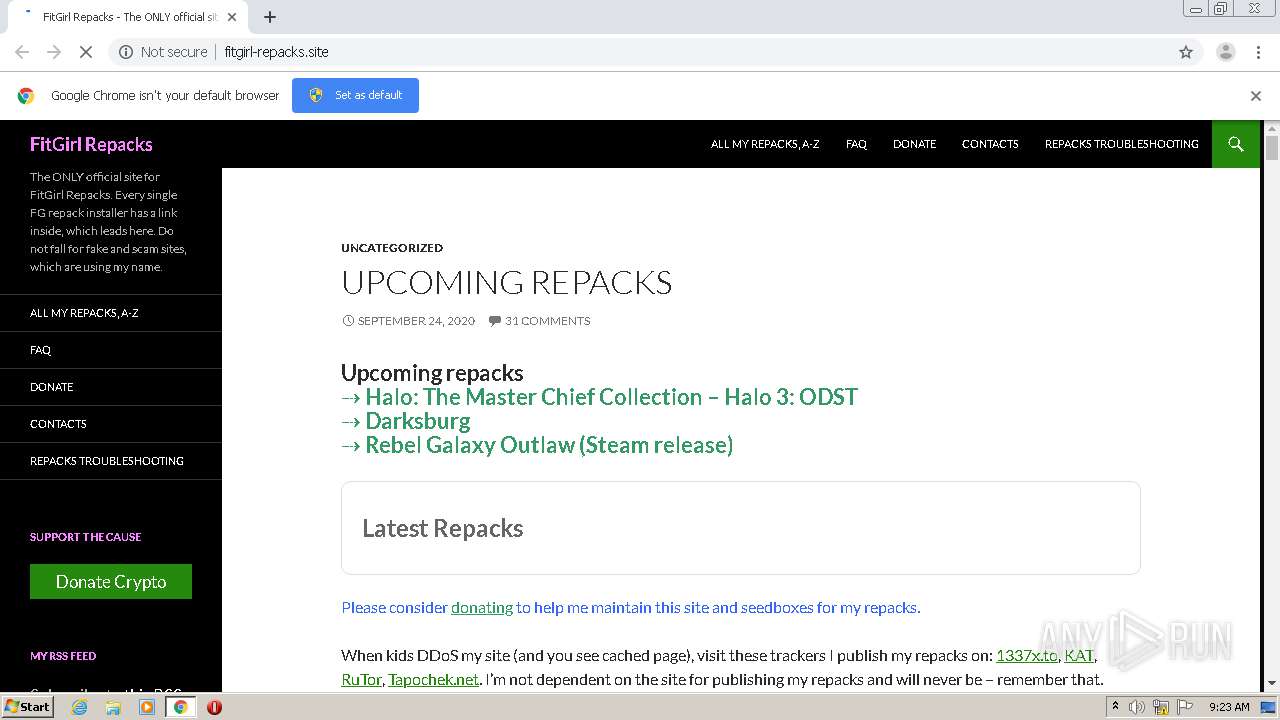
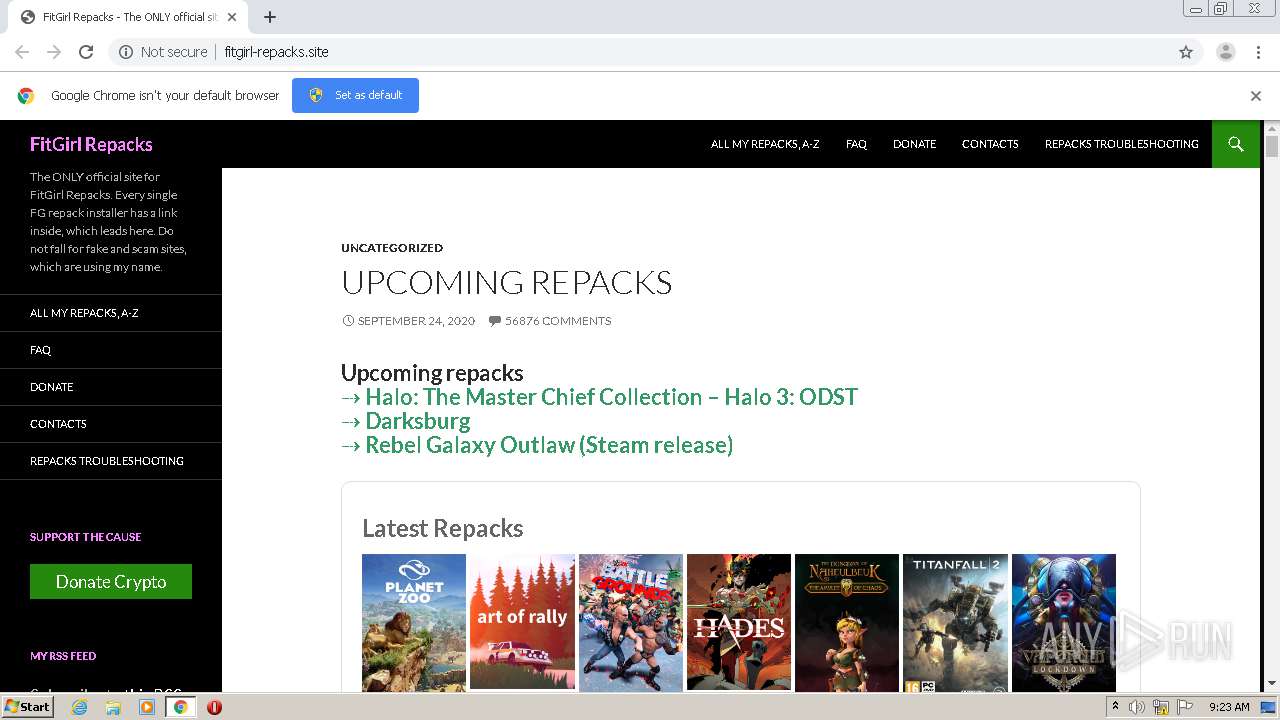
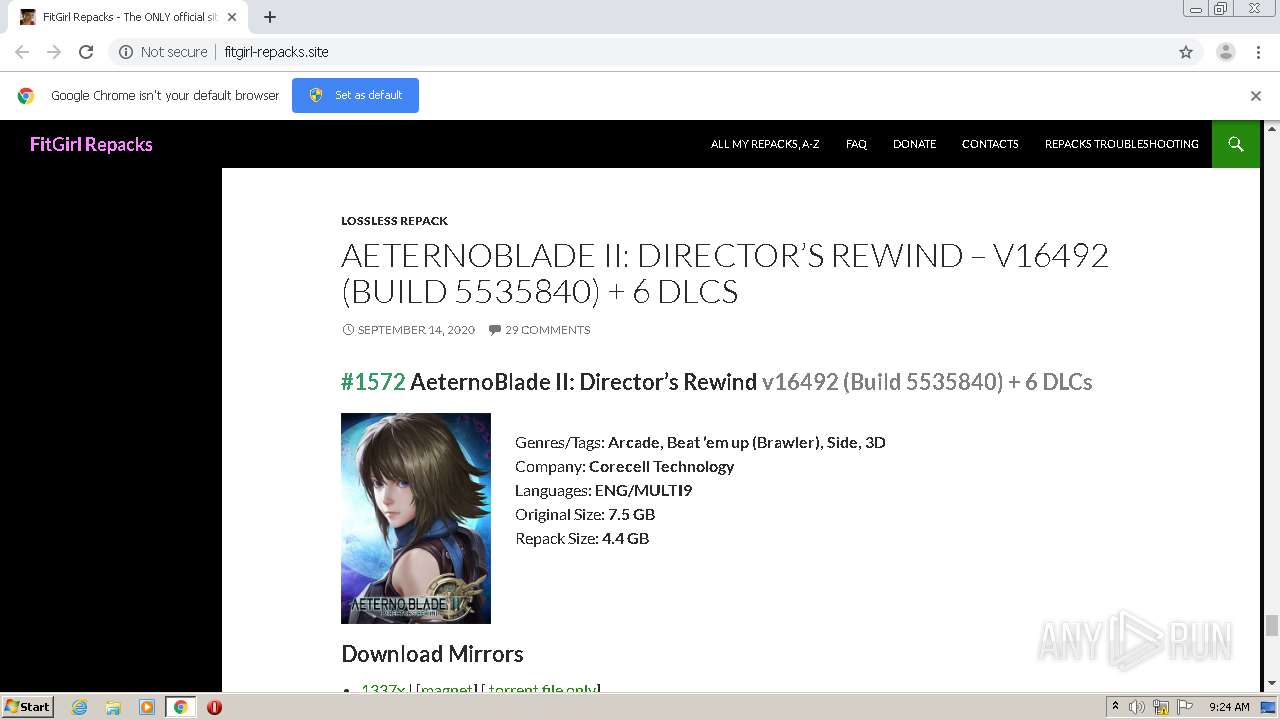
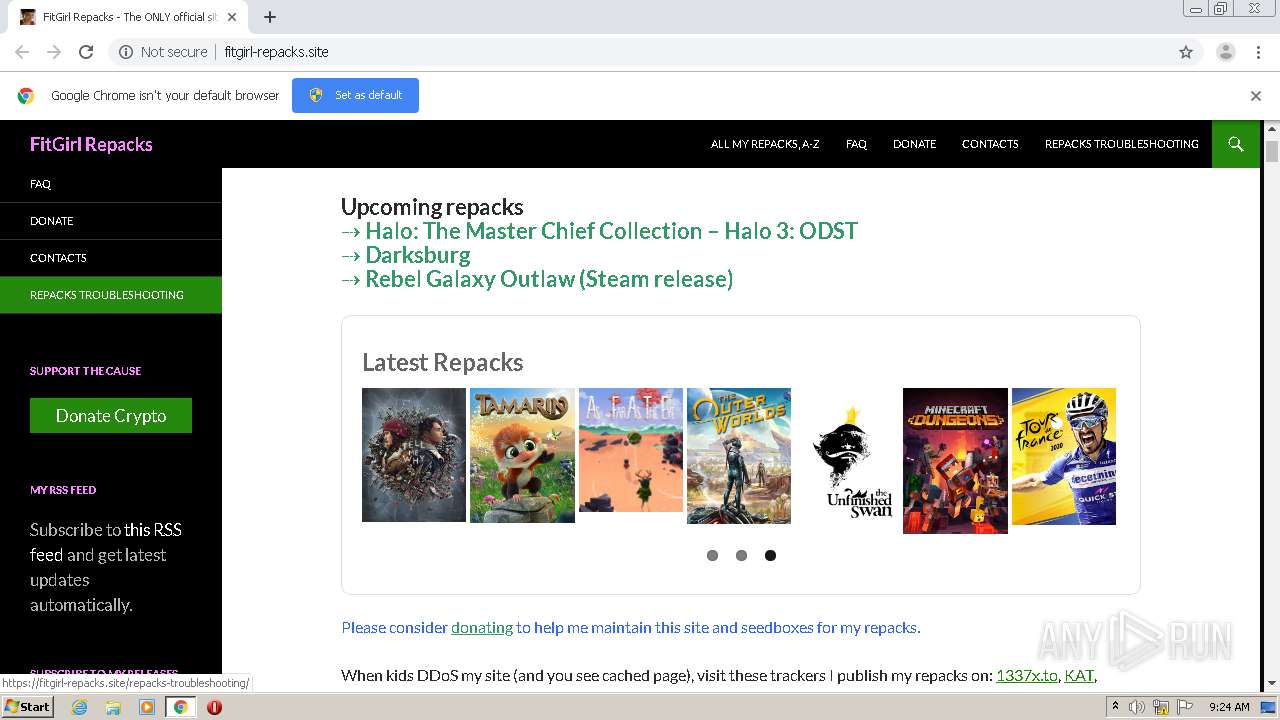
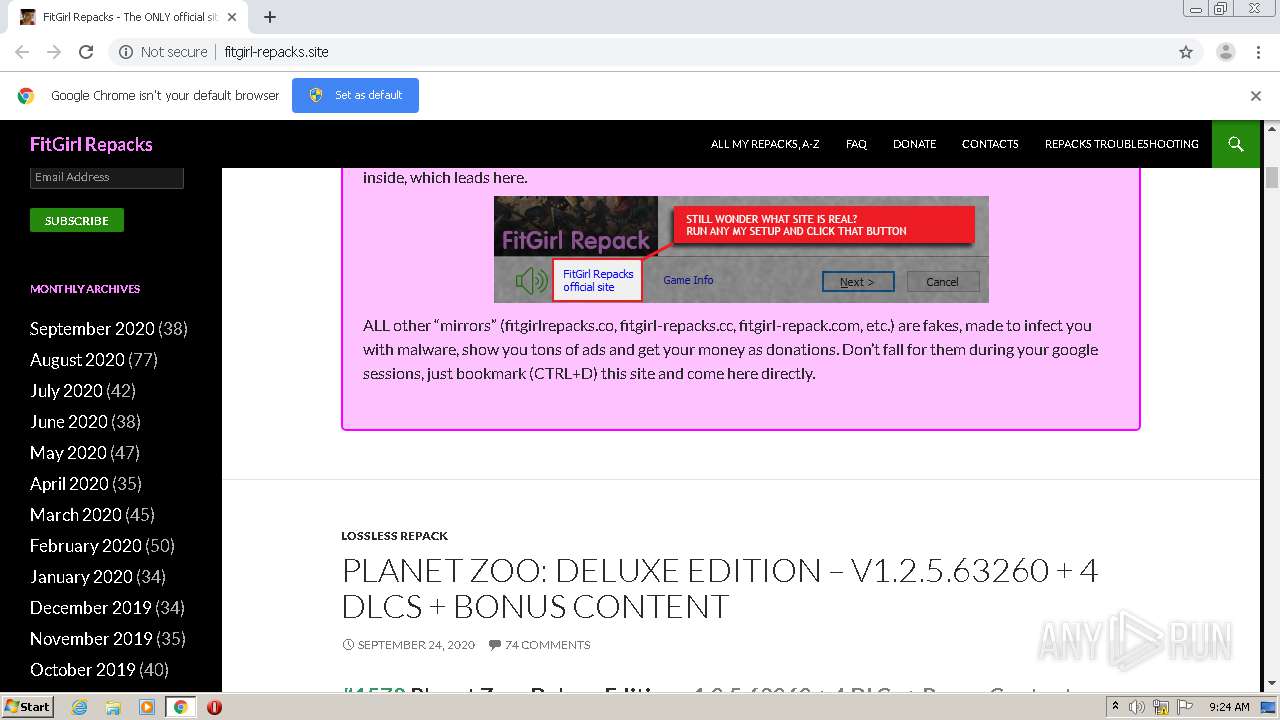
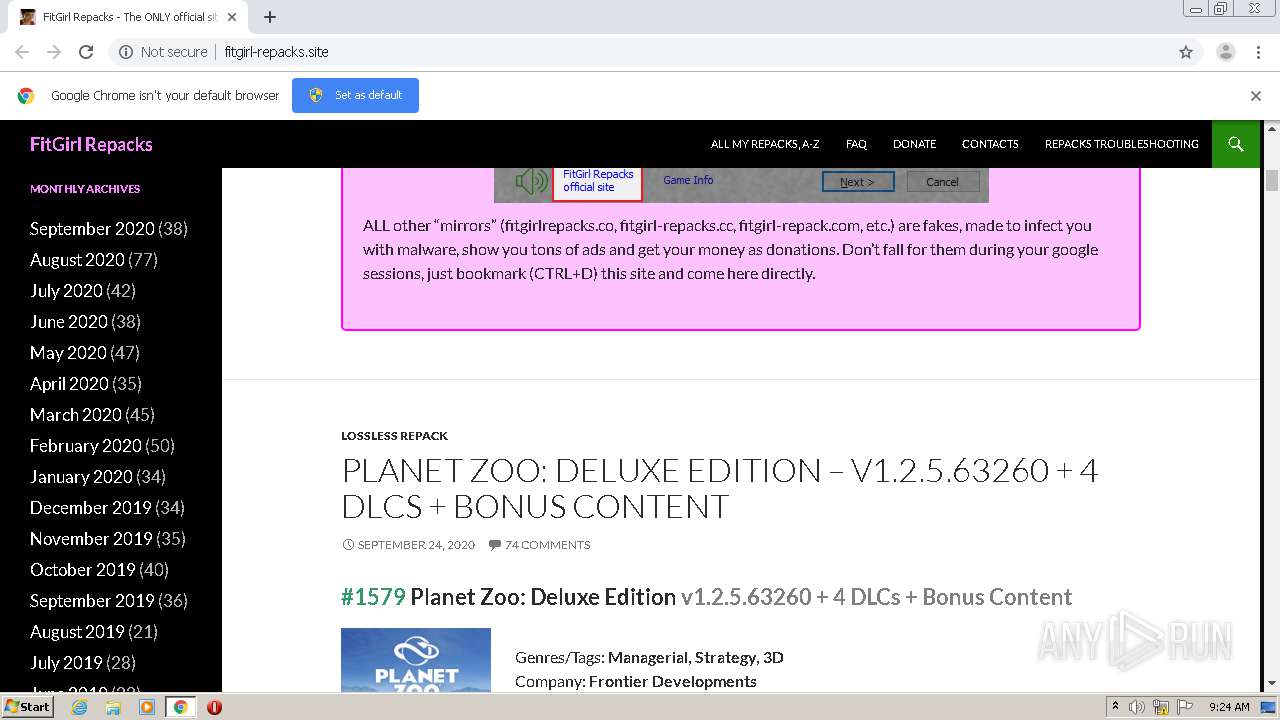
| URL: | http://fitgirl-repacks.site/ |
| Full analysis: | https://app.any.run/tasks/cd0b338d-ce6b-44de-8264-167d2171060d |
| Verdict: | Malicious activity |
| Analysis date: | September 24, 2020, 08:22:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7F1E7E2DC8EE5D2C653B798A3B730216 |
| SHA1: | D7032658B8E60FF508DFE581C37A88258A88D3B0 |
| SHA256: | 68C1B1E3CD4DA12B6472FD8BF7589EE750DCC4754C6158F98E5B335D74F037CC |
| SSDEEP: | 3:N1KYmlJOXMmKn:CYmsVKn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1772)
INFO
Application launched itself
- chrome.exe (PID: 1772)
Reads the hosts file
- chrome.exe (PID: 2356)
- chrome.exe (PID: 1772)
Changes settings of System certificates
- chrome.exe (PID: 2356)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
56
Monitored processes
18
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1380 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,3164489731041274036,784176385233726429,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14962591833097011580 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2504 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,3164489731041274036,784176385233726429,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=826161768593273980 --mojo-platform-channel-handle=3864 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,3164489731041274036,784176385233726429,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15995498151760837199 --mojo-platform-channel-handle=3980 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://fitgirl-repacks.site/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,3164489731041274036,784176385233726429,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8768670182083354687 --mojo-platform-channel-handle=1052 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,3164489731041274036,784176385233726429,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=9305543038343903629 --mojo-platform-channel-handle=1540 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,3164489731041274036,784176385233726429,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12808002939917798897 --mojo-platform-channel-handle=2948 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,3164489731041274036,784176385233726429,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=862602068164586358 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3832 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,3164489731041274036,784176385233726429,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=416915056346898599 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2208 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
608
Read events
533
Write events
71
Delete events
4
Modification events
| (PID) Process: | (1772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (764) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1772-13245409391649750 |
Value: 259 | |||
| (PID) Process: | (1772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (1772) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
51
Text files
178
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF160544.TMP | — | |
MD5:— | SHA256:— | |||
| 1772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF160554.TMP | — | |
MD5:— | SHA256:— | |||
| 1772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\bd753bbc-29e6-46ec-83d5-307c5fc3d8dc.tmp | — | |
MD5:— | SHA256:— | |||
| 1772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF160729.TMP | — | |
MD5:— | SHA256:— | |||
| 1772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
80
TCP/UDP connections
56
DNS requests
44
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
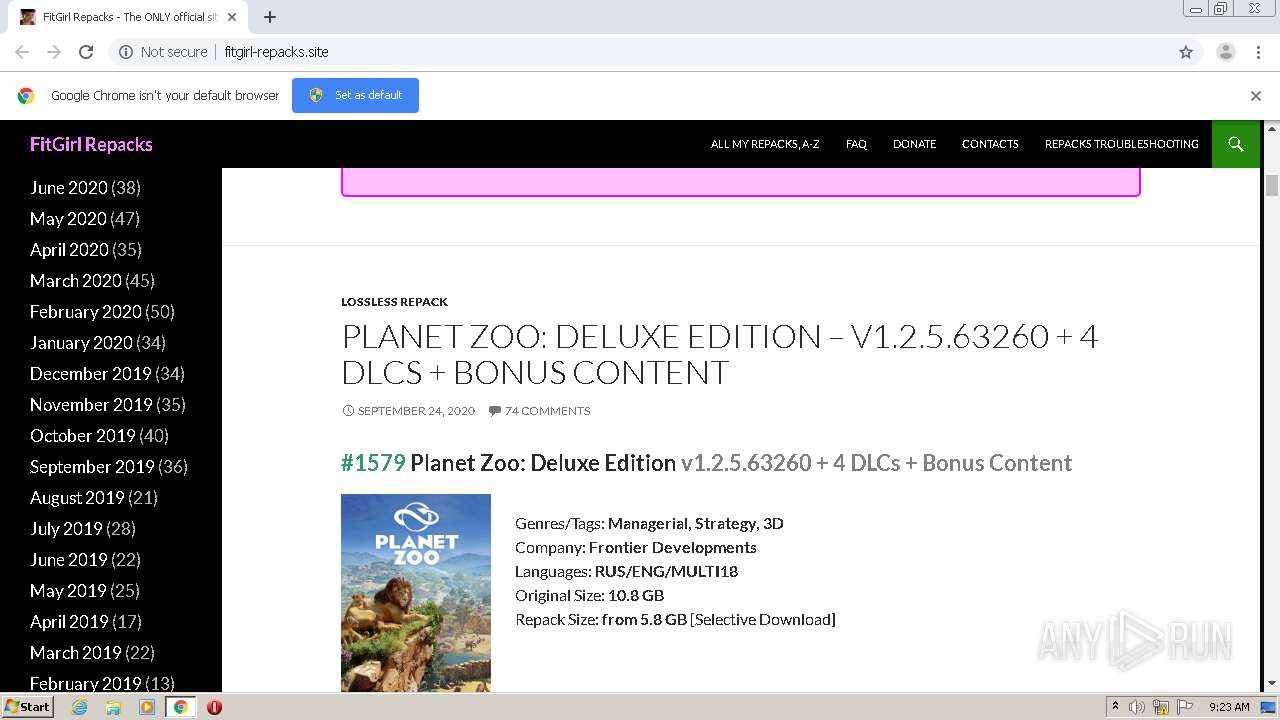
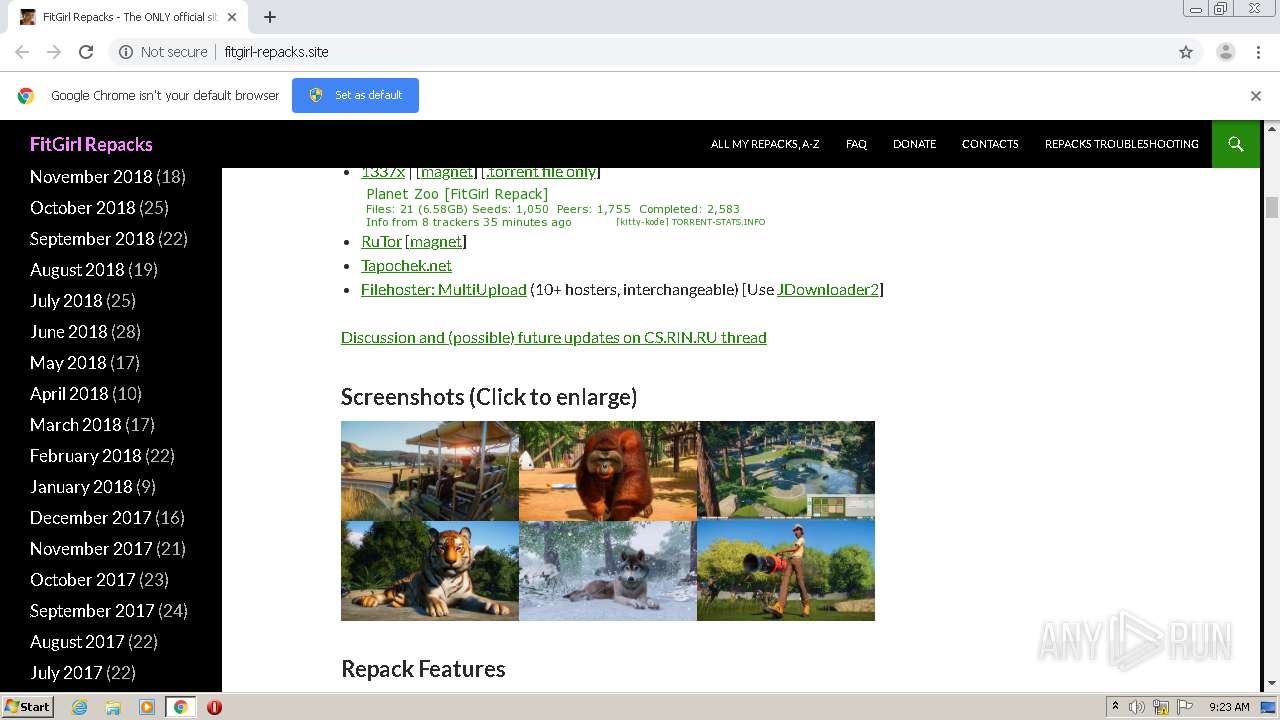
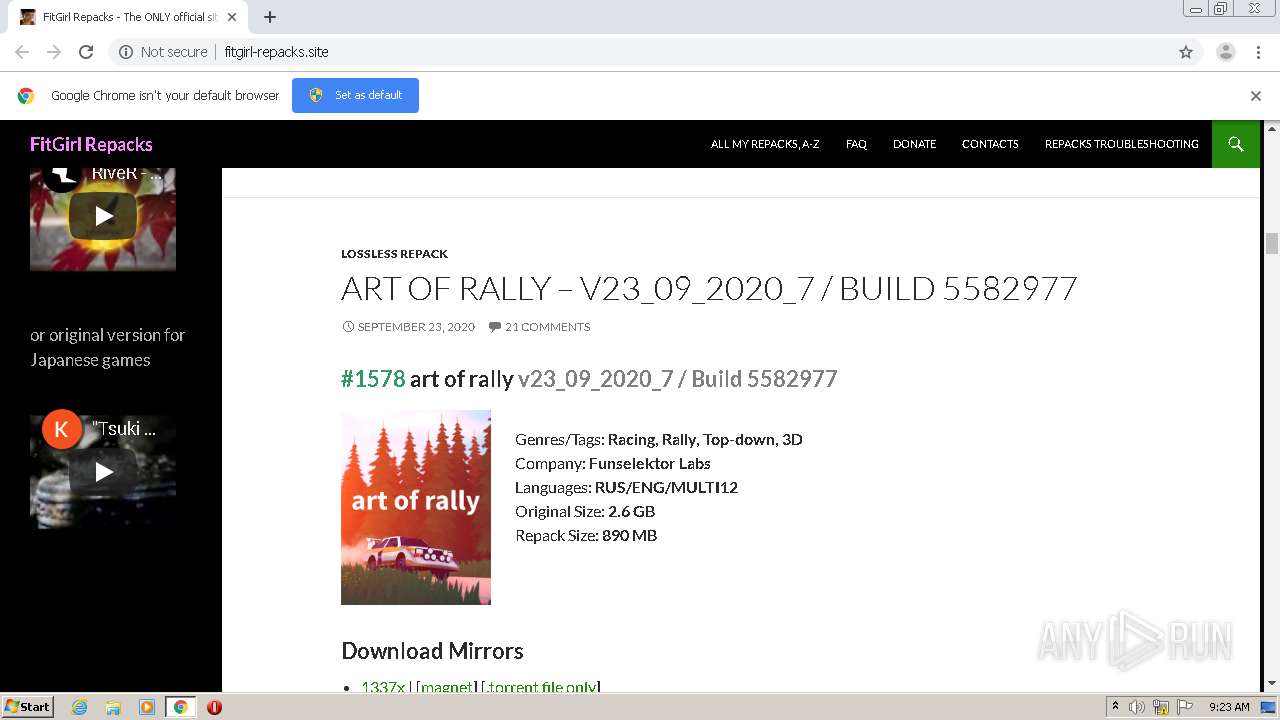
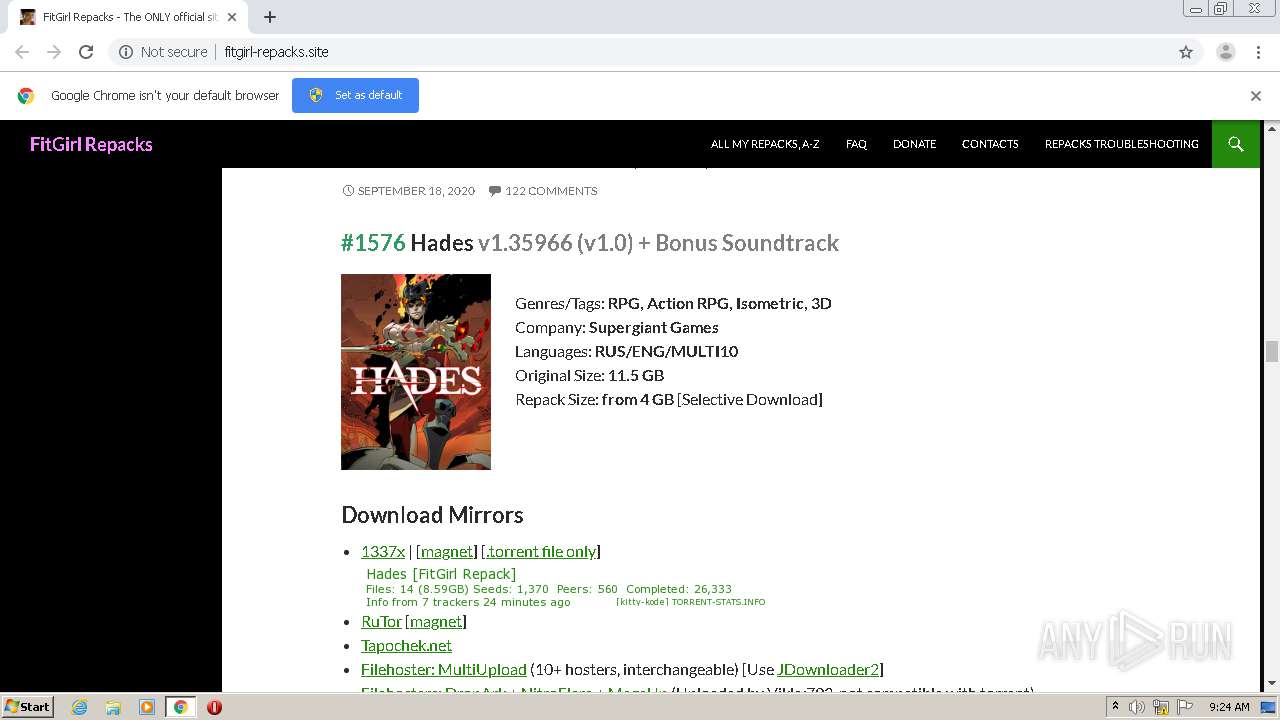
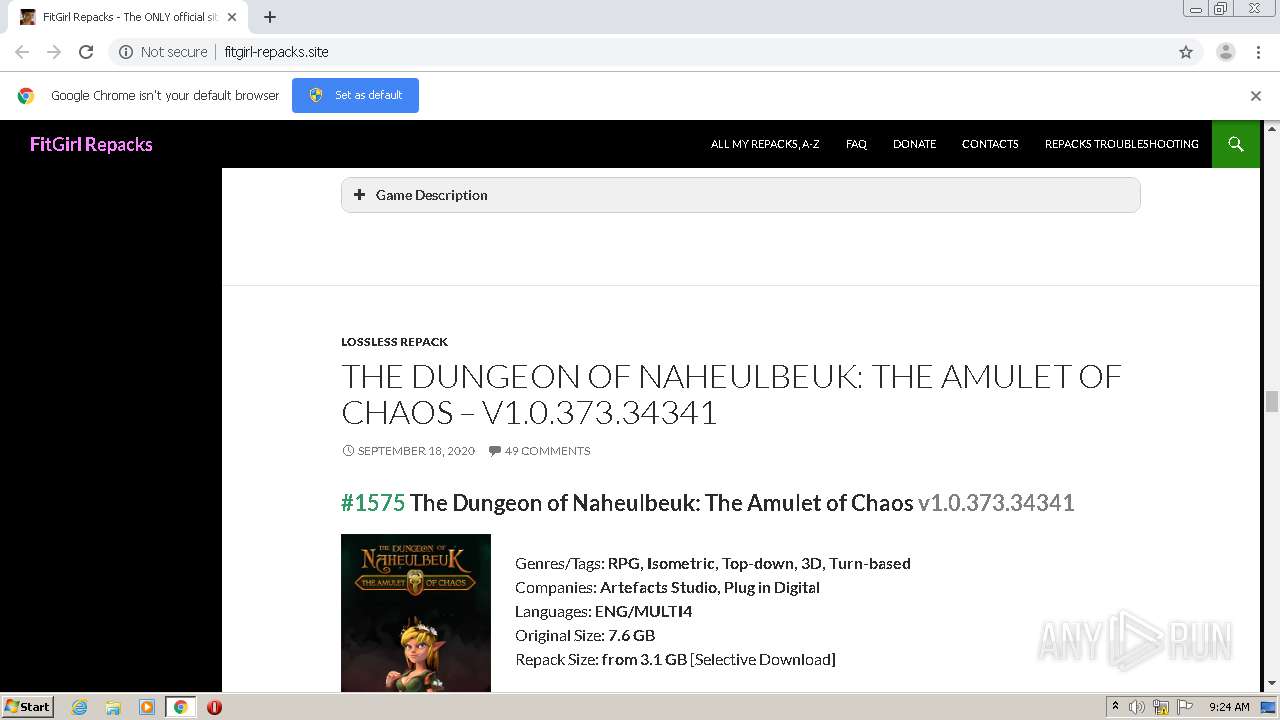
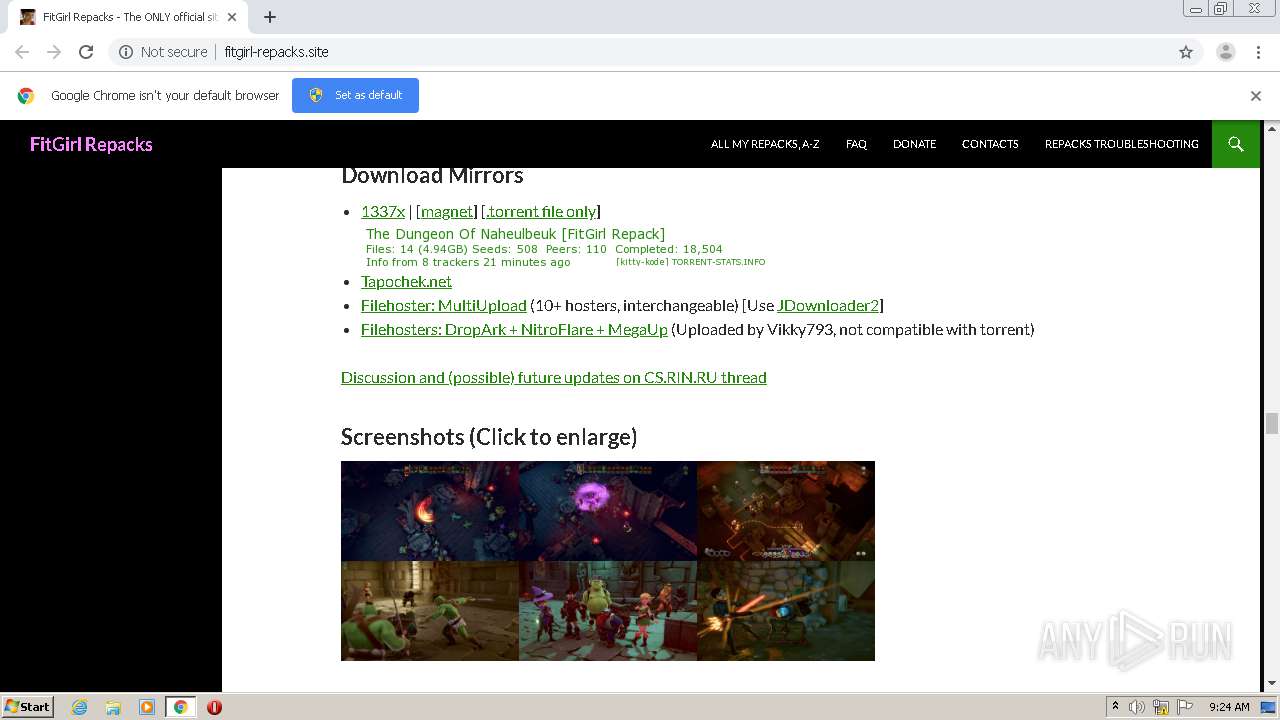
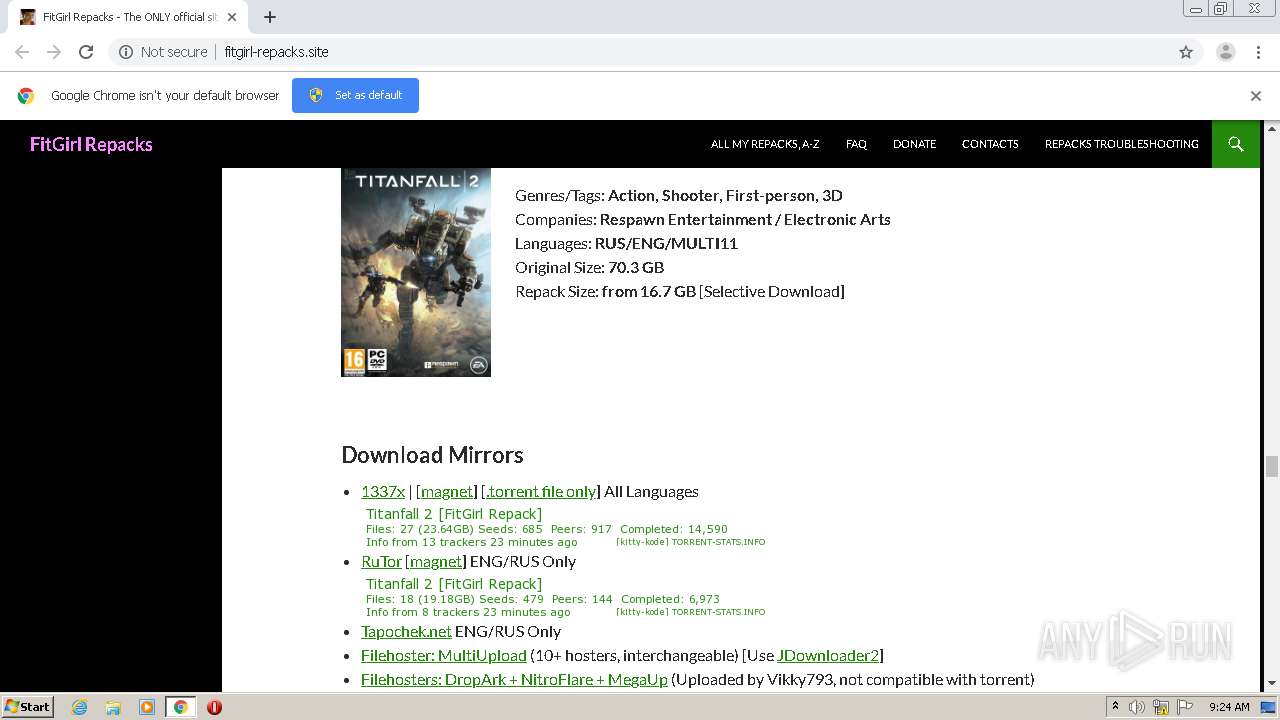
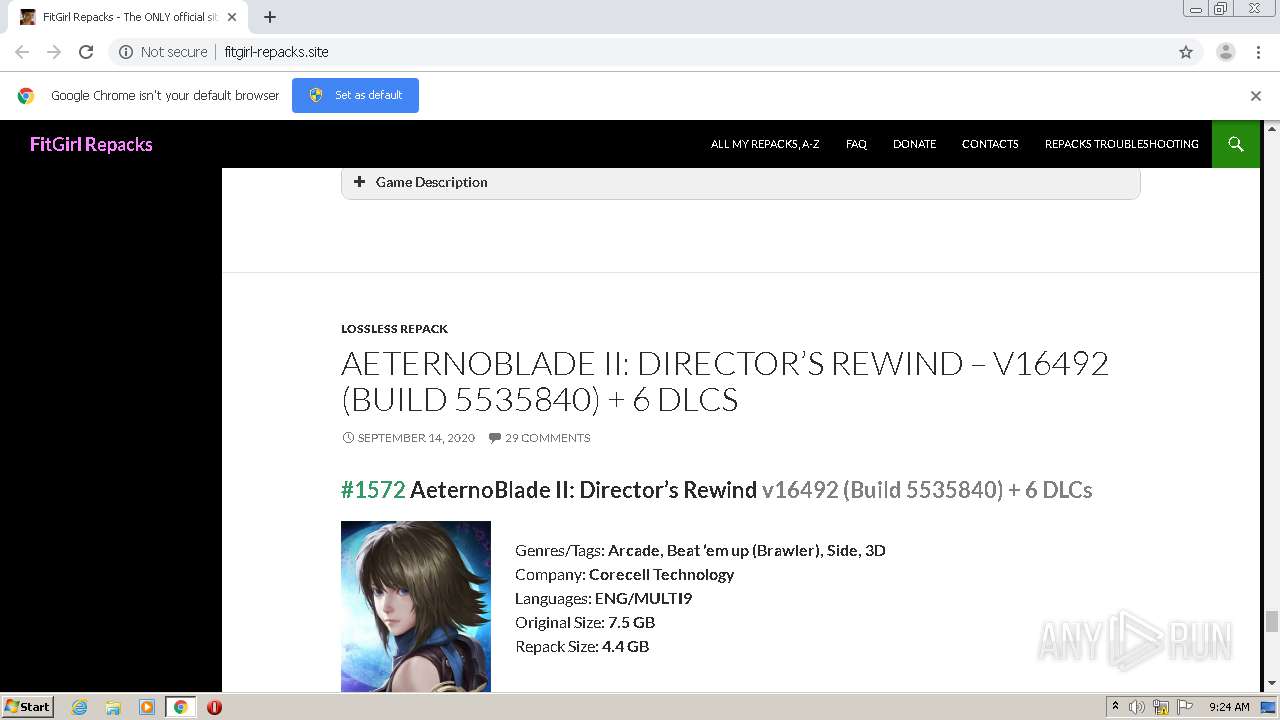
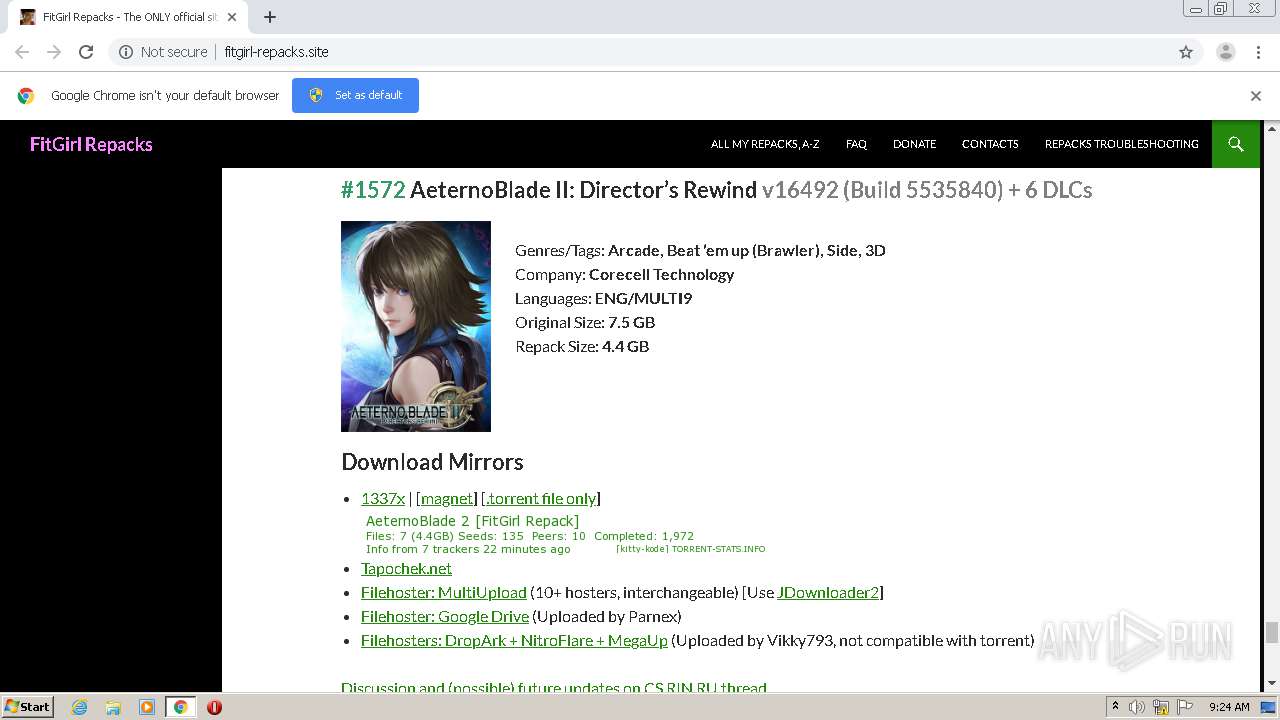
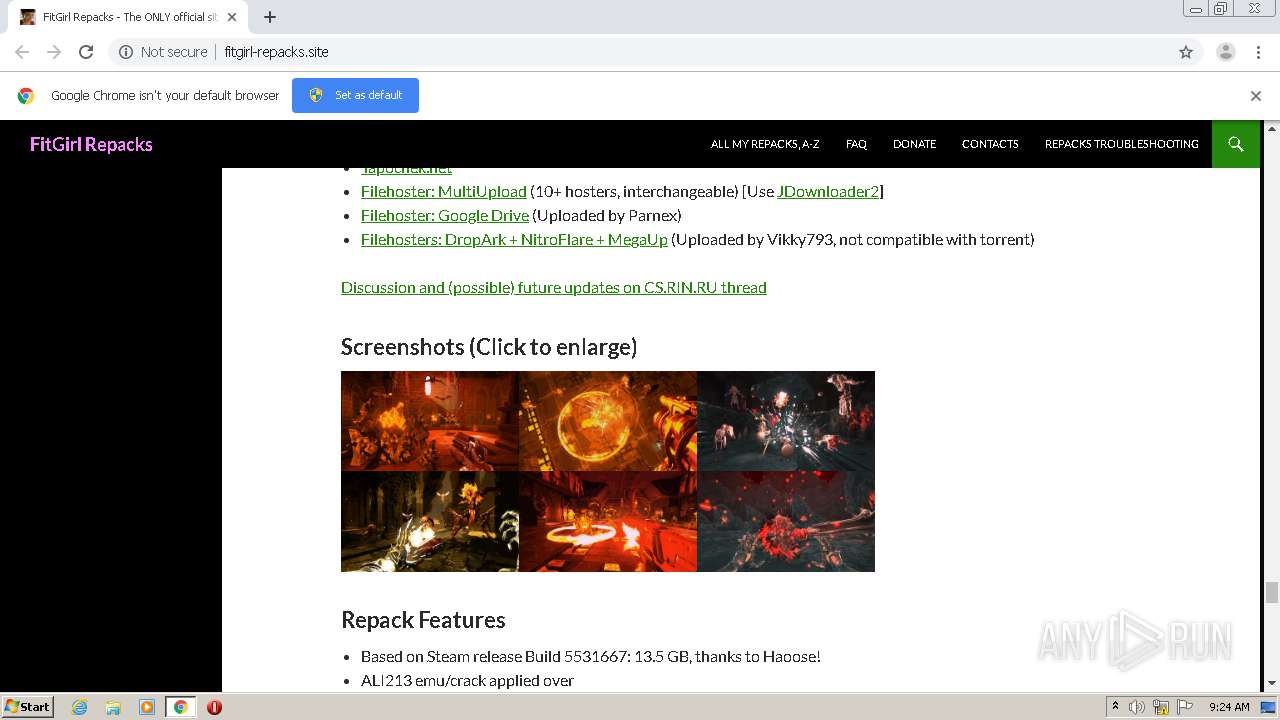
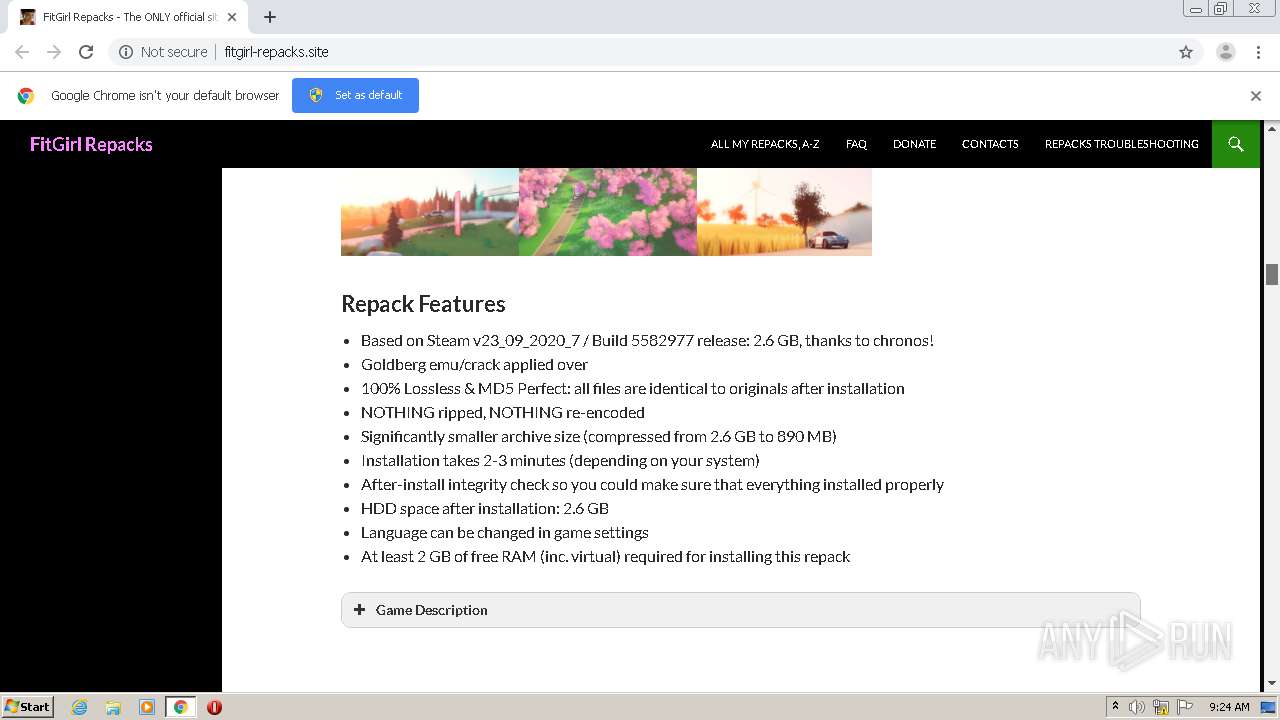
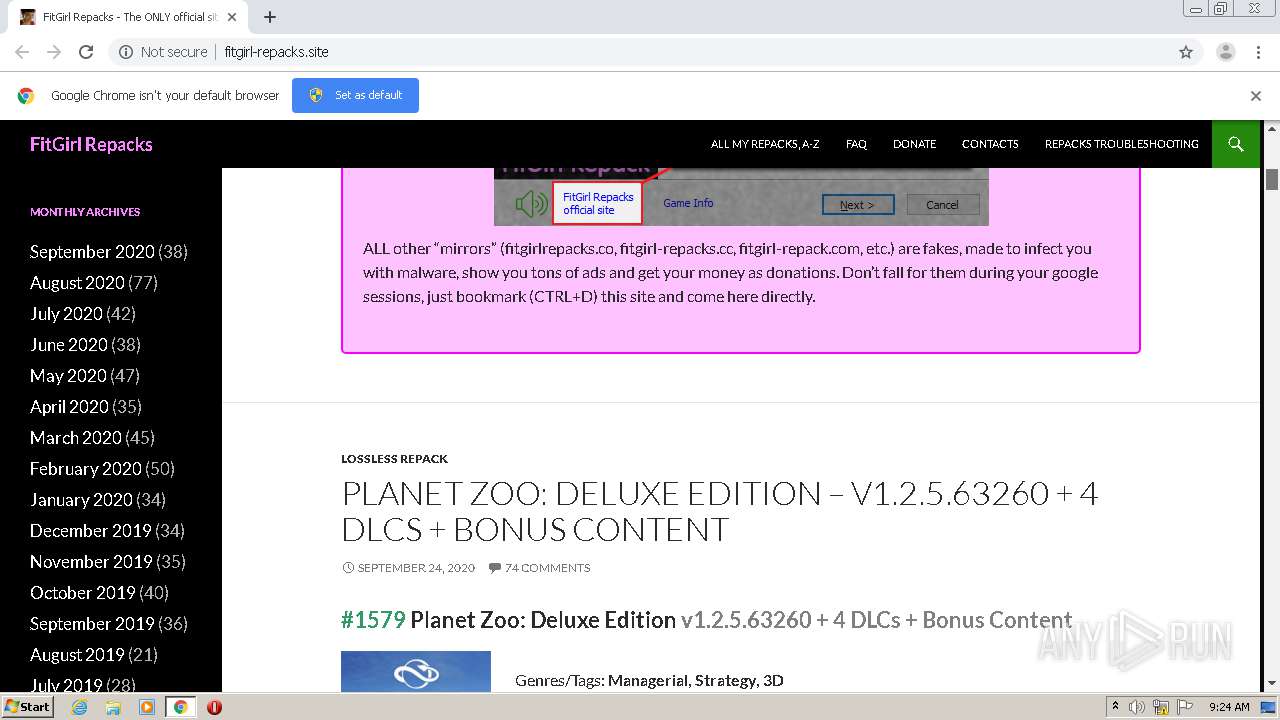
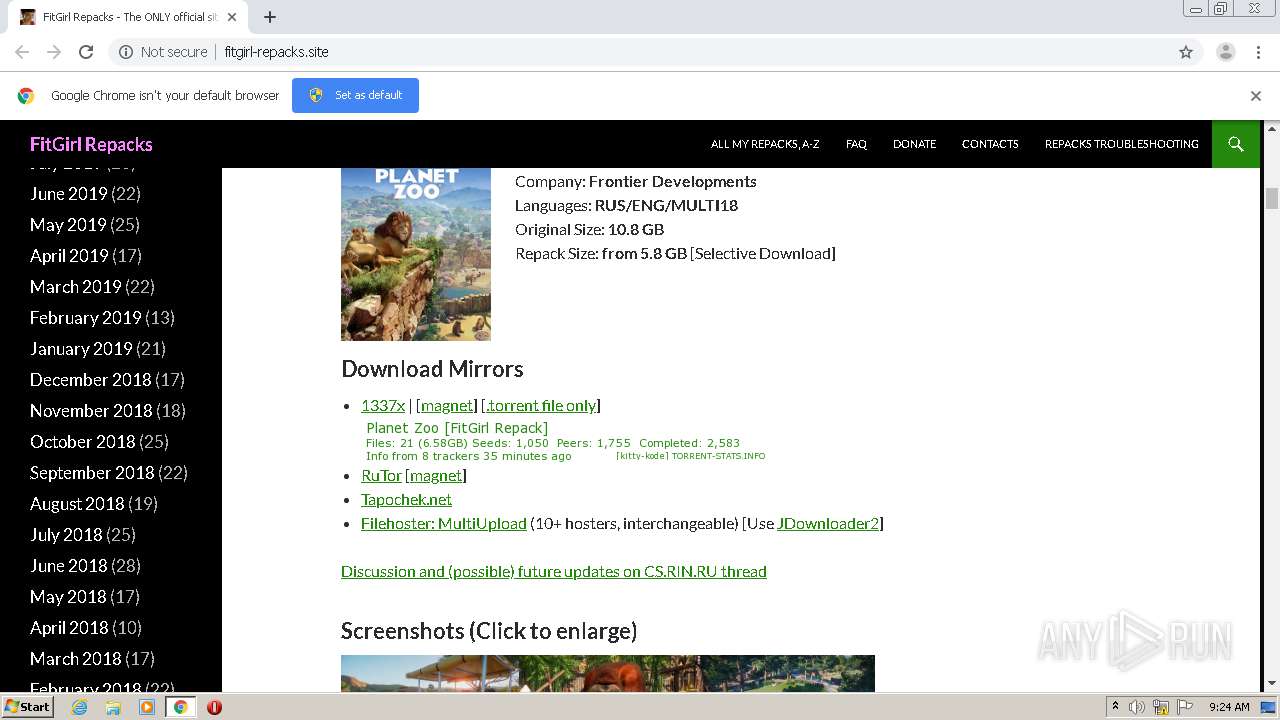
2356 | chrome.exe | GET | 200 | 104.28.19.127:80 | http://fitgirl-repacks.site/ | US | html | 25.3 Kb | suspicious |
2356 | chrome.exe | GET | 200 | 104.28.19.127:80 | http://fitgirl-repacks.site/wp-content/themes/twentyfourteen/style.css?ver=5.5 | US | text | 14.2 Kb | suspicious |
2356 | chrome.exe | GET | 200 | 104.28.19.127:80 | http://fitgirl-repacks.site/wp-content/plugins/jetpack/modules/theme-tools/compat/twentyfourteen.css?ver=5.5.2 | US | text | 1.62 Kb | suspicious |
2356 | chrome.exe | GET | 200 | 104.28.19.127:80 | http://fitgirl-repacks.site/wp-content/plugins/shortcodes-ultimate/includes/js/shortcodes/index.js?ver=5.6.1 | US | text | 3.33 Kb | suspicious |
2356 | chrome.exe | GET | 200 | 104.28.19.127:80 | http://fitgirl-repacks.site/wp-includes/css/dist/block-library/style.min.css?ver=5.5 | US | text | 7.95 Kb | suspicious |
2356 | chrome.exe | GET | 200 | 104.28.19.127:80 | http://fitgirl-repacks.site/wp-includes/js/jquery/jquery.js?ver=1.12.4-wp | US | text | 33.2 Kb | suspicious |
2356 | chrome.exe | GET | 200 | 104.28.19.127:80 | http://fitgirl-repacks.site/wp-content/plugins/jetpack/css/jetpack.css?ver=5.5.2 | US | text | 11.7 Kb | suspicious |
2356 | chrome.exe | GET | 200 | 104.28.19.127:80 | http://fitgirl-repacks.site/wp-includes/css/dashicons.min.css?ver=5.5 | US | text | 34.9 Kb | suspicious |
2356 | chrome.exe | GET | 200 | 104.28.19.127:80 | http://fitgirl-repacks.site/wp-content/plugins/wp-latest-posts/css/wplp_front.css?ver=5.5 | US | text | 3.15 Kb | suspicious |
2356 | chrome.exe | GET | 200 | 104.28.19.127:80 | http://fitgirl-repacks.site/wp-content/plugins/shortcodes-ultimate/includes/css/shortcodes.css?ver=5.6.1 | US | text | 7.70 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2356 | chrome.exe | 104.28.19.127:80 | fitgirl-repacks.site | Cloudflare Inc | US | suspicious |
2356 | chrome.exe | 172.217.22.237:443 | accounts.google.com | Google Inc. | US | unknown |
2356 | chrome.exe | 172.217.168.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2356 | chrome.exe | 80.233.186.12:443 | i112.fastpic.ru | Telia Latvija SIA | LV | unknown |
2356 | chrome.exe | 192.0.77.32:443 | s0.wp.com | Automattic, Inc | US | suspicious |
2356 | chrome.exe | 216.58.214.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2356 | chrome.exe | 172.217.22.206:443 | www.youtube.com | Google Inc. | US | whitelisted |
2356 | chrome.exe | 172.217.23.68:443 | www.google.com | Google Inc. | US | whitelisted |
2356 | chrome.exe | 172.217.22.238:443 | clients1.google.com | Google Inc. | US | whitelisted |
2356 | chrome.exe | 80.233.186.11:443 | i87.fastpic.ru | Telia Latvija SIA | LV | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
fitgirl-repacks.site |
| suspicious |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
s.w.org |
| whitelisted |
s0.wp.com |
| whitelisted |
i112.fastpic.ru |
| suspicious |
fonts.gstatic.com |
| whitelisted |
1337x.to |
| whitelisted |
cs.rin.ru |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |