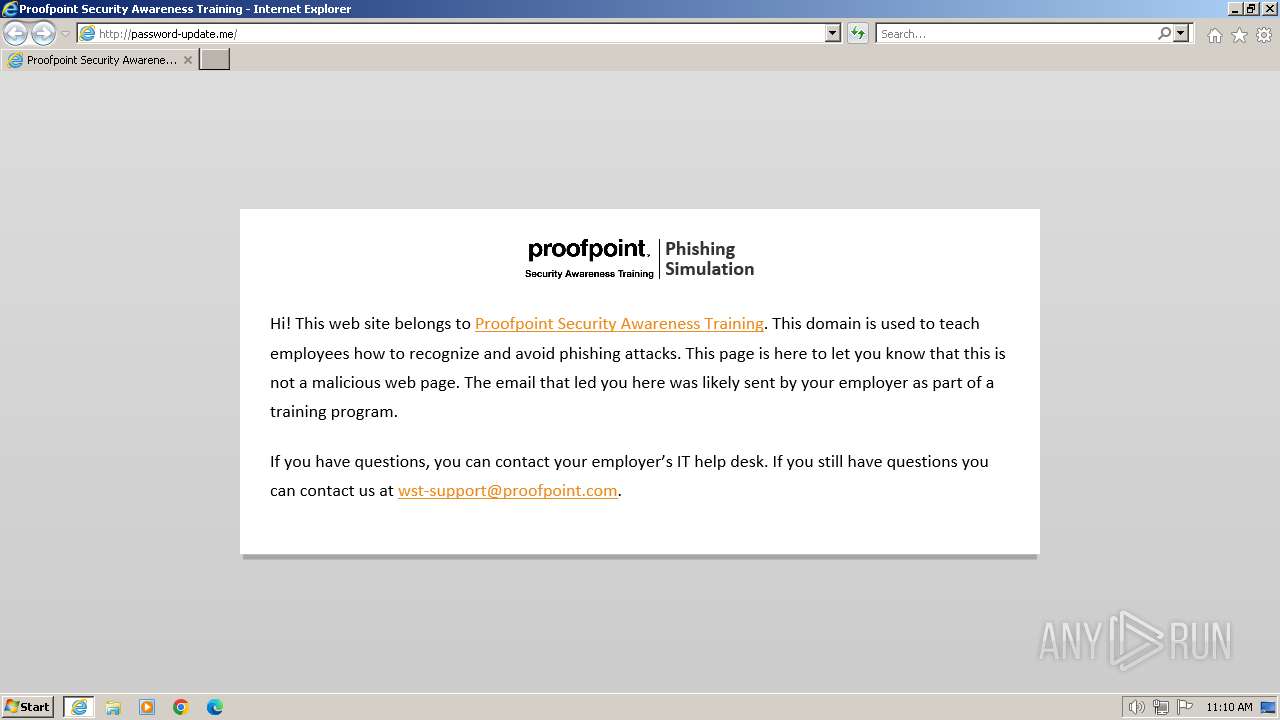
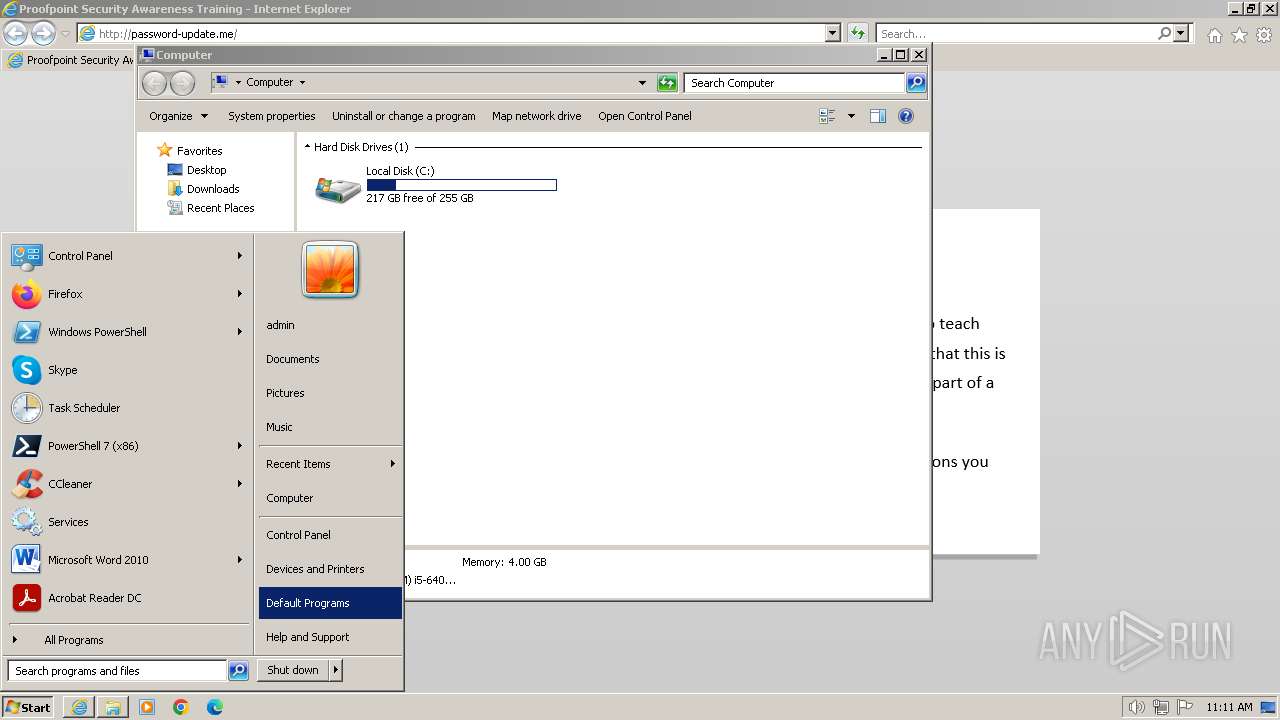
| URL: | password-update.me |
| Full analysis: | https://app.any.run/tasks/ec17c9cd-5343-4742-a750-57e43c935dbf |
| Verdict: | Malicious activity |
| Analysis date: | February 12, 2024, 11:10:48 |
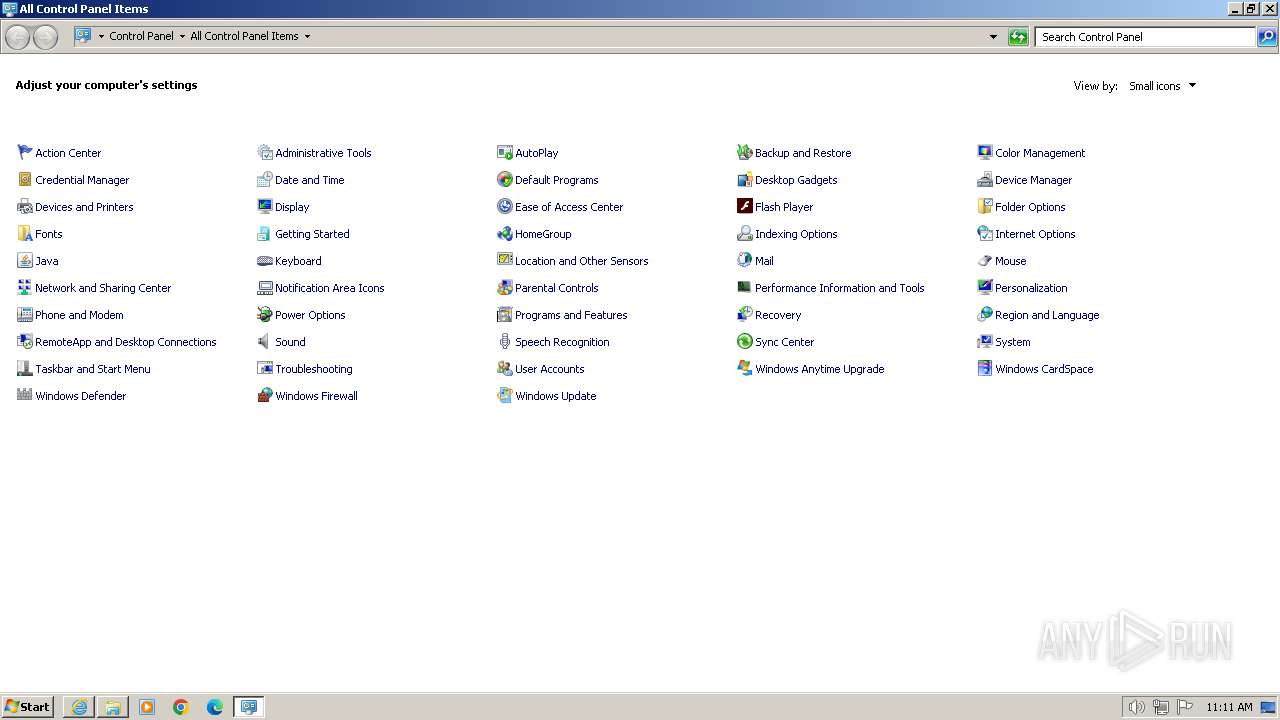
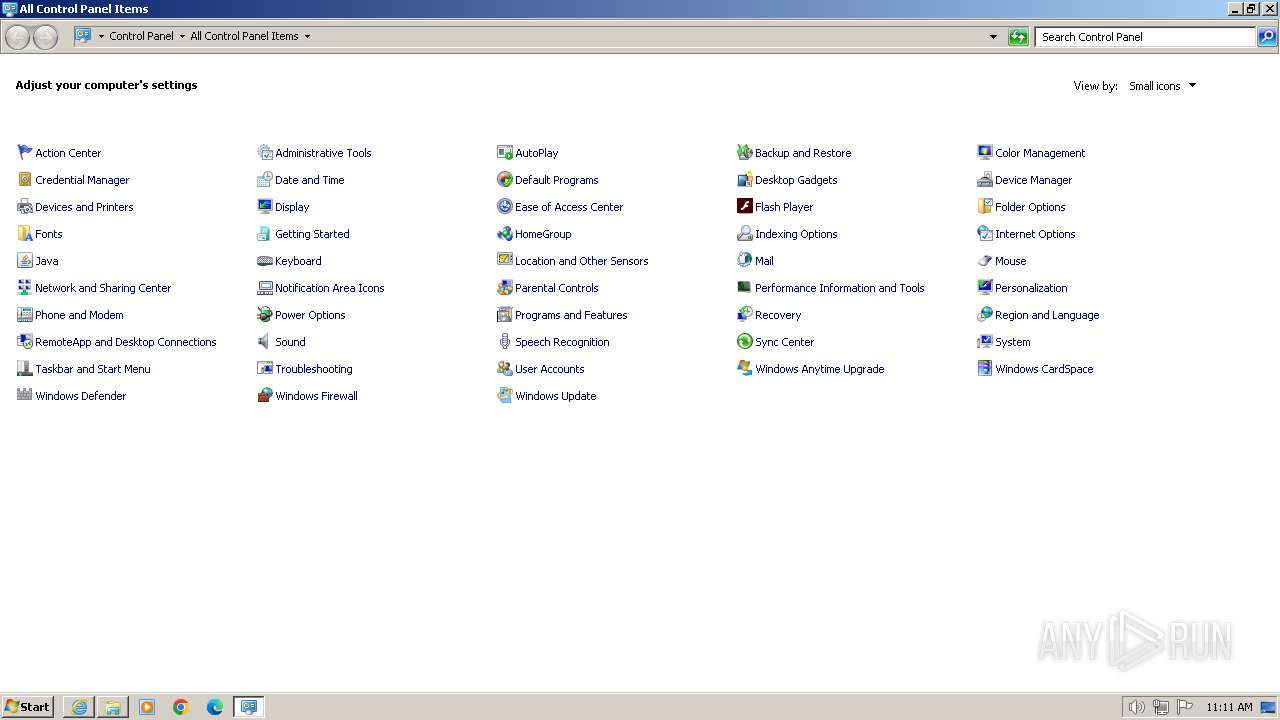
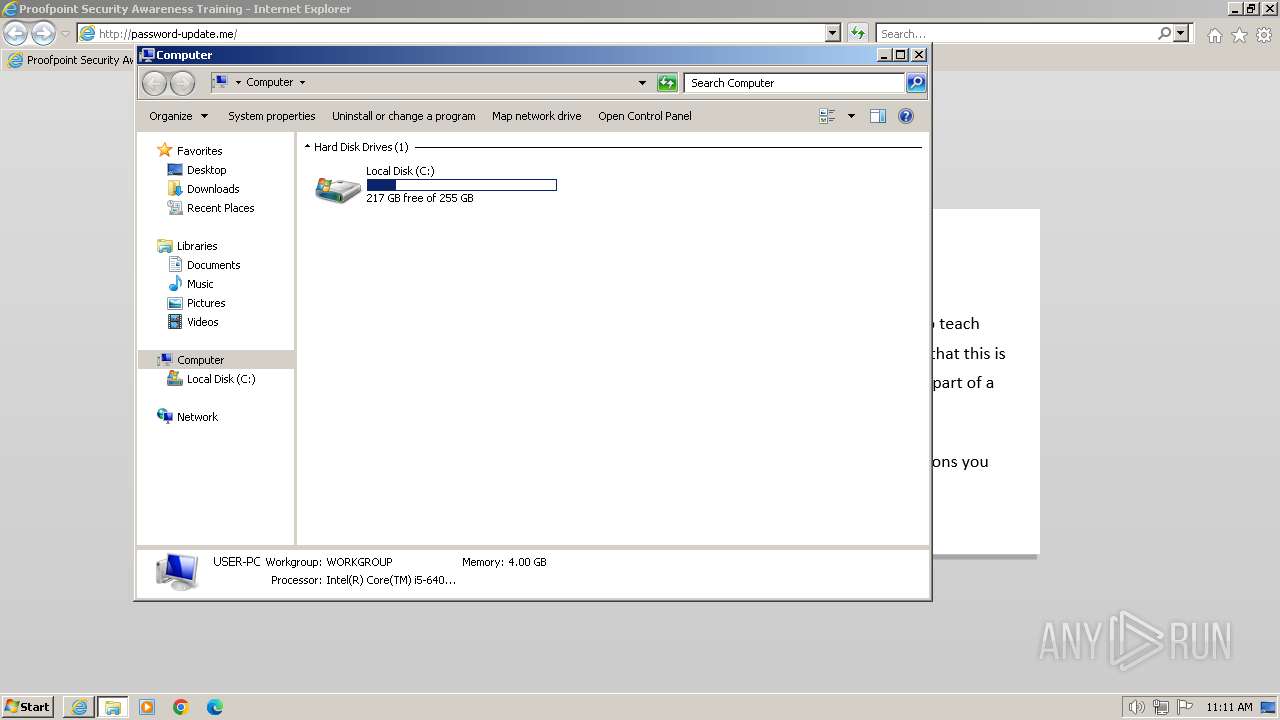
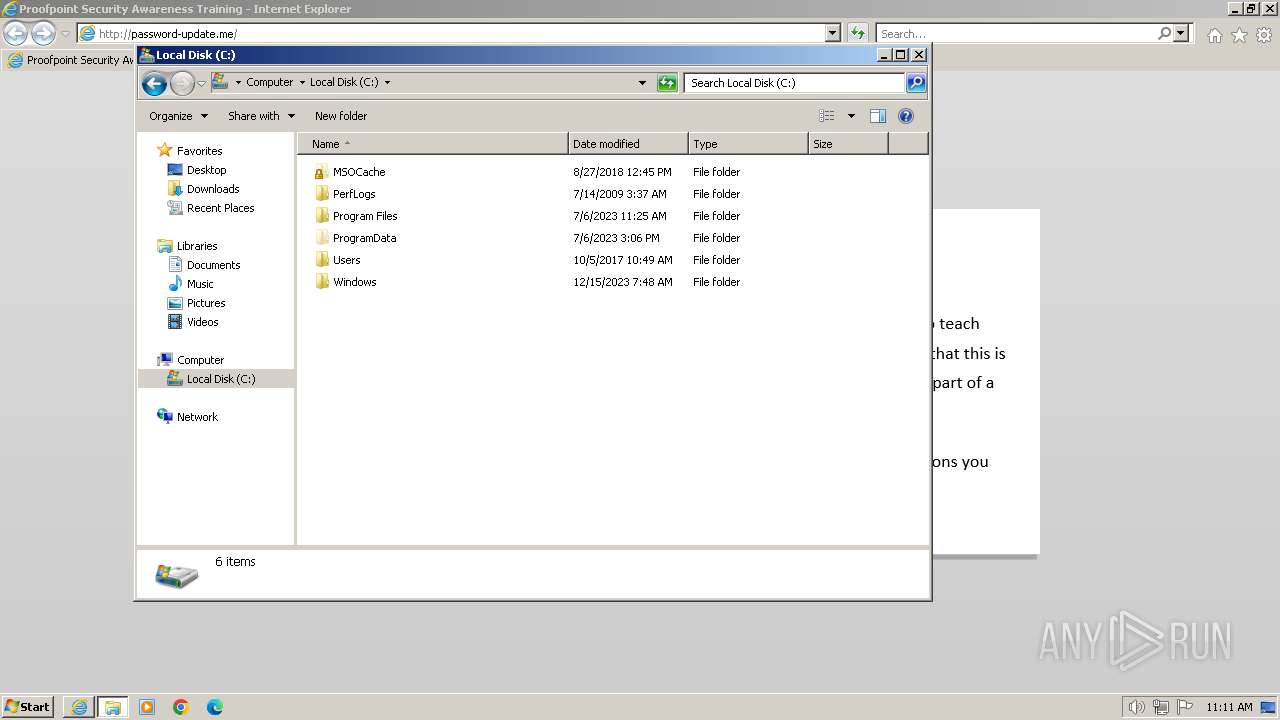
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6FC12C01E15B0FAD264C4183409433F7 |
| SHA1: | 13FE9C69EF20CBEC4EE6E887FBE43B0E65E060E7 |
| SHA256: | 68C63BB32819799BCC0FF243E9E395265B853F5950909A945A131DB550930A32 |
| SSDEEP: | 3:EBt:Eb |
MALICIOUS
No malicious indicators.SUSPICIOUS
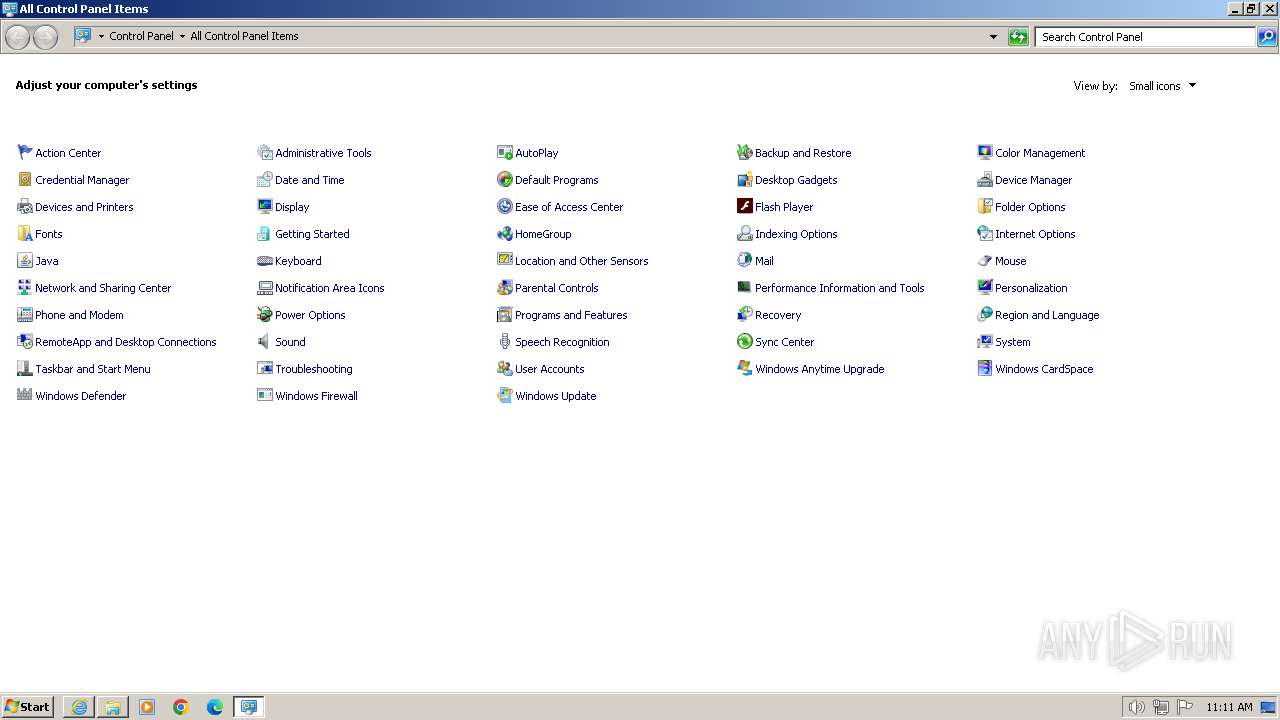
Reads settings of System Certificates
- windowsanytimeupgradeui.exe (PID: 2364)
Reads Microsoft Outlook installation path
- windowsanytimeupgradeui.exe (PID: 2364)
Reads the Internet Settings
- windowsanytimeupgradeui.exe (PID: 2364)
INFO
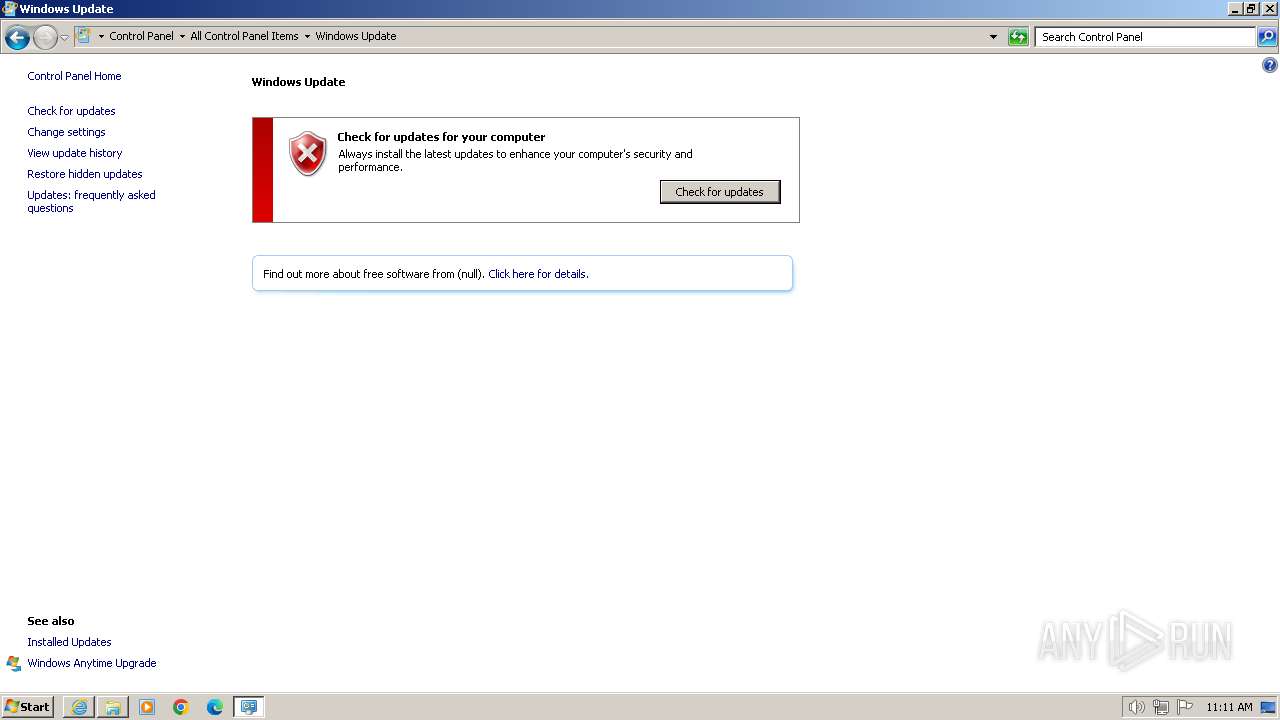
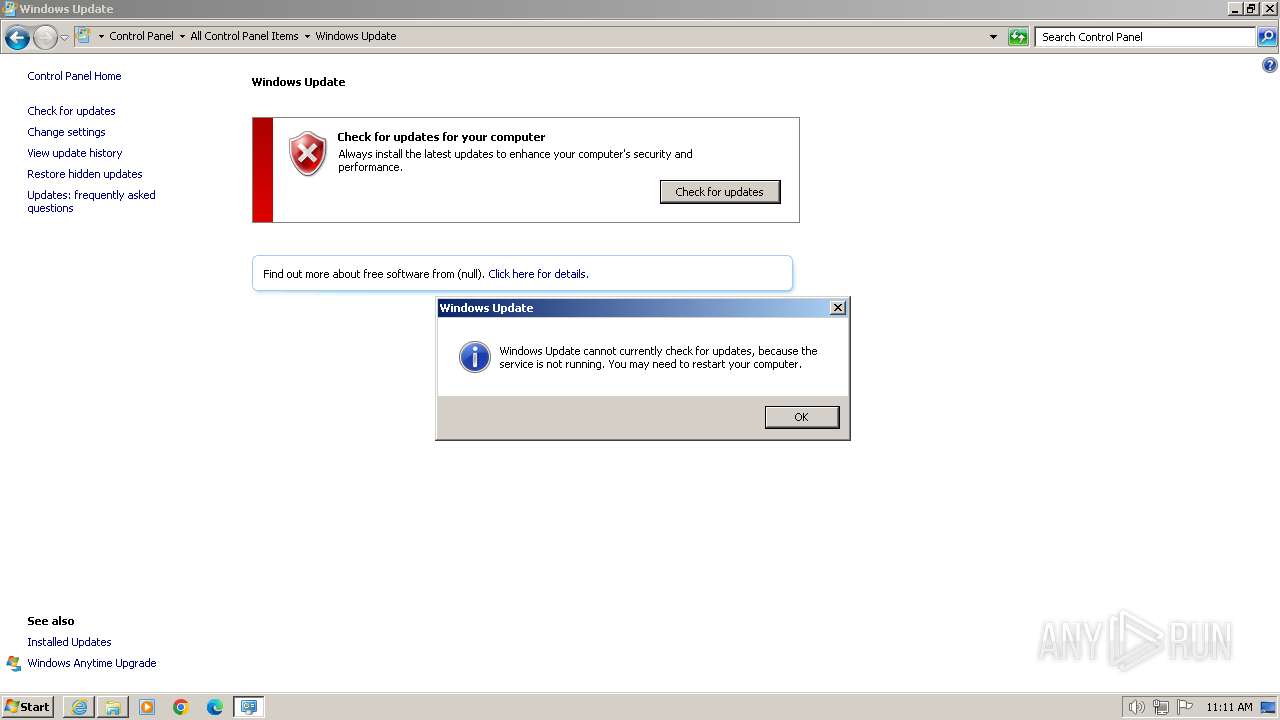
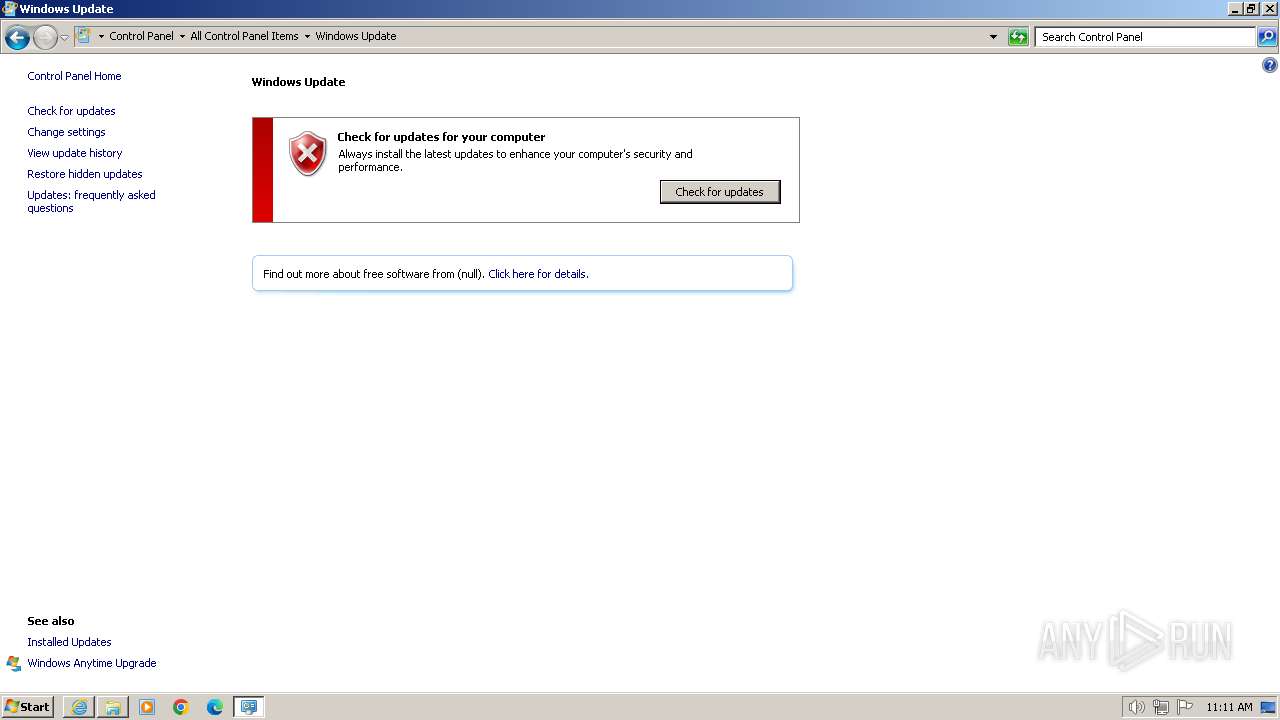
Reads Windows Product ID
- windowsanytimeupgradeui.exe (PID: 2364)
Checks proxy server information
- windowsanytimeupgradeui.exe (PID: 2364)
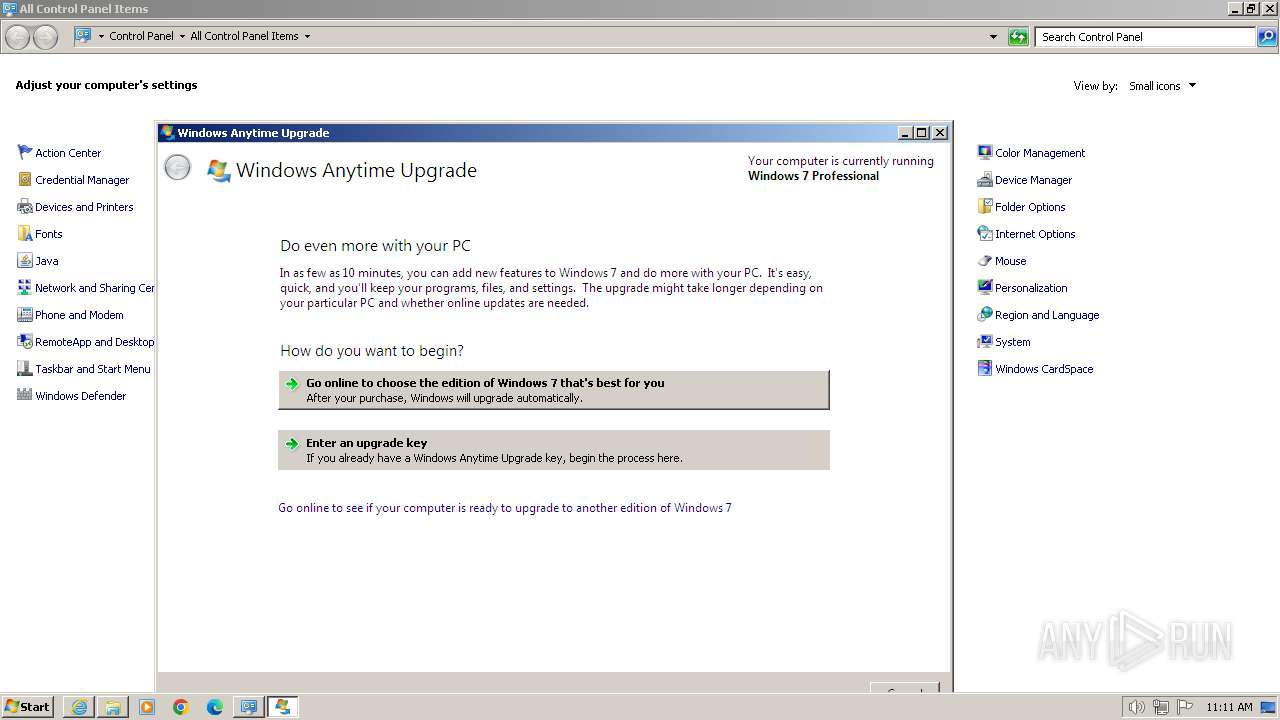
Manual execution by a user
- windowsanytimeupgradeui.exe (PID: 2364)
- windowsanytimeupgradeui.exe (PID: 1576)
Reads security settings of Internet Explorer
- windowsanytimeupgradeui.exe (PID: 2364)
Reads the software policy settings
- windowsanytimeupgradeui.exe (PID: 2364)
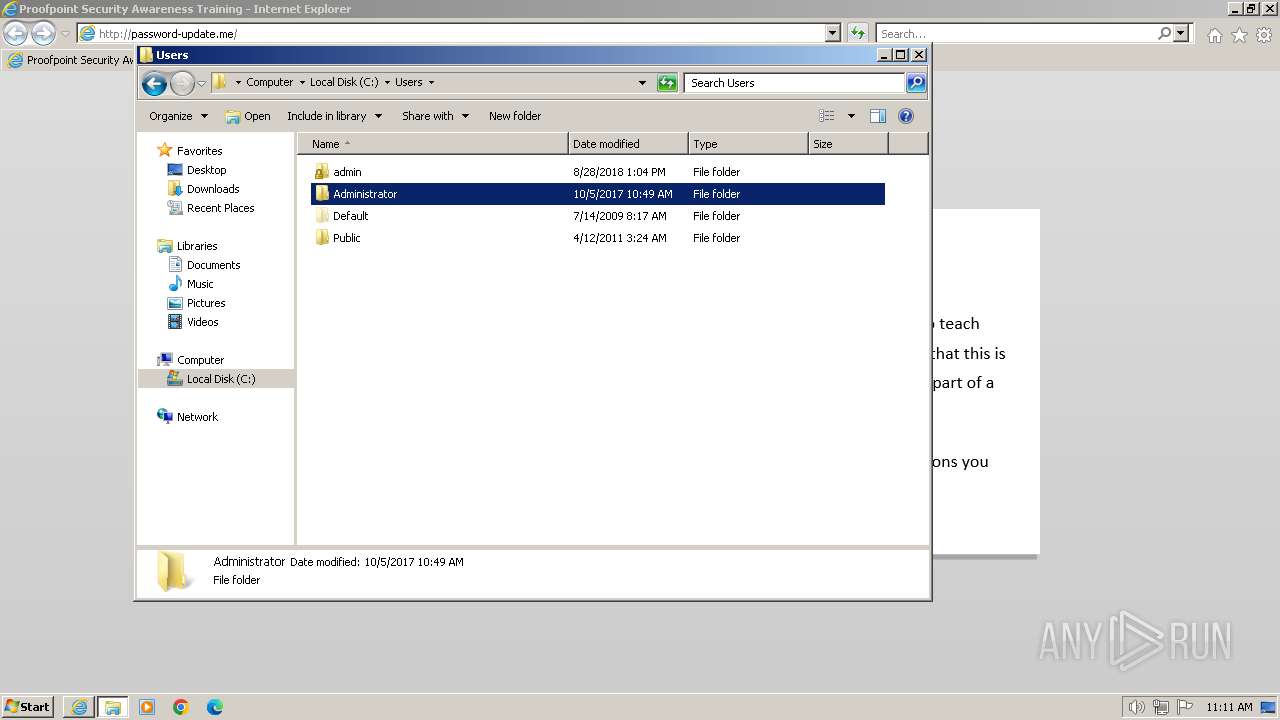
Creates files or folders in the user directory
- windowsanytimeupgradeui.exe (PID: 2364)
Application launched itself
- iexplore.exe (PID: 2160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
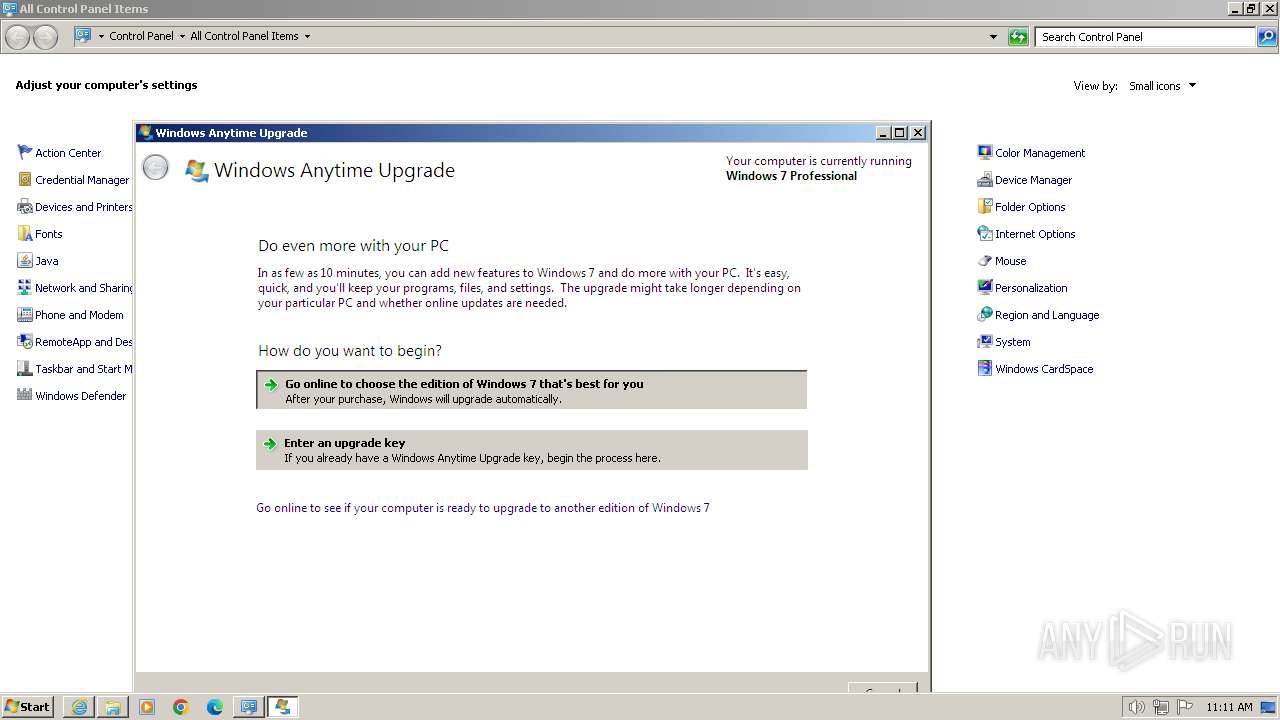
| 1576 | "C:\Windows\System32\windowsanytimeupgradeui.exe" | C:\Windows\System32\windowsanytimeupgradeui.exe | — | explorer.exe | |||||||||||
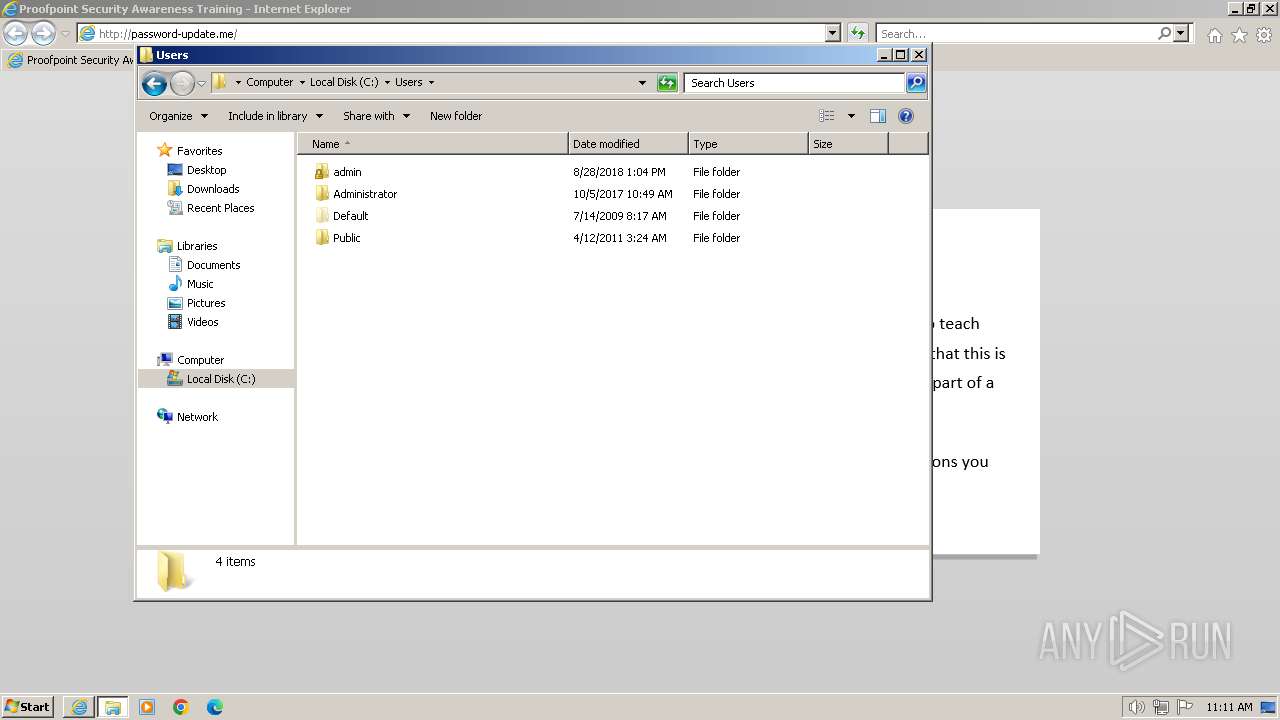
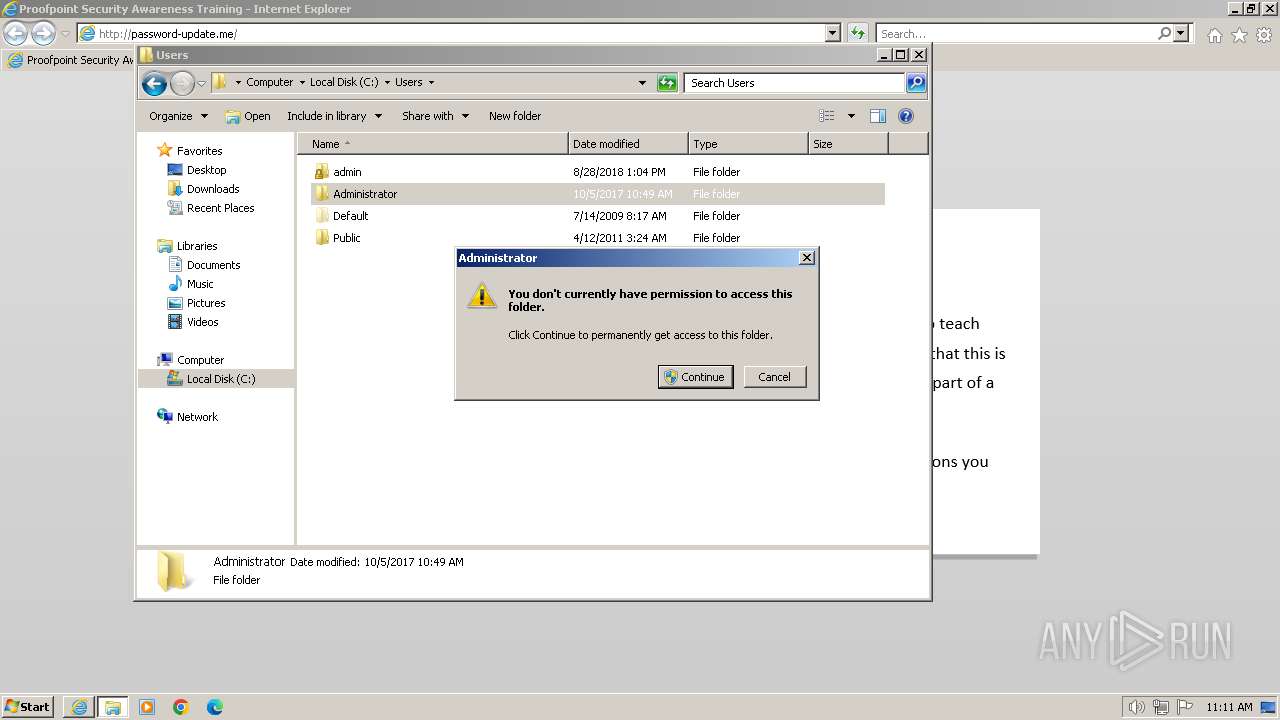
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Anytime Upgrade User Interface Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Internet Explorer\iexplore.exe" "password-update.me" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2364 | "C:\Windows\System32\windowsanytimeupgradeui.exe" | C:\Windows\System32\windowsanytimeupgradeui.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Anytime Upgrade User Interface Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2920 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2160 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
17 088
Read events
16 907
Write events
142
Delete events
39
Modification events
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 645899344 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31088036 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 946061844 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31088036 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
6
Text files
7
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2364 | windowsanytimeupgradeui.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Windows Anytime Upgrade\Upgrade.log | binary | |
MD5:7A3FB303253DA04DA241119BF8A7454A | SHA256:477D80678C9A8F0024A13F0E3ED95C92FE556EC8AD3F43D5A11F13B057F67AFF | |||
| 2364 | windowsanytimeupgradeui.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\80237EE4964FC9C409AAF55BF996A292_C0427F5F77D9B3A439FC620EDAAB6177 | der | |
MD5:ECFD6B81730453DB2DFF5E24F2E6EA9E | SHA256:3E82C426FA4074615ED71E14E5D3C4F2EDCECCD933174138CFC5C111991830F2 | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\psat_logo[1].png | image | |
MD5:C510B40B57C8DE8C431E25E89EAC656F | SHA256:313AC720267E0D852F0B17055B68087B1D1CC4CE24F075864D4AB57A7F83B199 | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\jquery.min[1].js | text | |
MD5:8FC25E27D42774AEAE6EDBC0A18B72AA | SHA256:B294E973896F8F874E90A8EB1A8908AC790980D034C4C4BDF0FC3D37B8ABF682 | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\4HPL13QO.htm | html | |
MD5:CF0AE9D292AC3C2D9C565AC15BCACC77 | SHA256:C0623A98220D6586761A01BC71F85279D1893F40E75400864B0F9048BC2B0BFE | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\all[1].js | text | |
MD5:097F74FC8F861ECE148262A652AB806A | SHA256:39B4614F1C87CF0CFD1BC3375642E95825CB2018E0318A36AAD766DDB5A8CBE9 | |||
| 2364 | windowsanytimeupgradeui.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\DE0D974FB4DC3536B9035FD604565AB7_4708B902F5E44C206F9CFEAB460AFD60 | binary | |
MD5:E66B610F5099D5A5BB5E99E89EE3D916 | SHA256:7B4437582CA6BD1BB2DDD25870346FB71FE6B6CF40E85E631A57AF2CBBD0A46E | |||
| 2160 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver685A.tmp | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\DOMStore\DOTBATAV\password-update[1].xml | text | |
MD5:C1DDEA3EF6BBEF3E7060A1A9AD89E4C5 | SHA256:B71E4D17274636B97179BA2D97C742735B6510EB54F22893D3A2DAFF2CEB28DB | |||
| 2160 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:5D2E801AE3F7DF50081E3BB1F01CDF68 | SHA256:8FAA139C1B9826FF7961DAFDEBA17F9C471B2B164313C0886F6E56A8222D354E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
24
DNS requests
13
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2920 | iexplore.exe | GET | 200 | 34.251.35.193:80 | http://password-update.me/ | unknown | html | 1.06 Kb | unknown |
2920 | iexplore.exe | GET | 200 | 34.251.35.193:80 | http://password-update.me/trace?id=infopage&msg=BrowserDetect%20-%20plugin%20Shockwave%20Flash&correlation_id=undefined | unknown | binary | 20 b | unknown |
2920 | iexplore.exe | GET | 200 | 34.251.35.193:80 | http://password-update.me/trace?id=infopage&msg=Skipping%20java%20detection&correlation_id=undefined | unknown | binary | 20 b | unknown |
2920 | iexplore.exe | GET | 200 | 34.251.35.193:80 | http://password-update.me/assets/ajax/libs/jquery/1.11.0/jquery.min.js | unknown | text | 32.5 Kb | unknown |
2920 | iexplore.exe | GET | 200 | 34.251.35.193:80 | http://password-update.me/assets/psat_logo.png | unknown | image | 10.2 Kb | unknown |
2920 | iexplore.exe | GET | 200 | 34.251.35.193:80 | http://password-update.me/assets/all.js?g=infopage | unknown | text | 7.02 Kb | unknown |
2920 | iexplore.exe | GET | 200 | 34.251.35.193:80 | http://password-update.me/trace?id=infopage&msg=BrowserDetect%20-%20localStorage%20%3D%20true&correlation_id=undefined | unknown | binary | 20 b | unknown |
2920 | iexplore.exe | GET | 200 | 34.251.35.193:80 | http://password-update.me/trace?id=infopage&msg=BrowserDetect%20-%20sessionStorage%20%3D%20true&correlation_id=undefined | unknown | binary | 20 b | unknown |
2920 | iexplore.exe | GET | 200 | 34.251.35.193:80 | http://password-update.me/trace?id=infopage&msg=BrowserDetect%20-%20hasCookies%20%3D%20true&correlation_id=undefined | unknown | binary | 20 b | unknown |
2920 | iexplore.exe | GET | 200 | 34.251.35.193:80 | http://password-update.me/trace?id=infopage&msg=BrowserDetect%20-%20browser_version%20%3D%2011&correlation_id=undefined | unknown | binary | 20 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2920 | iexplore.exe | 34.251.35.193:80 | password-update.me | AMAZON-02 | IE | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2160 | iexplore.exe | 34.251.35.193:80 | password-update.me | AMAZON-02 | IE | unknown |
2160 | iexplore.exe | 23.213.53.26:443 | www.bing.com | Akamai International B.V. | US | unknown |
2364 | windowsanytimeupgradeui.exe | 23.221.249.158:80 | go.microsoft.com | AKAMAI-AS | NL | unknown |
2364 | windowsanytimeupgradeui.exe | 96.17.7.190:443 | support.microsoft.com | Akamai International B.V. | FI | unknown |
2364 | windowsanytimeupgradeui.exe | 87.248.204.0:80 | ctldl.windowsupdate.com | LLNW | US | unknown |
2364 | windowsanytimeupgradeui.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
password-update.me |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
support.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2920 | iexplore.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Proofpoint Security Awareness Training |
2160 | iexplore.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Proofpoint Security Awareness Training |