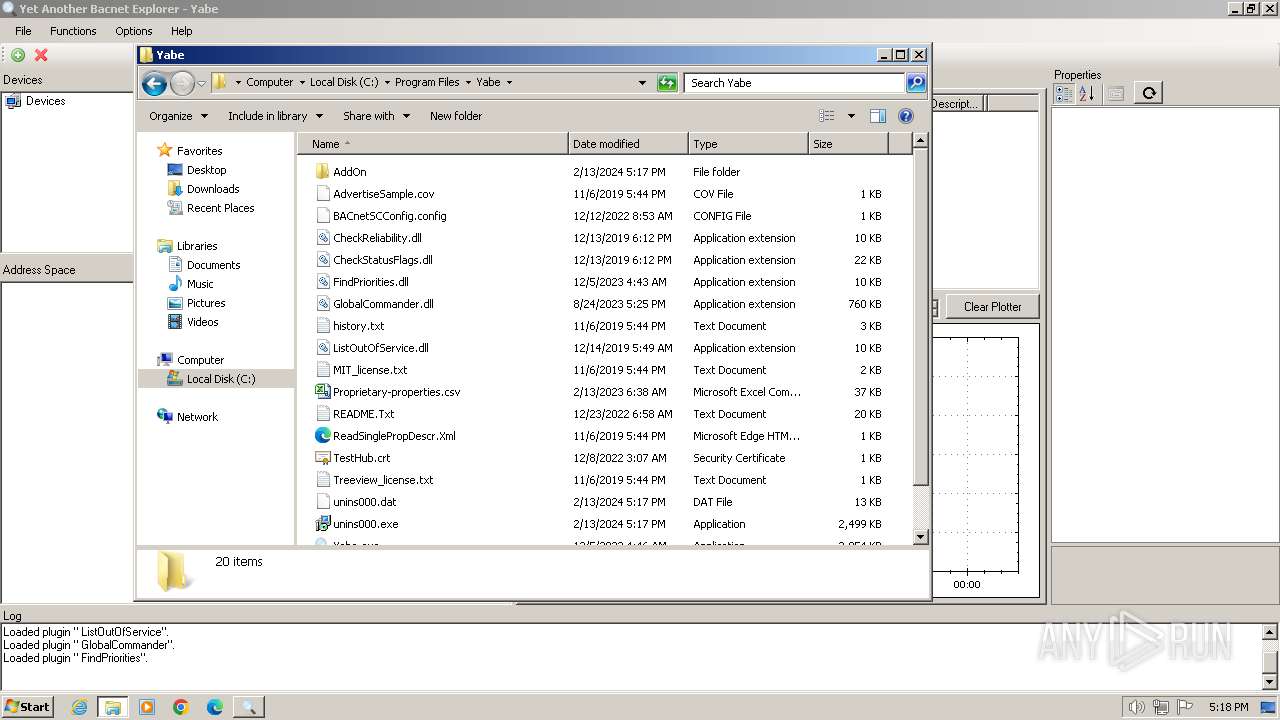
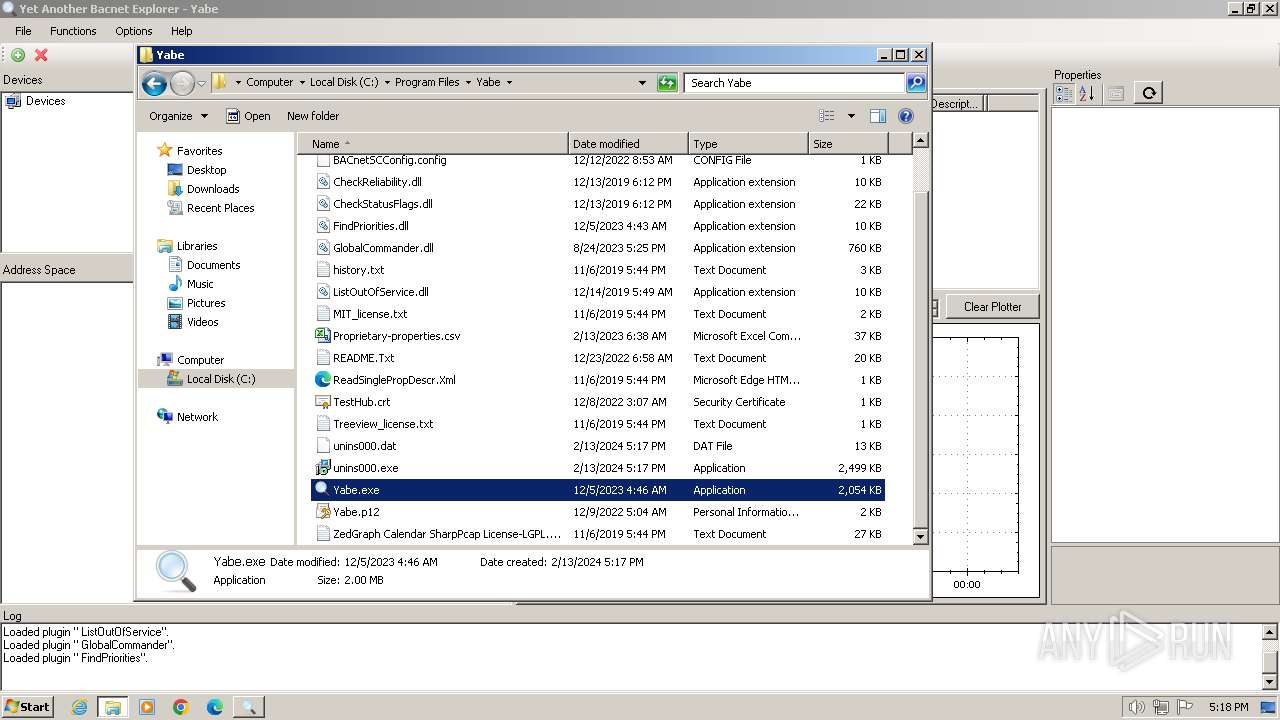
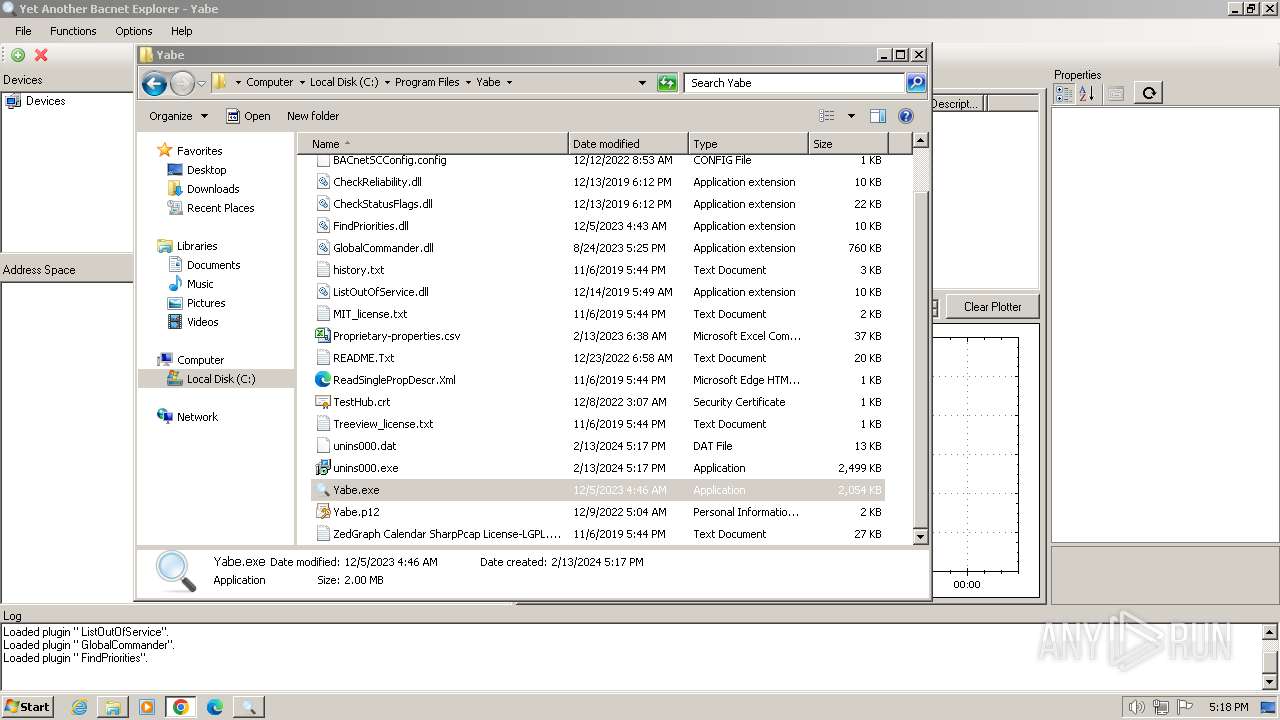
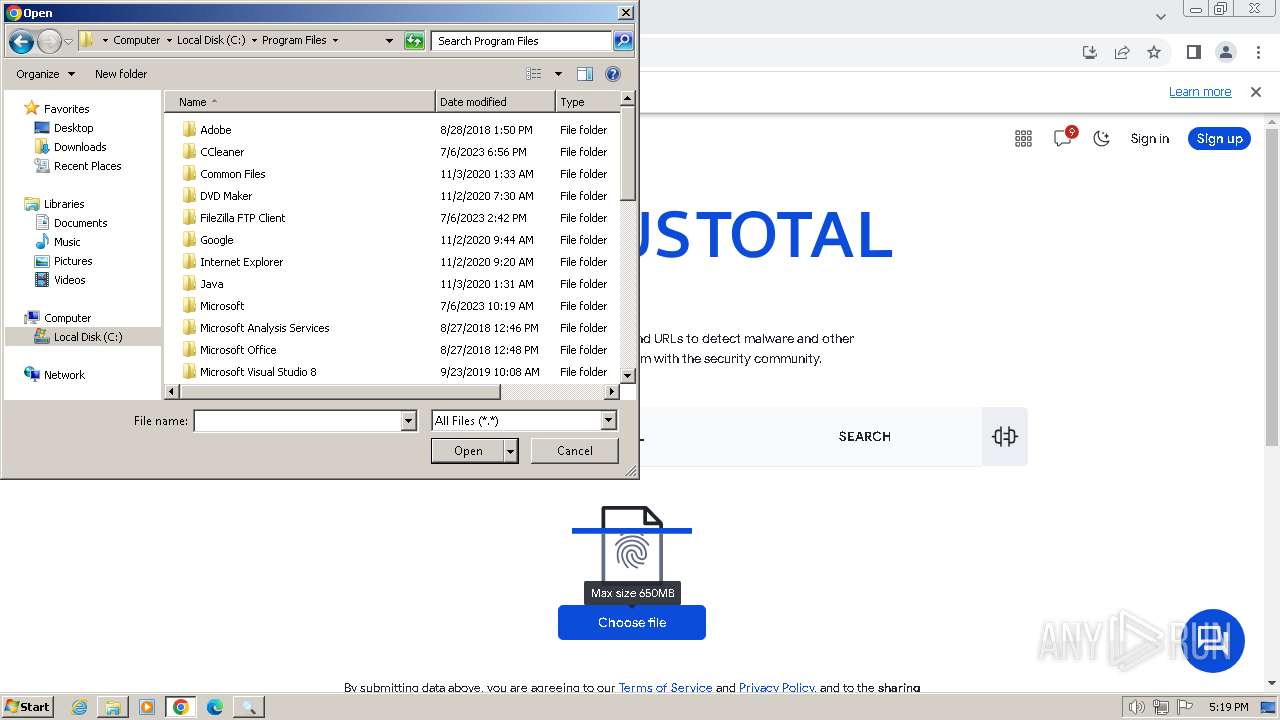
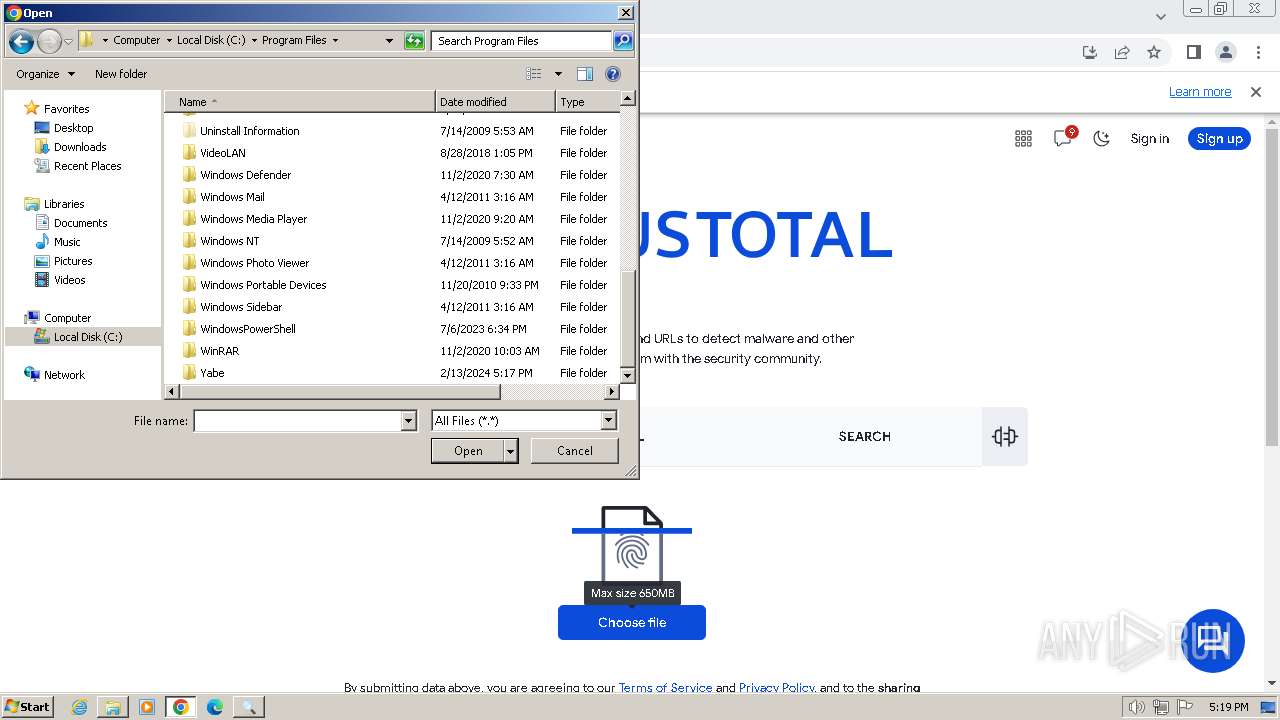
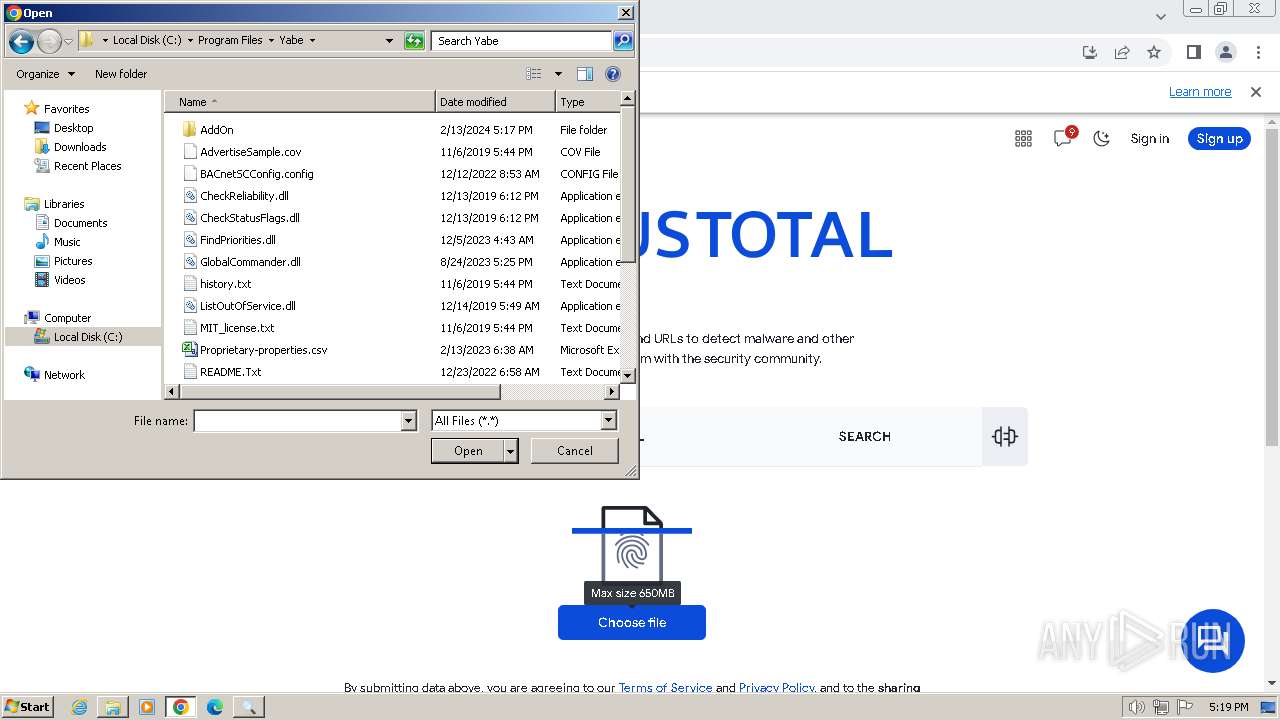
Creates files in the program directory
- SetupYabe_v1.3.2.tmp (PID: 2840)
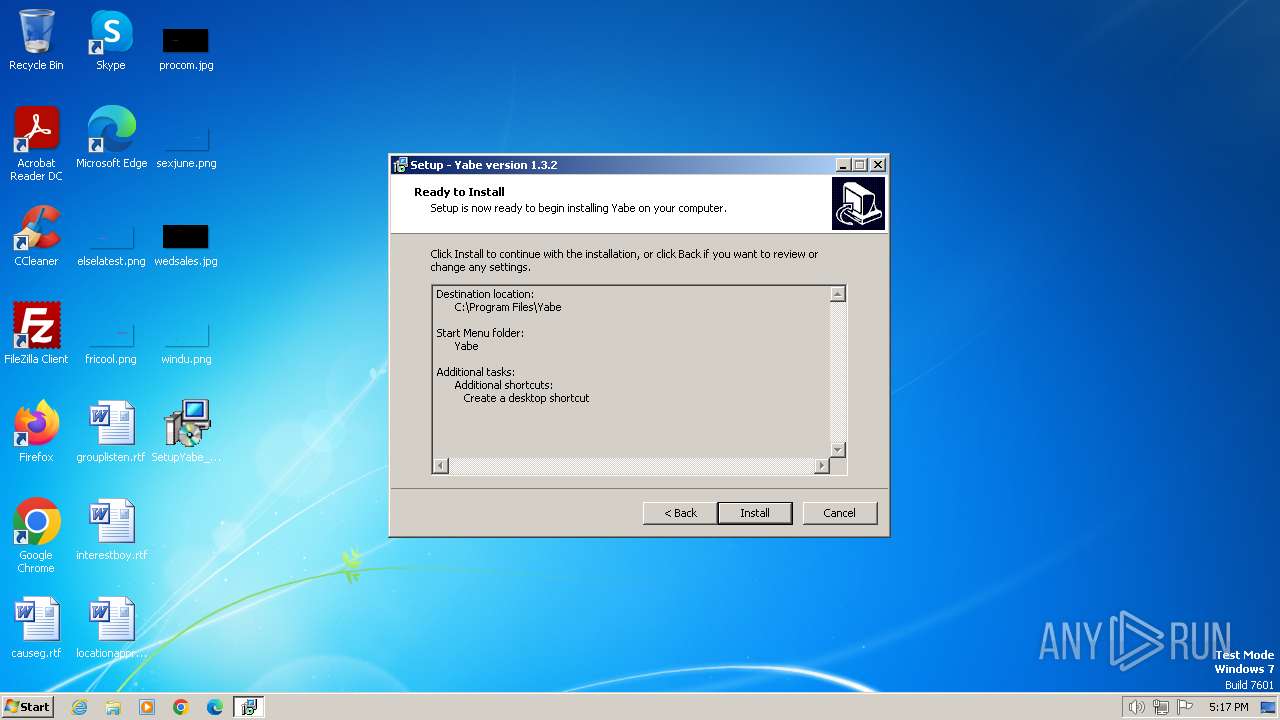
Creates a software uninstall entry
- SetupYabe_v1.3.2.tmp (PID: 2840)
Reads the machine GUID from the registry
- Yabe.exe (PID: 2232)
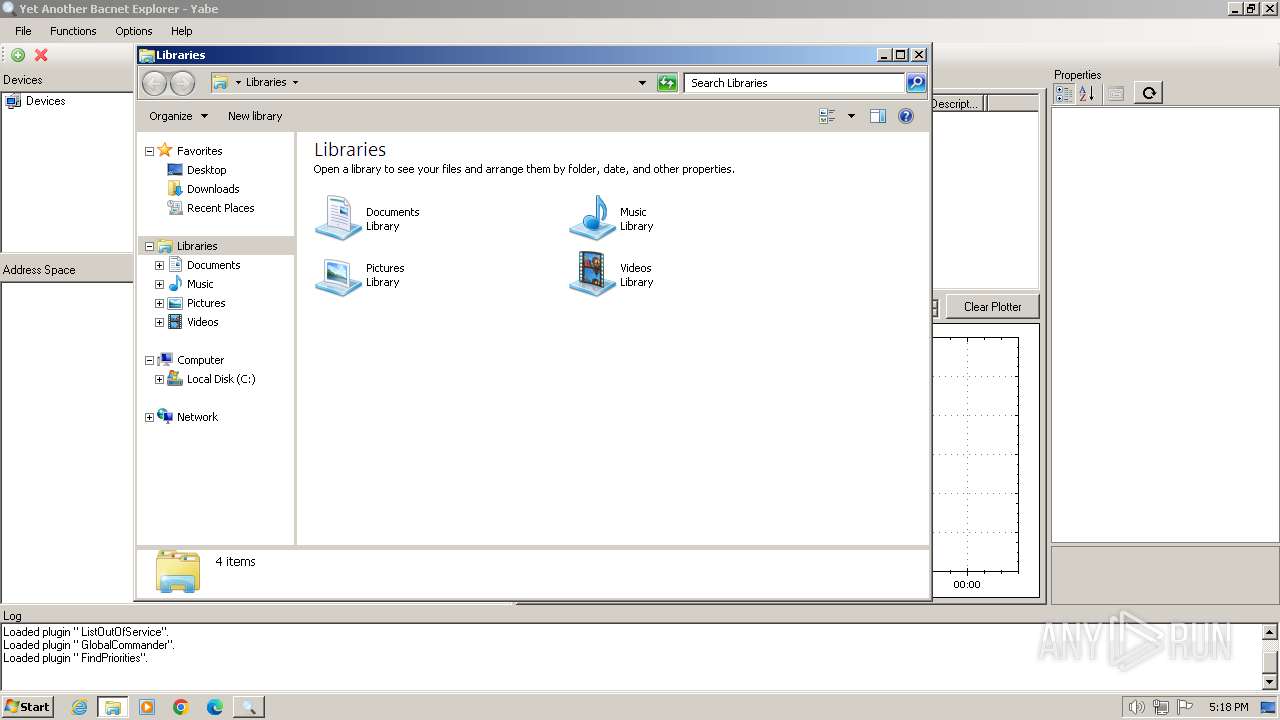
Manual execution by a user
- explorer.exe (PID: 2420)
- chrome.exe (PID: 2336)
Creates files or folders in the user directory
- Yabe.exe (PID: 2232)
Application launched itself
- chrome.exe (PID: 2336)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (51.8) |
|---|---|---|
| .exe | | | InstallShield setup (20.3) |
| .exe | | | Win32 EXE PECompact compressed (generic) (19.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.1) |
| .exe | | | Win32 Executable (generic) (2.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:10:12 11:15:57+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 682496 |
| InitializedDataSize: | 37888 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa7ed0 |
| OSVersion: | 6 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
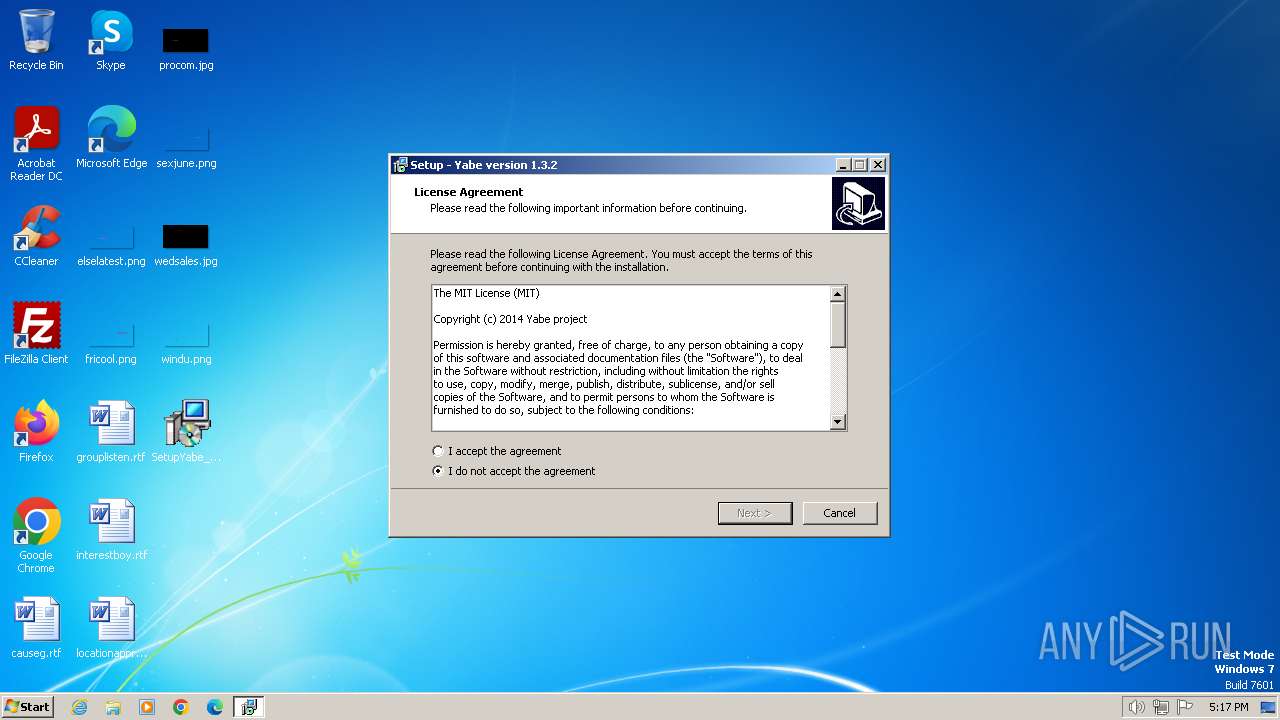
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Yabe Authors |
| FileDescription: | Yabe Setup |
| FileVersion: | |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | Yabe |
| ProductVersion: | 1.3.2 |
Total processes
72
Monitored processes
27
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3492 --field-trial-handle=1184,i,413730779291301526,14612731523626139068,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1664 --field-trial-handle=1184,i,413730779291301526,14612731523626139068,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2128 --field-trial-handle=1184,i,413730779291301526,14612731523626139068,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=2444 --field-trial-handle=1184,i,413730779291301526,14612731523626139068,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3580 --field-trial-handle=1184,i,413730779291301526,14612731523626139068,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1112 --field-trial-handle=1184,i,413730779291301526,14612731523626139068,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1584 --field-trial-handle=1184,i,413730779291301526,14612731523626139068,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=1456 --field-trial-handle=1184,i,413730779291301526,14612731523626139068,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1776 | "C:\Users\admin\Desktop\SetupYabe_v1.3.2.exe" /SPAWNWND=$18013E /NOTIFYWND=$E0170 | C:\Users\admin\Desktop\SetupYabe_v1.3.2.exe | SetupYabe_v1.3.2.tmp | ||||||||||||
User: admin Company: Yabe Authors Integrity Level: HIGH Description: Yabe Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1736 --field-trial-handle=1184,i,413730779291301526,14612731523626139068,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
20 628
Read events
20 334
Write events
281
Delete events
13
Modification events
| (PID) Process: | (2840) SetupYabe_v1.3.2.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 180B0000CADA848CA05EDA01 | |||
| (PID) Process: | (2840) SetupYabe_v1.3.2.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 3BEE88DAB973D63F2AB4A25F32F17060EE1FB4AD9CC4C8362E0D6433E77C50F9 | |||
| (PID) Process: | (2840) SetupYabe_v1.3.2.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2840) SetupYabe_v1.3.2.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\Yabe\Yabe.exe | |||
| (PID) Process: | (2840) SetupYabe_v1.3.2.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 12279B9B8C64A0978A7450F99AFC4195B720FBC34B3845B2E91A86B46F9165D0 | |||
| (PID) Process: | (2840) SetupYabe_v1.3.2.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{F8639277-80EB-4EC9-AE36-D4BF2115ABFA}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.0.3 (u) | |||
| (PID) Process: | (2840) SetupYabe_v1.3.2.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{F8639277-80EB-4EC9-AE36-D4BF2115ABFA}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\Yabe | |||
| (PID) Process: | (2840) SetupYabe_v1.3.2.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{F8639277-80EB-4EC9-AE36-D4BF2115ABFA}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Yabe\ | |||
| (PID) Process: | (2840) SetupYabe_v1.3.2.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{F8639277-80EB-4EC9-AE36-D4BF2115ABFA}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: Yabe | |||
| (PID) Process: | (2840) SetupYabe_v1.3.2.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{F8639277-80EB-4EC9-AE36-D4BF2115ABFA}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
Executable files
29
Suspicious files
101
Text files
75
Unknown types
70
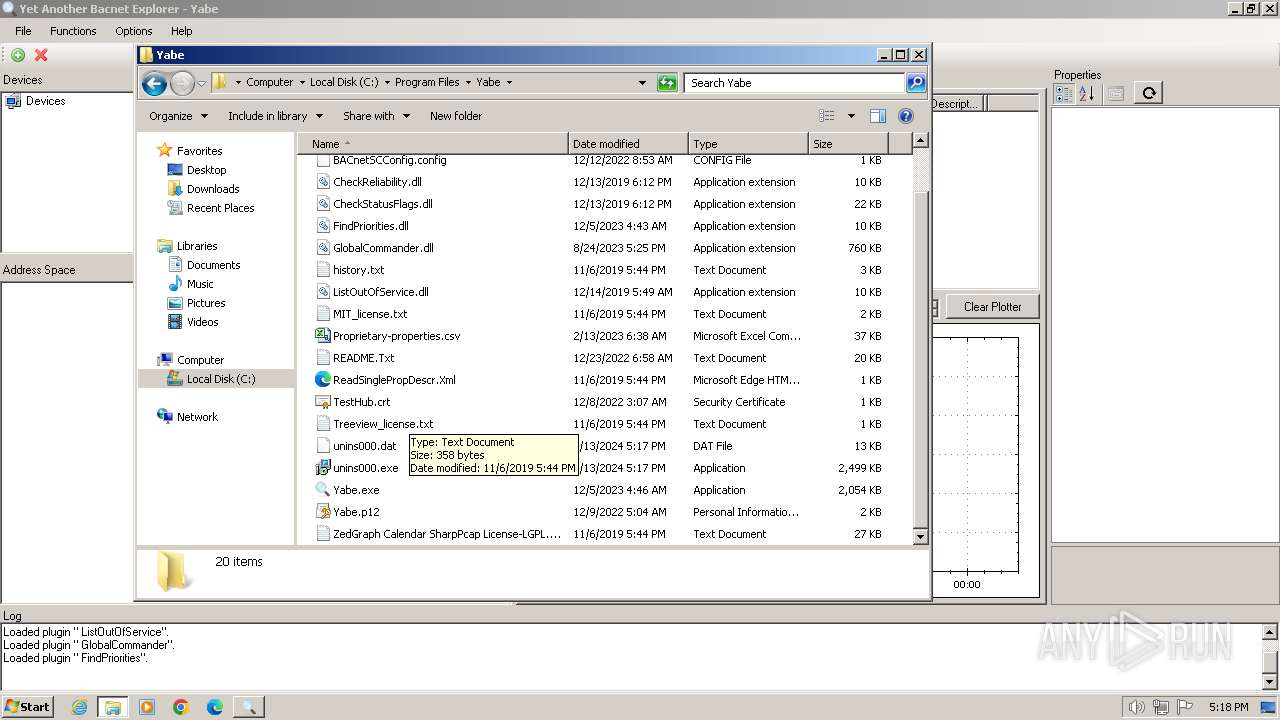
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2840 | SetupYabe_v1.3.2.tmp | C:\Program Files\Yabe\CheckStatusFlags.dll | executable | |
MD5:E27119029BD903EBC029D9022F09C92F | SHA256:60414AE77C965B8358AEB5E298272C24B38535316AEFC7C1309B027F187785EA | |||
| 3240 | SetupYabe_v1.3.2.exe | C:\Users\admin\AppData\Local\Temp\is-GO72O.tmp\SetupYabe_v1.3.2.tmp | executable | |
MD5:84DB4B4205F705DA71471DC6ECC061F5 | SHA256:647983EBDE53E0501FF1AF8EF6190DFEEA5CCC64CAF7DCE808F1E3D98FB66A3C | |||
| 2840 | SetupYabe_v1.3.2.tmp | C:\Program Files\Yabe\unins000.exe | executable | |
MD5:1518B6920374597F25DB89C77FB4B966 | SHA256:29D8D55F3DBEA7EF53C37871B7611E0BB7410933AE4E0AF8C69CD56217AA29A6 | |||
| 1776 | SetupYabe_v1.3.2.exe | C:\Users\admin\AppData\Local\Temp\is-RA8VP.tmp\SetupYabe_v1.3.2.tmp | executable | |
MD5:84DB4B4205F705DA71471DC6ECC061F5 | SHA256:647983EBDE53E0501FF1AF8EF6190DFEEA5CCC64CAF7DCE808F1E3D98FB66A3C | |||
| 2840 | SetupYabe_v1.3.2.tmp | C:\Program Files\Yabe\is-M01SM.tmp | executable | |
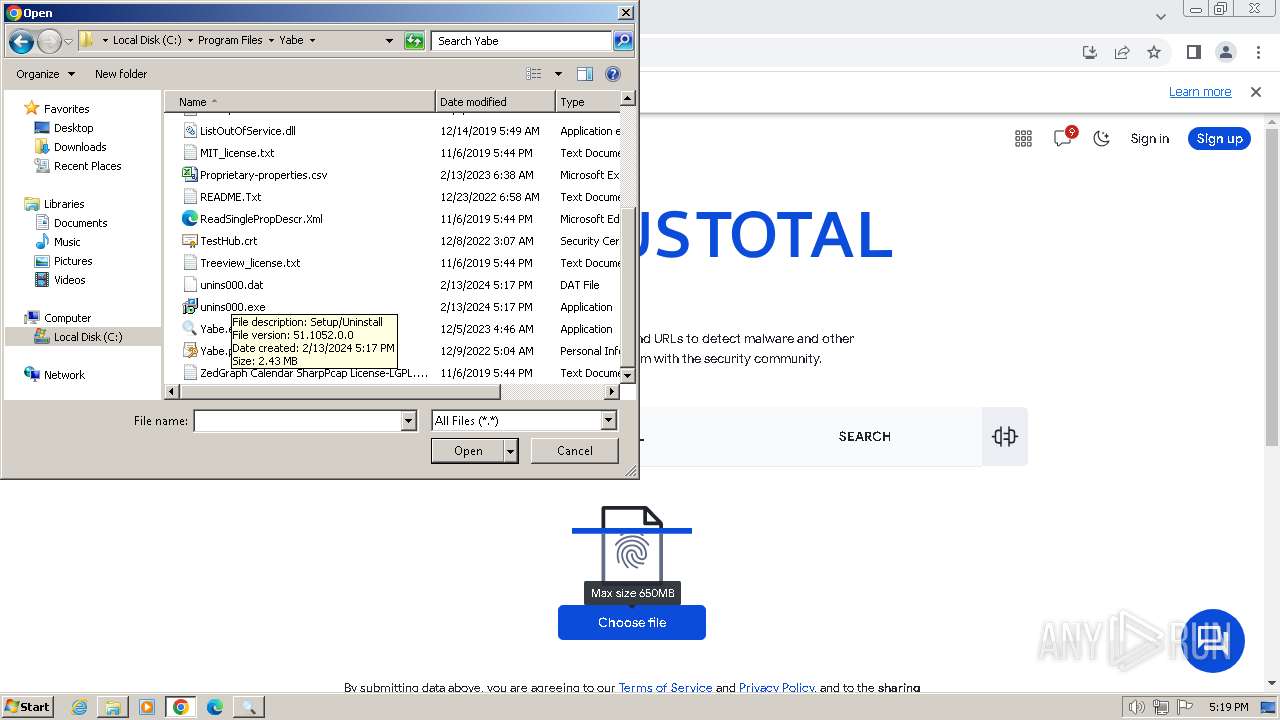
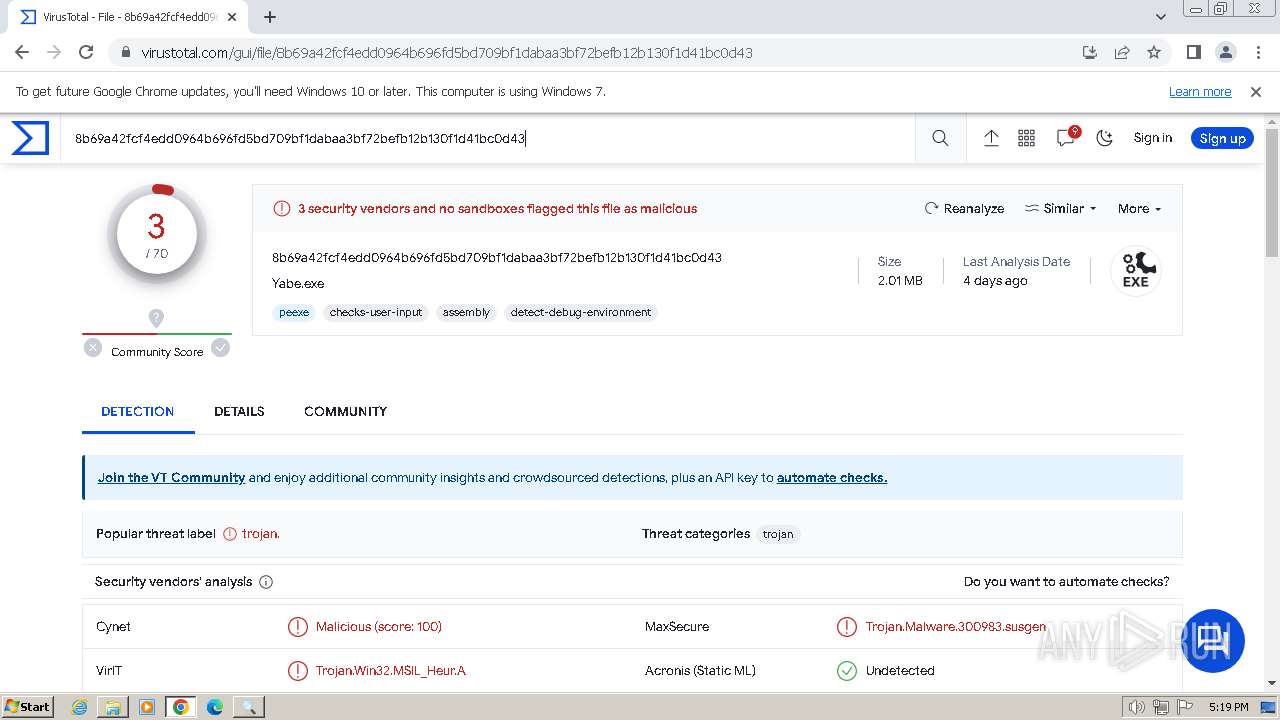
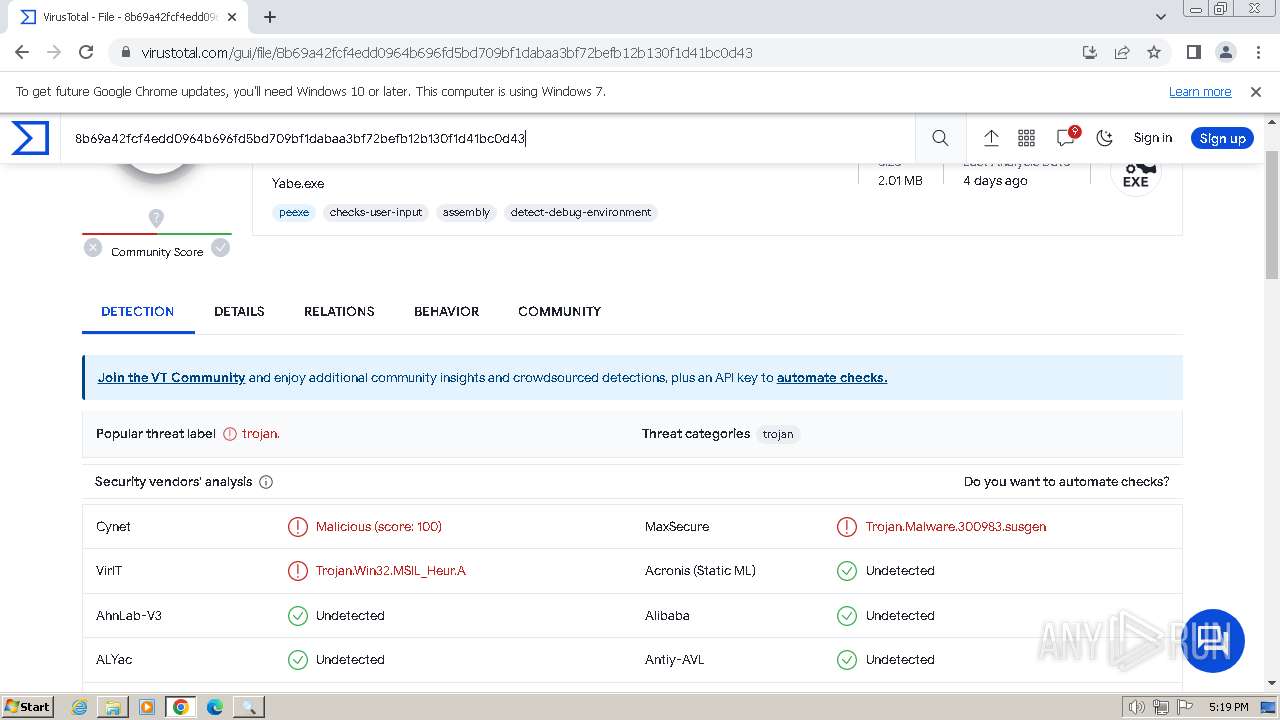
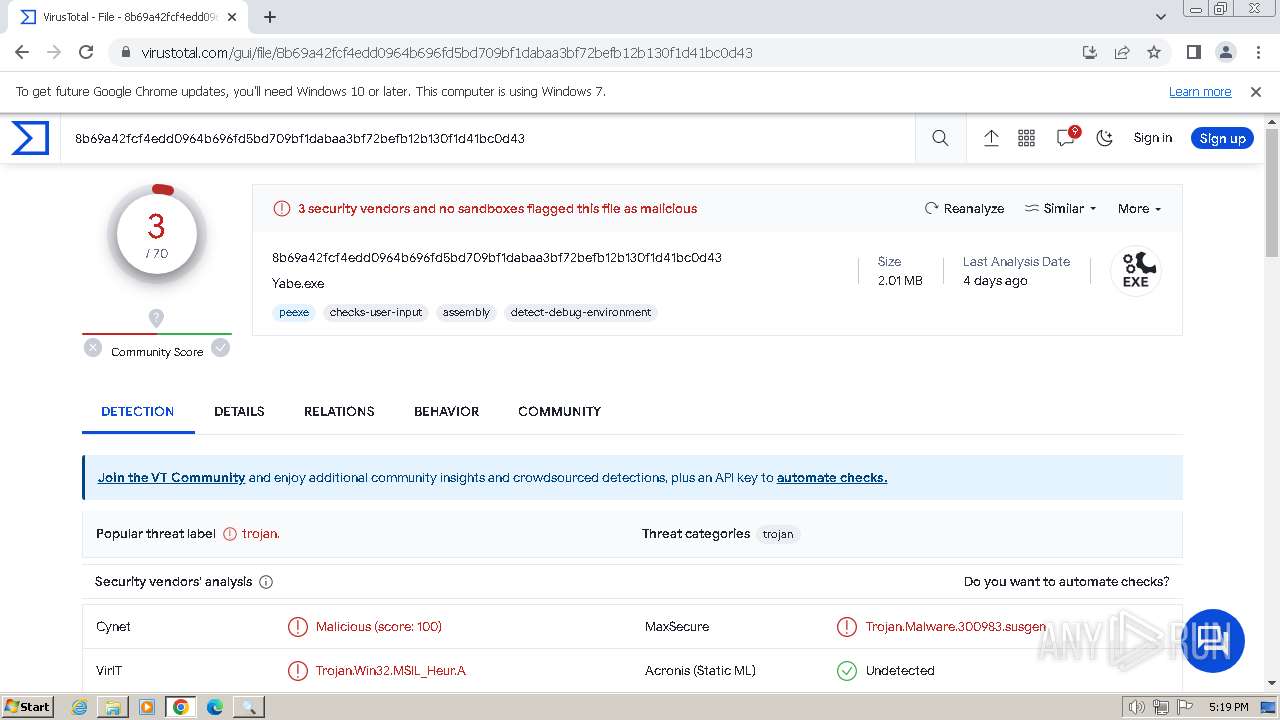
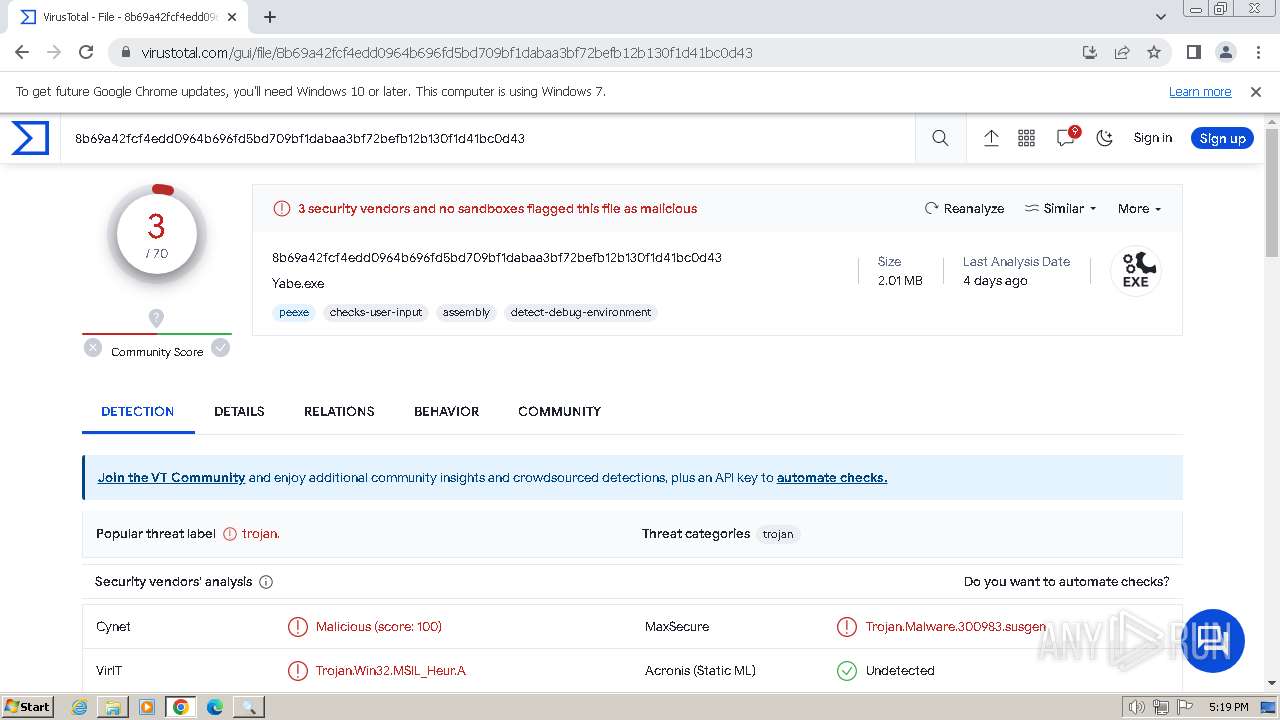
MD5:AD8A921252ED3F7B61F5275B03E8E853 | SHA256:8B69A42FCF4EDD0964B696FD5BD709BF1DABAA3BF72BEFB12B130F1D41BC0D43 | |||
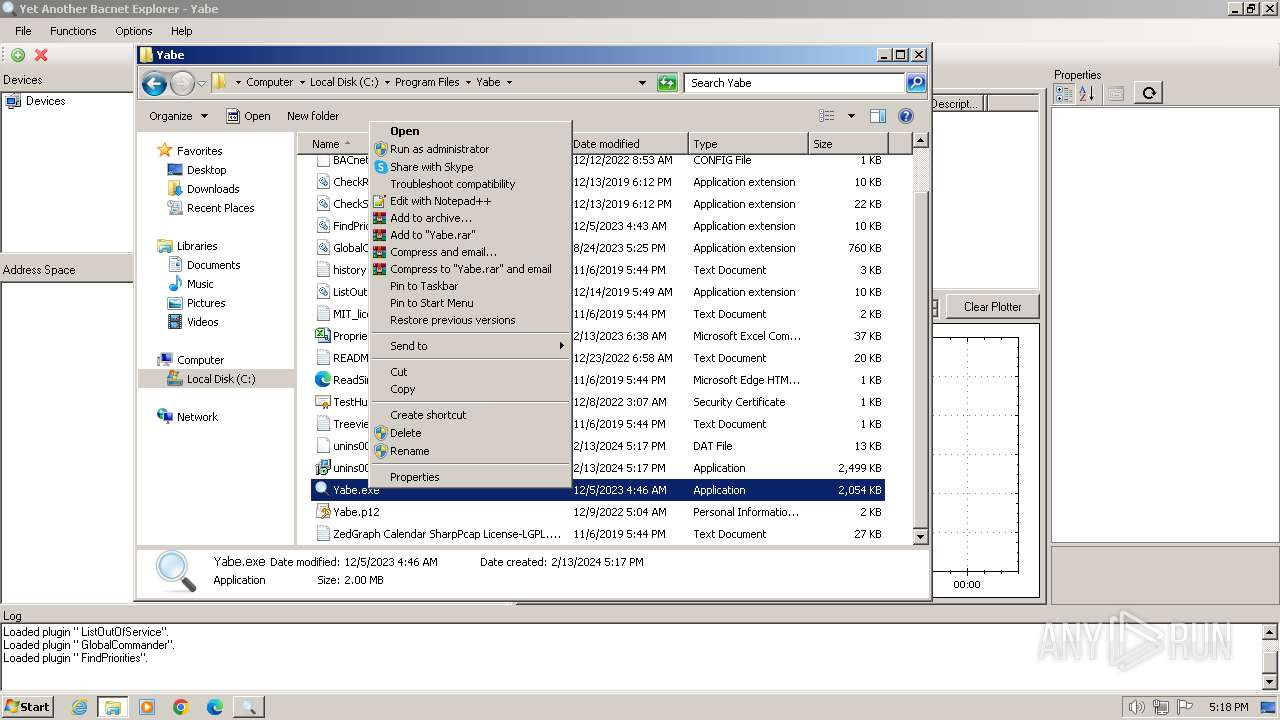
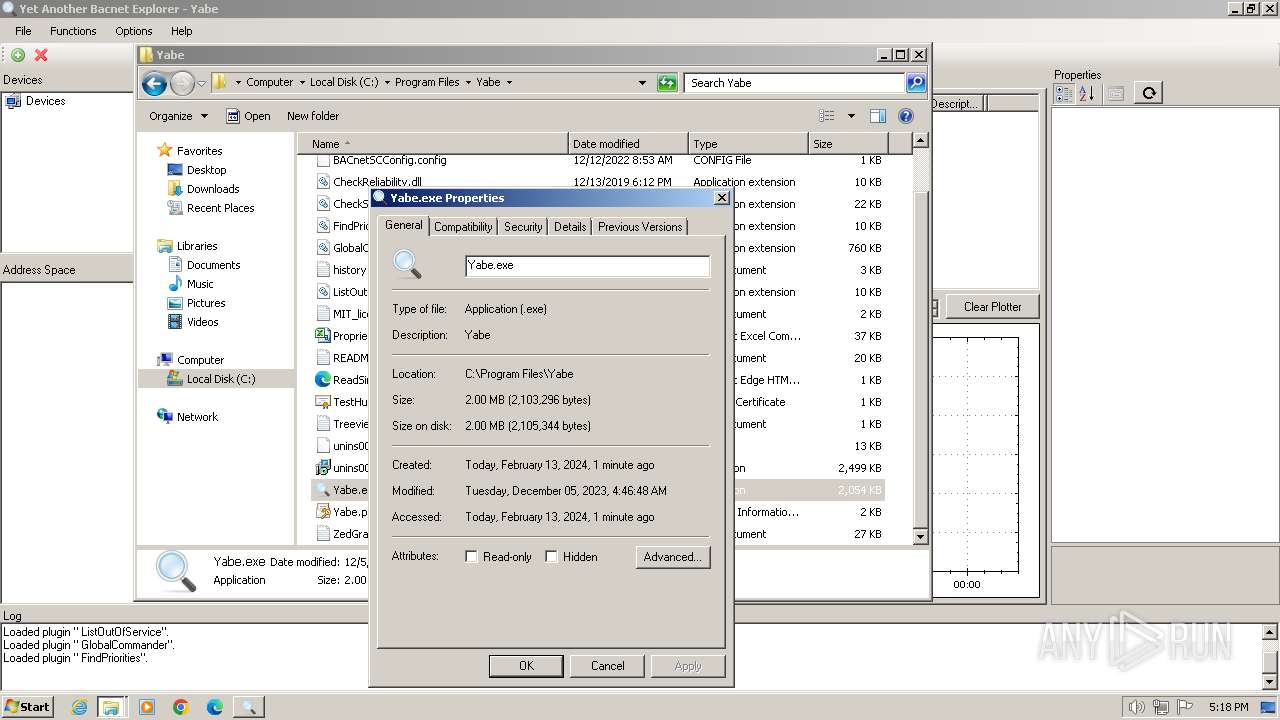
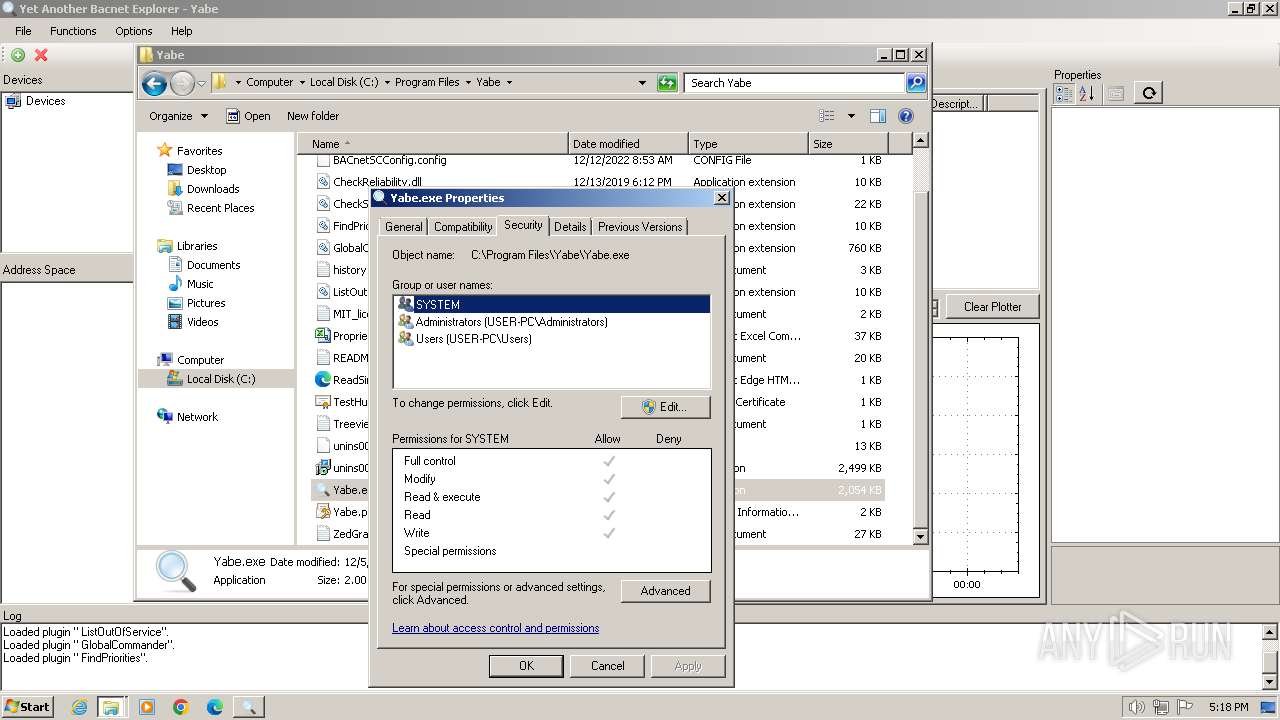
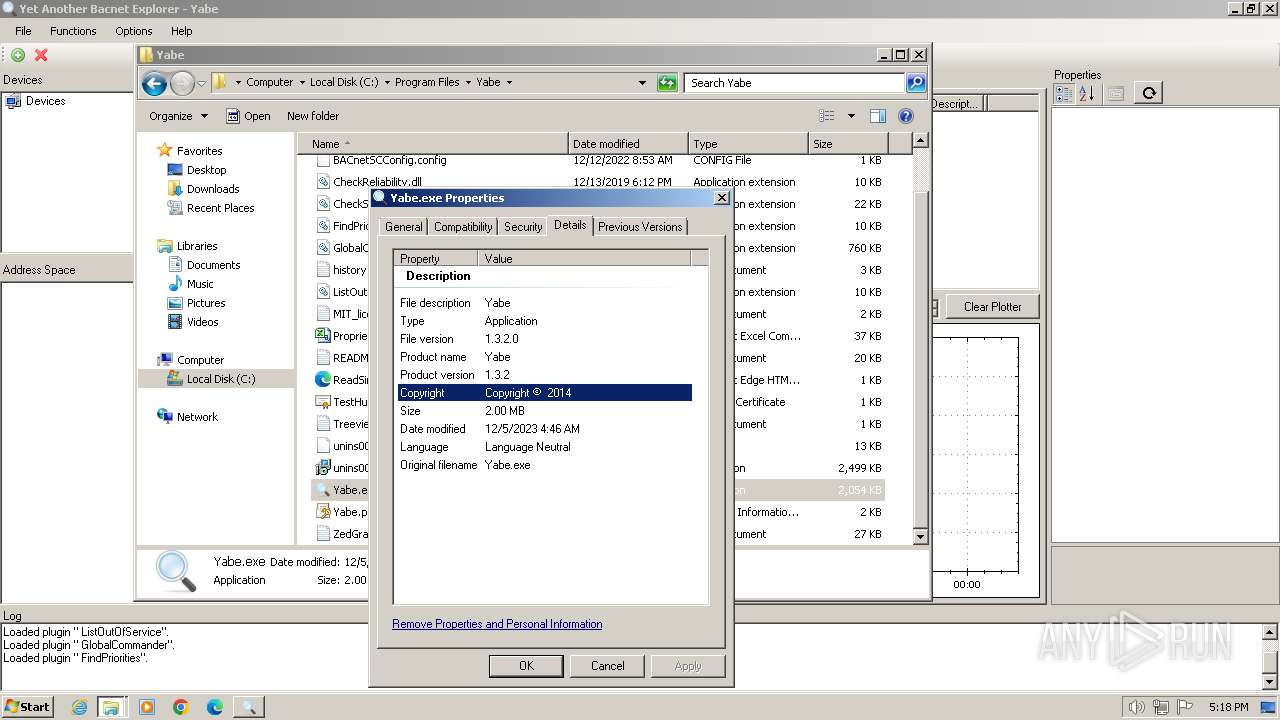
| 2840 | SetupYabe_v1.3.2.tmp | C:\Program Files\Yabe\Yabe.exe | executable | |
MD5:AD8A921252ED3F7B61F5275B03E8E853 | SHA256:8B69A42FCF4EDD0964B696FD5BD709BF1DABAA3BF72BEFB12B130F1D41BC0D43 | |||
| 2840 | SetupYabe_v1.3.2.tmp | C:\Program Files\Yabe\is-UHC0G.tmp | executable | |
MD5:1518B6920374597F25DB89C77FB4B966 | SHA256:29D8D55F3DBEA7EF53C37871B7611E0BB7410933AE4E0AF8C69CD56217AA29A6 | |||
| 2840 | SetupYabe_v1.3.2.tmp | C:\Program Files\Yabe\ListOutOfService.dll | executable | |
MD5:66CDCDD23CAEA81BEDB146FF8CF93FEE | SHA256:3E7CDF1382CBC8CC54F430EDF8CCCC2B1638E12AB7DC635B751BFBFE8C510A3E | |||
| 2840 | SetupYabe_v1.3.2.tmp | C:\Program Files\Yabe\is-V018B.tmp | executable | |
MD5:E27119029BD903EBC029D9022F09C92F | SHA256:60414AE77C965B8358AEB5E298272C24B38535316AEFC7C1309B027F187785EA | |||
| 2840 | SetupYabe_v1.3.2.tmp | C:\Program Files\Yabe\is-0PL6T.tmp | executable | |
MD5:786E9F795818CAF58921B825E73D70E0 | SHA256:8B33650483CEDF0D555278507F758B0EFA2A9FCE8CE5A3D5980E8CB0A35CC652 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
45
DNS requests
53
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acs7jwb4vh357wtsxdlrthyegyqq_2023.11.27.1202/ggkkehgbnfjpeggfpleeakpidbkibbmn_2023.11.27.1202_all_admxda2vchtoykhnnwzdlbnqqt6a.crx3 | US | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adtp63xadzqu6yysjolme33hjxoq_20220505/dhlpobdgcjafebgbbhjdnapejmpkgiie_20220505_all_adfdqqtvlhuhhtrt6irlkpynghca.crx3 | US | binary | 21.8 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adtp63xadzqu6yysjolme33hjxoq_20220505/dhlpobdgcjafebgbbhjdnapejmpkgiie_20220505_all_adfdqqtvlhuhhtrt6irlkpynghca.crx3 | US | binary | 53.2 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adtp63xadzqu6yysjolme33hjxoq_20220505/dhlpobdgcjafebgbbhjdnapejmpkgiie_20220505_all_adfdqqtvlhuhhtrt6irlkpynghca.crx3 | US | binary | 6.02 Kb | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adtp63xadzqu6yysjolme33hjxoq_20220505/dhlpobdgcjafebgbbhjdnapejmpkgiie_20220505_all_adfdqqtvlhuhhtrt6irlkpynghca.crx3 | US | — | — | unknown |
856 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acs7jwb4vh357wtsxdlrthyegyqq_2023.11.27.1202/ggkkehgbnfjpeggfpleeakpidbkibbmn_2023.11.27.1202_all_admxda2vchtoykhnnwzdlbnqqt6a.crx3 | US | binary | 8.68 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adtp63xadzqu6yysjolme33hjxoq_20220505/dhlpobdgcjafebgbbhjdnapejmpkgiie_20220505_all_adfdqqtvlhuhhtrt6irlkpynghca.crx3 | US | binary | 8.98 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adtp63xadzqu6yysjolme33hjxoq_20220505/dhlpobdgcjafebgbbhjdnapejmpkgiie_20220505_all_adfdqqtvlhuhhtrt6irlkpynghca.crx3 | US | binary | 28.6 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adtp63xadzqu6yysjolme33hjxoq_20220505/dhlpobdgcjafebgbbhjdnapejmpkgiie_20220505_all_adfdqqtvlhuhhtrt6irlkpynghca.crx3 | US | binary | 9.00 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adtp63xadzqu6yysjolme33hjxoq_20220505/dhlpobdgcjafebgbbhjdnapejmpkgiie_20220505_all_adfdqqtvlhuhhtrt6irlkpynghca.crx3 | US | binary | 8.28 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2172 | chrome.exe | 74.125.206.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
2336 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
2172 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
2172 | chrome.exe | 216.58.212.132:443 | www.google.com | GOOGLE | US | whitelisted |
2172 | chrome.exe | 142.250.186.163:443 | www.gstatic.com | GOOGLE | US | whitelisted |
2172 | chrome.exe | 142.250.185.110:443 | apis.google.com | GOOGLE | US | whitelisted |
2172 | chrome.exe | 142.250.184.206:443 | encrypted-tbn0.gstatic.com | GOOGLE | US | whitelisted |
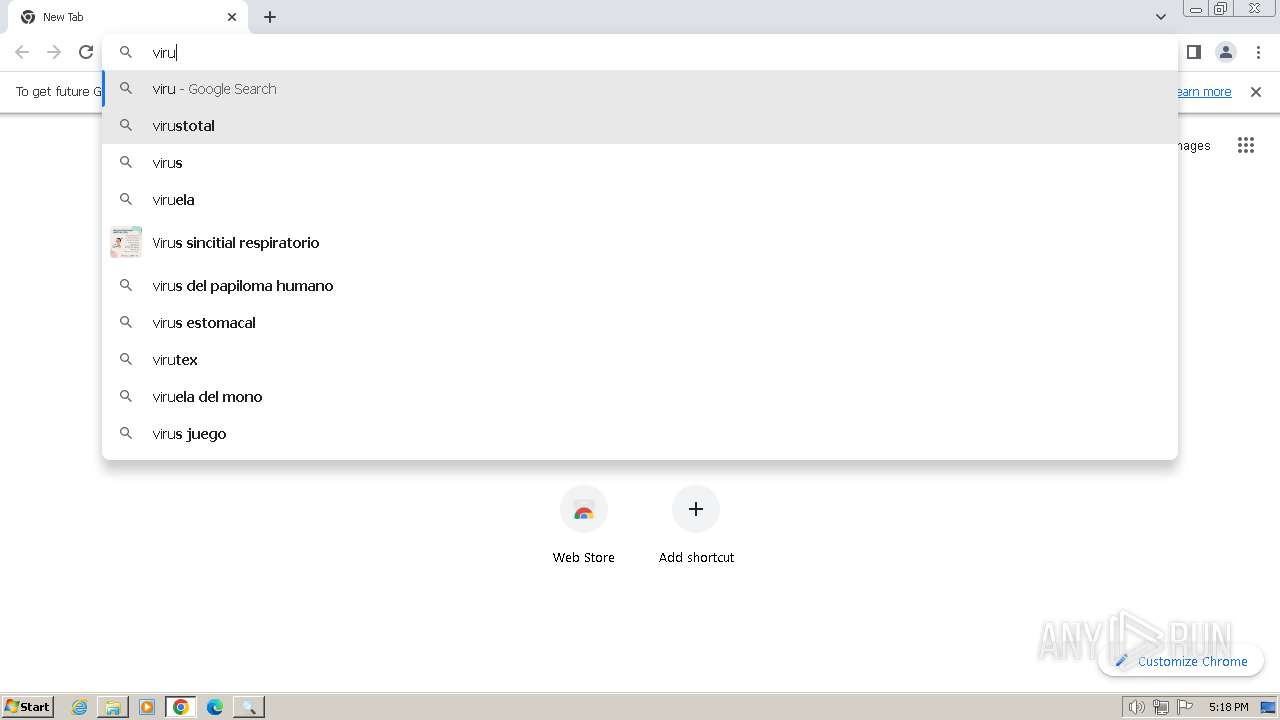
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
www.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
virustotal.com |
| whitelisted |
www.virustotal.com |
| whitelisted |
www.recaptcha.net |
| whitelisted |
Threats
Process | Message |
|---|---|
Yabe.exe | Loaded plugin " CheckStatusFlags".
|
Yabe.exe | Loaded plugin "CheckReliability".
|
Yabe.exe | Loaded plugin " FindPriorities".
|
Yabe.exe | Loaded plugin " ListOutOfService".
|
Yabe.exe | Loaded plugin " GlobalCommander".
|