| download: | 2.exe |
| Full analysis: | https://app.any.run/tasks/eacaa20e-1958-48c2-ba3f-b9b148047297 |
| Verdict: | Malicious activity |
| Analysis date: | September 03, 2019, 13:13:12 |
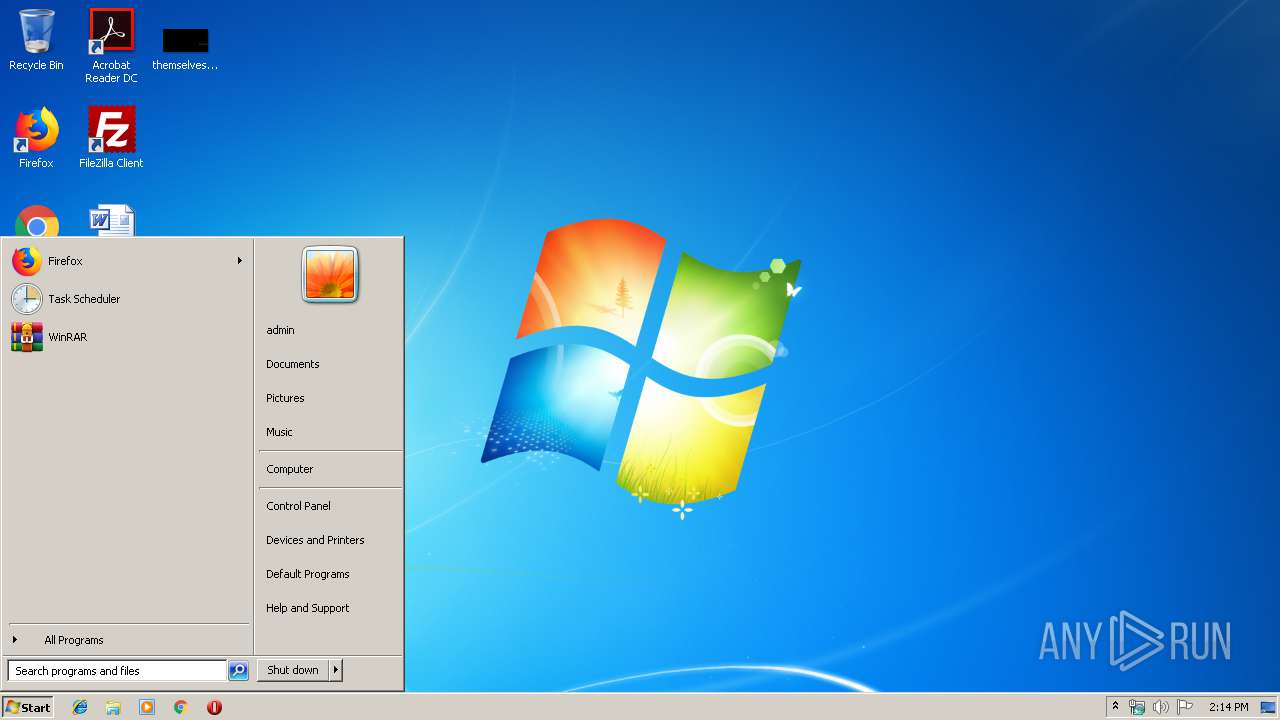
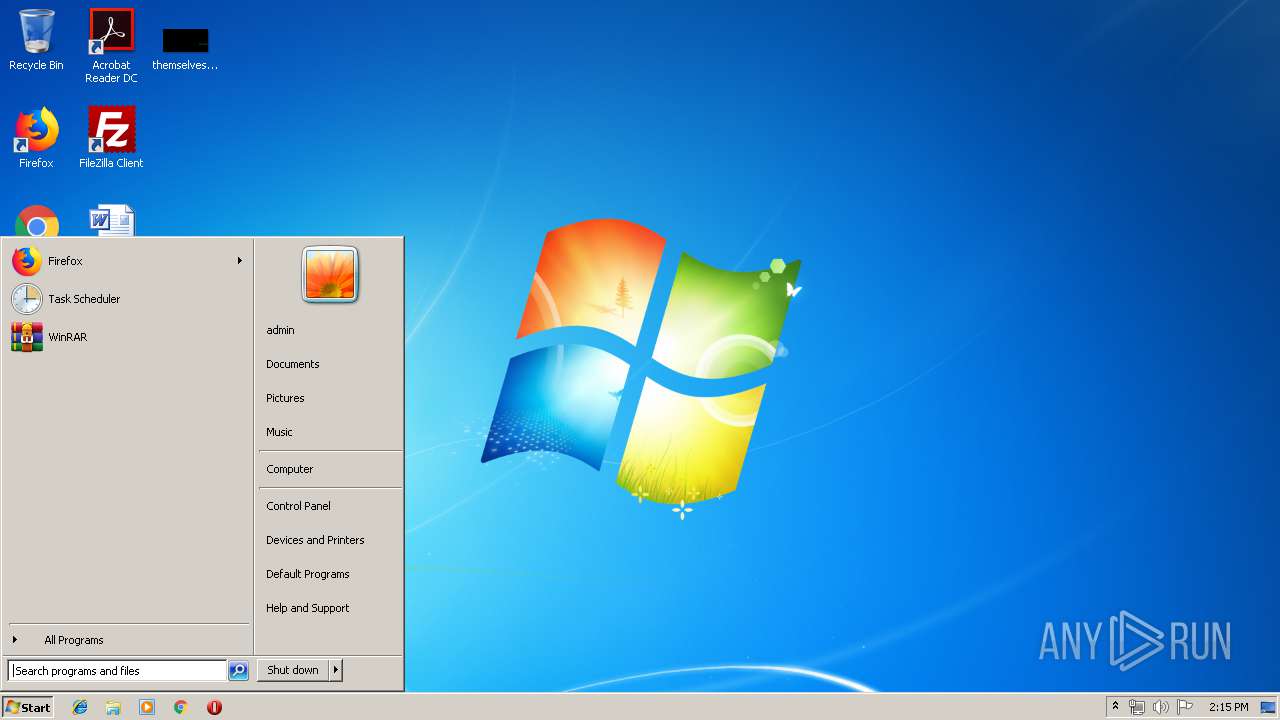
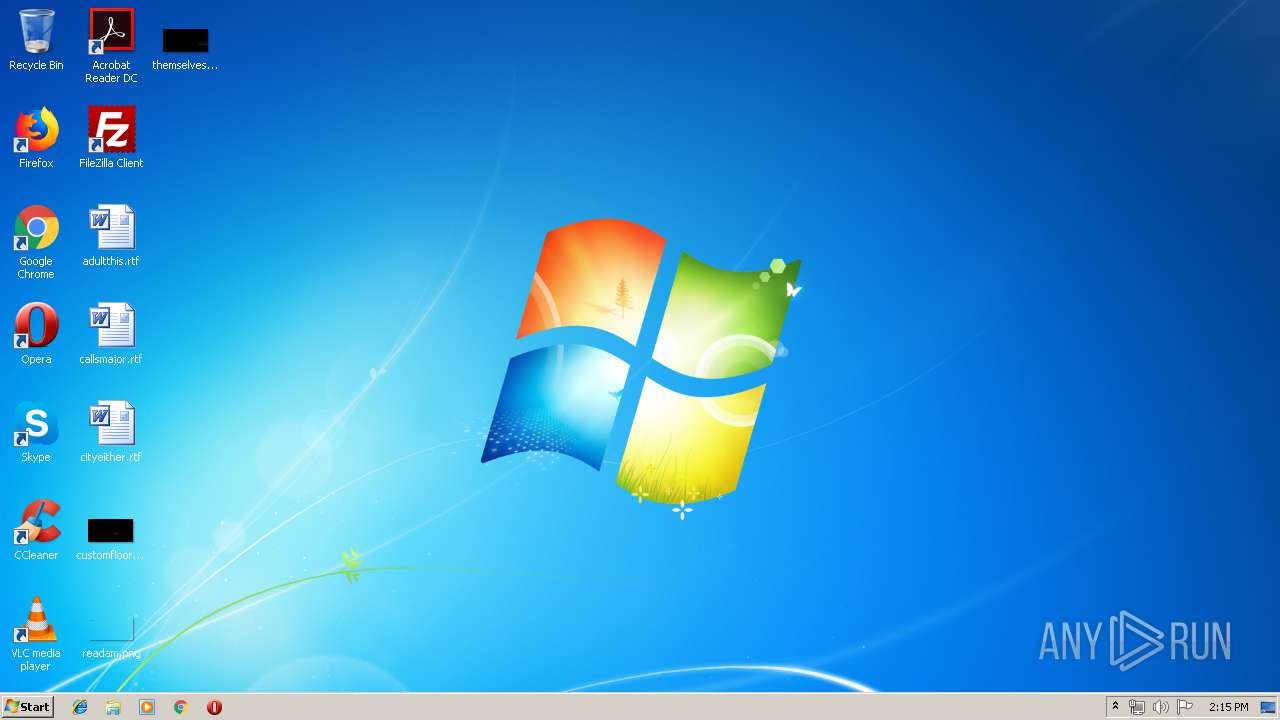
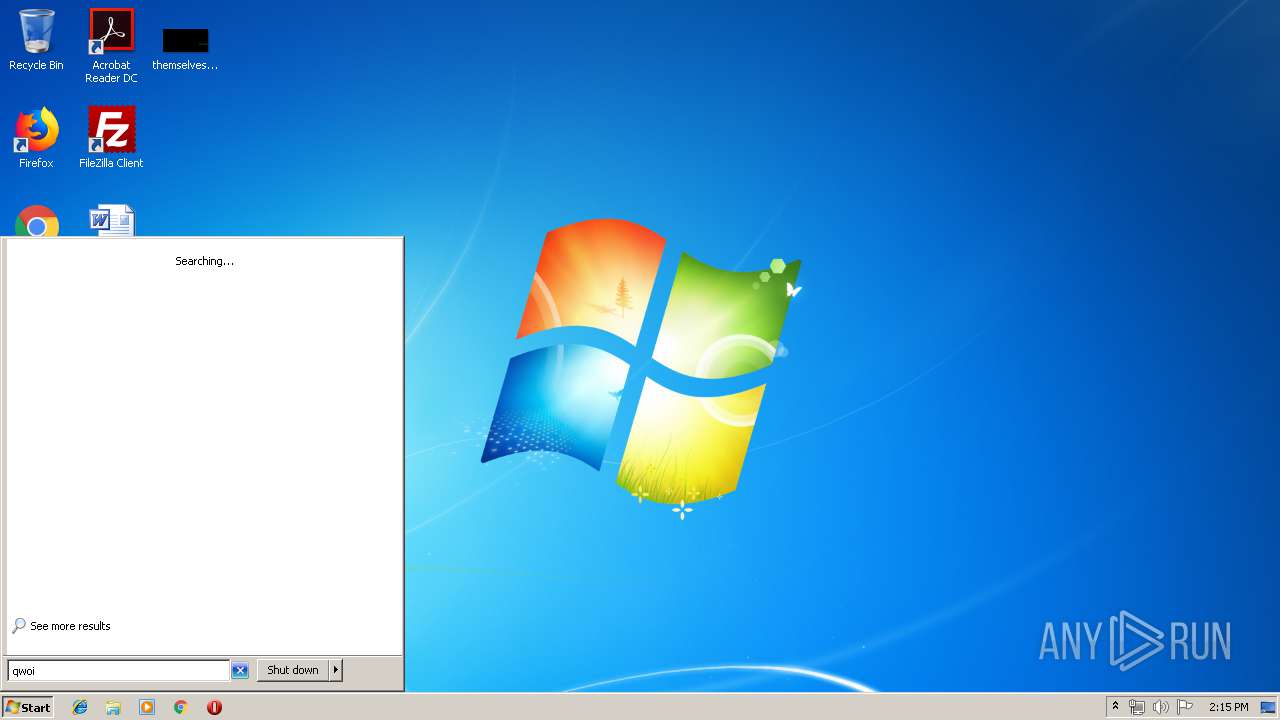
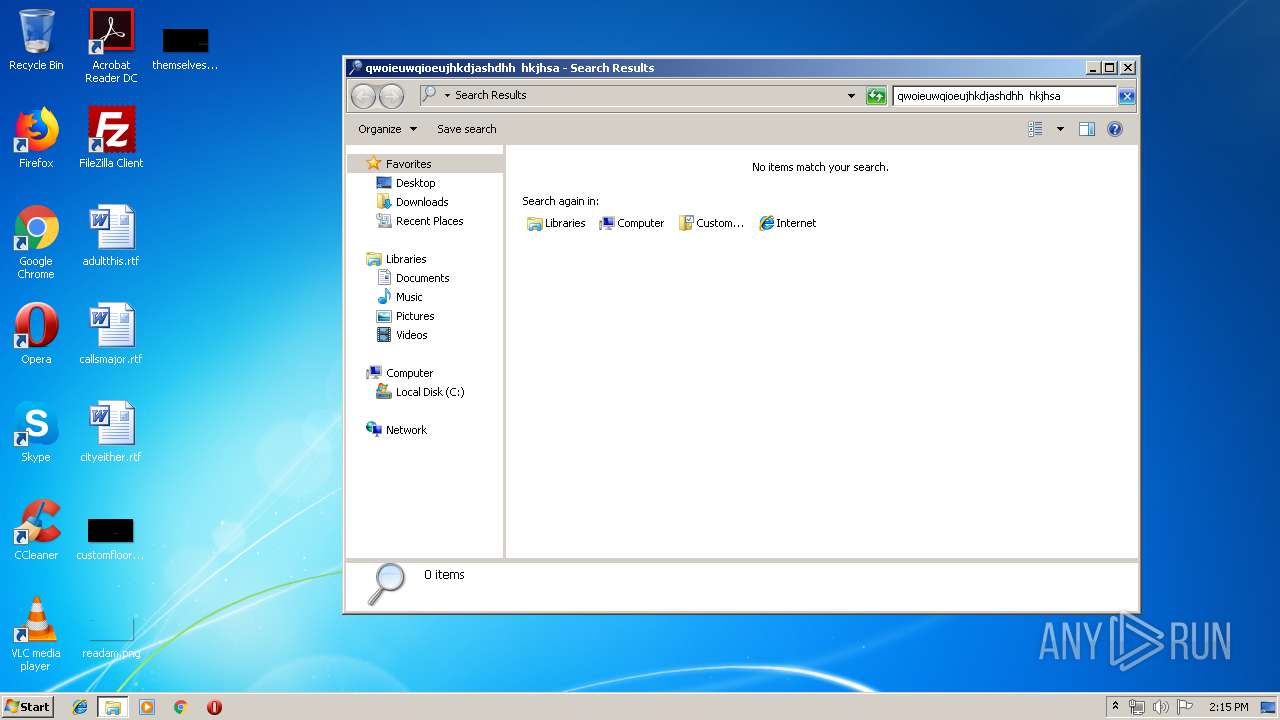
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | B1230834266597725156B77B7DE77C7D |
| SHA1: | 8ACF3C6E3ED84A4936E58F61B46C71ECA421D917 |
| SHA256: | 68D39CD88E7B991D5C420C7011064480C4AC28BF9185FA1C9E8FF3575F0193D4 |
| SSDEEP: | 12288:bl6R/oMveAXXlJpjxfp6KXj2A9DvbxtvvK1/VJ/r2Yb:4lde65jxfp6KT2UDvbxtvK1/VJyY |
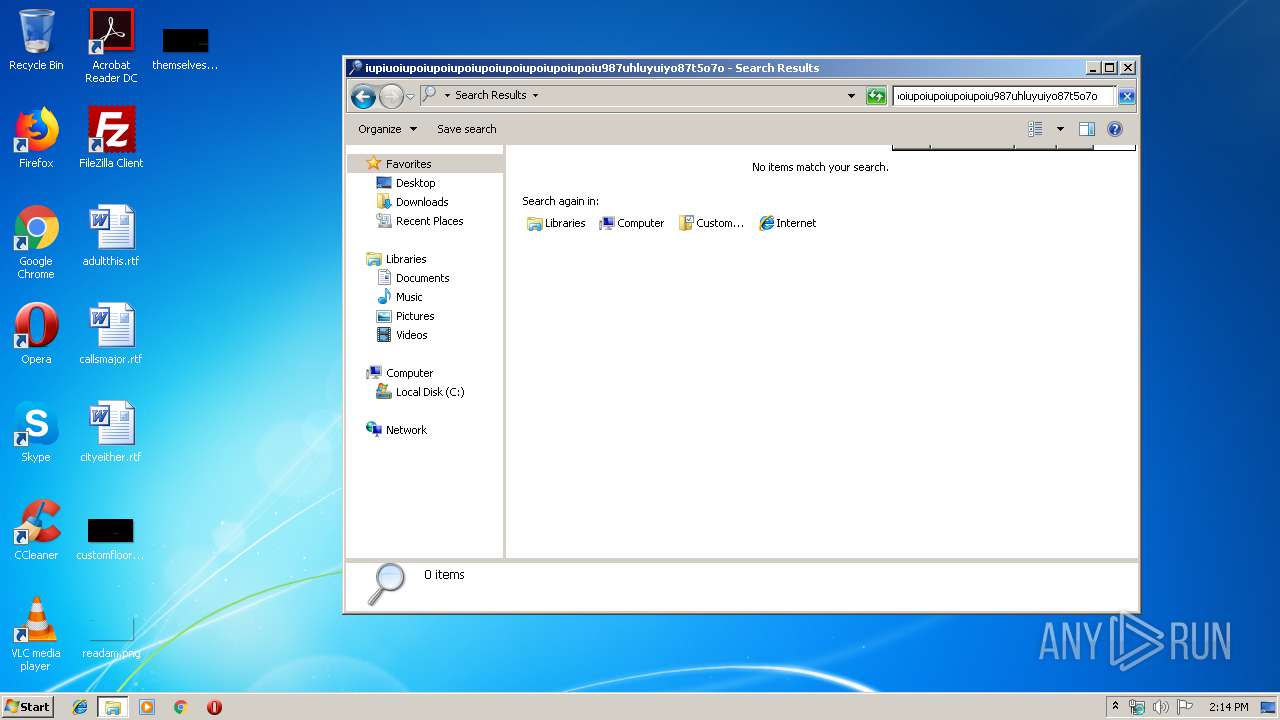
MALICIOUS
Runs PING.EXE for delay simulation
- cmd.exe (PID: 3160)
- cmd.exe (PID: 2304)
- cmd.exe (PID: 4020)
- cmd.exe (PID: 3924)
Application was dropped or rewritten from another process
- jusched.exe (PID: 2580)
- jusched.exe (PID: 3488)
Changes the autorun value in the registry
- jusched.exe (PID: 3488)
SUSPICIOUS
Executable content was dropped or overwritten
- 2.exe (PID: 3644)
- 52Ie495ivrL.exe (PID: 2436)
Starts itself from another location
- 2.exe (PID: 3644)
Application launched itself
- 52Ie495ivrL.exe (PID: 3560)
- jusched.exe (PID: 2580)
Uses NETSTAT.EXE to discover network connections
- cmd.exe (PID: 2392)
- cmd.exe (PID: 3532)
Starts CMD.EXE for commands execution
- 2.exe (PID: 3644)
- 52Ie495ivrL.exe (PID: 2436)
- jusched.exe (PID: 3488)
Creates files in the program directory
- 2.exe (PID: 3644)
- 52Ie495ivrL.exe (PID: 2436)
- jusched.exe (PID: 3488)
Uses TASKLIST.EXE to query information about running processes
- cmd.exe (PID: 3632)
- cmd.exe (PID: 3332)
Uses ICACLS.EXE to modify access control list
- cmd.exe (PID: 1000)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3684)
Creates files in the user directory
- jusched.exe (PID: 3488)
INFO
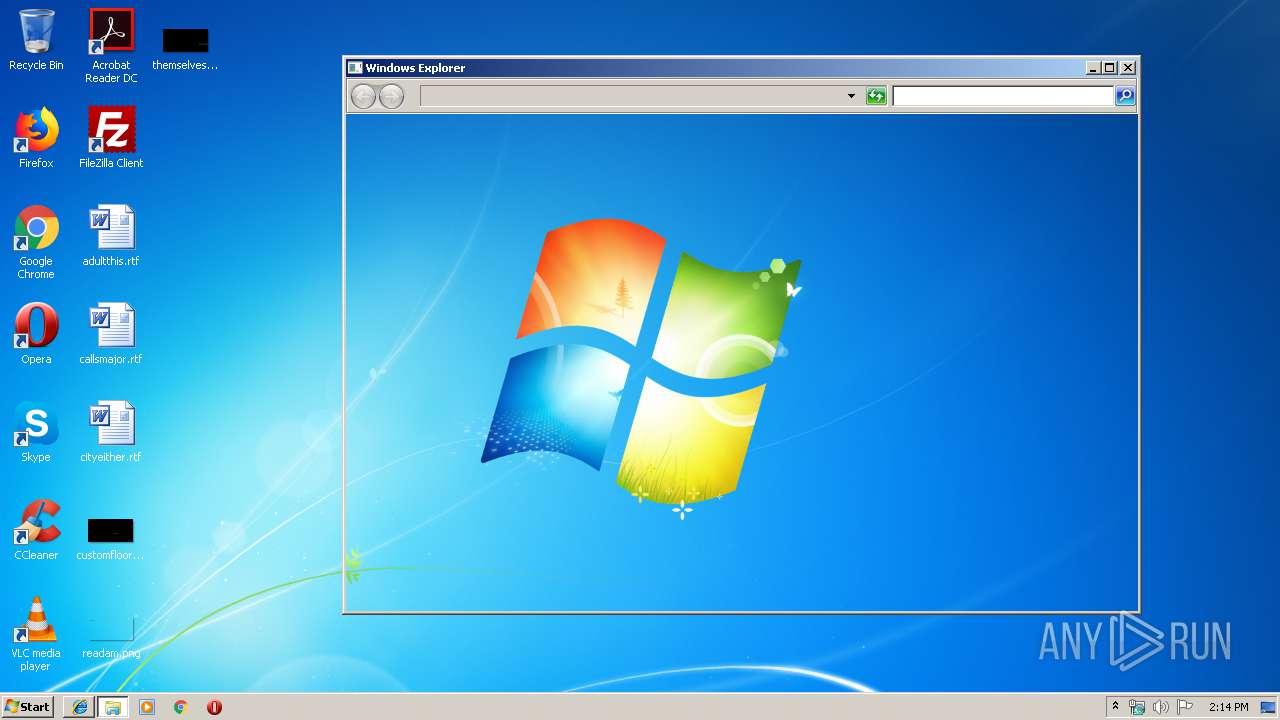
Dropped object may contain Bitcoin addresses
- jusched.exe (PID: 3488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:08:26 09:51:52+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 371712 |
| InitializedDataSize: | 500224 |
| UninitializedDataSize: | 6656 |
| EntryPoint: | 0x14e0 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 26-Aug-2019 07:51:52 |
| TLS Callbacks: | 2 callback(s) detected. |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 26-Aug-2019 07:51:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0005AB94 | 0x0005AC00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.43867 |
.data | 0x0005C000 | 0x00012860 | 0x00012A00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.33371 |
.rdata | 0x0006F000 | 0x0000B790 | 0x0000B800 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.37547 |
.bss | 0x0007B000 | 0x00001980 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0007D000 | 0x00000FC0 | 0x00001000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.22715 |
.CRT | 0x0007E000 | 0x00000034 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.278927 |
.tls | 0x0007F000 | 0x00000020 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.204488 |
Imports
KERNEL32.dll |
msvcrt.dll |
Total processes
85
Monitored processes
32
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1000 | cmd /c ""C:\Users\admin\AppData\Local\Temp\H6DQNHEdS5x6KL784tb2E2C4.bat" " | C:\Windows\system32\cmd.exe | — | 52Ie495ivrL.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2268 | taskkill /im java.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2304 | cmd /c ""C:\Users\admin\AppData\Local\Temp\hDtyXz4c5UQ70p9G6NANLT4nFeH.bat" " | C:\Windows\system32\cmd.exe | — | 2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2392 | cmd /c ""C:\Users\admin\AppData\Local\Temp\AQW5Q1ewZ9O9IvVaQ4h3R3WTYCSV.bat" " | C:\Windows\system32\cmd.exe | — | 52Ie495ivrL.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2392 | cmd /c ""C:\Users\admin\AppData\Local\Temp\Inh6EnG4xchyF408C13poZsv6I5AsY.bat" " | C:\Windows\system32\cmd.exe | — | jusched.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2436 | "C:\ProgramData\52Ie495ivrL.exe" khXg297EEfJ122N3lWe6C | C:\ProgramData\52Ie495ivrL.exe | 52Ie495ivrL.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2540 | ping -n 3 127.0.0.1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2580 | "C:\ProgramData\Java\jre8\bin\jusched.exe" default | C:\ProgramData\Java\jre8\bin\jusched.exe | — | 52Ie495ivrL.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java Update Scheduler Exit code: 0 Version: 2.8.211.14 Modules
| |||||||||||||||
| 2832 | icacls "C:\ProgramData\Java" /t /c /grant Everyone:(f) | C:\Windows\system32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2924 | cmd /c ""C:\Users\admin\AppData\Local\Temp\NJ8M4lu5r8Sq95dB00gUkSsaR2r061.bat" " | C:\Windows\system32\cmd.exe | — | 52Ie495ivrL.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
126
Read events
125
Write events
1
Delete events
0
Modification events
| (PID) Process: | (3488) jusched.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | extmgr |
Value: wscript.exe "C:\Users\admin\AppData\Roaming\Microsoft\Windows NT\extmgr.js" | |||
Executable files
2
Suspicious files
1
Text files
33
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2436 | 52Ie495ivrL.exe | C:\Users\admin\AppData\Local\Temp\AQW5Q1ewZ9O9IvVaQ4h3R3WTYCSV.bat | — | |
MD5:— | SHA256:— | |||
| 2436 | 52Ie495ivrL.exe | C:\Users\admin\AppData\Local\Temp\H6DQNHEdS5x6KL784tb2E2C4.bat | — | |
MD5:— | SHA256:— | |||
| 3644 | 2.exe | C:\ProgramData\52Ie495ivrL.exe | executable | |
MD5:— | SHA256:— | |||
| 3560 | 52Ie495ivrL.exe | C:\Users\admin\AppData\Local\Temp\khXg297EEfJ122N3lWe6C | text | |
MD5:— | SHA256:— | |||
| 3488 | jusched.exe | C:\Users\admin\AppData\Local\Temp\48v0Fi7Y2vRq8ffirGq7IwBOYq12sd.bat | — | |
MD5:— | SHA256:— | |||
| 2436 | 52Ie495ivrL.exe | C:\Users\admin\AppData\Local\Temp\ecMfJ41wdYZ0XbiM2059MSKZa.bat | text | |
MD5:— | SHA256:— | |||
| 2436 | 52Ie495ivrL.exe | C:\Users\admin\AppData\Local\Temp\R3wqYml25JBtGWWhWBSrkD.bat | text | |
MD5:— | SHA256:— | |||
| 2580 | jusched.exe | C:\Users\admin\AppData\Local\Temp\qPZxwbXmr4M8uG245I63j33vh52Q | text | |
MD5:— | SHA256:— | |||
| 2924 | cmd.exe | C:\Users\admin\AppData\Local\Temp\29Ib1aeK2p9B64j832OtudX7yFDPp6.txt | text | |
MD5:— | SHA256:— | |||
| 2436 | 52Ie495ivrL.exe | C:\Users\admin\AppData\Local\Temp\NJ8M4lu5r8Sq95dB00gUkSsaR2r061.bat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2436 | 52Ie495ivrL.exe | 193.242.211.184:12858 | sebains.kozow.com | easystores GmbH | NL | unknown |
3488 | jusched.exe | 185.100.85.198:52051 | clockdoplannow.hopto.org | Flokinet Ltd | RO | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sebains.kozow.com |
| unknown |
clockdoplannow.hopto.org |
| malicious |