| File name: | example.rtf |
| Full analysis: | https://app.any.run/tasks/c033e8dd-c4ba-47eb-95f9-5fff864bd3aa |
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2019, 05:51:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with no line terminators |
| MD5: | 48F31C6F2619441F9150C5182F33FED4 |
| SHA1: | 2D82997F01C11B1BE9AE0151613C7C6DA5F74DF3 |
| SHA256: | 68BB3E0D6AB40A2B59C19B7B1A88BC55C16932484E88D6FD000FA9AF68B5787E |
| SSDEEP: | 48:rOjNsP06EOWBgj5eaqJ6TDJT/hfJT/wJT/RVzwBrUQcQK49246JT/vWtp:rl06Lqgj5eaqW/mJwZ3Kw60P |
MALICIOUS
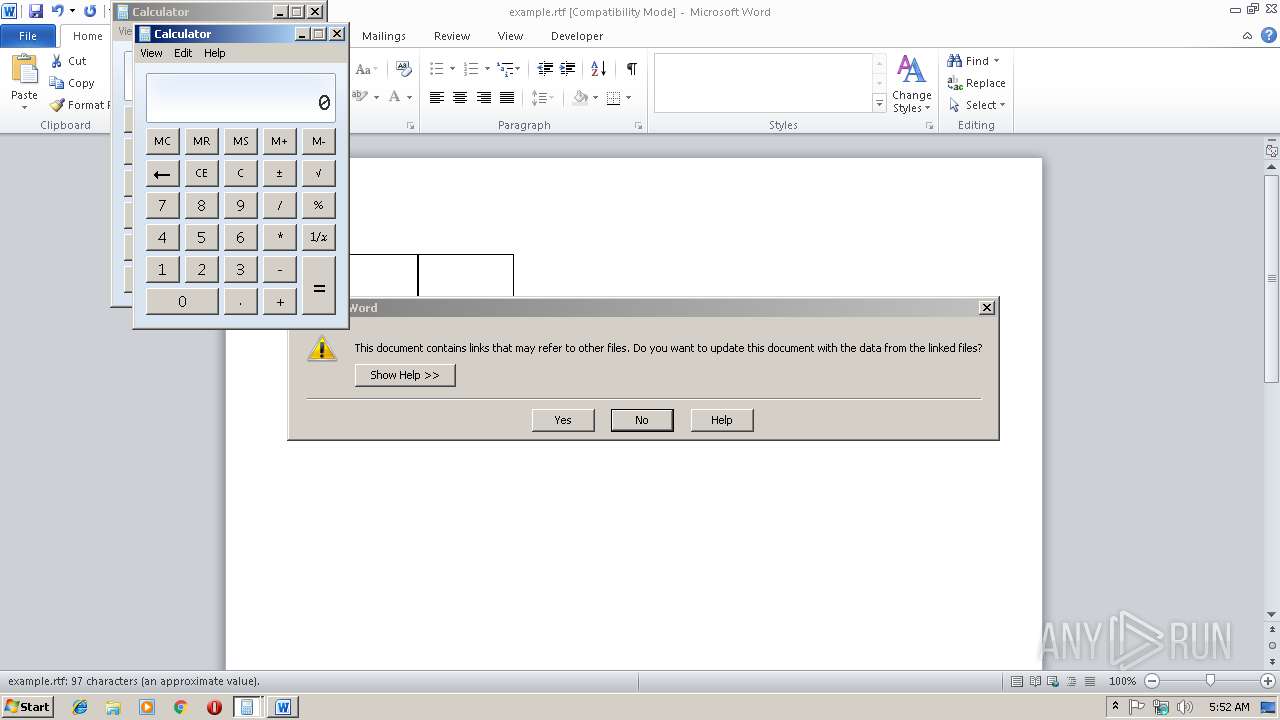
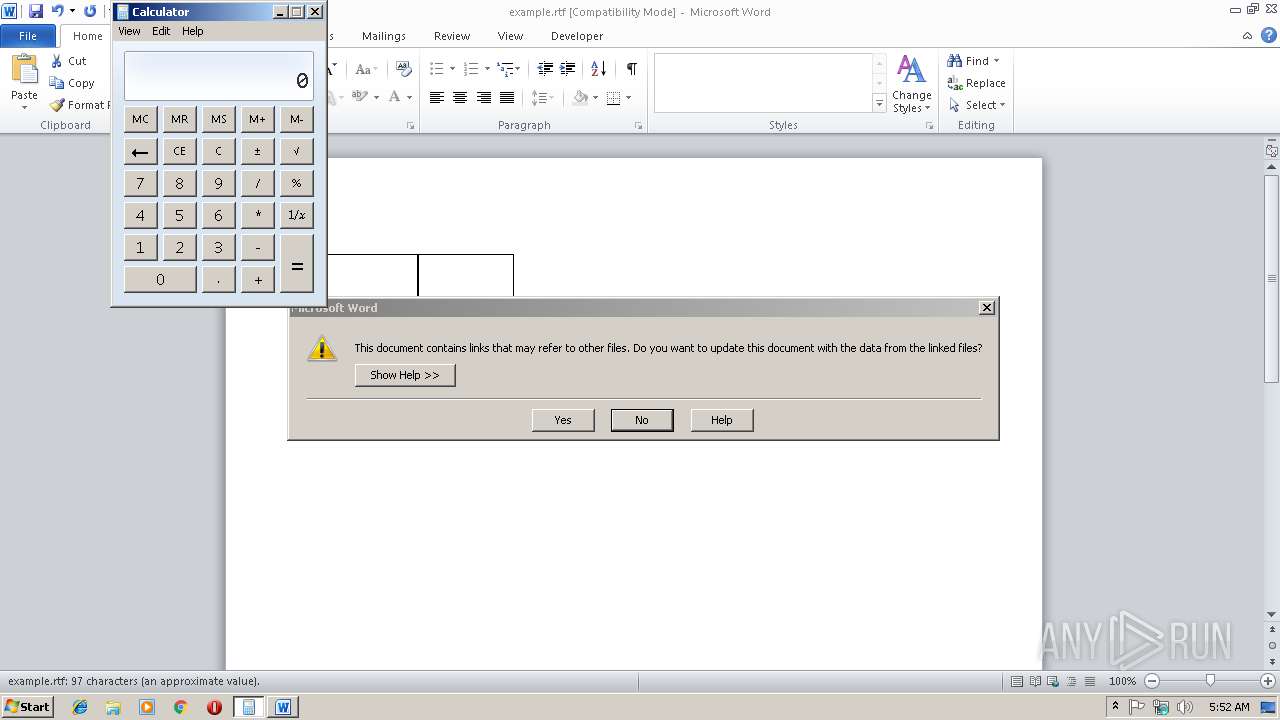
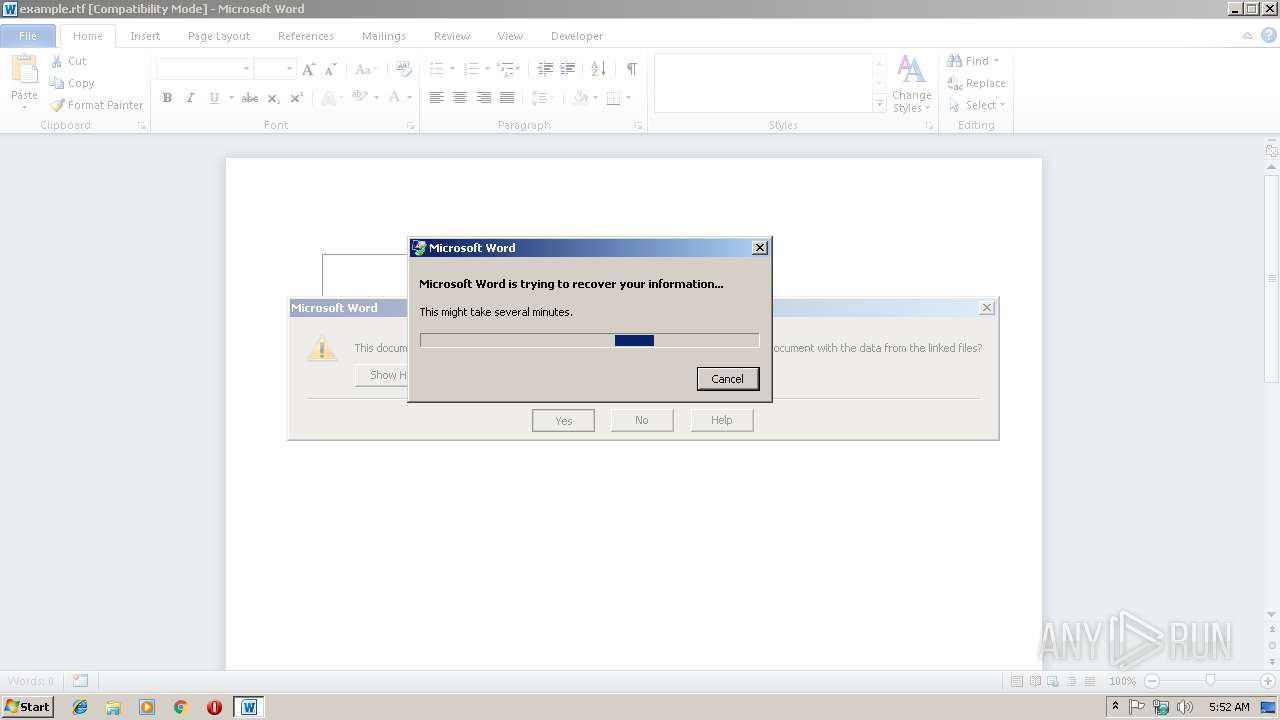
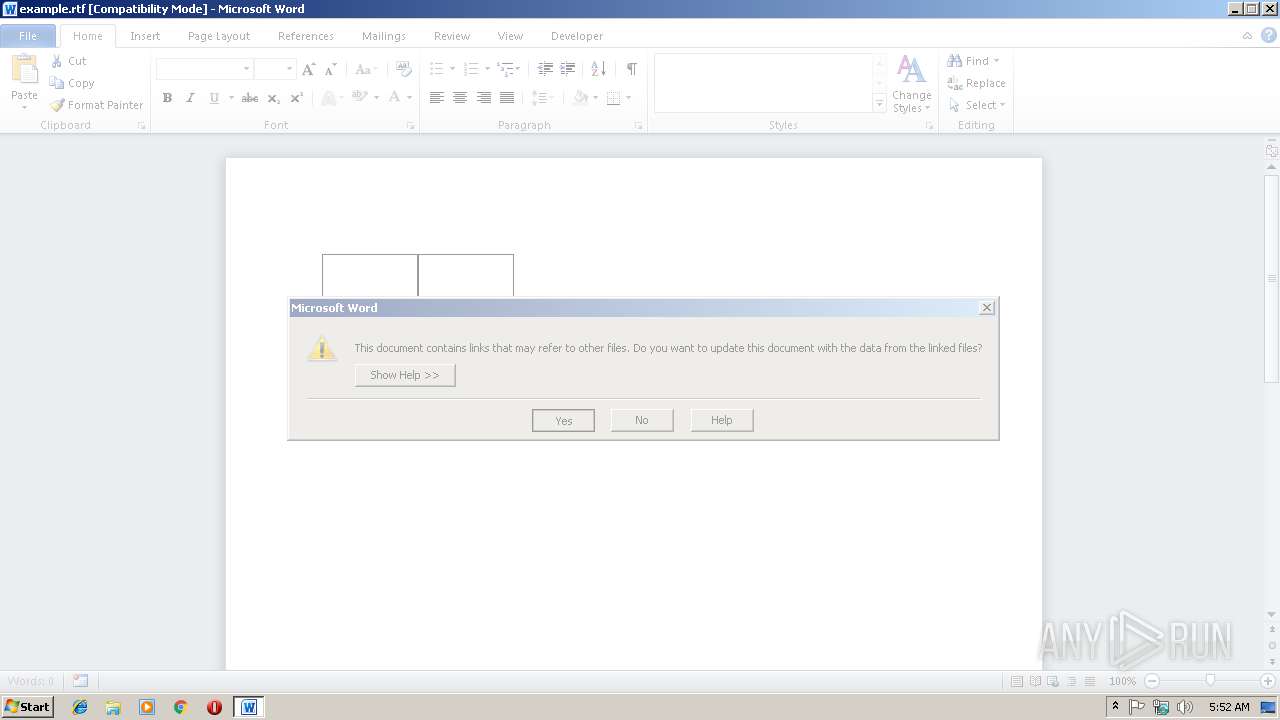
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2804)
SUSPICIOUS
No suspicious indicators.INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2804)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2804)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
33
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
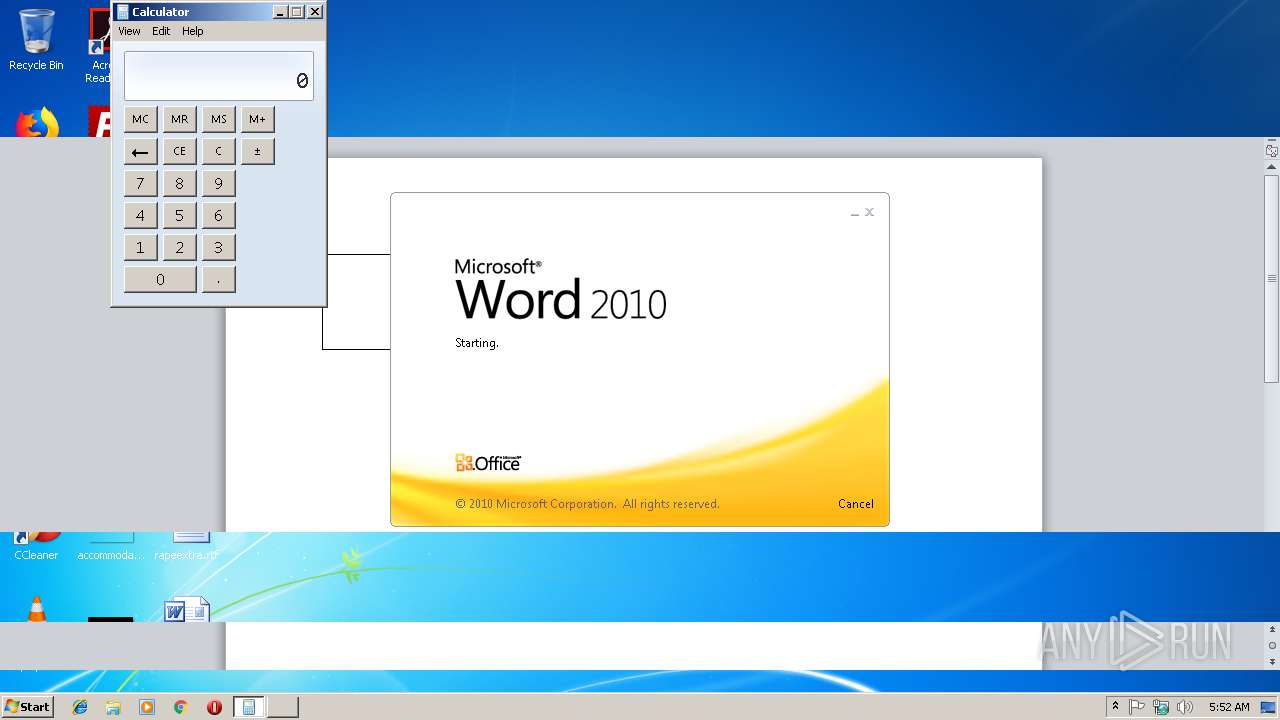
| 1948 | "C:\Windows\System32\calc.exe" | C:\Windows\System32\calc.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Calculator Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
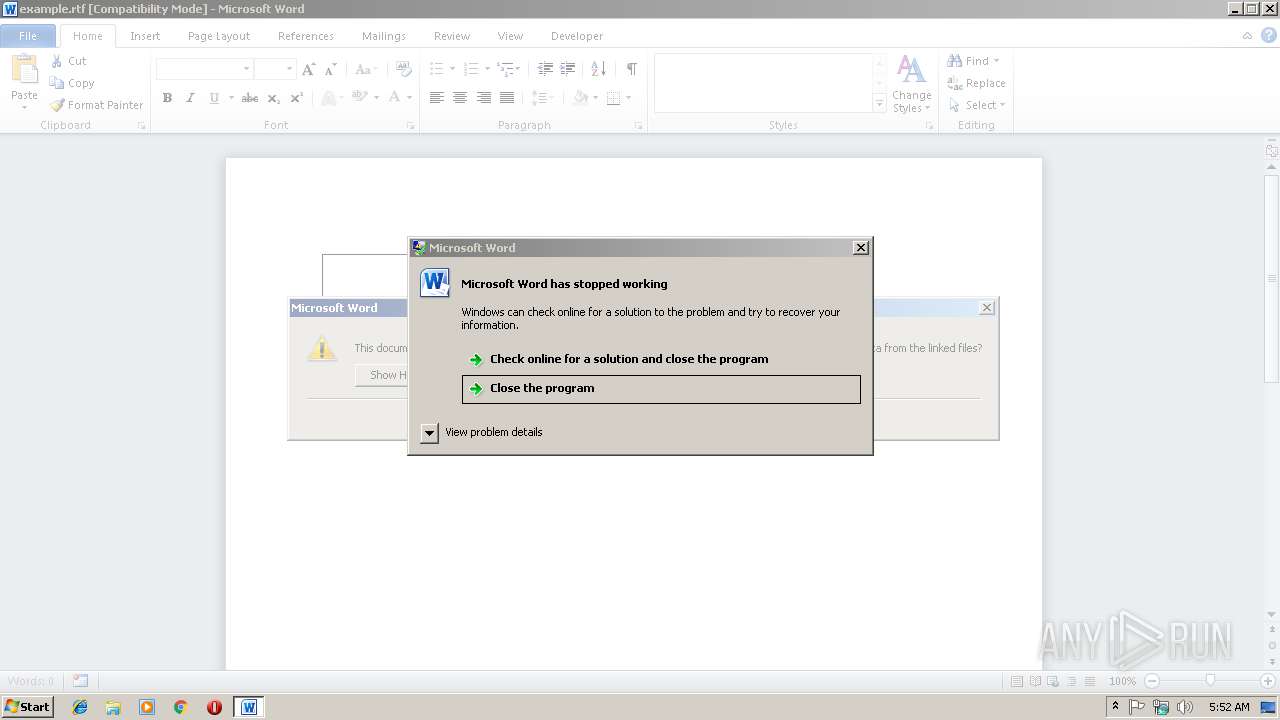
| 2580 | "C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE" -x -s 1348 | C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Application Error Reporting Exit code: 0 Version: 14.0.6015.1000 Modules
| |||||||||||||||
| 2804 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\example.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3680 | C:\Windows\system32\dwwin.exe -x -s 1348 | C:\Windows\system32\dwwin.exe | — | DW20.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Watson Client Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3708 | "C:\Windows\System32\calc.exe" | C:\Windows\System32\calc.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Calculator Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
732
Read events
695
Write events
35
Delete events
2
Modification events
| (PID) Process: | (2804) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | {0$ |
Value: 7B302400F40A0000010000000000000000000000 | |||
| (PID) Process: | (2804) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2804) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2804) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1314062366 | |||
| (PID) Process: | (2804) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1314062480 | |||
| (PID) Process: | (2804) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1314062481 | |||
| (PID) Process: | (2804) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: F40A0000767C553917C8D40100000000 | |||
| (PID) Process: | (2804) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 2$ |
Value: 20322400F40A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2804) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 2$ |
Value: 20322400F40A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2804) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
5
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2804 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR98CB.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2804 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{E9B5C50B-96A0-41DB-8BB7-089D393CEB15}.tmp | — | |
MD5:— | SHA256:— | |||
| 2804 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{188F40FB-AC26-4613-AC04-CFFF591997D3}.tmp | — | |
MD5:— | SHA256:— | |||
| 2804 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFBC896C97DB180C2E.TMP | — | |
MD5:— | SHA256:— | |||
| 3680 | dwwin.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportArchive\AppCrash_WINWORD.EXE_382c76d25639807cee55a78b73ffed14addcc43_0e7a0c55\Report.wer | binary | |
MD5:— | SHA256:— | |||
| 2804 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Word\LiveRecovery save of example.asd | document | |
MD5:— | SHA256:— | |||
| 2804 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Word\~WRL0001.tmp | document | |
MD5:— | SHA256:— | |||
| 2804 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2804 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Word\~WRD0000.tmp | document | |
MD5:— | SHA256:— | |||
| 2804 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{4E01AAB1-1ADC-47F5-92E6-6DDF87BF159B}.tmp | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report